| File name: | juego_online.exe |
| Full analysis: | https://app.any.run/tasks/2899ab66-02fa-4fa7-8d23-6af8ea1d4b63 |
| Verdict: | No threats detected |
| Analysis date: | July 09, 2019, 17:43:36 |
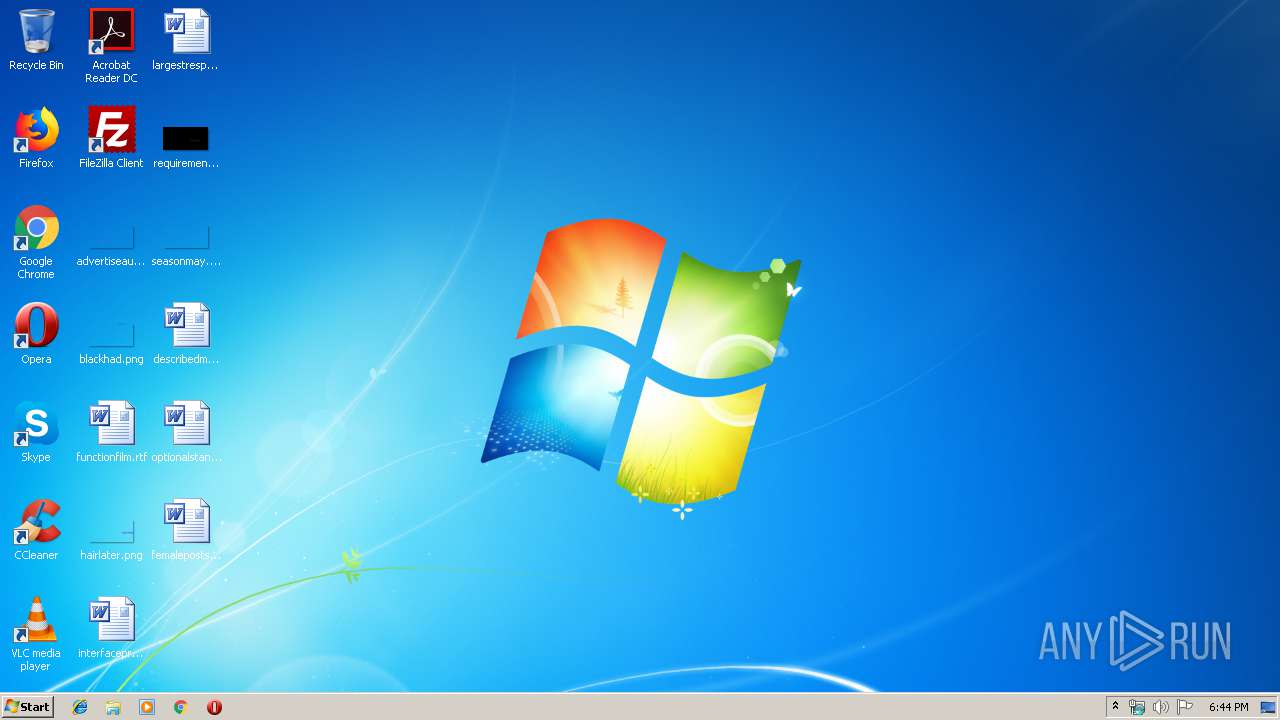
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 719909DED36DE993005D0D083E50E3E5 |
| SHA1: | 29E700011A4C7BC5373D5C85EF4E9A29A192BDF9 |
| SHA256: | 33D98D0D2325EDAF891C49BD0D7B8ABBB2662D9B53532F1EE5C2A0AC72009BE2 |
| SSDEEP: | 98304:ZNw6/yIFwCvvvldO+4liUiZHDP4Ij1Mu3KGcUvQmVea:ZH/x5vvN/VUaDAwD5PvQaea |
MALICIOUS
Loads dropped or rewritten executable
- dosbox.exe (PID: 3816)
Application was dropped or rewritten from another process
- dosbox.exe (PID: 3816)
SUSPICIOUS
Executable content was dropped or overwritten
- juego_online.exe (PID: 3272)
INFO
Dropped object may contain Bitcoin addresses
- juego_online.exe (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:22 06:59:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 81920 |
| InitializedDataSize: | 102912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-May-2007 04:59:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-May-2007 04:59:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014000 | 0x00013600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44419 |
.data | 0x00015000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91827 |
.idata | 0x0001C000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1239 |
.rsrc | 0x0001D000 | 0x00017650 | 0x00017800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.04083 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06643 | 831 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | Russian - Russia | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | Russian - Russia | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | Russian - Russia | RT_STRING |
100 | 1.91924 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 7.05441 | 84602 | Latin 1 / Western European | Process Default Language | RT_BITMAP |
ASKNEXTVOL | 3.42532 | 642 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
GETPASSWORD1 | 3.29928 | 314 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
LICENSEDLG | 3.17045 | 232 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3272 | "C:\Users\admin\AppData\Local\Temp\juego_online.exe" | C:\Users\admin\AppData\Local\Temp\juego_online.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
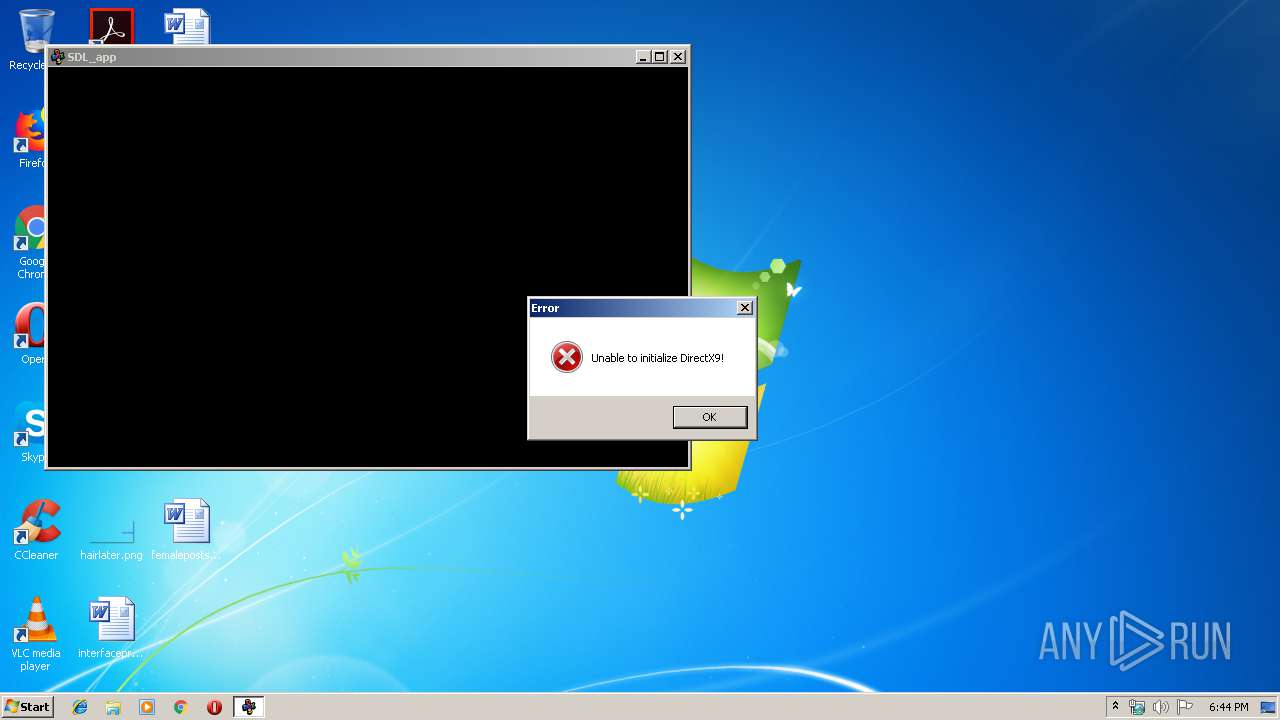
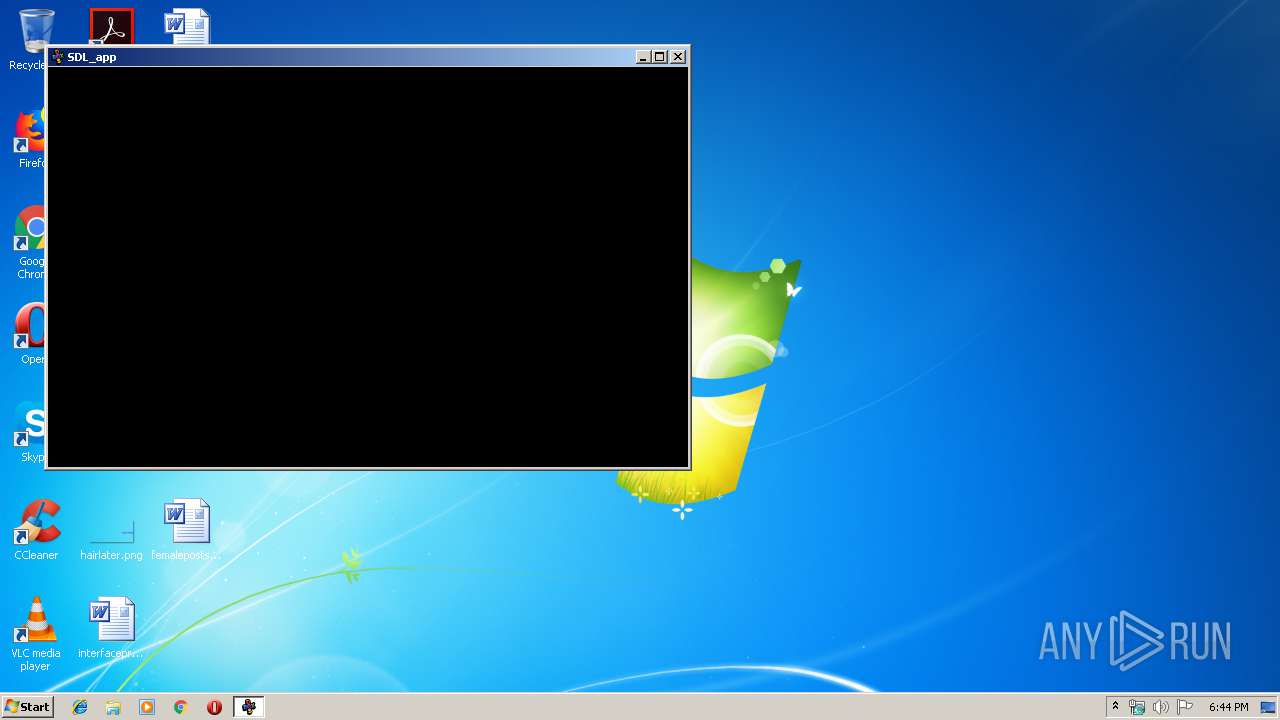
| 3816 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\dosbox.exe" -conf dosbox.conf -noconsole | C:\Users\admin\AppData\Local\Temp\RarSFX0\dosbox.exe | — | juego_online.exe | |||||||||||
User: admin Company: DOSBox Team Integrity Level: MEDIUM Description: DOSBox DOS Emulator Exit code: 0 Version: 0, 74, 0, 0 Modules
| |||||||||||||||
Total events
460
Read events
447
Write events
13
Delete events
0
Modification events
| (PID) Process: | (3272) juego_online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3272) juego_online.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: dosbox.exe | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1288448402 | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Version |
Value: 0A050000 | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DOSBOX.EXE | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Id |
Value: DOSBOX.EXE4CCC29920017D600 | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | MostRecentStart |
Value: 4AD817E97D36D501 | |||
| (PID) Process: | (3816) dosbox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: dosbox.exe | |||
Executable files
11
Suspicious files
22
Text files
74
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dosbox_admin.exe | executable | |
MD5:3F42501C0E15EDF83F8254BBA596F488 | SHA256:0CED8443E02BDA7346918490D06F6ACA8D6744049BB635876F5AA2742FCAAAD5 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DLL\3dfxSpl2.dll | executable | |
MD5:16CDCB220642017D2FD776486911117E | SHA256:3854B2A60F9C6B410E33D25ADA09F4767339C0B2FEAC8D3844049E168E379241 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DLL\glide.ini | text | |
MD5:5E279729DFE2ADDFB92613CFB460F1FB | SHA256:C0F23F8EC2CB5B66A7F966E69A7C09874C693DEED0B1D49C71DD3CA33BCFC9DE | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DLL\glide2x.ovl | executable | |
MD5:39B6D33E6E4F9C31F9EC787FCA5FEE2F | SHA256:C83091D27CEB32007B2294CA7157AC5ABA88799D1FEC318F0156CF10D0F8DA32 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DLL\glide2x.dll | executable | |
MD5:466C02FDB3A1F5A8E766B4CAF9335F3D | SHA256:165BA3CDEAC7CEDB4116979B9388B2E925E82062EC988CCFC0DC21D430217A14 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DLL\d3dx9.dll | executable | |
MD5:E415862612E65F10D7D888443ECD7594 | SHA256:5EDEED79F2359527A55B8189CFA8B9B121CD608D44EEAD905A0F3436938AD532 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DOCS\AUTHORS.txt | text | |
MD5:B218DD39016F8A1C01D355CA0B399073 | SHA256:BE56F587400F0A3B5A6CE69DF6FD800219FA88AA82529AF325353EA0D901F256 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DOCS\COPYING.txt | text | |
MD5:46AAF69A91703493B666F212A04F2D8D | SHA256:DA0ECA0FB517AC939D167924C9D4B3F8750A6B7191932EF2CB145ACFA624AC7E | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DOCS\SVN-specific manuals\USAGE_EN.TXT | text | |
MD5:A1A2FD4A1C5F00A1E0E09CED067651A9 | SHA256:AA1FB90D31005BF6E82FF4F6027B104AE7D1689629F071B3CA28C18E60D48217 | |||
| 3272 | juego_online.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\DOCS\Official manuals\README_KR.txt | text | |
MD5:C7AC16563FA0C713DD13CCC8A4F76439 | SHA256:392790A8E6F9E388B8BFDB51E0A3B505BC93E2DD98ADFF9FED1129468212893D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report