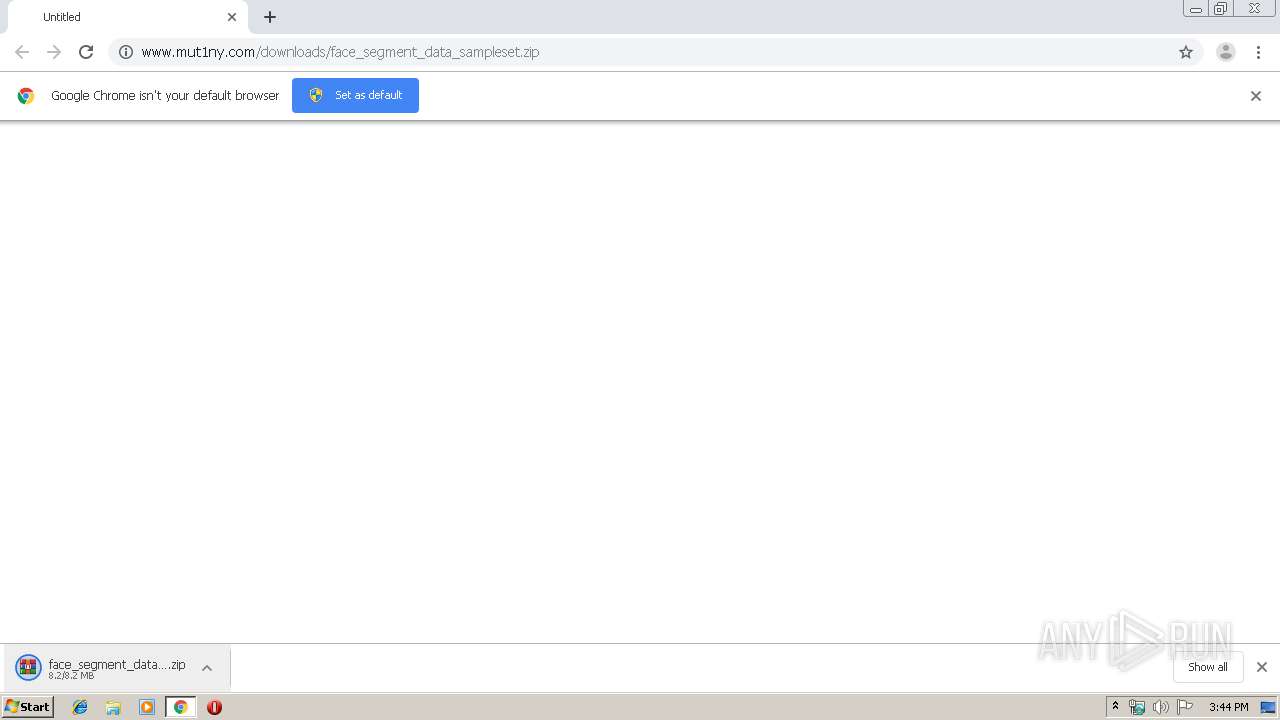
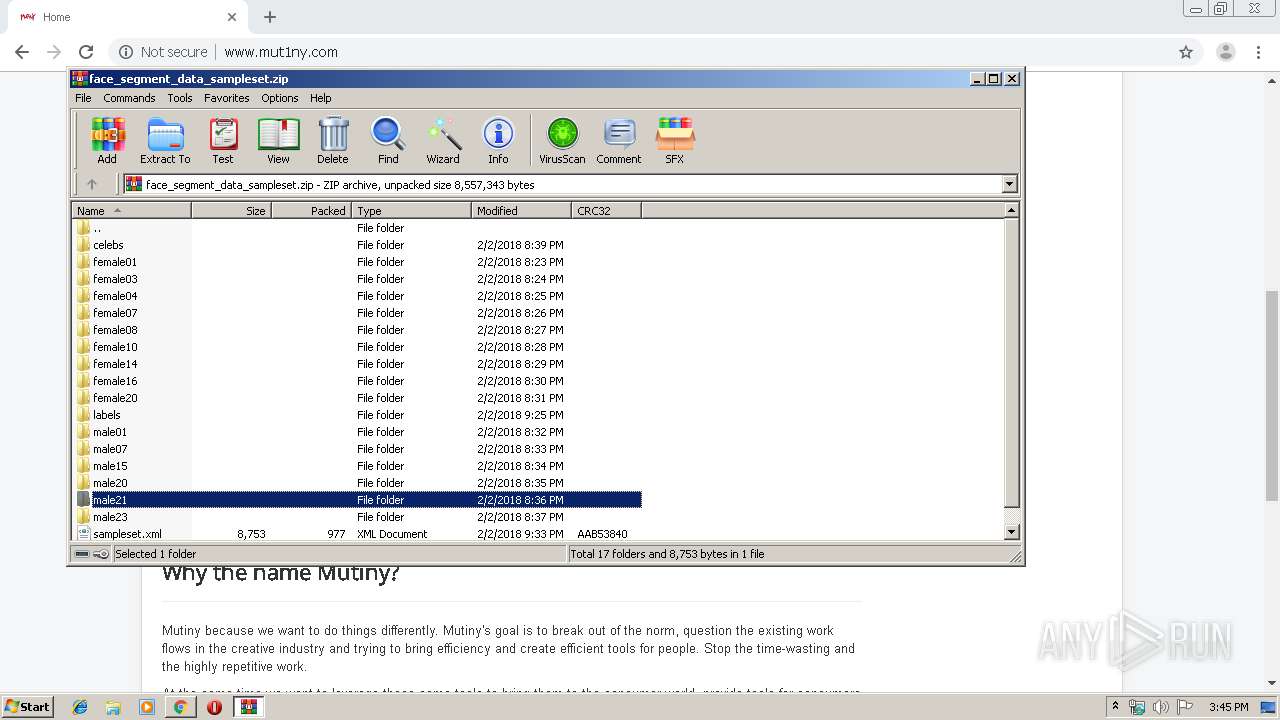
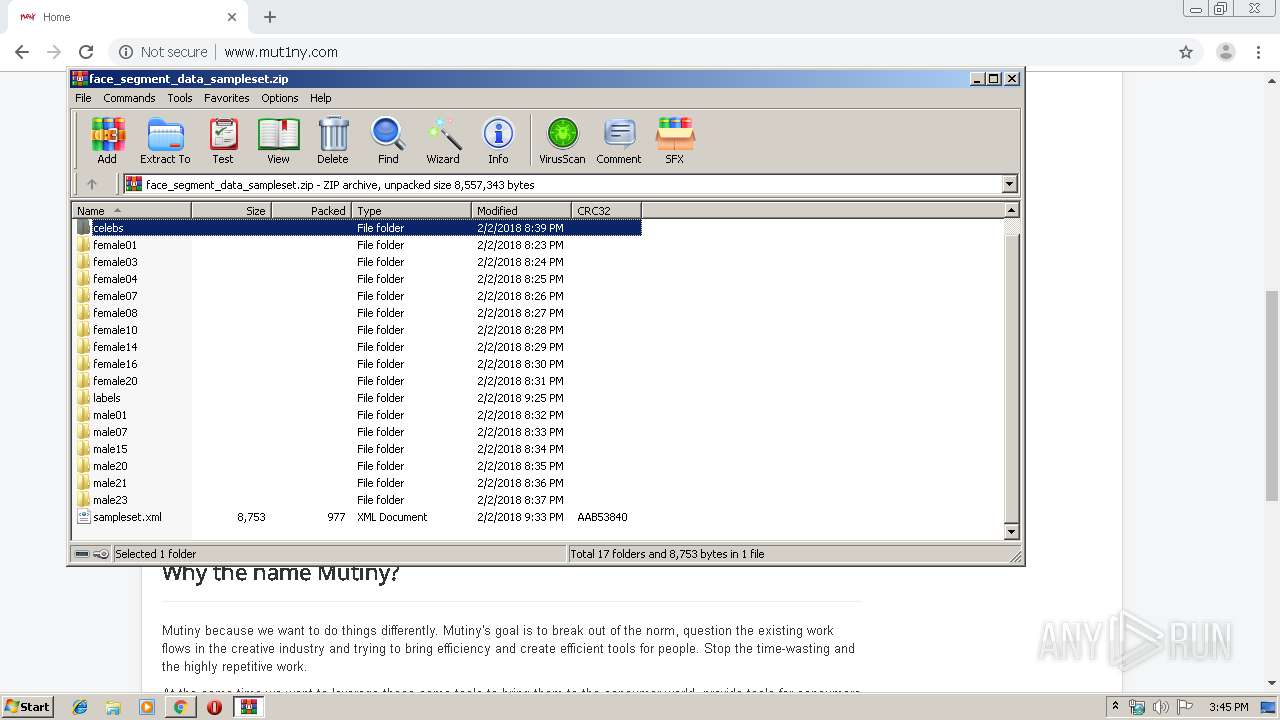
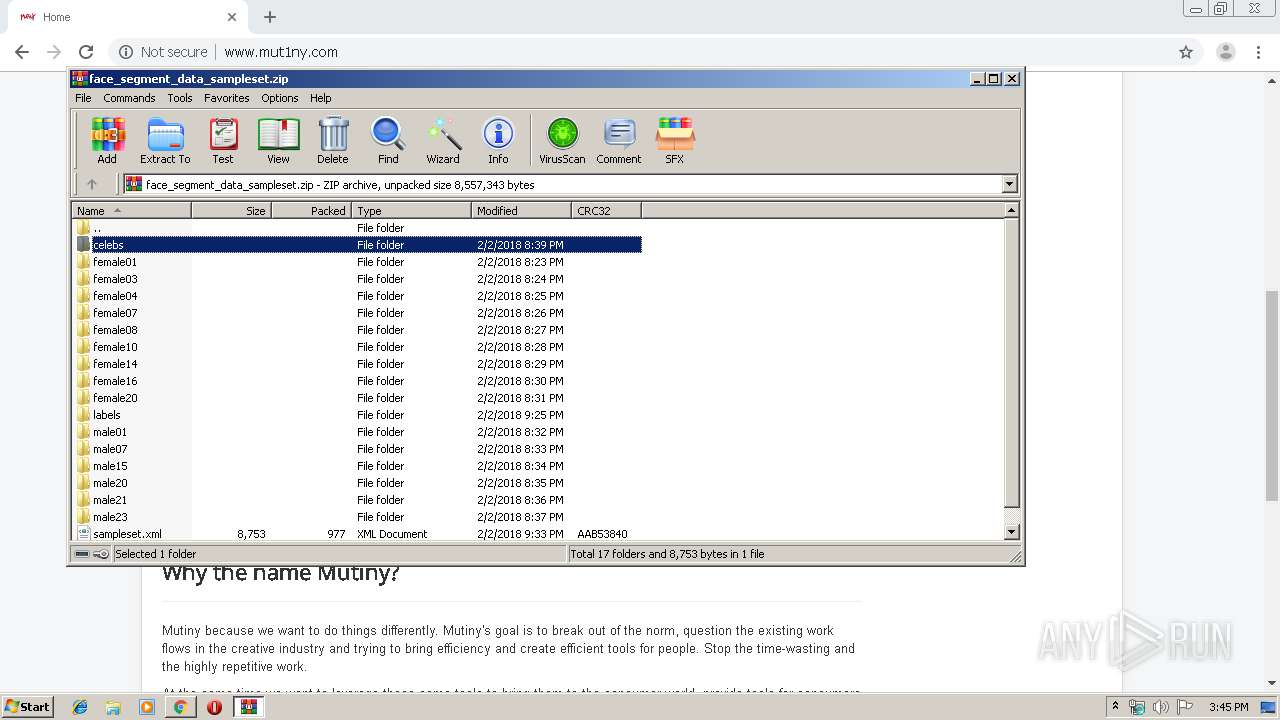
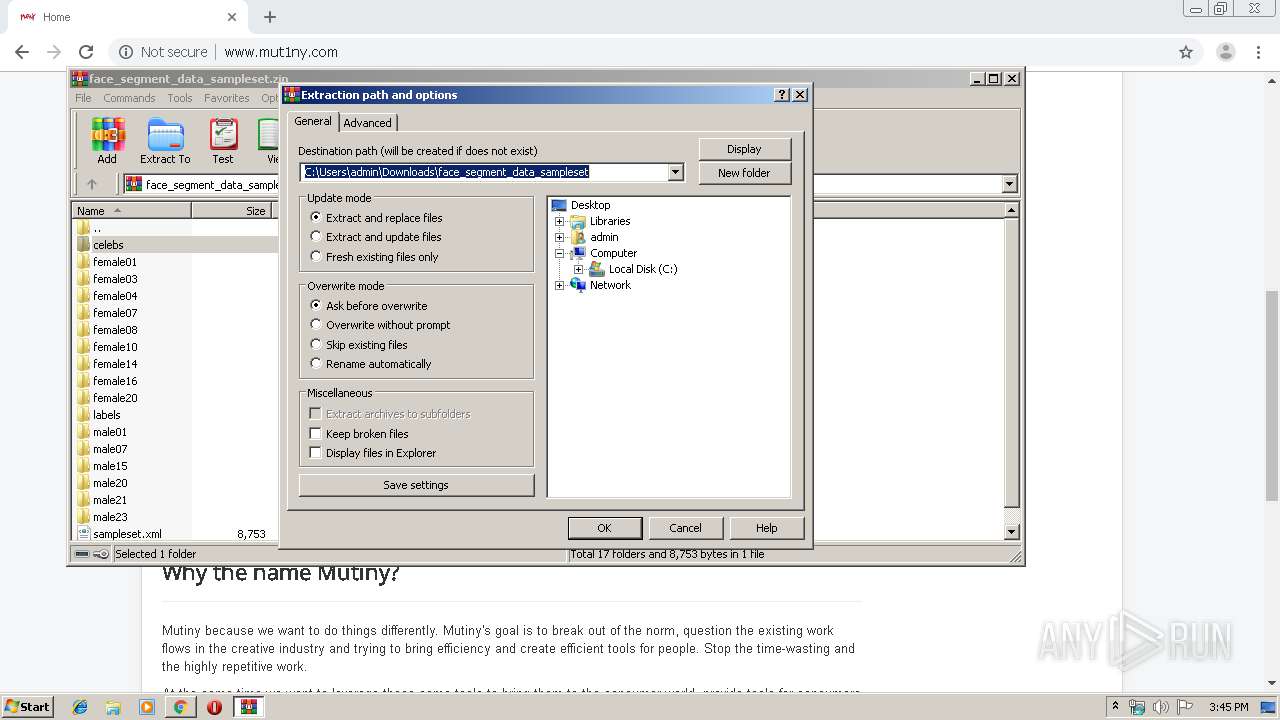
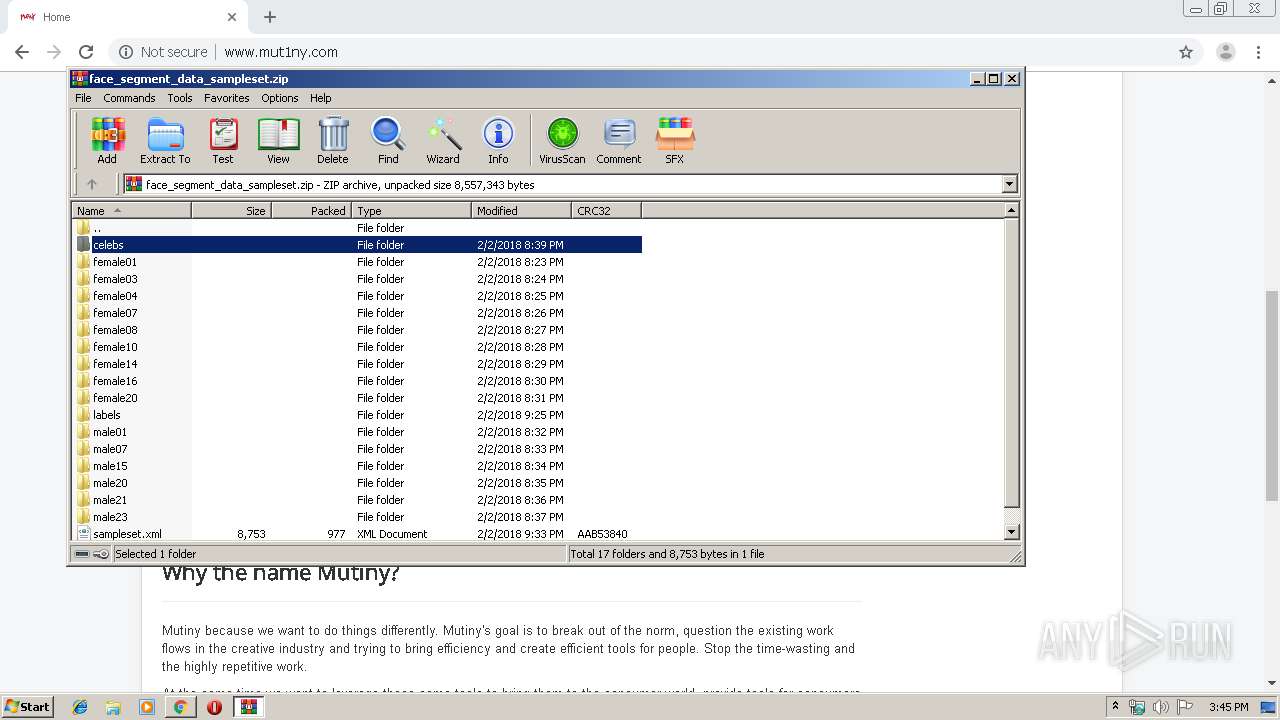
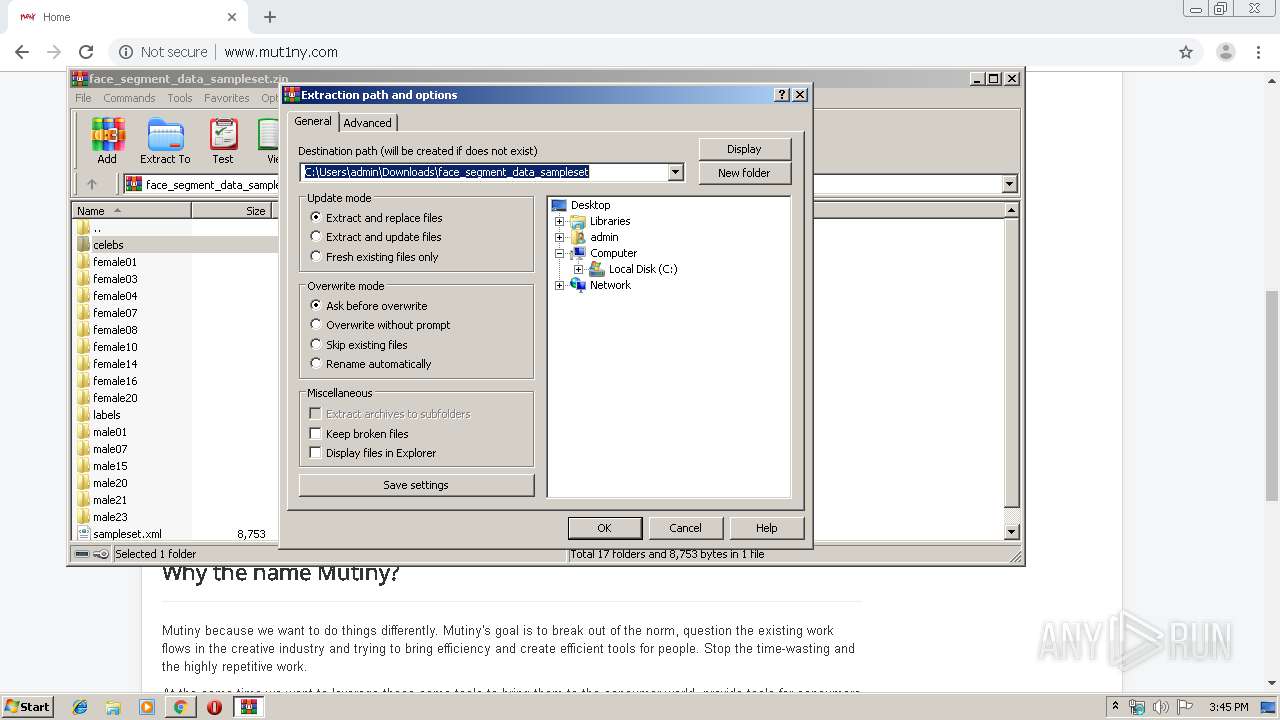
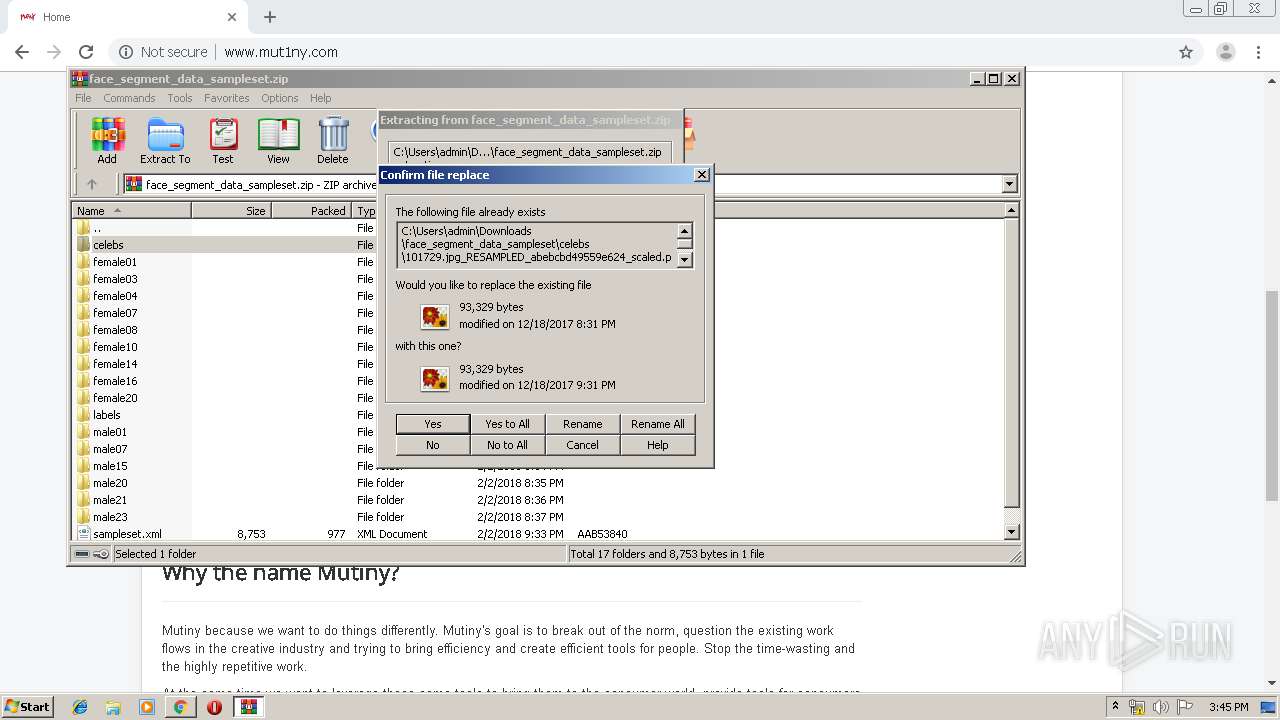
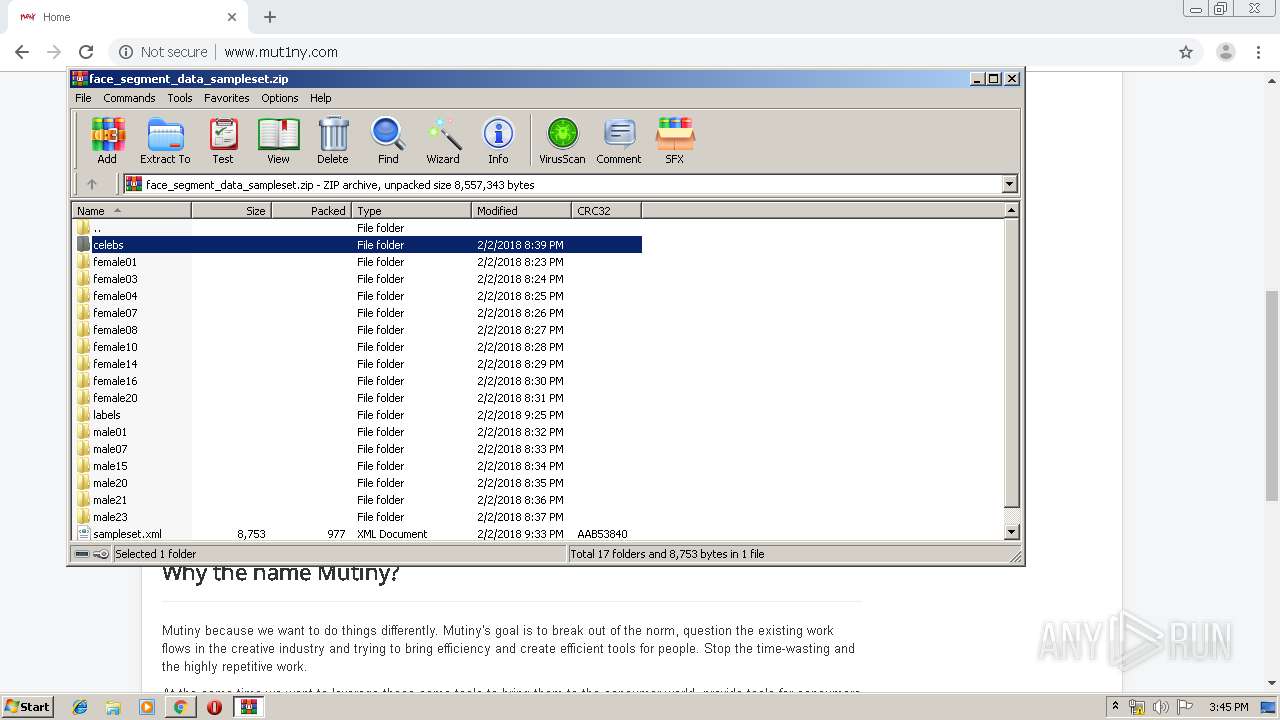
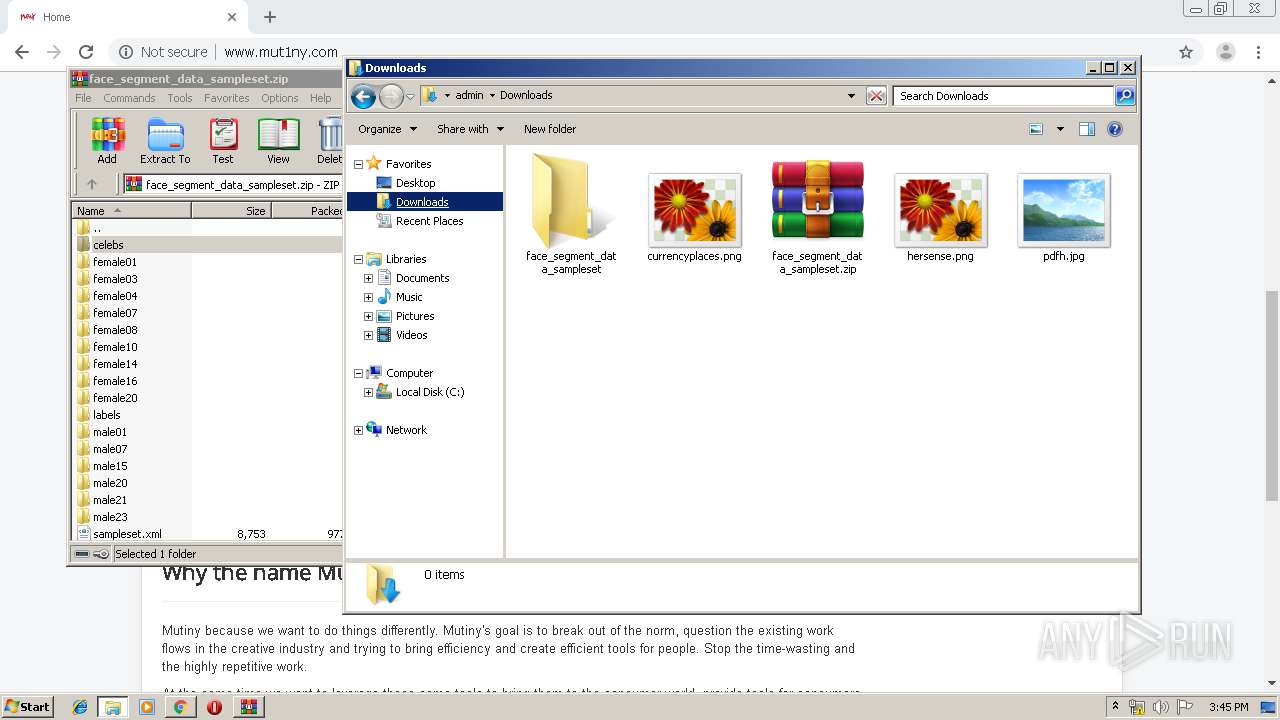
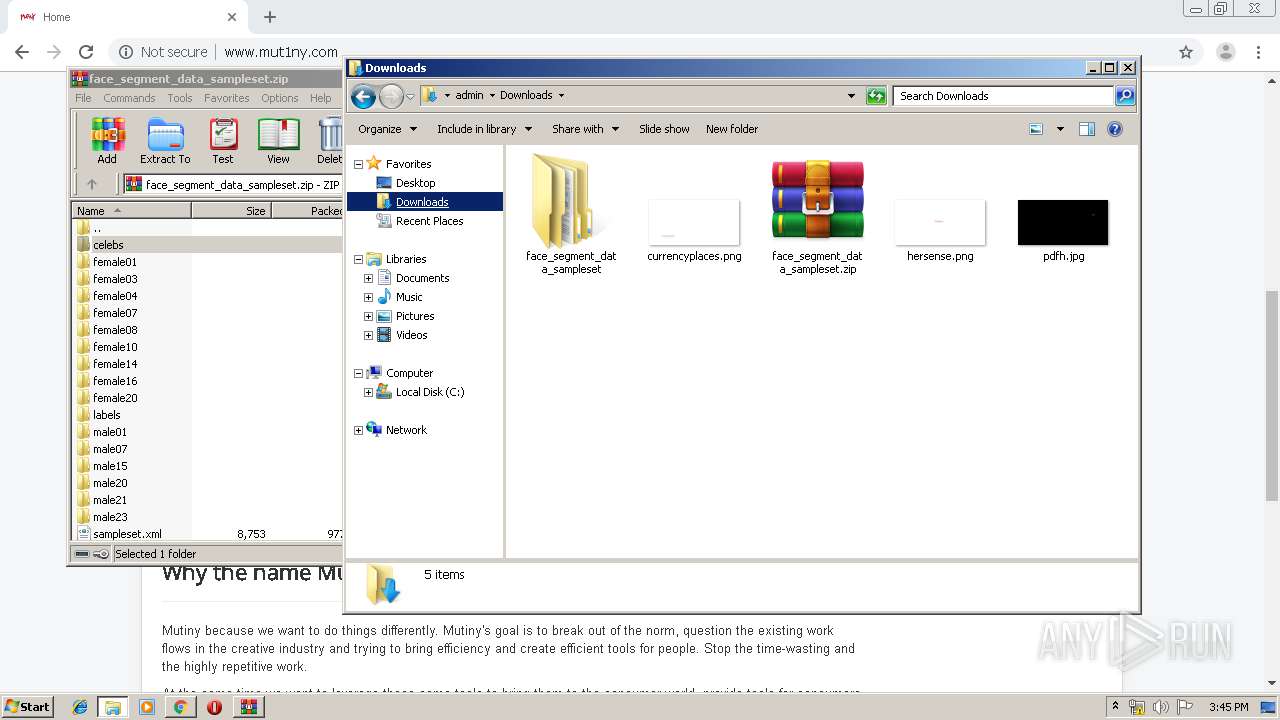
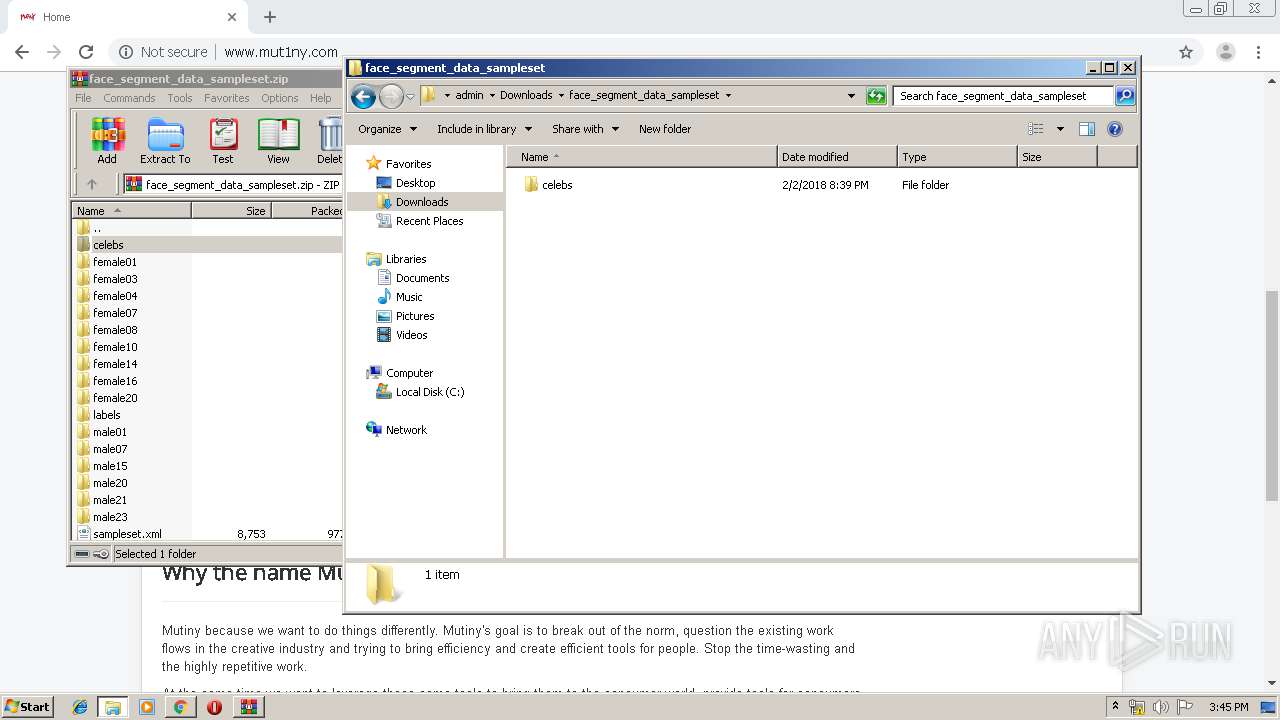
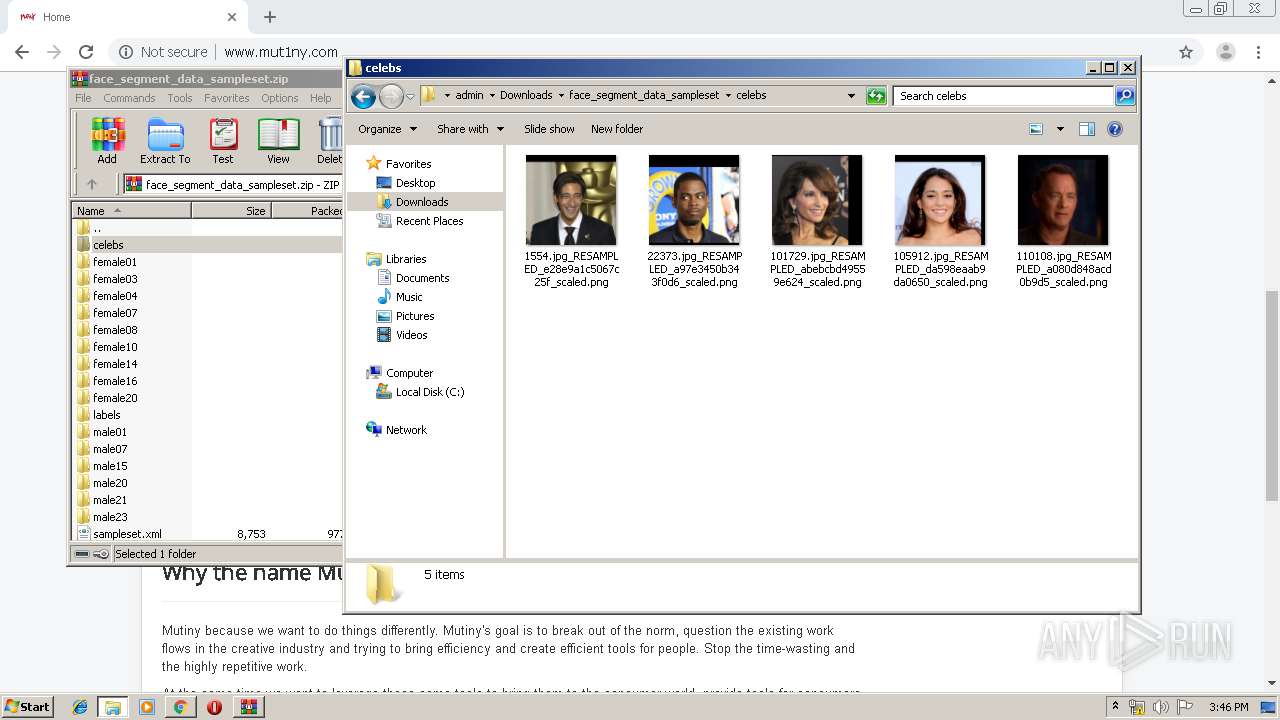
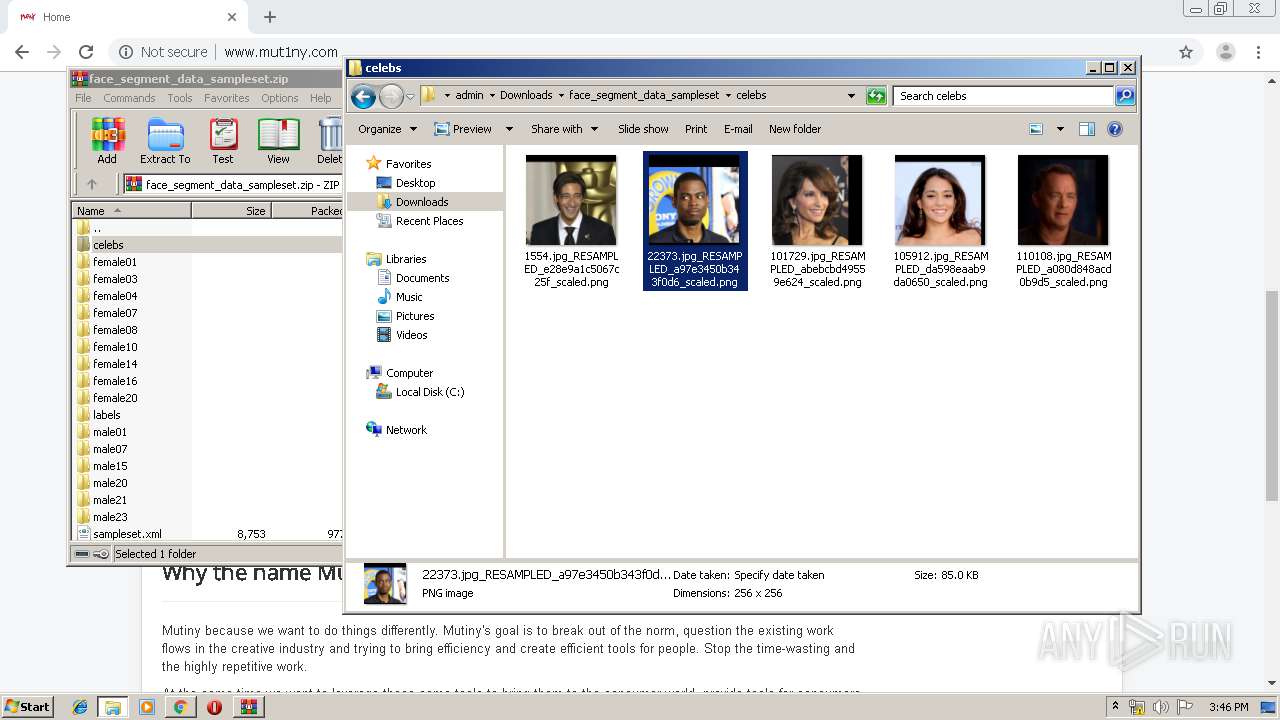
| URL: | http://www.mut1ny.com/downloads/face_segment_data_sampleset.zip |
| Full analysis: | https://app.any.run/tasks/e9b71a62-ddf3-4fa5-bbba-b60669e9a7f1 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 15:44:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 36F7089E888AF549EC8A8D62CBADD196 |
| SHA1: | 908D4A6B048452C2CB09D112BA653067CF5BA54C |
| SHA256: | 33ED1A65965533DACAF983CD4E716379FF39261A4A6A61B6B5D2CA23175463D5 |
| SSDEEP: | 3:N1KJS4W4IBXKW/RM+cn:Cc4SaMc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2428)
INFO
Reads the hosts file
- chrome.exe (PID: 2428)
- chrome.exe (PID: 1856)
Reads settings of System Certificates
- chrome.exe (PID: 1856)
Reads Internet Cache Settings
- chrome.exe (PID: 2428)
Manual execution by user
- explorer.exe (PID: 1328)
Application launched itself
- chrome.exe (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5925777833934018630 --mojo-platform-channel-handle=2892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7000648471517689591 --mojo-platform-channel-handle=3384 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11036667980996431568 --mojo-platform-channel-handle=4560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2451371580170565476 --mojo-platform-channel-handle=2612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3987731657156330084 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14329790213615597128 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2406967029401504239 --mojo-platform-channel-handle=4184 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16973284147742605948 --mojo-platform-channel-handle=1564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10896770893600579759 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 461
Read events
1 322
Write events
133
Delete events
6
Modification events
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2484) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2428-13220120675676750 |
Value: 259 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2428) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
261
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a27f2d00-626c-4a0a-8161-f120ec669b4c.tmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a94a.TMP | text | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:9543068B6751E1F3E11F91D72EE78D95 | SHA256:D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
30
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1856 | chrome.exe | GET | 404 | 217.160.0.224:80 | http://www.mut1ny.com/favicon.ico | DE | html | 1.59 Kb | malicious |
1856 | chrome.exe | GET | 403 | 217.160.0.224:80 | http://www.mut1ny.com/downloads/ | DE | html | 586 b | malicious |
1856 | chrome.exe | GET | 301 | 217.160.0.224:80 | http://www.mut1ny.com/downloads | DE | html | 240 b | malicious |
1856 | chrome.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/apps/domainpark/show_afd_ads.js | US | html | 1.37 Kb | whitelisted |
1856 | chrome.exe | GET | 200 | 217.160.0.224:80 | http://www.mut1ny.com/downloads/face_segment_data_sampleset.zip | DE | compressed | 8.18 Mb | malicious |
1856 | chrome.exe | GET | 200 | 217.160.0.224:80 | http://www.mut1ny.com/ | DE | html | 3.18 Kb | malicious |
1856 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://sedoparking.com/search/registrar.php?domain=www.mut1ny.com&rpv=2®istrar=IONOSParkingDE&gst=3B1g9Gy1QuamkCgX0fXXvmv2m50KlY0DrEoLSmhP2qk3i_H3TPQ2Br7v5SV7L3slhGXvM8wHHKiwucoj9pMDACKCxXLRhSALjA&ref= | DE | html | 19.6 Kb | whitelisted |
1856 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://sedoparking.com/frmpark/www.mut1ny.com/IONOSParkingDE/park.js | DE | html | 671 b | whitelisted |
1856 | chrome.exe | GET | 200 | 217.160.0.224:80 | http://www.mut1ny.com/images/headers/logo2.png | DE | image | 57.8 Kb | malicious |
1856 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://sedoparking.com/search/tsc.php?200=MzMzNDY2Mzc2&21=ODUuMjAzLjIwLjU=&681=MTU3NTY0NzA5N2MxMDFkYTBjMTRmZjliNTIzNjkzMWY4MjRkOWUxYzUz&crc=c92fd819120f725233856e5b863c97490364655a&cv=1 | DE | compressed | 19.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1856 | chrome.exe | 91.195.240.136:80 | sedoparking.com | SEDO GmbH | DE | malicious |
— | — | 216.58.210.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 216.58.207.35:80 | www.gstatic.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
1856 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 217.160.0.224:80 | www.mut1ny.com | 1&1 Internet SE | DE | malicious |
— | — | 217.160.0.224:80 | www.mut1ny.com | 1&1 Internet SE | DE | malicious |
— | — | 172.217.23.138:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1856 | chrome.exe | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.mut1ny.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sedoparking.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
img.sedoparking.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
adimg.uimserv.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1856 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |