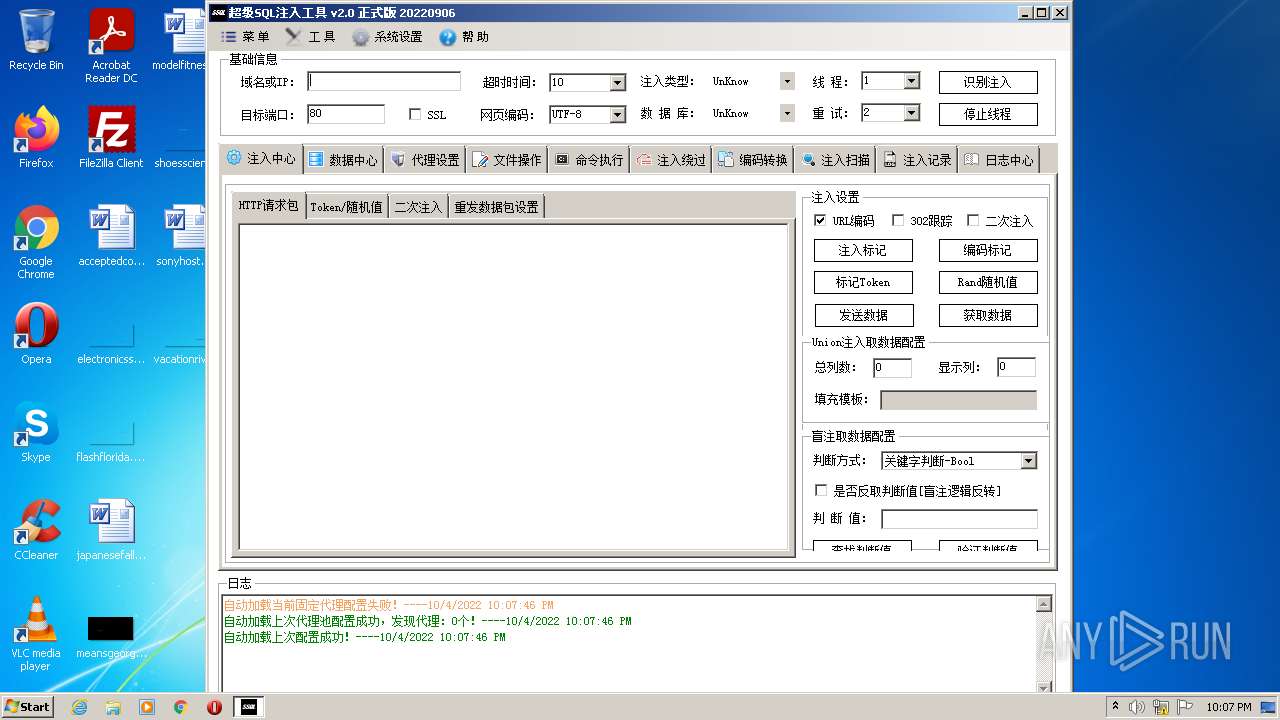
| File name: | SuperSQLInjection.exe |
| Full analysis: | https://app.any.run/tasks/aad2fce0-ae96-487c-a03b-7d8f4931bf33 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 21:07:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2C58F6DE8EE96BF1E33FC939445A566E |
| SHA1: | D313AC51B0DF7913E255C54E66BC33AB2B5A2A0C |
| SHA256: | 33C453EF3F104403FD34753780248BC3B1F3EE8590B3B92F270E3646397D3707 |
| SSDEEP: | 12288:1rBjpOUREzLw2f1WrG8HXXQGh07nzhF+dfdQ6styoUgbdY75/lzH+RB:1rBj0+EzLwW1T8HQH7nlF+foZB |
MALICIOUS
Actions looks like stealing of personal data
- SuperSQLInjection.exe (PID: 3724)
Drops executable file immediately after starts
- SuperSQLInjection.exe (PID: 3724)
- Setup.exe (PID: 856)
Changes the autorun value in the registry
- Setup.exe (PID: 856)
Application was dropped or rewritten from another process
- svchost.exe (PID: 3464)
- SuperSQLInjection .exe (PID: 2536)
- Setup.exe (PID: 856)
- Setup.exe (PID: 1120)
SUSPICIOUS
Reads the computer name
- SuperSQLInjection.exe (PID: 3724)
- SuperSQLInjection .exe (PID: 2536)
- Setup.exe (PID: 1120)
- Setup.exe (PID: 856)
- svchost.exe (PID: 3464)
Checks supported languages
- SuperSQLInjection.exe (PID: 3724)
- Setup.exe (PID: 856)
- Setup.exe (PID: 1120)
- SuperSQLInjection .exe (PID: 2536)
- svchost.exe (PID: 3464)
Drops a file with a compile date too recent
- SuperSQLInjection.exe (PID: 3724)
- Setup.exe (PID: 856)
Executable content was dropped or overwritten
- SuperSQLInjection.exe (PID: 3724)
- Setup.exe (PID: 856)
Creates files in the user directory
- Setup.exe (PID: 856)
Creates executable files which already exist in Windows
- Setup.exe (PID: 856)
Reads Environment values
- SuperSQLInjection .exe (PID: 2536)
- svchost.exe (PID: 3464)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-Sep-06 09:06:50 |
| Debug artifacts: |
|
| Comments: | 超级SQL注入工具 |
| CompanyName: | www.shack2.org |
| FileDescription: | 超级SQL注入工具 |
| FileVersion: | 2.2022.09.06 |
| InternalName: | SuperSQLInjection.exe |
| LegalCopyright: | Copyright © 2014-2022 |
| OriginalFilename: | SuperSQLInjection.exe |
| ProductName: | 超级SQL注入工具 |
| ProductVersion: | 2.2022.09.06 |
| Assembly Version: | 2.2022.9.6 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 4 |
| TimeDateStamp: | 2022-Sep-06 09:06:50 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 969140 | 969216 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46262 |
.sdata | 983040 | 312 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.90266 |
.rsrc | 991232 | 8456 | 8704 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.50902 |
.reloc | 1007616 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.65999 | 872 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 2.63578 | 6760 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.1815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | SuperSQLInjection.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1120 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | — | SuperSQLInjection.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Temp\SuperSQLInjection .exe" | C:\Users\admin\AppData\Local\Temp\SuperSQLInjection .exe | SuperSQLInjection.exe | ||||||||||||
User: admin Company: www.shack2.org Integrity Level: MEDIUM Description: 超级SQL注入工具 Exit code: 0 Version: 2.2022.09.06 Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svchost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svchost.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 8.1.1.7900 Modules
| |||||||||||||||
| 3724 | "C:\Users\admin\AppData\Local\Temp\SuperSQLInjection.exe" | C:\Users\admin\AppData\Local\Temp\SuperSQLInjection.exe | Explorer.EXE | ||||||||||||
User: admin Company: www.shack2.org Integrity Level: MEDIUM Description: 超级SQL注入工具 Exit code: 0 Version: 2.2022.09.06 Modules
| |||||||||||||||
Total events
3 173
Read events
3 132
Write events
41
Delete events
0
Modification events
| (PID) Process: | (3724) SuperSQLInjection.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3724) SuperSQLInjection.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3724) SuperSQLInjection.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3724) SuperSQLInjection.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (856) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Corporation Security |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svchost.exe | |||
| (PID) Process: | (856) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (856) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (856) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (856) Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3464) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | SuperSQLInjection.exe | C:\Users\admin\AppData\Local\Temp\SuperSQLInjection .exe | executable | |
MD5:— | SHA256:— | |||
| 856 | Setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svchost.zip | compressed | |
MD5:BBF128484E7EA29053C6DB91849067EA | SHA256:5E6F03B5AE15131C2AD374C563273389B3340168FF647433A6B5E7ACCE468B05 | |||
| 856 | Setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\svchost.exe | executable | |
MD5:301E8D9A2445DD999CE816C17D8DBBB3 | SHA256:2EA1FA52A6896CE0100084E3696712D76B4D1E995CA0012954BAE3107562A9EB | |||
| 3724 | SuperSQLInjection.exe | C:\Users\admin\AppData\Local\Temp\Setup.exe | executable | |
MD5:0E6C9432CBA1614FCCC232F201028C72 | SHA256:C9A2FAFFEE3DE29E278A89E54B07EDB1F520F5E665480A1002D401FD83CDE2E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
3
Threats
0
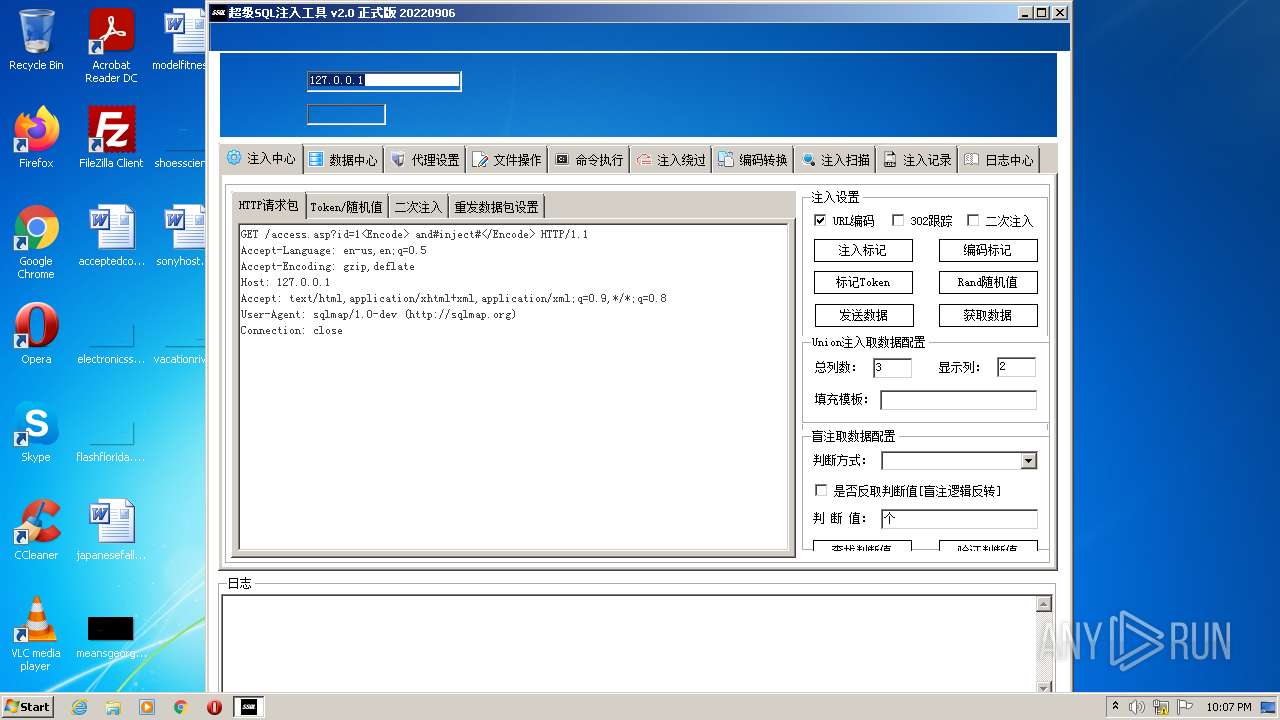
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | SuperSQLInjection .exe | GET | 200 | 103.140.126.221:80 | http://www.shack2.org/soft/getNewVersion?ENNAME=SSuperSQLInjection&NO=Windows%207%20Professional_002473381550298792560580364476967332872324859630450755_n%3a18C4897E77EE&VERSION=20220906 | unknown | text | 240 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3464 | svchost.exe | 144.126.144.223:80 | amazonhost.thedreamsop.com | CONTABO | US | malicious |
2536 | SuperSQLInjection .exe | 103.140.126.221:80 | www.shack2.org | Cloudie Limited | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amazonhost.thedreamsop.com |
| suspicious |
www.shack2.org |
| suspicious |