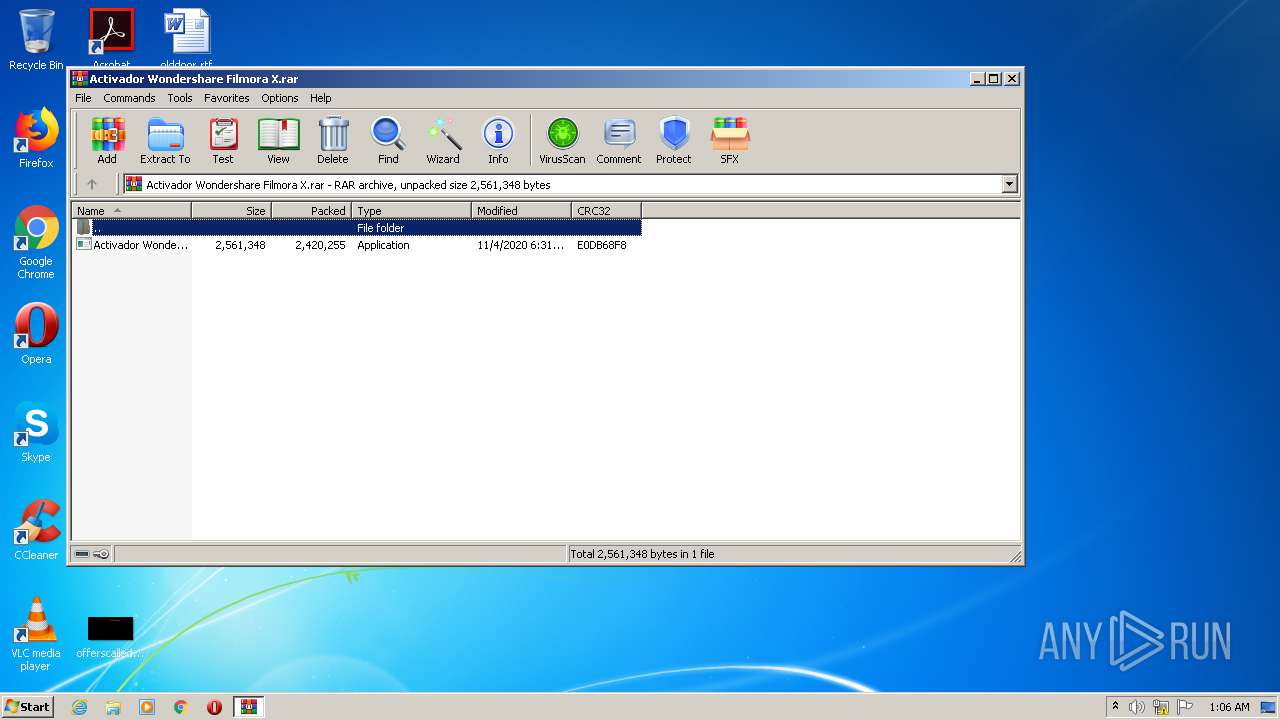
| File name: | Activador Wondershare Filmora X.rar |
| Full analysis: | https://app.any.run/tasks/0eb3f82e-fe21-45f2-bc3c-20b2577cec9c |
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2020, 01:05:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5B28423BB183F7DD615522449C7B9C79 |
| SHA1: | 2236261A14E56C3854CE45EA7D784B6542344C08 |
| SHA256: | 33D781541DF7BA835775931CDD3A1B21164BE3A00E1FD2221E5B1162D6FCDD7D |
| SSDEEP: | 49152:ybUGKrN9HEJg1/0xOxjXOXhD5qqCkNQwV/bICGtFNGgOfr5wjt:yZKB9w8/0xnhwyNtbnKLB |
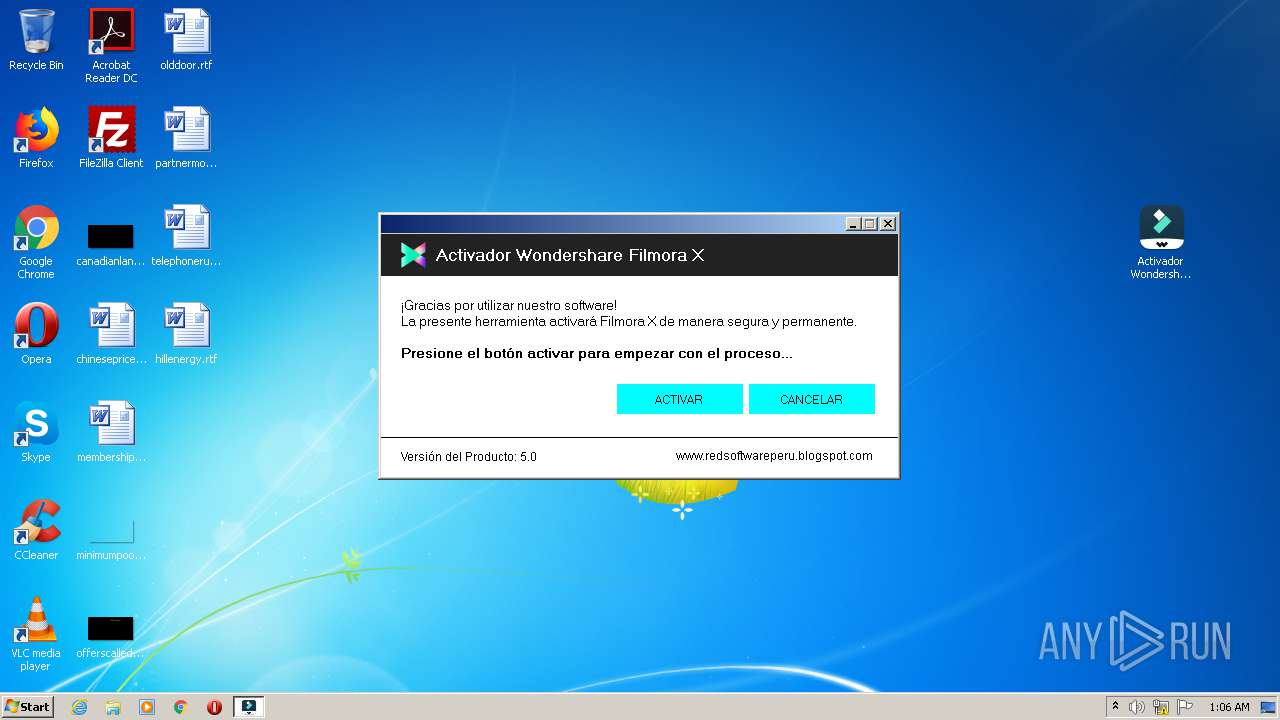
MALICIOUS
Application was dropped or rewritten from another process
- Activador Wondershare Filmora X.exe (PID: 2552)
- Activador Wondershare Filmora X.exe (PID: 1020)
- Activador Wondershare Filmora X.exe (PID: 2024)
SUSPICIOUS
Executable content was dropped or overwritten
- Activador Wondershare Filmora X.exe (PID: 2552)
- Activador Wondershare Filmora X.exe (PID: 1020)
Creates files in the program directory
- Activador Wondershare Filmora X.exe (PID: 2552)
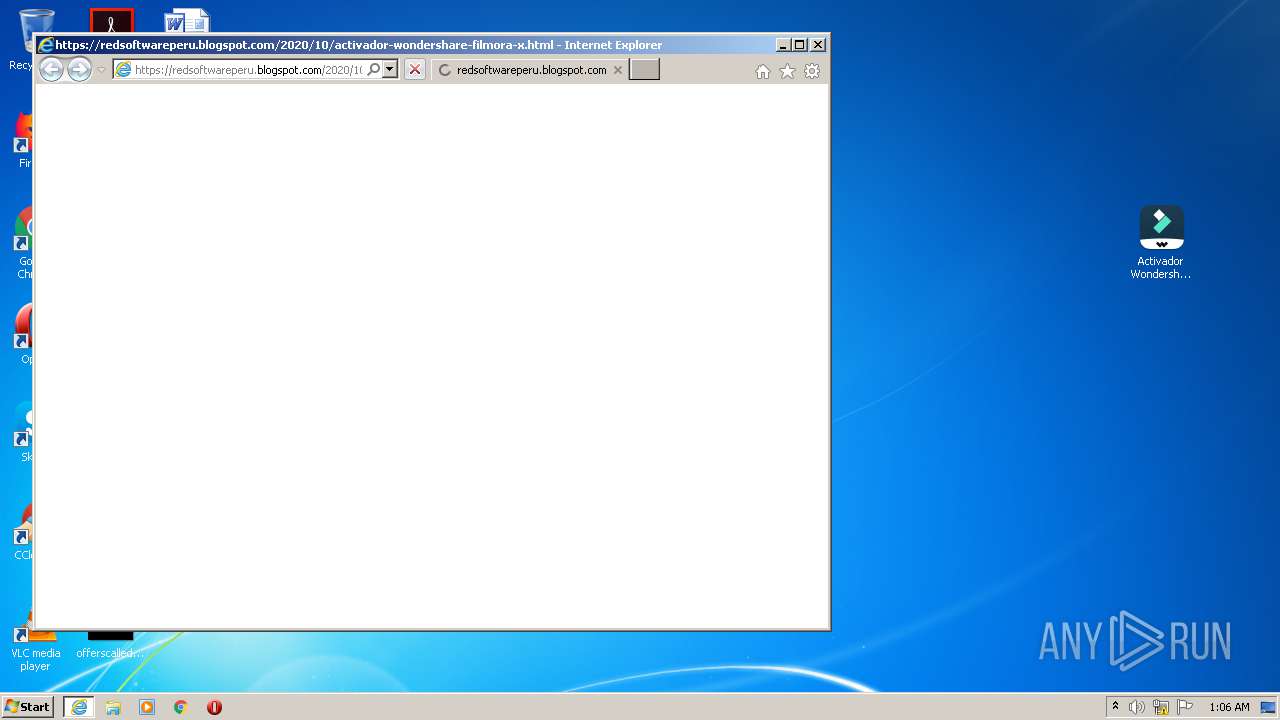
Starts Internet Explorer
- Activador Wondershare Filmora X.exe (PID: 2552)
INFO
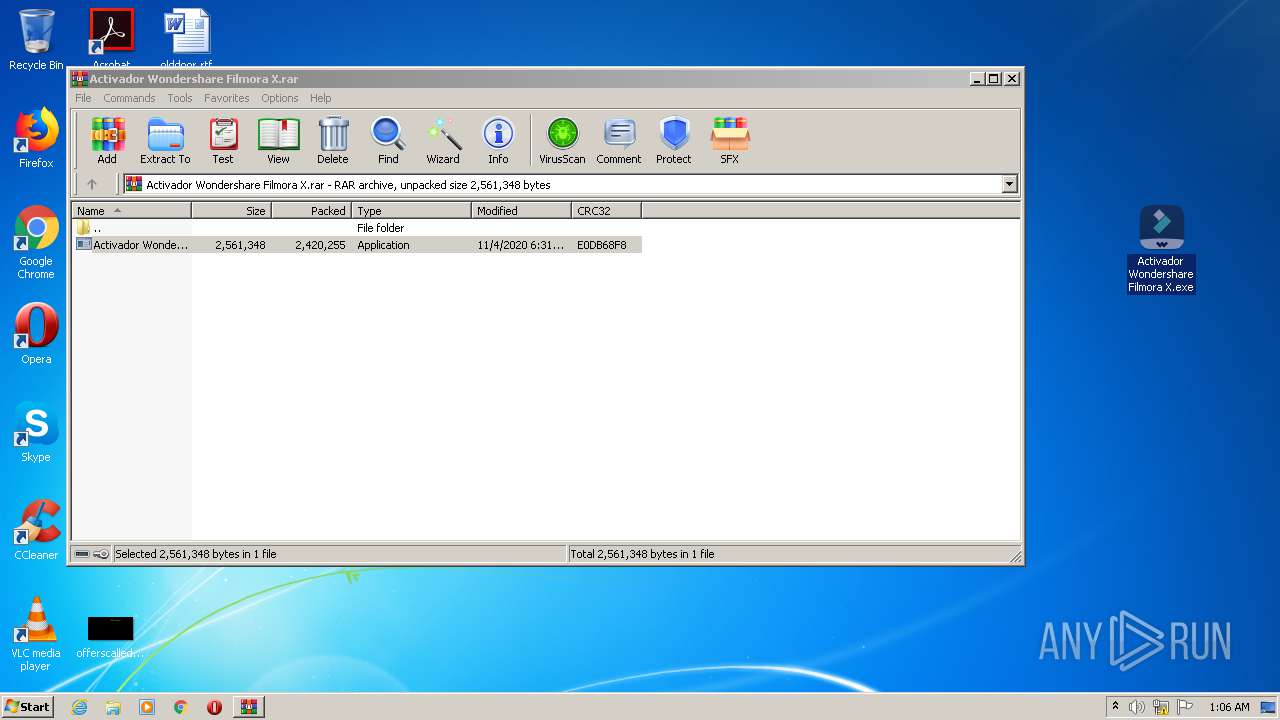
Manual execution by user
- Activador Wondershare Filmora X.exe (PID: 1020)
Reads internet explorer settings
- iexplore.exe (PID: 2944)
Reads Internet Cache Settings
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 2560)
Dropped object may contain Bitcoin addresses
- Activador Wondershare Filmora X.exe (PID: 1020)
- Activador Wondershare Filmora X.exe (PID: 2552)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2944)
Reads settings of System Certificates
- iexplore.exe (PID: 2944)
Application launched itself
- iexplore.exe (PID: 2560)
Changes internet zones settings
- iexplore.exe (PID: 2560)
Changes settings of System certificates
- iexplore.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
44
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Users\admin\Desktop\Activador Wondershare Filmora X.exe" | C:\Users\admin\Desktop\Activador Wondershare Filmora X.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2024 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Activador Wondershare Filmora X.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Activador Wondershare Filmora X.exe | — | Activador Wondershare Filmora X.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Activador Wondershare Filmora X Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Activador Wondershare Filmora X.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Activador Wondershare Filmora X.exe | Activador Wondershare Filmora X.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Activador Wondershare Filmora X Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Internet Explorer\iexplore.exe" https://redsoftwareperu.blogspot.com/2020/10/activador-wondershare-filmora-x.html | C:\Program Files\Internet Explorer\iexplore.exe | Activador Wondershare Filmora X.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2844 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Activador Wondershare Filmora X.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2560 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 349
Read events
1 258
Write events
91
Delete events
0
Modification events
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Activador Wondershare Filmora X.rar | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2844) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
26
Suspicious files
71
Text files
30
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2844.11038\Activador Wondershare Filmora X.exe | — | |
MD5:— | SHA256:— | |||
| 1020 | Activador Wondershare Filmora X.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\WsAP-Filmora.dll | executable | |
MD5:— | SHA256:— | |||
| 2552 | Activador Wondershare Filmora X.exe | C:\Program Files (x86)\Wondershare\Wondershare Filmora\WsAP-Filmora.dll | executable | |
MD5:— | SHA256:— | |||
| 2552 | Activador Wondershare Filmora X.exe | C:\Program Files\Wondershare\Wondershare Filmora (Spanish ES)\UpdateRegister.dll | executable | |
MD5:— | SHA256:— | |||
| 1020 | Activador Wondershare Filmora X.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Activador Wondershare Filmora X.exe | executable | |
MD5:— | SHA256:— | |||
| 2552 | Activador Wondershare Filmora X.exe | C:\Program Files\Wondershare\Wondershare Filmora\WsAP-Filmora.dll | executable | |
MD5:— | SHA256:— | |||
| 1020 | Activador Wondershare Filmora X.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\bin\UpdateRegister.dll | executable | |
MD5:— | SHA256:— | |||
| 2552 | Activador Wondershare Filmora X.exe | C:\Program Files\Wondershare\Wondershare Filmora\UpdateRegister.dll | executable | |
MD5:— | SHA256:— | |||
| 2552 | Activador Wondershare Filmora X.exe | C:\Program Files\Wondershare\Wondershare Filmora (Spanish ES)\WsAP-Filmora.dll | executable | |
MD5:— | SHA256:— | |||
| 2552 | Activador Wondershare Filmora X.exe | C:\Program Files (x86)\Wondershare\Wondershare Filmora\UpdateRegister.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
52
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2944 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAx6xYnQq491CAAAAABgZV8%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAx6xYnQq491CAAAAABgZV8%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDfMxBFBJlDZgIAAAAAfxRn | US | der | 472 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAqpS1r6cKNwl5rFBkfvrJw%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAx6xYnQq491CAAAAABgZV8%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEC4Xlj0DtgFyCAAAAABgZcU%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | iexplore.exe | 172.217.16.129:443 | redsoftwareperu.blogspot.com | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 209.197.3.15:443 | stackpath.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2944 | iexplore.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 172.217.21.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 216.58.212.169:443 | www.blogger.com | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2944 | iexplore.exe | 199.232.192.134:443 | red-software-peru.disqus.com | — | US | suspicious |
2944 | iexplore.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
redsoftwareperu.blogspot.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
www.blogger.com |
| shared |
3.bp.blogspot.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |