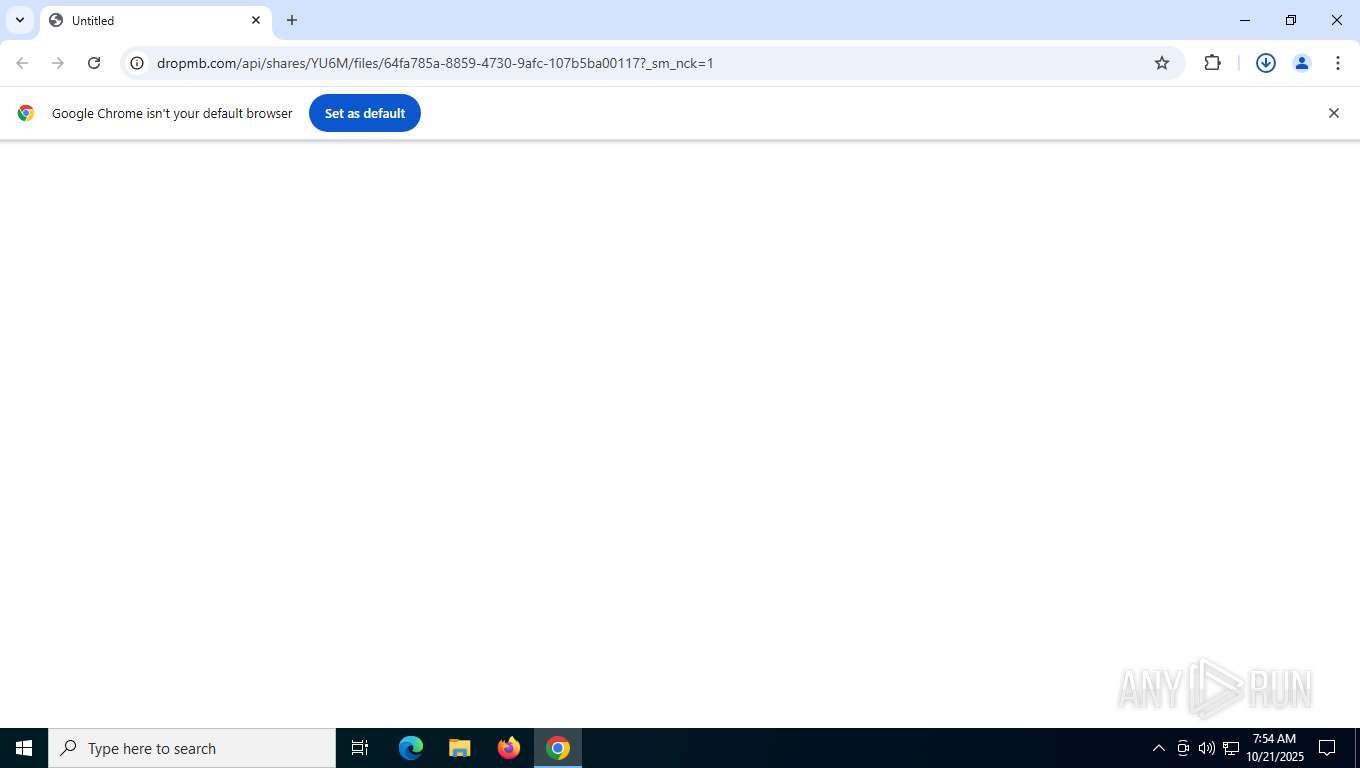
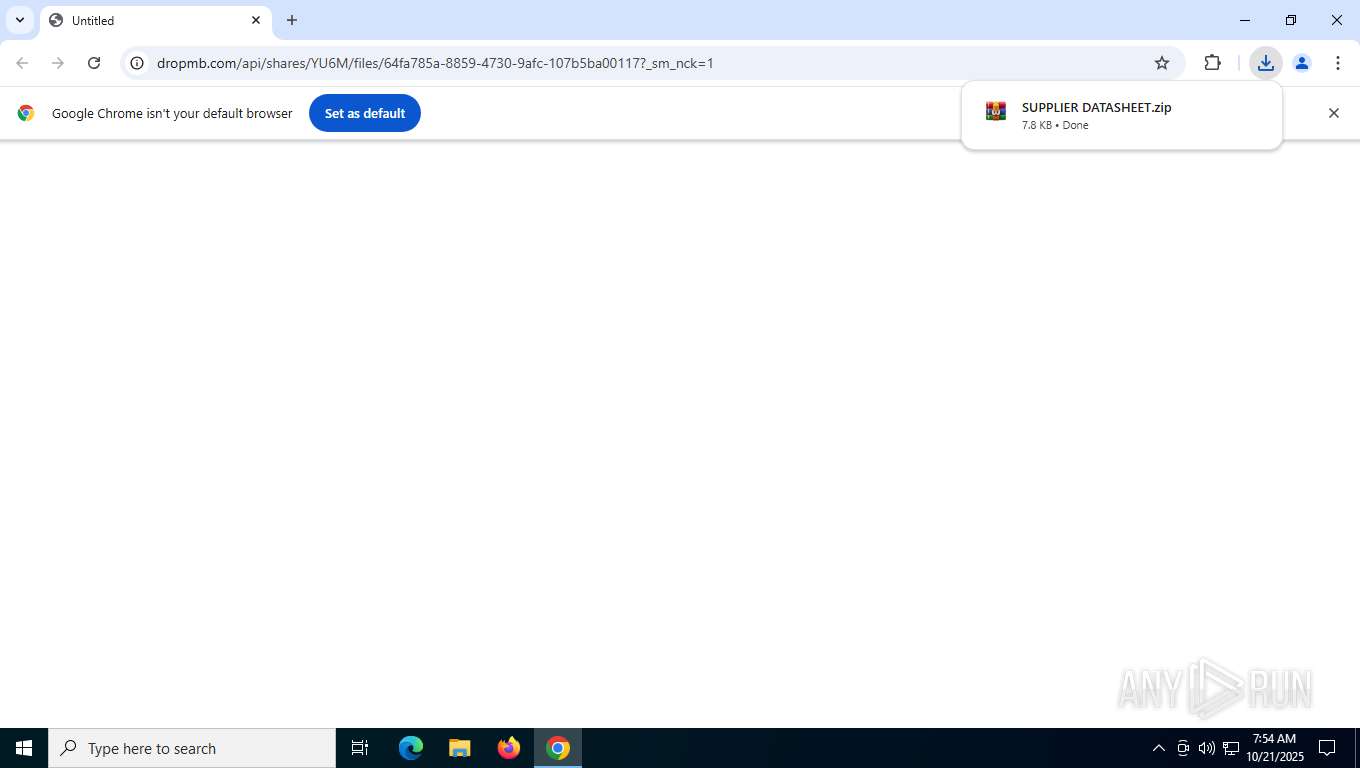
| URL: | https://dropmb.com/api/shares/YU6M/files/64fa785a-8859-4730-9afc-107b5ba00117?_sm_nck=1 |
| Full analysis: | https://app.any.run/tasks/29e68222-4ac4-4a88-82ba-fb4e1f3a91b9 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2025, 07:54:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4EAF899AB22A99611DFF729DCDF40A9D |
| SHA1: | 6AA3D0F9C347B92D668AB6486AFEFBA03C592A8A |
| SHA256: | 337892977A212A1D837EB2A3CDF8AEDEB1DD70A5792B220014077539AABAC77F |
| SSDEEP: | 3:N8PKV6tE9KenwTTzTeSSLScIRPhvzQqS5:2FE03TLNQScIXvzQZ |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 8956)
- reg.exe (PID: 8288)
- reg.exe (PID: 6676)
- reg.exe (PID: 1152)
- reg.exe (PID: 7240)
Run PowerShell with an invisible window
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 7700)
Bypass execution policy to execute commands
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
SUSPICIOUS
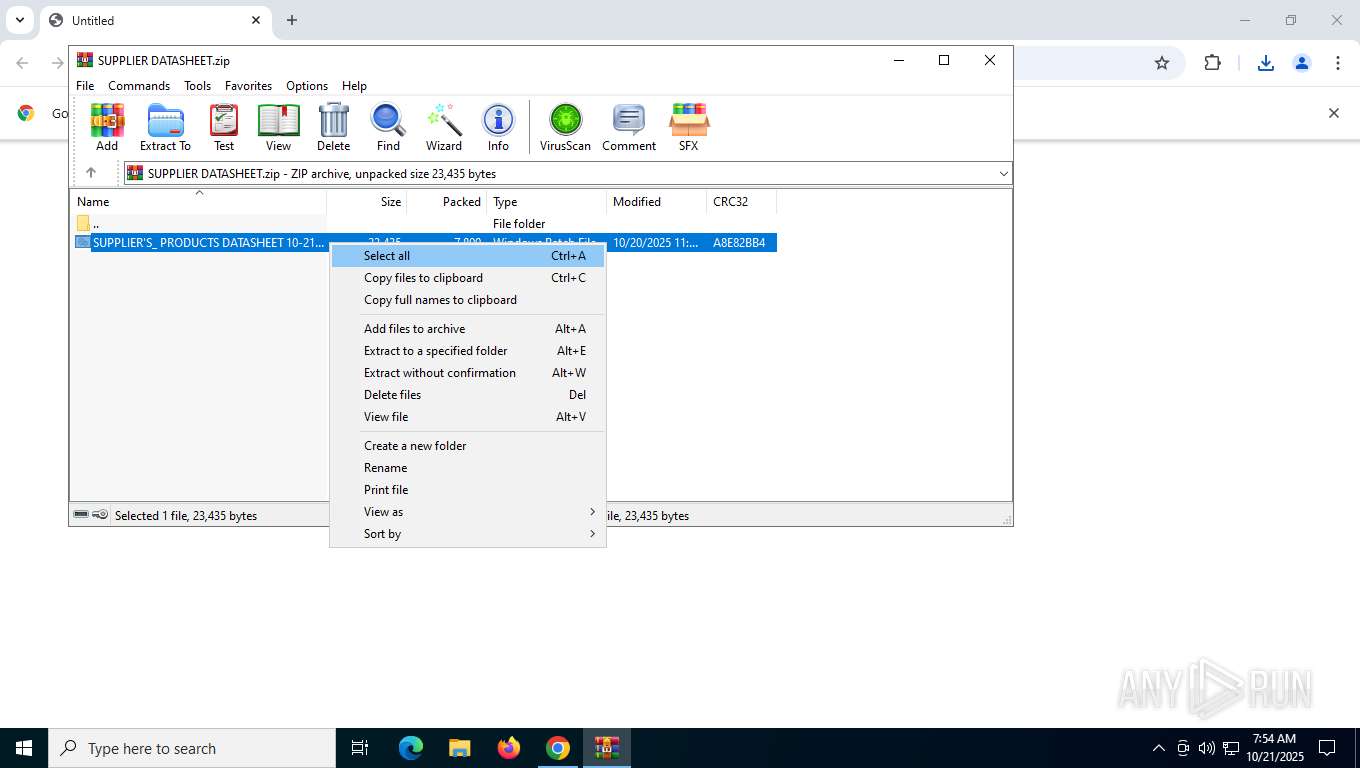
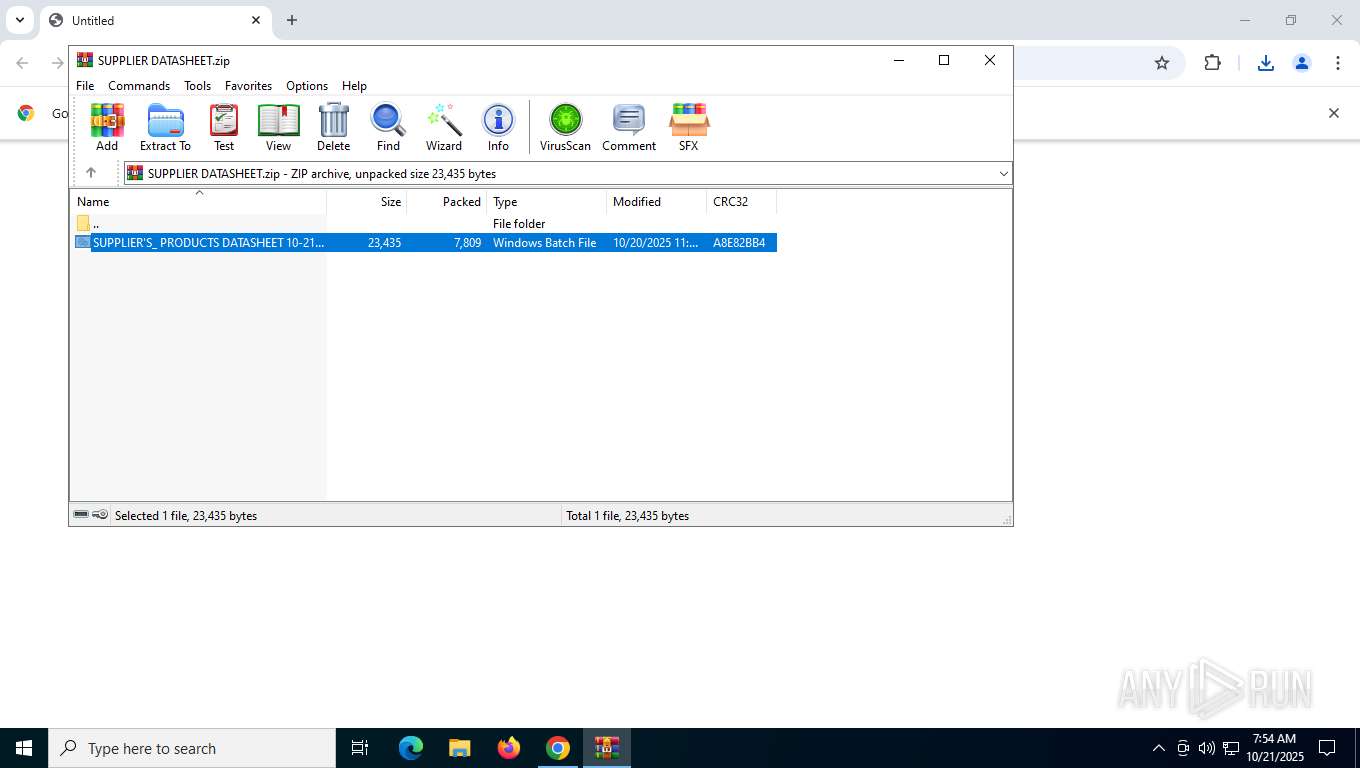
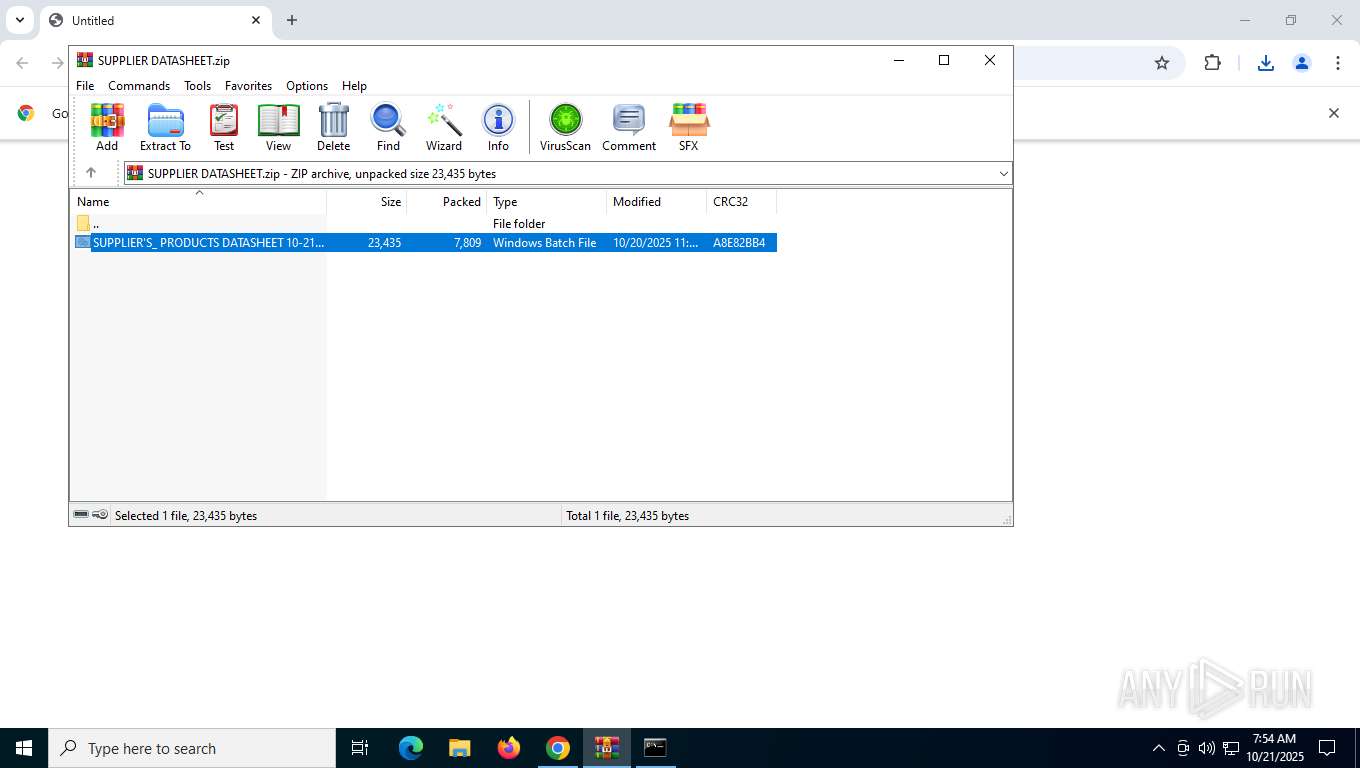
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 8304)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8920)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 7700)
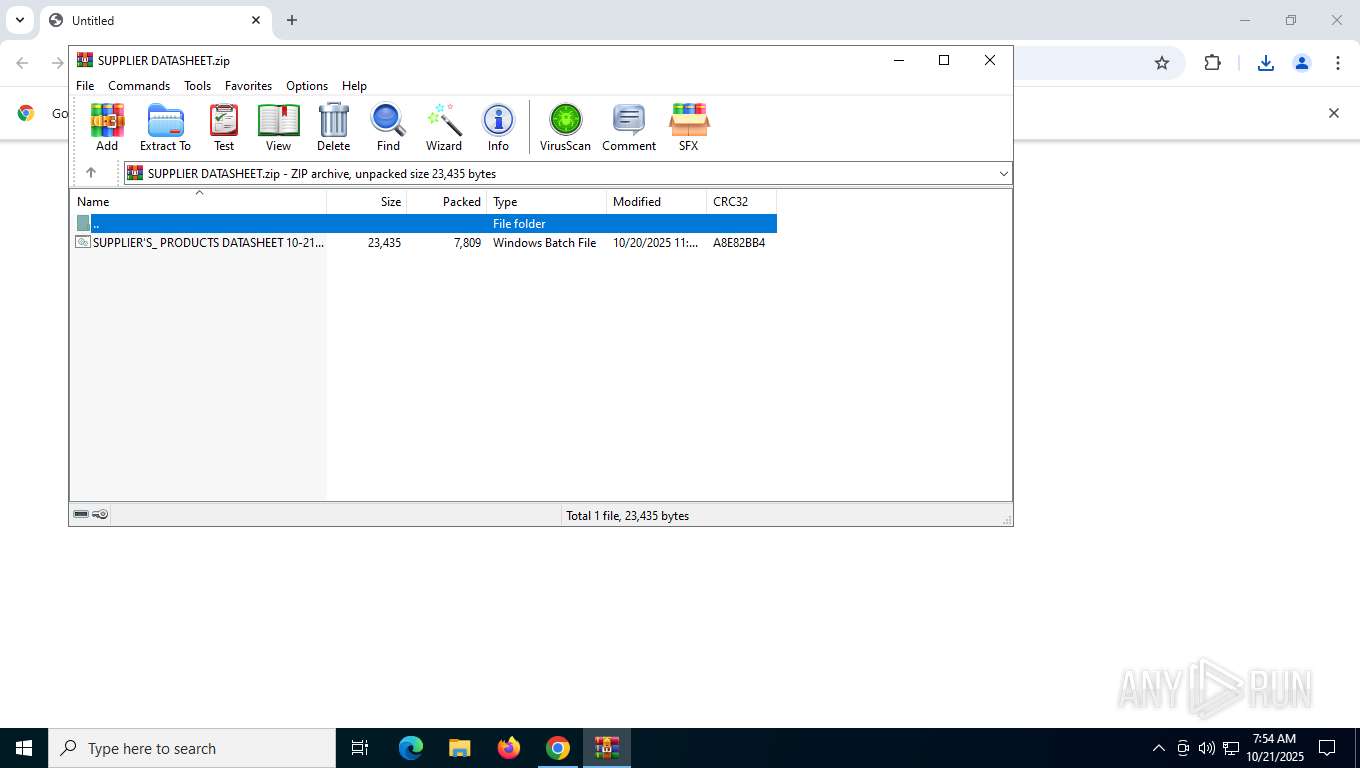
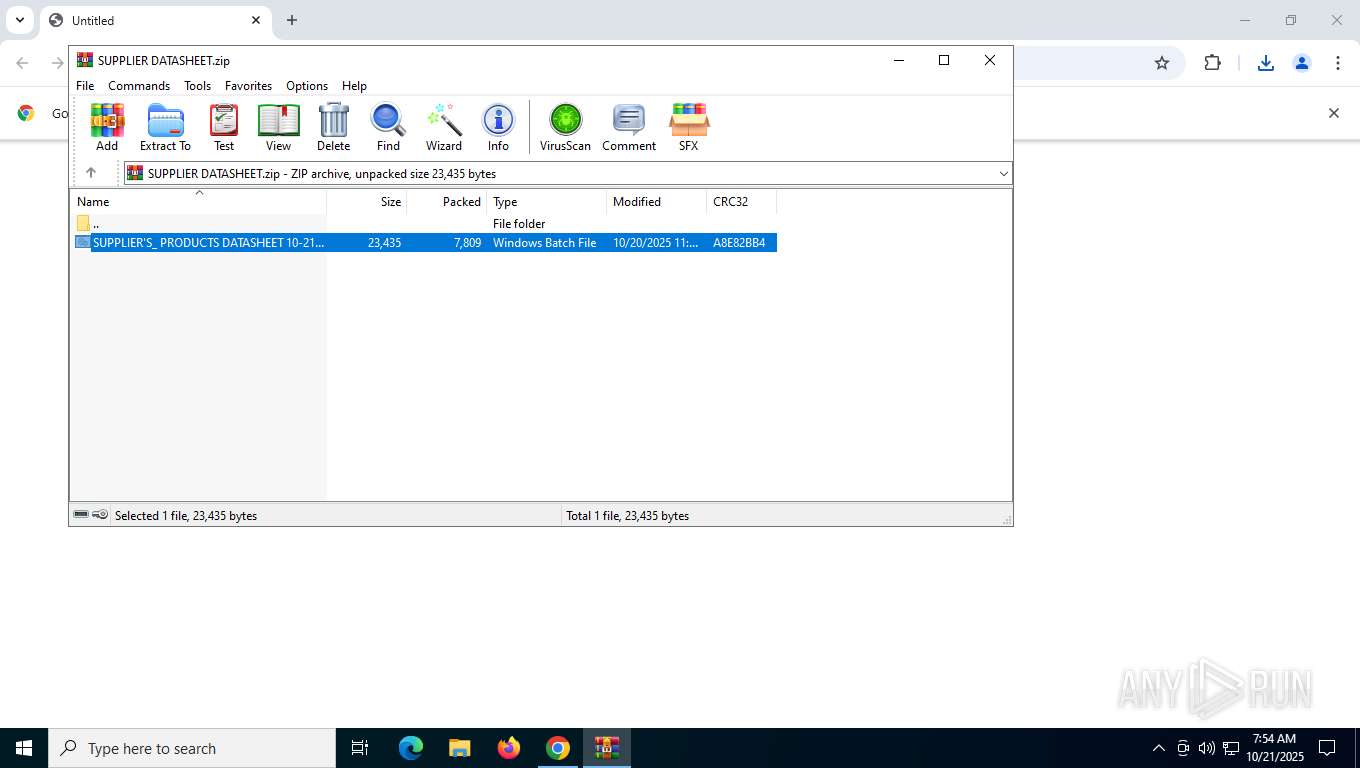
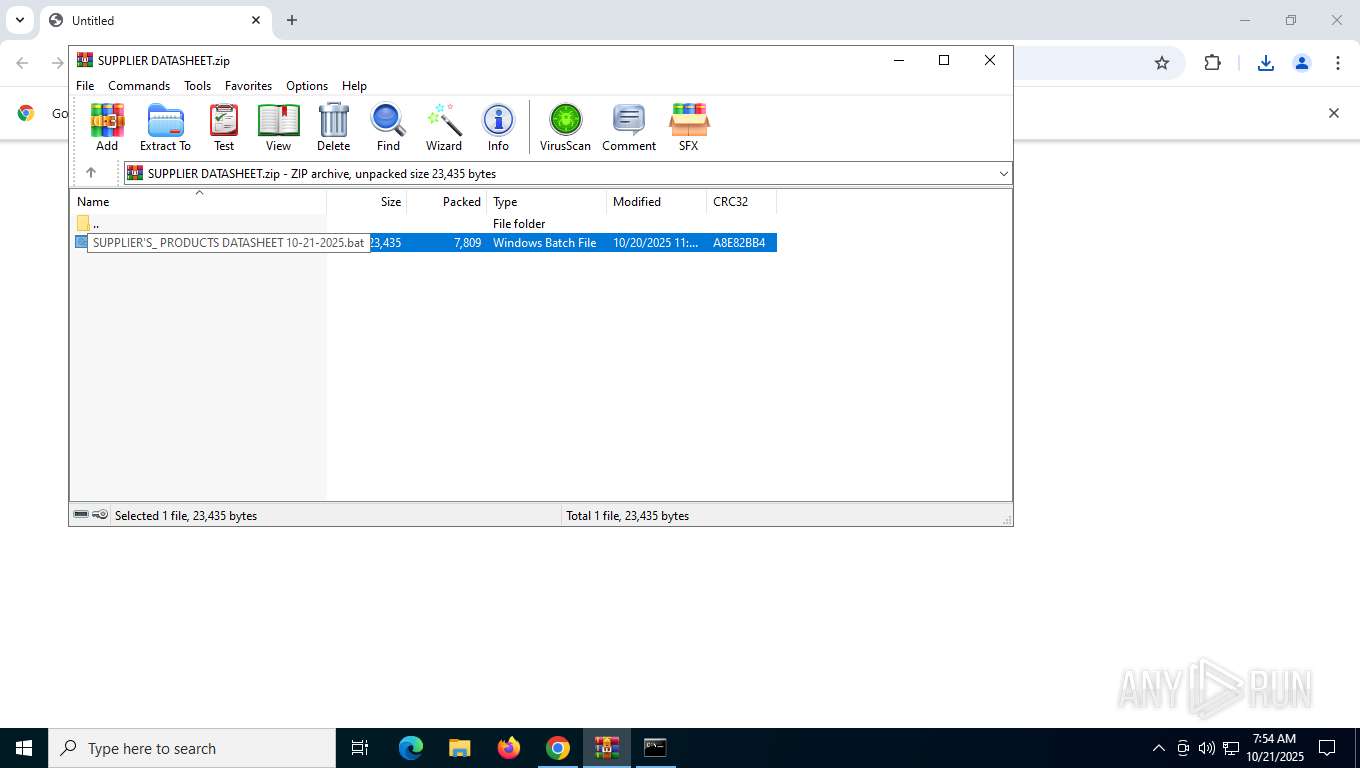
Executing commands from a ".bat" file
- cmd.exe (PID: 8824)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 8516)
- WinRAR.exe (PID: 8304)
- cmd.exe (PID: 8920)
- cmd.exe (PID: 8500)
Application launched itself
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8920)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 7700)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 7700)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 7700)
The process executes Powershell scripts
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 7700)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8888)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 7700)
CSC.EXE is used to compile C# code
- csc.exe (PID: 9112)
- csc.exe (PID: 8596)
- csc.exe (PID: 5412)
- csc.exe (PID: 7420)
- csc.exe (PID: 1488)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
Executable content was dropped or overwritten
- csc.exe (PID: 9112)
- csc.exe (PID: 8596)
- csc.exe (PID: 7420)
- csc.exe (PID: 5412)
- csc.exe (PID: 1488)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8304)
Connects to unusual port
- powershell.exe (PID: 8988)
There is functionality for taking screenshot (YARA)
- powershell.exe (PID: 8988)
INFO
Application launched itself
- chrome.exe (PID: 7792)
Launching a file from the Downloads directory
- chrome.exe (PID: 7792)
Reads Microsoft Office registry keys
- chrome.exe (PID: 7792)
Launching a file from a Registry key
- reg.exe (PID: 8956)
- reg.exe (PID: 8288)
- reg.exe (PID: 6676)
- reg.exe (PID: 1152)
- reg.exe (PID: 7240)
Checks supported languages
- cvtres.exe (PID: 9132)
- csc.exe (PID: 9112)
- csc.exe (PID: 8596)
- cvtres.exe (PID: 8600)
- csc.exe (PID: 7420)
- cvtres.exe (PID: 7516)
- csc.exe (PID: 5412)
- cvtres.exe (PID: 3460)
- csc.exe (PID: 1488)
- cvtres.exe (PID: 4312)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
Reads the machine GUID from the registry
- csc.exe (PID: 9112)
- csc.exe (PID: 8596)
- csc.exe (PID: 7420)
- csc.exe (PID: 5412)
- csc.exe (PID: 1488)
Create files in a temporary directory
- cvtres.exe (PID: 9132)
- csc.exe (PID: 9112)
- csc.exe (PID: 8596)
- cvtres.exe (PID: 8600)
- csc.exe (PID: 7420)
- cvtres.exe (PID: 7516)
- csc.exe (PID: 5412)
- cvtres.exe (PID: 3460)
- csc.exe (PID: 1488)
- cvtres.exe (PID: 4312)
Checks proxy server information
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
- slui.exe (PID: 8416)
Reads Internet Explorer settings
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
Disables trace logs
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8360)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 9128)
- powershell.exe (PID: 4956)
Creates files in the program directory
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 7700)
Found Base64 encoded text manipulation via PowerShell (YARA)
- cmd.exe (PID: 8888)
Potential remote process memory reading (Base64 Encoded 'ReadProcessMemory')
- cmd.exe (PID: 8888)
- powershell.exe (PID: 8988)
Potential remote process memory writing (Base64 Encoded 'WriteProcessMemory')
- cmd.exe (PID: 8888)
- powershell.exe (PID: 8988)
Found Base64 encoded access to Marshal class via PowerShell (YARA)
- cmd.exe (PID: 8888)
Found Base64 encoded reflection usage via PowerShell (YARA)
- cmd.exe (PID: 8888)
Reads the software policy settings
- slui.exe (PID: 8416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
60
Malicious processes
15
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "SecurityHelper" /t REG_SZ /d "\"C:\ProgramData\WinRAR.bat\"" /f | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=3592,i,12377294352966771475,545797640420788369,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1232 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1488 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\5ddmixrb.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1680 | powershell.exe -ExecutionPolicy Bypass -WindowStyle Hidden -NoProfile -File "C:\ProgramData\WinRAR.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2180 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Y " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=5936,i,12377294352966771475,545797640420788369,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3460 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES70AD.tmp" "c:\Users\admin\AppData\Local\Temp\CSCE354208A45B4107AA14F49D33B32DB9.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 4312 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4B0.tmp" "c:\Users\admin\AppData\Local\Temp\CSCD6DB58AED3D442A2ABEC9A51D9A7FFD5.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 4732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4432,i,12377294352966771475,545797640420788369,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4740 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
15 063
Read events
15 048
Write events
15
Delete events
0
Modification events
| (PID) Process: | (7792) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7792) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7792) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7792) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7792) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7792) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (8304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8304) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
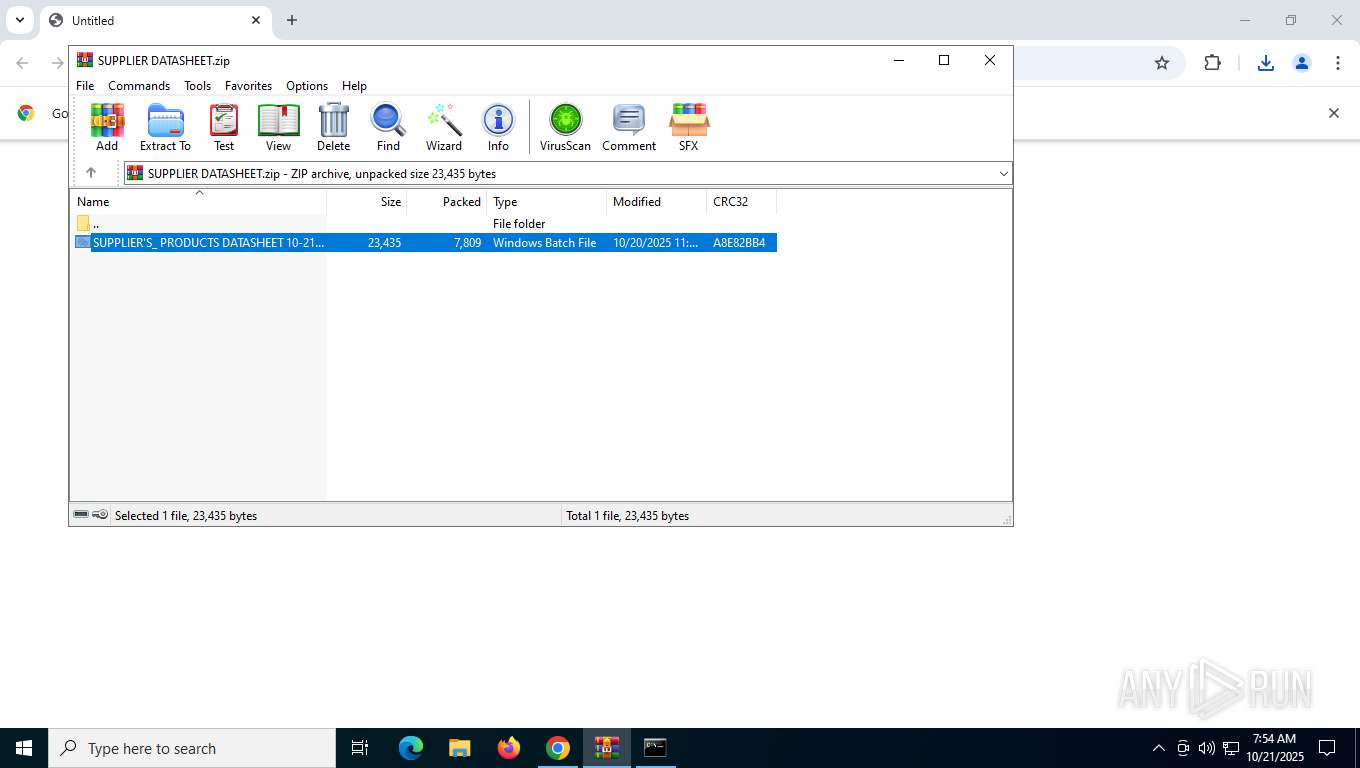
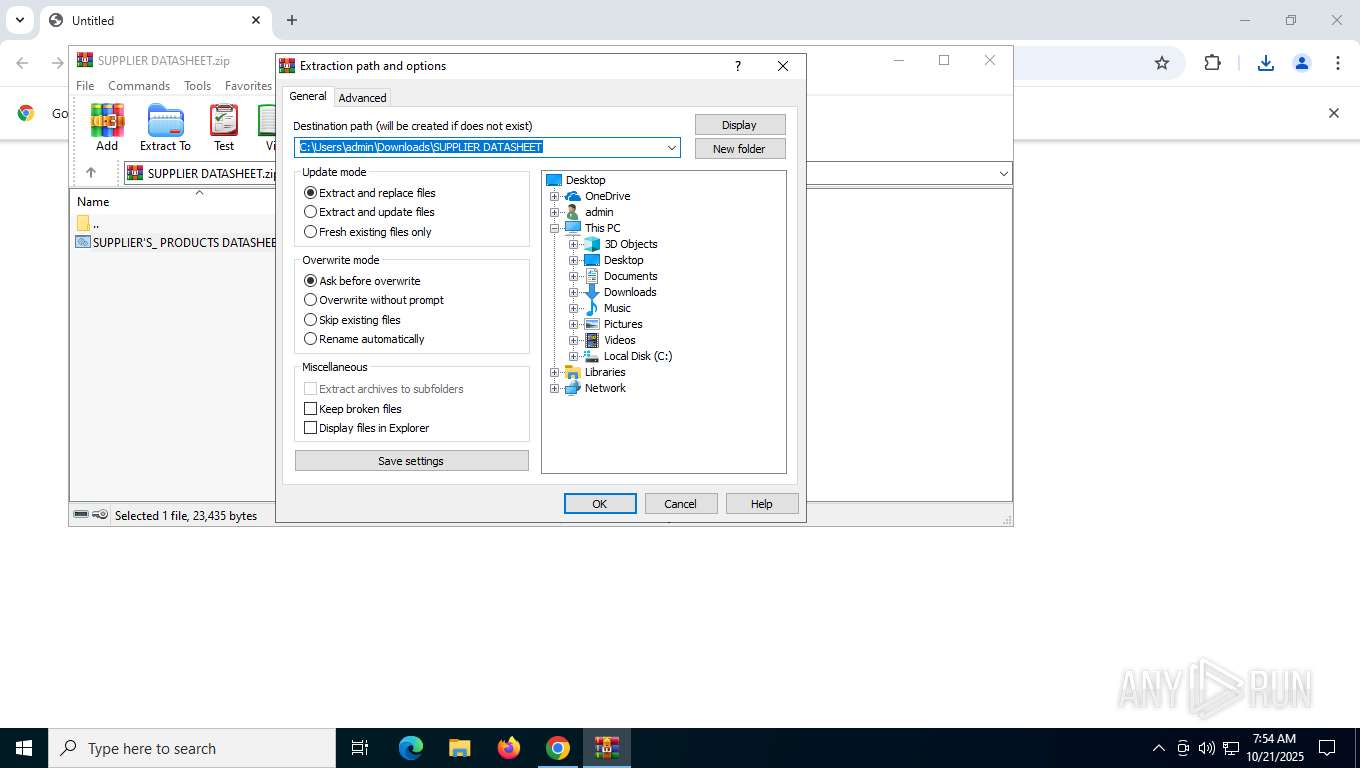
Value: C:\Users\admin\Downloads\SUPPLIER DATASHEET.zip | |||
Executable files
6
Suspicious files
55
Text files
58
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfb7dd.TMP | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFfb7dd.TMP | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFfb7ed.TMP | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfb7ed.TMP | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFfb7ed.TMP | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
60
DNS requests
39
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7016 | svchost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7340 | backgroundTaskHost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
8080 | chrome.exe | GET | 200 | 142.250.185.142:80 | http://clients2.google.com/time/1/current?cup2key=8:UPha4jf2LGHIkib7mTbEedFlIhEuRnMaFUuivIQapyE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 104 b | whitelisted |
2736 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4444 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzFkOTU2ODctM2JiNS00NDJhLTg2ZmEtYjM0ODZiM2YxNmVm/1.0.0.19_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
4444 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzFkOTU2ODctM2JiNS00NDJhLTg2ZmEtYjM0ODZiM2YxNmVm/1.0.0.19_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 1.09 Kb | whitelisted |
4444 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzFkOTU2ODctM2JiNS00NDJhLTg2ZmEtYjM0ODZiM2YxNmVm/1.0.0.19_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | compressed | 56 b | whitelisted |
4444 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzFkOTU2ODctM2JiNS00NDJhLTg2ZmEtYjM0ODZiM2YxNmVm/1.0.0.19_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 1.72 Kb | whitelisted |
7016 | svchost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7300 | backgroundTaskHost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3208 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5948 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.17.113.82:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
7016 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7016 | svchost.exe | 23.51.98.7:80 | ocsp.digicert.com | Akamai International B.V. | US | whitelisted |
7300 | backgroundTaskHost.exe | 2.17.113.82:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
7300 | backgroundTaskHost.exe | 23.51.98.7:80 | ocsp.digicert.com | Akamai International B.V. | US | whitelisted |
3440 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
dropmb.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |