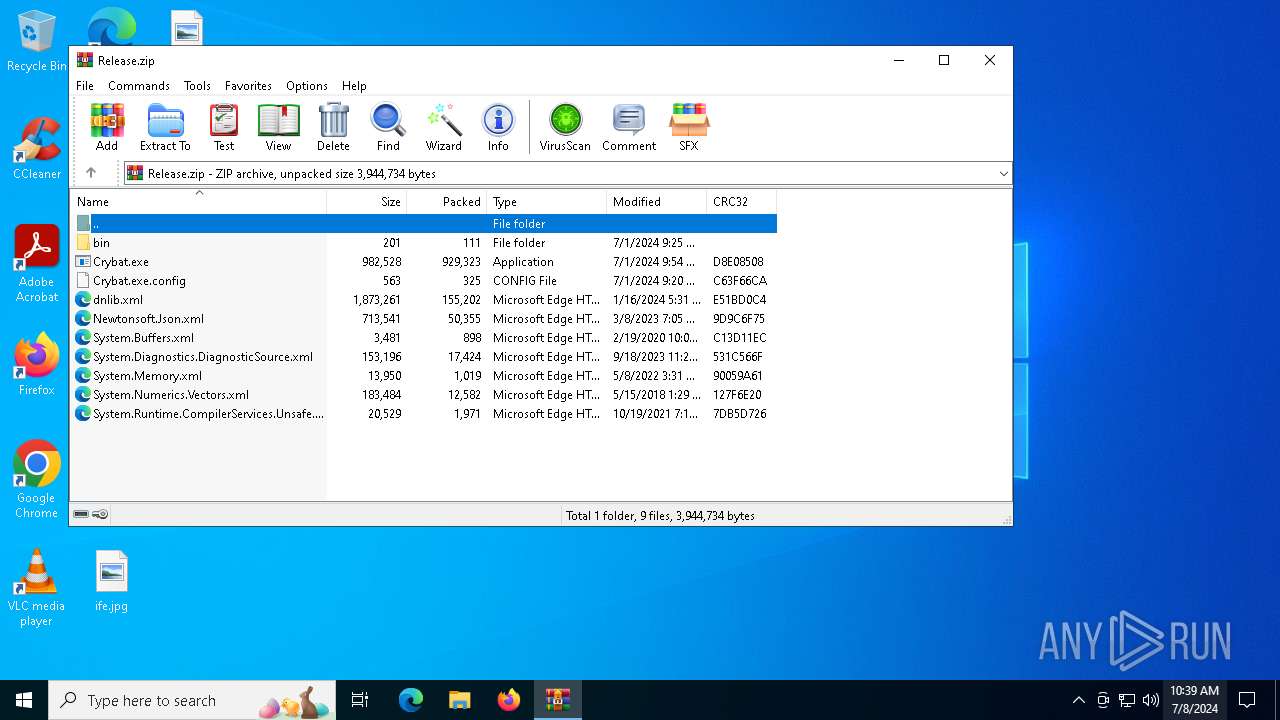
| File name: | Release.zip |
| Full analysis: | https://app.any.run/tasks/d5ad4bde-9211-4e11-868a-482b784e71ef |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2024, 10:39:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 0732D394560BB5EBA4AFBDF4C62D27F4 |
| SHA1: | 1FEEA0BCC9D9B4149C1CB6A000E05C0817FB6E31 |
| SHA256: | 33F2F6C55B6DC7BA169BA10DE870F41D881414C84A02C25998C65FB5980CD0C3 |
| SSDEEP: | 49152:kWmBzs0QTF7+mdz89BQZXXPl6XTjVjz9JxH+WKVKTUmRpFMDxfMsctnHQu6dpIXZ:kLA0KFamdg9BQ9/l6XT5xrBTUmcfMs0J |
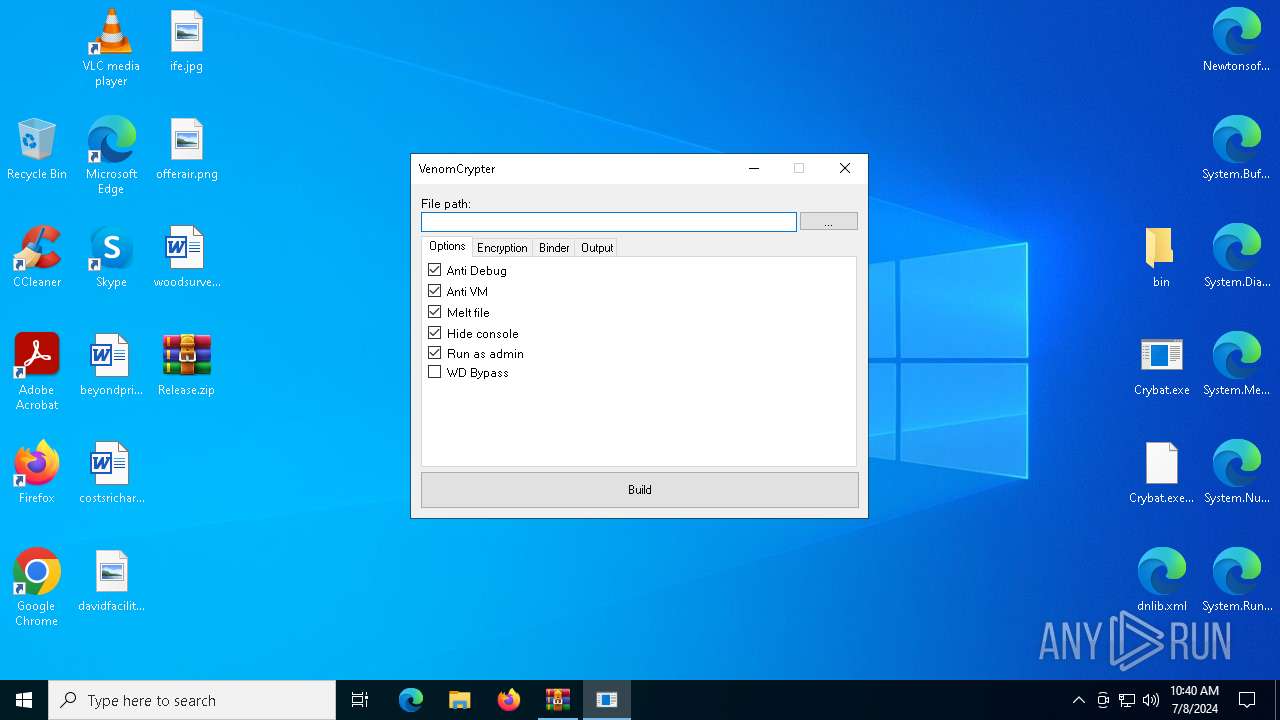
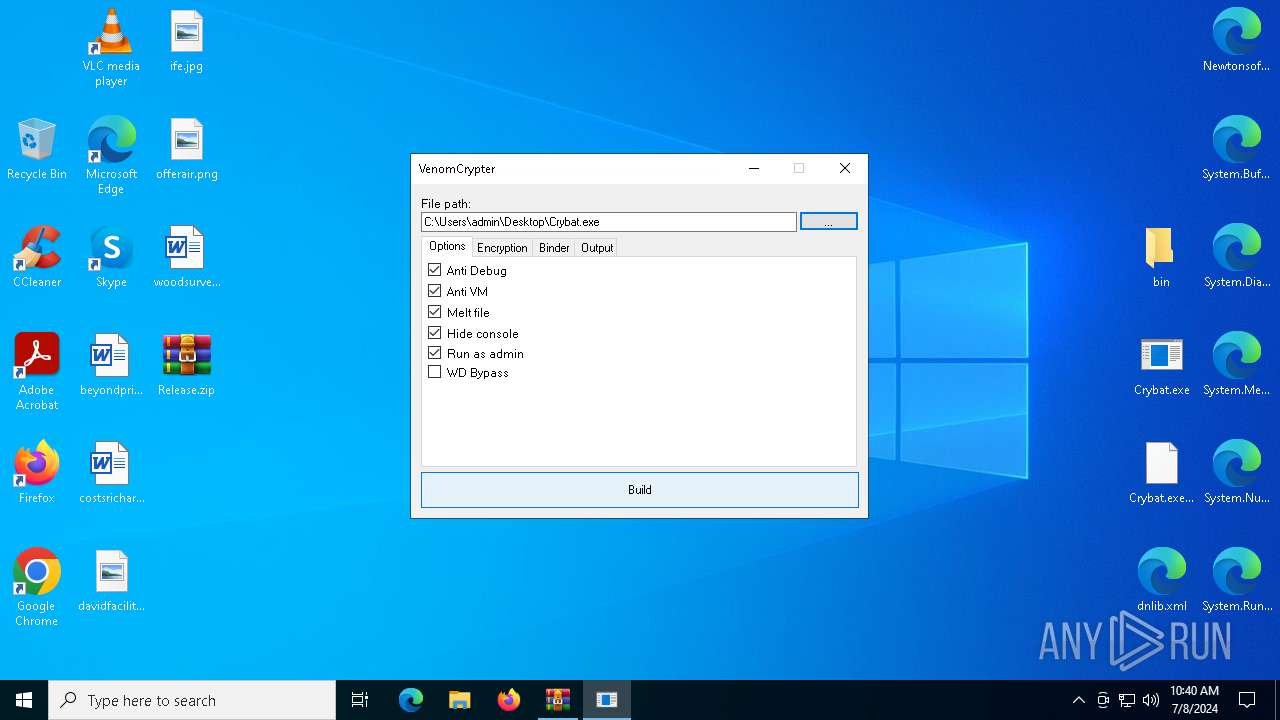
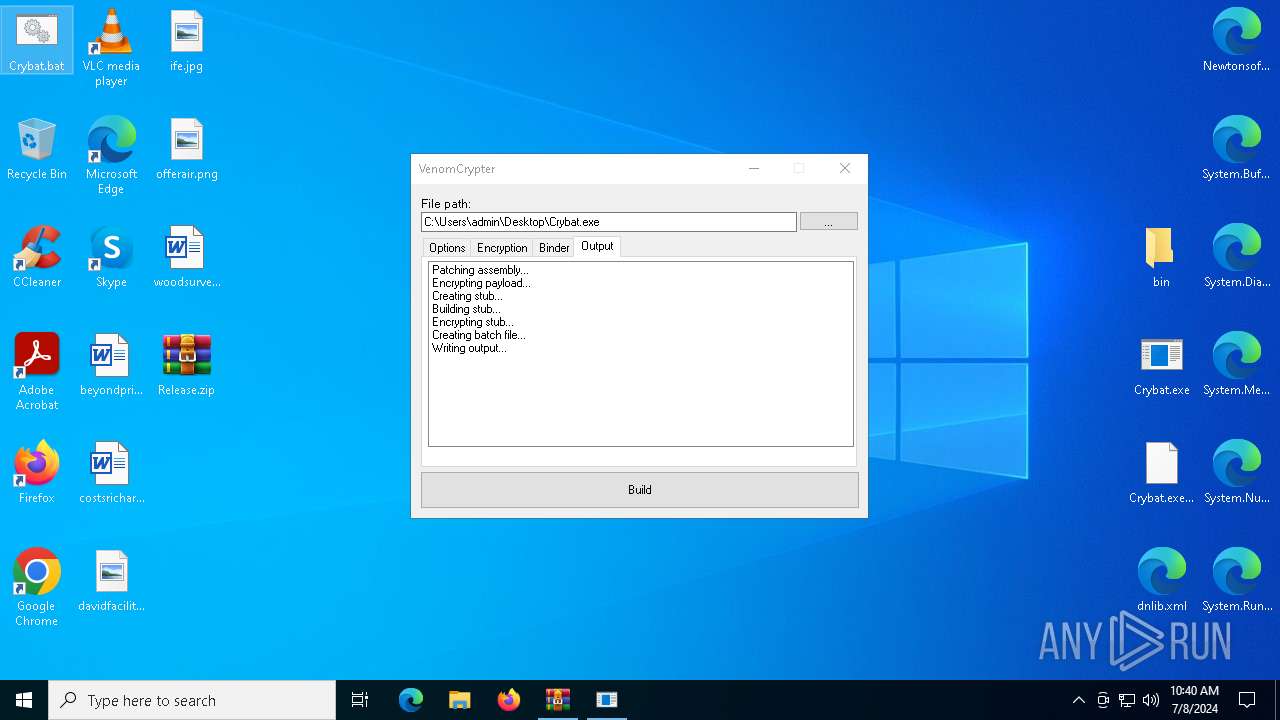
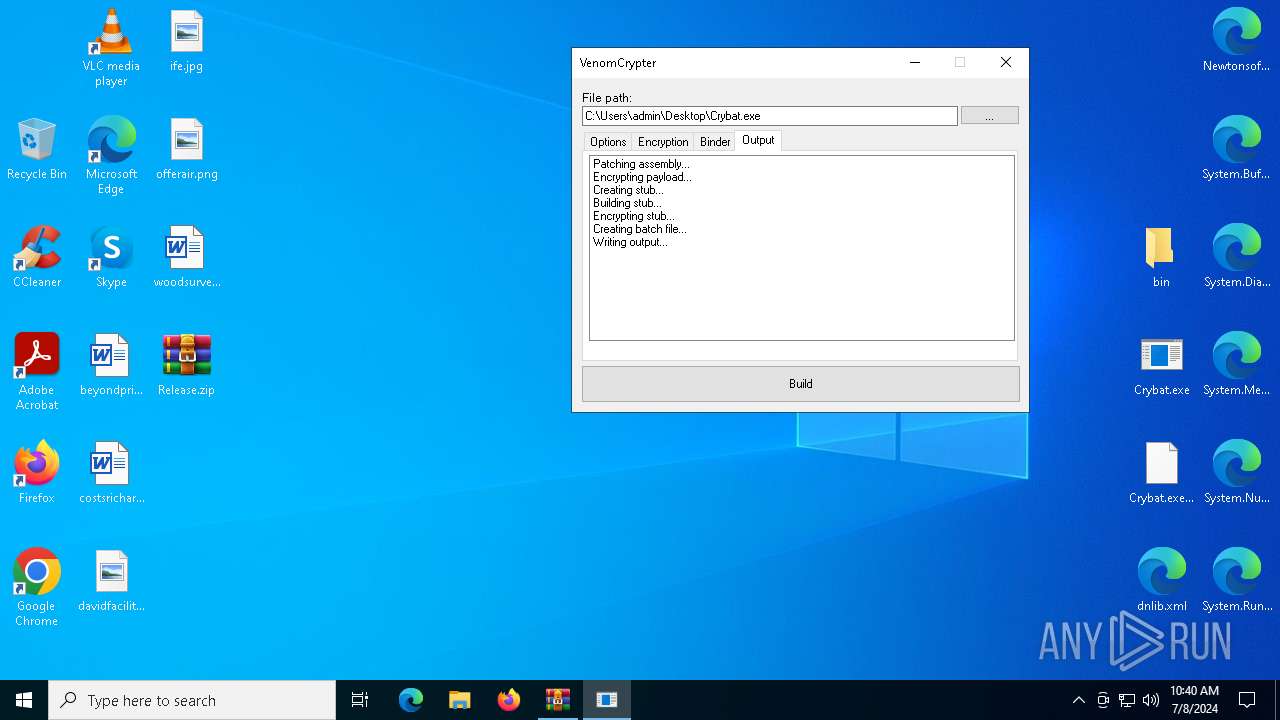
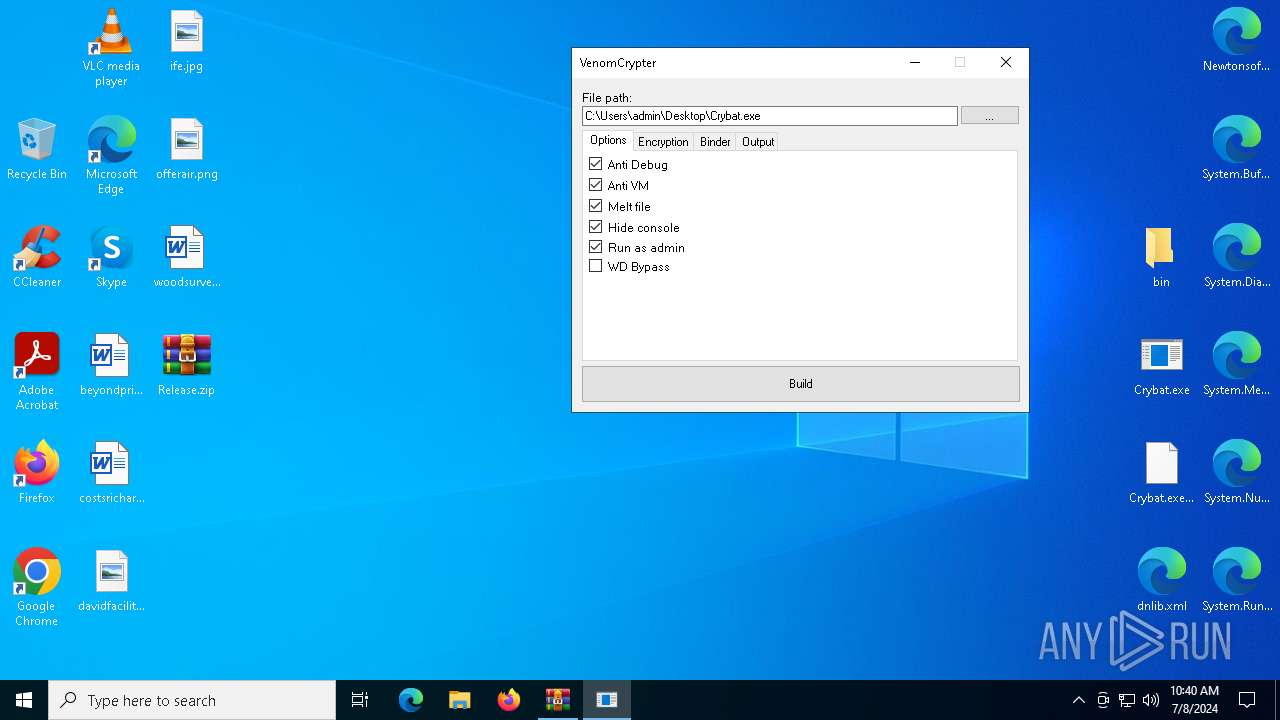
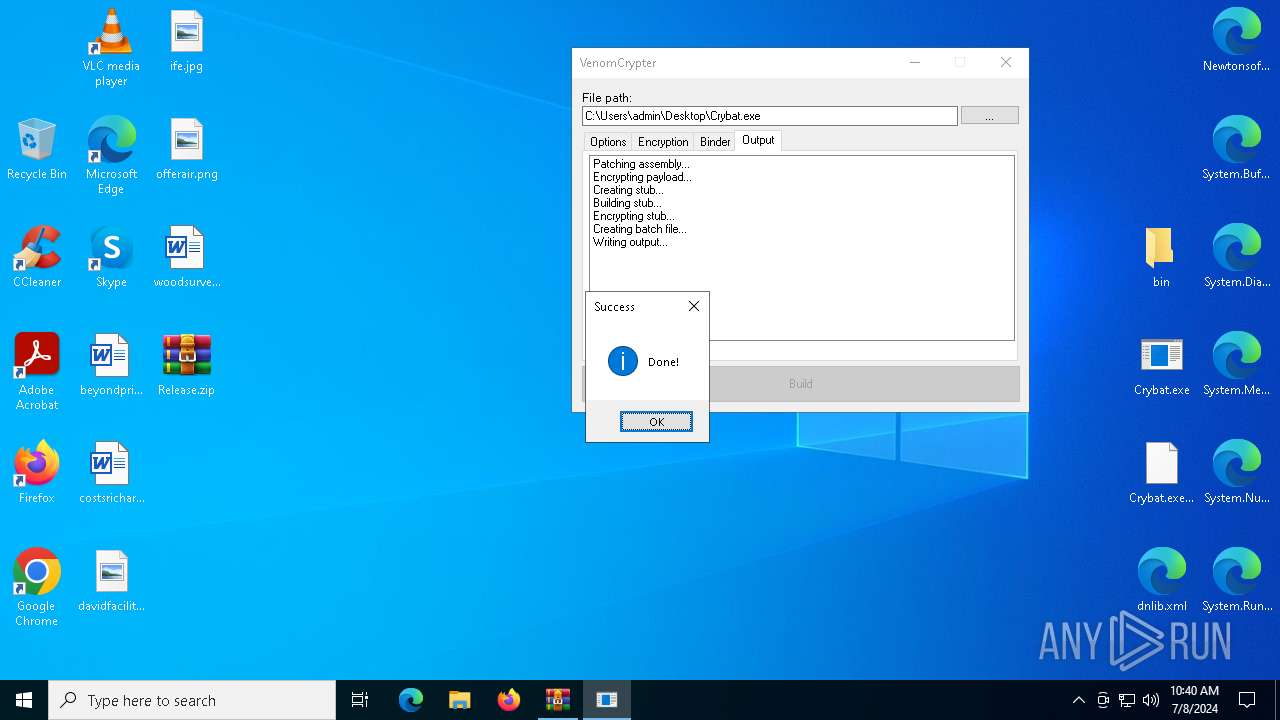
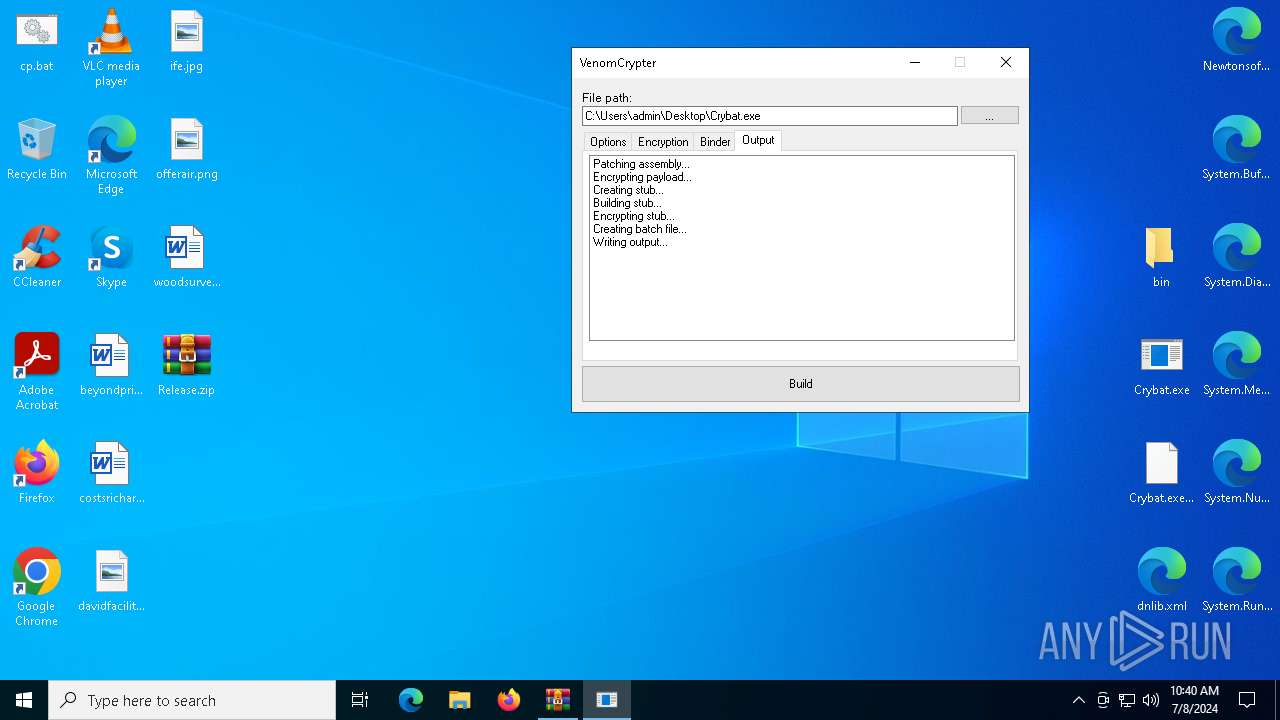
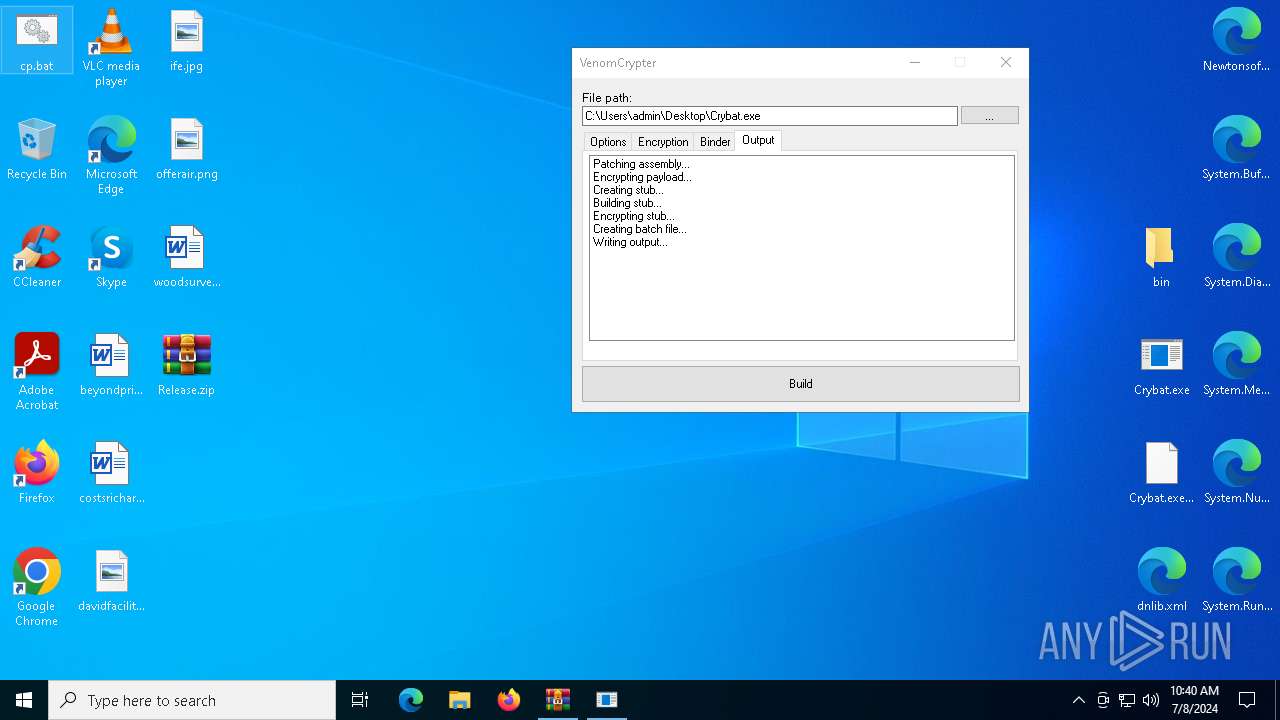
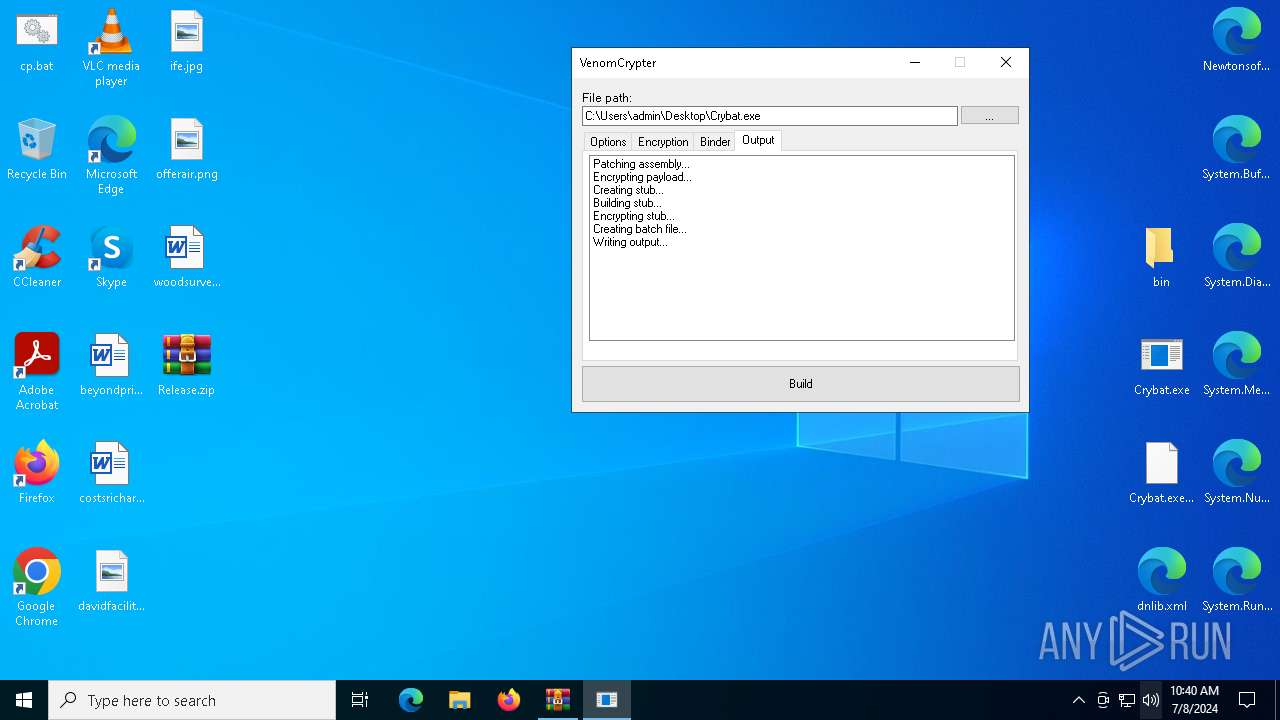
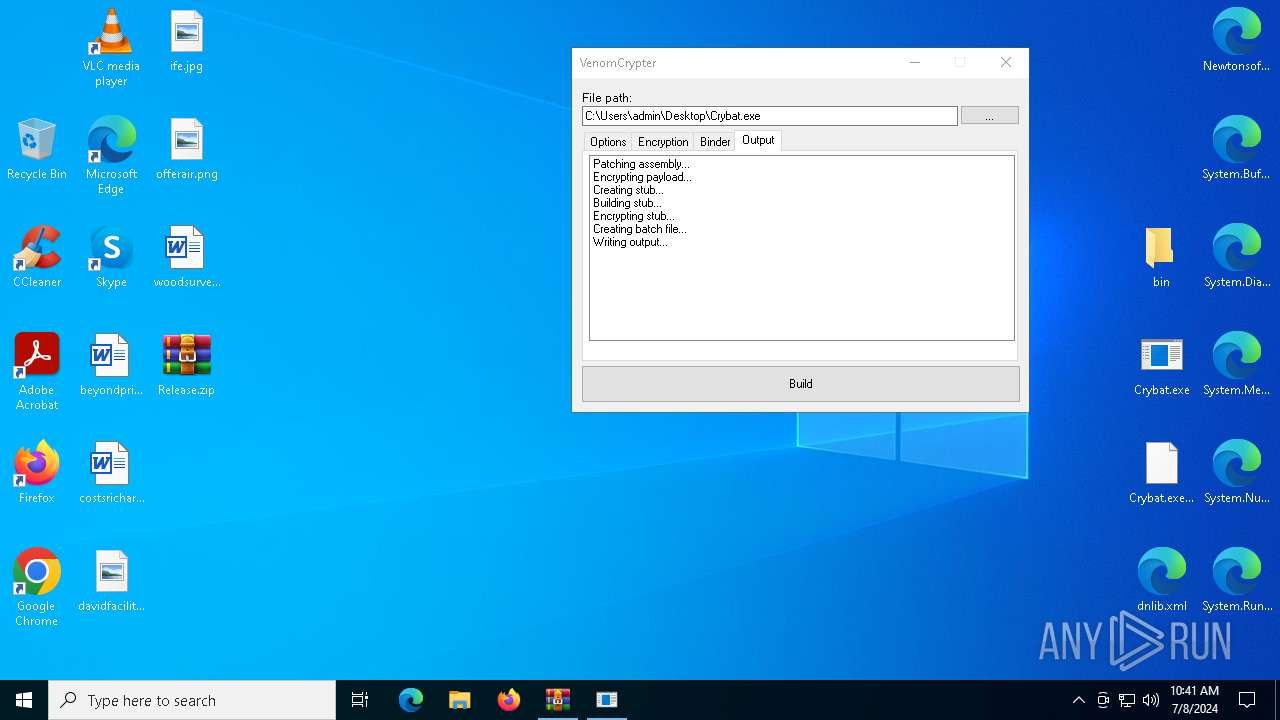
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4976)
- csc.exe (PID: 6760)
- csc.exe (PID: 2060)
Starts Visual C# compiler
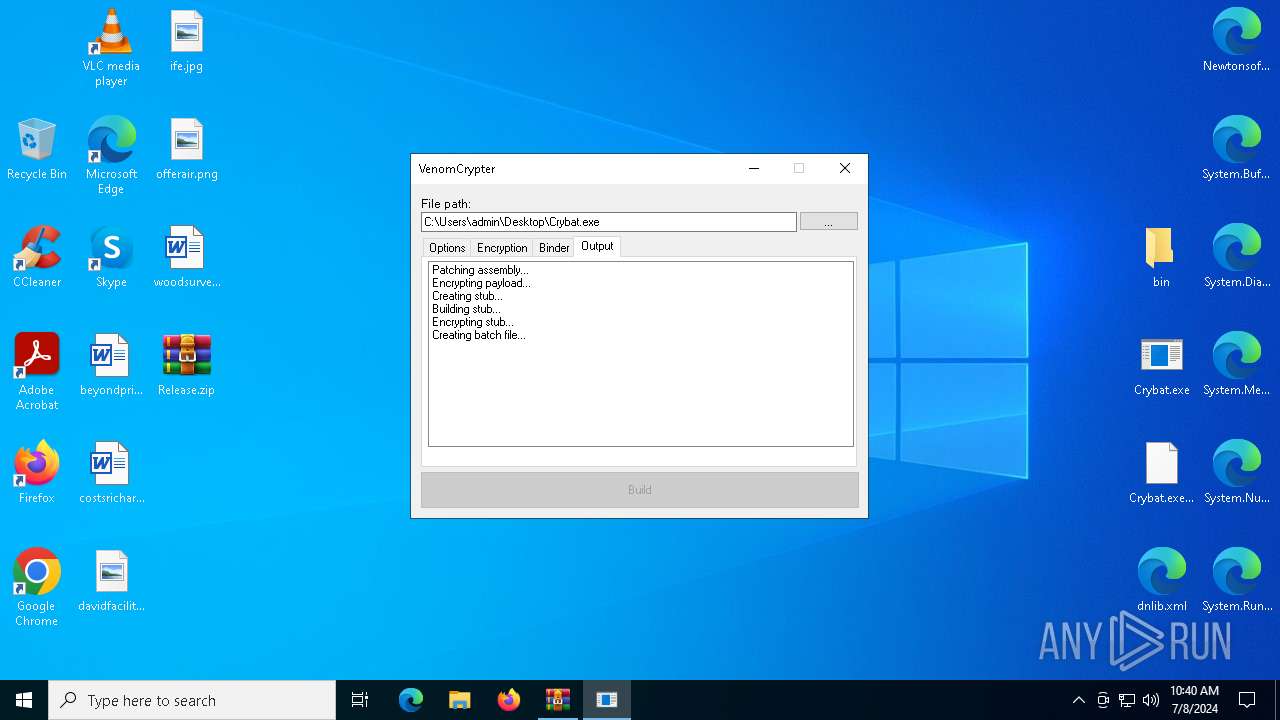
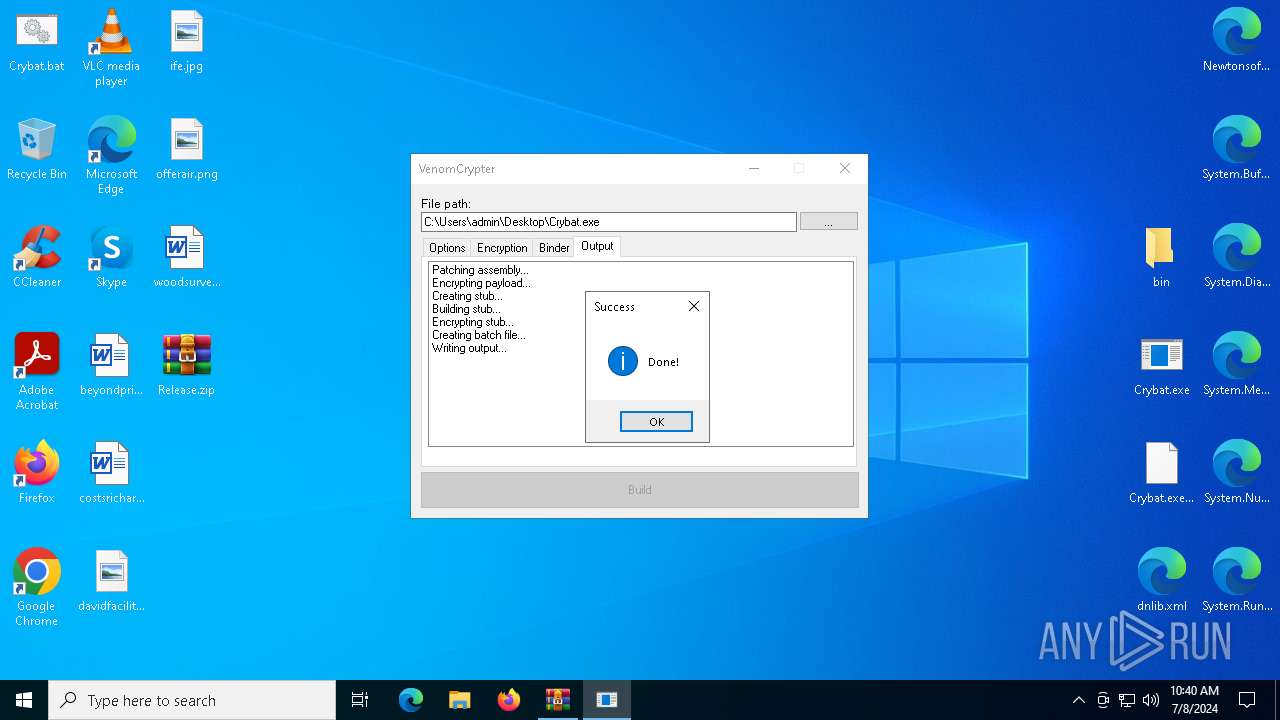
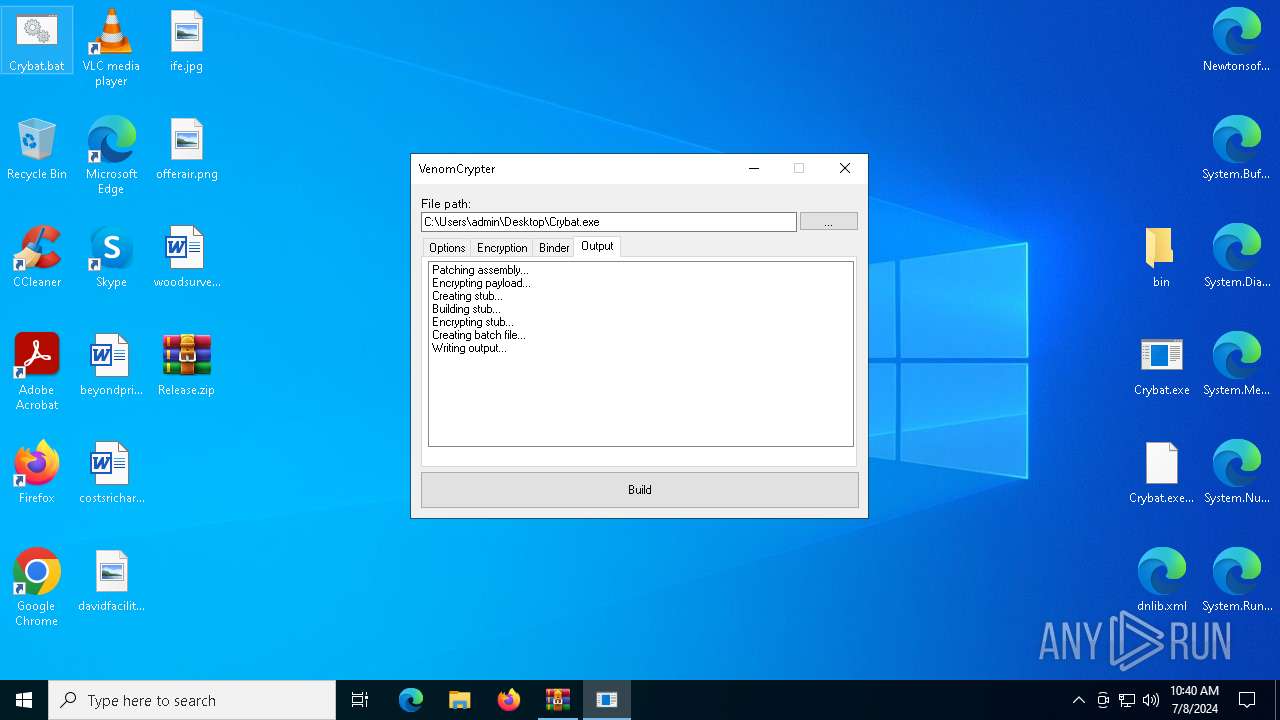
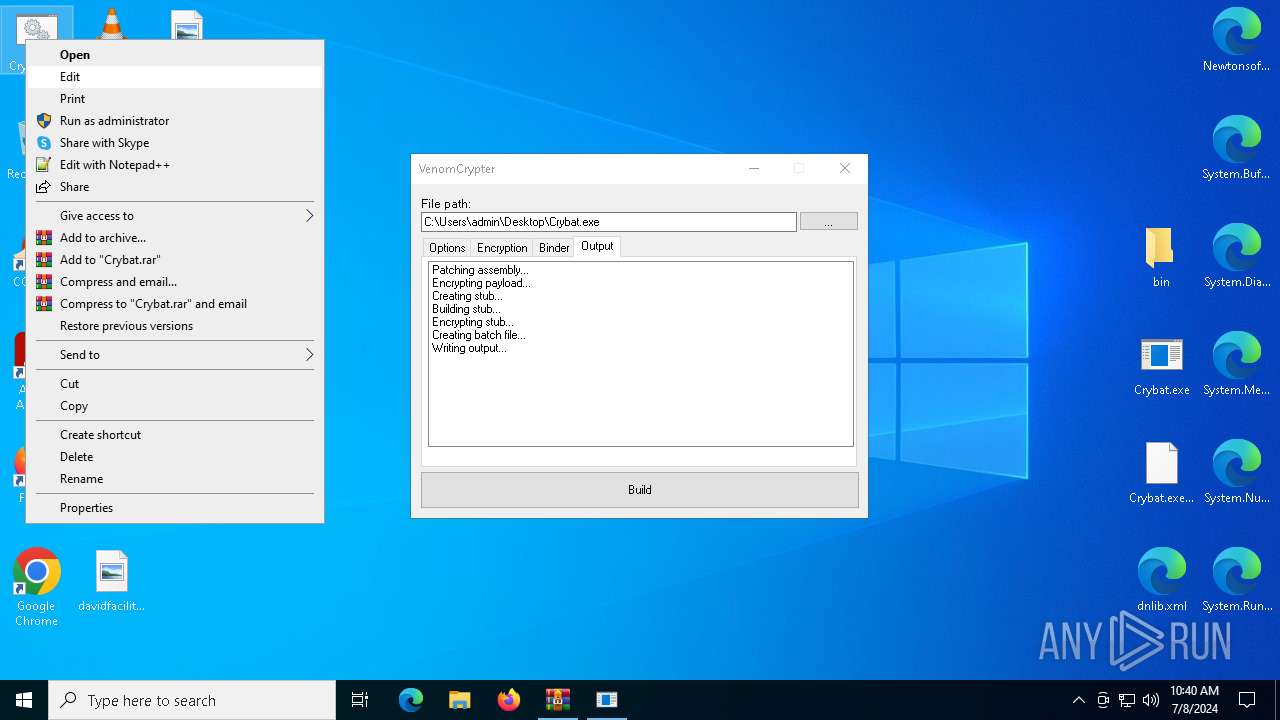
- Crybat.exe (PID: 4072)
SUSPICIOUS
Reads security settings of Internet Explorer
- Crybat.exe (PID: 4072)
Uses .NET C# to load dll
- Crybat.exe (PID: 4072)
Executable content was dropped or overwritten
- csc.exe (PID: 6760)
- csc.exe (PID: 2060)
INFO
Checks supported languages
- Crybat.exe (PID: 4072)
- csc.exe (PID: 6760)
- cvtres.exe (PID: 448)
- cvtres.exe (PID: 7068)
- csc.exe (PID: 2060)
Reads Environment values
- Crybat.exe (PID: 4072)
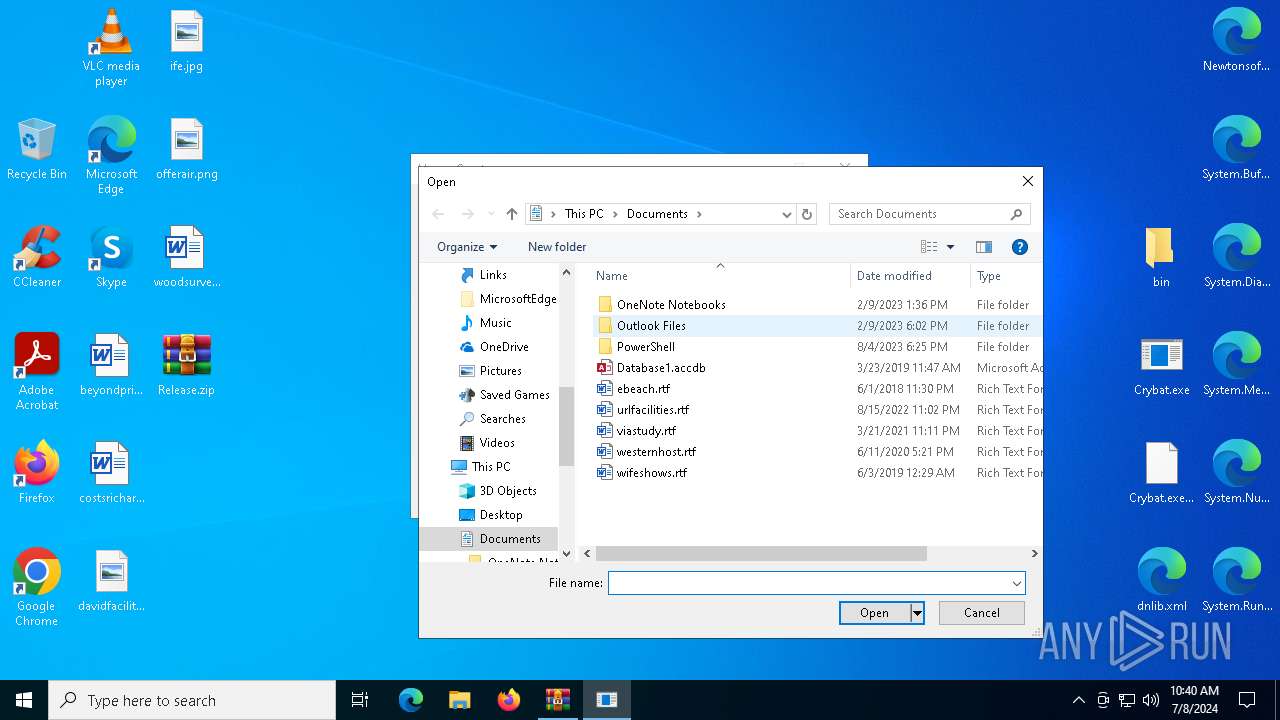
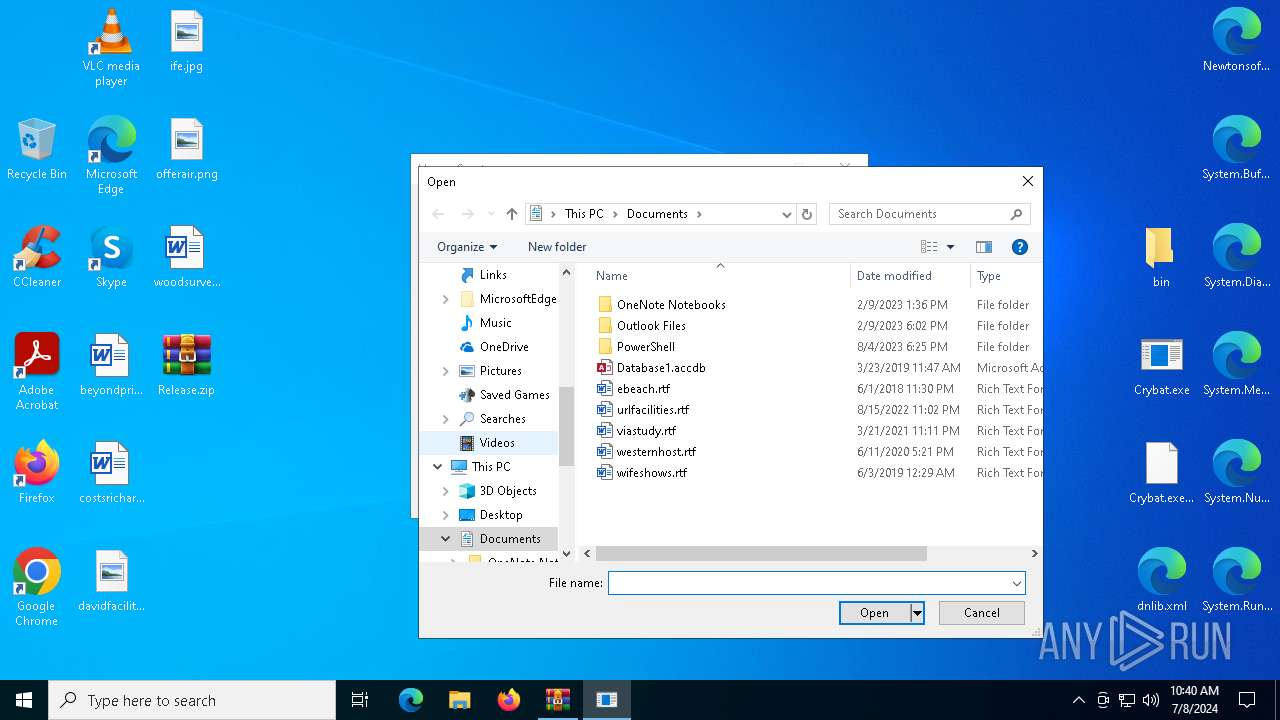
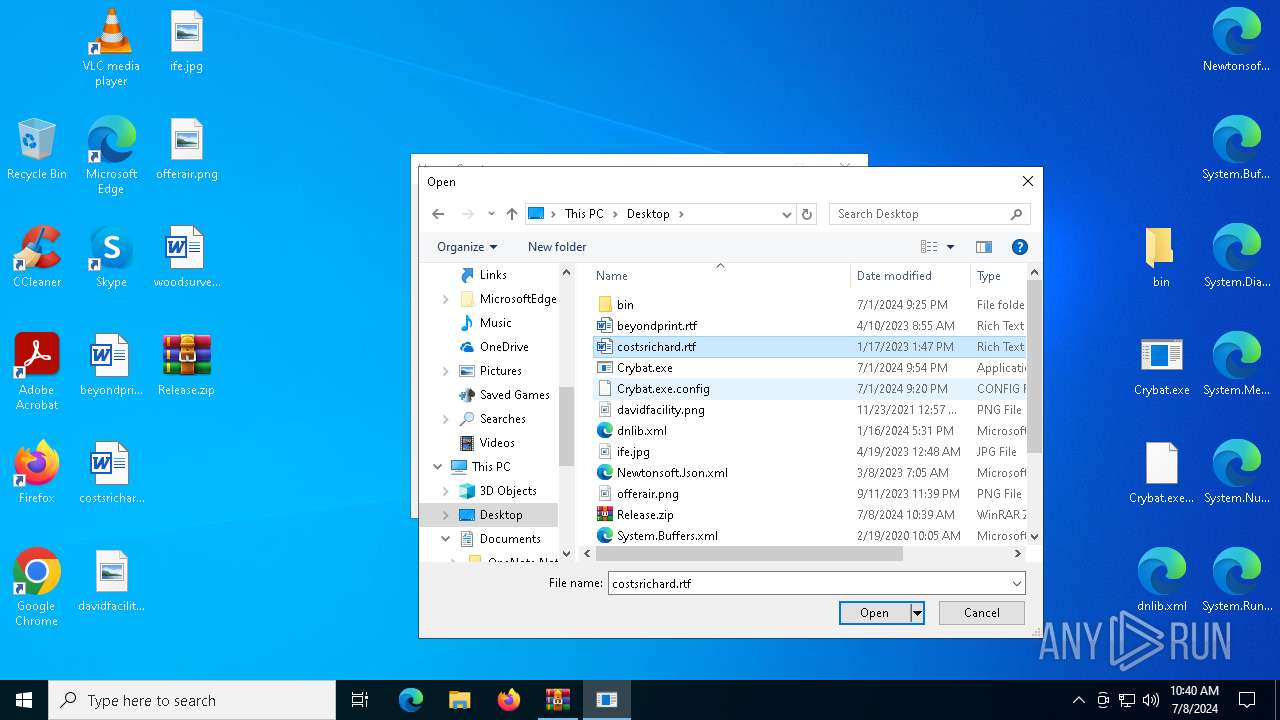
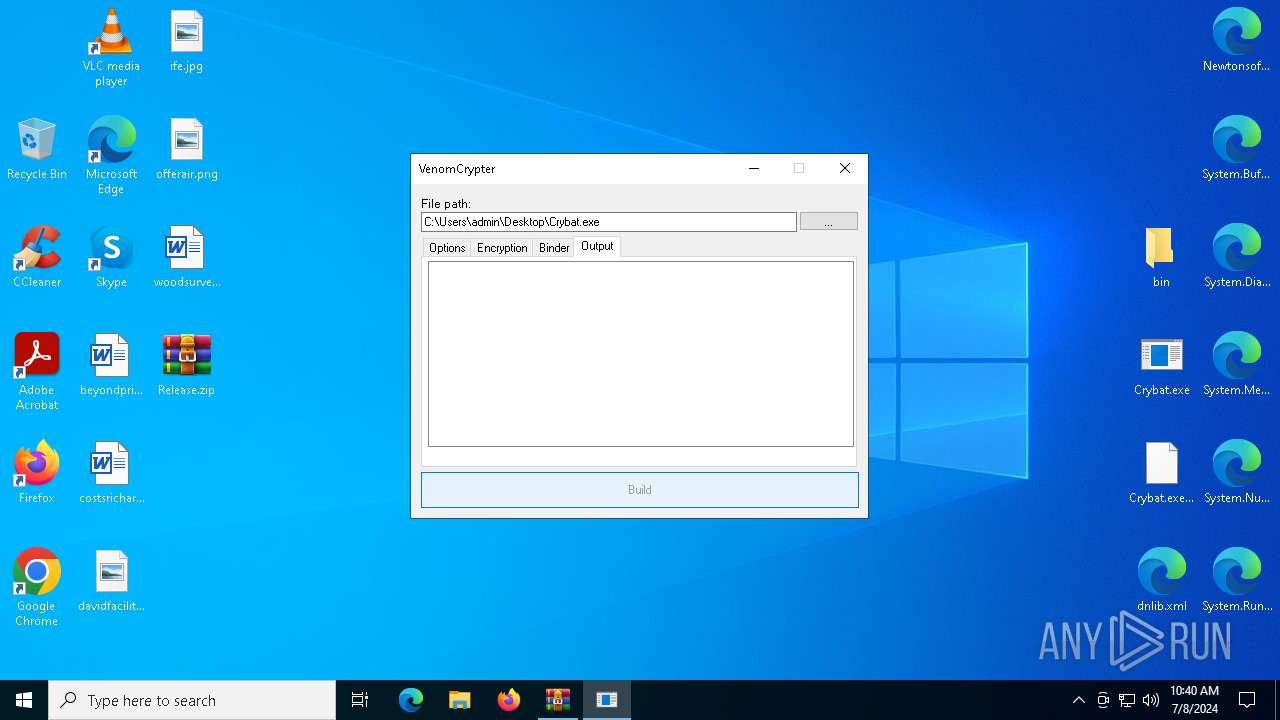
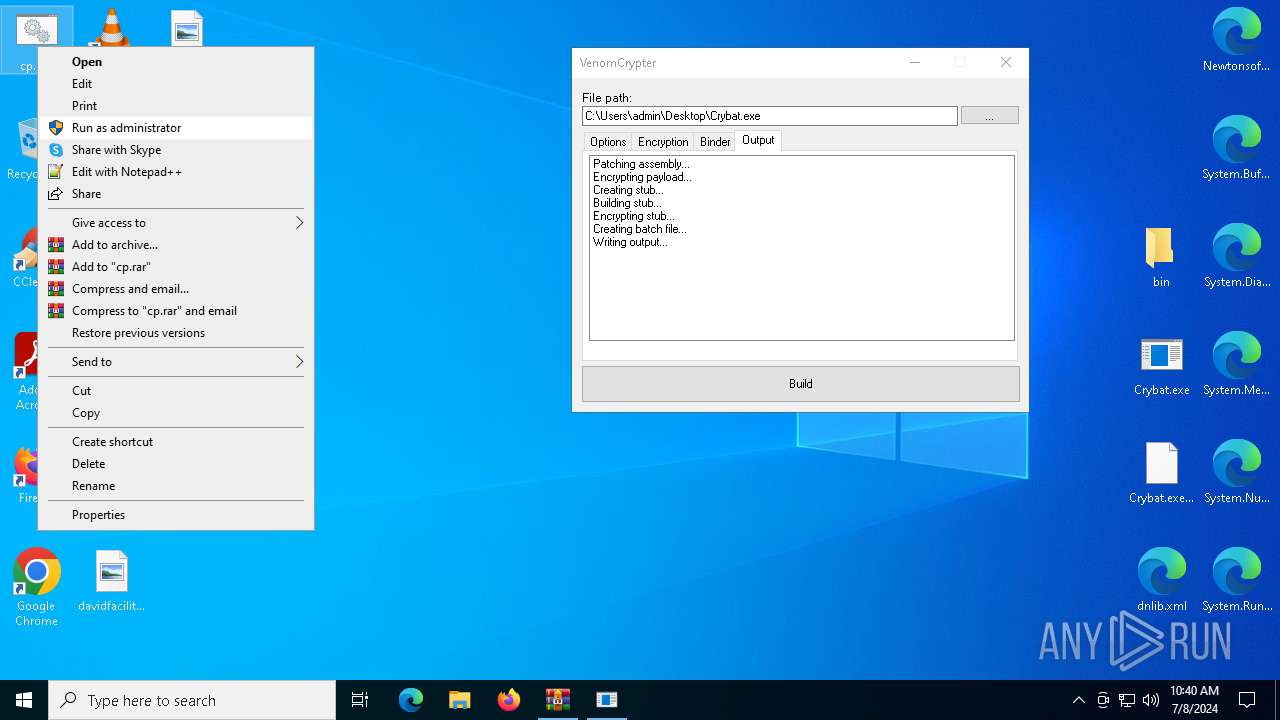
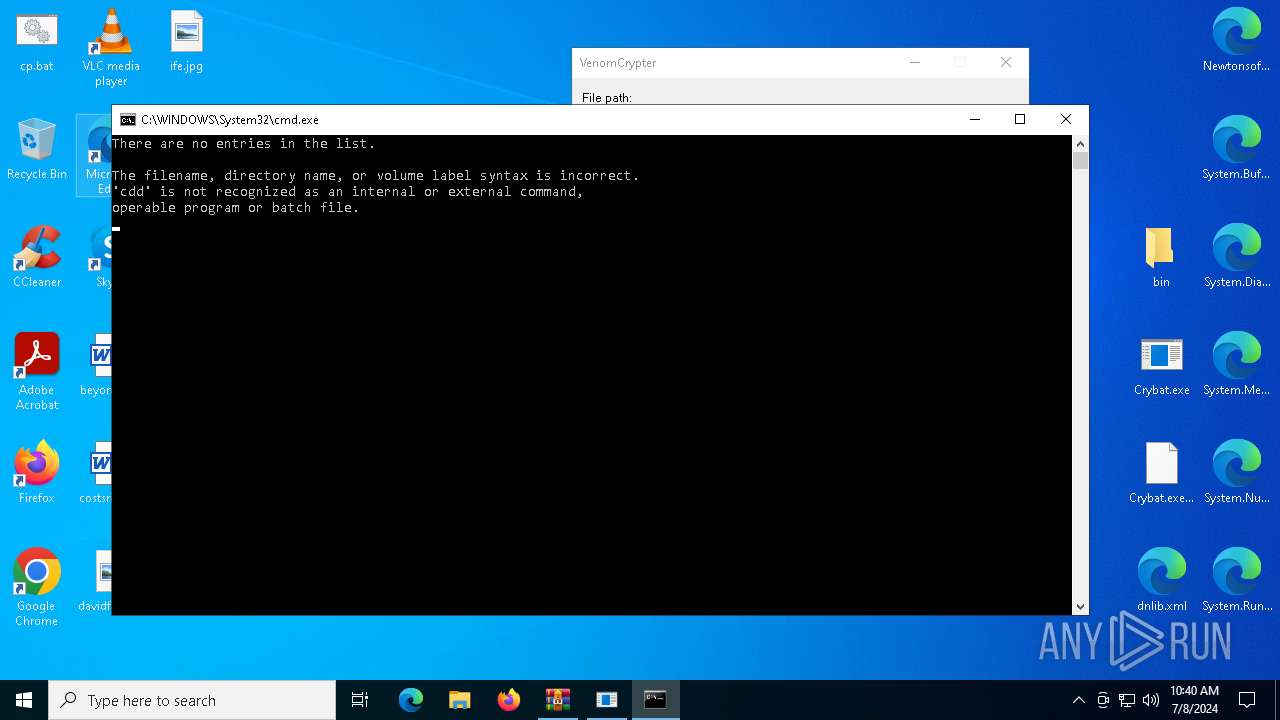
Manual execution by a user
- Crybat.exe (PID: 4072)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 5504)
Disables trace logs
- Crybat.exe (PID: 4072)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4976)
Reads the machine GUID from the registry
- Crybat.exe (PID: 4072)
- csc.exe (PID: 6760)
- csc.exe (PID: 2060)
Reads the software policy settings
- Crybat.exe (PID: 4072)
Checks proxy server information
- Crybat.exe (PID: 4072)
Reads the computer name
- Crybat.exe (PID: 4072)
Create files in a temporary directory
- Crybat.exe (PID: 4072)
- cvtres.exe (PID: 448)
- csc.exe (PID: 6760)
- csc.exe (PID: 2060)
- cvtres.exe (PID: 7068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:01 22:54:14 |
| ZipCRC: | 0xd8e08508 |
| ZipCompressedSize: | 929323 |
| ZipUncompressedSize: | 982528 |
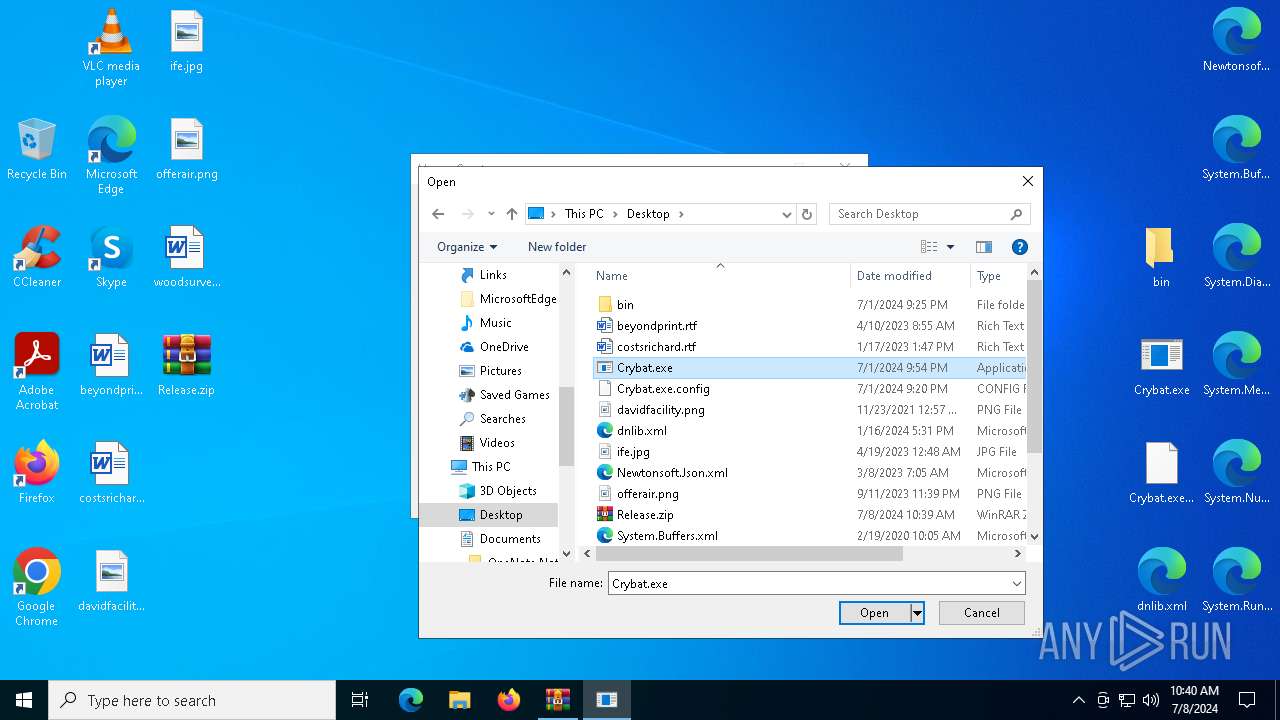
| ZipFileName: | Crybat.exe |
Total processes
152
Monitored processes
16
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC48B.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC5FC84BE79B148C09C967FD8C080B950.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1924 | net file | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2060 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\1uj1rm12.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | Crybat.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | C:\WINDOWS\system32\net1 file | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2912 | net file | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
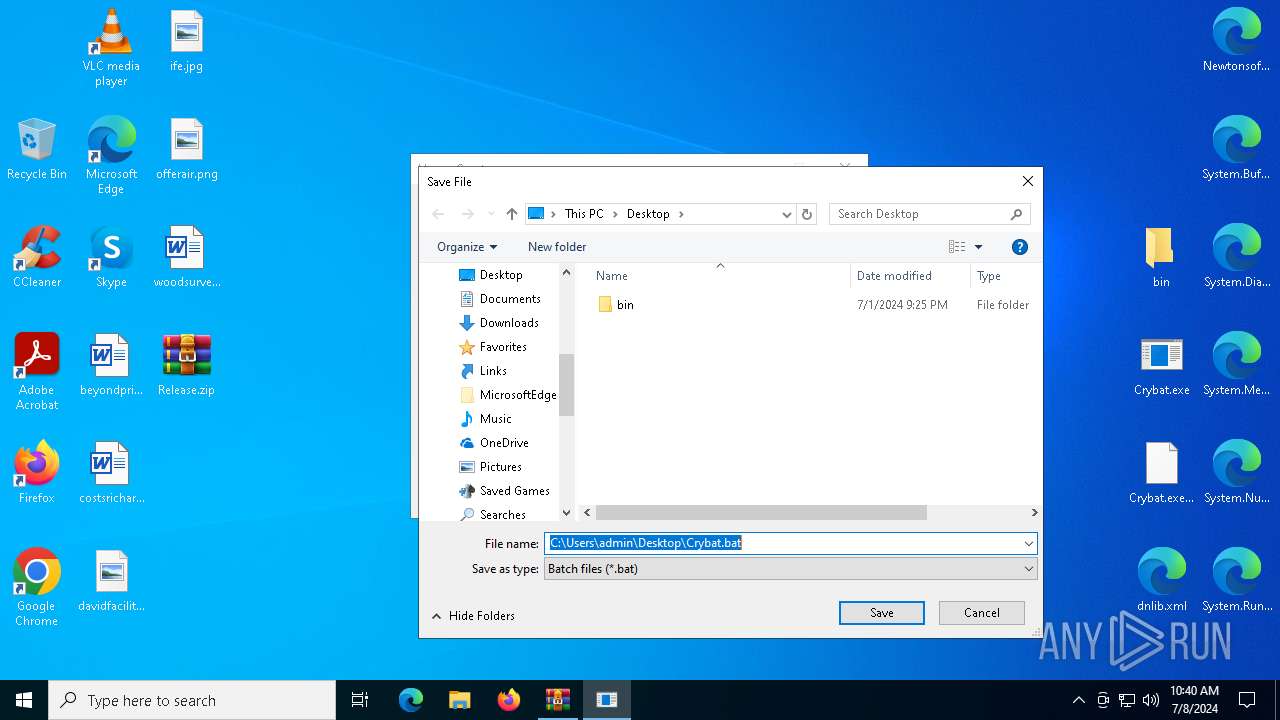
| 4024 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\Crybat.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4072 | "C:\Users\admin\Desktop\Crybat.exe" | C:\Users\admin\Desktop\Crybat.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Crybat Version: 1.0.0.0 Modules
| |||||||||||||||
| 4976 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Release.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5504 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\cp.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 222
Read events
17 032
Write events
174
Delete events
16
Modification events
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Release.zip | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4072) Crybat.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4072) Crybat.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Crybat_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
3
Suspicious files
6
Text files
16
Unknown types
0
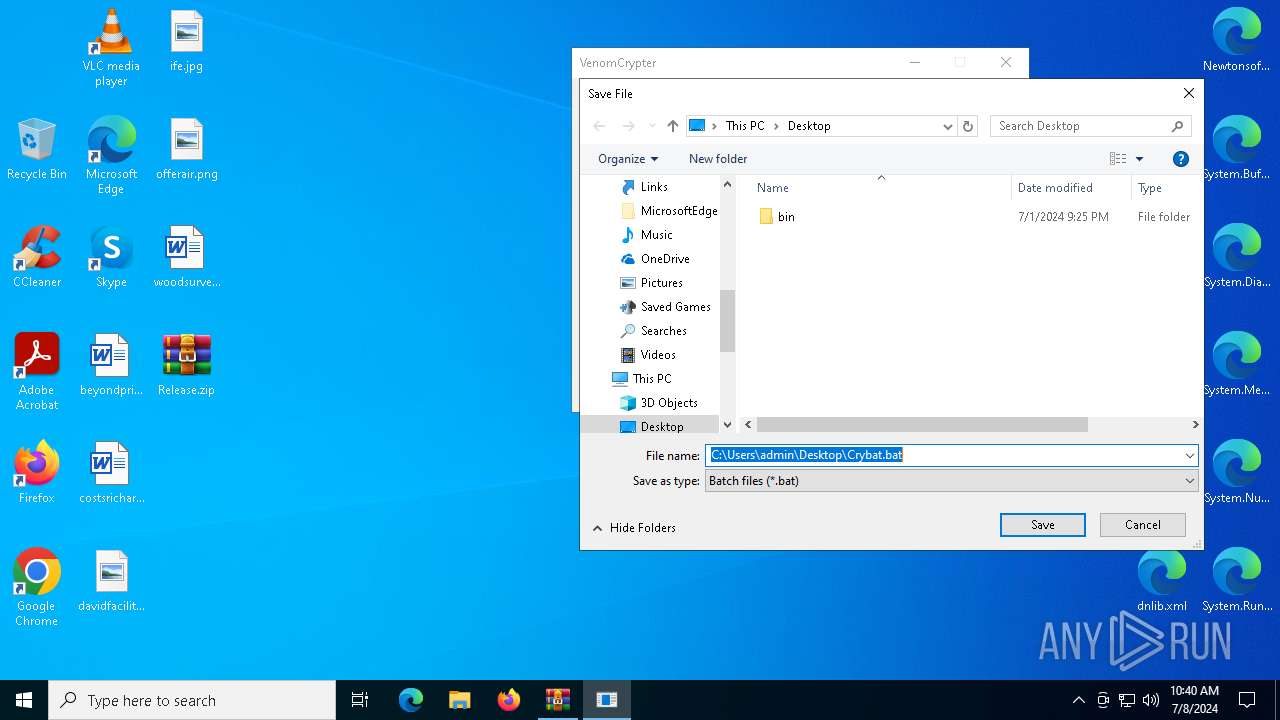
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | Crybat.exe | C:\Users\admin\AppData\Local\Temp\xzc2mpbr.0.cs | text | |
MD5:64B90248D44717821D2741E233BAD305 | SHA256:EB19F65D765A2AE81CD304C0D68363D394F6771C4C8B233A532901B59F946327 | |||
| 4976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4976.843\System.Memory.xml | xml | |
MD5:ADD19745A43B2515280CE24671863114 | SHA256:D5714C96607EB1A9D0F90F57CA194D8A9C3EDE0656A1D1F461E78B209F054813 | |||
| 4976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4976.843\Newtonsoft.Json.xml | xml | |
MD5:D398FFE9FDAC6A53A8D8BB26F29BBB3C | SHA256:79EE87D4EDE8783461DE05B93379D576F6E8575D4AB49359F15897A854B643C4 | |||
| 4072 | Crybat.exe | C:\Users\admin\AppData\Local\Temp\xzc2mpbr.cmdline | text | |
MD5:7803C15856473D6CDC4F975F41877176 | SHA256:EBC94DF6B4D9B7001FEA1F7CC532F07579900958B9A22DFA7D3F43DF531980E3 | |||
| 4072 | Crybat.exe | C:\Users\admin\Desktop\Crybat.bat | text | |
MD5:1B00B8963633D70401090C76A8938315 | SHA256:3855B4A71DEFC729F8AFDBD9DA7985AD553EEE5E94D3CCD6202422A04119C32F | |||
| 6760 | csc.exe | C:\Users\admin\AppData\Local\Temp\xzc2mpbr.out | text | |
MD5:8CB8DDB519011889B86B3F70C403A282 | SHA256:2C1D638D6B04124B7257E9625EE20B763458A5646040FB08CABF370F9A62D149 | |||
| 6760 | csc.exe | C:\Users\admin\AppData\Local\Temp\tmpC2C6.tmp | executable | |
MD5:3BFB48C02B0B94C5D4C12B6AC6B77E40 | SHA256:AD60B7106D693965929768C20EFBE5D15B26FC286B23C0A2EB15BBACAF9F0308 | |||
| 4072 | Crybat.exe | C:\Users\admin\AppData\Local\Temp\1uj1rm12.0.cs | text | |
MD5:8200FC352F50F3372485498A39EF40E4 | SHA256:5622D5BFB67DF8E1CB5DBFA9FFF88A1076980386E09973DA2F4B3C1582ADA99D | |||
| 4976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4976.843\System.Buffers.xml | xml | |
MD5:1C55860DD93297A6EA2FAD2974834C3A | SHA256:2EC7FB12E11F9831E40524427F6D88A3C9FFDD56CCFA81D373467B75B479A578 | |||
| 4976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4976.843\System.Runtime.CompilerServices.Unsafe.xml | xml | |
MD5:C782E92ABBFC0531226F735C6AC56498 | SHA256:39C2D4A63A186D423E9C866F4D3E9A6ACBA0103398F20BAF8B92A38744894215 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
67
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3508 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
5940 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
2300 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
7052 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
7052 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2056 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1292 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6004 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4656 | SearchApp.exe | 2.16.110.168:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3508 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3508 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |