| File name: | GHOST FUD CRYPTER.exe |
| Full analysis: | https://app.any.run/tasks/14be5ce6-a039-4b44-bd42-08be63ace680 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 11:59:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 15 sections |
| MD5: | 513424ED6D555BF357EE44846F510FAF |
| SHA1: | 3C2EE69C49A7D28A7720937D273836293C75DC36 |
| SHA256: | 339A880408B453DF07D35DBA3979144B2CEE3A778BC3906E52D1B72ACAF5B045 |
| SSDEEP: | 49152:BJMr7Nwia8d0JBJm6b7xeJnQ7SN0xD/j285goJ0a/f4h8Rsm/fTyBQif5q5W3iF1:Kq60JBDFeD0xDRBS4D9F0YO/te6xM |
MALICIOUS
Modifies files in the Chrome extension folder
- diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 1764)
SUSPICIOUS
Suspicious files were dropped or overwritten
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Executing commands from a ".bat" file
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1760)
- cmd.exe (PID: 864)
Starts CMD.EXE for commands execution
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Executable content was dropped or overwritten
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Starts application with an unusual extension
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Reads browser cookies
- diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 1764)
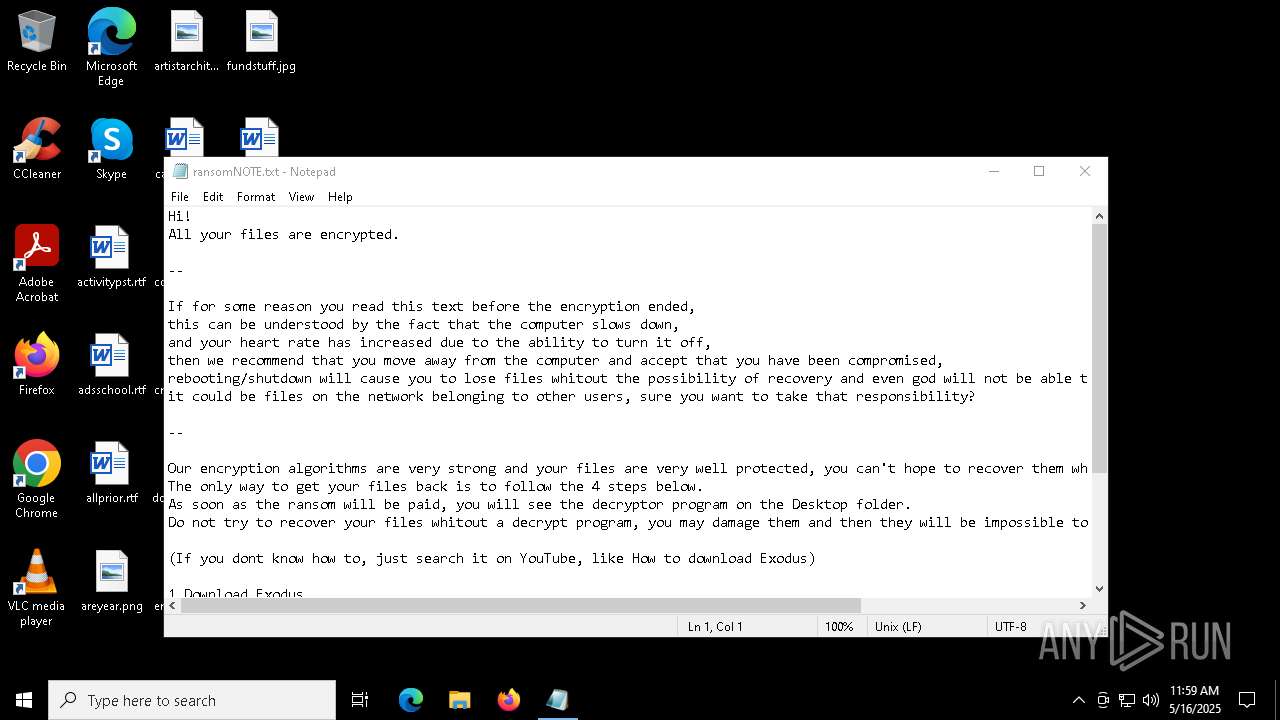
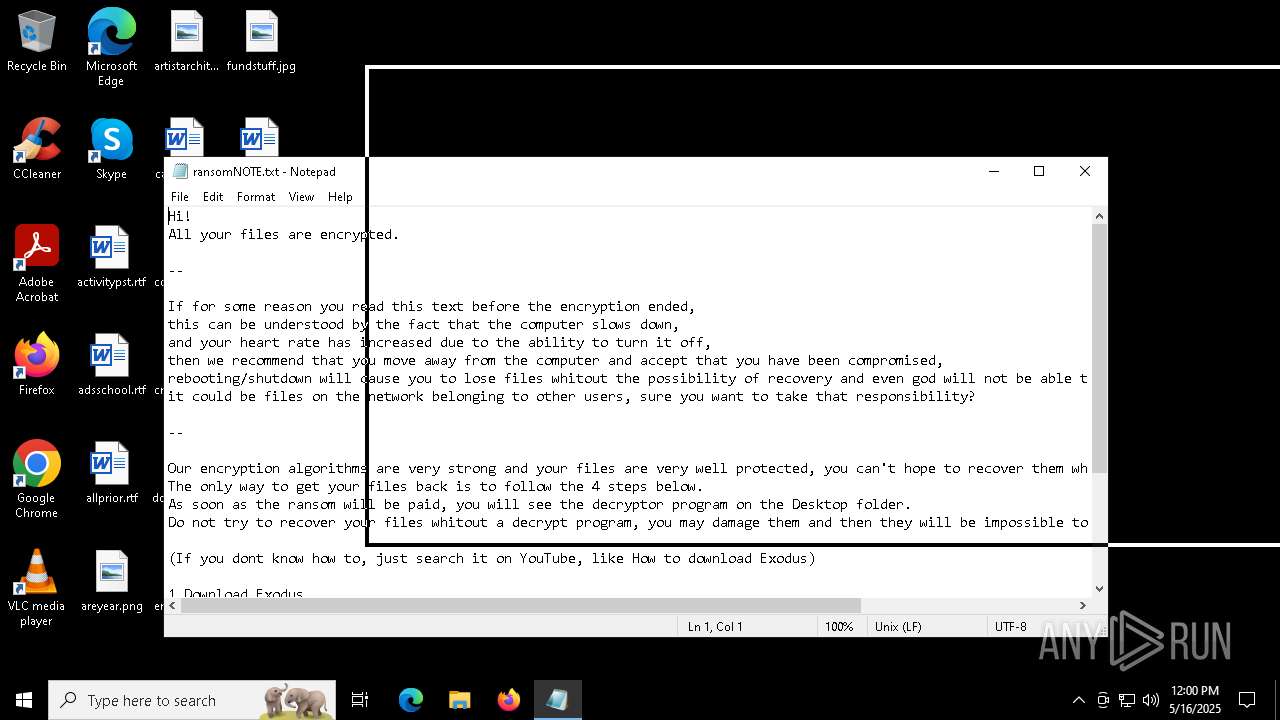
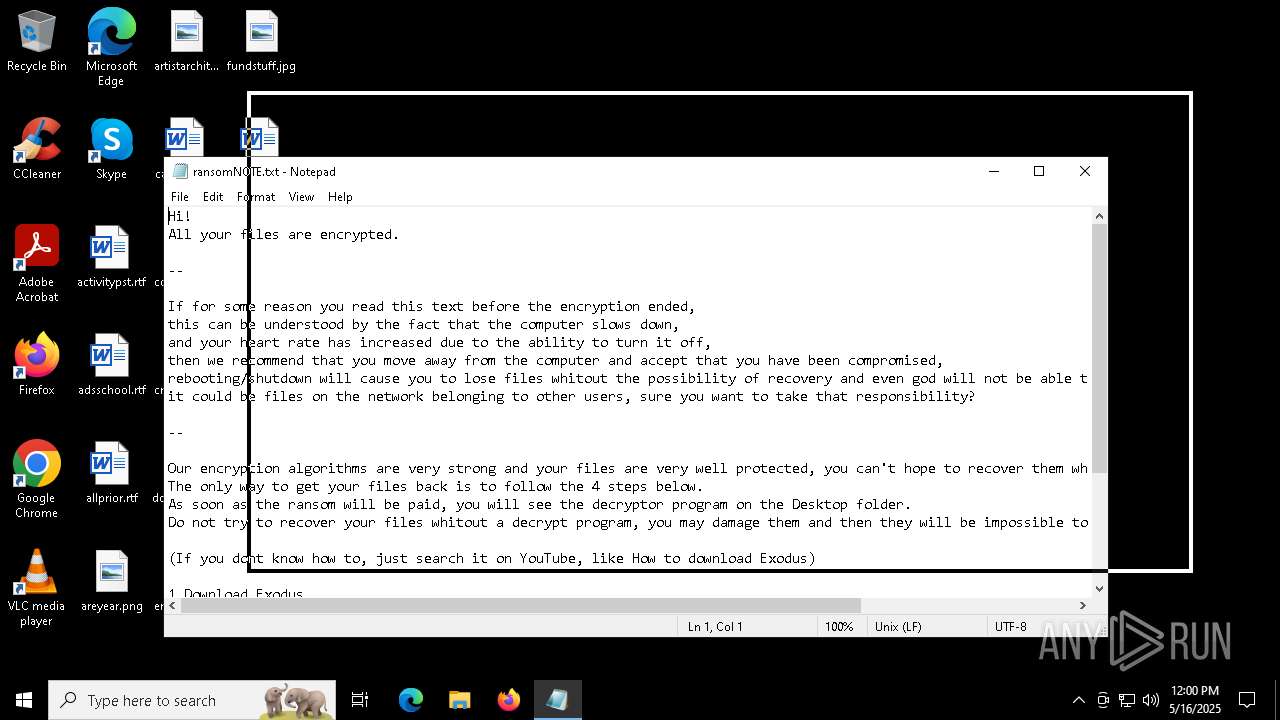
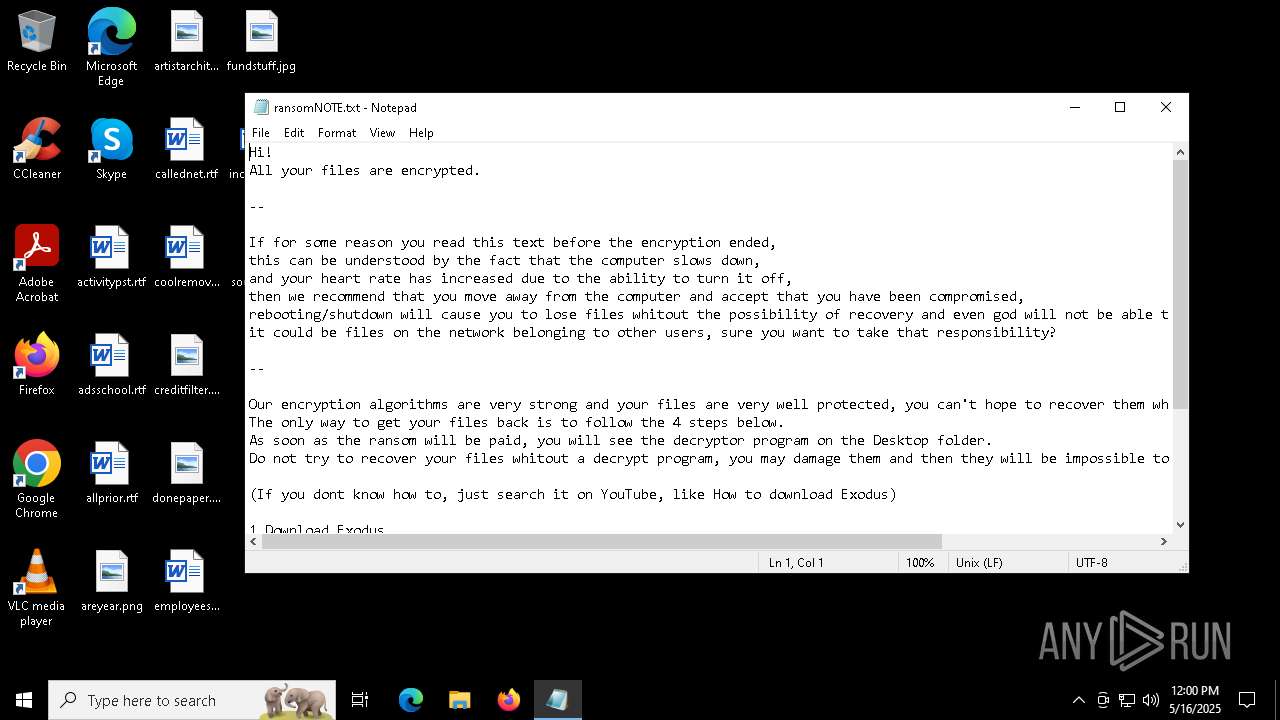
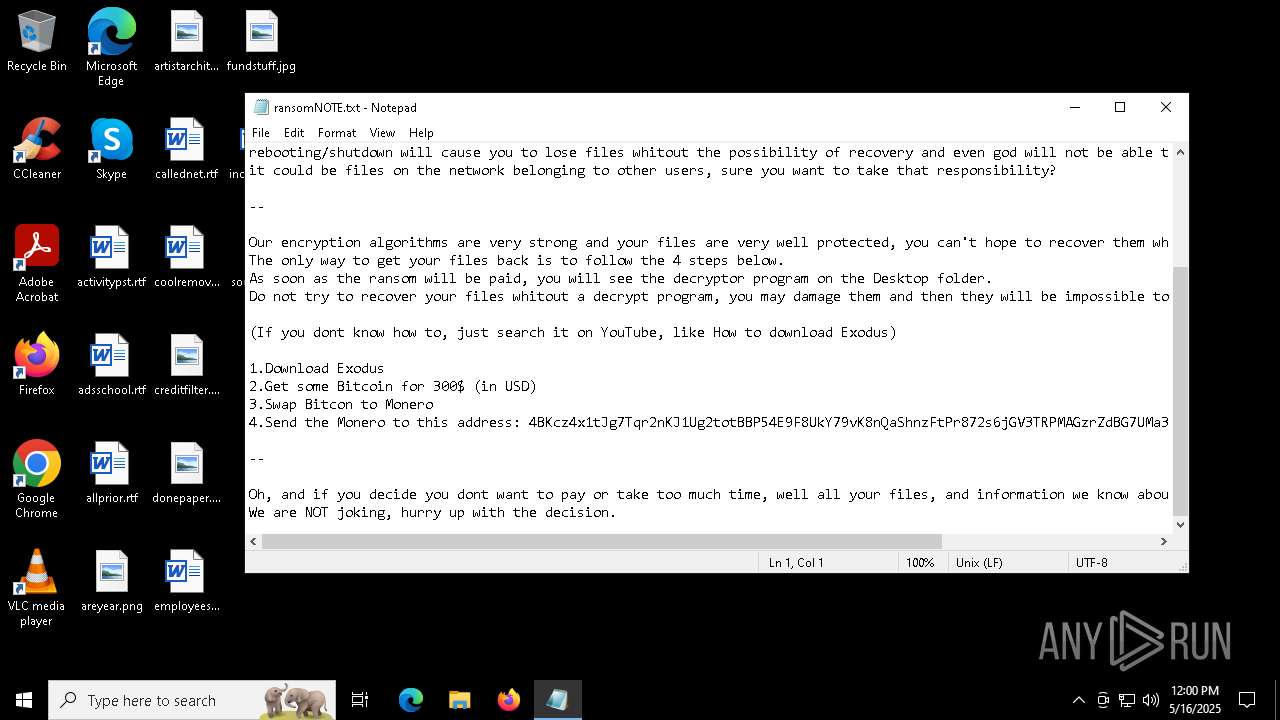
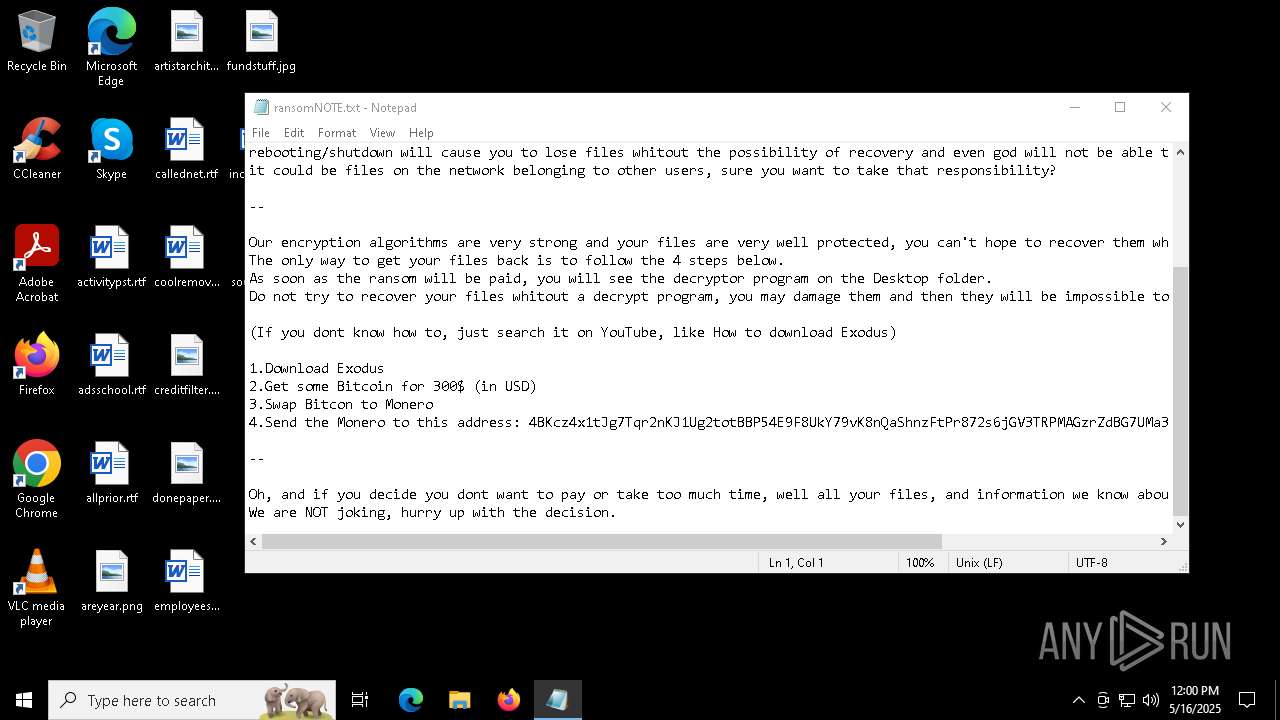
Start notepad (likely ransomware note)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Write to the desktop.ini file (may be used to cloak folders)
- diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 1764)
INFO
Drops encrypted JS script (Microsoft Script Encoder)
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Checks supported languages
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
- diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 1764)
- SearchApp.exe (PID: 7512)
Reads the computer name
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
- SearchApp.exe (PID: 7512)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Potential library load (Base64 Encoded 'LoadLibrary')
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Potential modification of remote process state (Base64 Encoded 'SetThreadContext')
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- GHOST FUD CRYPTER.exe (PID: 2384)
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
Application based on Golang
- adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 4200)
- GHOST FUD CRYPTER.exe (PID: 2384)
Create files in a temporary directory
- diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat (PID: 1764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 740352 |
| InitializedDataSize: | 59904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x652c0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
Total processes
139
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | cmd /C "attrib +h C:\Users\admin\Downloads\diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat" | C:\Windows\System32\cmd.exe | — | adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | attrib +h C:\Users\admin\Downloads\adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | attrib +h C:\Users\admin\Downloads\diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | cmd /C "attrib +h C:\Users\admin\Downloads\adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat" | C:\Windows\System32\cmd.exe | — | GHOST FUD CRYPTER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | C:\Users\admin\Downloads\diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\Downloads\diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | — | adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\GHOST FUD CRYPTER.exe" | C:\Users\admin\AppData\Local\Temp\GHOST FUD CRYPTER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4200 | C:\Users\admin\Downloads\adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\Downloads\adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | GHOST FUD CRYPTER.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4892 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 248
Read events
10 581
Write events
663
Delete events
4
Modification events
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\ContactPermissions\Get |
| Operation: | write | Name: | Id |
Value: 02000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\RulesV2Device\HttpRequestCmd |
| Operation: | write | Name: | HeaderTemplate |
Value: 58002D005300650061007200630068002D00490047003A002000250032000D000A0058002D005300650061007200630068002D00550049004C0061006E0067003A002000250033000D000A0058002D005300650061007200630068002D004D00610072006B00650074003A002000250034000D000A0058002D005300650061007200630068002D0043006C00690065006E007400490044003A002000250035000D000A0058002D004100670065006E0074002D00520075006C0065007300560065007200730069006F006E003A002000250036000D000A0058002D004100670065006E0074002D005200650073006F006C007500740069006F006E003A002000250037000D000A0058002D004100670065006E0074002D00440065007600690063006500490064003A002000250038000D000A0058002D0042004D002D004F0045004D003A002000250039000D000A0058002D0042004D002D004D004F003A0020002500310030000D000A0058002D004100670065006E0074002D00500068006F006E0065004F0053005600650072003A0020002500310031000D000A00540069006D0065007A006F006E0065003A0020002500310032000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\ContactPermissions\Get |
| Operation: | write | Name: | HeaderTemplate |
Value: 43006F006E00740065006E0074002D0054007900700065003A0020006100700070006C00690063006100740069006F006E002F006A0073006F006E000D000A0058002D004100670065006E0074002D00440065007600690063006500490064003A002000250031000D000A0058002D005300650061007200630068002D00490047003A002000250032000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\RulesV2Device\HttpRequestCmd |
| Operation: | write | Name: | ParamCount |
Value: 0C000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\ContactPermissions\Get |
| Operation: | write | Name: | UrlTemplate |
Value: 2F007000650072006D0069007300730069006F006E0073002F0063006F006E00740061006300740073000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\RulesV2Device\HttpRequestCmd |
| Operation: | write | Name: | UrlTemplate |
Value: 250031000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\ContactPermissions\Get |
| Operation: | write | Name: | ParamCount |
Value: 02000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\ContactPermissions\Get |
| Operation: | write | Name: | HttpMethod |
Value: 00000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\RulesV2Device\HttpRequestCmd |
| Operation: | write | Name: | HttpMethod |
Value: 00000000DA122CFF59C6DB01 | |||
| (PID) Process: | (7512) SearchApp.exe | Key: | \REGISTRY\A\{7ba2865e-f584-c91e-2d69-61532732e1eb}\LocalState\OnlineServices\Providers\ContactPermissions\Get |
| Operation: | write | Name: | PayloadEscapeBitField |
Value: 00000000DA122CFF59C6DB01 | |||
Executable files
18
Suspicious files
2 611
Text files
184
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_FirstMile_Right_Sec_Surface | binary | |
MD5:AB23DEDEF5808FDF59CB81850EDECBF8 | SHA256:EFB52950984E80455DE6B87FD00F2D63E2CE935D39F1FFC8945859B5295886D8 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_Reader_Convert_LHP_Banner | binary | |
MD5:A75F79022F2C438EDE41AAB2E99AA5BA | SHA256:C3F31AF346ED3131320E3D061D69DE54866384527E23CBBD730565E2DE2C7E96 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_Reader_Disc_LHP_Banner | binary | |
MD5:C85747727BB59A90226D5A99FFECFCFF | SHA256:52F576EE229984CDA67B9E6AC6E12C3080B84ECC45CE5A8EA18230CA6A59C5F4 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Comms\Unistore\data\AggregateCache.uca | text | |
MD5:498C997429E80B2A06DBDC73A18F6713 | SHA256:D6FA0E7CD13179D66C167B383FE2613CCE593AE918A0F9D8073075B654EBA910 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_Reader_Edit_LHP_Banner | binary | |
MD5:0477DF11F356A183236E2D5073B466BE | SHA256:8C96E46E359EF4071933EAB425A8047BB28DB21667DDB27F1DA35CE4E164A86E | |||
| 2384 | GHOST FUD CRYPTER.exe | C:\Users\admin\Downloads\adiwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | executable | |
MD5:5A188FE50EF67683FB6DAAFC262A4160 | SHA256:14A3FB3A4B574DE080A528E2B73D286976A6C4CE2400B1F60AE64275F71AD7F5 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_Reader_Disc_LHP_Retention | binary | |
MD5:CCA26EBB1684B860952FAA44E6243970 | SHA256:ACDECEFFD55178584CC4EA2CA76EA9CF80C0125900D77B1B02C25342D2D58120 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_Reader_RHP_Intent_Banner | binary | |
MD5:A95EAA74C32FC380F5A2C44C3B30E64A | SHA256:F93BD22F4257B46E2B1D95C53E47D07EDDB7F50F47BA4997B6BBF260942ADEB9 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\DC_Reader_More_LHP_Banner | binary | |
MD5:39ABFAA12053BDC35DAD0A71CAB98615 | SHA256:3326A020D5C8F6FE4C5E8567AD7E55ED9259E1D3B2558DC274D678A06C606574 | |||
| 1764 | diwejdiowejdoiewdeowedopwedxcmkedtmpScript.bat | C:\Users\admin\AppData\Local\Adobe\Color\ACECache11.lst | binary | |
MD5:FFB2DDDCA033B6E52CF51089B45F54B7 | SHA256:FDC60FDFEB7EA6133D66BA29B190951FABBFC2753EC2980F6D7D8663430F77F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7512 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8116 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8116 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |