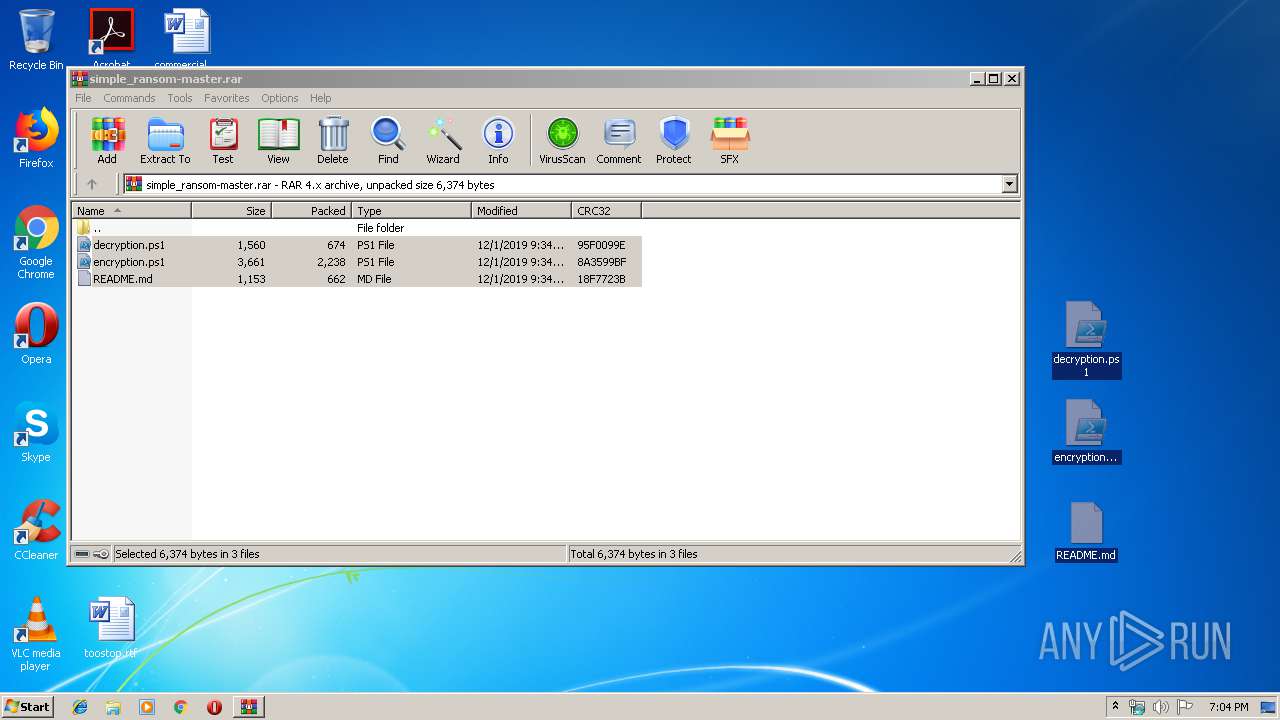
| File name: | simple_ransom-master.rar |
| Full analysis: | https://app.any.run/tasks/cd617f86-ea8b-470b-82a3-c04b969be36e |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 19:03:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
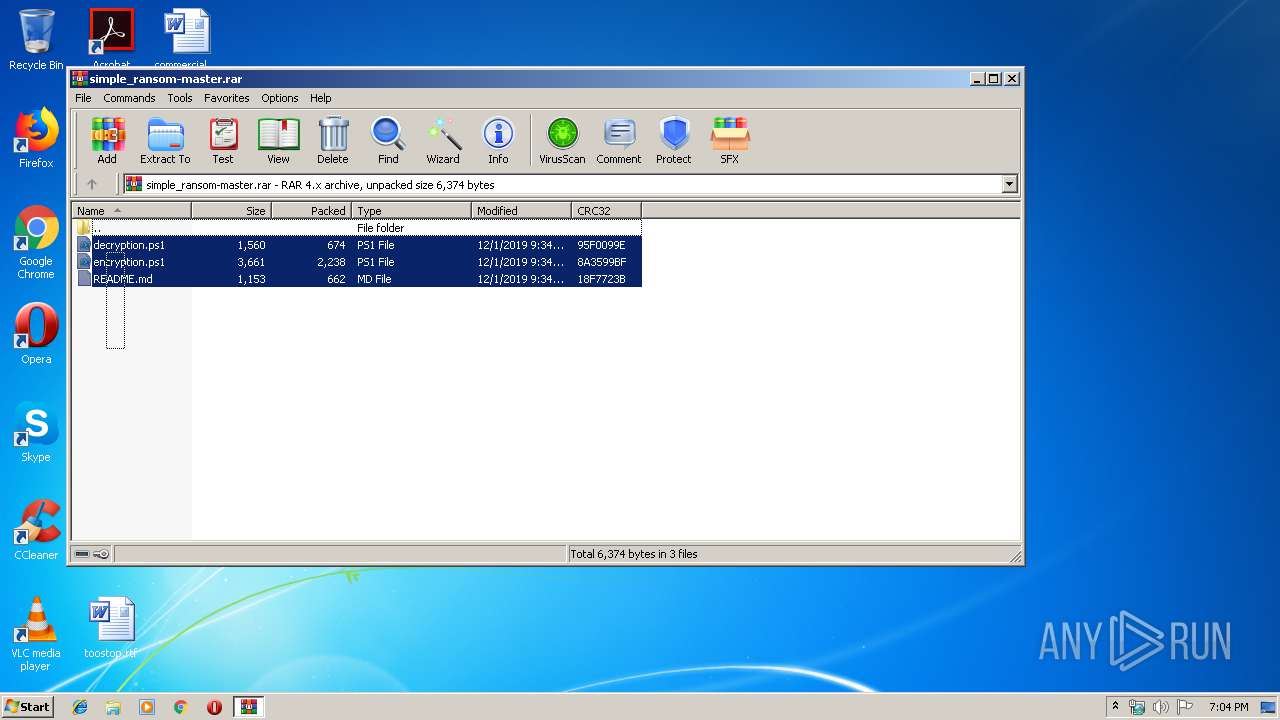
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | C4EA0A02783E30B0F76D70F3C68B9149 |
| SHA1: | 0644CDB46874EBBC77AA1EF1E04A71EBEFE31FE2 |
| SHA256: | 33892EC8D4E4A069B588DE585069FCAC60F26DCF6766D483811D97D3D8002DD9 |
| SSDEEP: | 48:0zQ/veL7cxjDm8l9z9m/2XVMeC0G/gEWOEhBVvQyfmF4oOggWcJJXpOZF:GevefcZx922XVMvAOSBVYmmFr9/Qg |
MALICIOUS
No malicious indicators.SUSPICIOUS
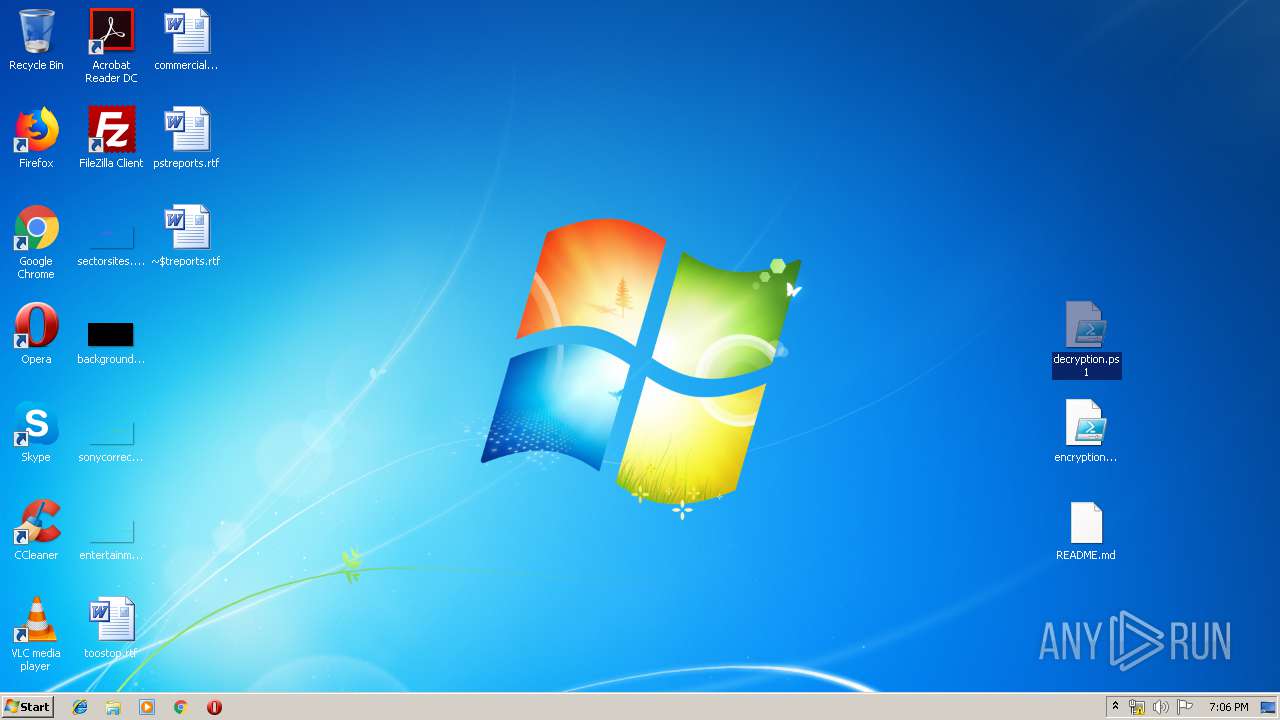
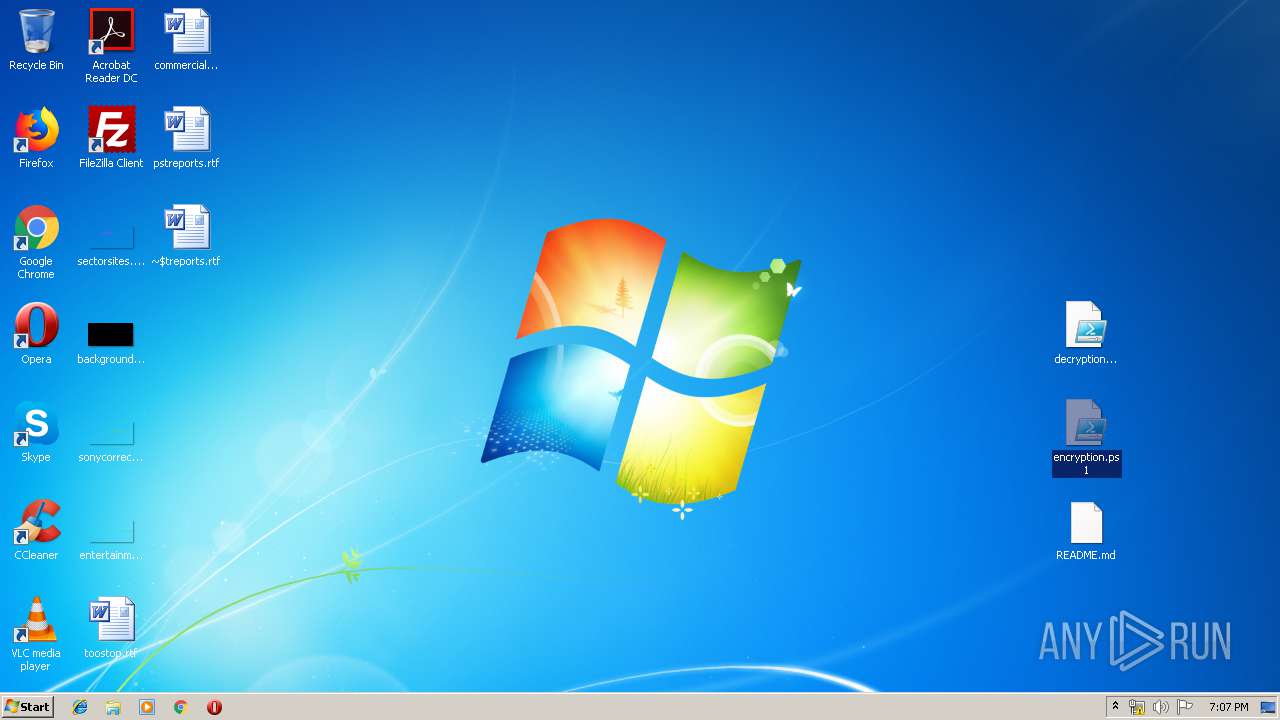
Creates files in the user directory
- powershell.exe (PID: 2604)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 1528)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 3528)
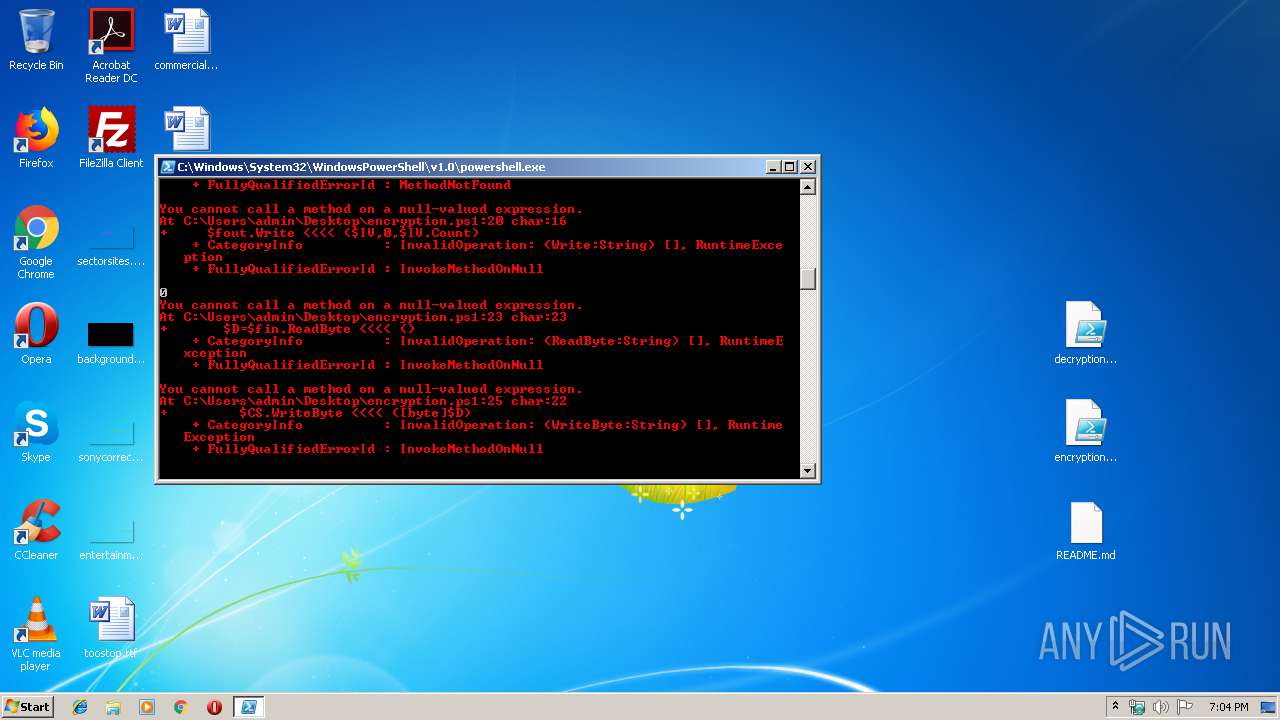
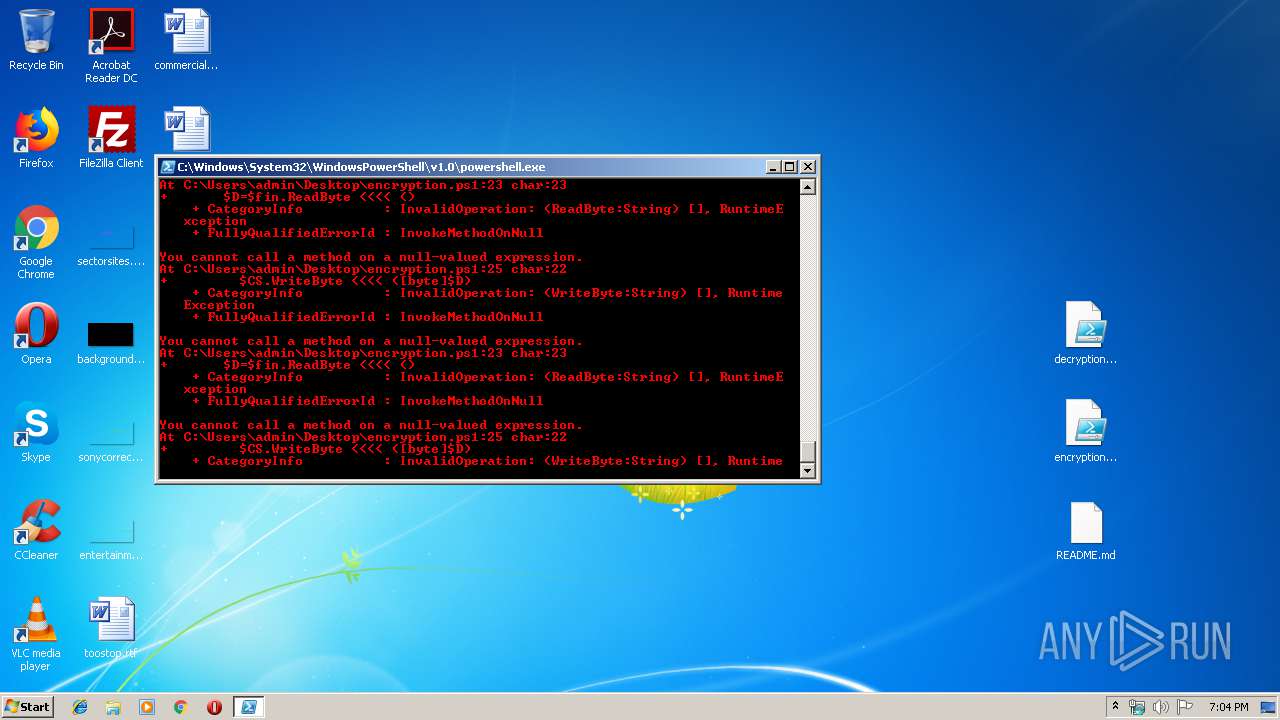
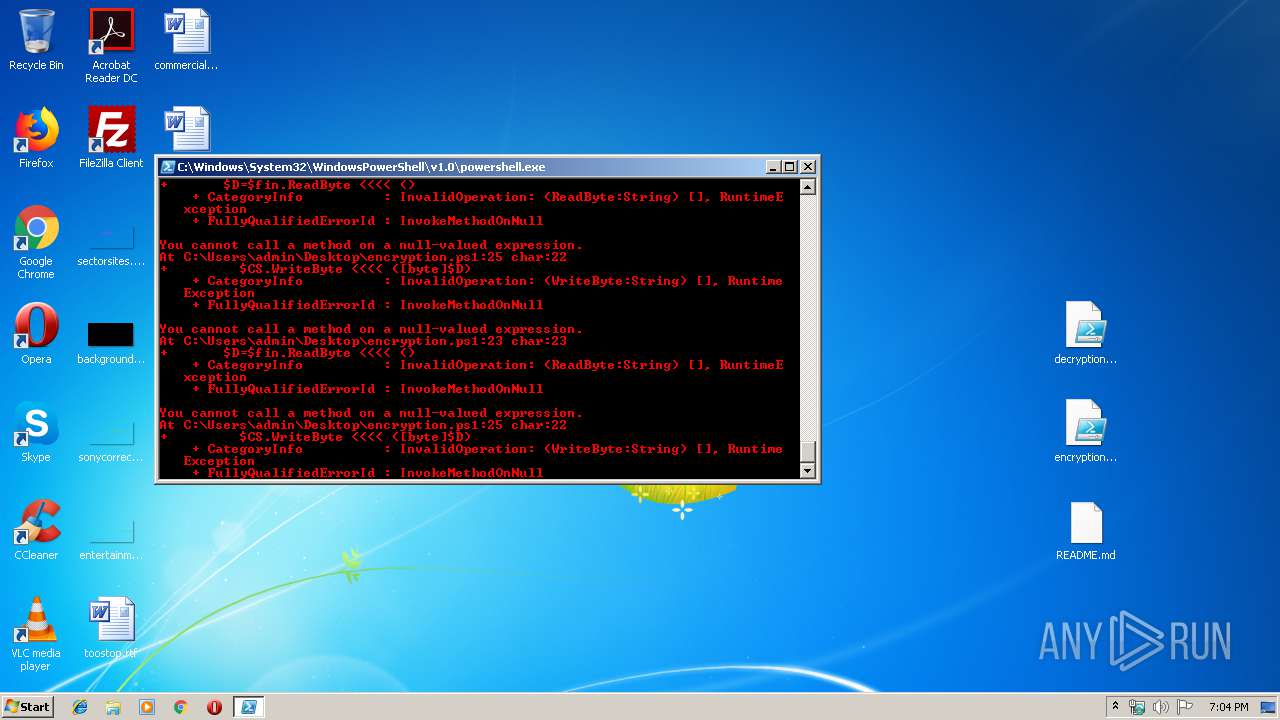
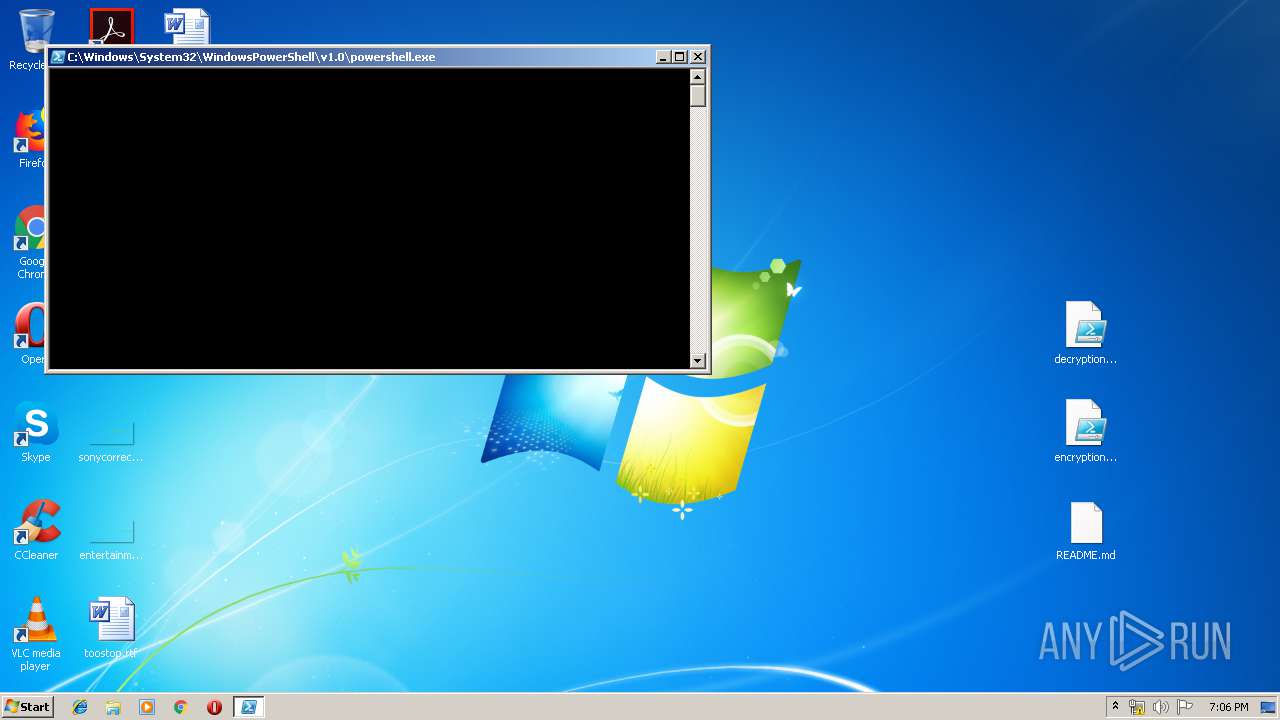
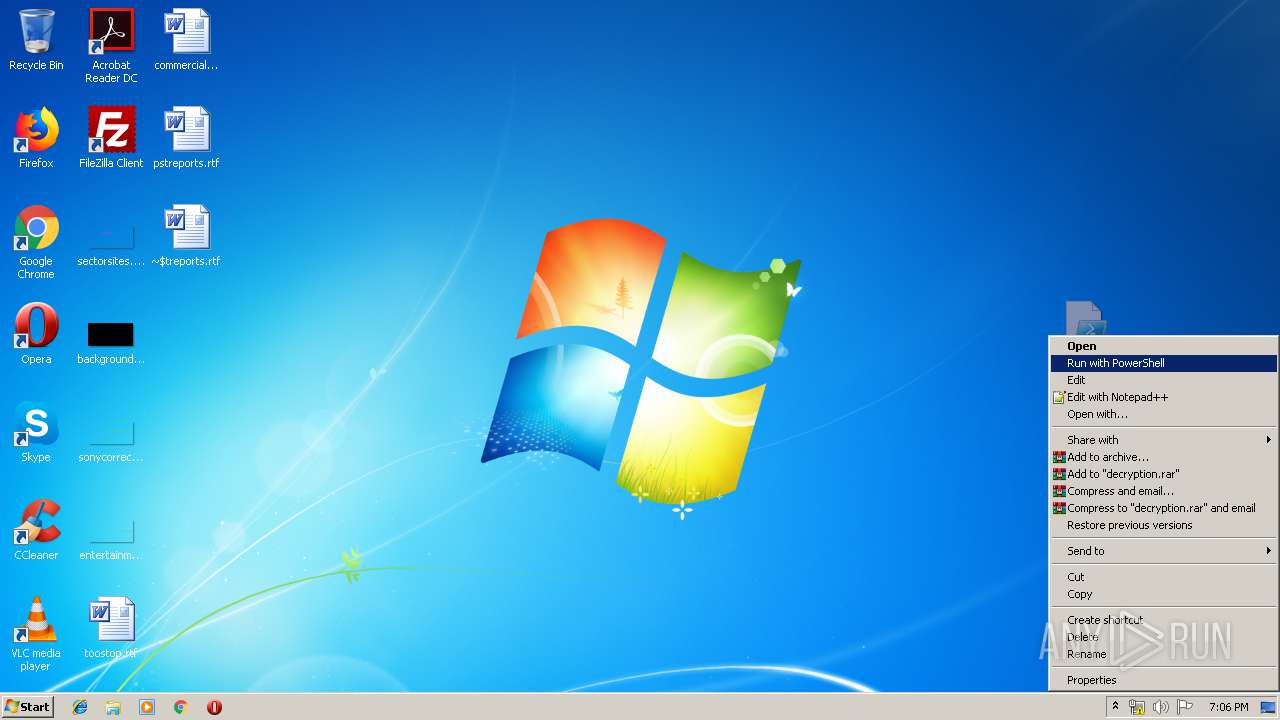
PowerShell script executed
- powershell.exe (PID: 2604)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 1528)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 3528)
INFO
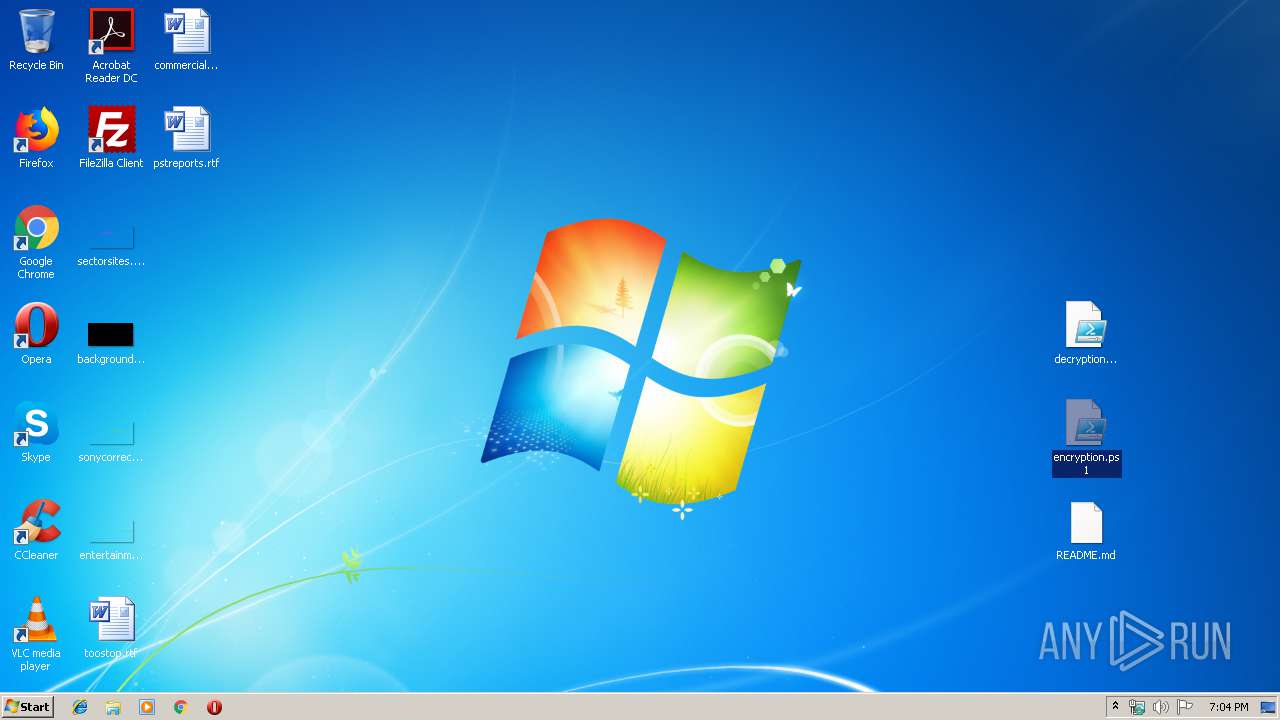
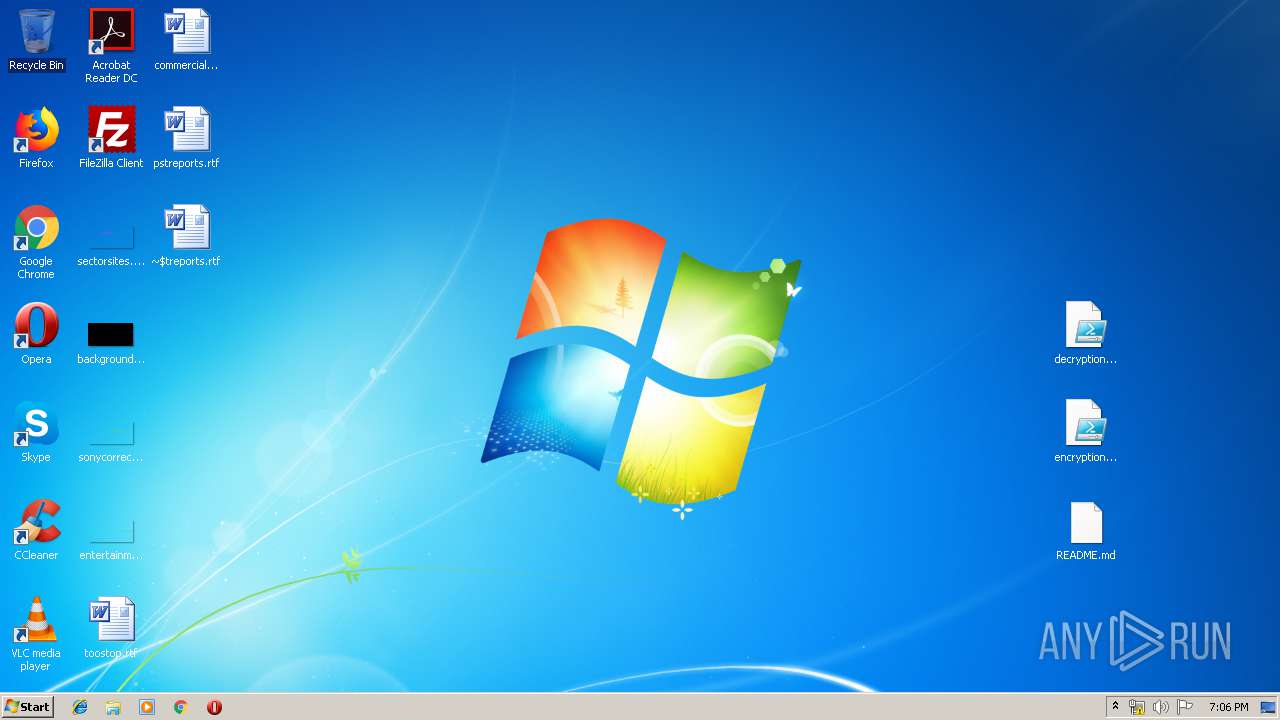
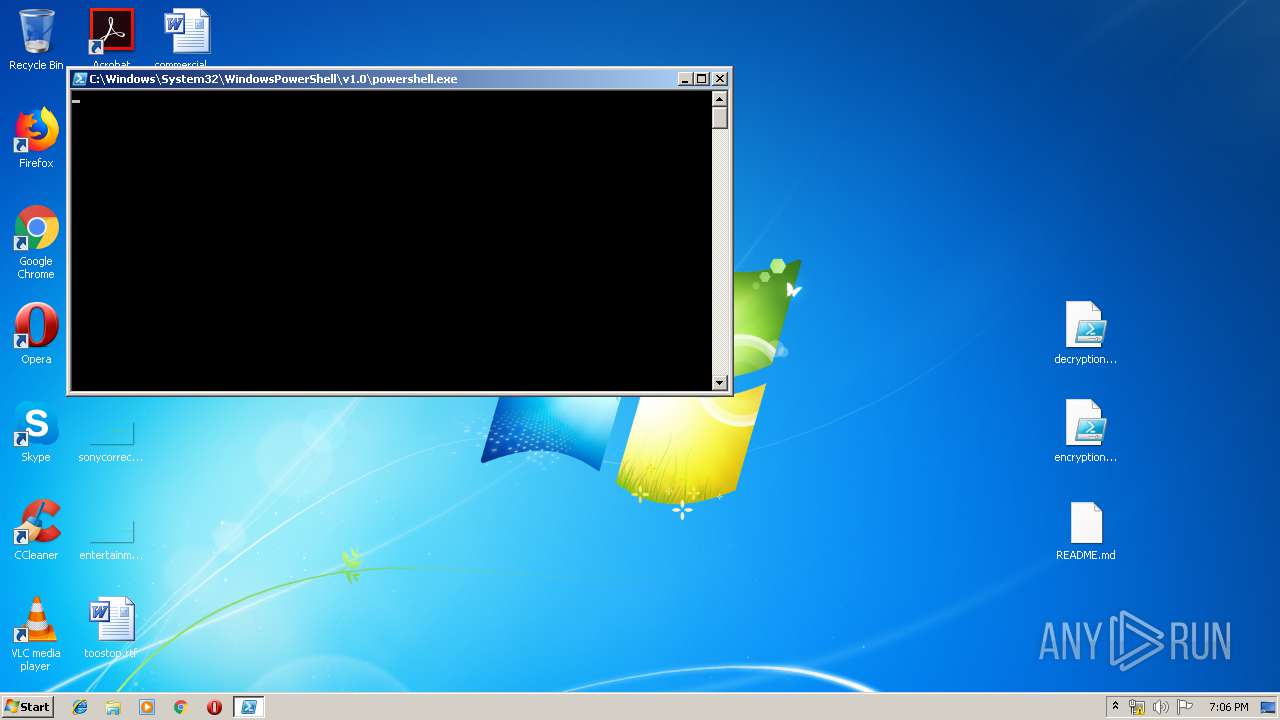
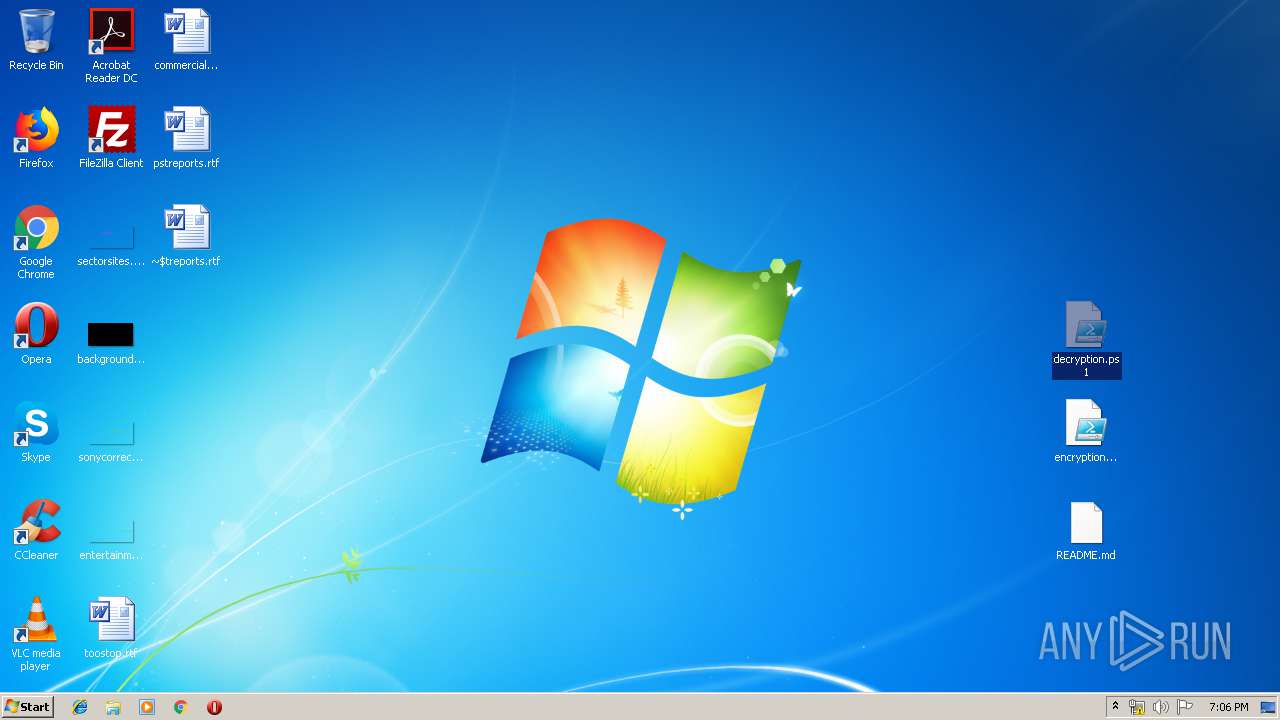
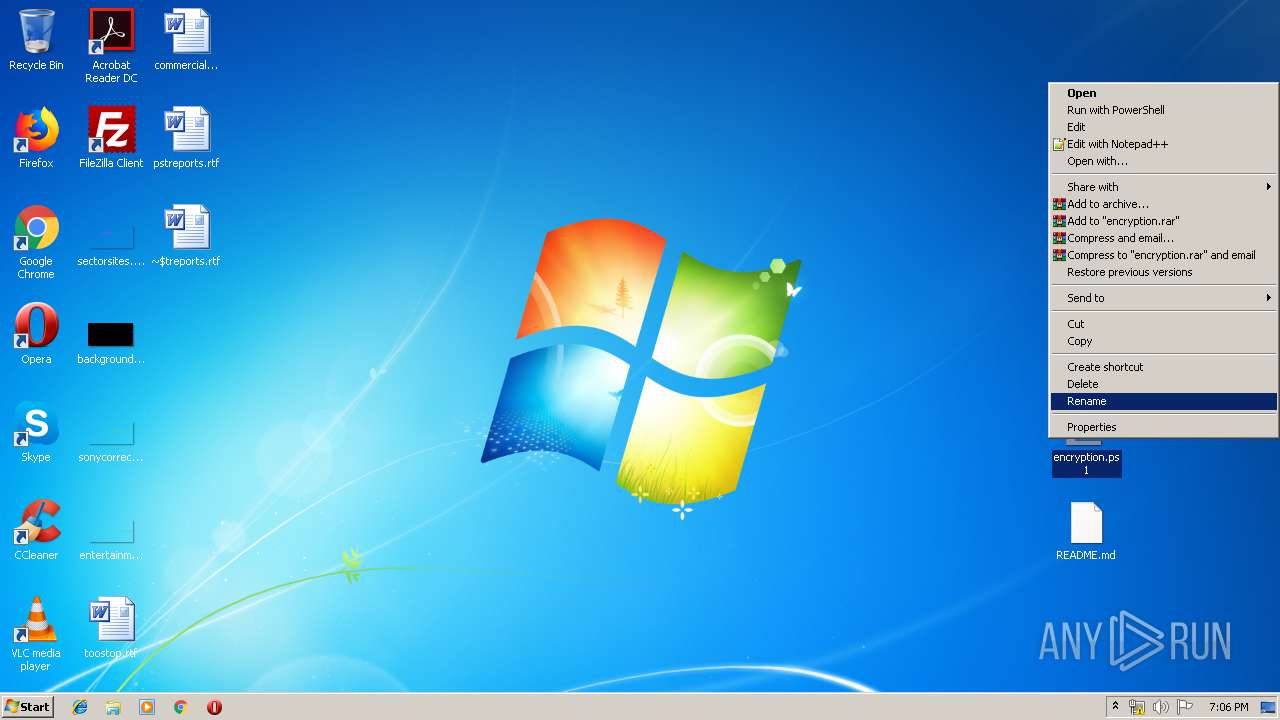
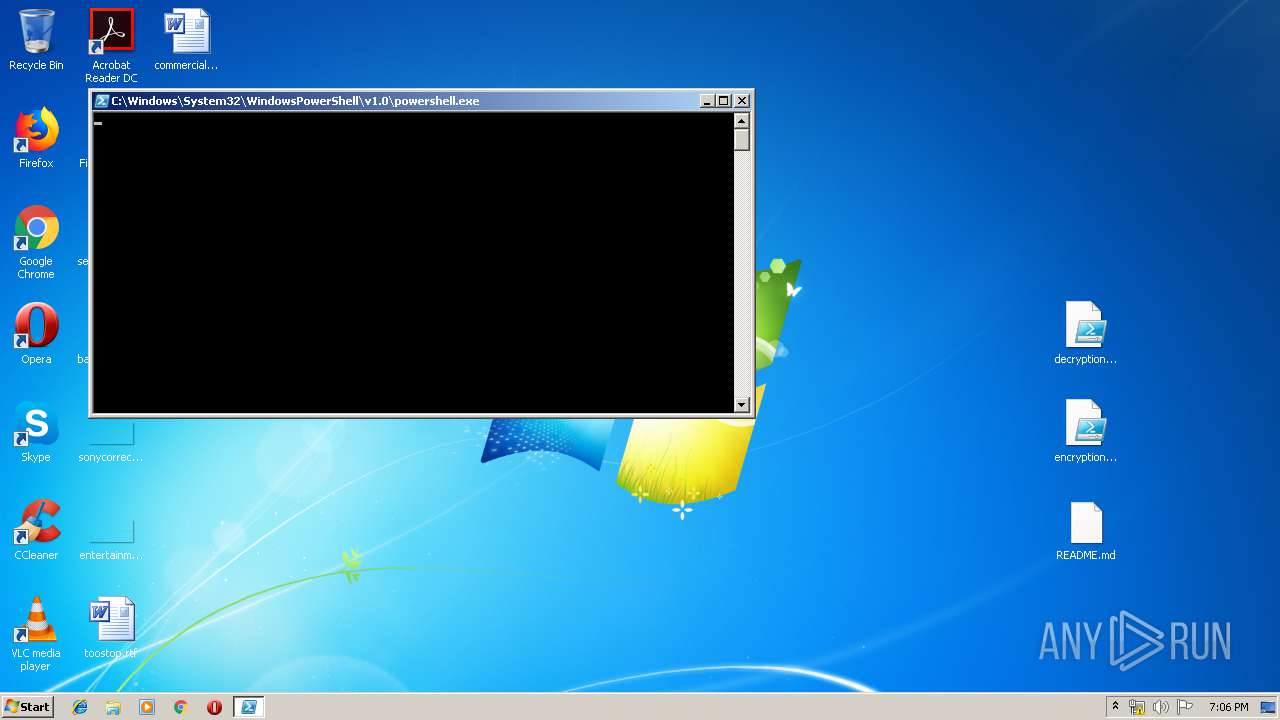
Manual execution by user
- WINWORD.EXE (PID: 1728)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 2604)
- powershell.exe (PID: 1528)
- WINWORD.EXE (PID: 4020)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 3528)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1728)
- WINWORD.EXE (PID: 4020)
Creates files in the user directory
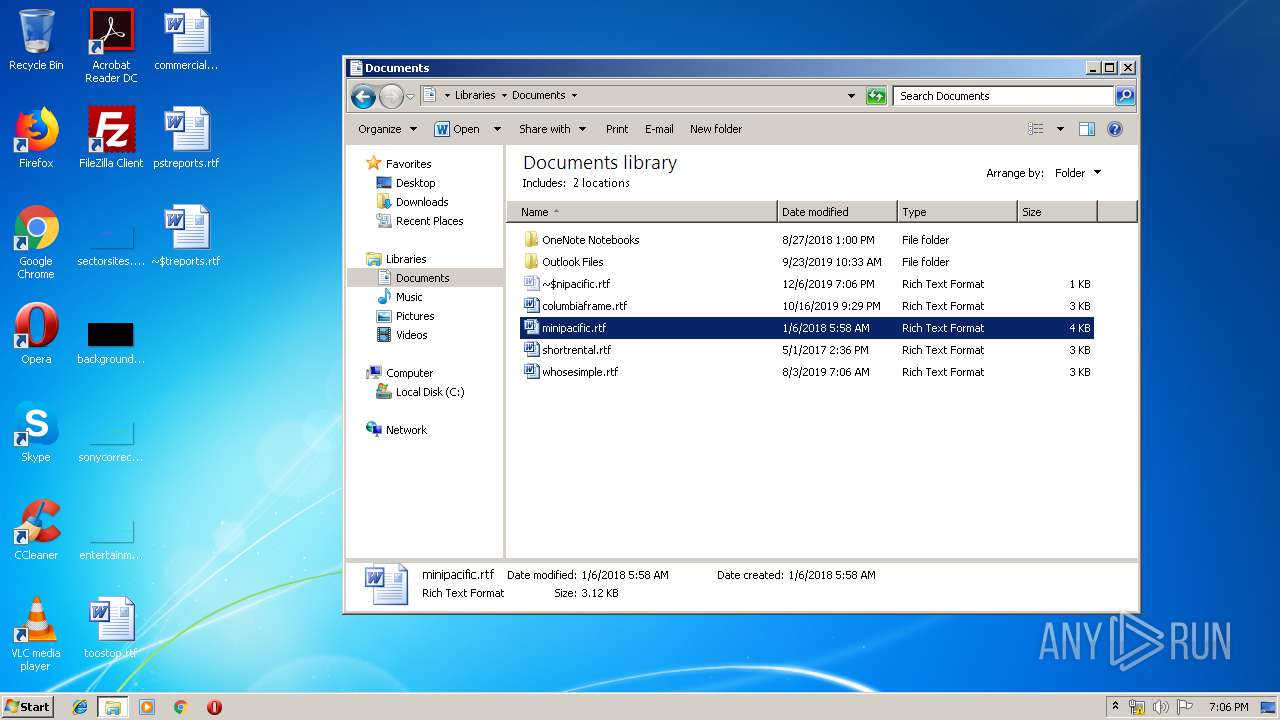
- WINWORD.EXE (PID: 1728)
- WINWORD.EXE (PID: 4020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 692 |
|---|---|
| UncompressedSize: | 1153 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:12:01 21:34:12 |
| PackingMethod: | Normal |
| ArchivedFileName: | README.md |
Total processes
51
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
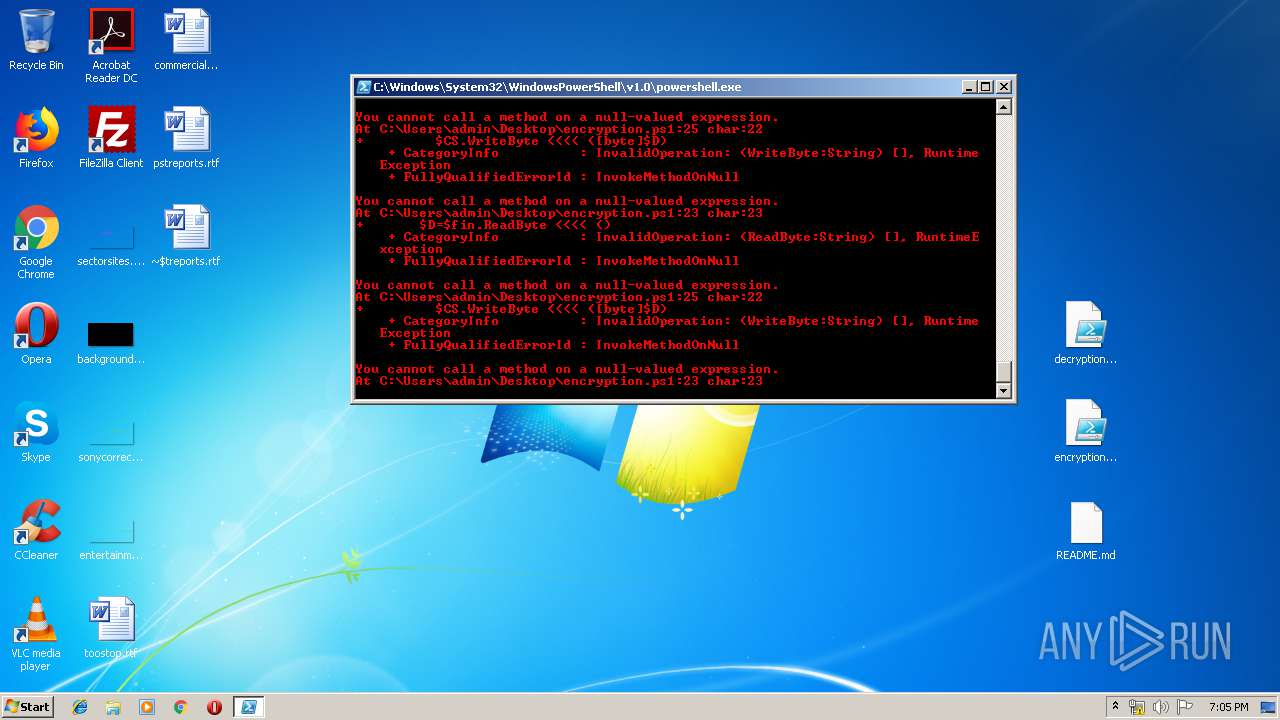
| 1528 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\decryption.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\pstreports.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2188 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\decryption.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
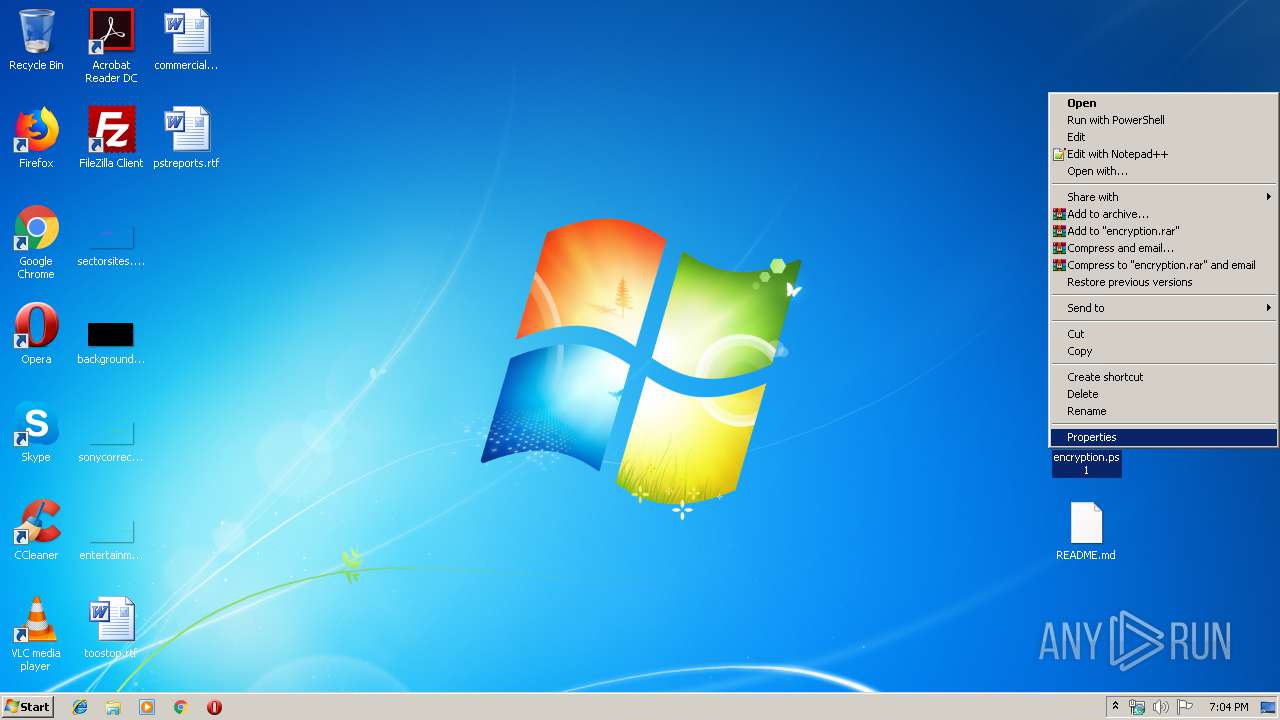
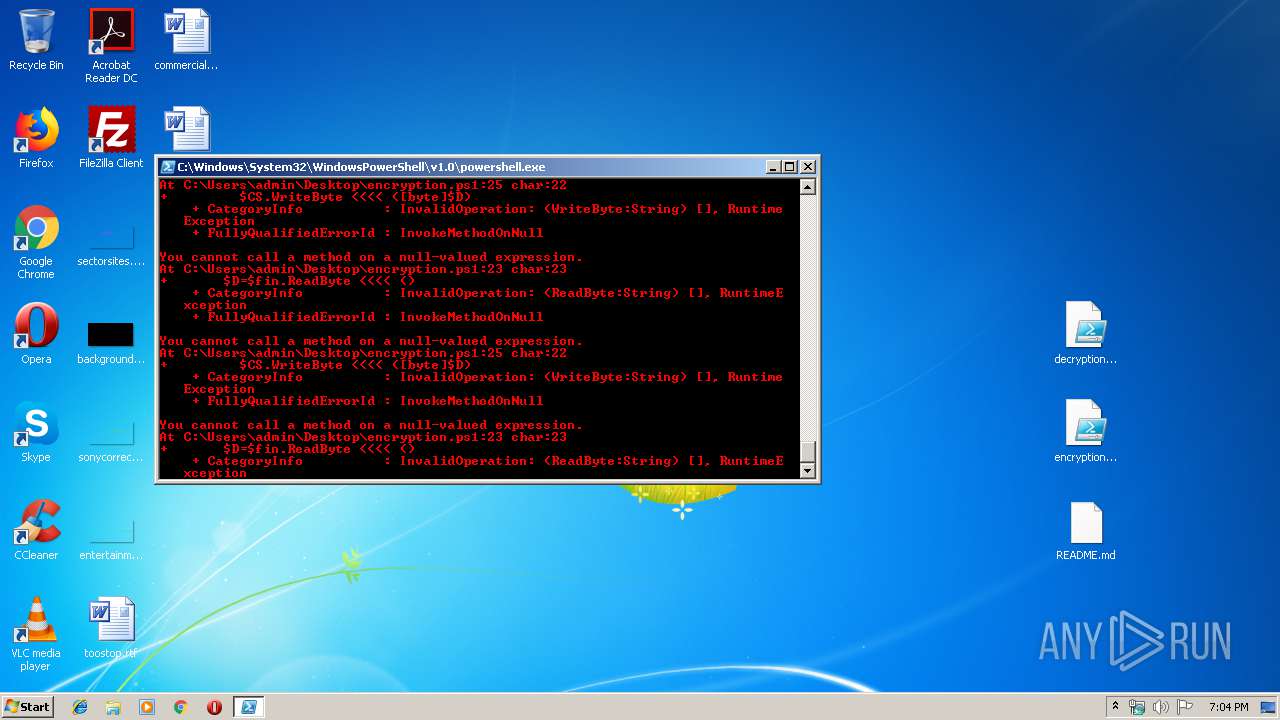
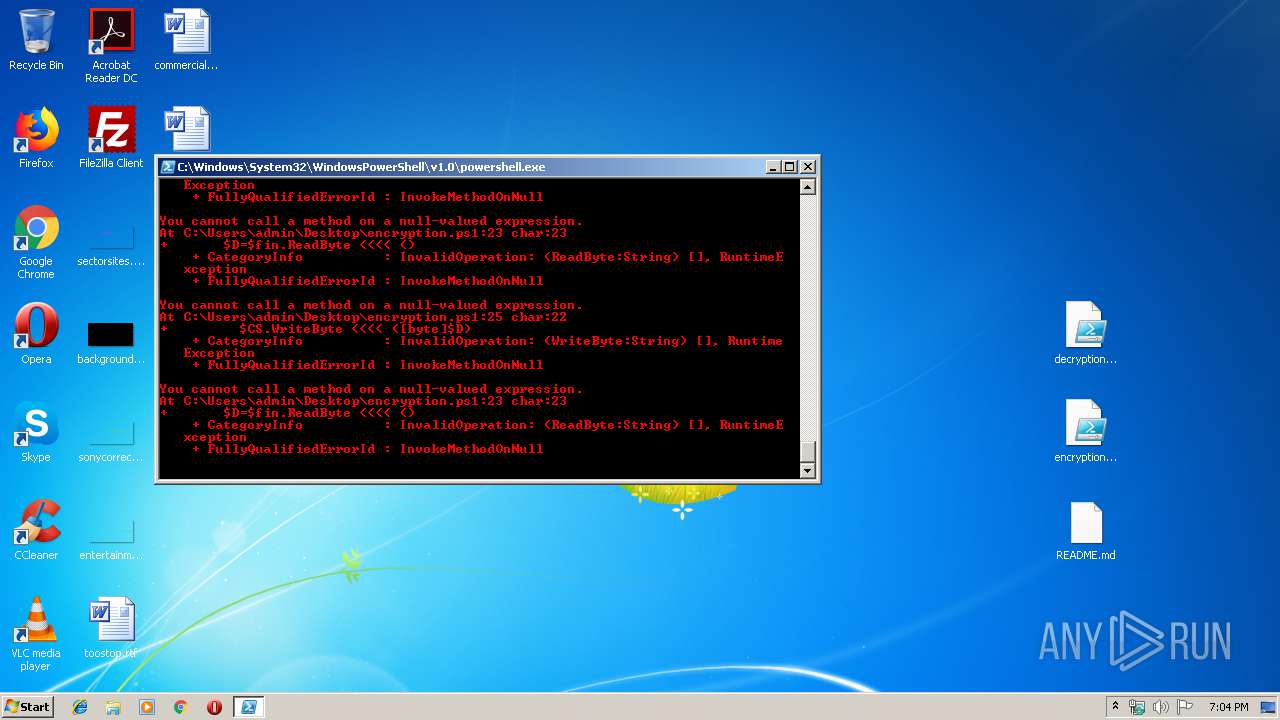
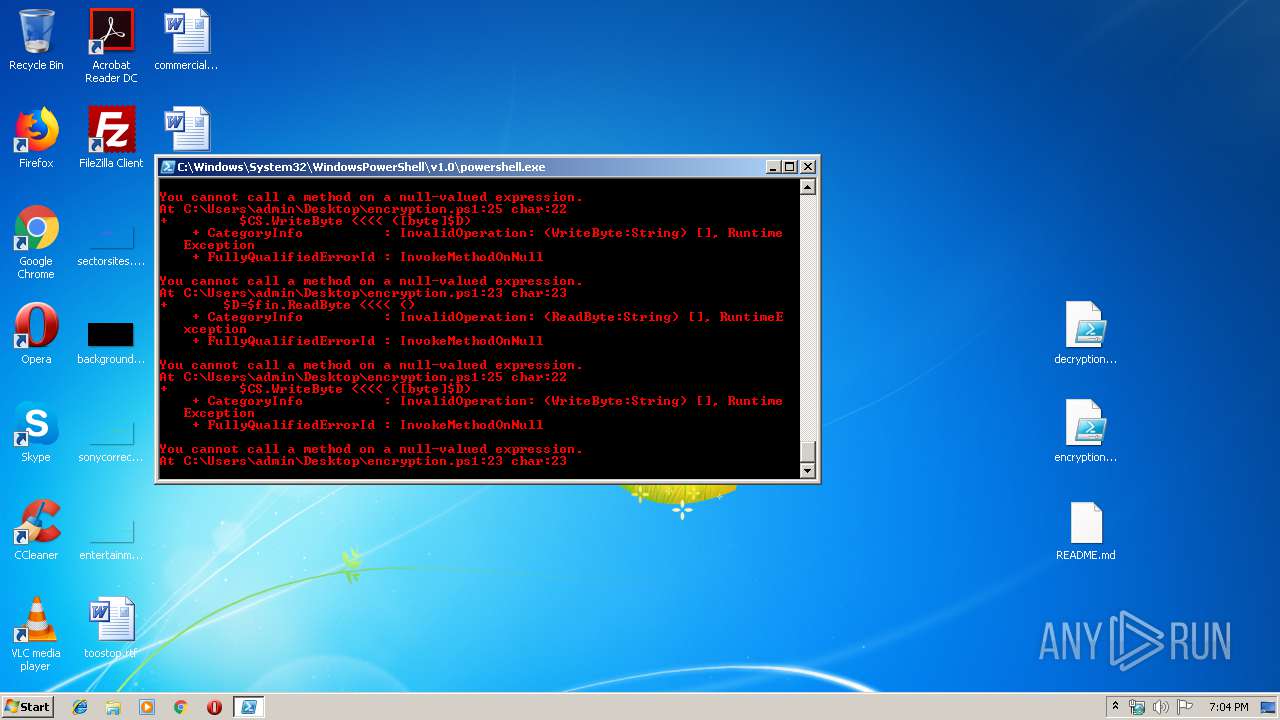
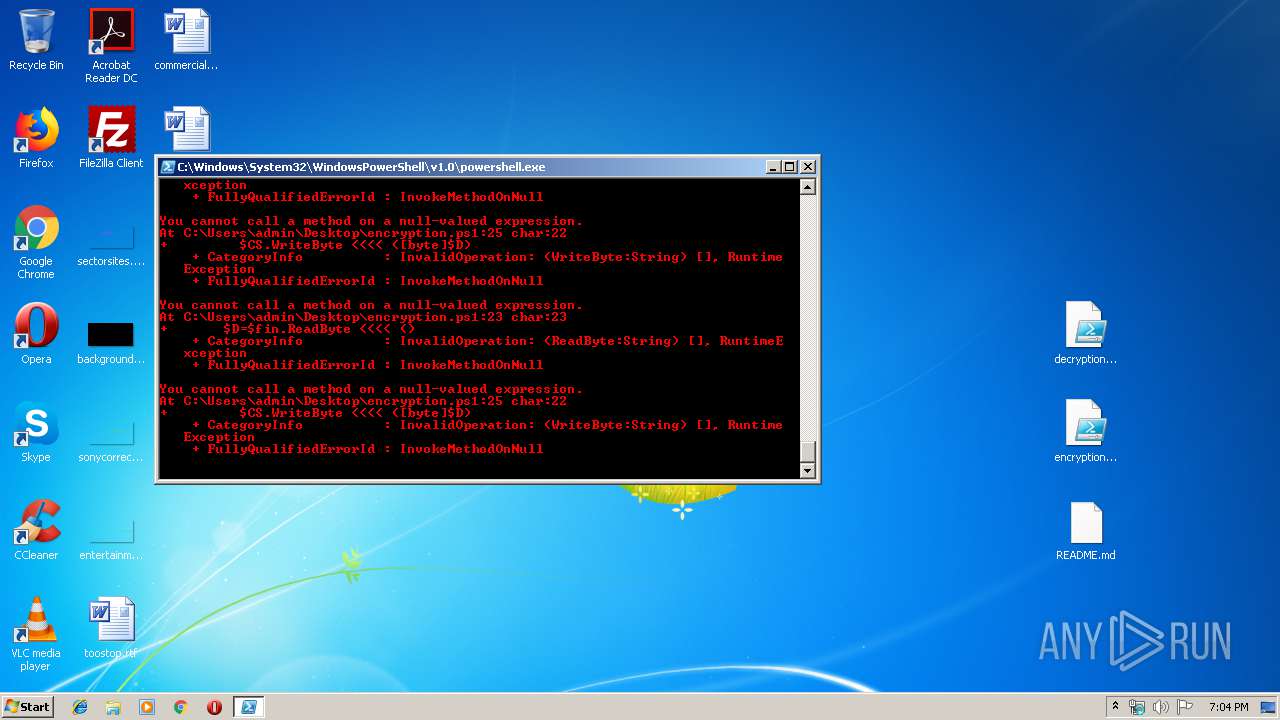
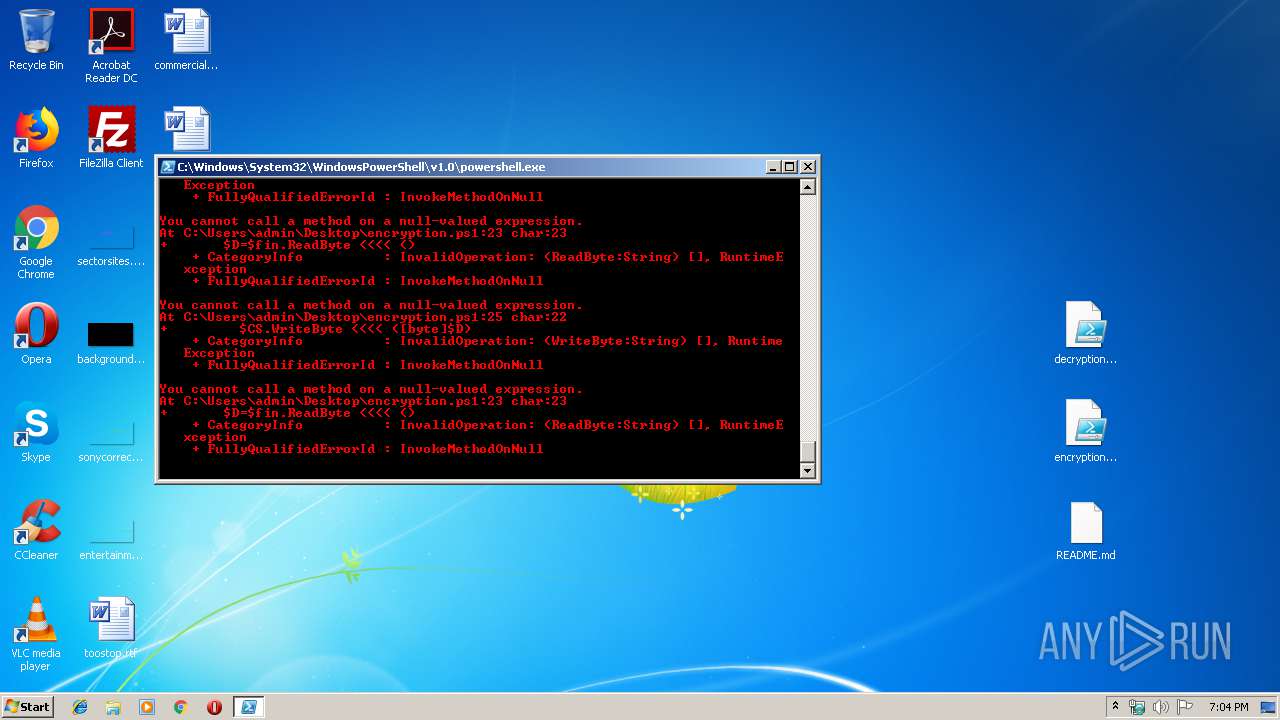
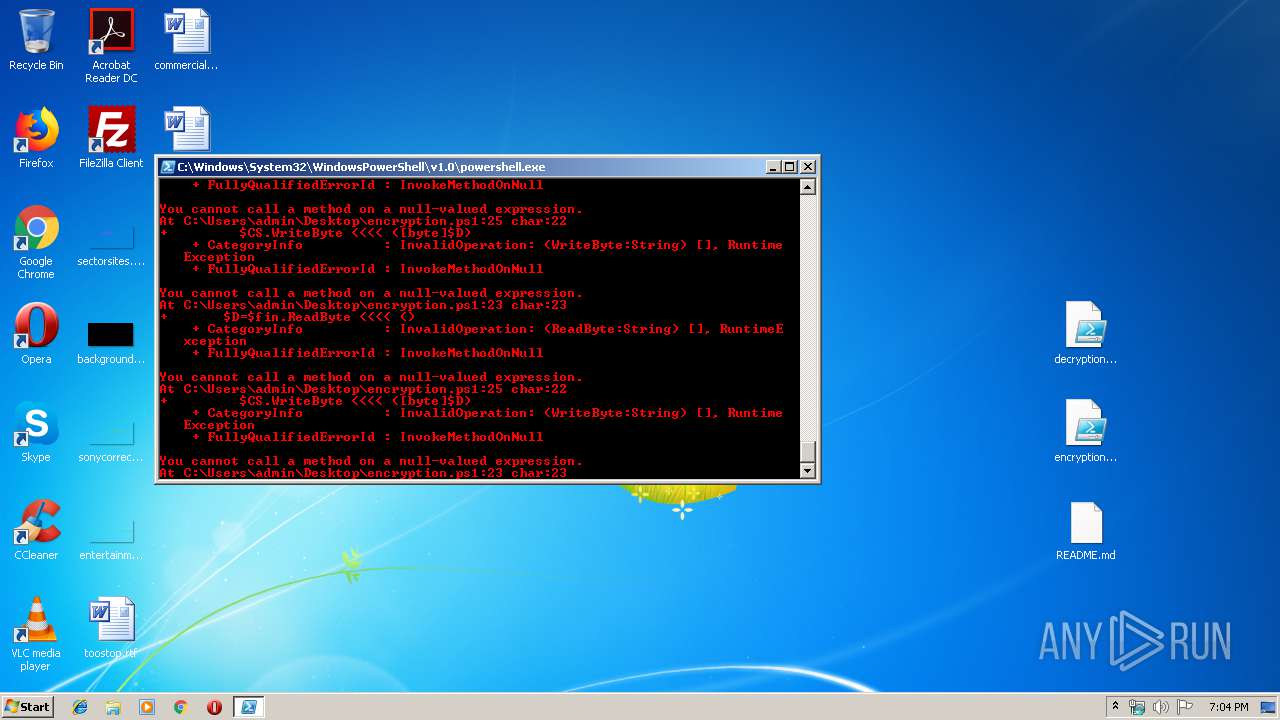
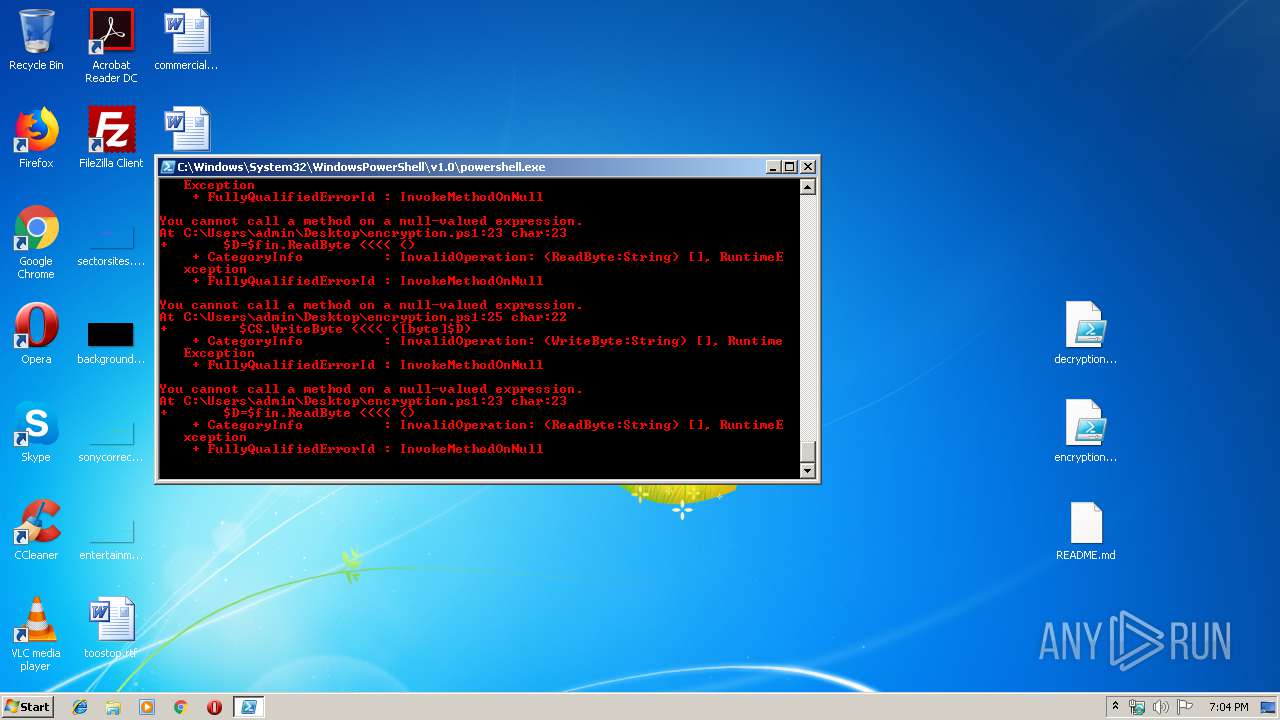
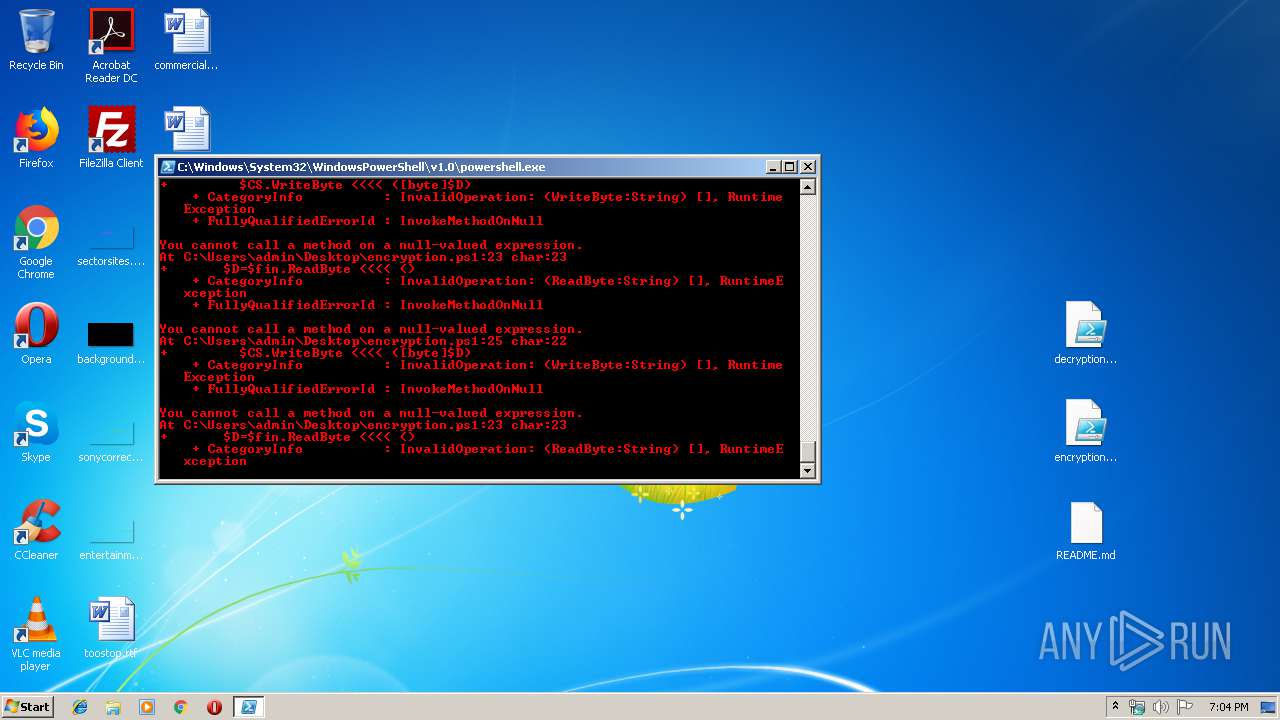
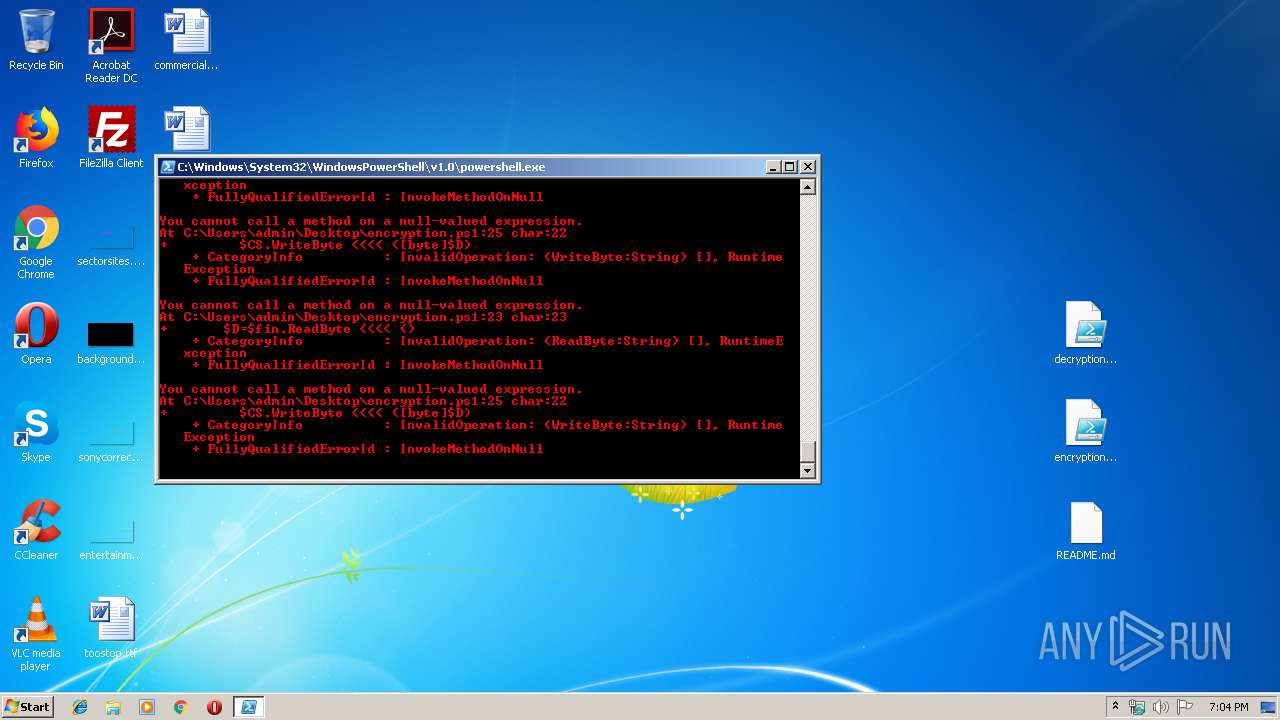
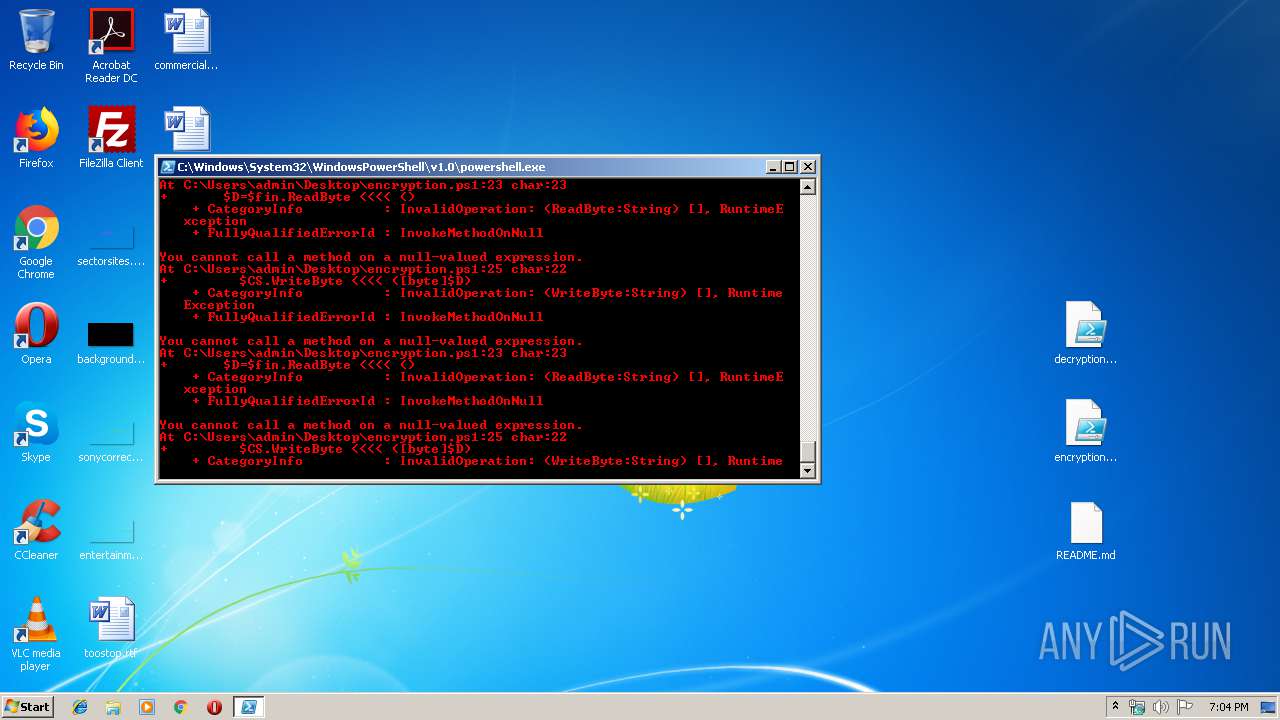
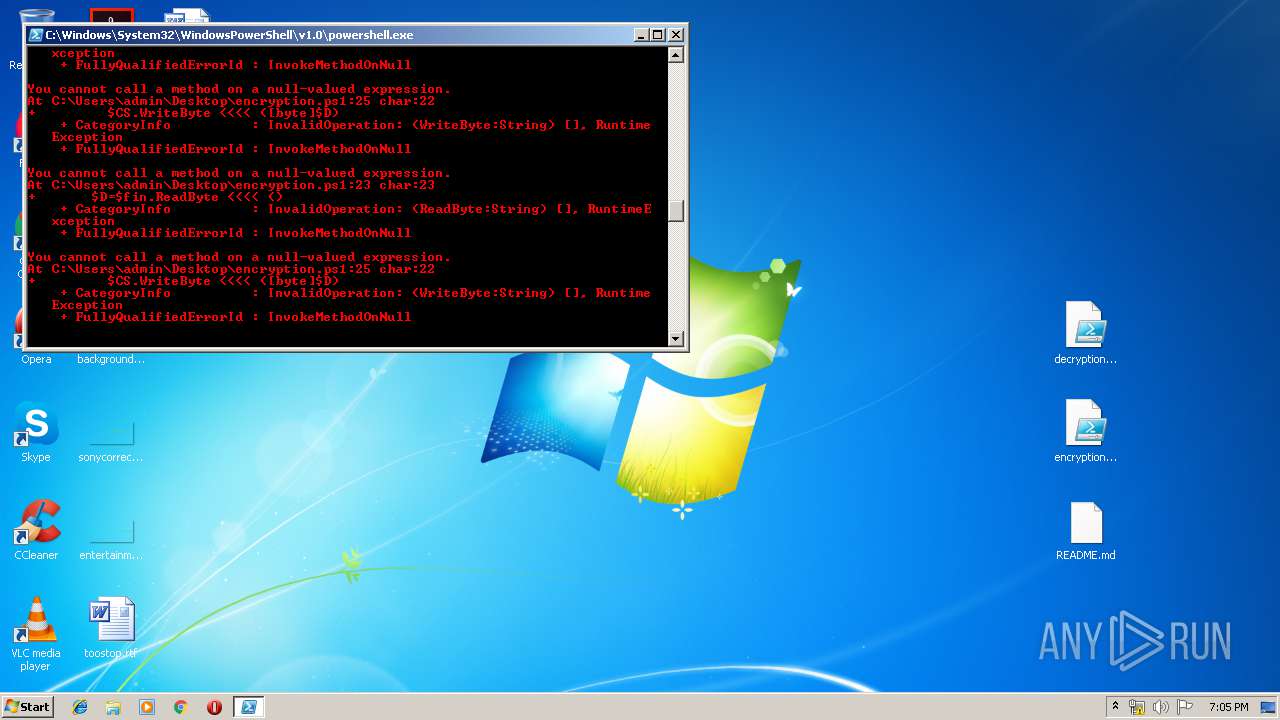
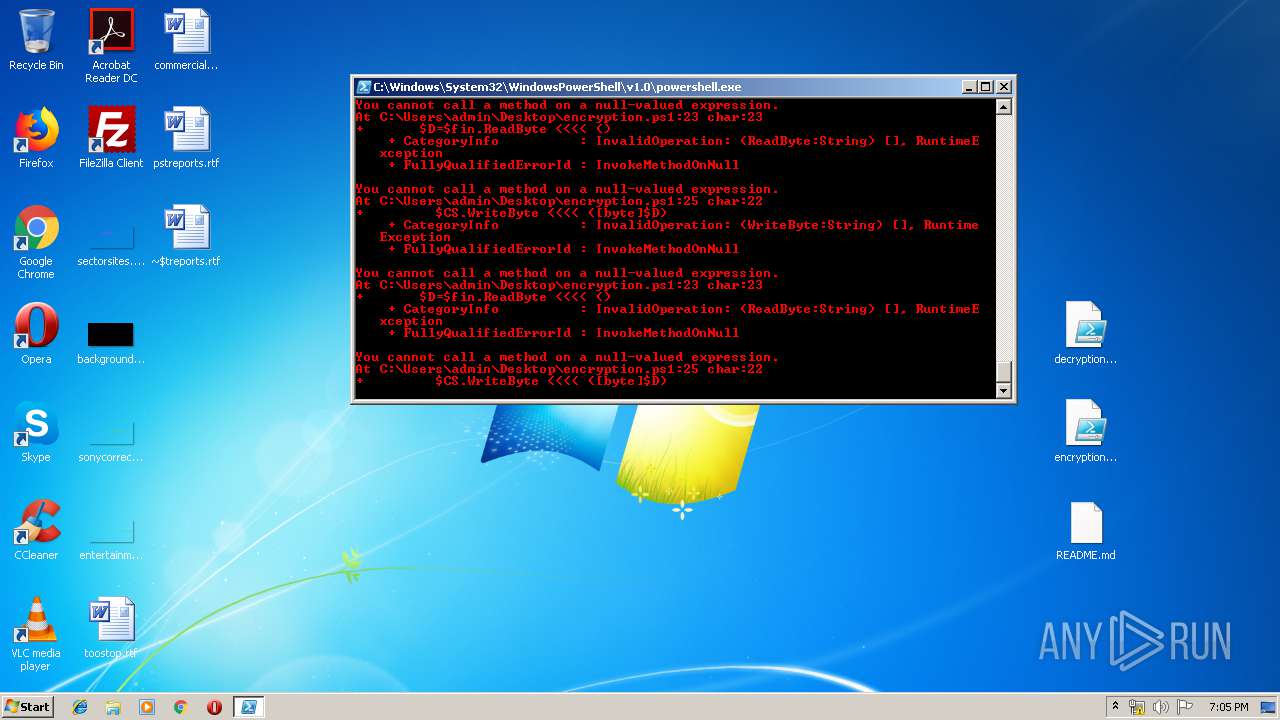
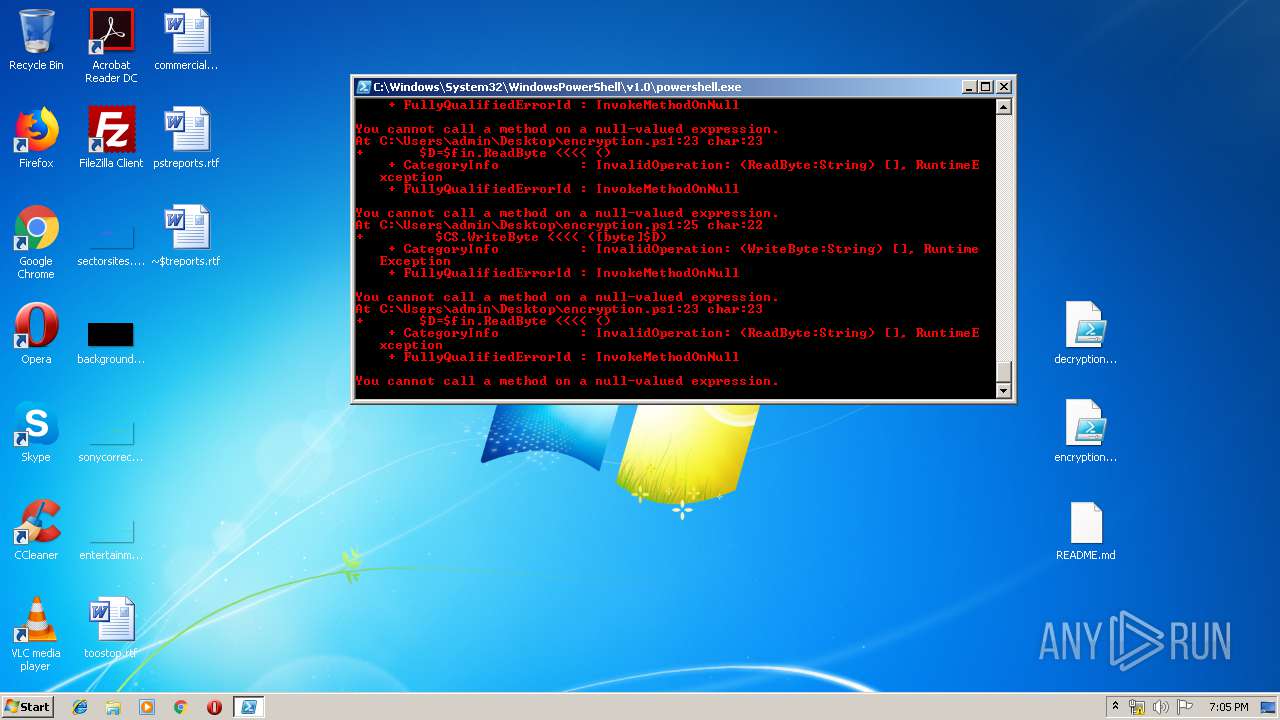
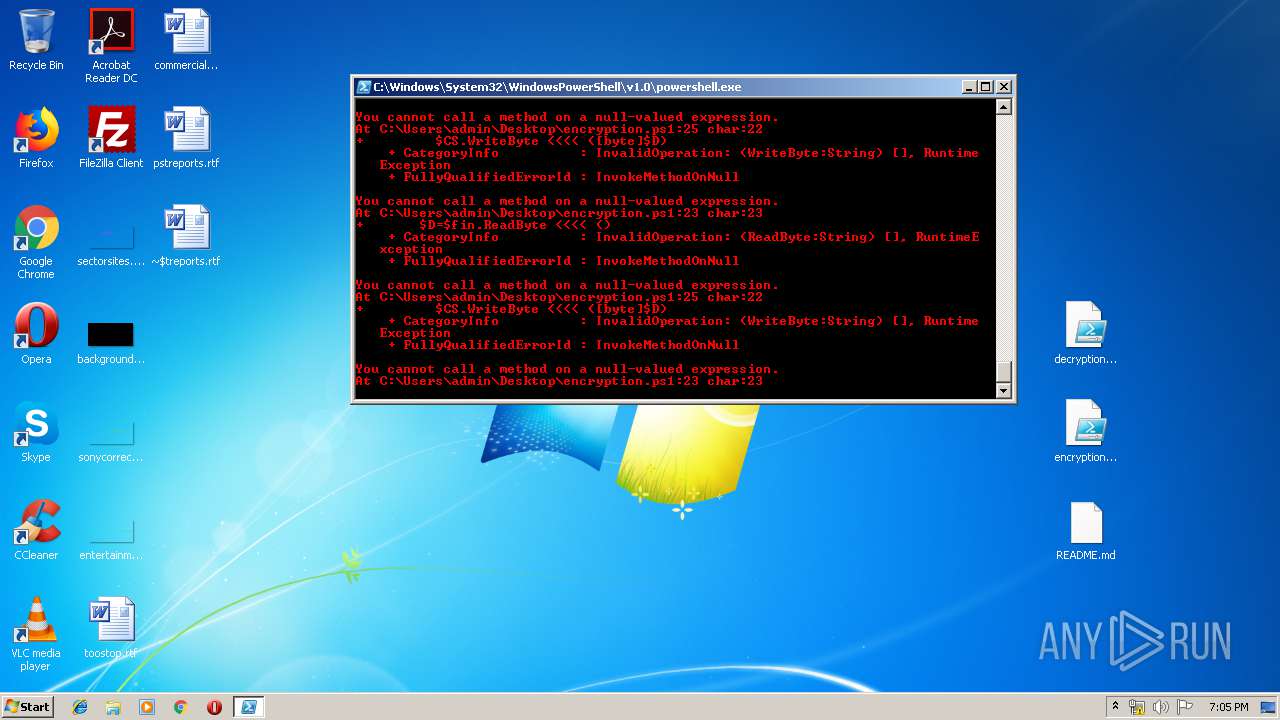
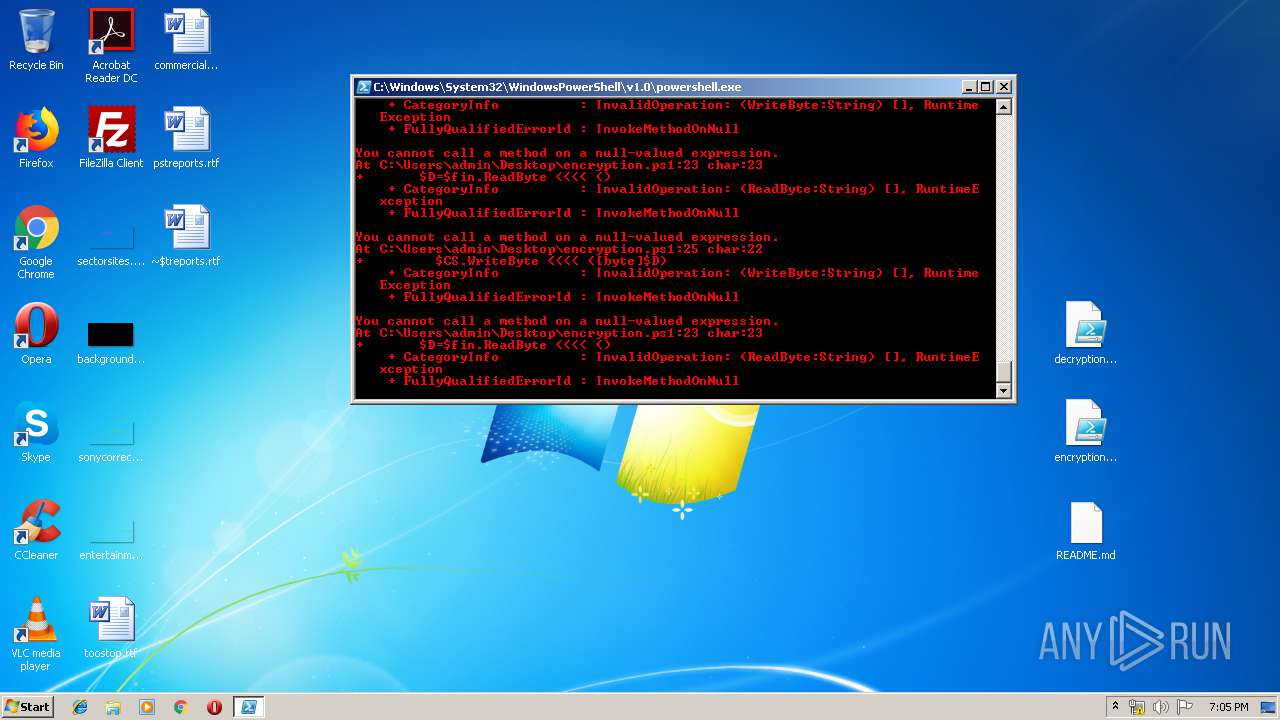
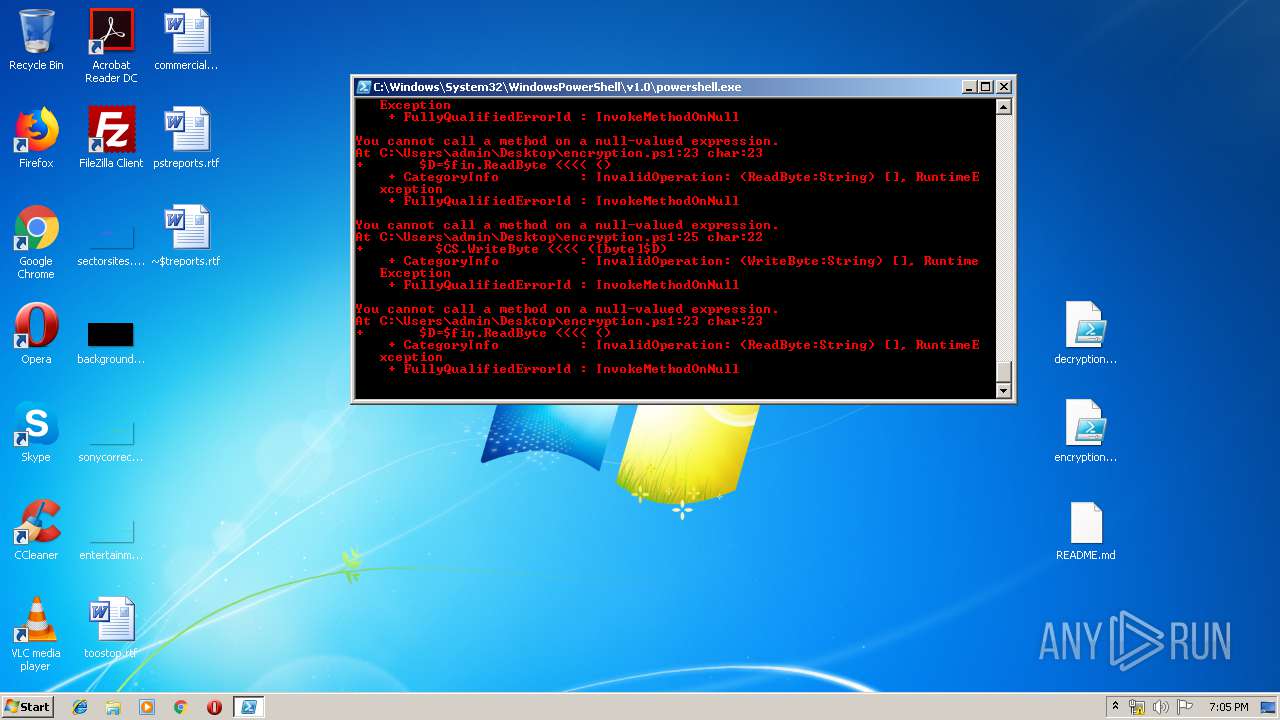
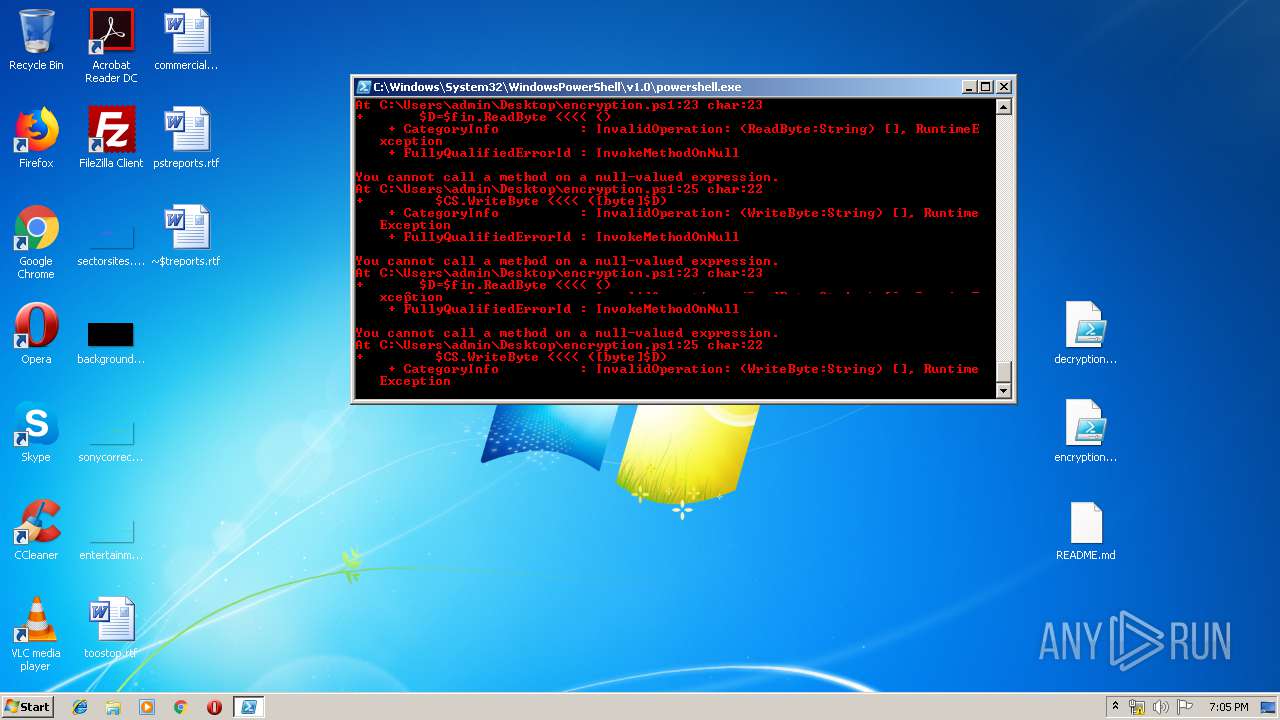
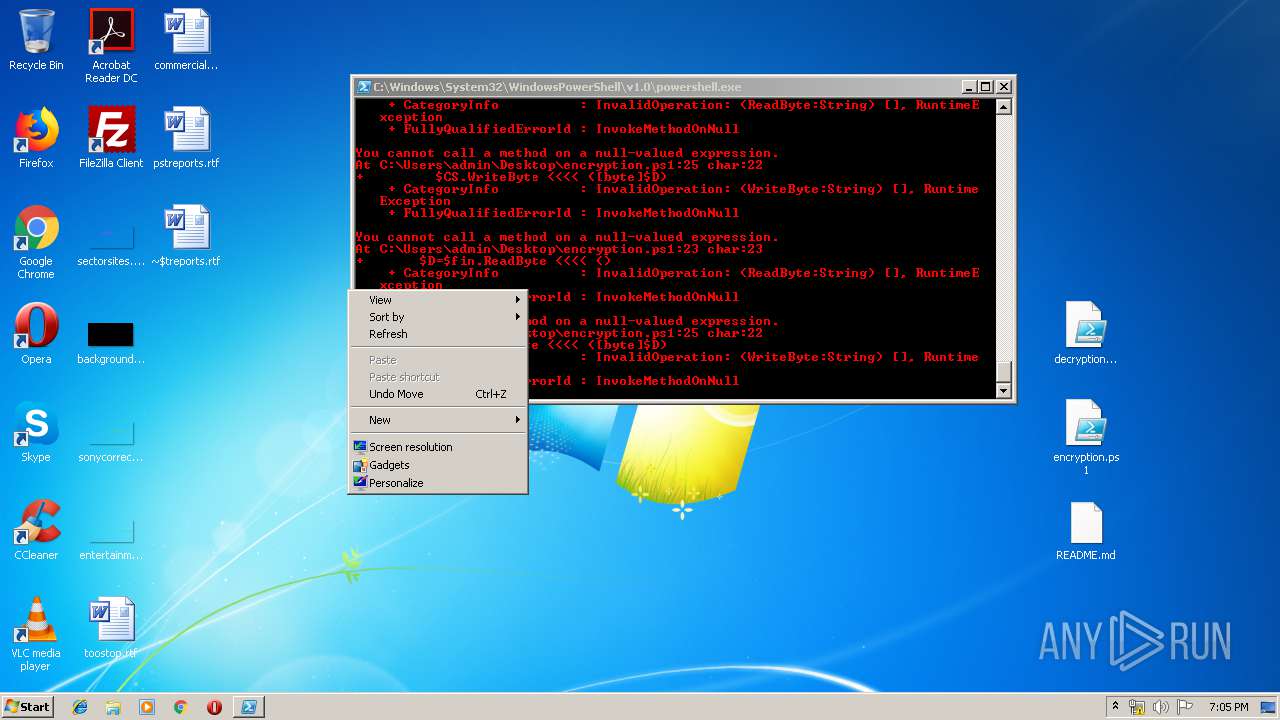
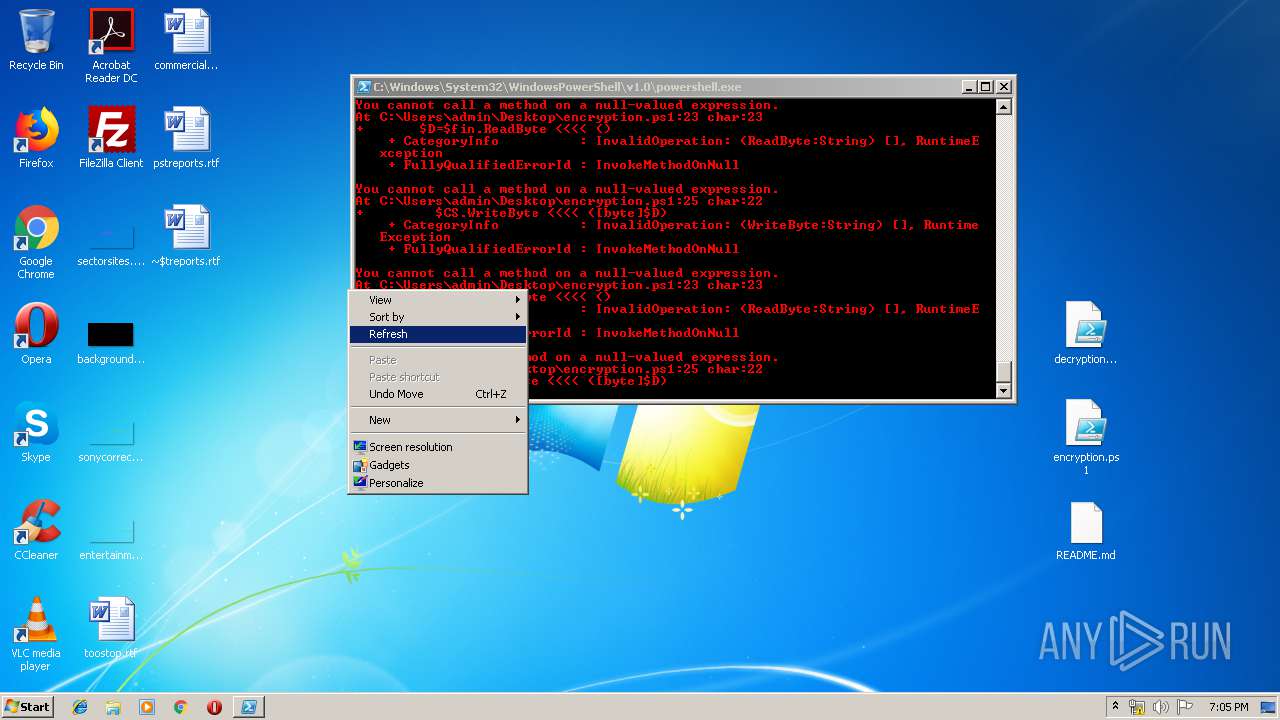
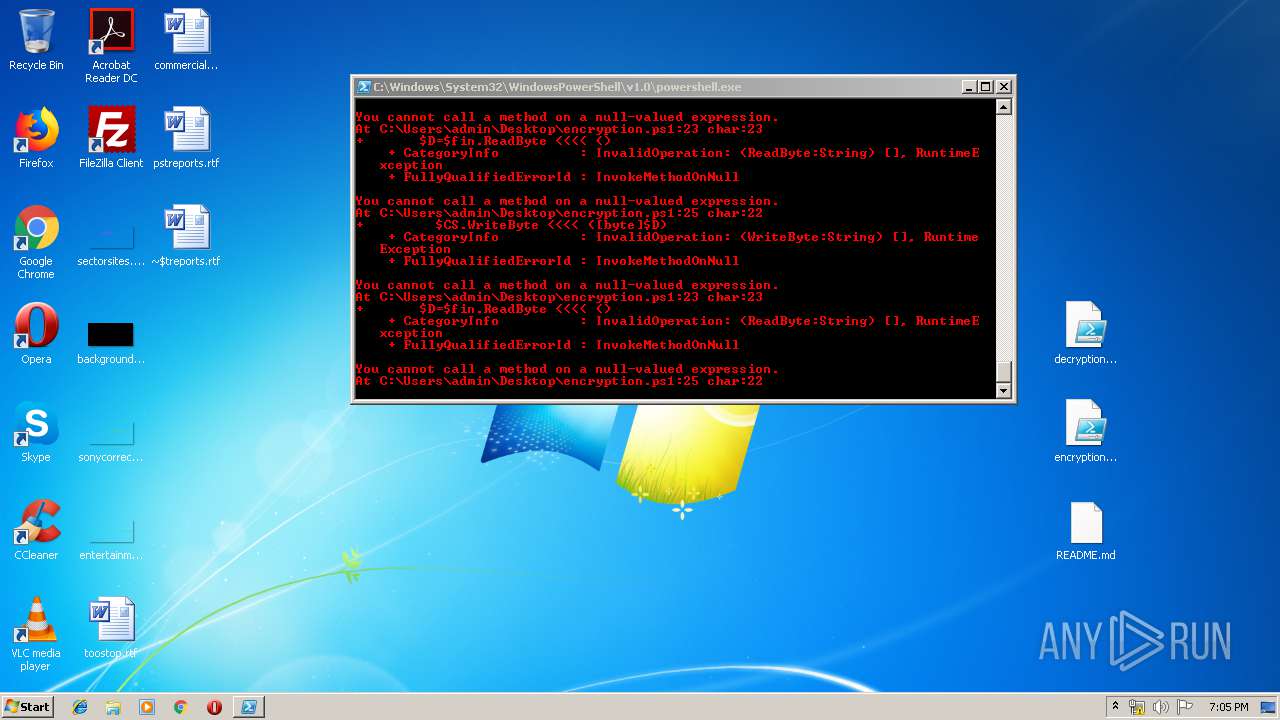
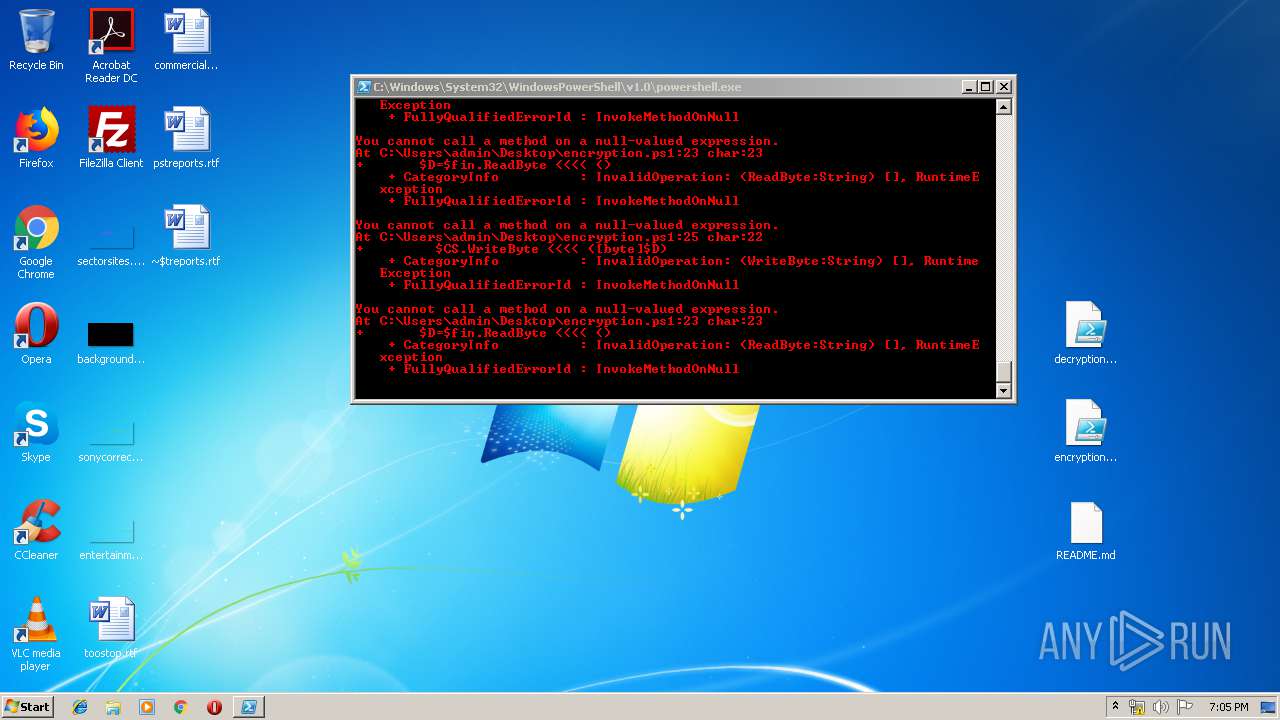
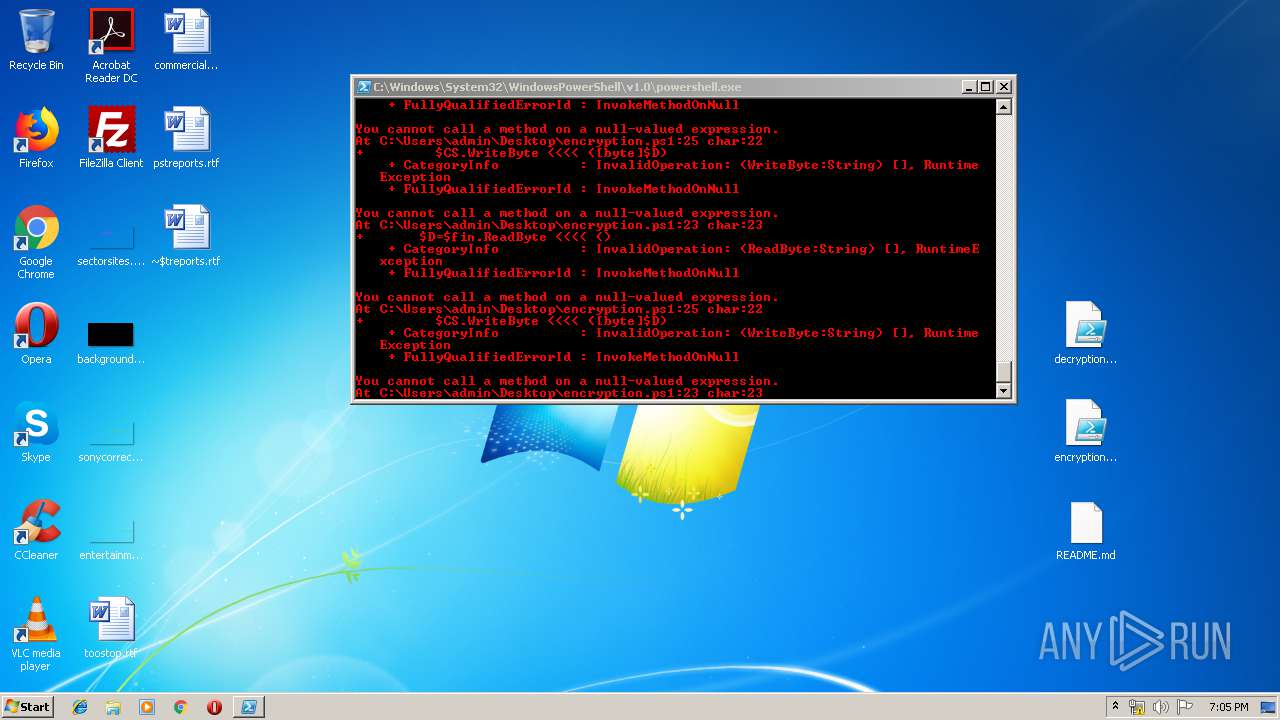
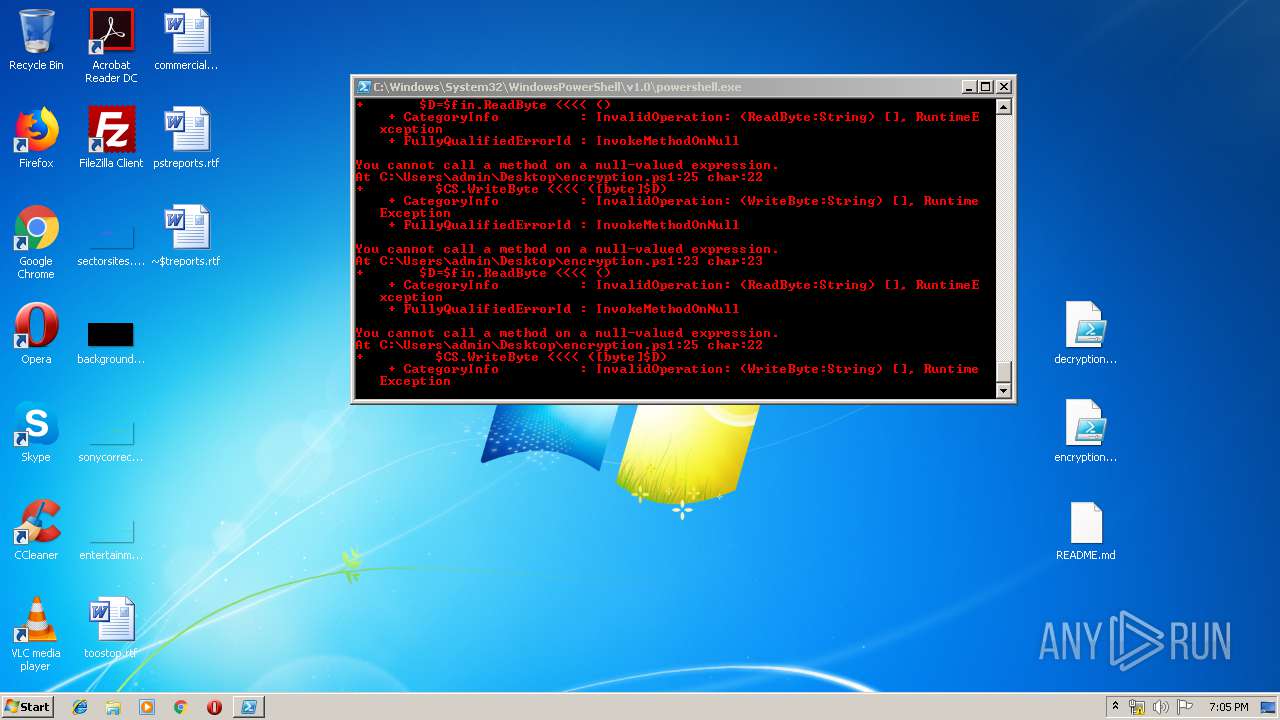
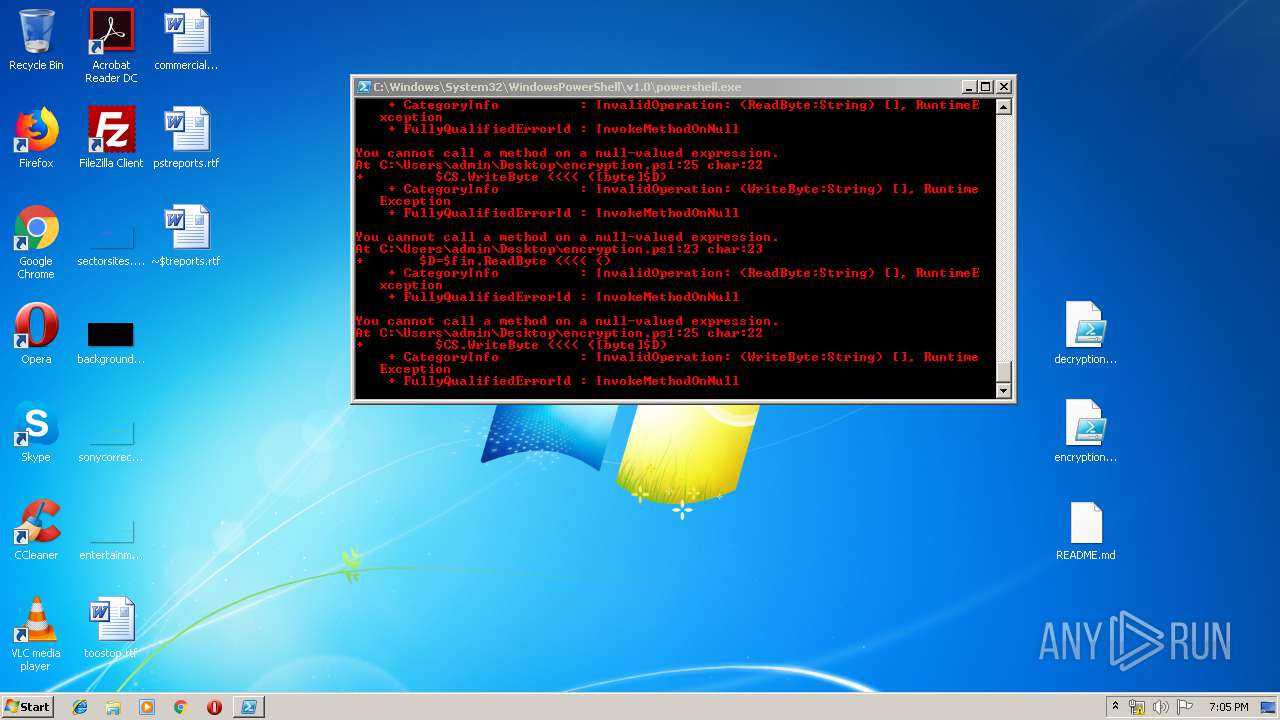
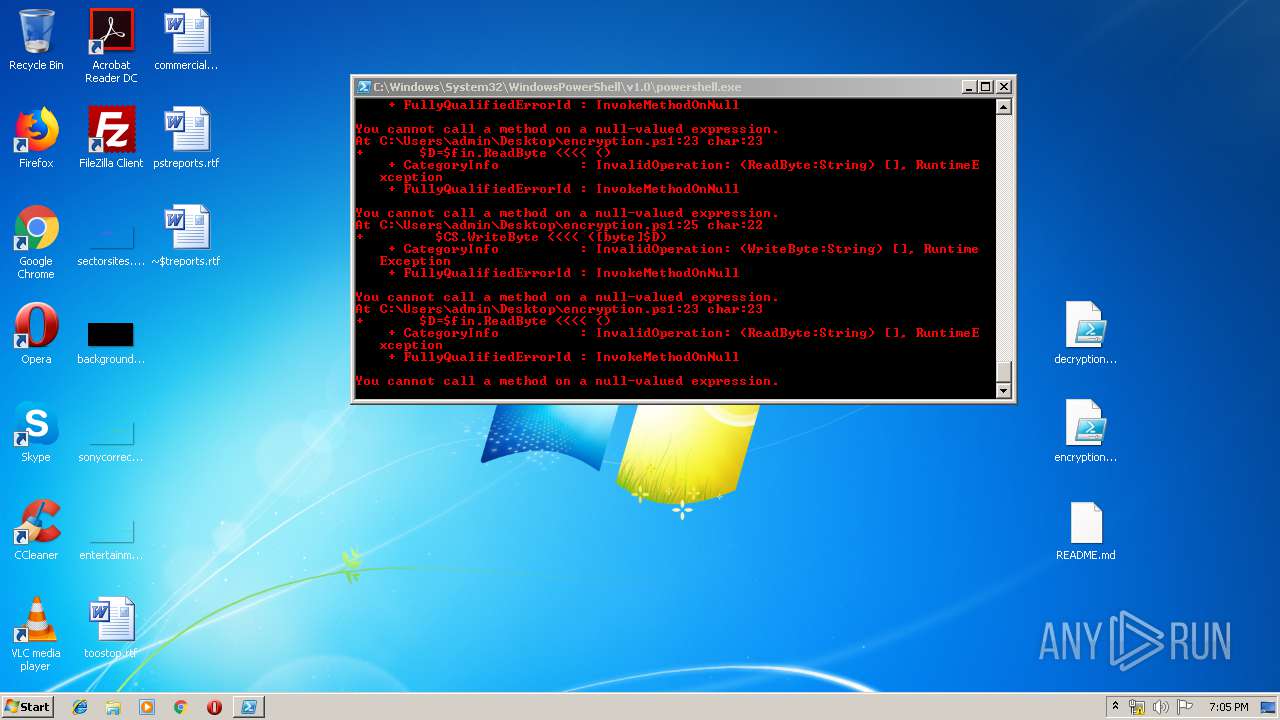
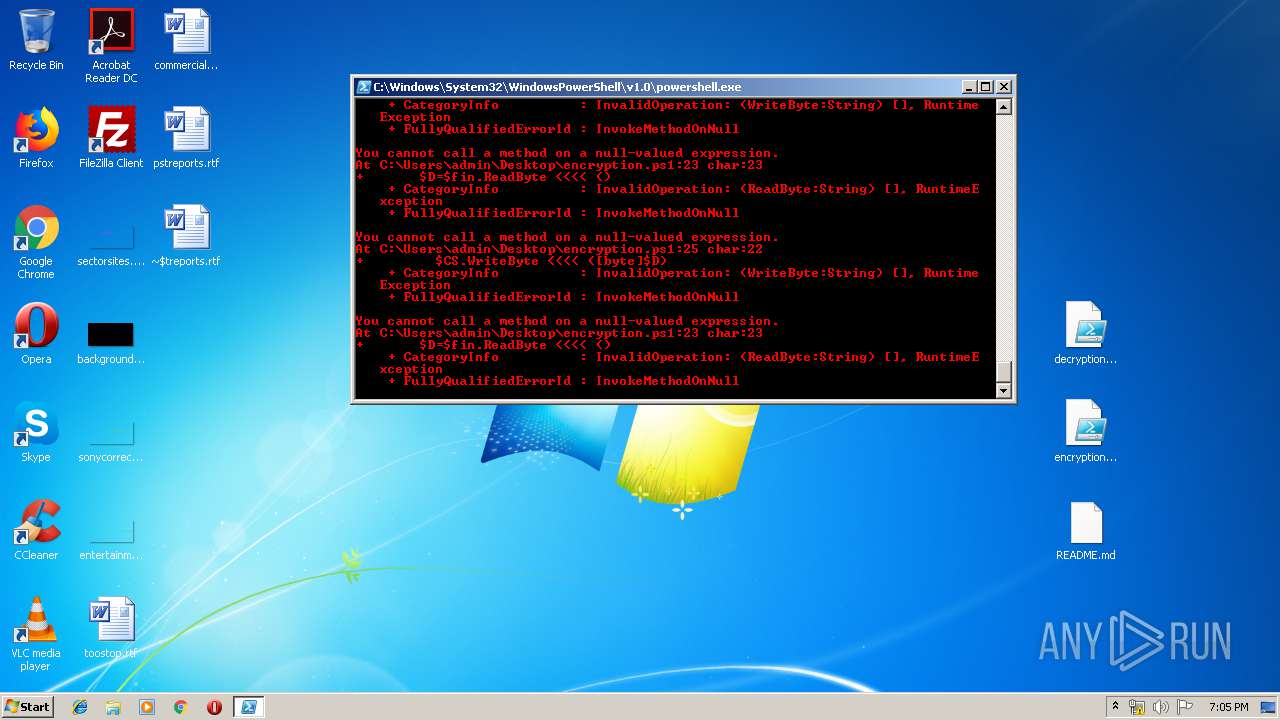
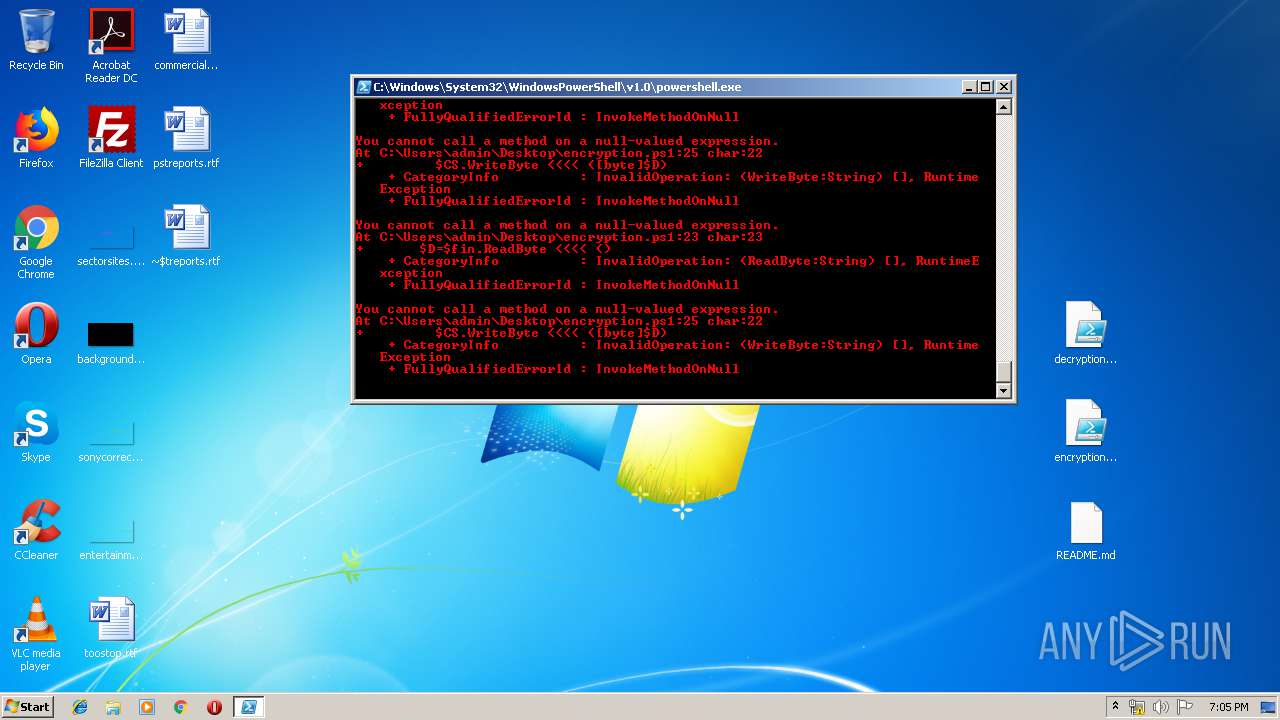
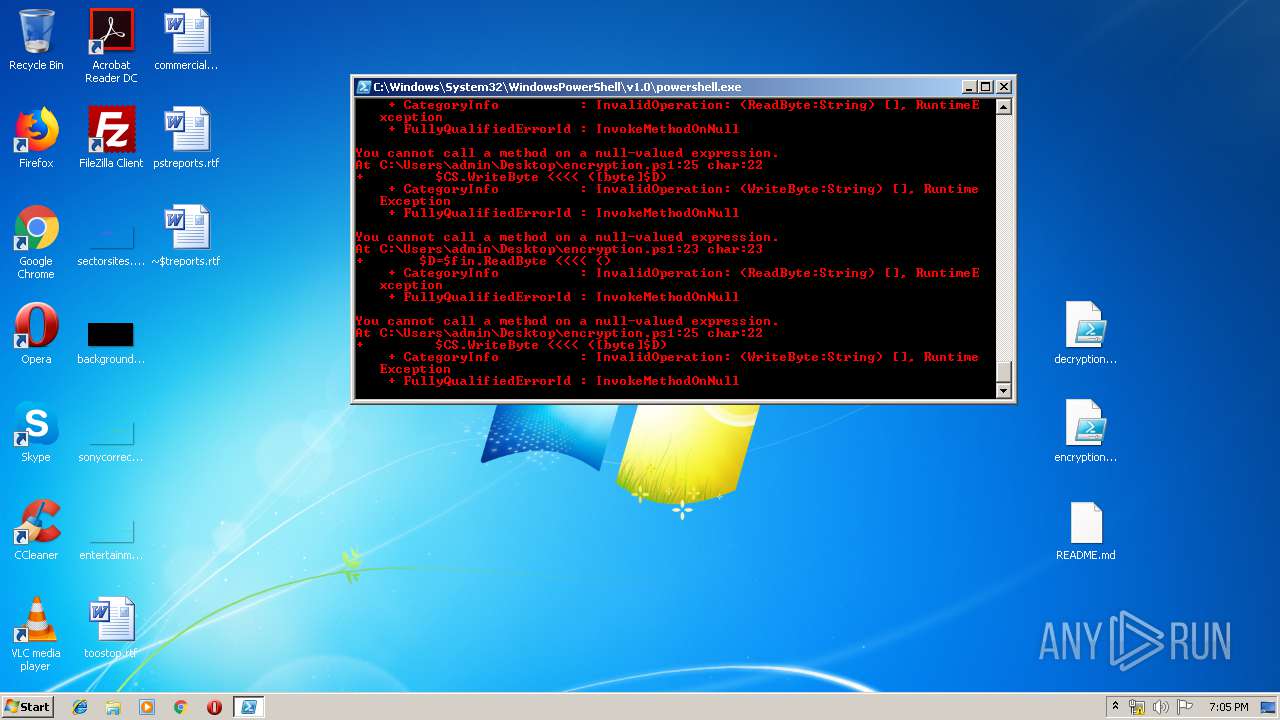
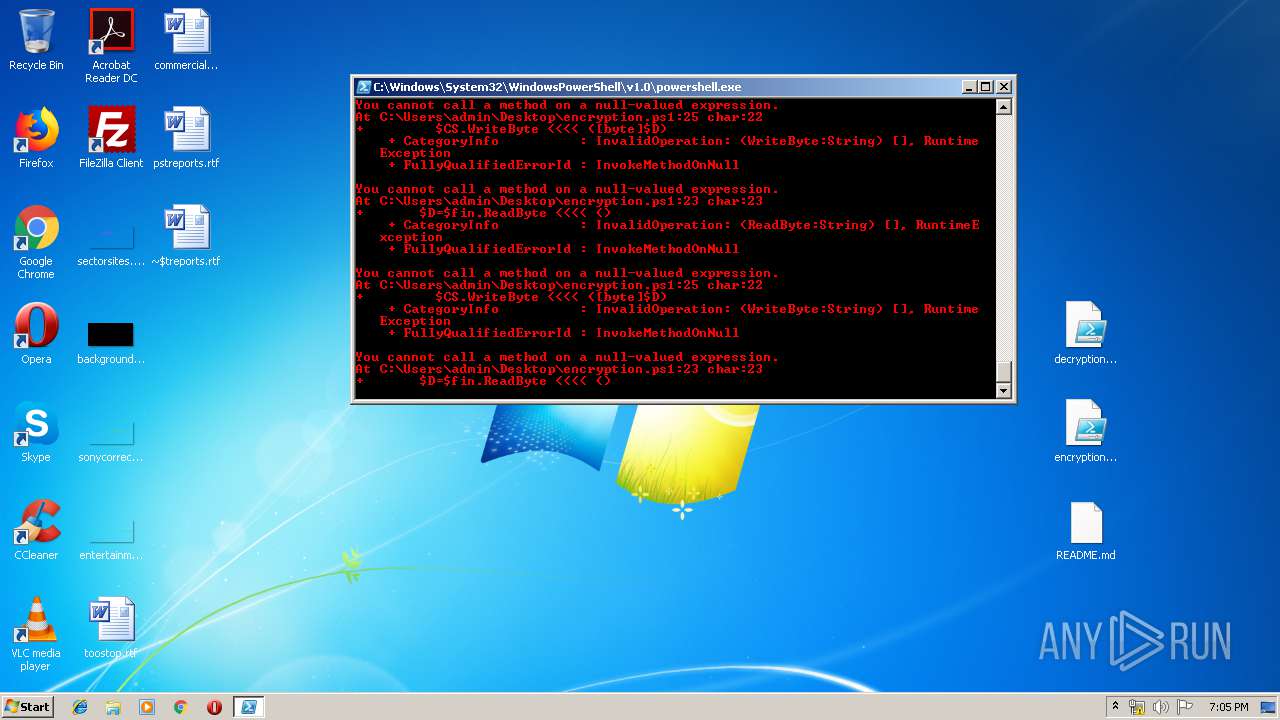
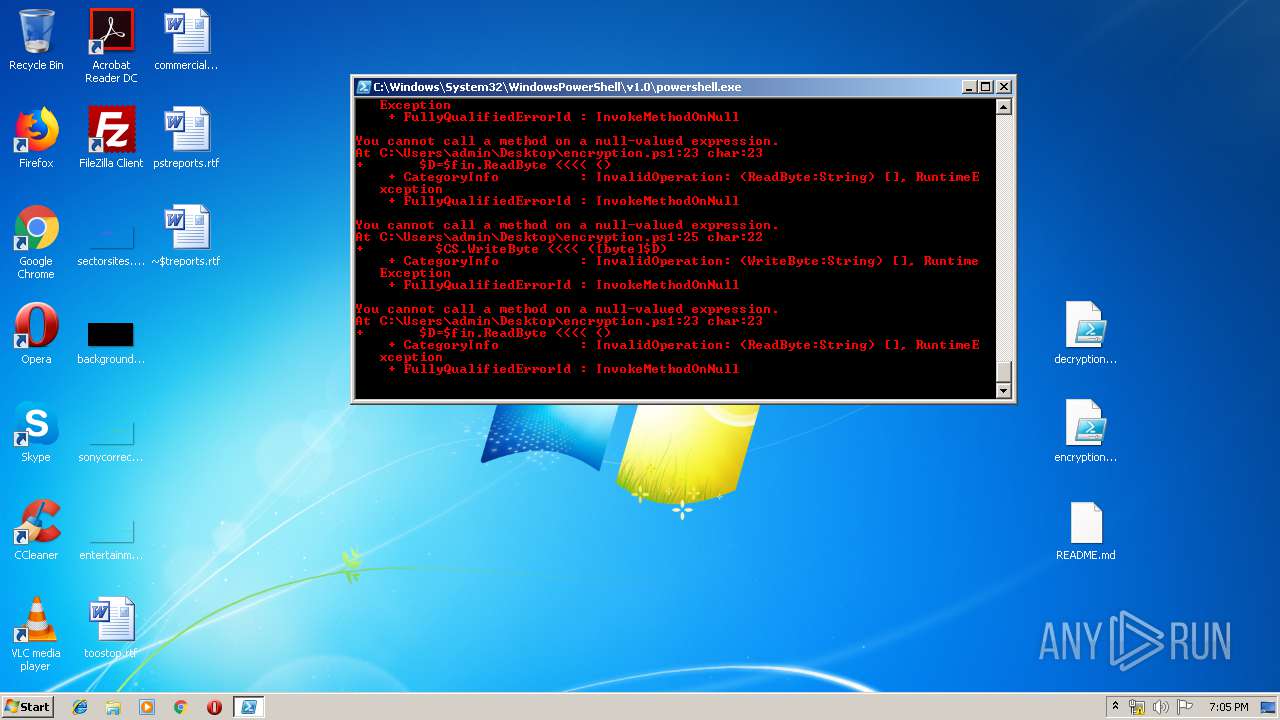
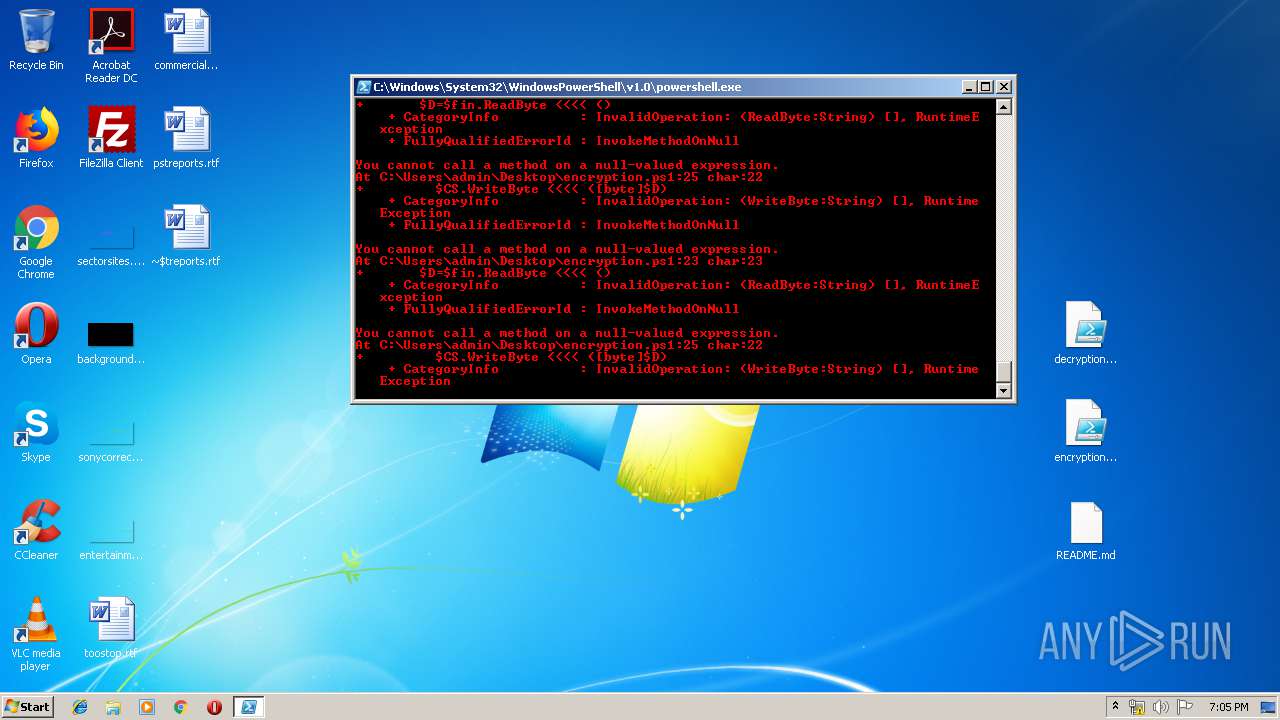
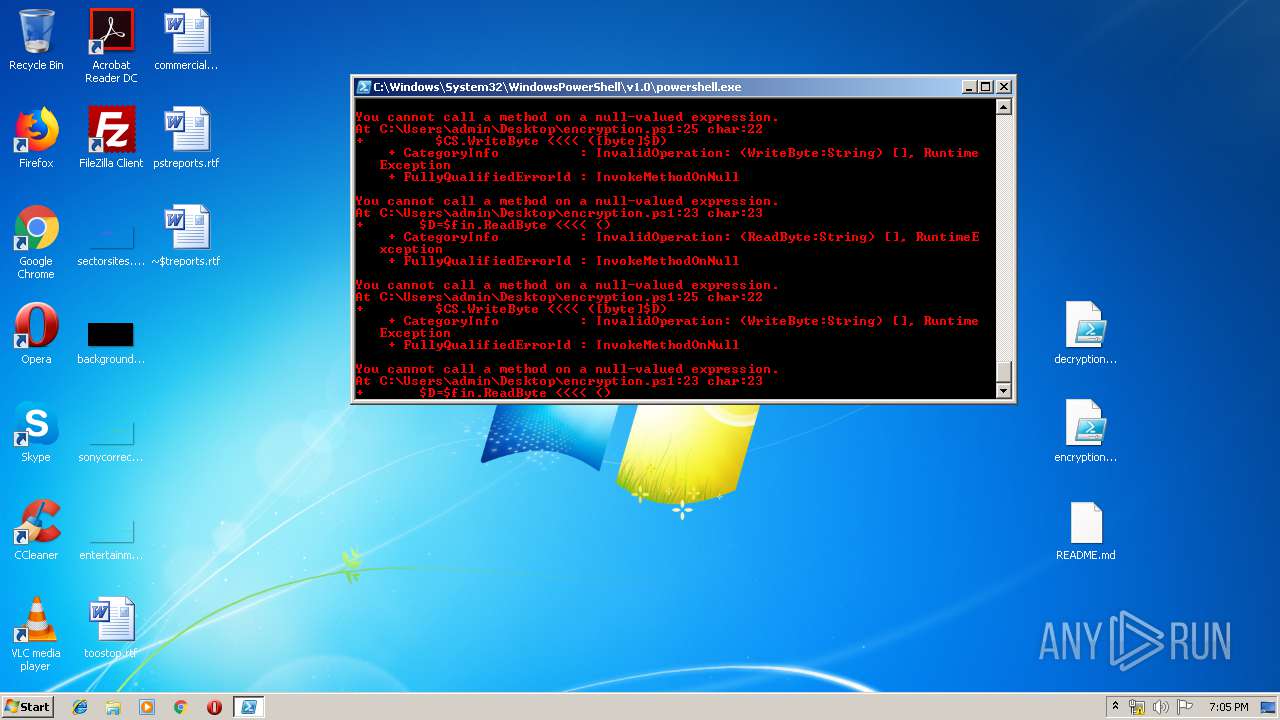
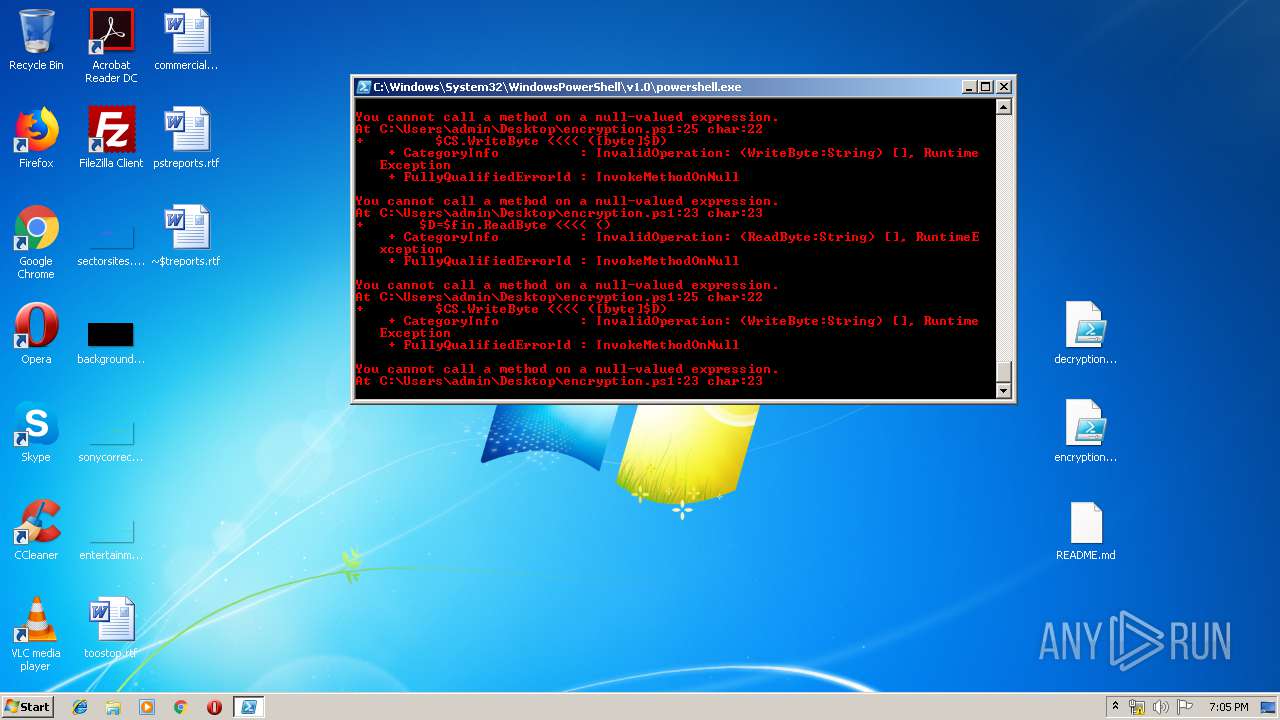
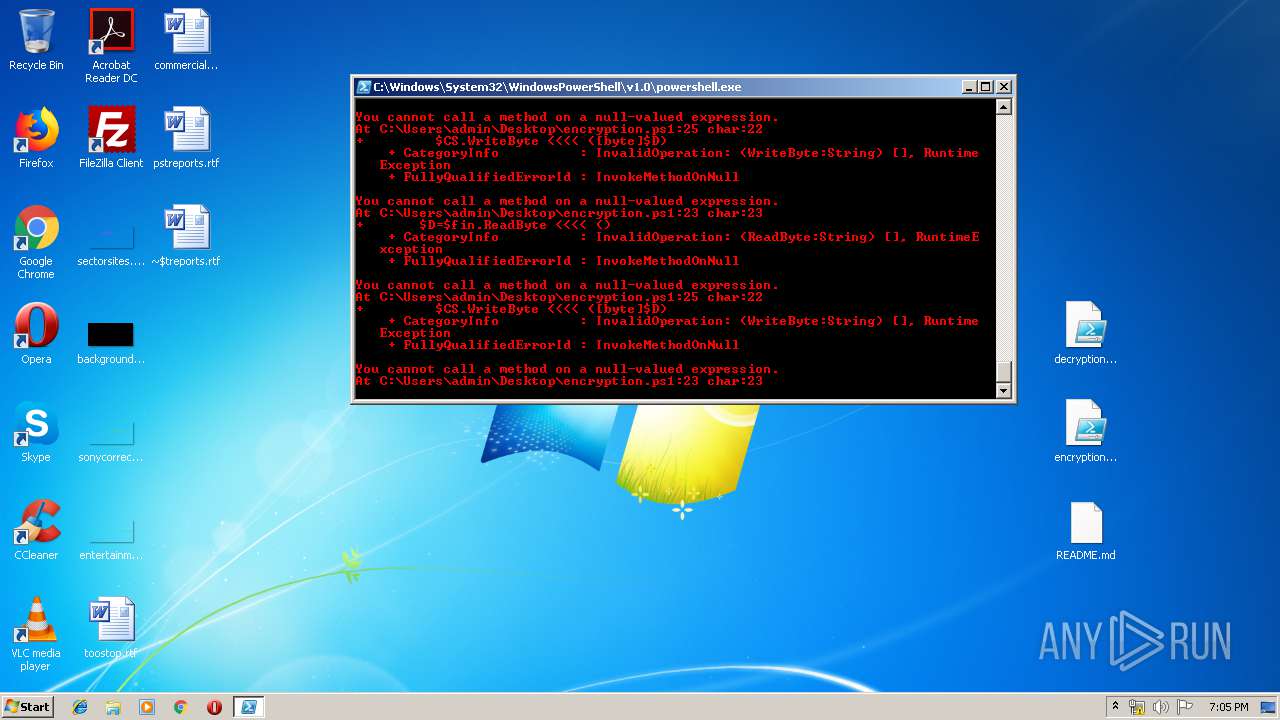
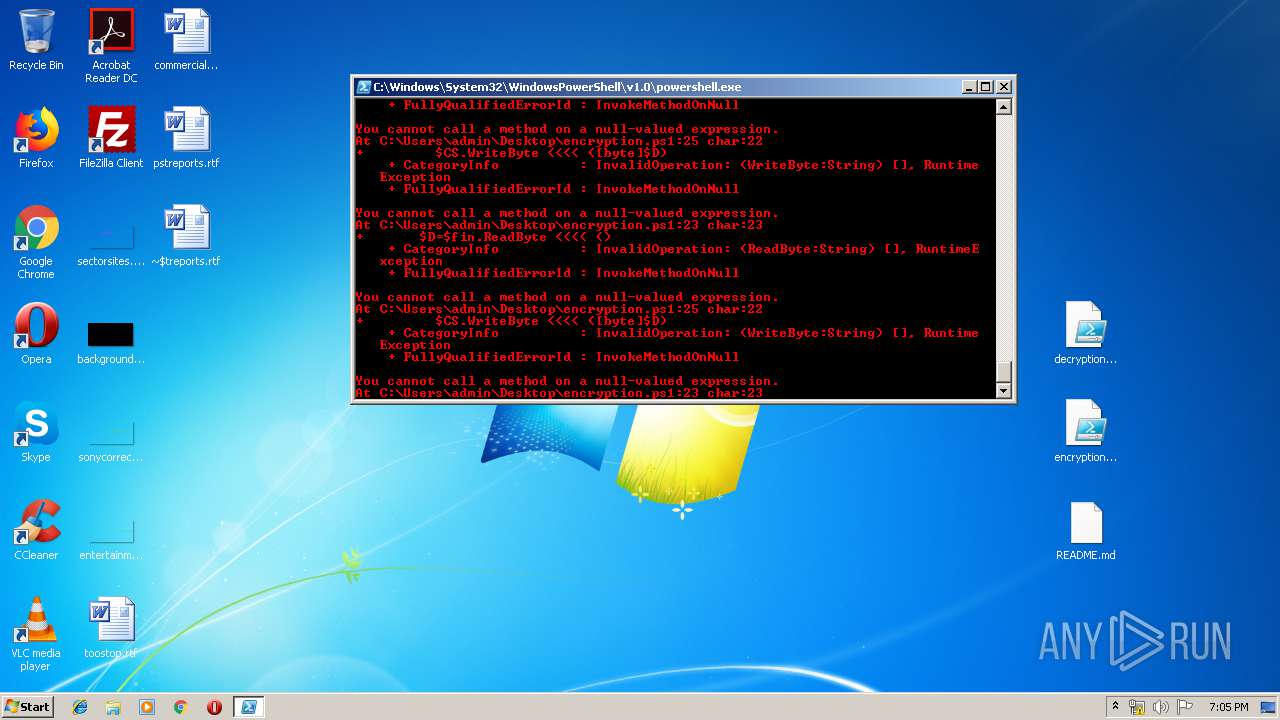
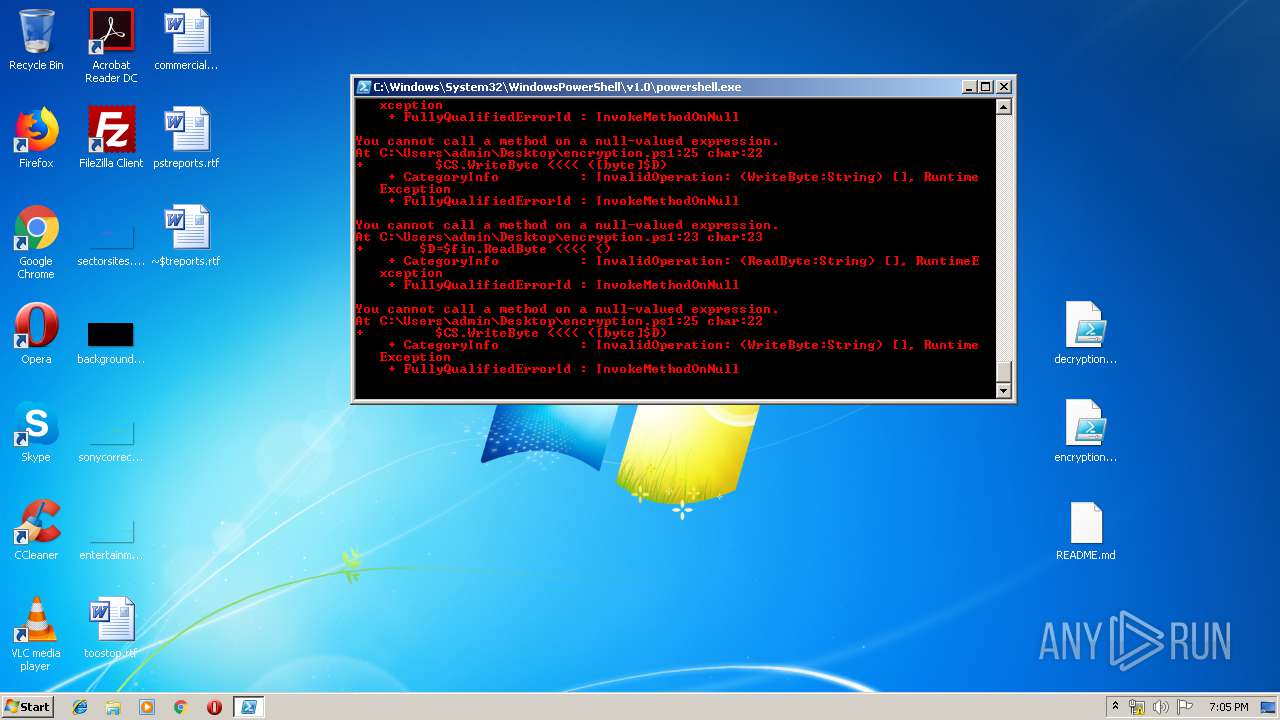
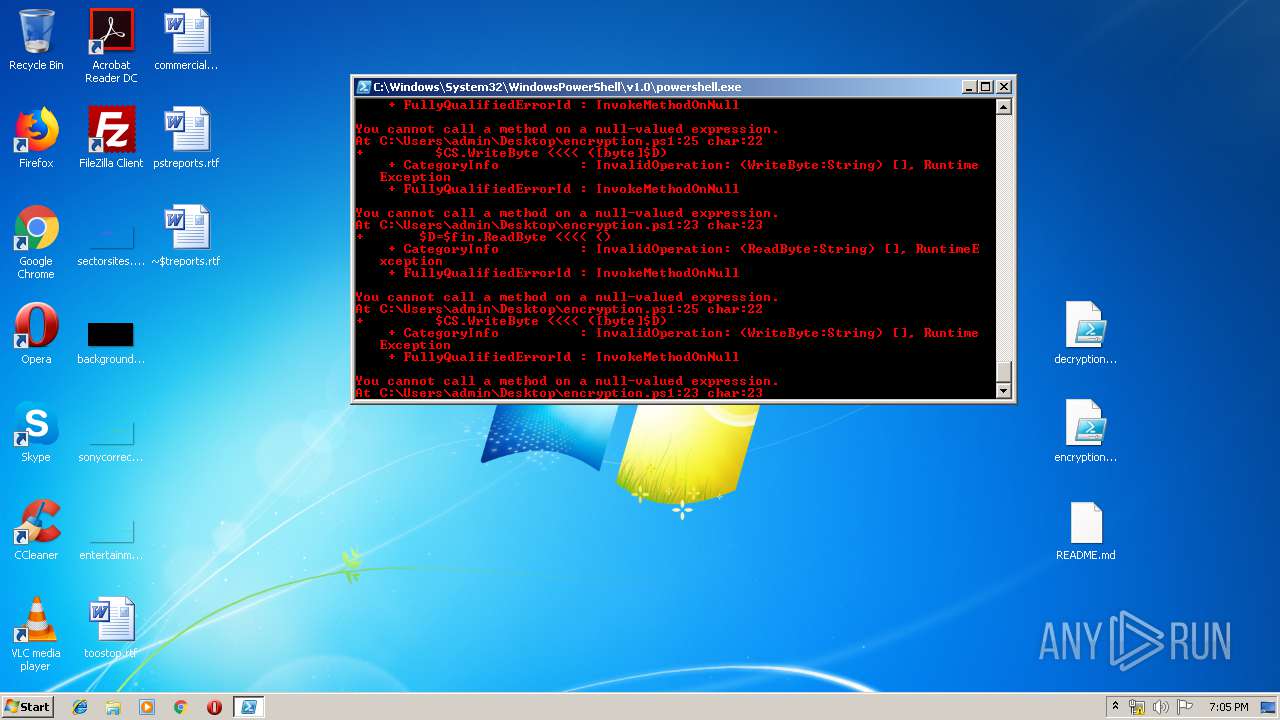
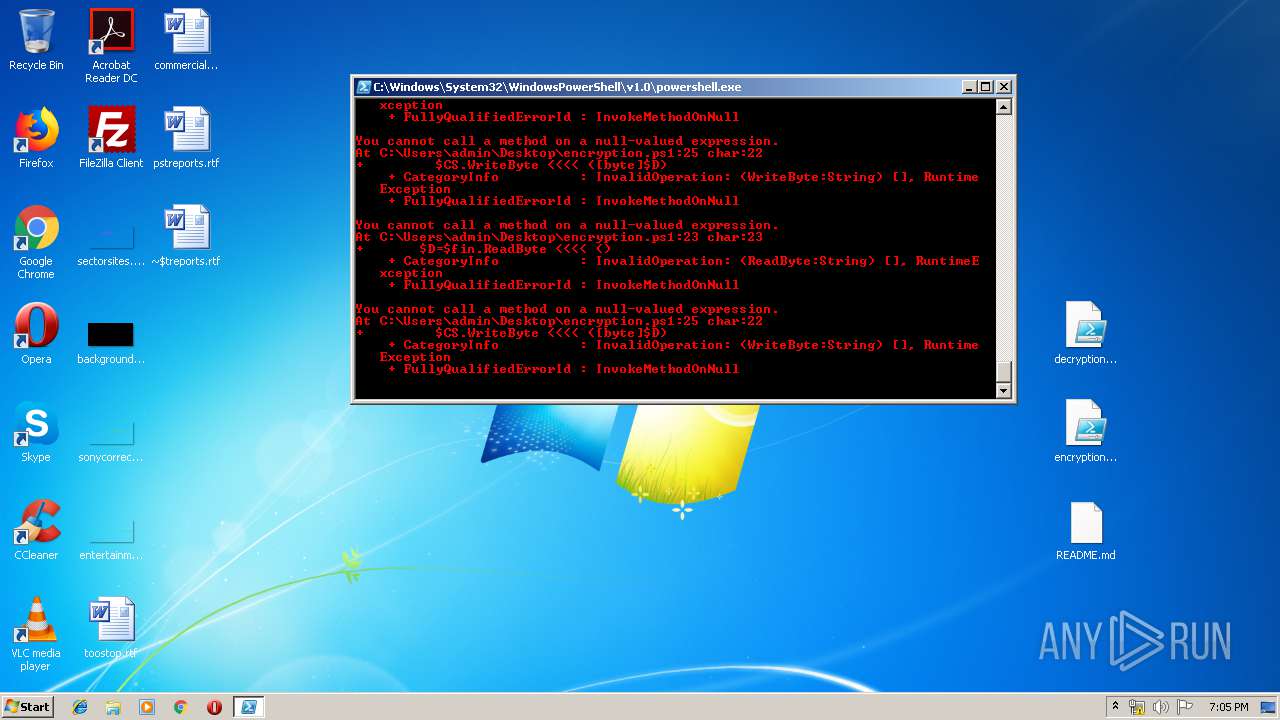
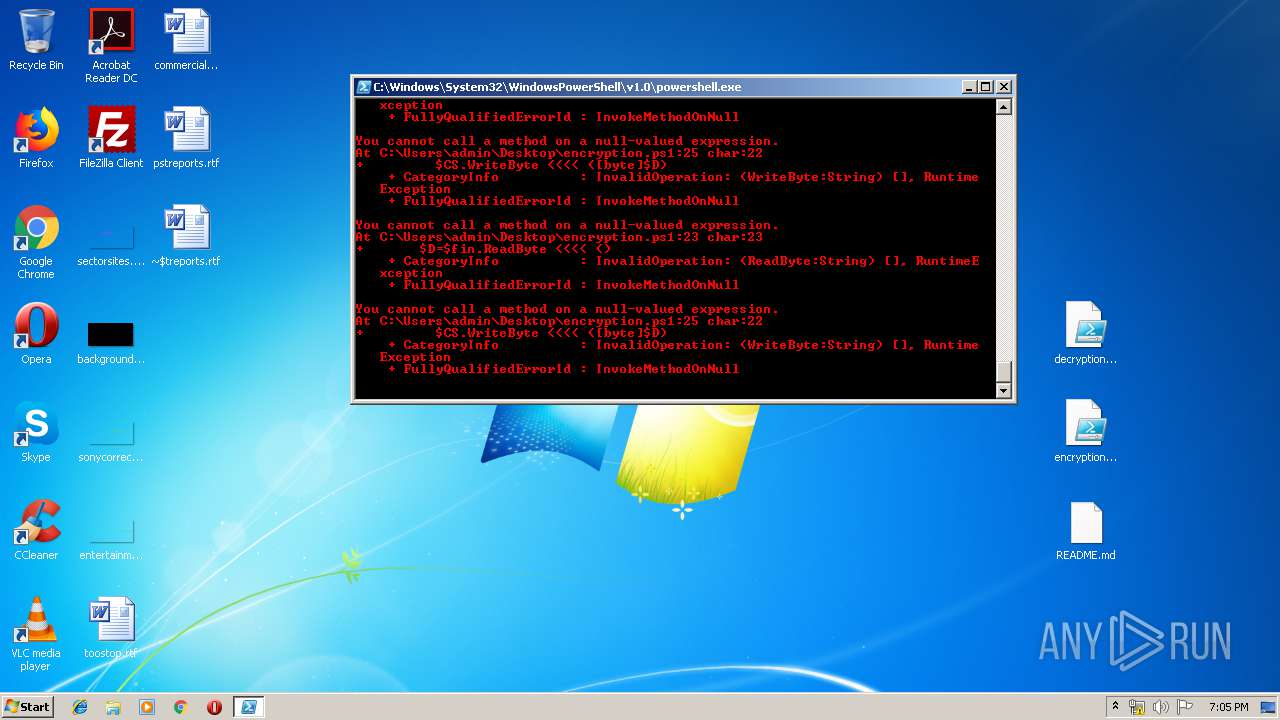
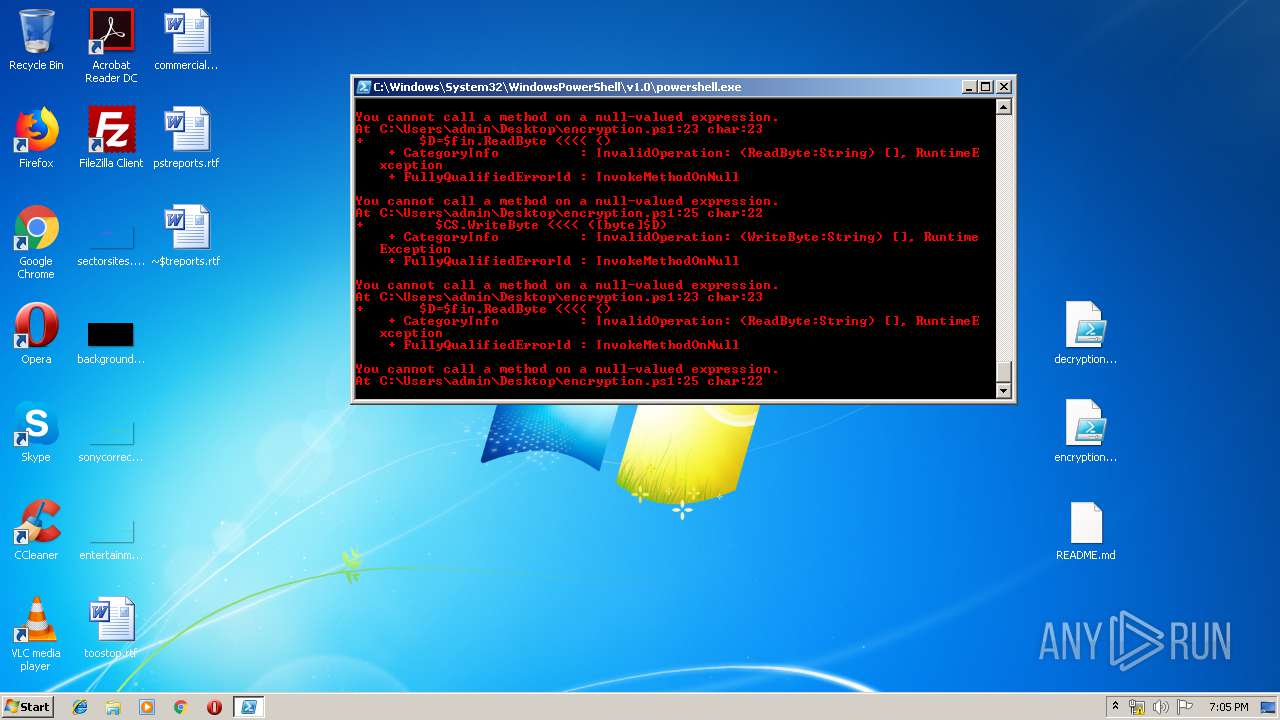
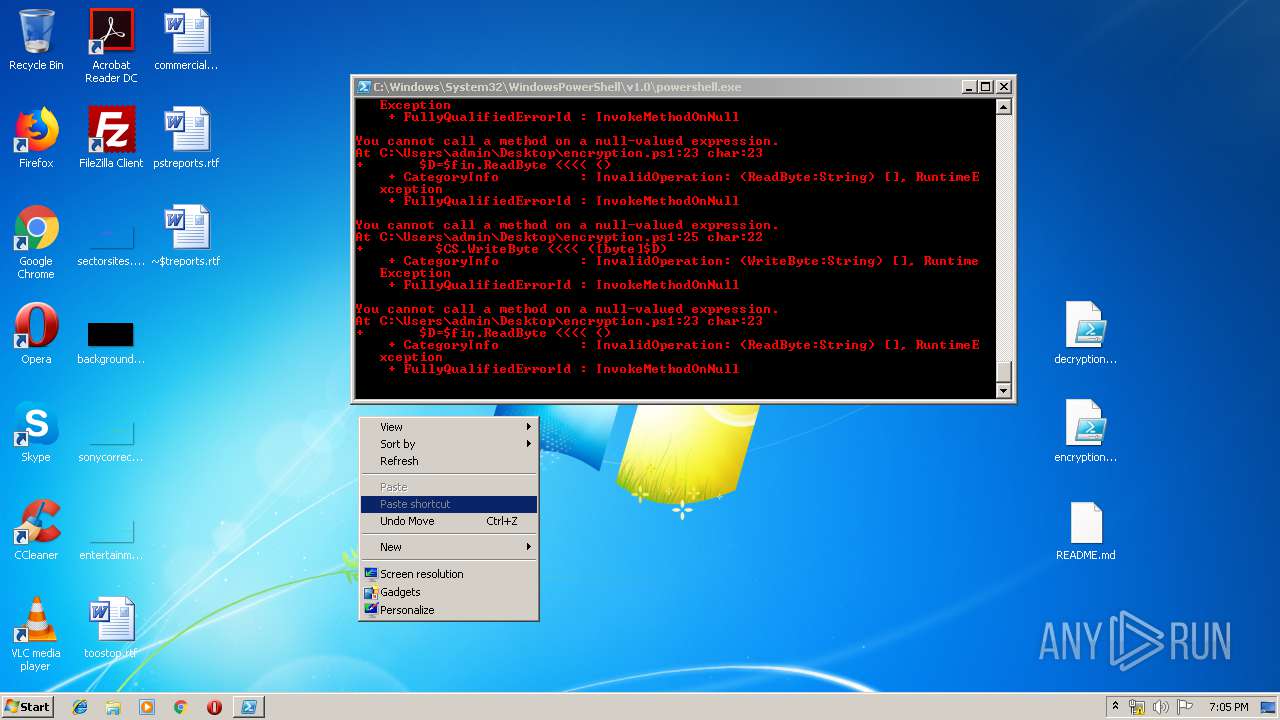
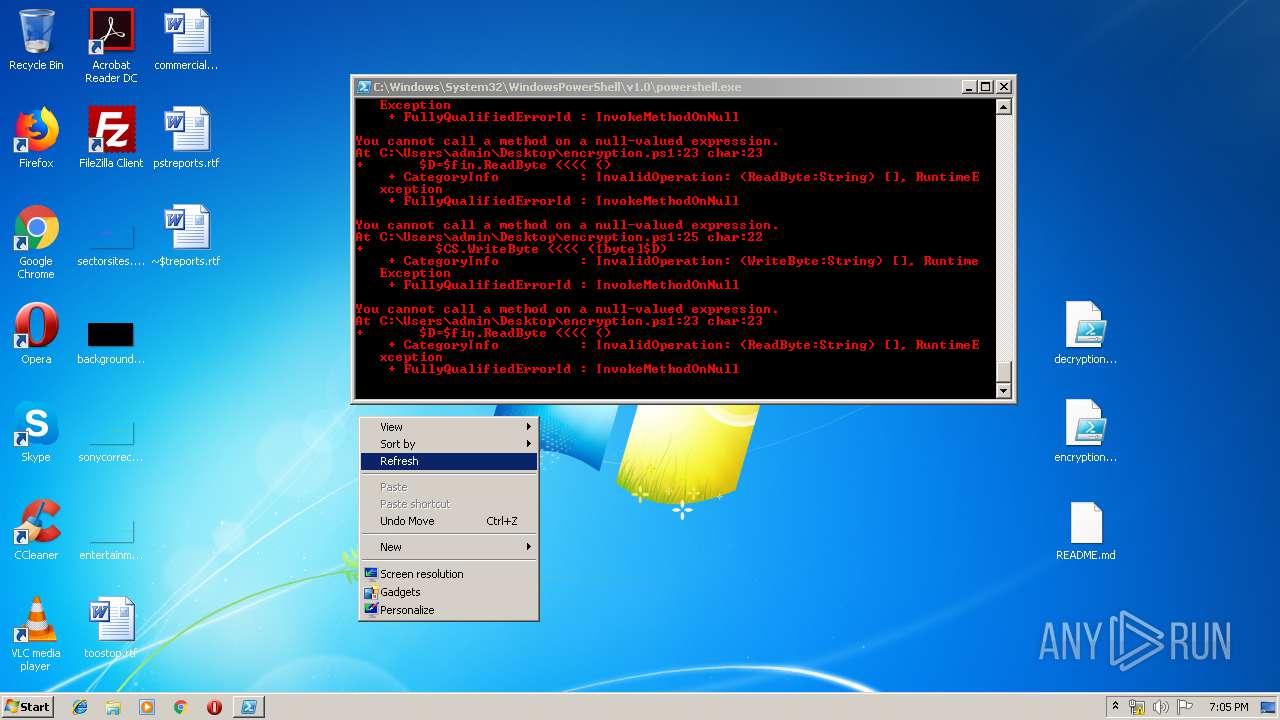
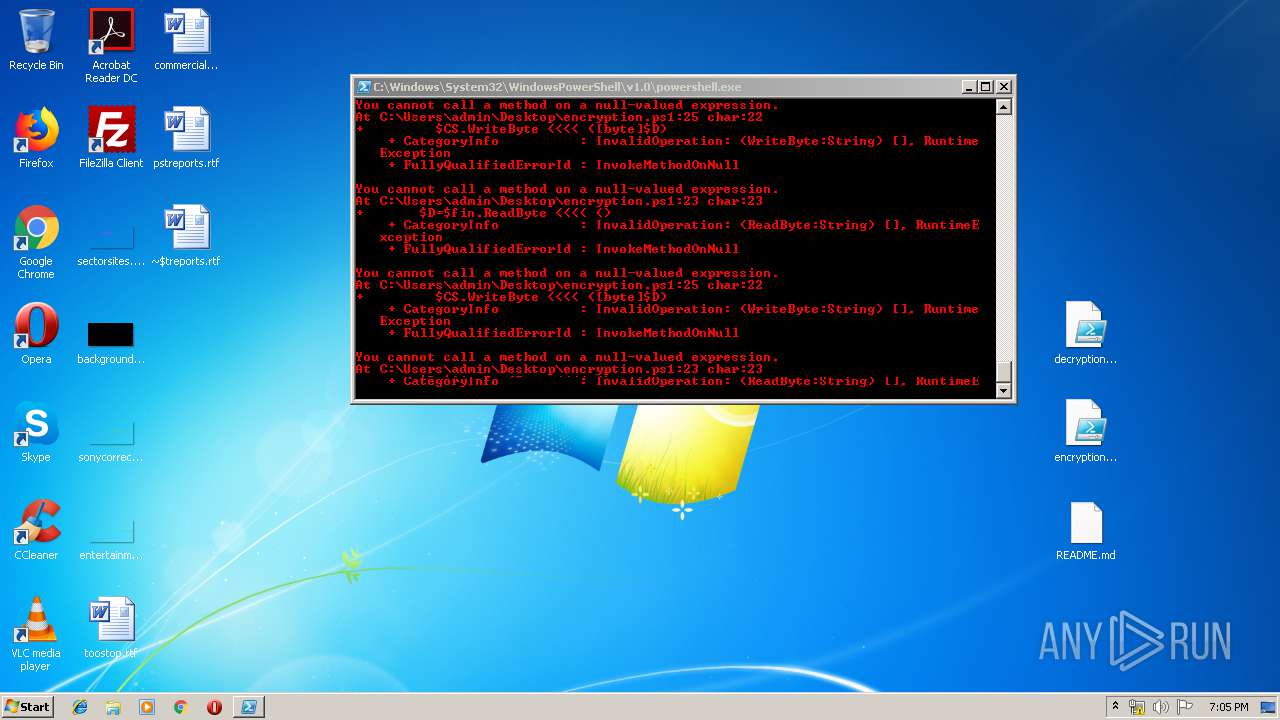
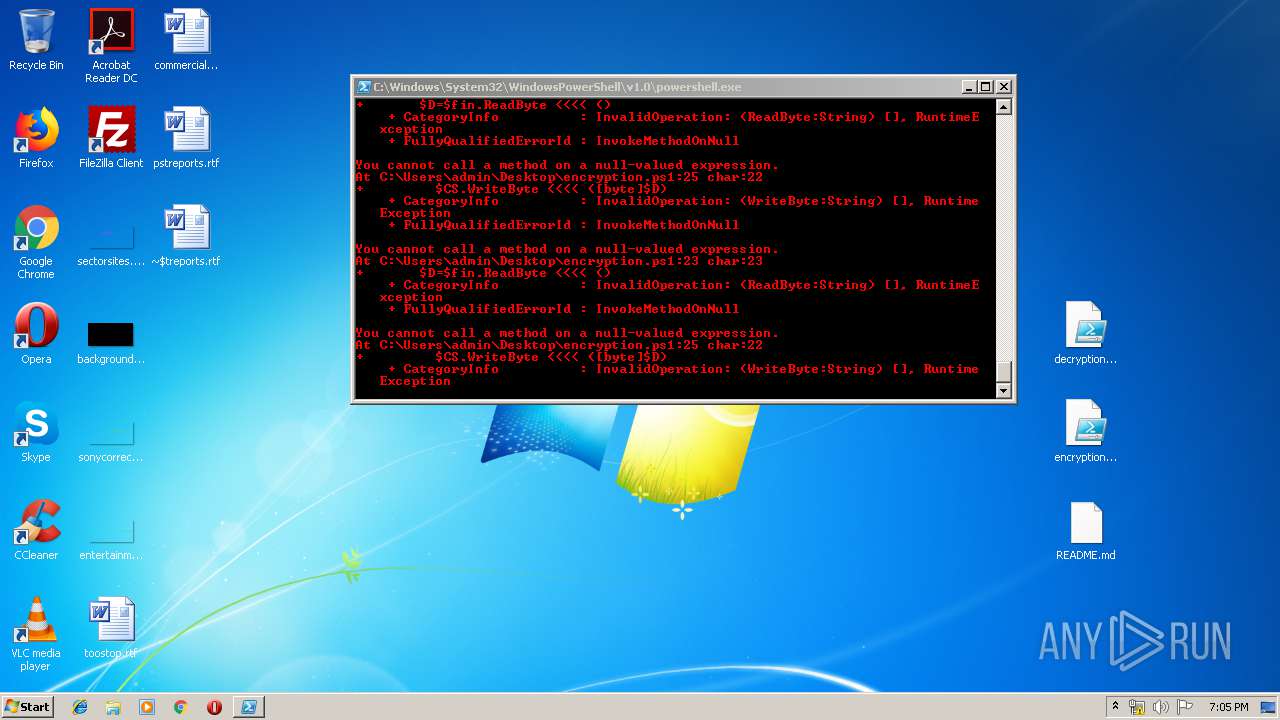
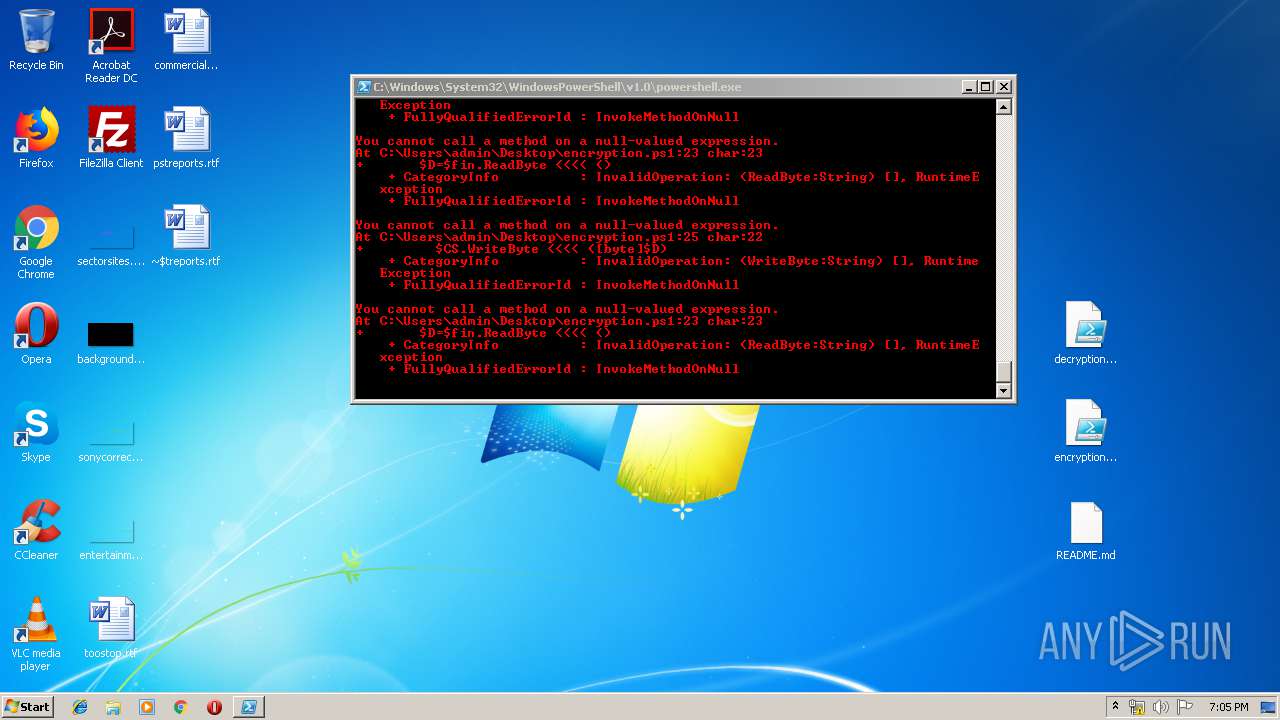
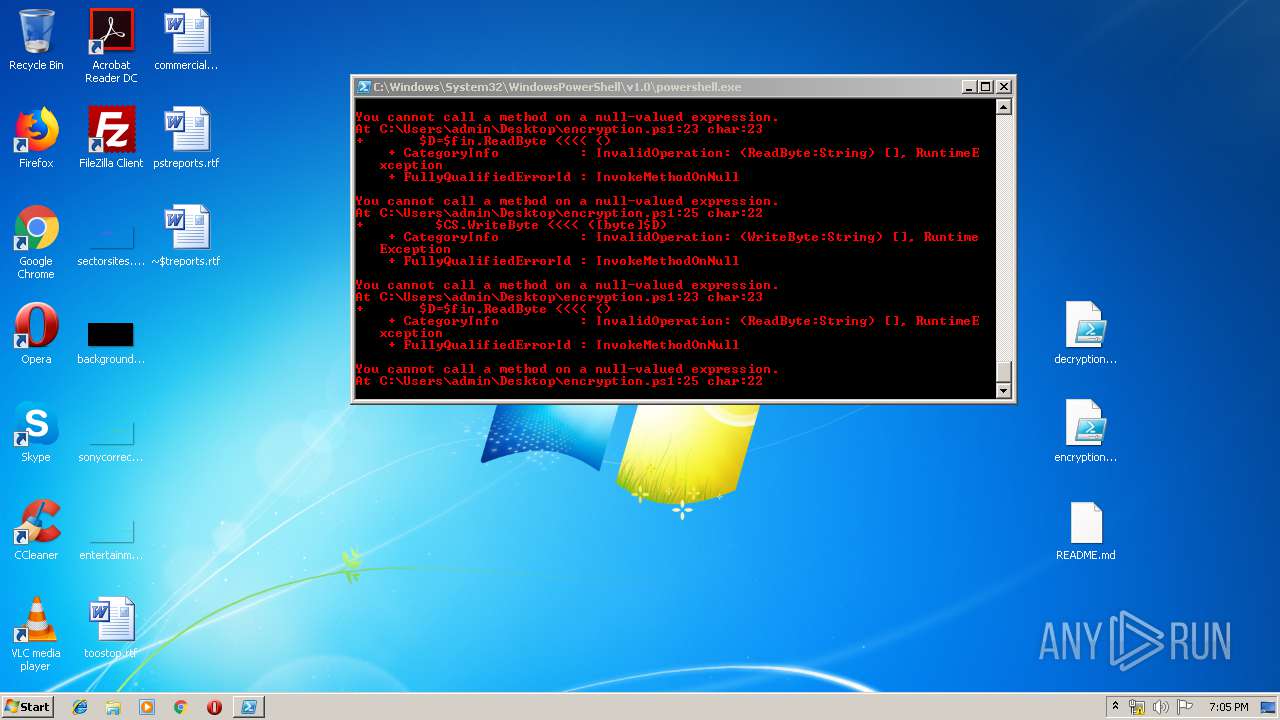
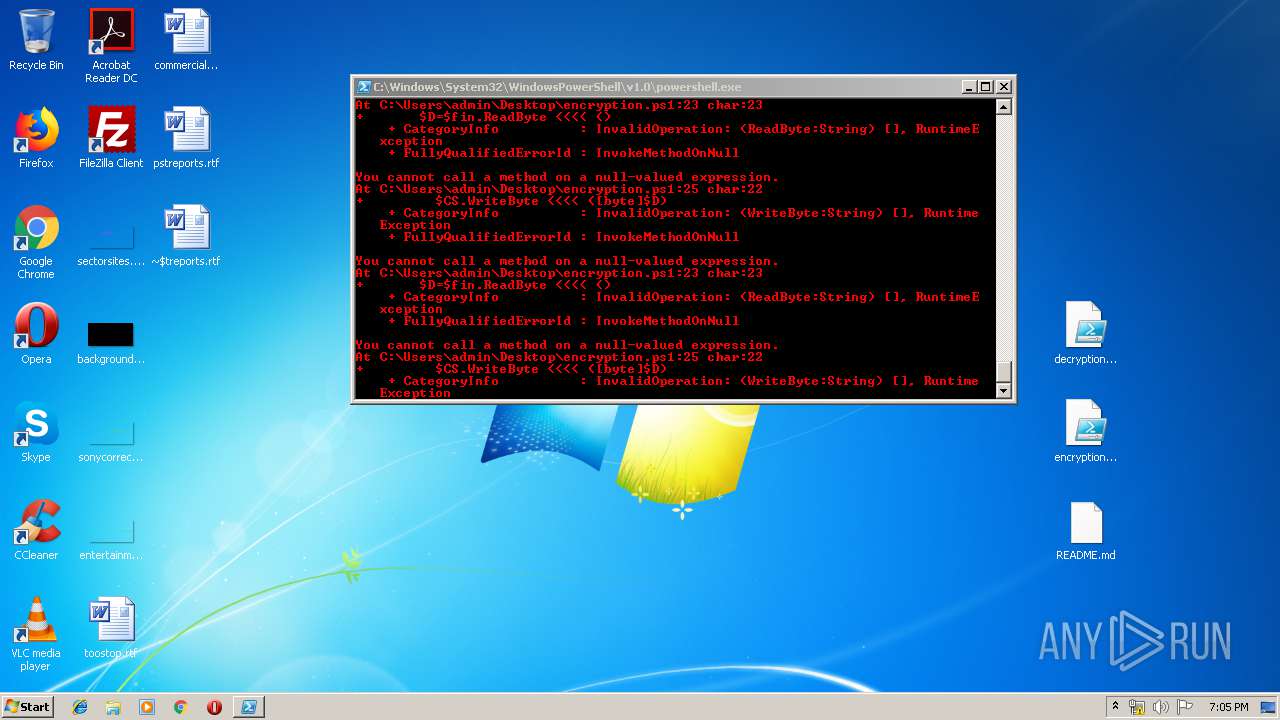
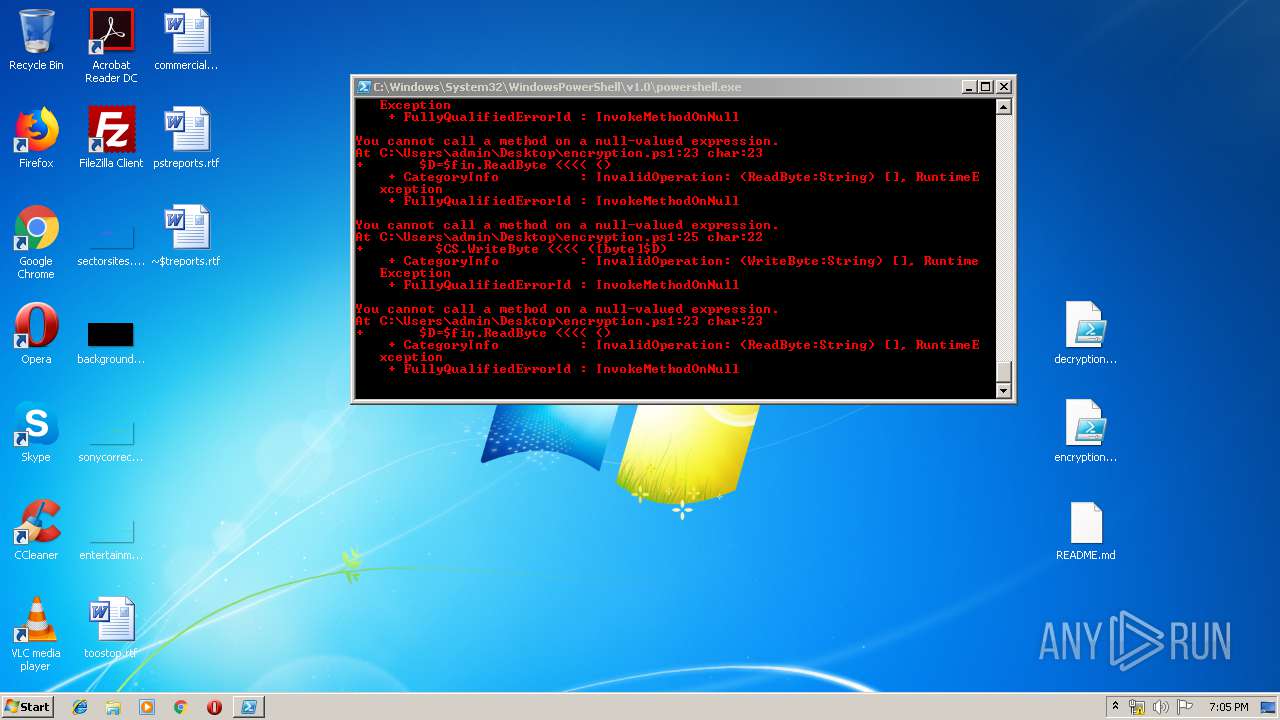
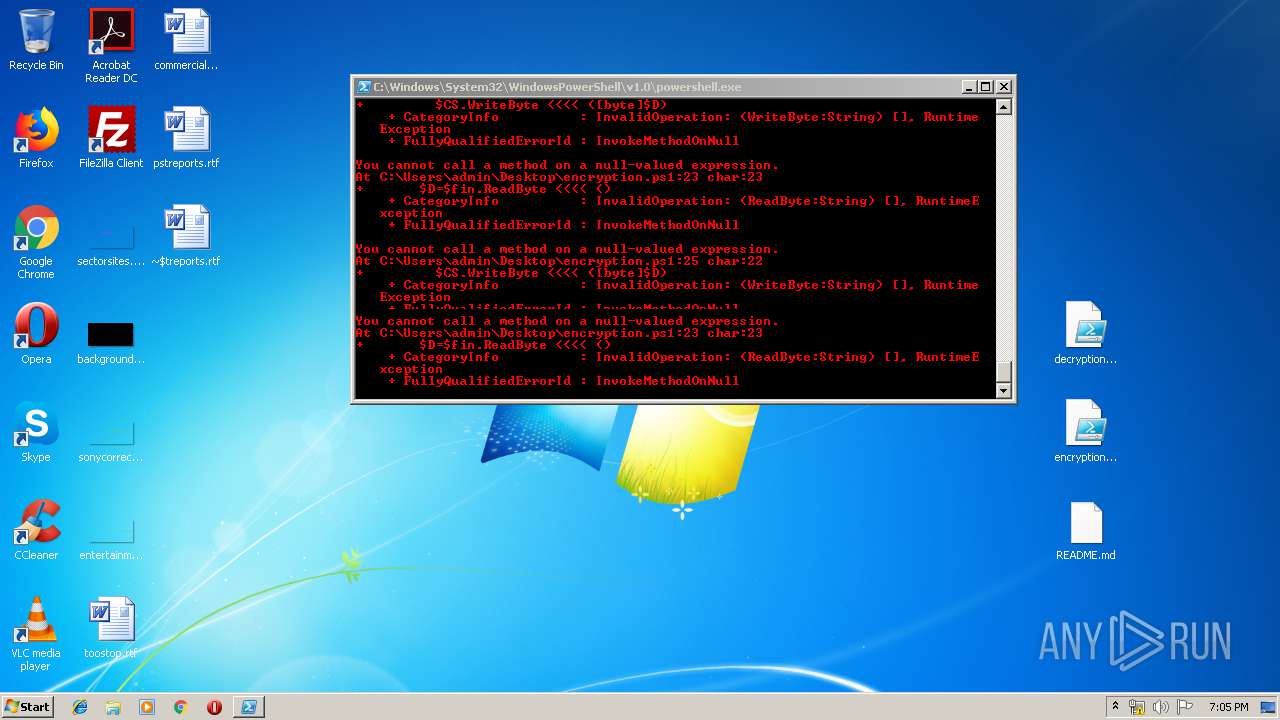
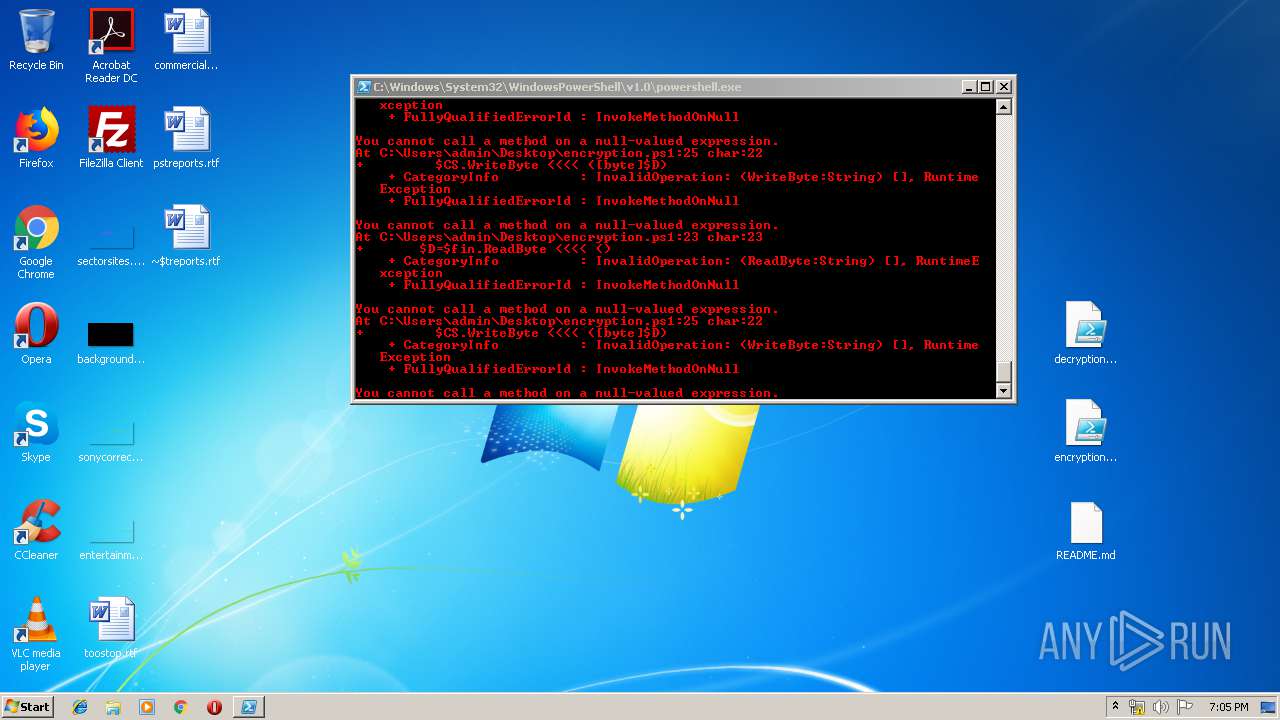
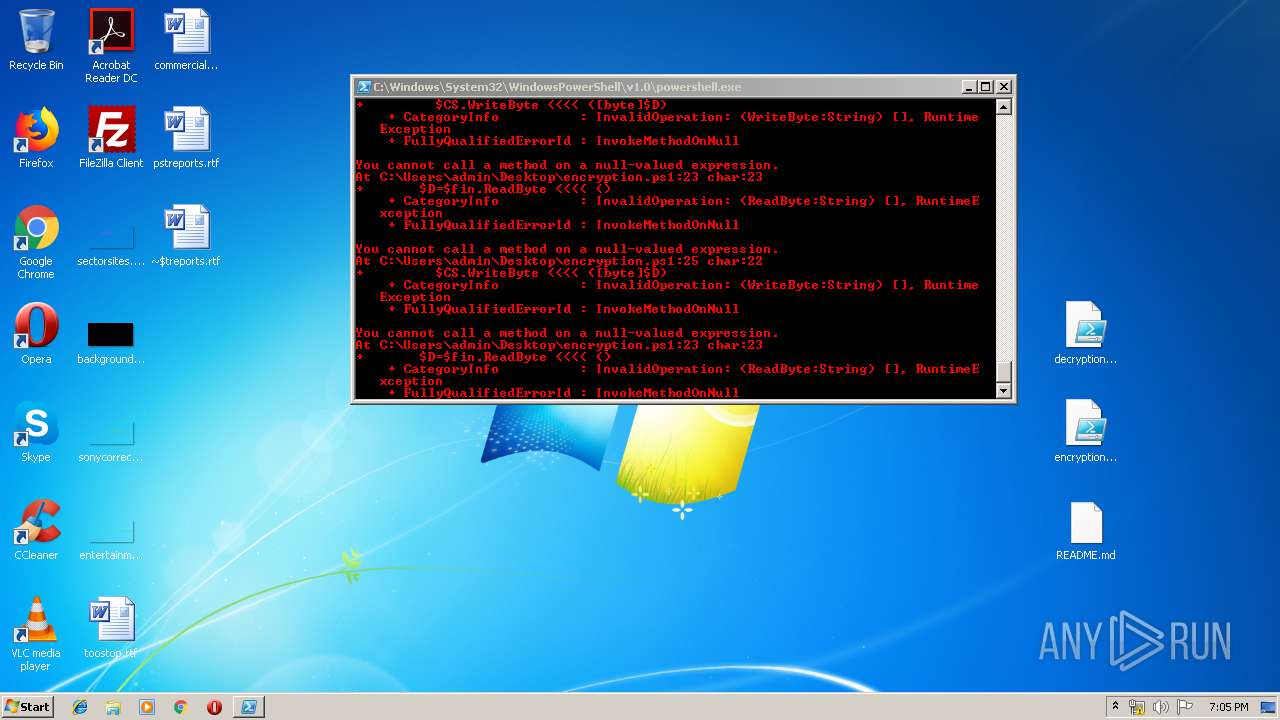
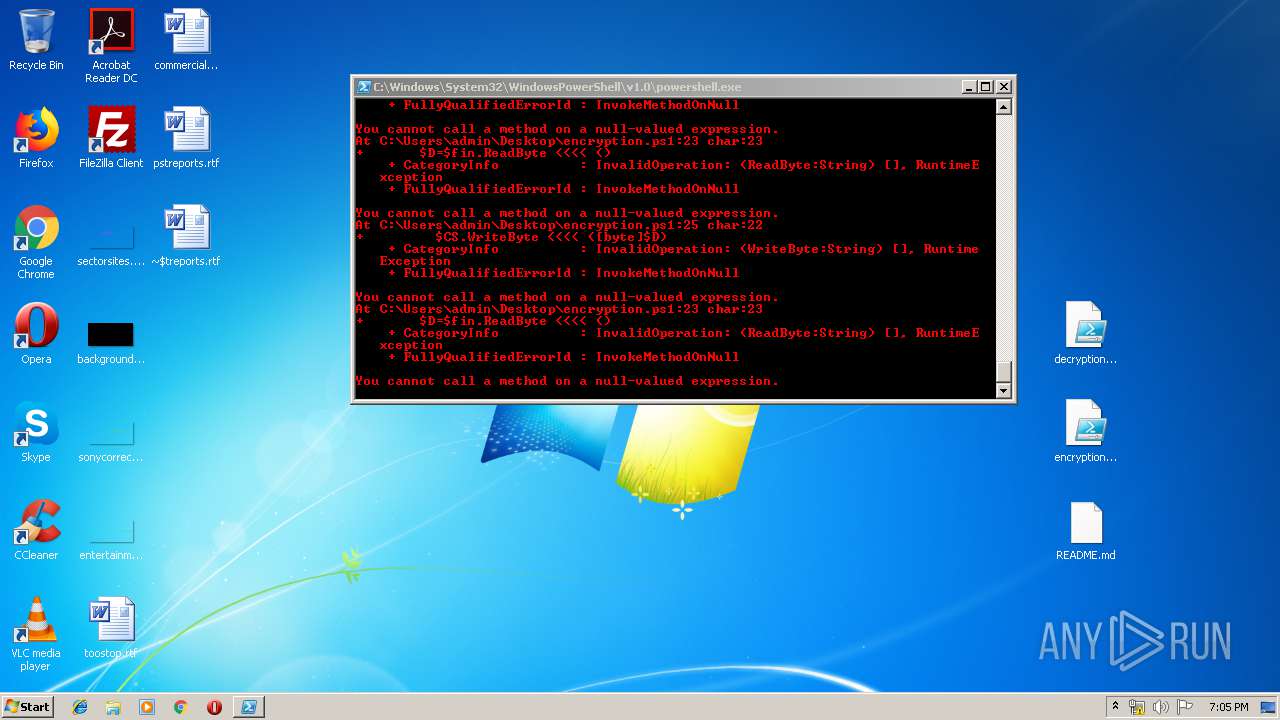
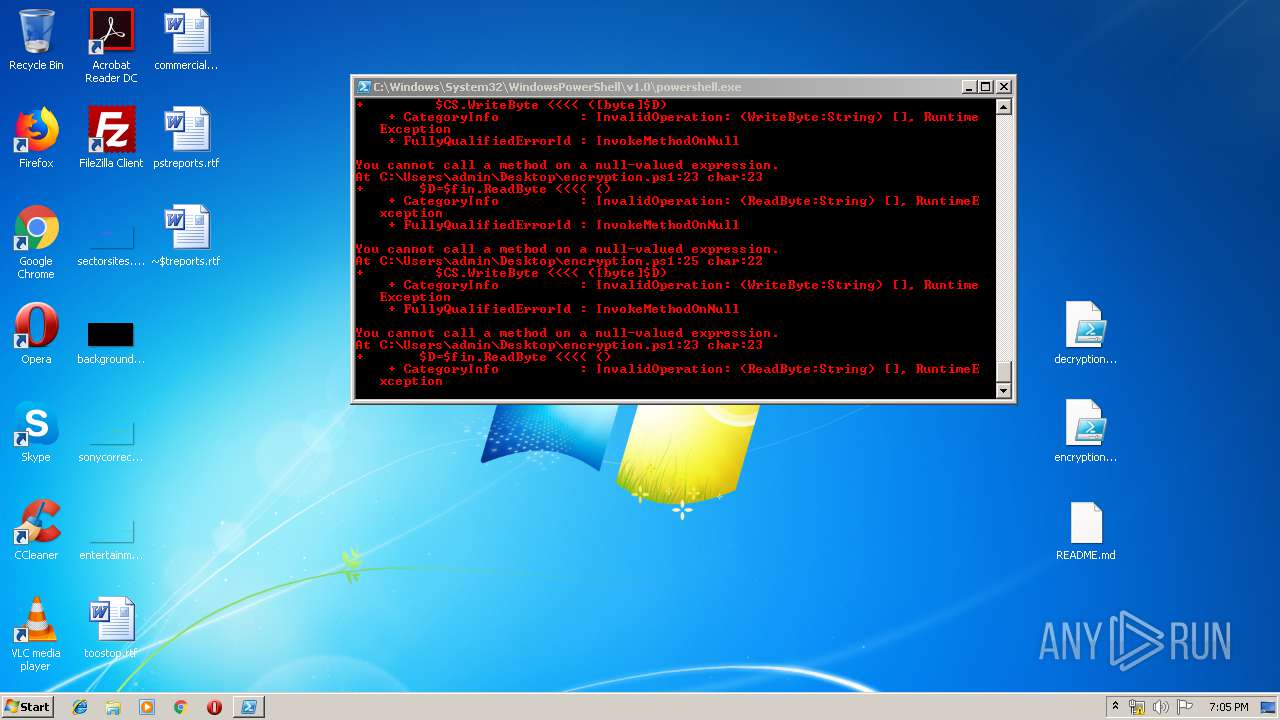
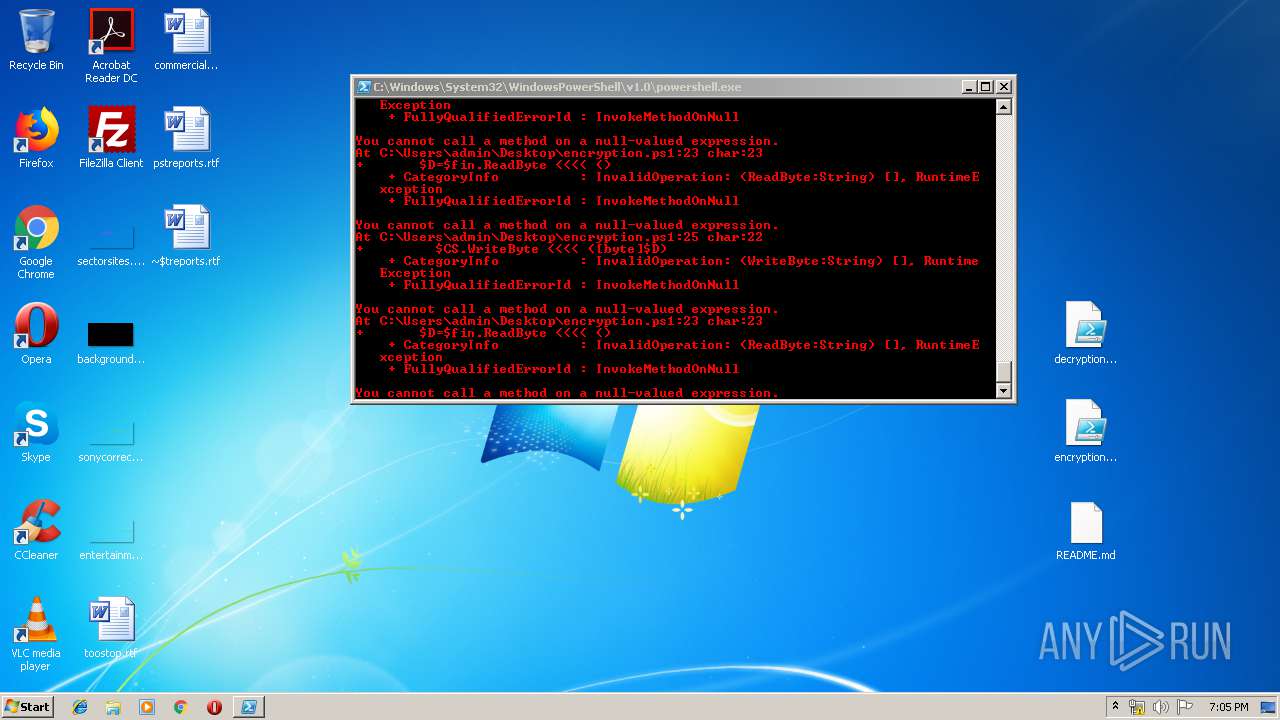
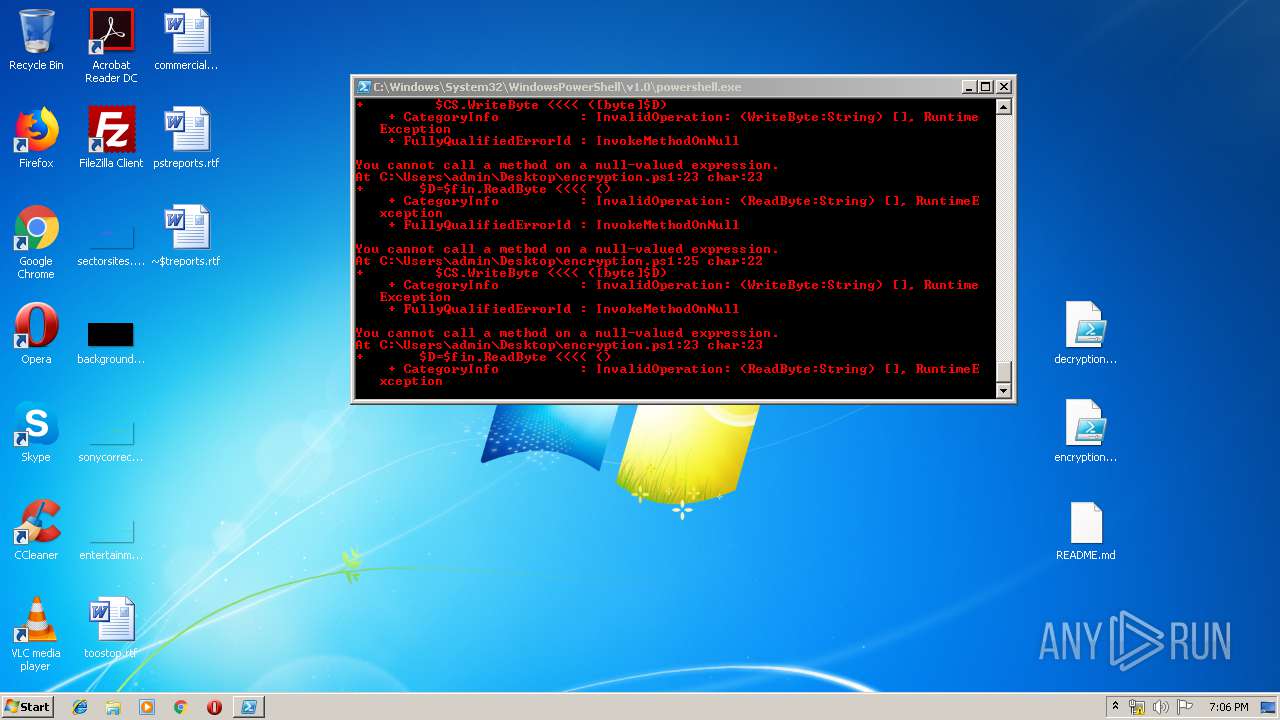
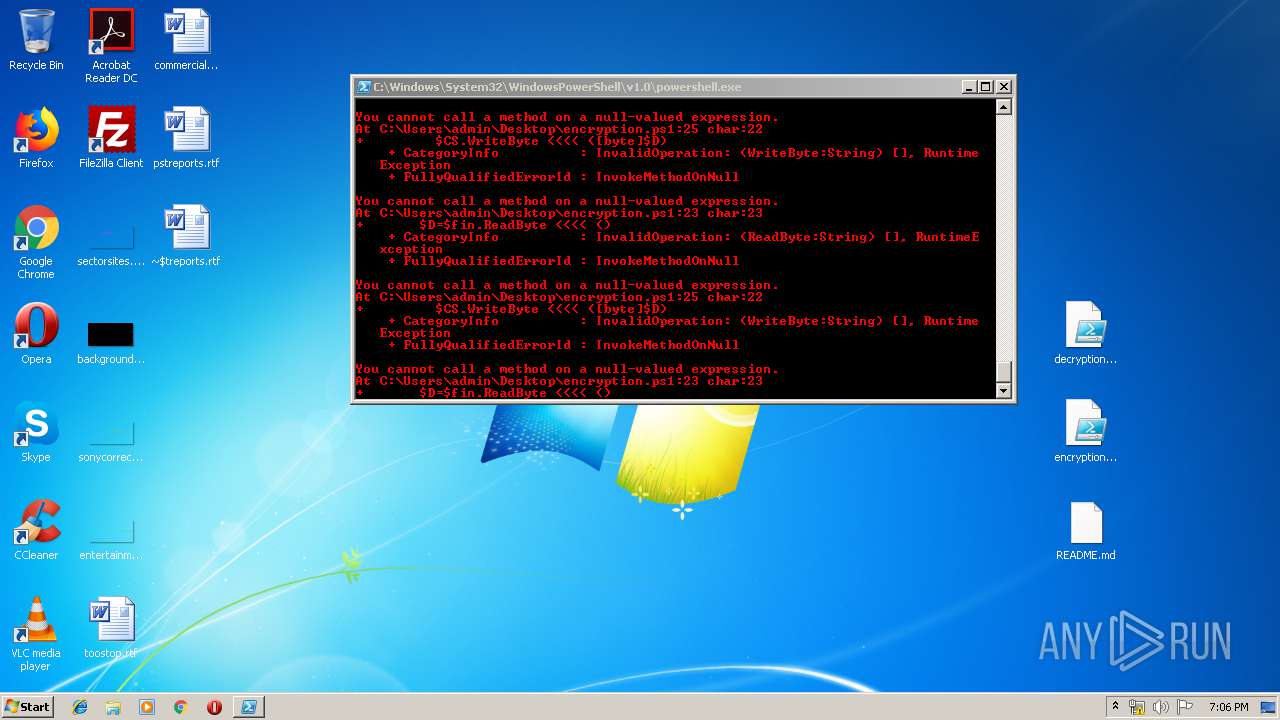
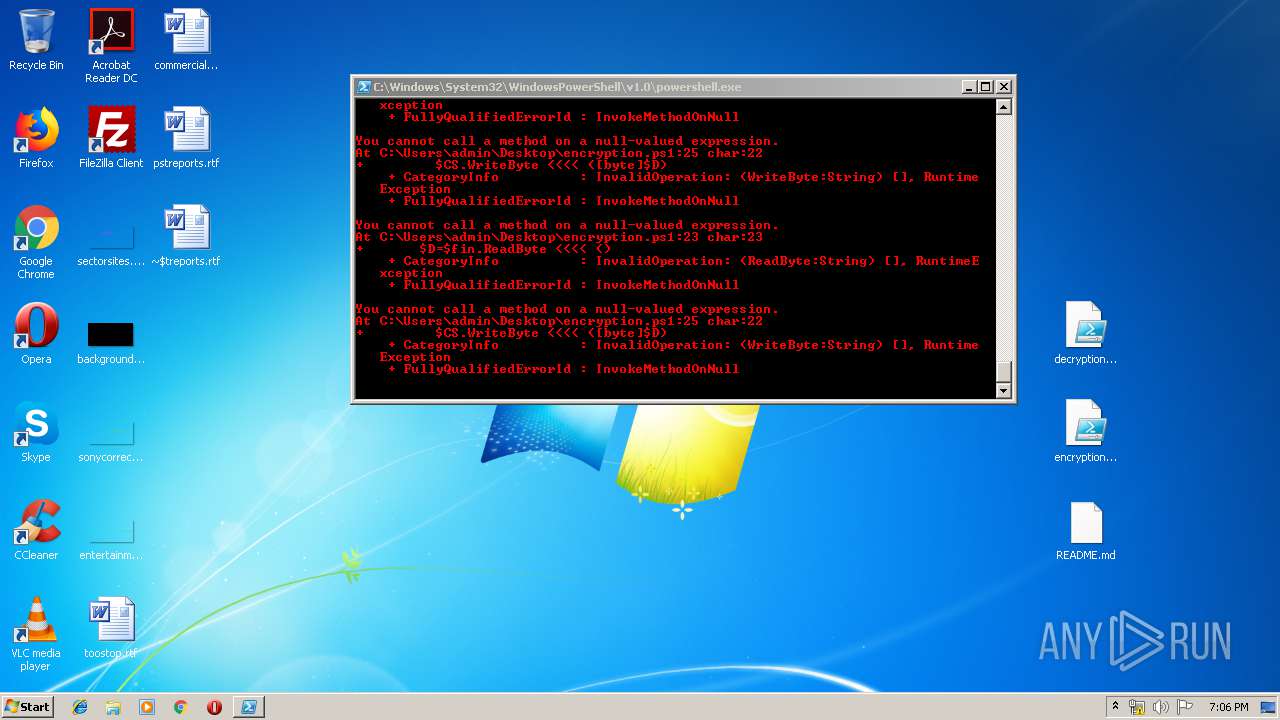
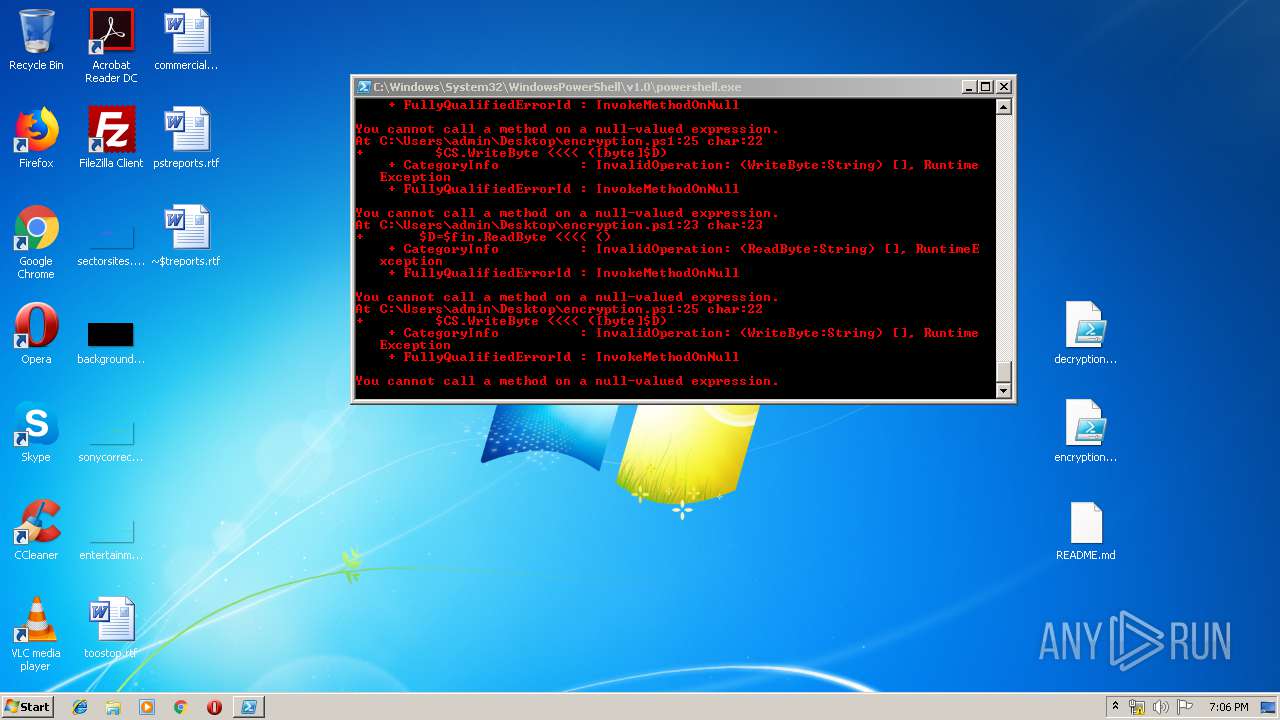
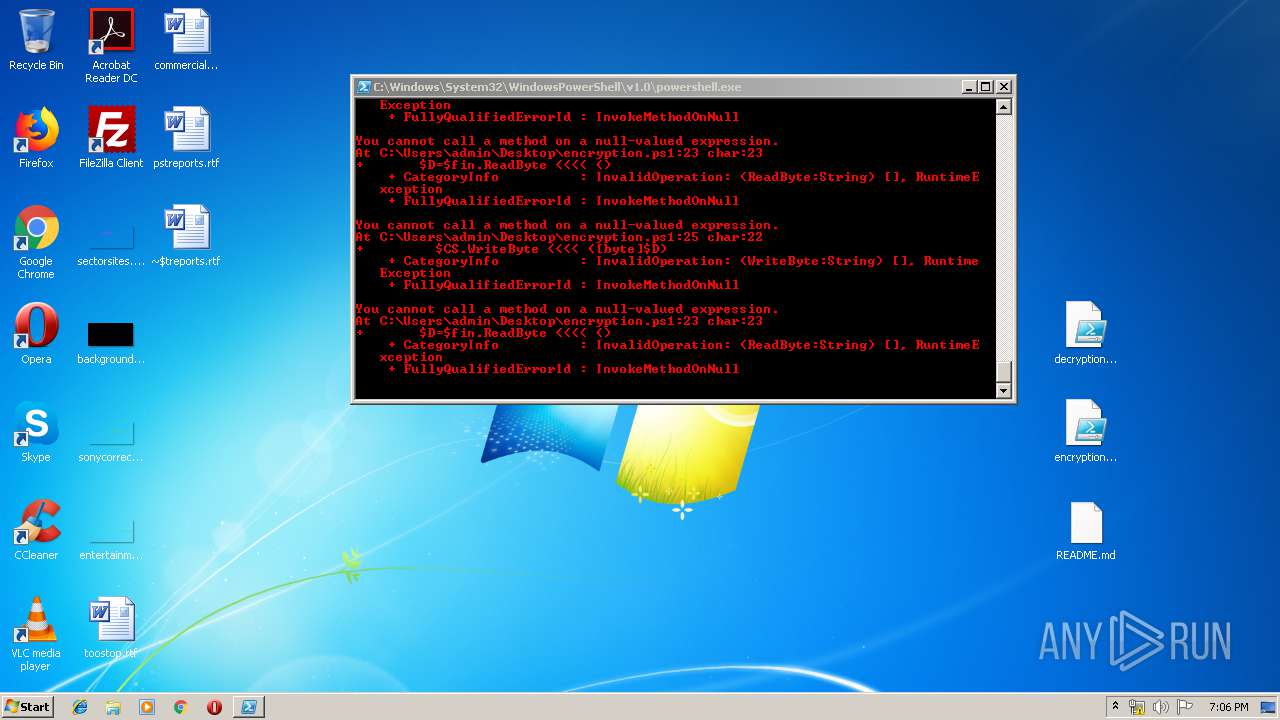
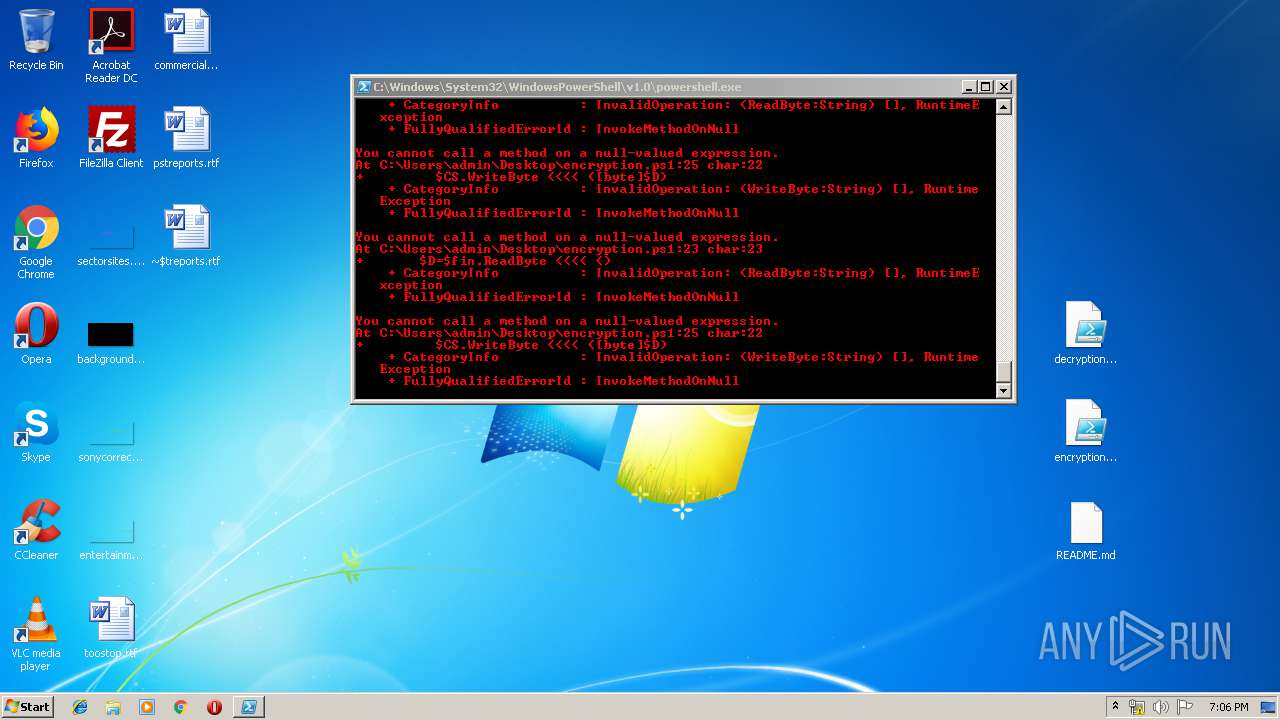
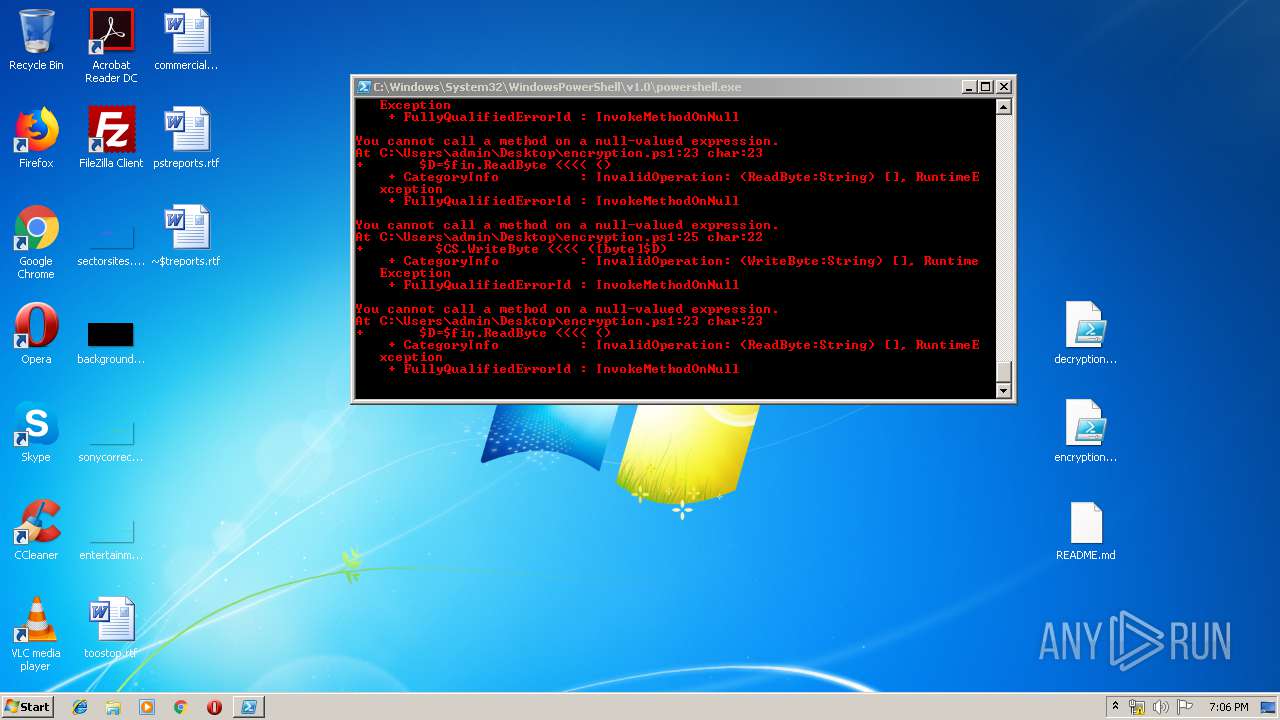
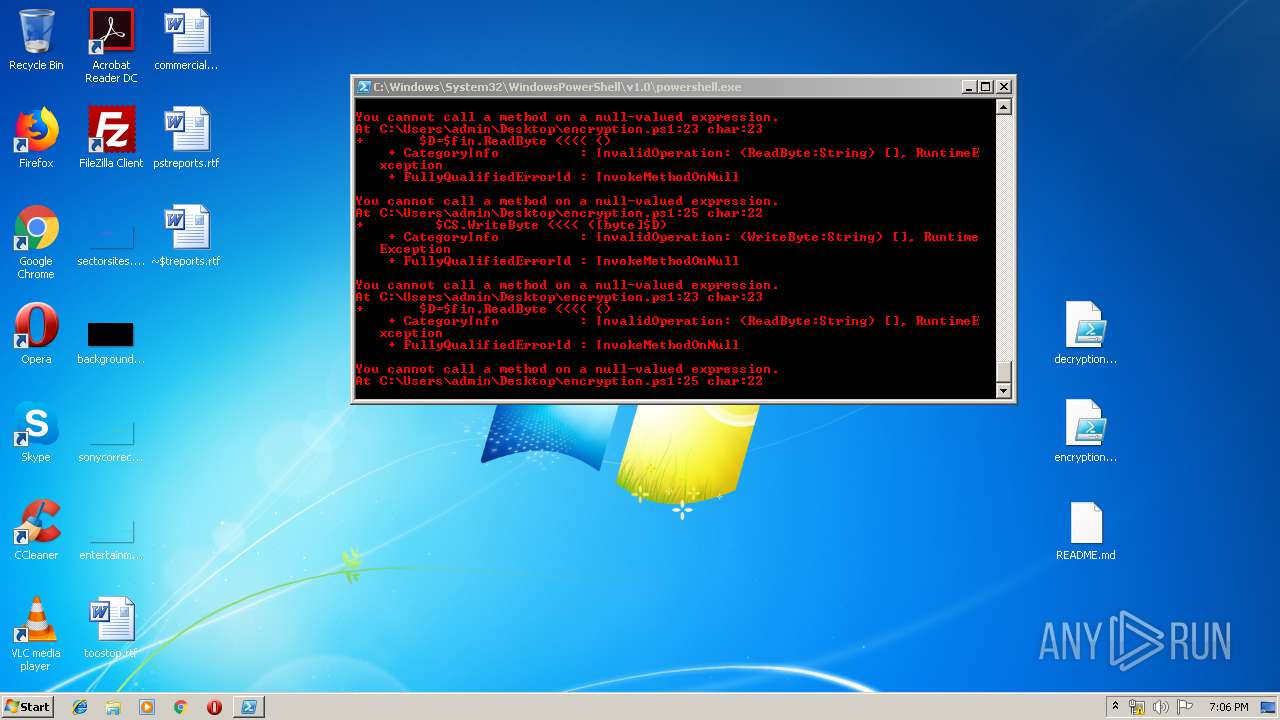
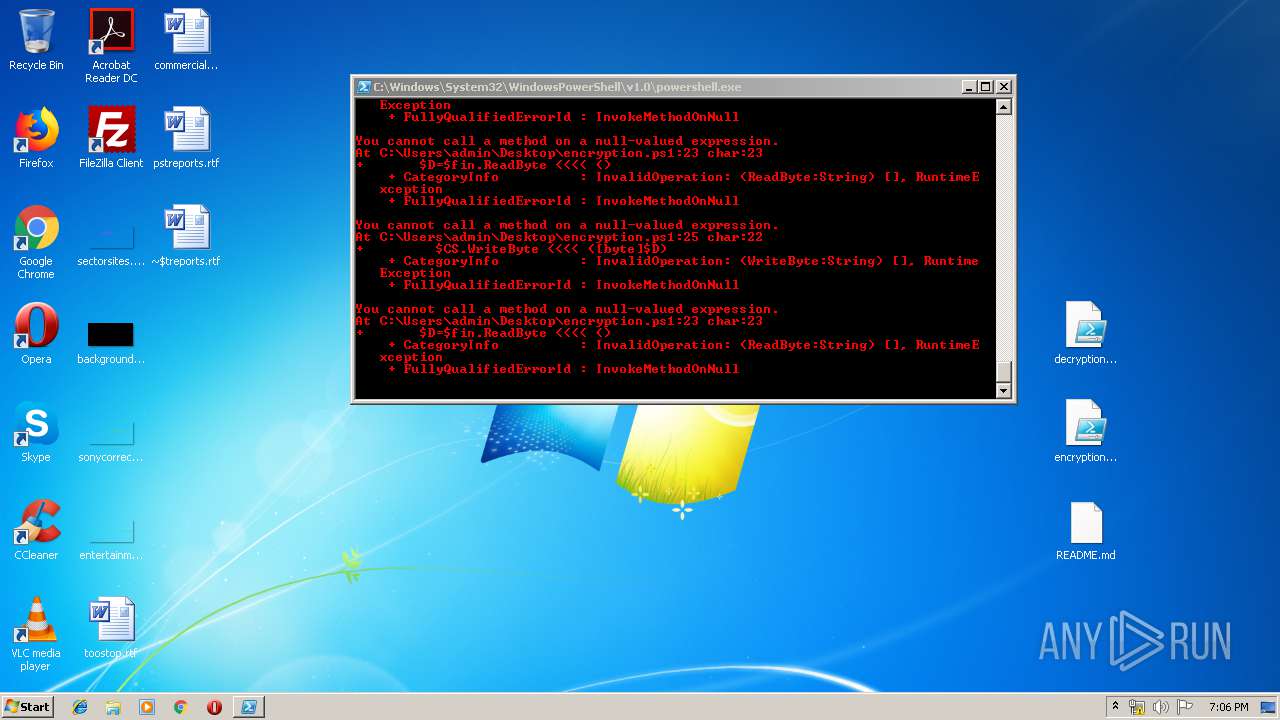
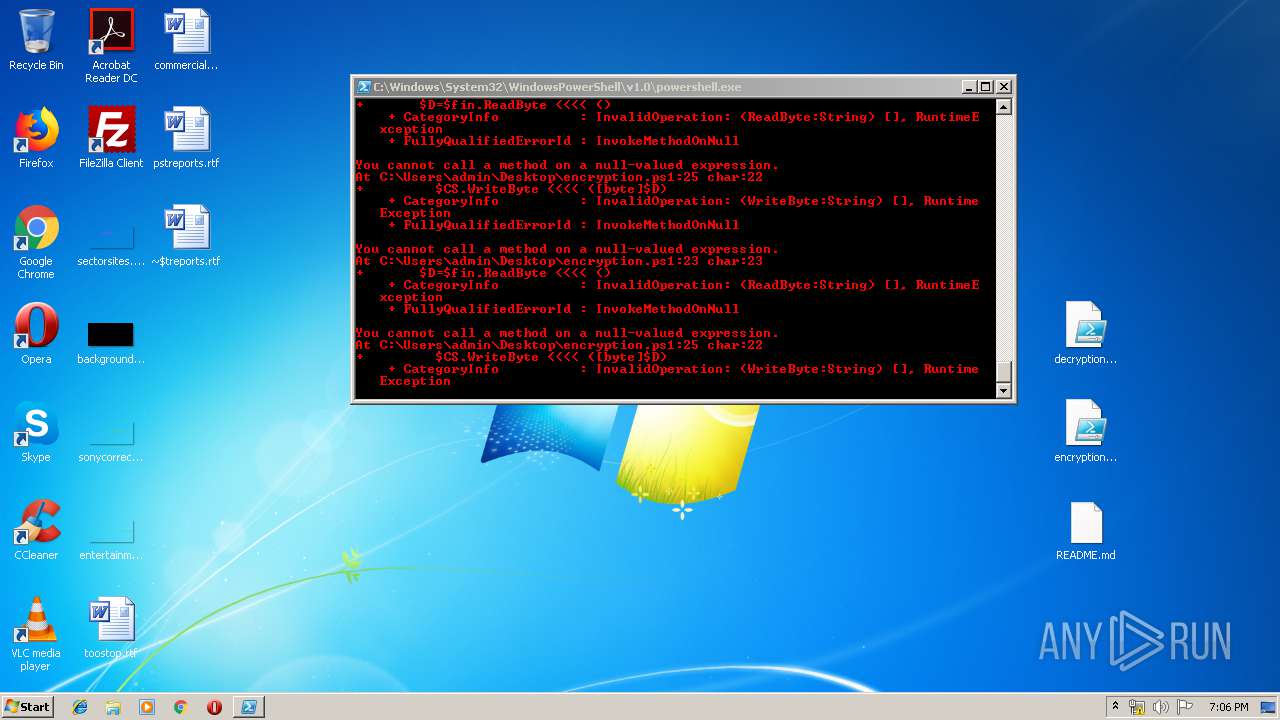
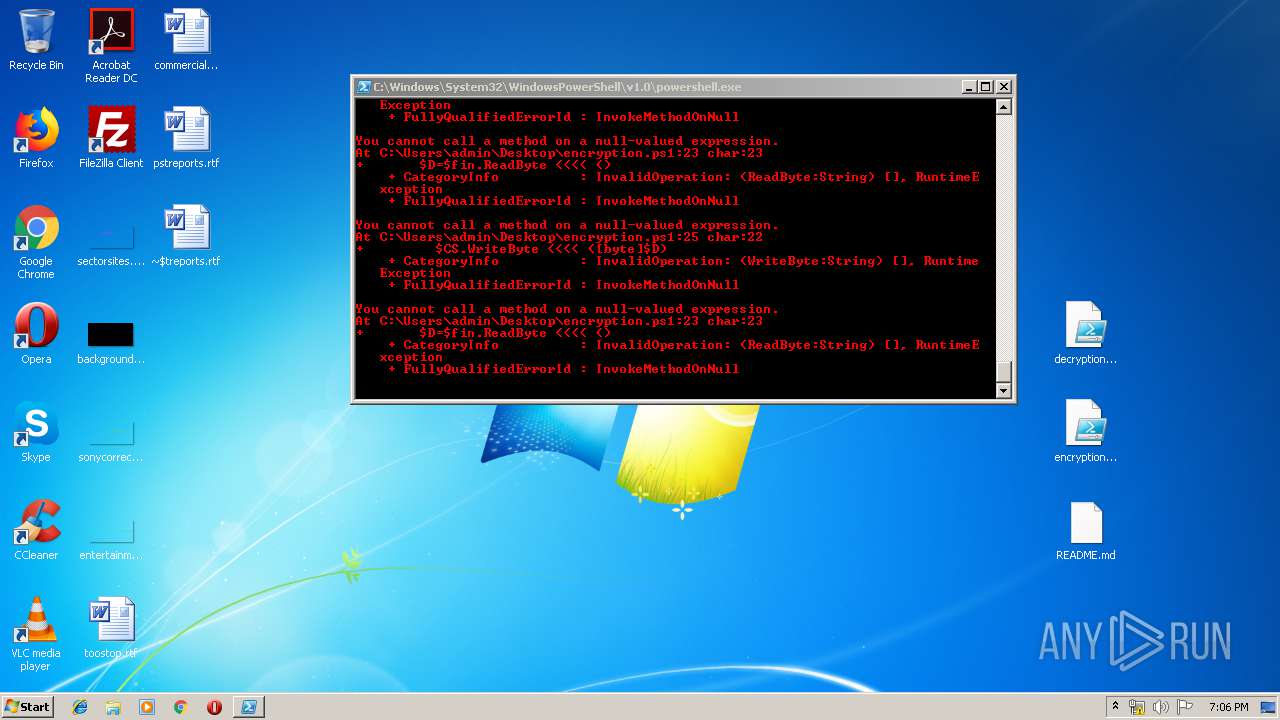
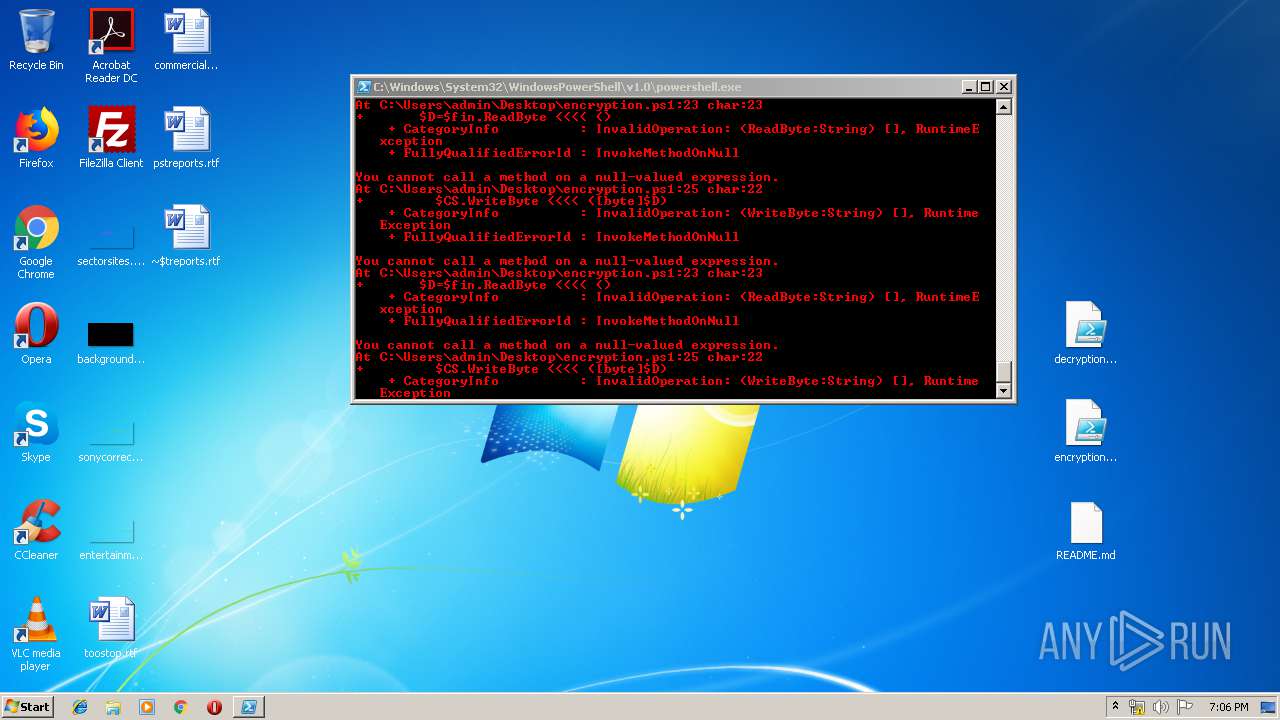
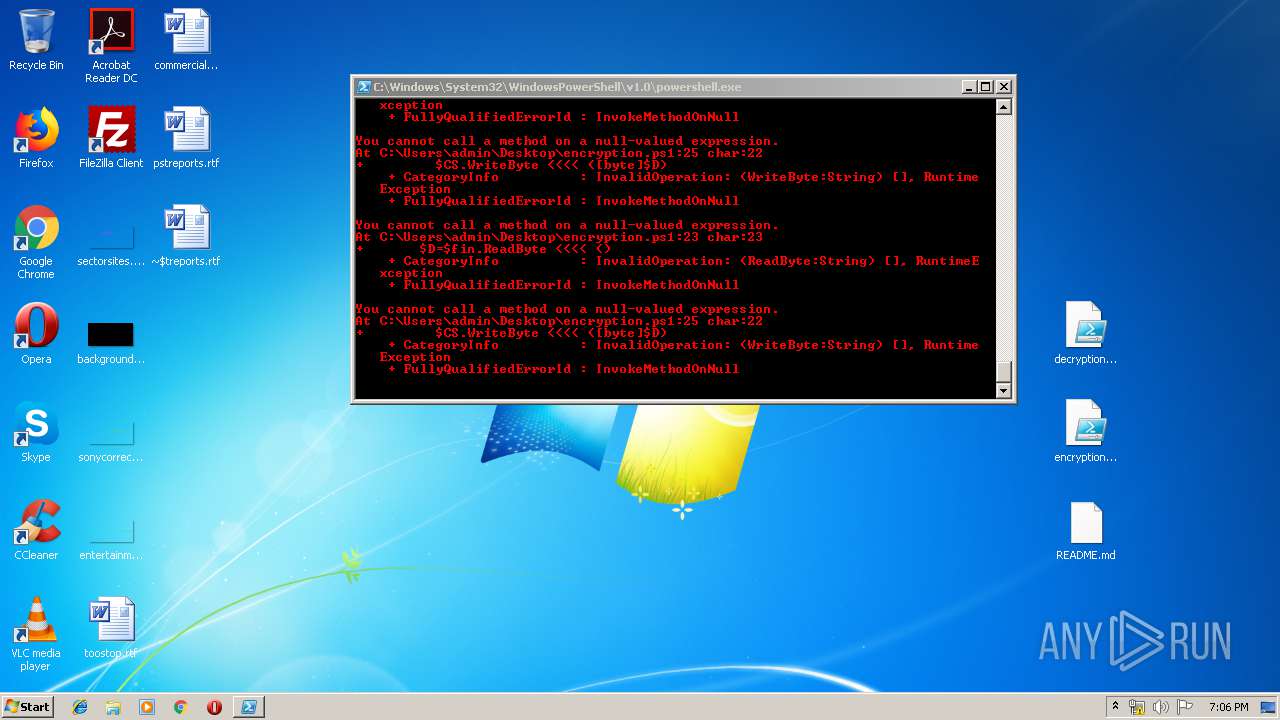
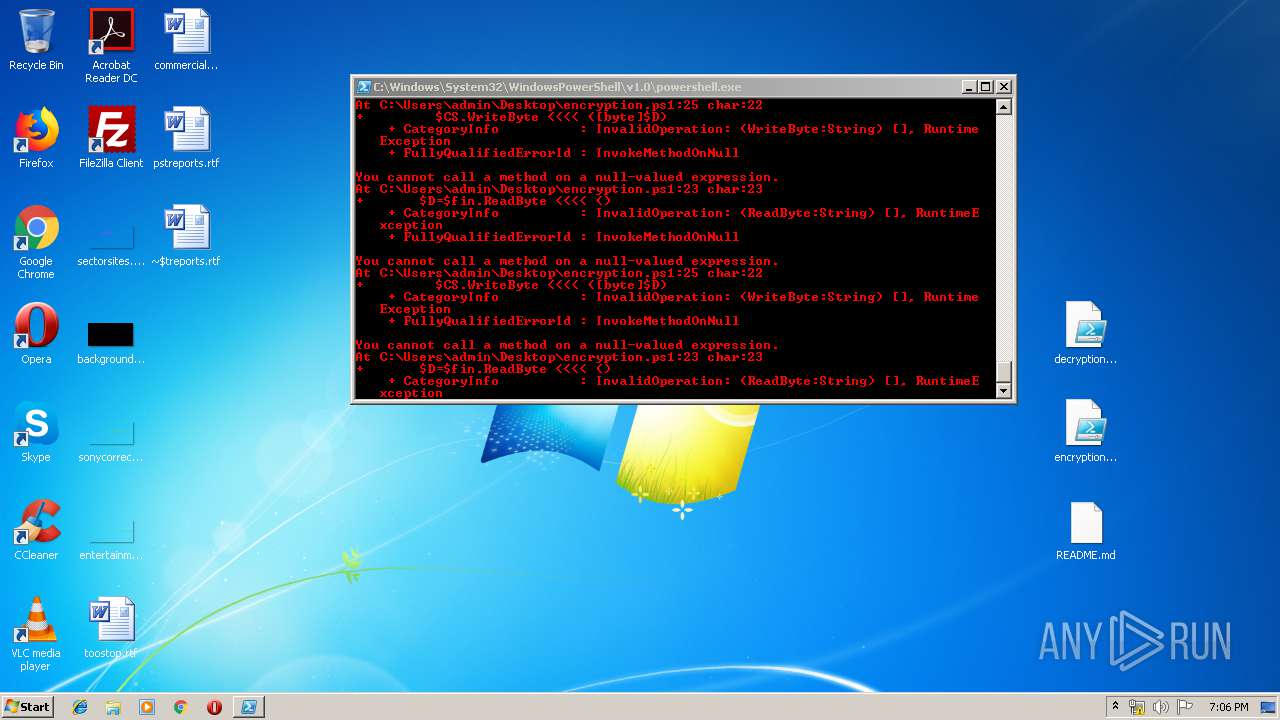
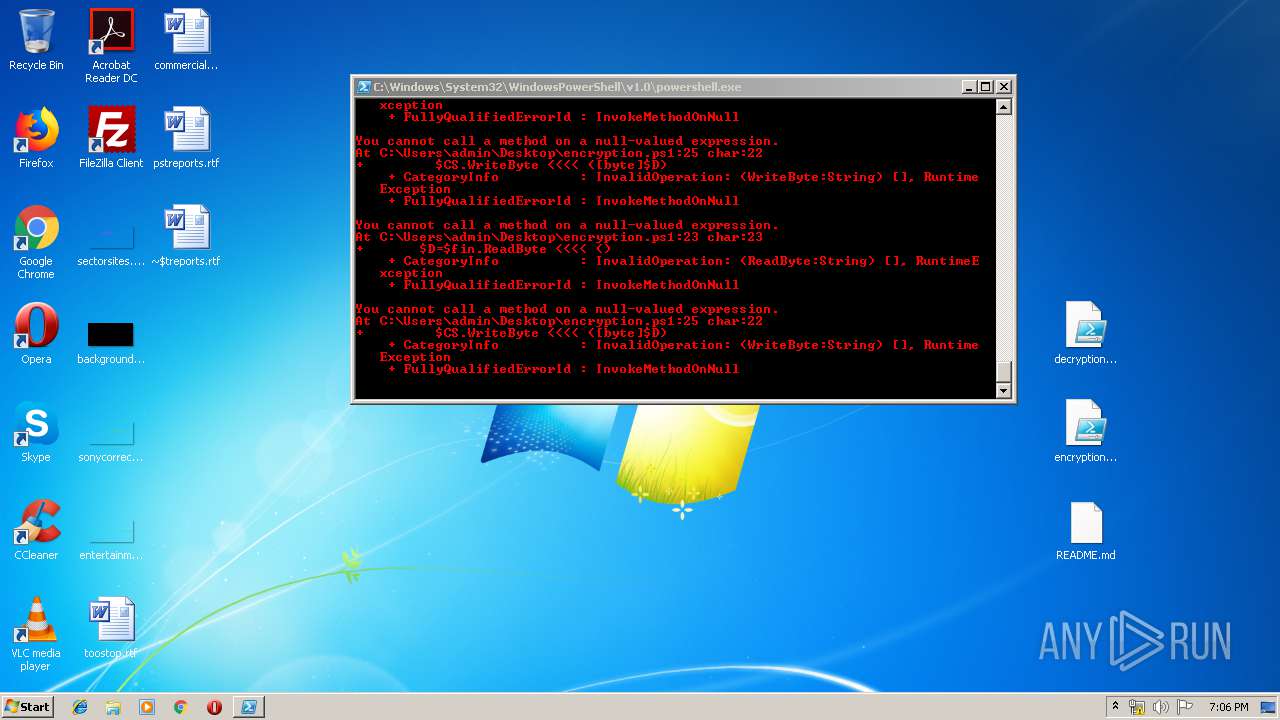
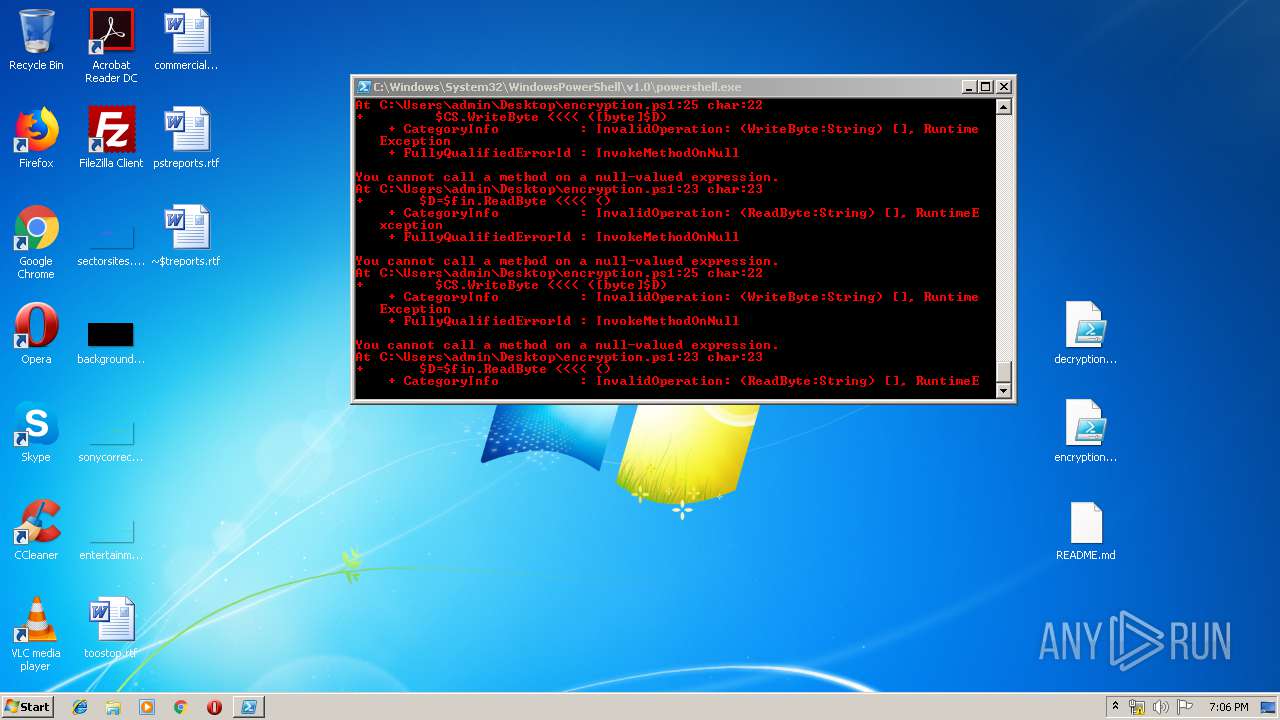
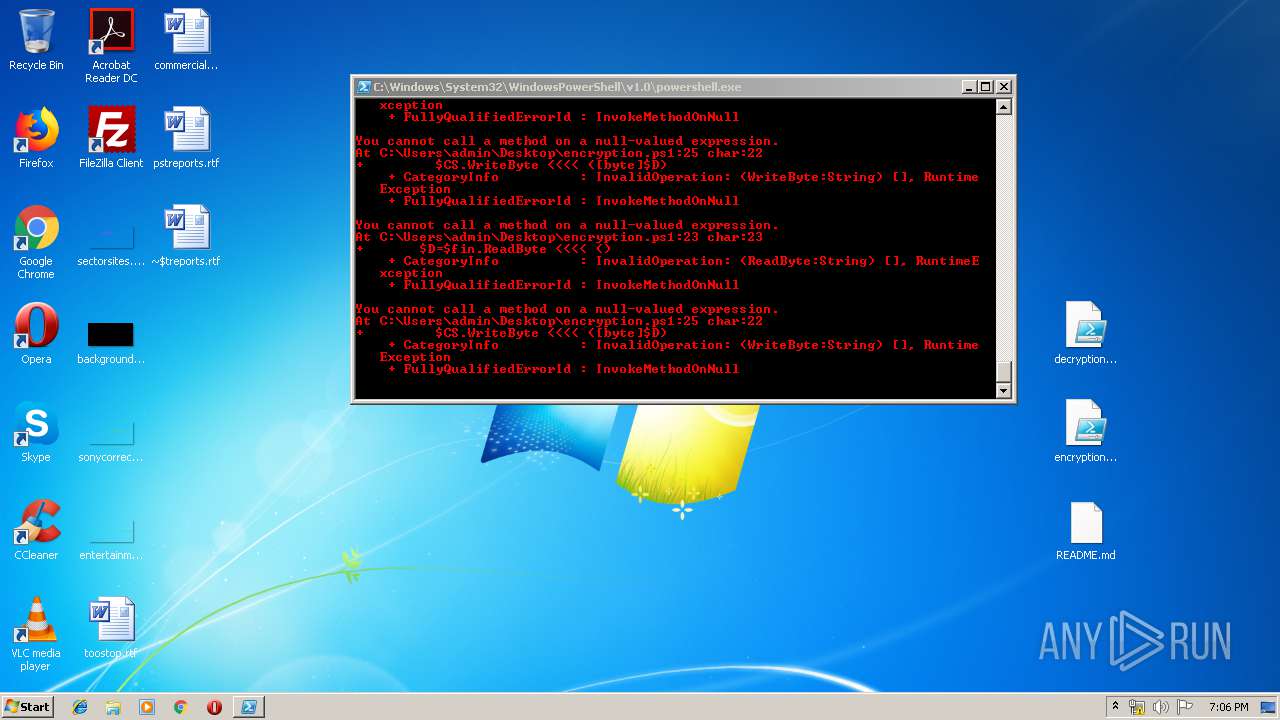
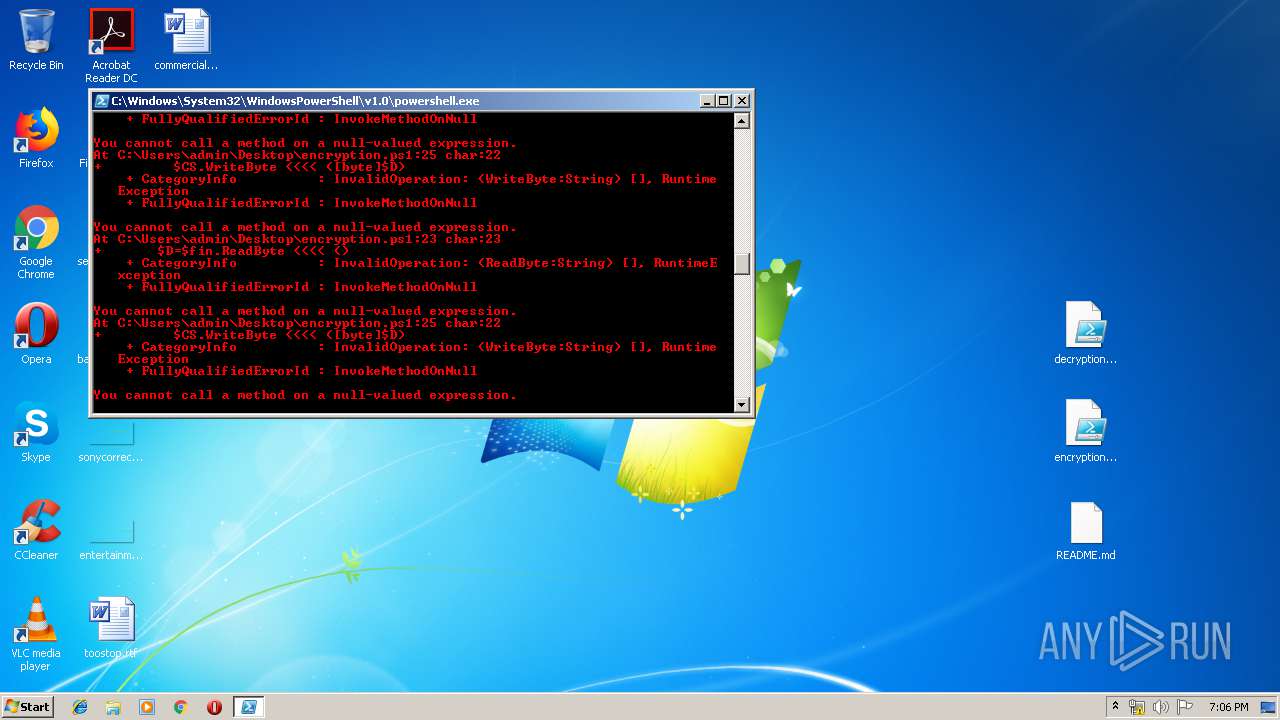
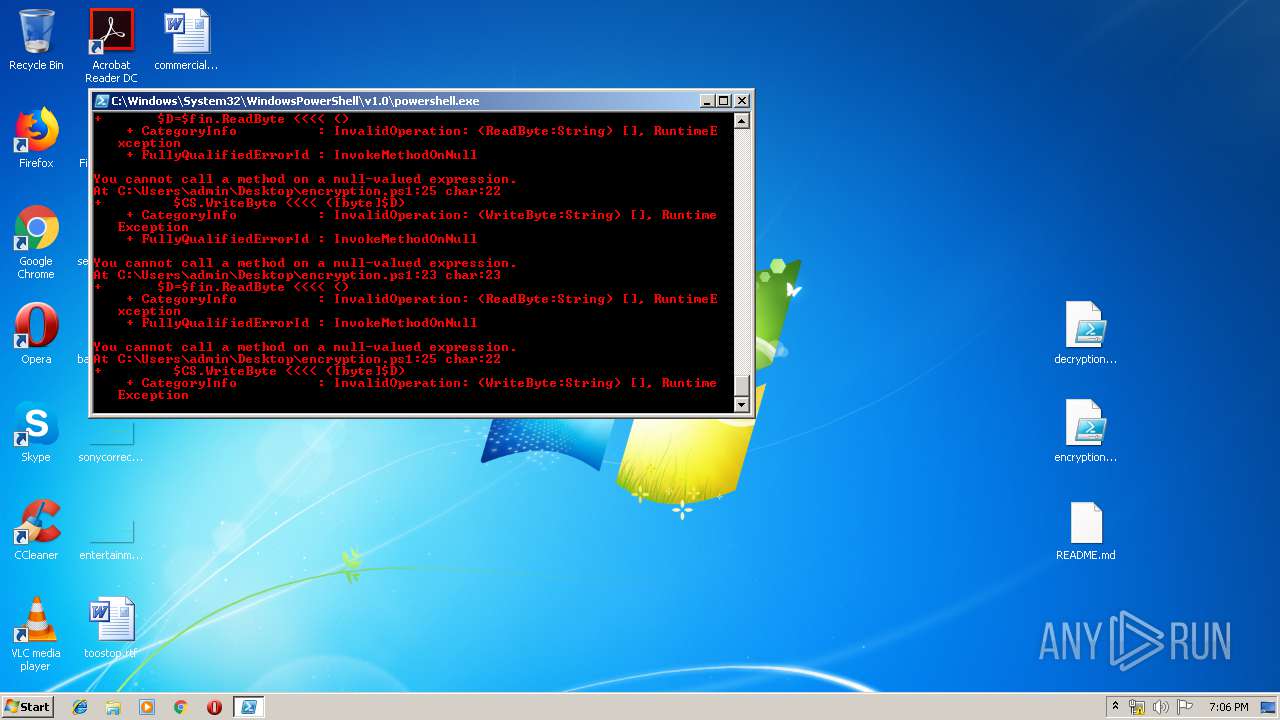
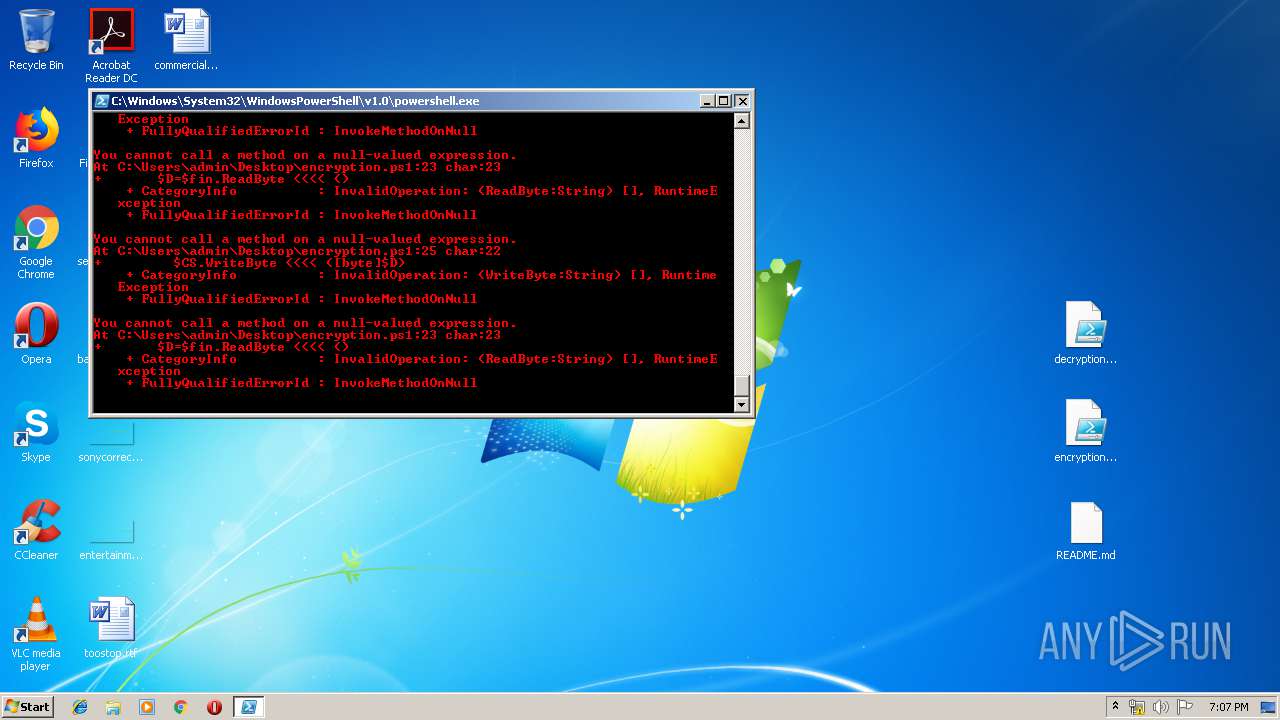
| 2604 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\encryption.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
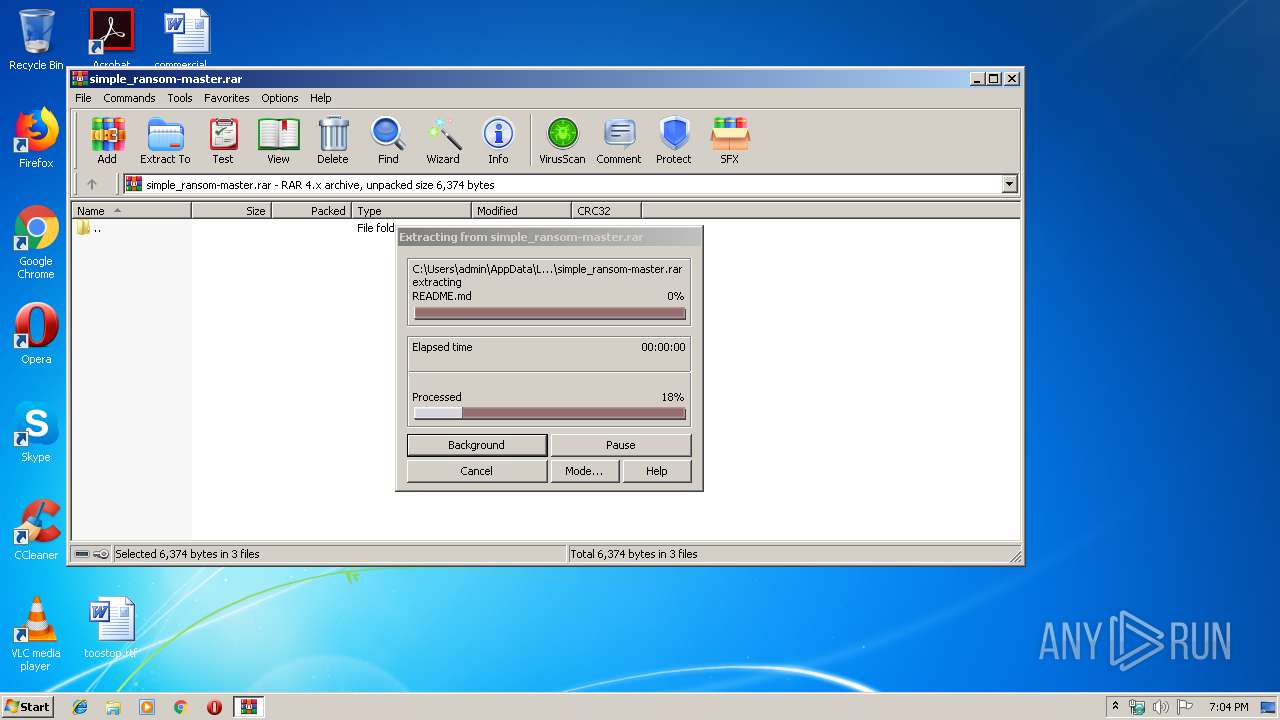
| 3332 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\simple_ransom-master.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3528 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\encryption.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\encryption.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
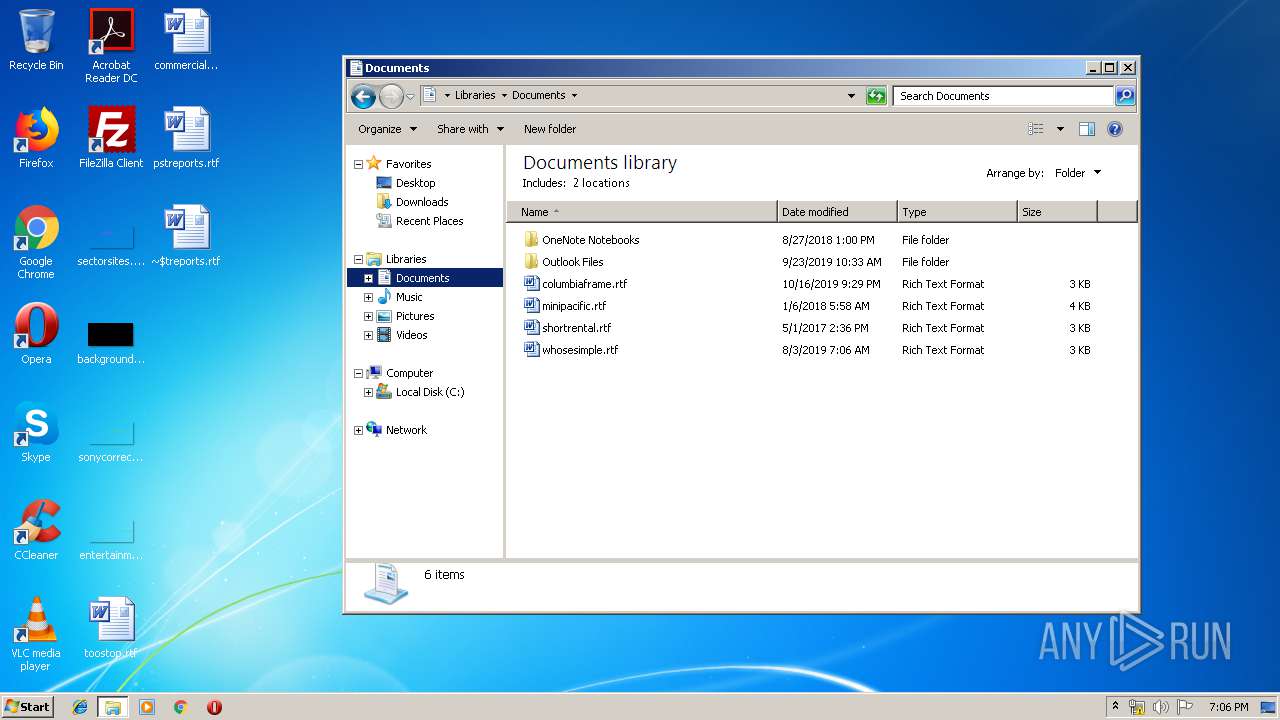
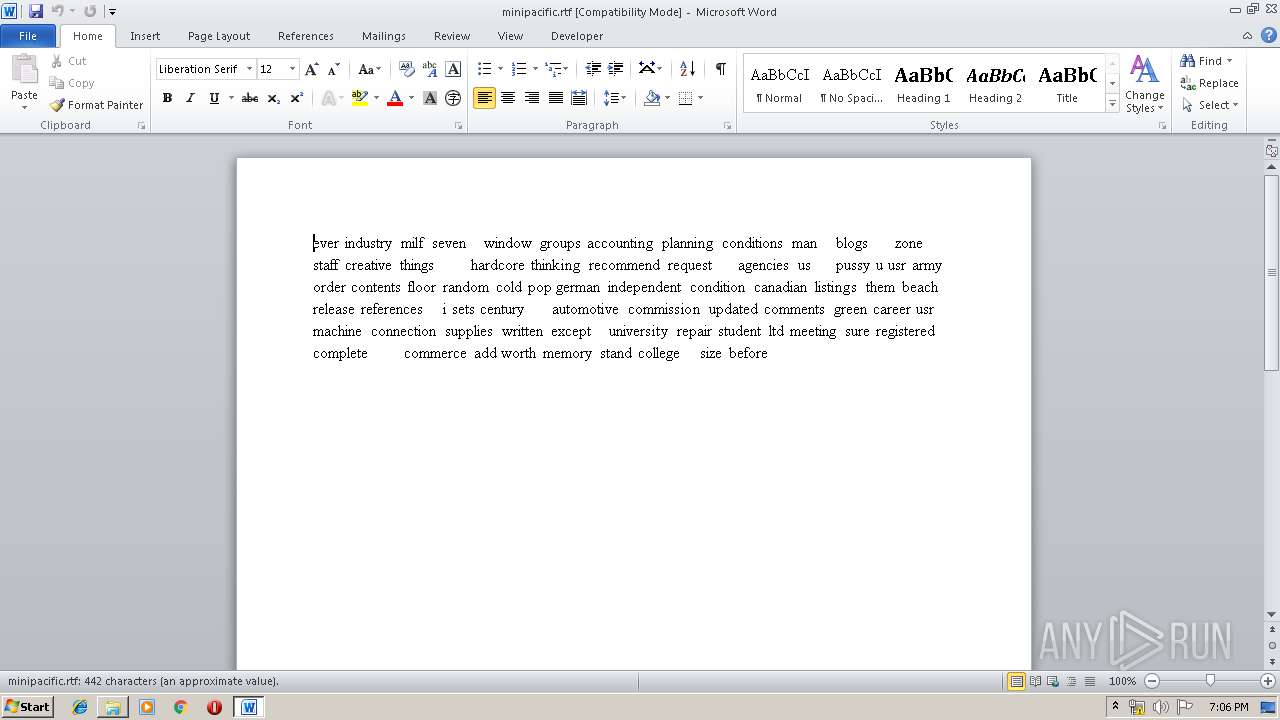
| 4020 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\minipacific.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 296
Read events
2 469
Write events
552
Delete events
275
Modification events
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\simple_ransom-master.rar | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
10
Text files
6
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3332.5947\decryption.ps1 | — | |
MD5:— | SHA256:— | |||
| 3964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X8HM7LOMKKUQQUONDWYF.temp | — | |
MD5:— | SHA256:— | |||
| 1728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4E64.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3123FF30-6C4F-4211-9F2D-69B11C973DC8}.tmp | — | |
MD5:— | SHA256:— | |||
| 1728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{4AC91A85-E878-44DE-9B36-614F74A6498C}.tmp | — | |
MD5:— | SHA256:— | |||
| 1728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{3F5FF5E0-665A-49E7-9C94-0100680BFD64}.tmp | — | |
MD5:— | SHA256:— | |||
| 2604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1U5WKI5K251OB4LUZNY9.temp | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBE30.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{145BE1A6-94F6-41B7-BF6D-49E0625ACC10}.tmp | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{76C87790-F710-4F18-8B75-973504702185}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report