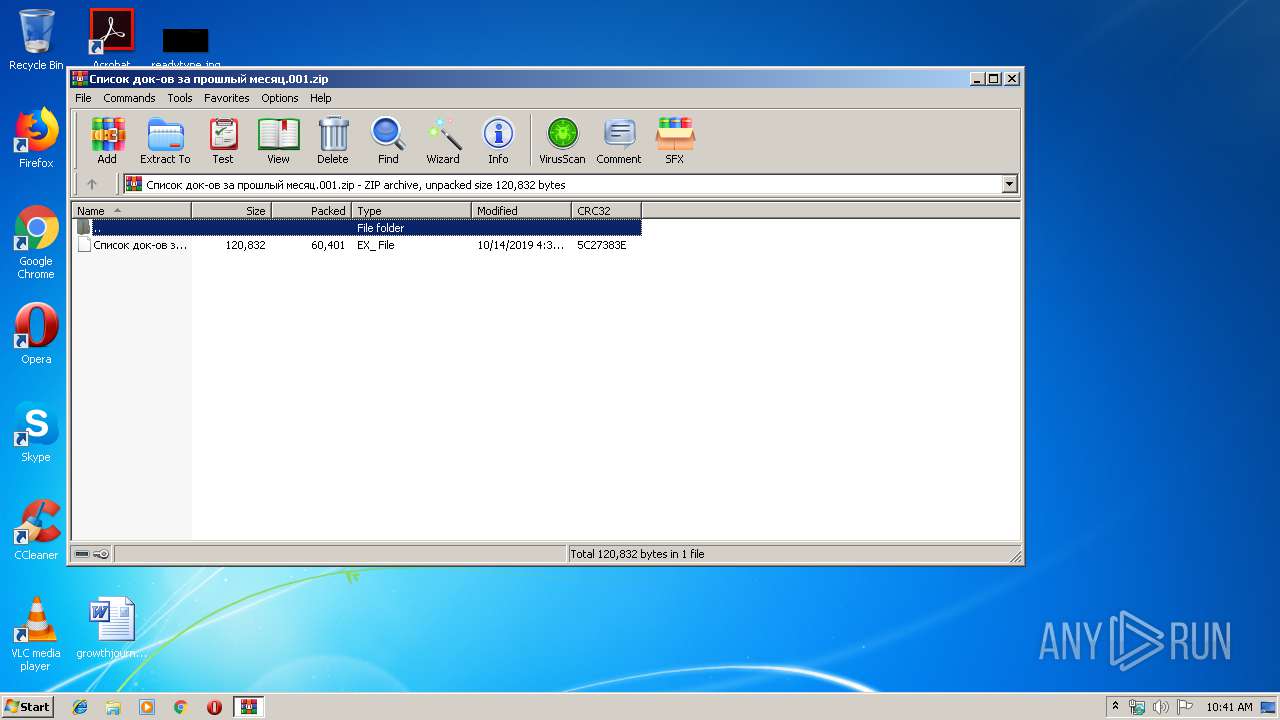
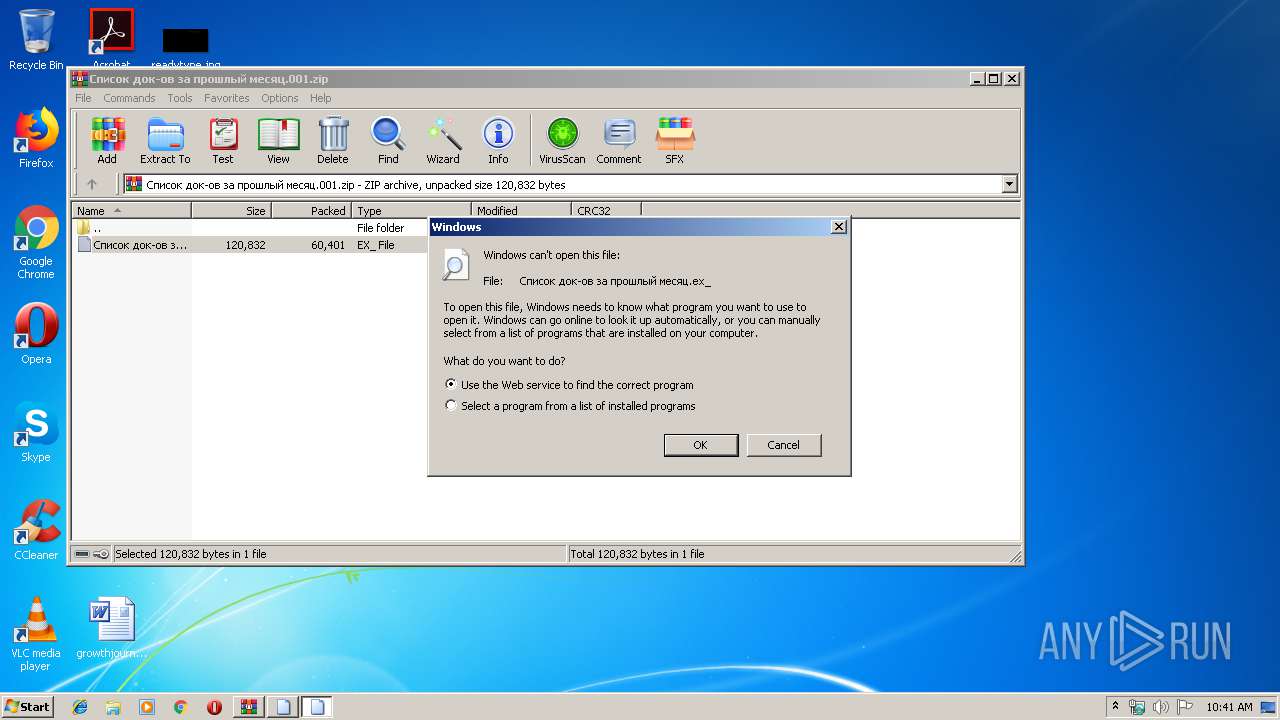
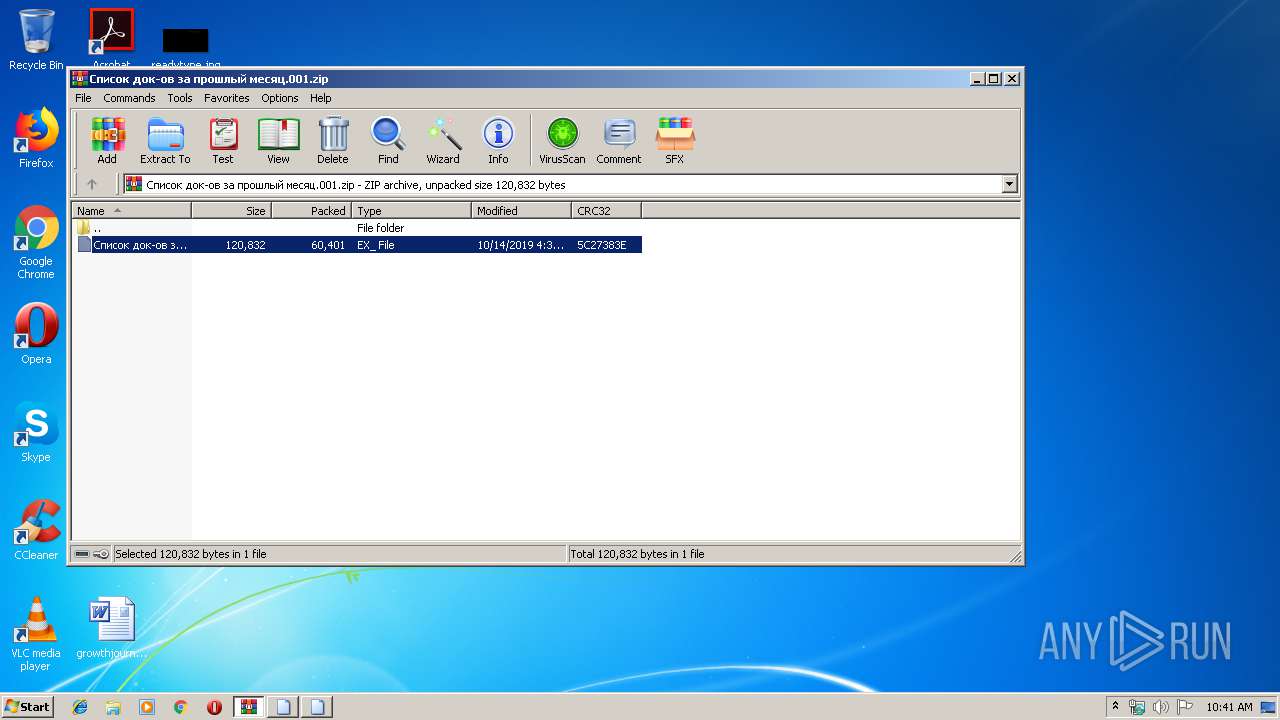
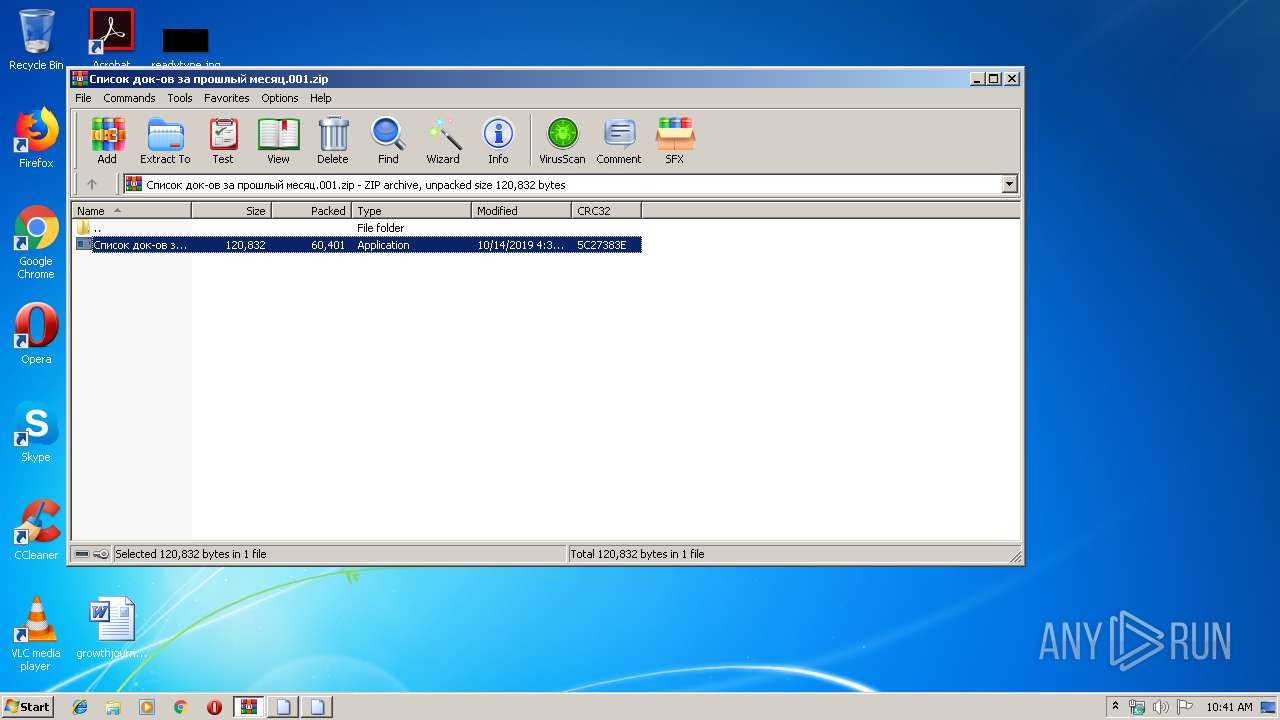
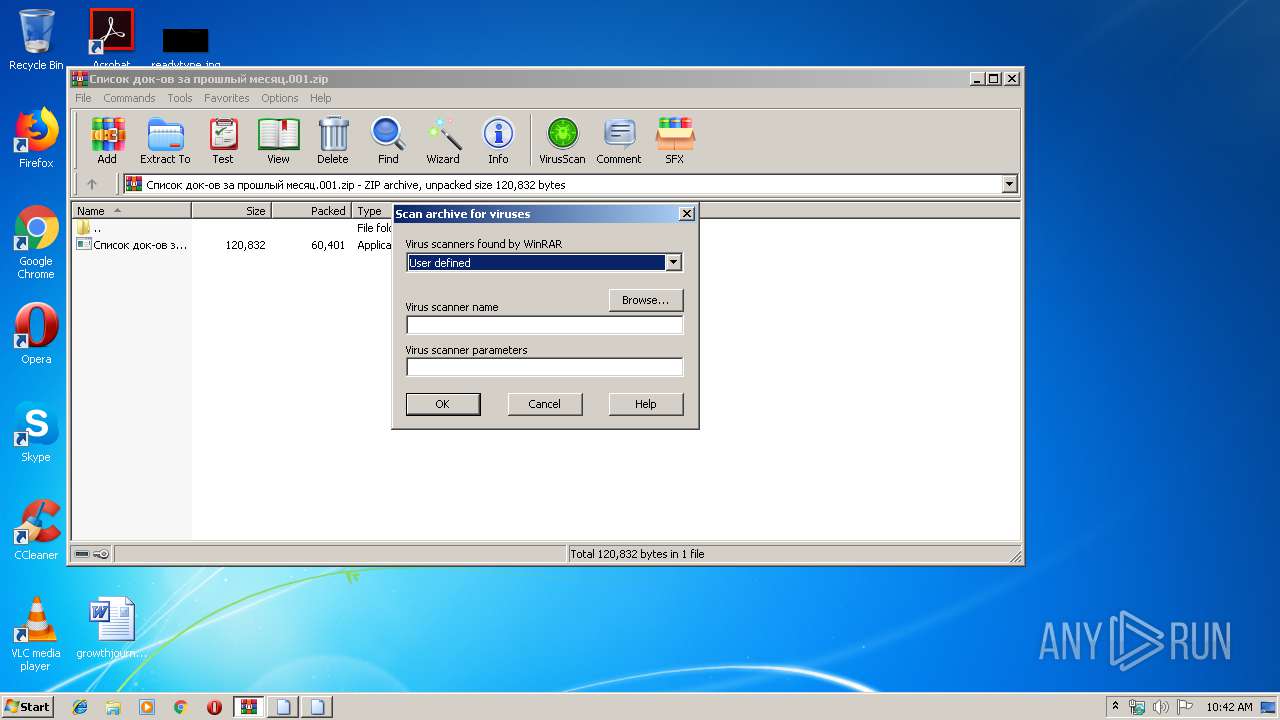
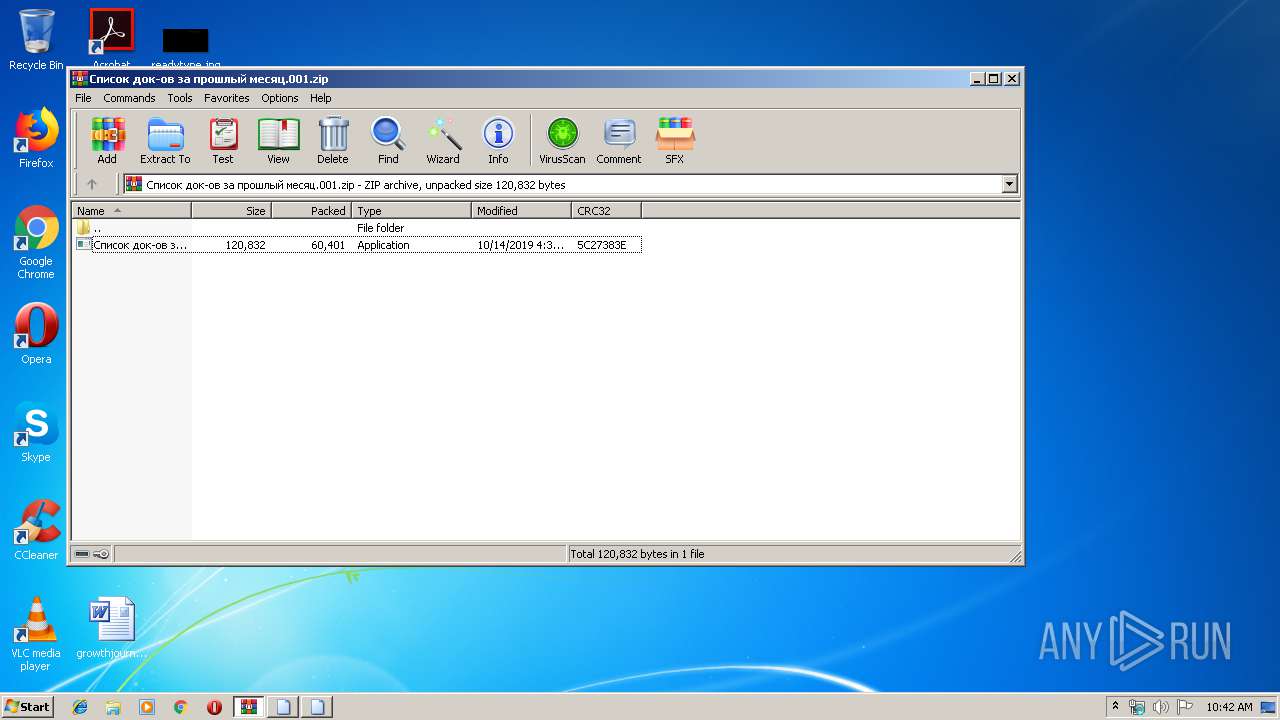
| File name: | Список док-ов за прошлый месяц.001 |
| Full analysis: | https://app.any.run/tasks/d4be0918-a15e-4ebf-8c1c-630b0b309d6a |
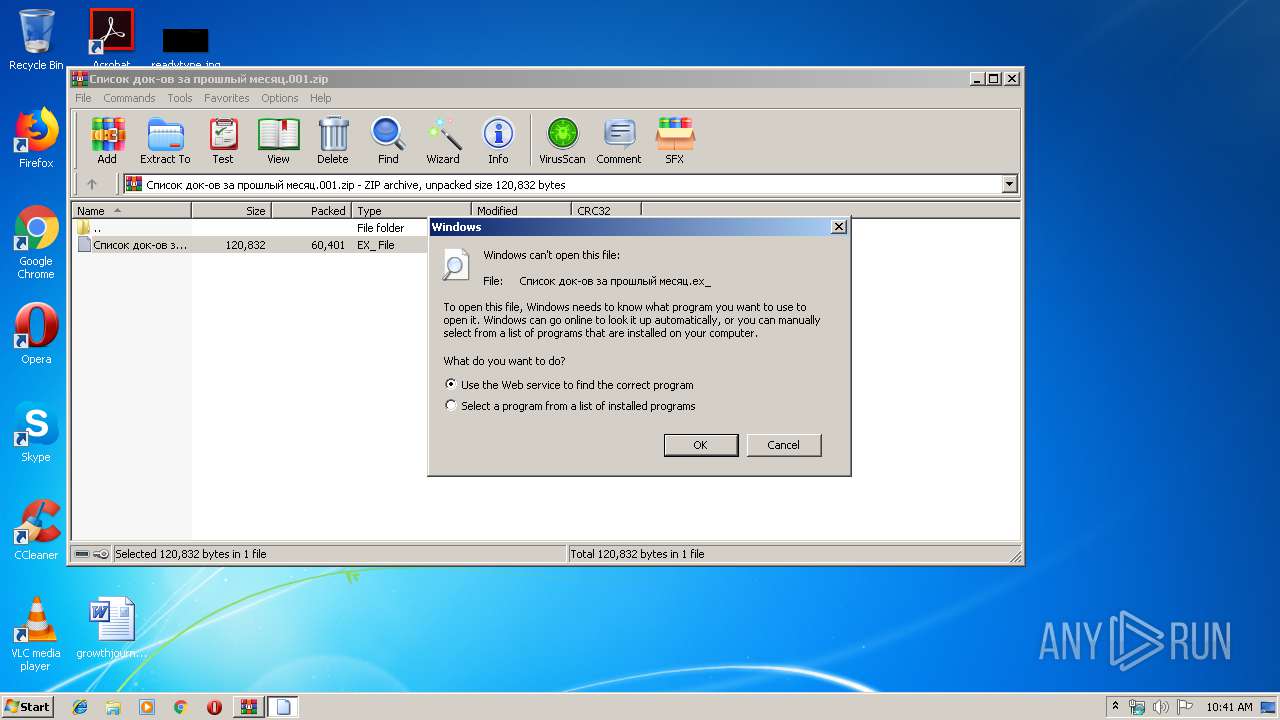
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 09:41:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 91861FD3E18AC68FF47A66AEE0F5A108 |
| SHA1: | 1962D2C9C978852A1A139932754B3D748C9B464D |
| SHA256: | 33BC07770775C641077A82A234B9EBED450F51F7367727955E6F4626BC3E9C90 |
| SSDEEP: | 1536:OsAvTG/ZguVvrWZQj8bnbv7tDEWVUlYgUdw78eMoQb3/tEg:fAvTG/xW/vBpVU+d40oQb1r |
MALICIOUS
Application was dropped or rewritten from another process
- Список док-ов за прошлый месяц.exe (PID: 320)
- Список док-ов за прошлый месяц.exe (PID: 1036)
SUSPICIOUS
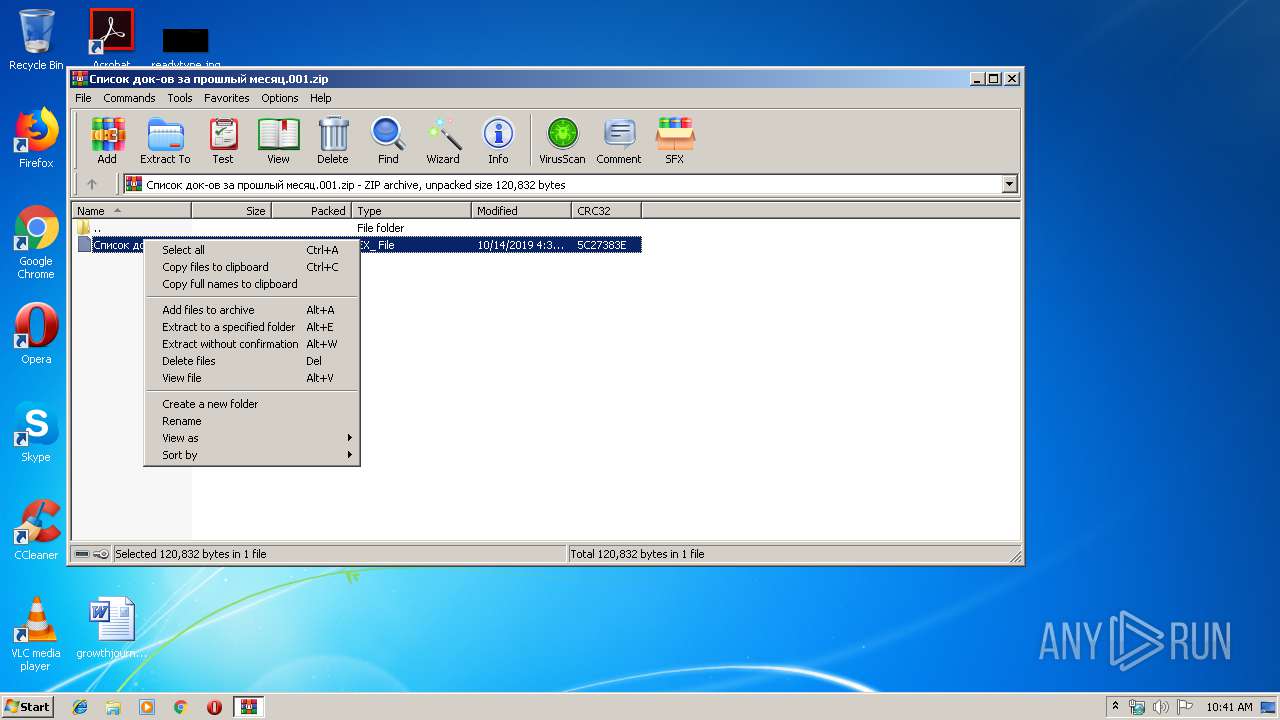
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 1944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1944)
INFO
Application was crashed
- Список док-ов за прошлый месяц.exe (PID: 320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
40
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.11809\Список док-ов за прошлый месяц.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.11809\Список док-ов за прошлый месяц.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.11809\Список док-ов за прошлый месяц.exe" dfsr | C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.11809\Список док-ов за прошлый месяц.exe | Список док-ов за прошлый месяц.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Список док-ов за прошлый месяц.001.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2832 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa1944.10475\Список док-ов за прошлый месяц.ex_ | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa1944.10379\Список док-ов за прошлый месяц.ex_ | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
556
Read events
519
Write events
37
Delete events
0
Modification events
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Список док-ов за прошлый месяц.001.zip | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rzi_1944.11678 | — | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1944.11809\Список док-ов за прошлый месяц.exe | executable | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1944.10379\Список док-ов за прошлый месяц.ex_ | executable | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1944.10475\Список док-ов за прошлый месяц.ex_ | executable | |
MD5:— | SHA256:— | |||
| 1944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Список док-ов за прошлый месяц.001.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1036 | Список док-ов за прошлый месяц.exe | 104.16.54.3:443 | blockchain.info | Cloudflare Inc | US | shared |
1036 | Список док-ов за прошлый месяц.exe | 34.206.50.228:443 | api.blockcypher.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blockchain.info |
| shared |
api.blockcypher.com |
| malicious |