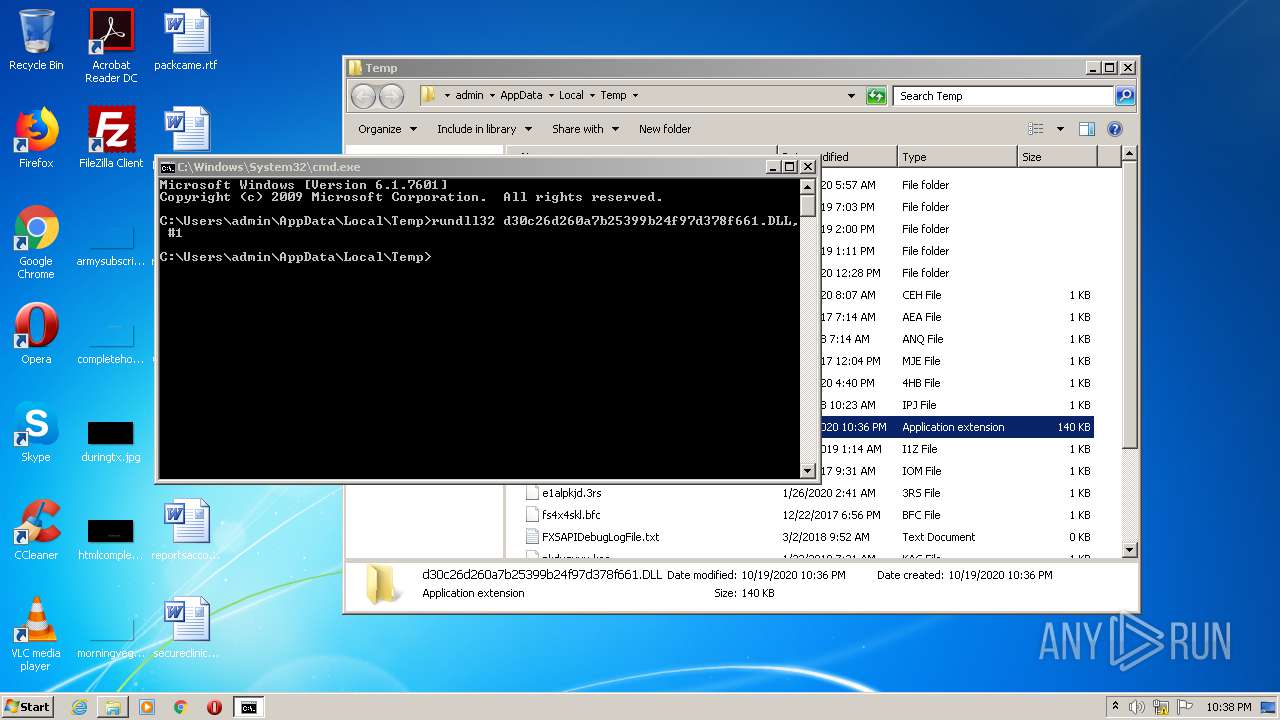
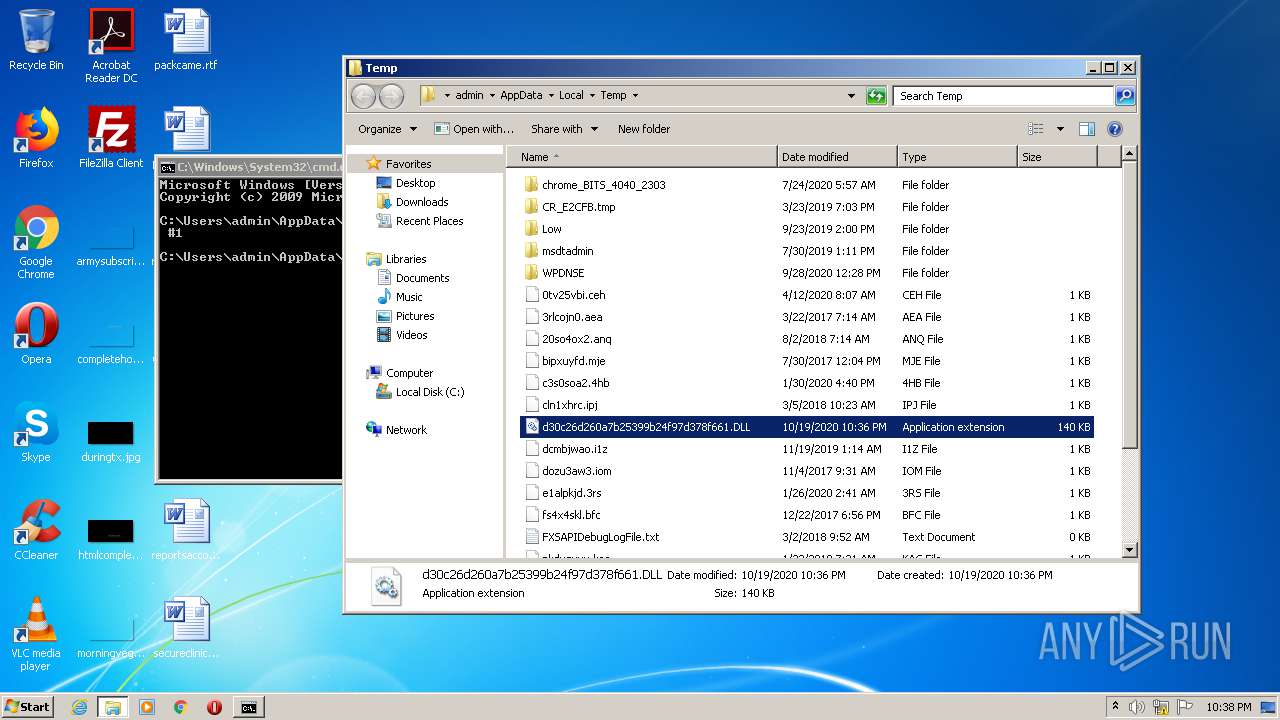
| File name: | d30c26d260a7b25399b24f97d378f661.DLL |
| Full analysis: | https://app.any.run/tasks/aaca56dd-476f-46cc-8b44-43b73deef52c |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:36:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | D30C26D260A7B25399B24F97D378F661 |
| SHA1: | 4F7F5B3919B757C07F7B64485D3C8674191156AF |
| SHA256: | 33BC940890385358C40928C4E23504AF1C5BB8A3406E930320CE1D2AABB40326 |
| SSDEEP: | 1536:3PETbGImcLvic0FexAhznoTj/JTo5HIj+2z0oNJHjSI6jZxM3vZx3iR7SOQ:3PEXGW3MeAF2xQCTpnF6jbM/b3iRe |
MALICIOUS
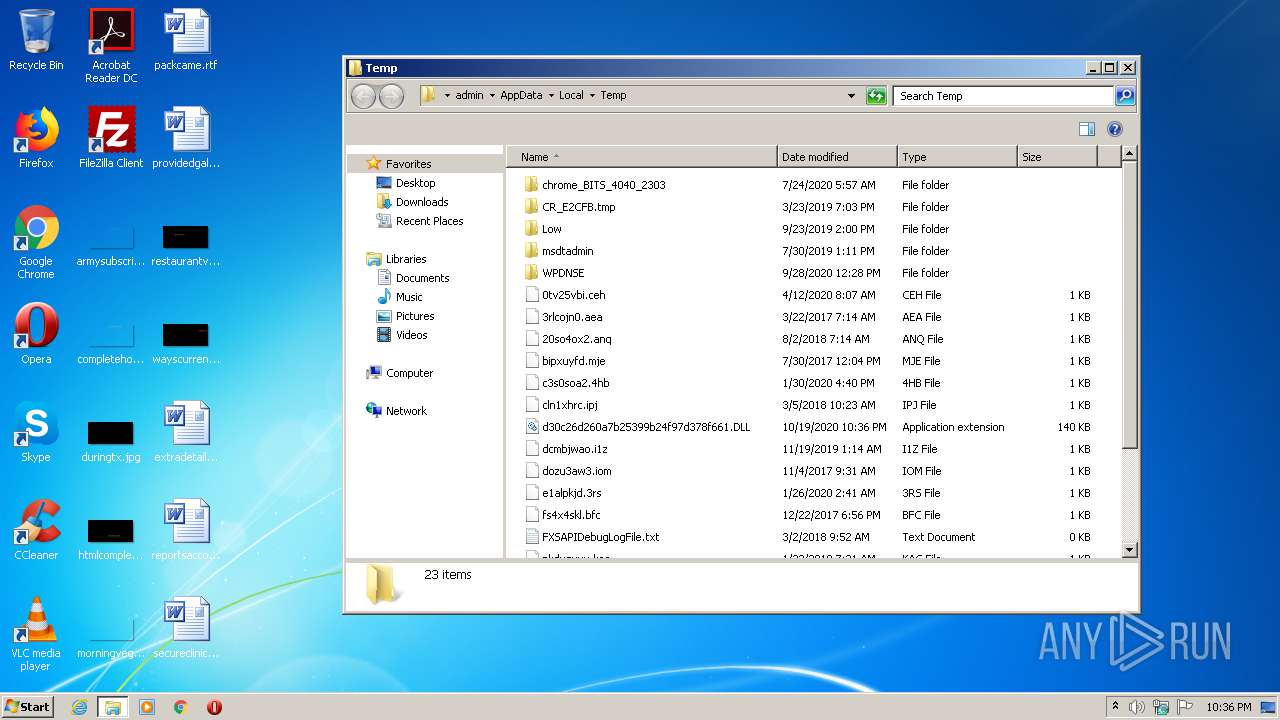
Runs app for hidden code execution
- explorer.exe (PID: 324)
Loads dropped or rewritten executable
- explorer.exe (PID: 324)
- rundll32.exe (PID: 2508)
SUSPICIOUS
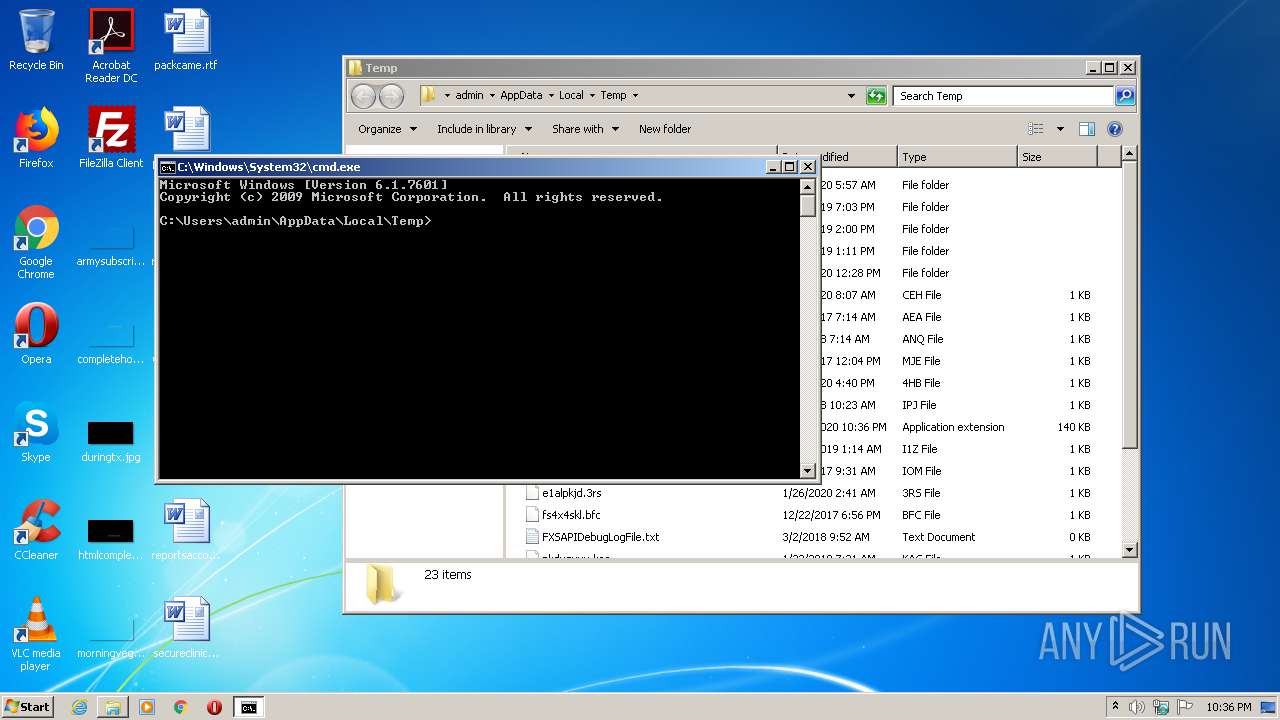
Starts CMD.EXE for commands execution
- explorer.exe (PID: 324)
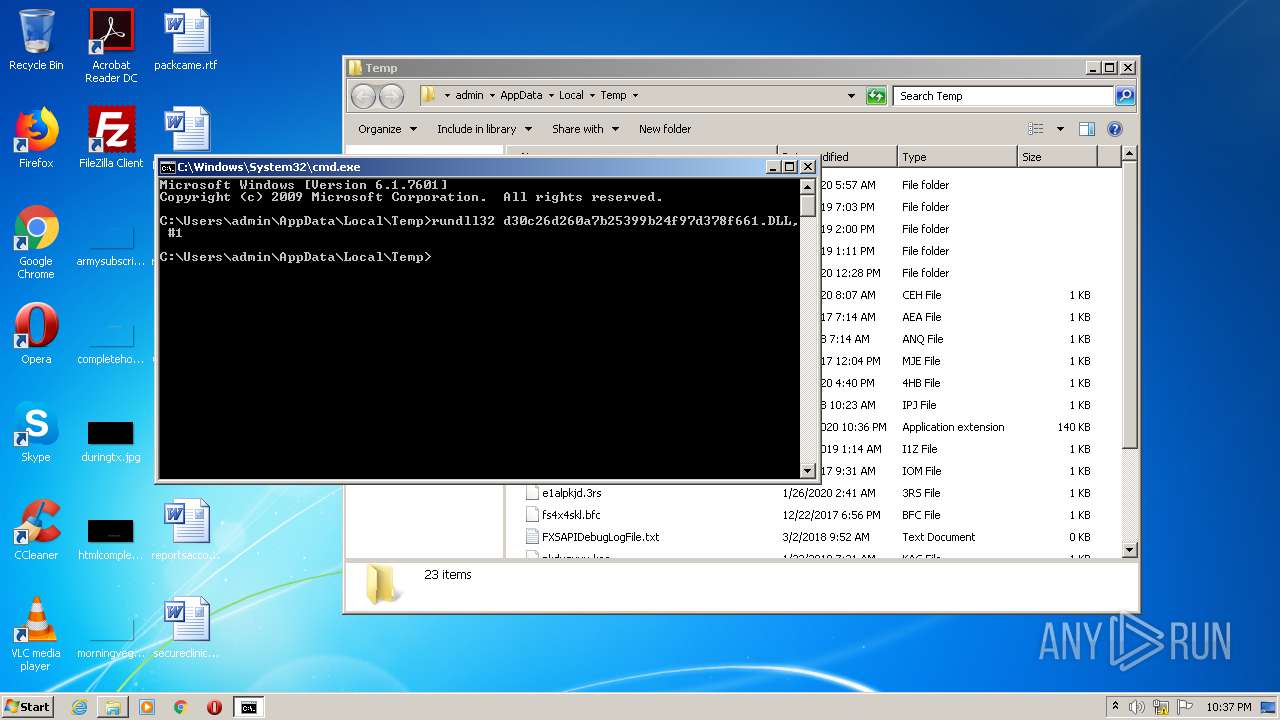
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3280)
- explorer.exe (PID: 324)
Starts Internet Explorer
- rundll32.exe (PID: 2292)
INFO
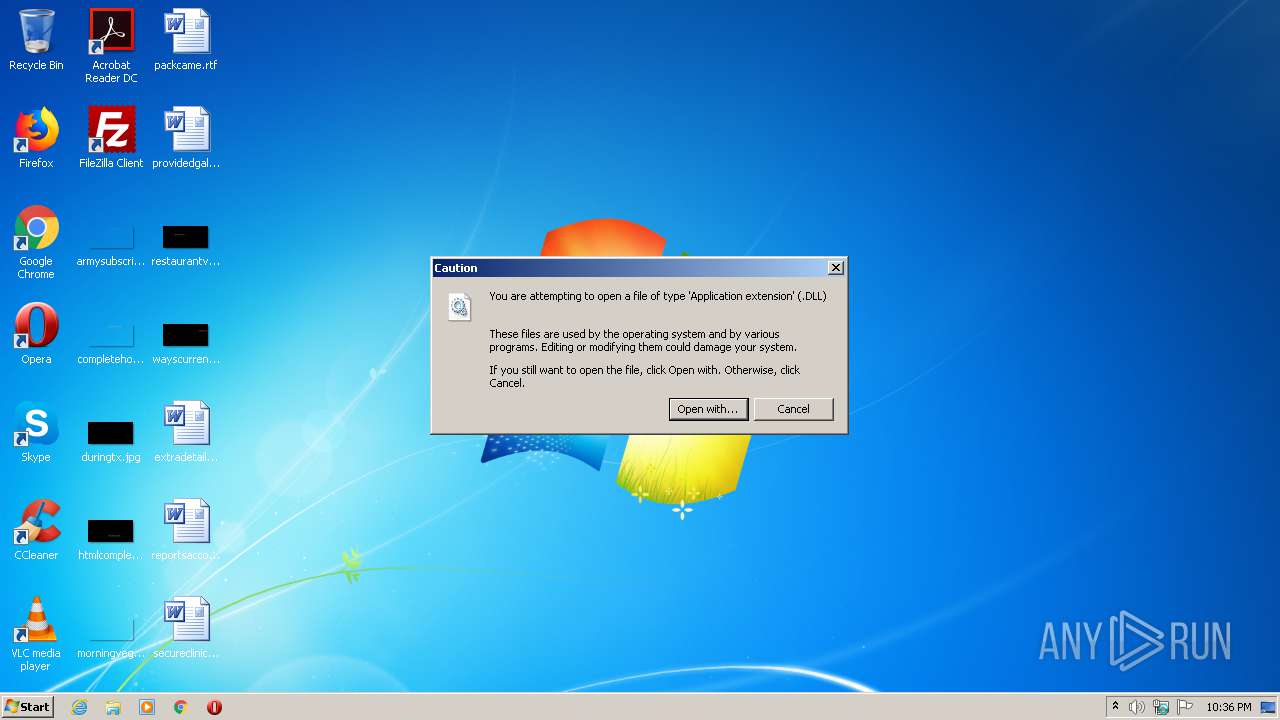
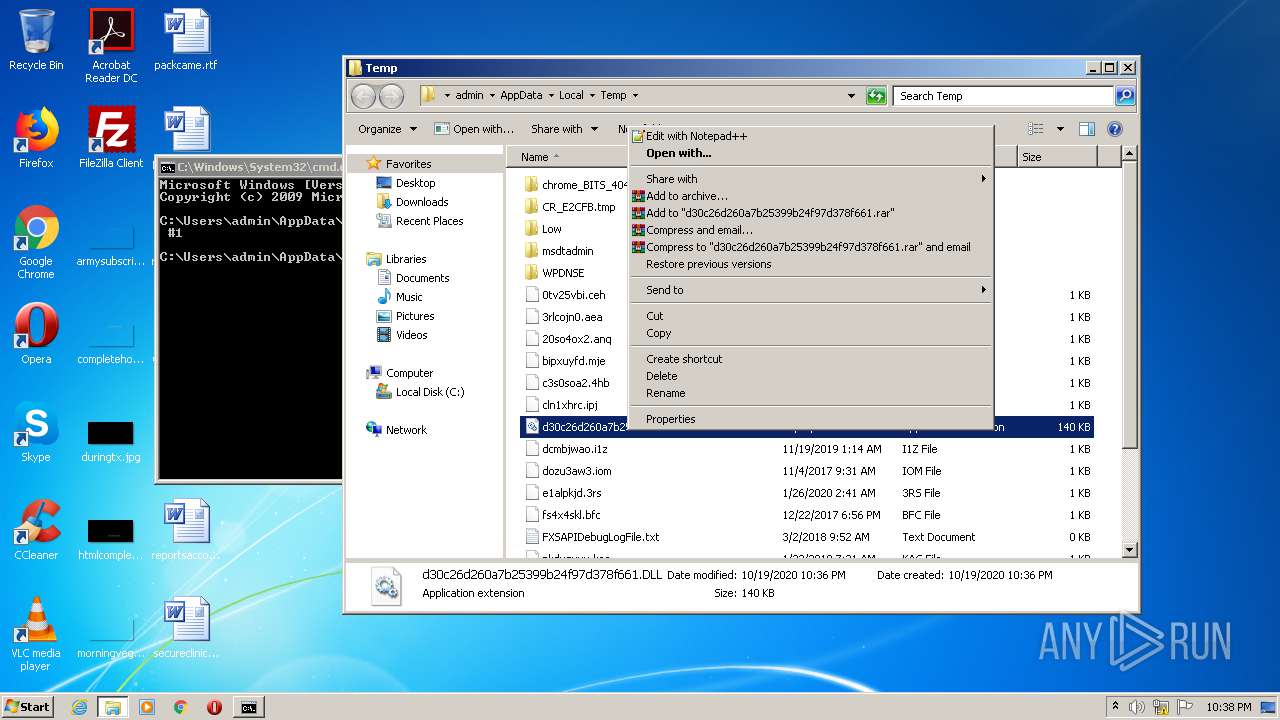
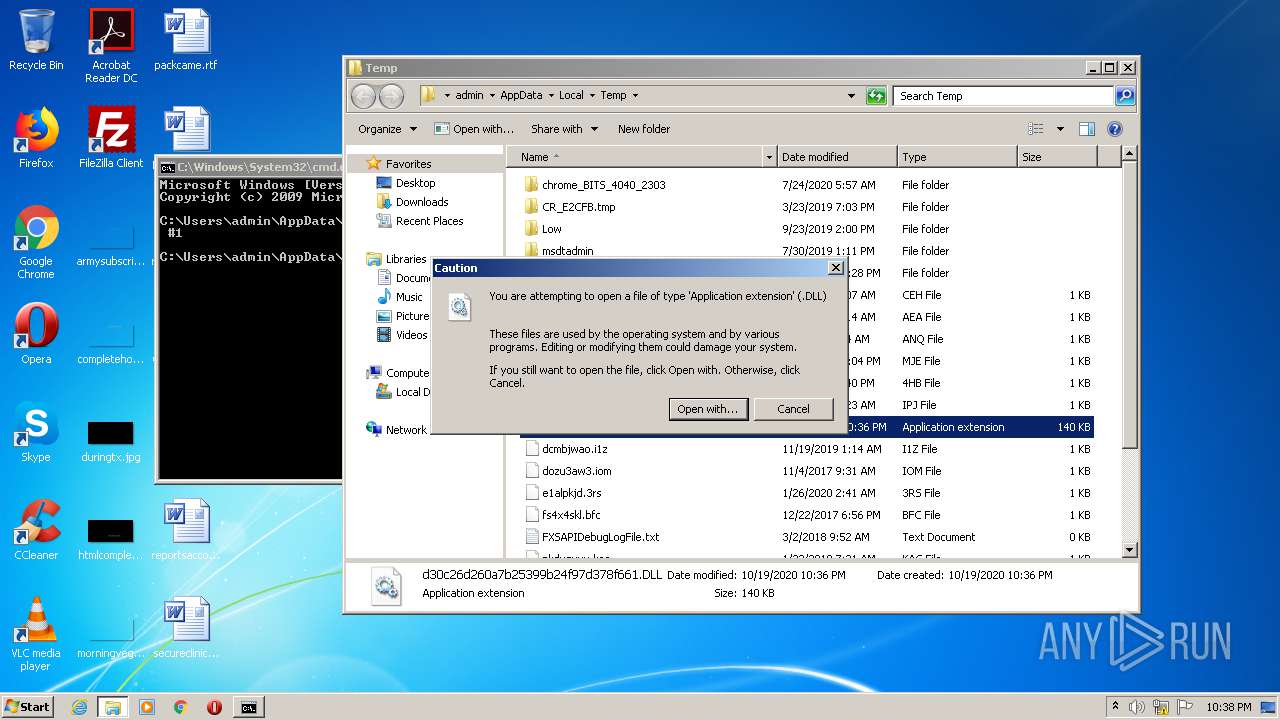
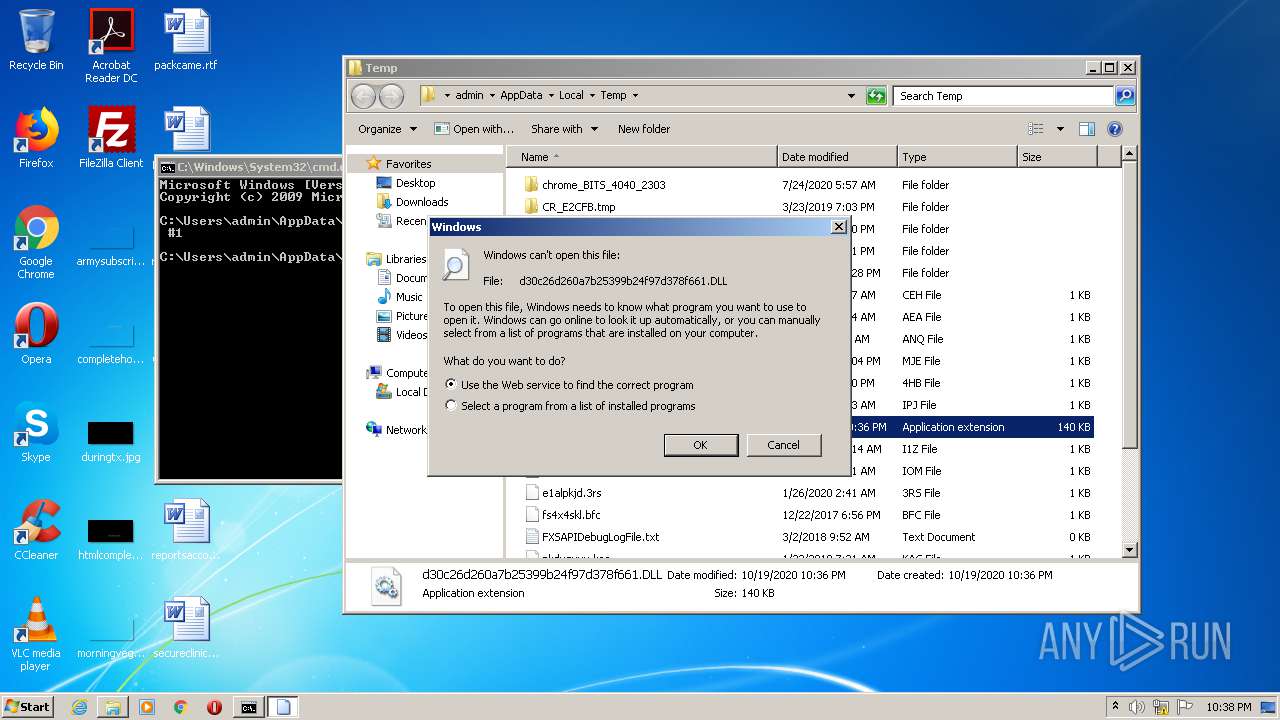
Manual execution by user
- verclsid.exe (PID: 2852)
- cmd.exe (PID: 3280)
Reads Internet Cache Settings
- iexplore.exe (PID: 1476)
- iexplore.exe (PID: 3984)
Changes internet zones settings
- iexplore.exe (PID: 1476)
Application launched itself
- iexplore.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:10:03 17:05:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 98304 |
| InitializedDataSize: | 421888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3d0f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.7.131 |
| ProductVersionNumber: | 3.4.7.131 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Carfeet |
| ProductName: | Well indicate |
| FileDescription: | Well indicate |
| FileVersion: | 3.4.7.131 |
| LegalCopyright: | Copyright © Carfeet 1998-2017 |
| OriginalFileName: | Basic.dll |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Oct-2020 15:05:15 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Carfeet |
| ProductName: | Well indicate |
| FileDescription: | Well indicate |
| FileVersion: | 3.4.7.131 |
| LegalCopyright: | Copyright © Carfeet 1998-2017 |
| OriginalFilename: | Basic.dll |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Oct-2020 15:05:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001774D | 0x00018000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.85371 |
.rdata | 0x00019000 | 0x00003E38 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27751 |
.data | 0x0001D000 | 0x0005E048 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.48965 |
.rsrc | 0x0007C000 | 0x00000460 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.50453 |
.reloc | 0x0007D000 | 0x00002482 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.69528 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40725 | 604 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.79597 | 346 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
MSWSOCK.dll |
NETAPI32.dll |
PSAPI.DLL |
Exports
Title | Ordinal | Address |
|---|---|---|
Addwalk | 1 | 0x00017DA0 |
DllRegisterServer | 2 | 0x00017B20 |
Multiplywell | 3 | 0x00018130 |
Object | 4 | 0x00013560 |
Round | 5 | 0x00017C20 |
Total processes
42
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
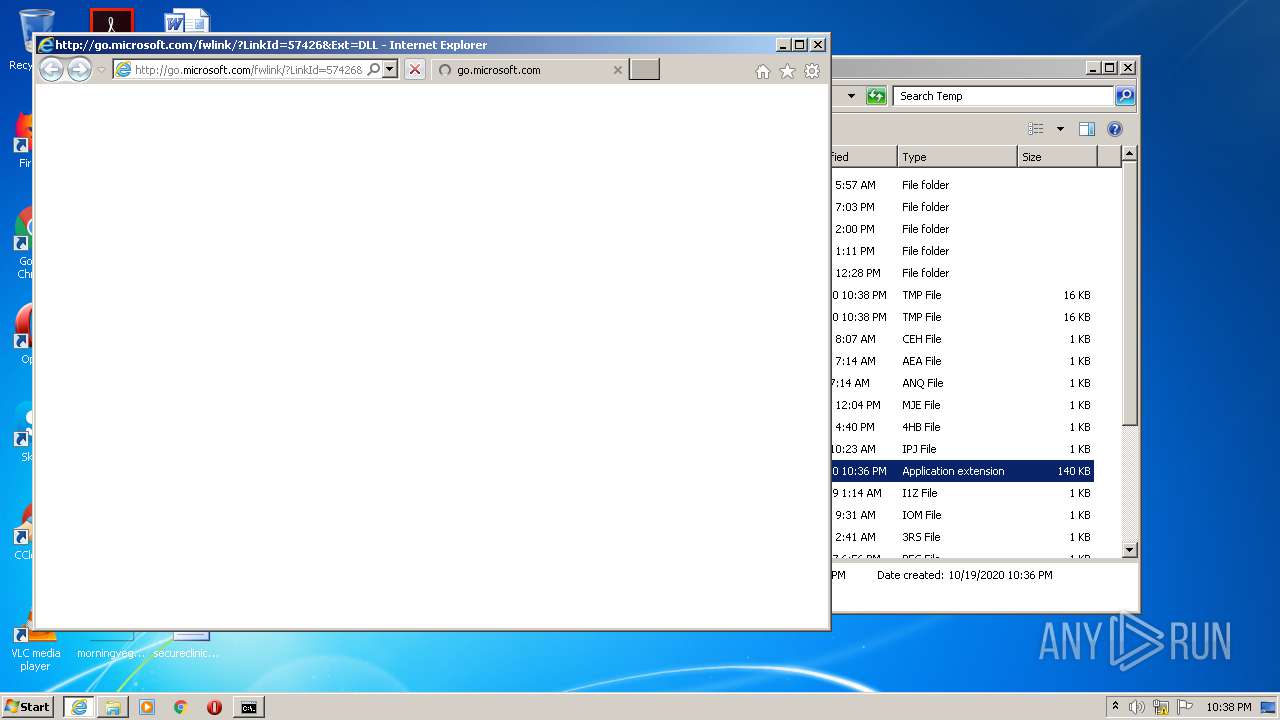
| 1476 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=DLL | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
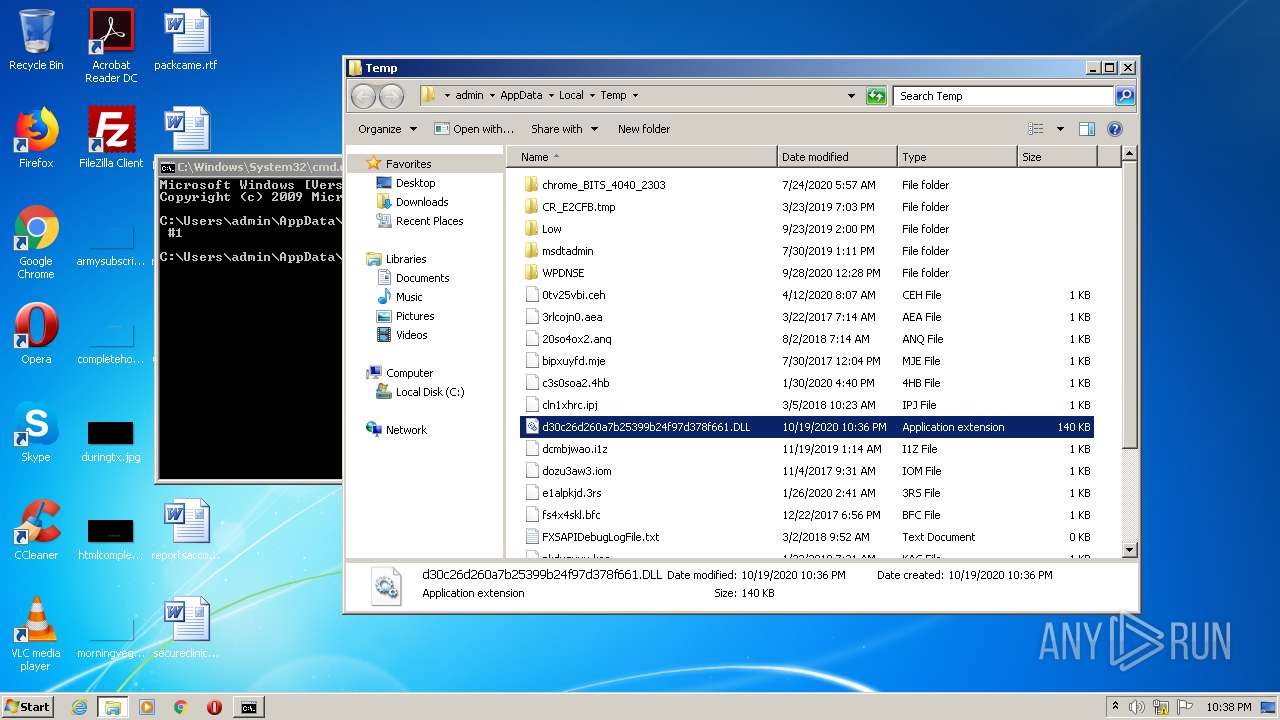
| 2292 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\d30c26d260a7b25399b24f97d378f661.DLL | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2508 | rundll32 d30c26d260a7b25399b24f97d378f661.DLL, #1 | C:\Windows\system32\rundll32.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\d30c26d260a7b25399b24f97d378f661.DLL | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3280 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1476 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 755
Read events
1 446
Write events
308
Delete events
1
Modification events
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {E345F35F-9397-435C-8F95-4E922C26259E} {000214E6-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000066CE88EB5FA6D601 | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0B2C9183-C9FA-4C53-AE21-C900B0C39965} {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} 0x401 |
Value: 0100000000000000F8CCA7EB5FA6D601 | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000001000000020000000B000000000000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | a |
Value: C:\Users\admin\AppData\Local\Temp\1 | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (324) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
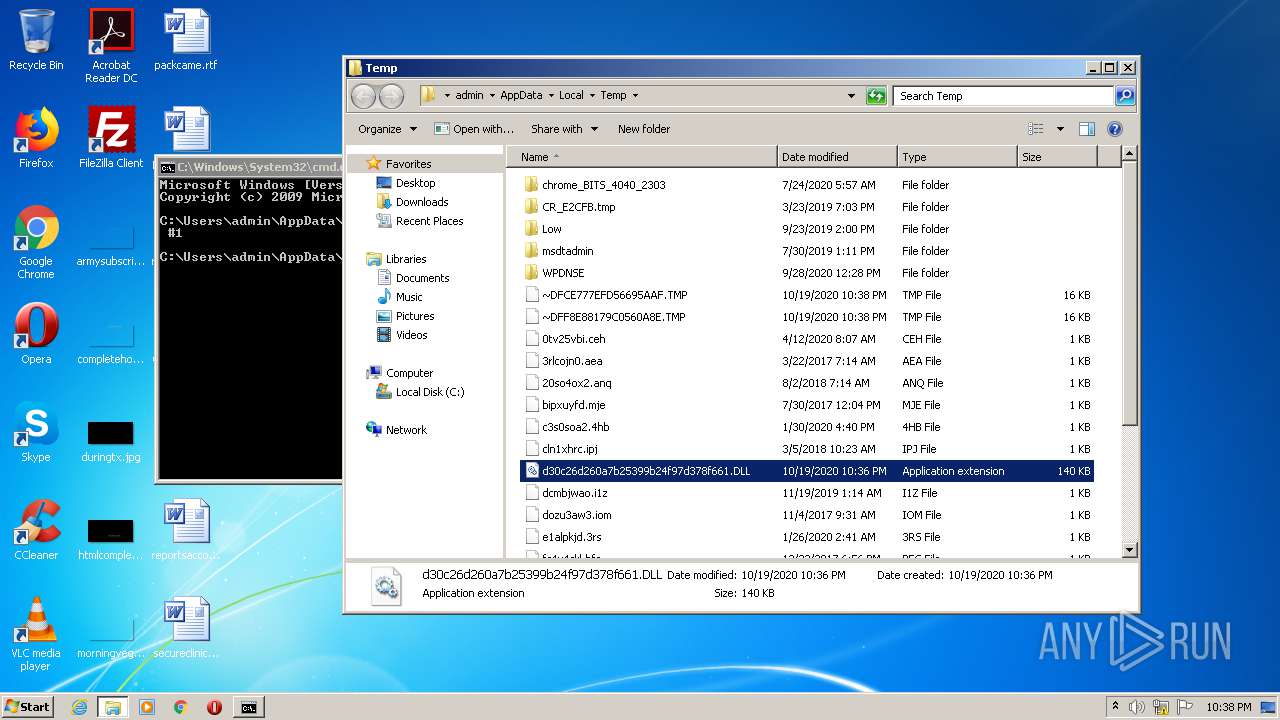
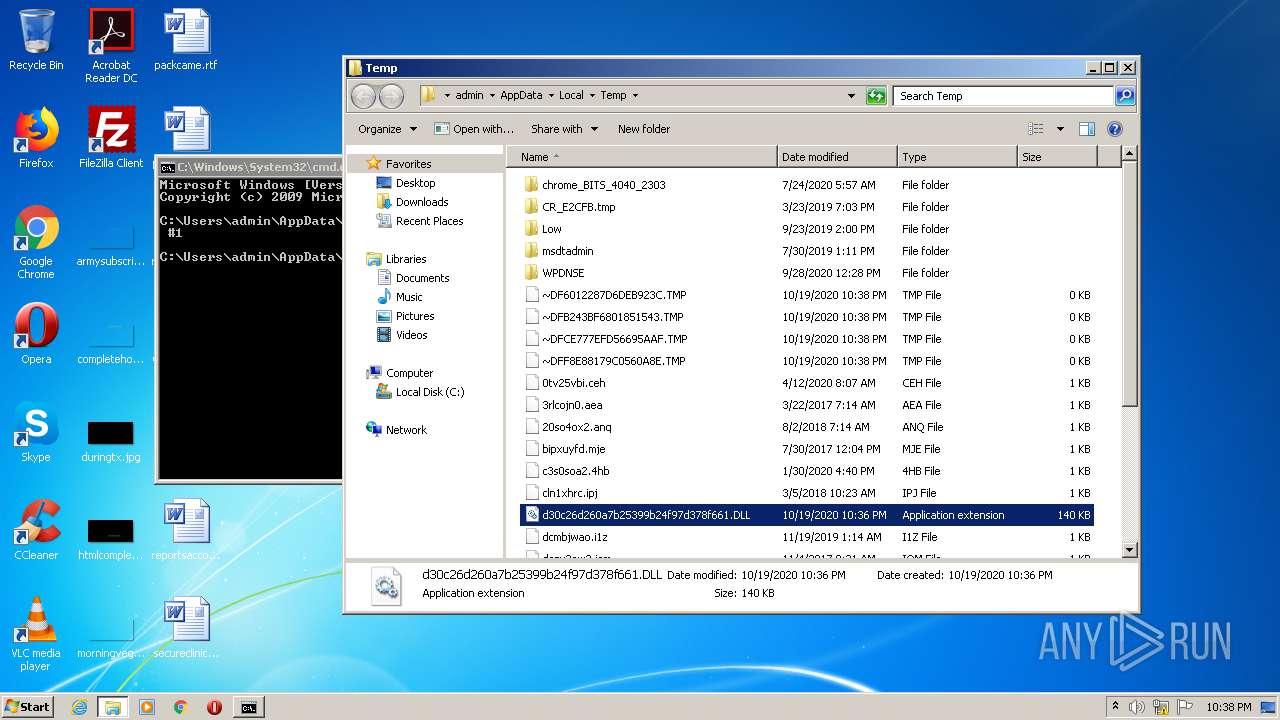
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB243BF6801851543.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6012287D6DEB923C.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF8E88179C0560A8E.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{76526933-1253-11EB-B232-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCE777EFD56695AAF.TMP | — | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{76526931-1253-11EB-B232-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42A7EDC2-DE02-11E9-92C0-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 1476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{7CFB1A8E-1253-11EB-B232-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
34
DNS requests
38
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | iexplore.exe | GET | — | 23.43.114.188:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=DLL | NL | — | — | whitelisted |
1476 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.244.42.195:443 | help.twitter.com | Twitter Inc. | US | suspicious |
2508 | rundll32.exe | 104.108.38.224:443 | support.oracle.com | Akamai Technologies, Inc. | NL | unknown |
— | — | 104.108.38.224:443 | support.oracle.com | Akamai Technologies, Inc. | NL | unknown |
— | — | 23.210.248.4:443 | www.intel.com | Akamai International B.V. | NL | whitelisted |
2508 | rundll32.exe | 23.210.248.4:443 | www.intel.com | Akamai International B.V. | NL | whitelisted |
2508 | rundll32.exe | 23.203.92.40:443 | support.apple.com | Akamai Technologies, Inc. | US | unknown |
— | — | 104.244.42.131:443 | help.twitter.com | Twitter Inc. | US | suspicious |
2508 | rundll32.exe | 2.21.36.173:443 | support.microsoft.com | GTT Communications Inc. | FR | malicious |
1476 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3984 | iexplore.exe | 23.43.114.188:80 | go.microsoft.com | Akamai International B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
help.twitter.com |
| whitelisted |
support.oracle.com |
| whitelisted |
www.intel.com |
| whitelisted |
support.apple.com |
| whitelisted |
support.microsoft.com |
| malicious |
loadfelicio.fit |
| unknown |
dns.msftncsi.com |
| shared |
go.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2508 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2508 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .fit TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .fit TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .fit TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .fit TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .fit TLD |
2508 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2508 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2508 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |