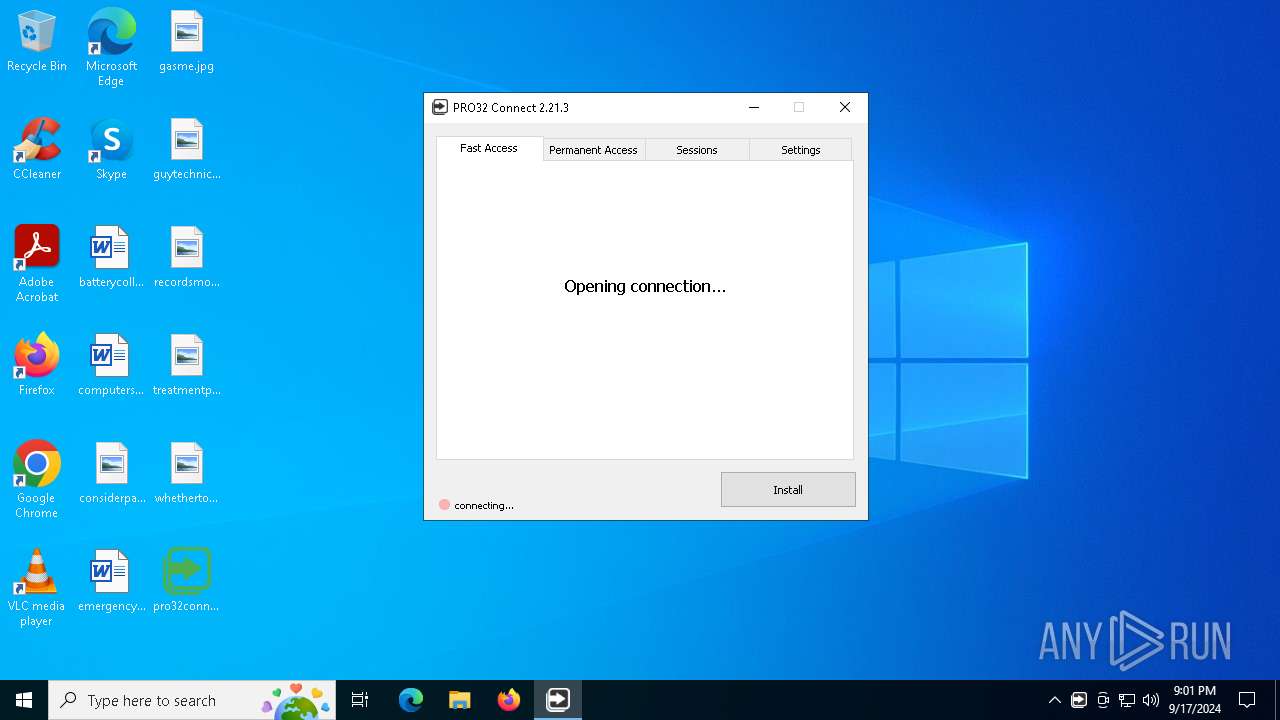
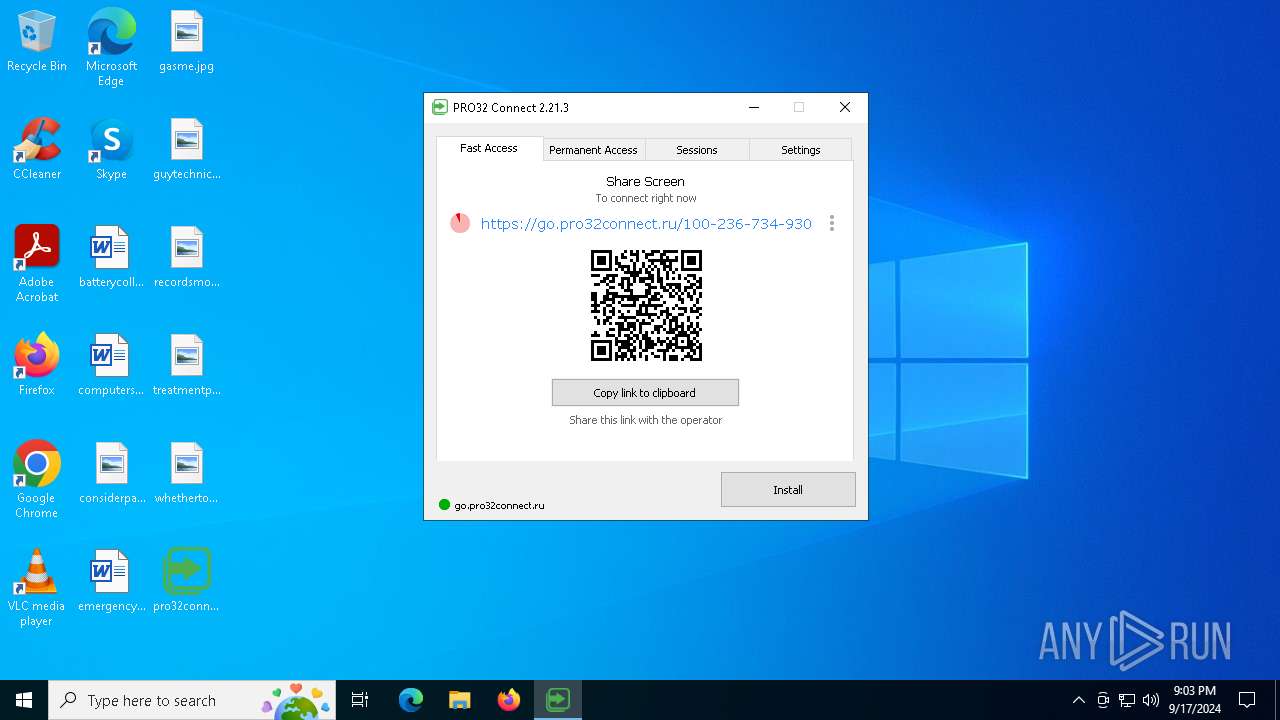
| File name: | pro32connect.exe |
| Full analysis: | https://app.any.run/tasks/423310f2-f56d-4b9f-bbda-dd605ca78083 |
| Verdict: | Malicious activity |
| Analysis date: | September 17, 2024, 21:00:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 36E8EC8DAF60F62DA06E1A8FA26CDCFE |
| SHA1: | D8F7F11D391BF0A6F98EEECC5B30A1B52E0AD9BE |
| SHA256: | 337438DBC9EE3A0652E5805207416DED542E86AE42458FFA94F409E698608B9B |
| SSDEEP: | 98304:dr5LHQQayiDctjRGACmYlfqh4PJB5H0DqXqGH11NH9vxPY+0FELERU+A5bZxj14C:PNrz4 |
MALICIOUS
GETMESCREEN has been detected (SURICATA)
- pro32connect.exe (PID: 2080)
SUSPICIOUS
Connects to unusual port
- pro32connect.exe (PID: 2080)
Application launched itself
- pro32connect.exe (PID: 2080)
- pro32connect.exe (PID: 5212)
Executable content was dropped or overwritten
- pro32connect.exe (PID: 2080)
INFO
UPX packer has been detected
- pro32connect.exe (PID: 2080)
- pro32connect.exe (PID: 3708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:07:12 13:31:07+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 4235264 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | 22249472 |
| EntryPoint: | 0x1942850 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.21.3.0 |
| ProductVersionNumber: | 2.21.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0009) |
| CharacterSet: | Unicode |
| CompanyName: | PRO32 Connect |
| InternalName: | PRO32 Connect |
| OriginalFileName: | pro32connect.exe |
| ProductName: | PRO32 Connect |
| FileVersion: | 2.21.3 |
| LegalCopyright: | Copyright (C) 2023 |
| ProductVersion: | 2.21.3 |
Total processes
126
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\ProgramData\PRO32 Connect\abffiwawyziohioipkbbwyvsdkxcdsn-elevate.exe" -elevate \\.\pipe\elevateGS512abffiwawyziohioipkbbwyvsdkxcdsn | C:\ProgramData\PRO32 Connect\abffiwawyziohioipkbbwyvsdkxcdsn-elevate.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 1 Modules
| |||||||||||||||
| 2080 | "C:\Users\admin\Desktop\pro32connect.exe" | C:\Users\admin\Desktop\pro32connect.exe | pro32connect.exe | ||||||||||||
User: admin Company: PRO32 Connect Integrity Level: HIGH Version: 2.21.3 Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\Desktop\pro32connect.exe" -gpipe \\.\pipe\PCommand97PRO32^Connect -gui | C:\Users\admin\Desktop\pro32connect.exe | pro32connect.exe | ||||||||||||
User: admin Company: PRO32 Connect Integrity Level: HIGH Version: 2.21.3 Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\Desktop\pro32connect.exe" -cpipe \\.\pipe\PCommand96PRO32^Connect -cmem 0000pipe0PCommand96PRO32^Connect7v7uvh7y0j8c4t3 -child | C:\Users\admin\Desktop\pro32connect.exe | pro32connect.exe | ||||||||||||
User: SYSTEM Company: PRO32 Connect Integrity Level: SYSTEM Exit code: 1 Version: 2.21.3 Modules
| |||||||||||||||
| 5212 | "C:\Users\admin\Desktop\pro32connect.exe" | C:\Users\admin\Desktop\pro32connect.exe | — | explorer.exe | |||||||||||
User: admin Company: PRO32 Connect Integrity Level: MEDIUM Exit code: 0 Version: 2.21.3 Modules
| |||||||||||||||
Total events
1 642
Read events
1 625
Write events
17
Delete events
0
Modification events
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyType |
Value: 0 | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyPort |
Value: 0 | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyLogin |
Value: | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyPassword |
Value: | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyType |
Value: 0 | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2080) pro32connect.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GetScreen\PRO32 Connect |
| Operation: | write | Name: | ProxyPort |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | pro32connect.exe | C:\ProgramData\PRO32 Connect\memory\0000pipe0PCommand96PRO32^Connect7v7uvh7y0j8c4t3 | — | |
MD5:— | SHA256:— | |||
| 5212 | pro32connect.exe | C:\ProgramData\PRO32 Connect\logs\20240917.log | text | |
MD5:4DF99347A591AEE5F126A74A3F38633A | SHA256:2B50C76B56CF82970B3D77EFB74E4163E4C60ECEBB3866AD0B7D278099B430B7 | |||
| 2080 | pro32connect.exe | C:\ProgramData\PRO32 Connect\settings.dat | binary | |
MD5:E21BB136A1BCE42DC353899A551B4A16 | SHA256:CB5F0725E889E1AC13870A9846D1502351BB81DB9E22A5D8C378AFC0208DFE2F | |||
| 2080 | pro32connect.exe | C:\Users\admin\AppData\Local\PRO32 Connect\settings.dat | binary | |
MD5:E21BB136A1BCE42DC353899A551B4A16 | SHA256:CB5F0725E889E1AC13870A9846D1502351BB81DB9E22A5D8C378AFC0208DFE2F | |||
| 2080 | pro32connect.exe | C:\ProgramData\PRO32 Connect\abffiwawyziohioipkbbwyvsdkxcdsn-elevate.exe | executable | |
MD5:36E8EC8DAF60F62DA06E1A8FA26CDCFE | SHA256:337438DBC9EE3A0652E5805207416DED542E86AE42458FFA94F409E698608B9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
29
DNS requests
10
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6468 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 101 | 82.202.238.211:443 | https://pro32connect.ru/signal/agent | RU | — | — | unknown |
1744 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 101 | 212.41.3.20:443 | https://px3.pro32connect.ru/download/agent?token=test | RU | — | — | unknown |
— | — | GET | 101 | 92.223.103.205:443 | https://px1.pro32connect.ru/download/agent?token=test | RU | — | — | unknown |
— | — | GET | 101 | 212.41.3.24:443 | https://px2.pro32connect.ru/download/agent?token=test | RU | — | — | unknown |
— | — | GET | 101 | 212.41.3.21:443 | https://image.pro32connect.ru/upload/0087aeebe163cdddc7f0e22e5aa107f1d538da93b215decce6fbeea3e4e774792efe1980b5035ad09849893d4a383cb6dc0cf90c3e4308f0c82aee69f67b57a8630ab31b495e067a2d7e0b24e7813bf59d9d6b87d1e4e24a64b000965b5ebac5f862a8bc4d777eec2788a0 | RU | — | — | unknown |
2968 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1744 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6468 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1744 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6468 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2080 | pro32connect.exe | 82.202.238.210:443 | pro32connect.ru | OOO Network of data-centers Selectel | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
pro32connect.ru |
| unknown |
px2.pro32connect.ru |
| unknown |
px1.pro32connect.ru |
| unknown |
px3.pro32connect.ru |
| unknown |
image.pro32connect.ru |
| unknown |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
2080 | pro32connect.exe | Misc activity | REMOTE [ANY.RUN] GetMeScreen Remote Desktop Software |
2080 | pro32connect.exe | Misc activity | REMOTE [ANY.RUN] GetMeScreen Remote Desktop Software |
2080 | pro32connect.exe | Misc activity | REMOTE [ANY.RUN] GetMeScreen Remote Desktop Software |
2080 | pro32connect.exe | Misc activity | REMOTE [ANY.RUN] GetMeScreen Remote Desktop Software |
2080 | pro32connect.exe | Misc activity | REMOTE [ANY.RUN] GetMeScreen Remote Desktop Software |
2080 | pro32connect.exe | Misc activity | REMOTE [ANY.RUN] GetMeScreen Remote Desktop Software |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |