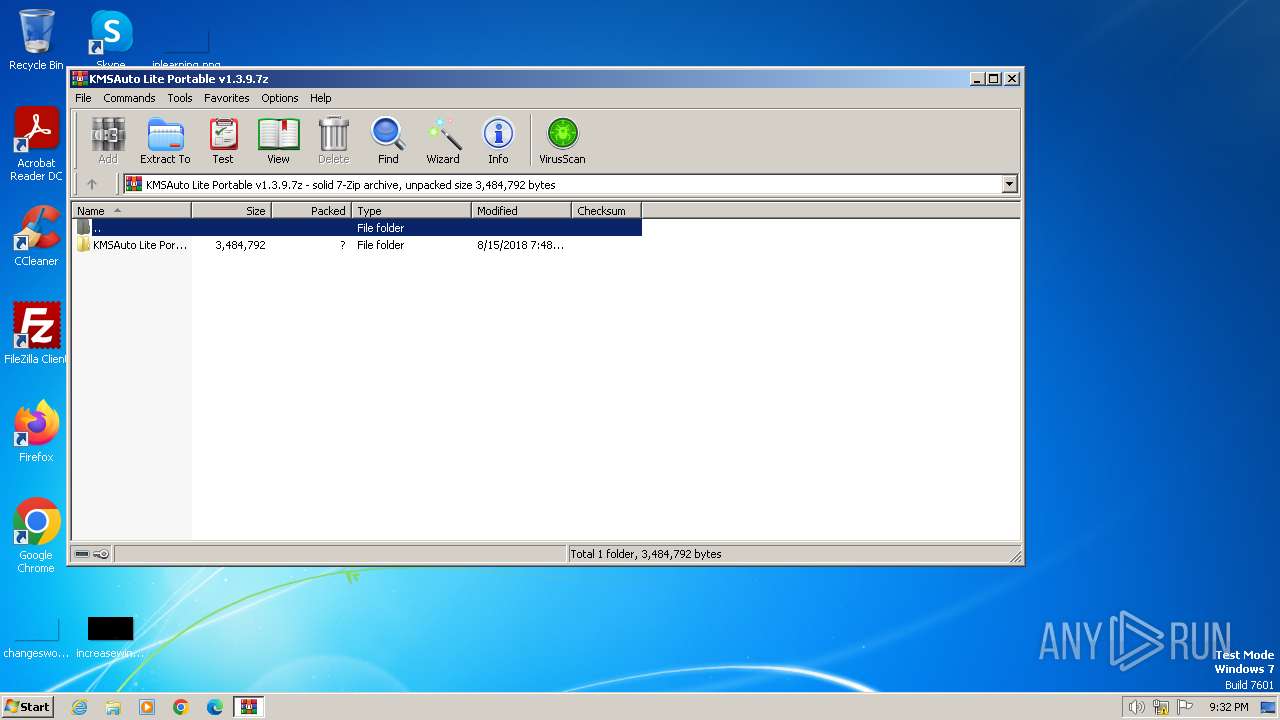
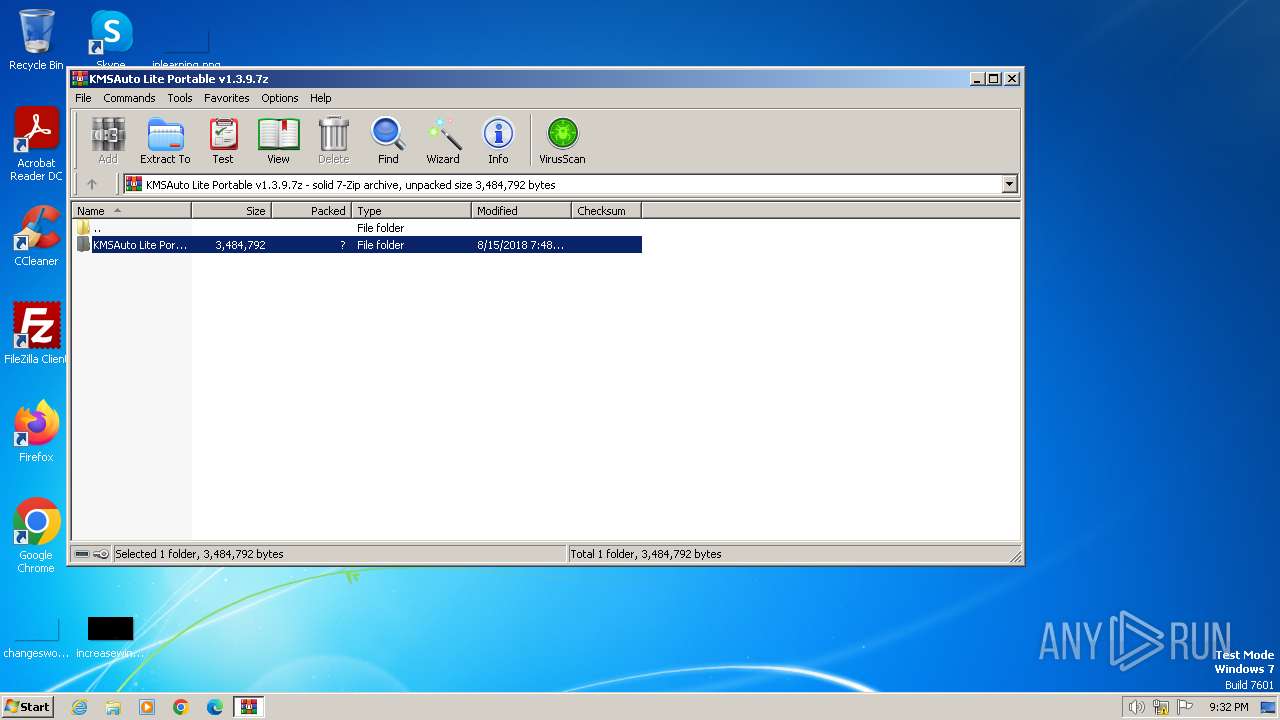
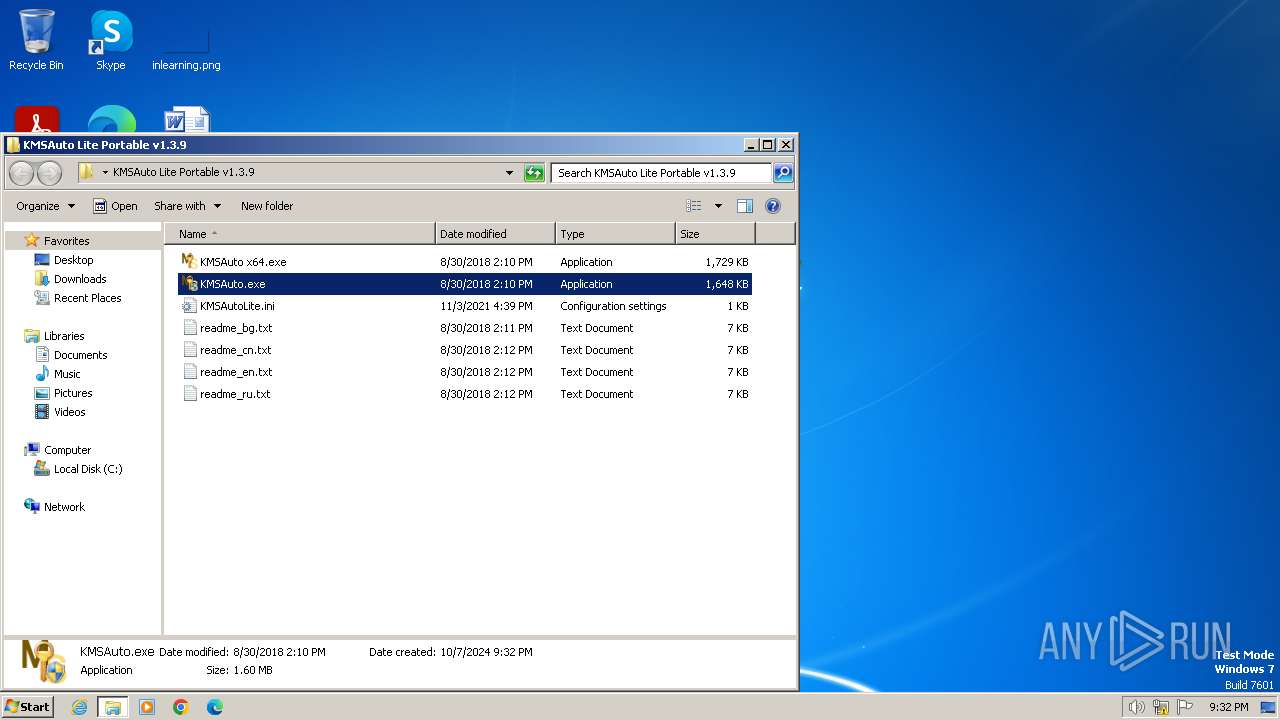
| File name: | KMSAuto Lite Portable v1.3.9.7z |
| Full analysis: | https://app.any.run/tasks/5ba531d2-665f-4bf4-93a9-d3875f11a262 |
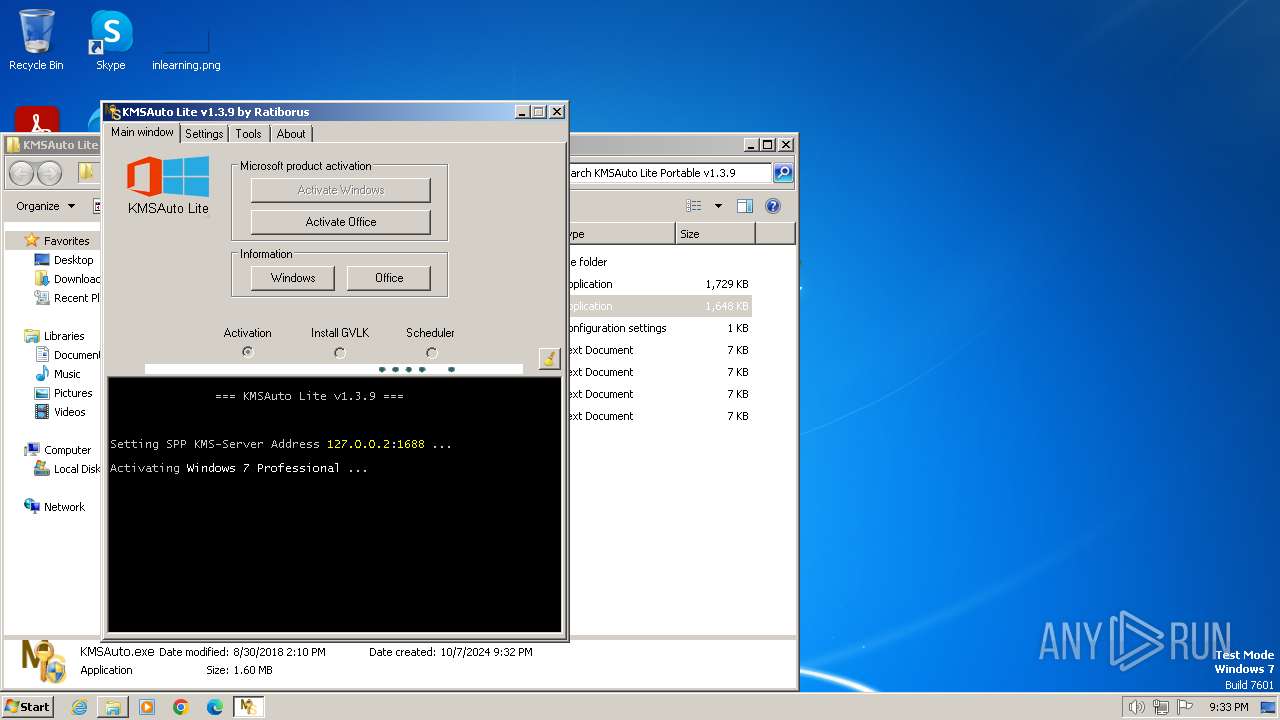
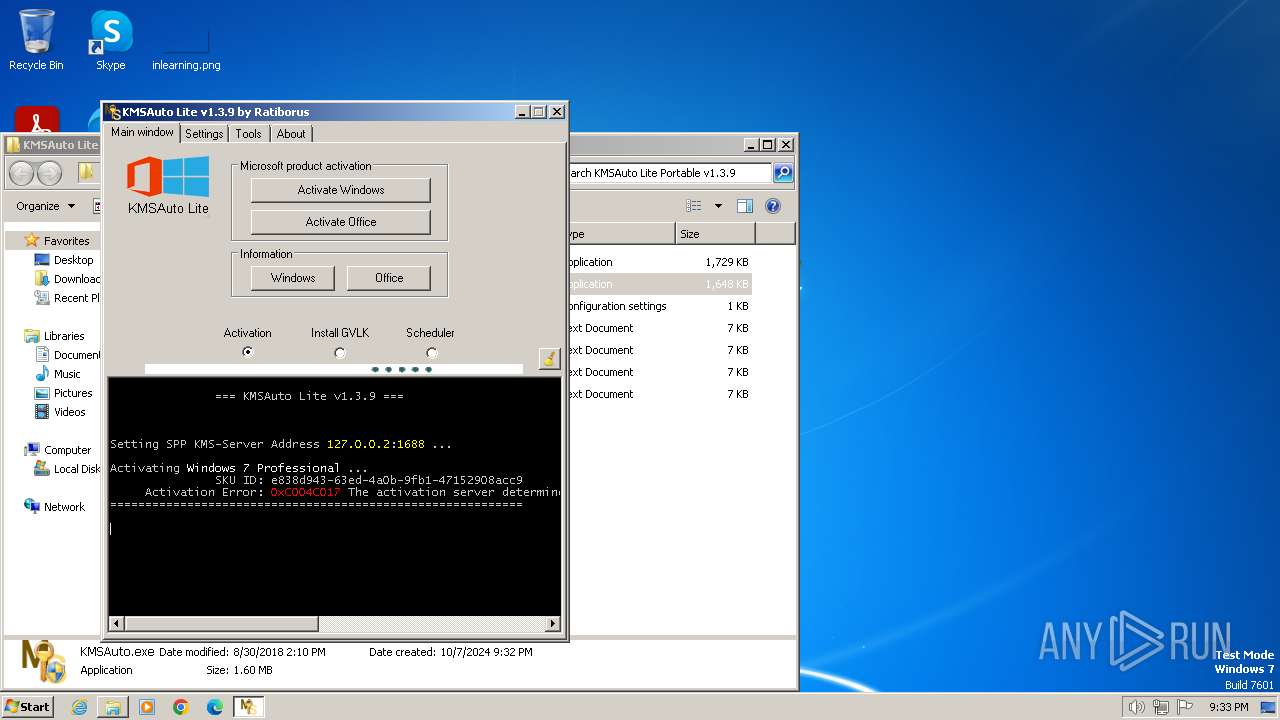
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2024, 20:32:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.3 |
| MD5: | 0E57EC3B5EA7BFF1E269E3823A89D224 |
| SHA1: | B8836993C043010B9B848269174808203A94F731 |
| SHA256: | 33A2BC1D2619A4B3F0D7C8D3AF62F946C3A1A1E17F7EC2D7E5A37548CF3FCFAB |
| SSDEEP: | 98304:hI8J1jxEN7ZAYMpyJD9HdyVXipRu8+X+efXG0bkBmbWx8T7/xingHMOcHo2z5Vg+:AAg |
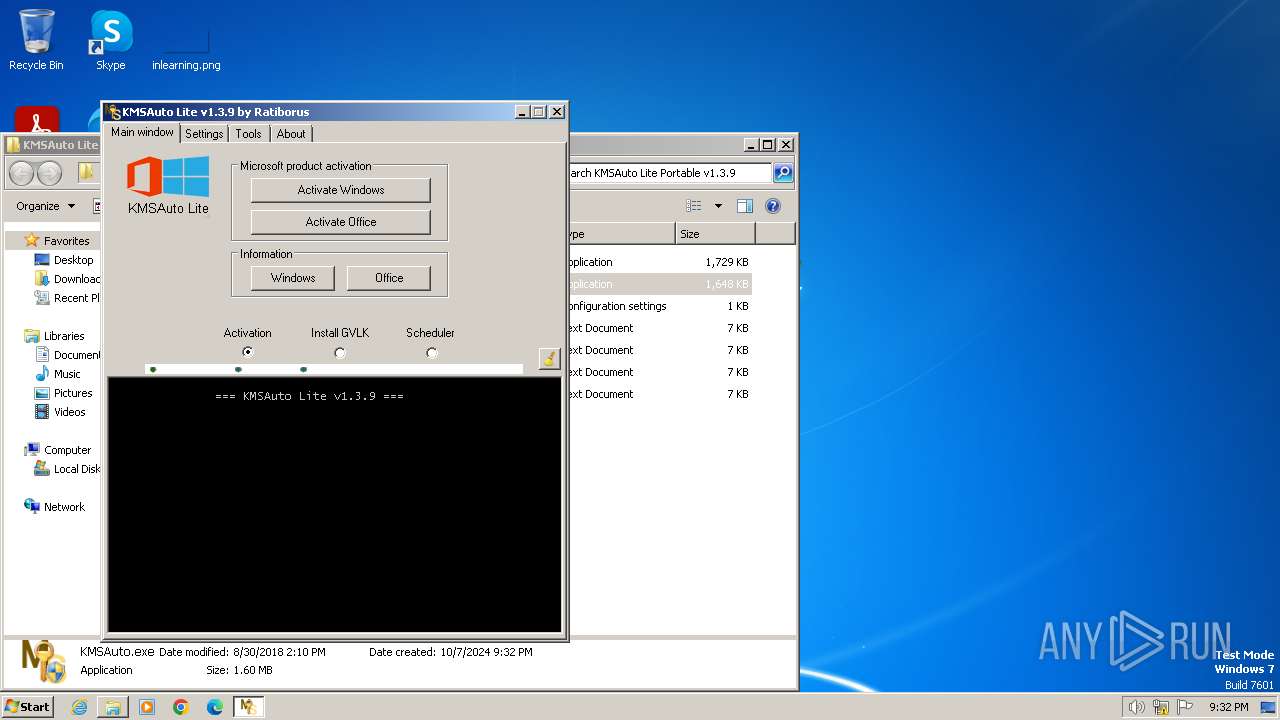
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4060)
SUSPICIOUS
Starts CMD.EXE for commands execution
- KMSAuto.exe (PID: 3228)
Drops 7-zip archiver for unpacking
- KMSAuto.exe (PID: 3228)
Executable content was dropped or overwritten
- KMSAuto.exe (PID: 3228)
- bin.dat (PID: 1356)
Starts application with an unusual extension
- cmd.exe (PID: 1364)
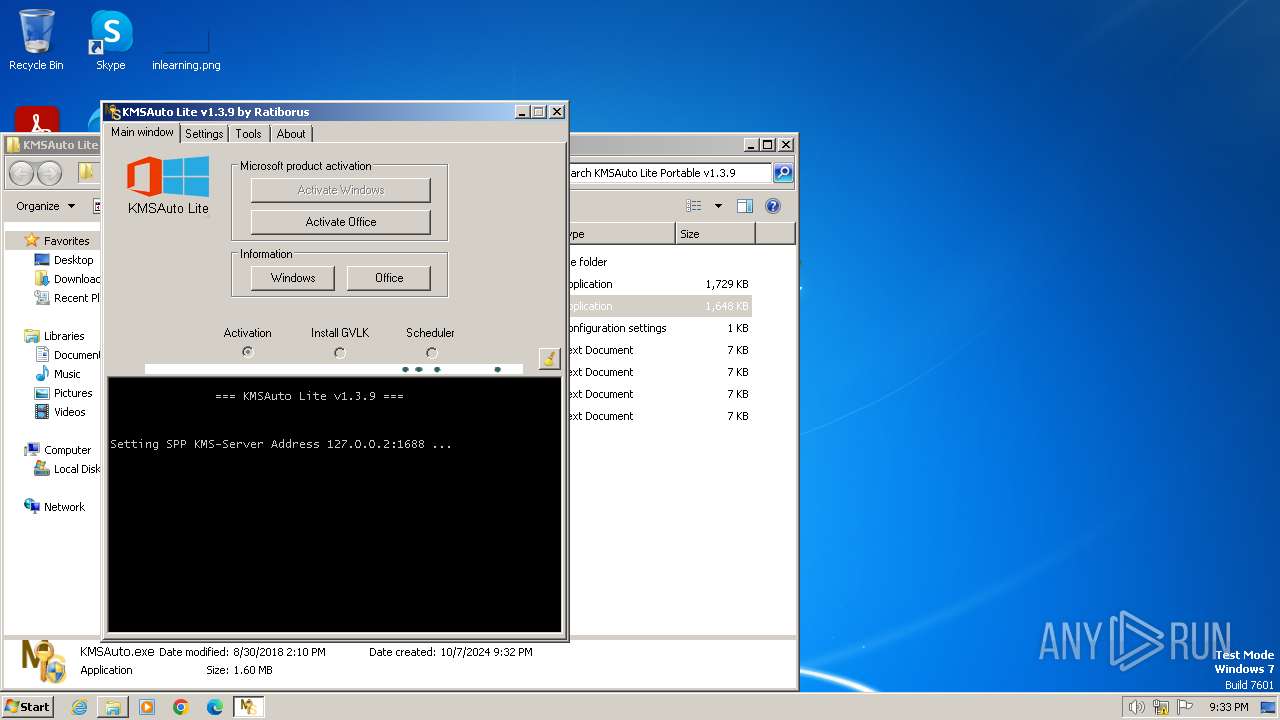
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 268)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 2900)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 656)
- cmd.exe (PID: 3176)
Creates or modifies Windows services
- KMSAuto.exe (PID: 3228)
Executes as Windows Service
- KMSSS.exe (PID: 3216)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto.exe (PID: 3228)
- cmd.exe (PID: 2024)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 4080)
Starts SC.EXE for service management
- cmd.exe (PID: 2532)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3736)
The process executes VB scripts
- cmd.exe (PID: 4072)
- cmd.exe (PID: 1992)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 3032)
- cscript.exe (PID: 1744)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 1744)
- cscript.exe (PID: 3032)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 1744)
- cscript.exe (PID: 3032)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 1744)
- cscript.exe (PID: 3032)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 4072)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 3032)
- cscript.exe (PID: 1744)
INFO
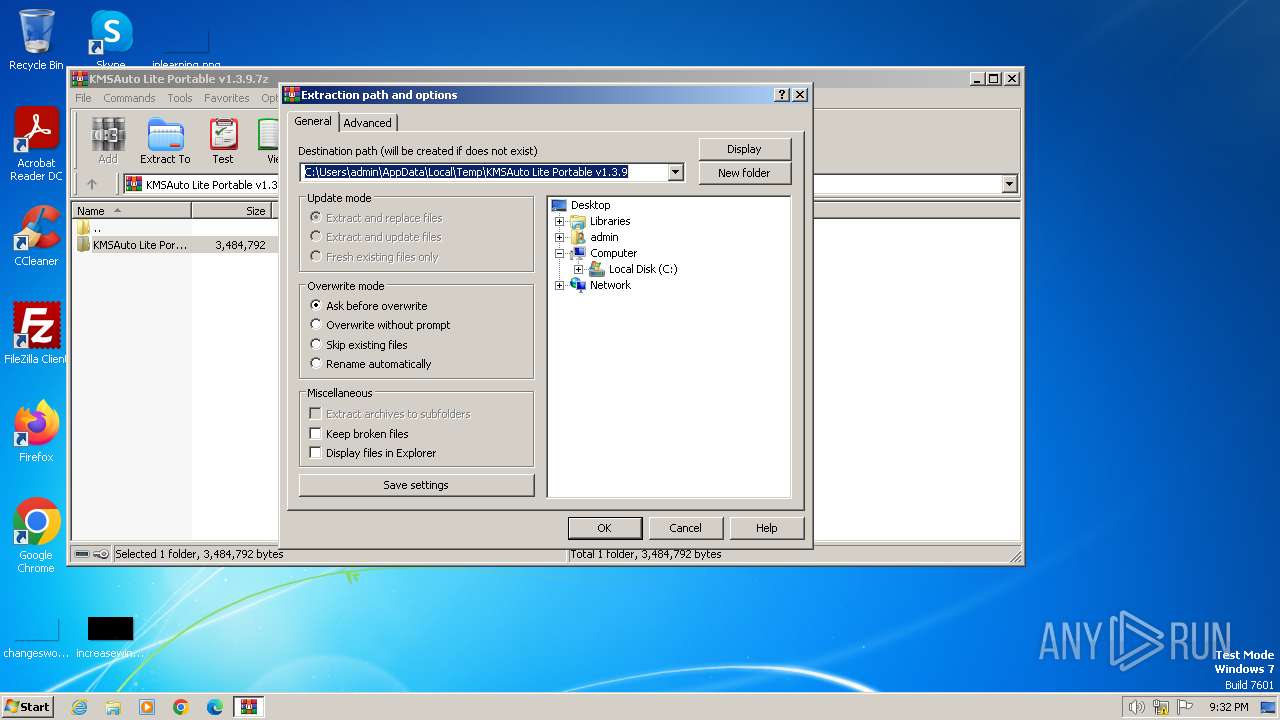
The process uses the downloaded file
- WinRAR.exe (PID: 4060)
Checks supported languages
- KMSAuto.exe (PID: 3228)
- bin.dat (PID: 1356)
- KMSSS.exe (PID: 3216)
- wmpnscfg.exe (PID: 840)
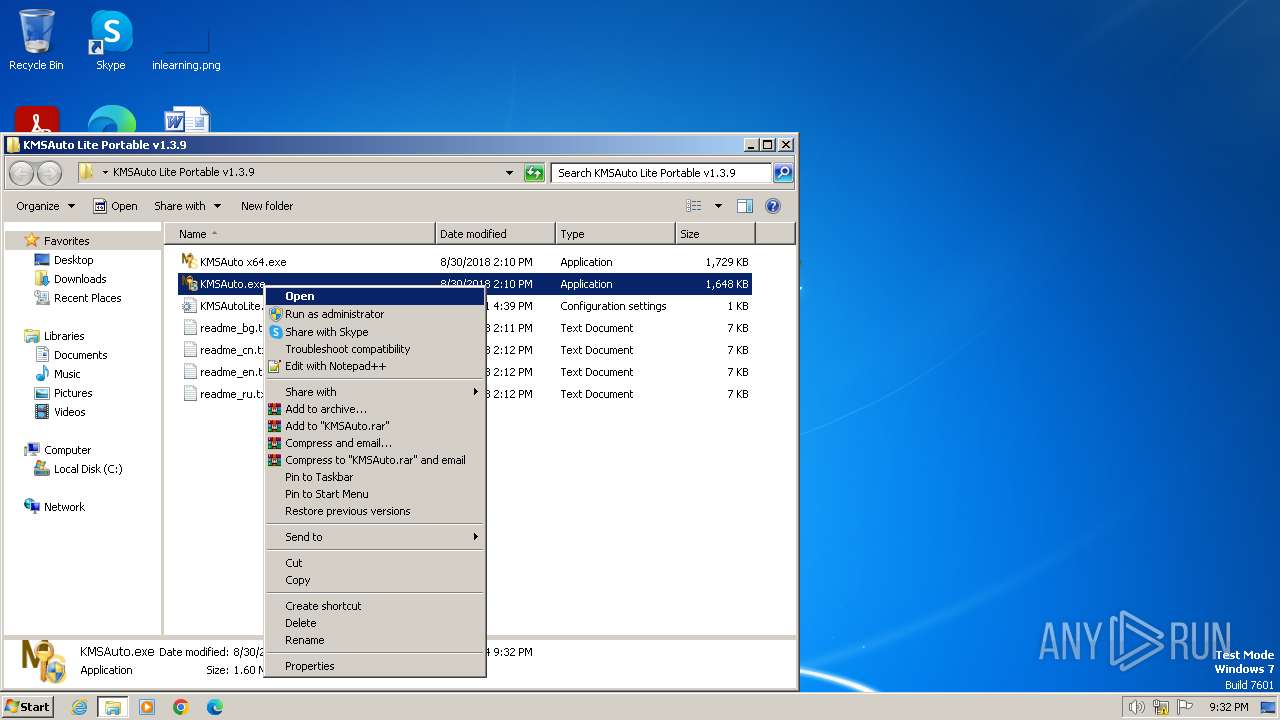
Manual execution by a user
- KMSAuto.exe (PID: 3228)
- KMSAuto.exe (PID: 2720)
- wmpnscfg.exe (PID: 840)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4060)
Reads Environment values
- KMSAuto.exe (PID: 3228)
Reads product name
- KMSAuto.exe (PID: 3228)
Reads the computer name
- KMSAuto.exe (PID: 3228)
- KMSSS.exe (PID: 3216)
- wmpnscfg.exe (PID: 840)
Reads the machine GUID from the registry
- KMSAuto.exe (PID: 3228)
- KMSSS.exe (PID: 3216)
UPX packer has been detected
- KMSAuto.exe (PID: 3228)
Create files in a temporary directory
- KMSAuto.exe (PID: 3228)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1744)
- cscript.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (gen) (100) |
|---|
Total processes
102
Monitored processes
42
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | sc.exe stop KMSEmulator | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 268 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 348 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 840 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | bin.dat -y -pkmsauto | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\KMSAuto_Files\bin.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 18.05 Modules
| |||||||||||||||
| 1364 | "C:\Windows\System32\cmd.exe" /c bin.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1432 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServiceName /d 127.0.0.2 /t REG_SZ /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | "C:\Windows\System32\reg.exe" DELETE "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f | C:\Windows\System32\reg.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 626
Read events
5 308
Write events
305
Delete events
13
Modification events
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSAuto Lite Portable v1.3.9.7z | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
4
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
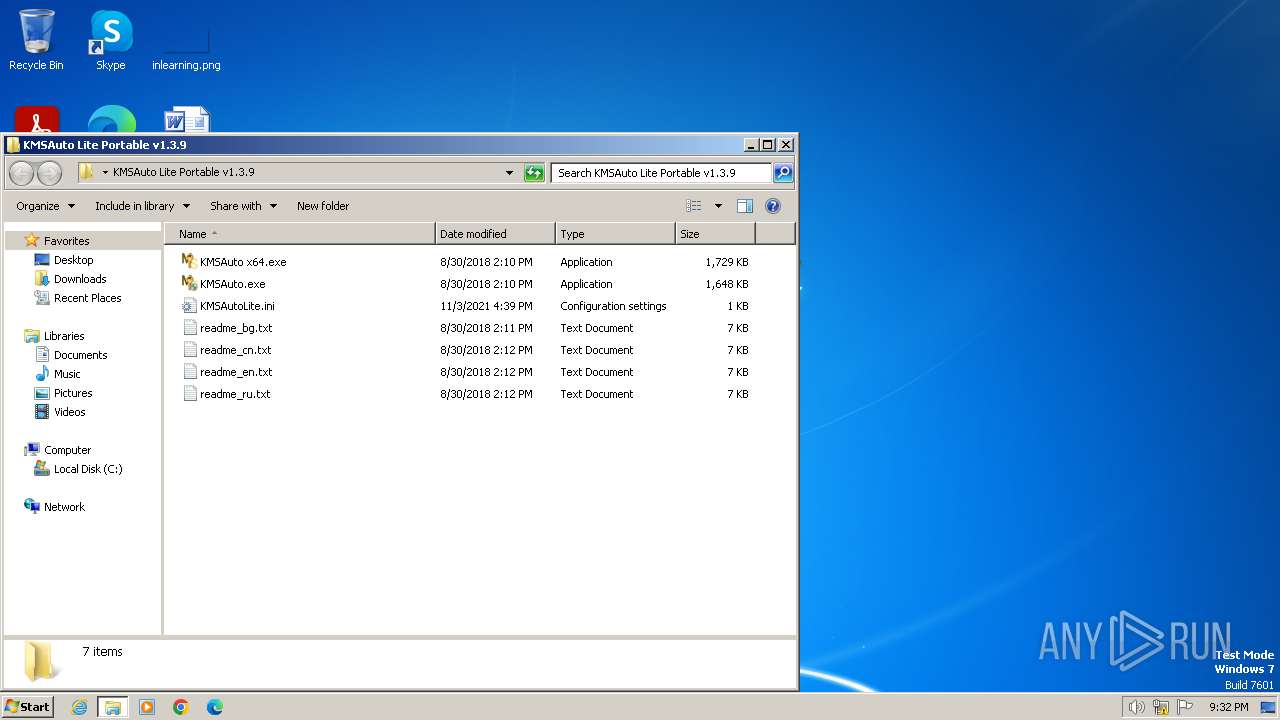
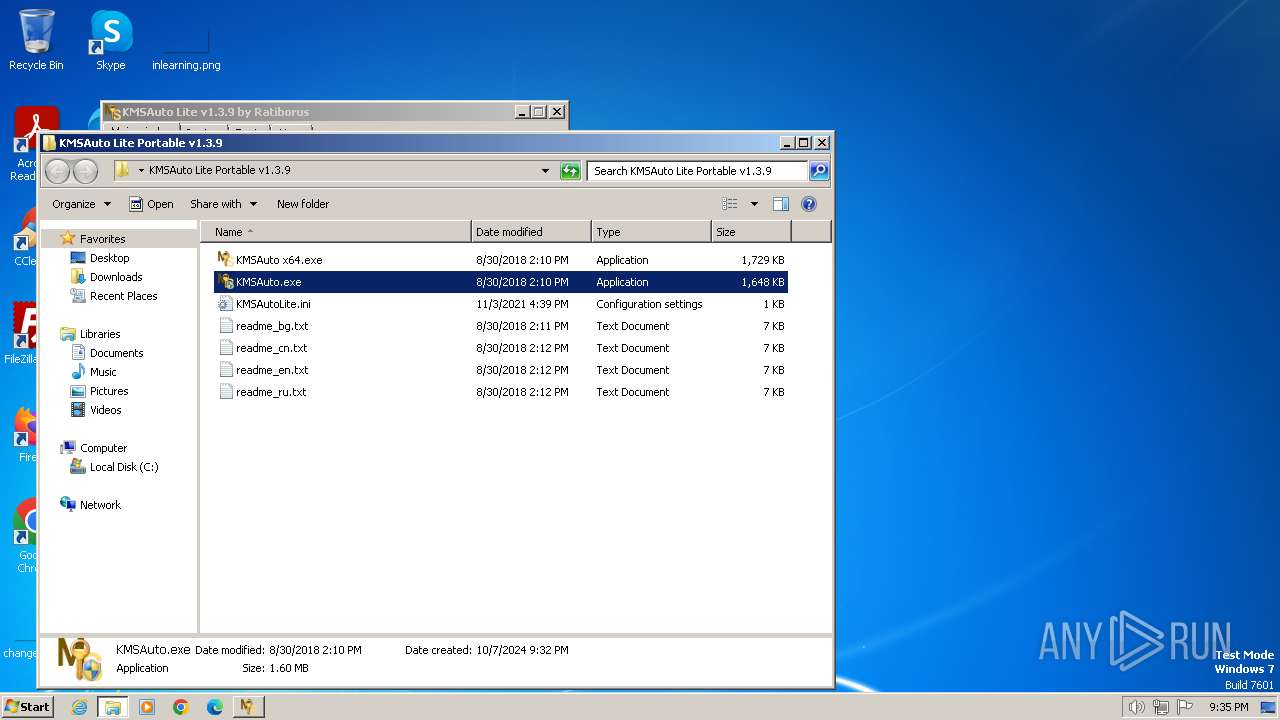
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | KMSAuto.exe | C:\Users\admin\AppData\Local\Temp\slmgr.vbs | text | |
MD5:38482A5013D8AB40DF0FB15EAE022C57 | SHA256:AC5C46B97345465A96E9AE1EDAFF44B191A39BF3D03DC1128090B8FFA92A16F8 | |||
| 3216 | KMSSS.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\KMSAuto_Files\bin\KMSSS.log | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 3228 | KMSAuto.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\KMSAuto_Files\bin.dat | executable | |
MD5:084A2A1BF7B305A95E753758BE93CFF3 | SHA256:4988DF92E1BDE8385B31814CED43AF73A21A4FEB06D0D6637B1EB8BC2BF20A18 | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\readme_bg.txt | text | |
MD5:632F944826FBECEA4F366B1BA45FF635 | SHA256:9D58363B858B6C2462AE726D7CDFF573724B27043FFC85C9EE9FD309E694304B | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\KMSAutoLite.ini | text | |
MD5:298B7F6C3C02BFEA91D53986D8945E02 | SHA256:EEE928219D399B02E823028AD65BD6E66C88533199C13F509CE70DD13C1C4E2F | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\readme_cn.txt | text | |
MD5:C45E890427B9E9300CEEC72B71B780EF | SHA256:CB16E57211D64D53585A512711565F6DF6C877BCD01E43F3A2C6CEBF576BE0F6 | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\readme_en.txt | text | |
MD5:135F0009D16806F5C1CD776C8EF64CD0 | SHA256:11AD75DD0B76FE2AF1EE25109121781FB1295267085F676FCEF4F5AF49CDA94B | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\readme_ru.txt | text | |
MD5:A1588CC7CD8FC0BB40EF74955CE8F20B | SHA256:52D17FB29A97B1E603D335940B19D2DD557F58A72AE69965F72F1521CFFA0DFF | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\KMSAuto x64.exe | executable | |
MD5:AAACBBC58A78FFCC674AFEEC04069D3D | SHA256:92F154A1E3FDBC25EB3FE28DB00BACB50021118FA3C324CF96A4E1DF19820974 | |||
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\KMSAuto Lite Portable v1.3.9\KMSAuto.exe | executable | |
MD5:6834838DFCEE3860B51D75F3770FF7E5 | SHA256:4FDD378C271A33AA5DDD7224A7EC5C533367814D53D25E860C168F98C4E11317 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
964 | WmiPrvSE.exe | POST | 302 | 23.218.210.69:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | unknown | — | — | whitelisted |
964 | WmiPrvSE.exe | POST | 302 | 23.218.210.69:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | unknown | — | — | whitelisted |
964 | WmiPrvSE.exe | POST | 302 | 23.218.210.69:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
964 | WmiPrvSE.exe | 23.218.210.69:80 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
964 | WmiPrvSE.exe | 52.161.91.37:443 | activation.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |