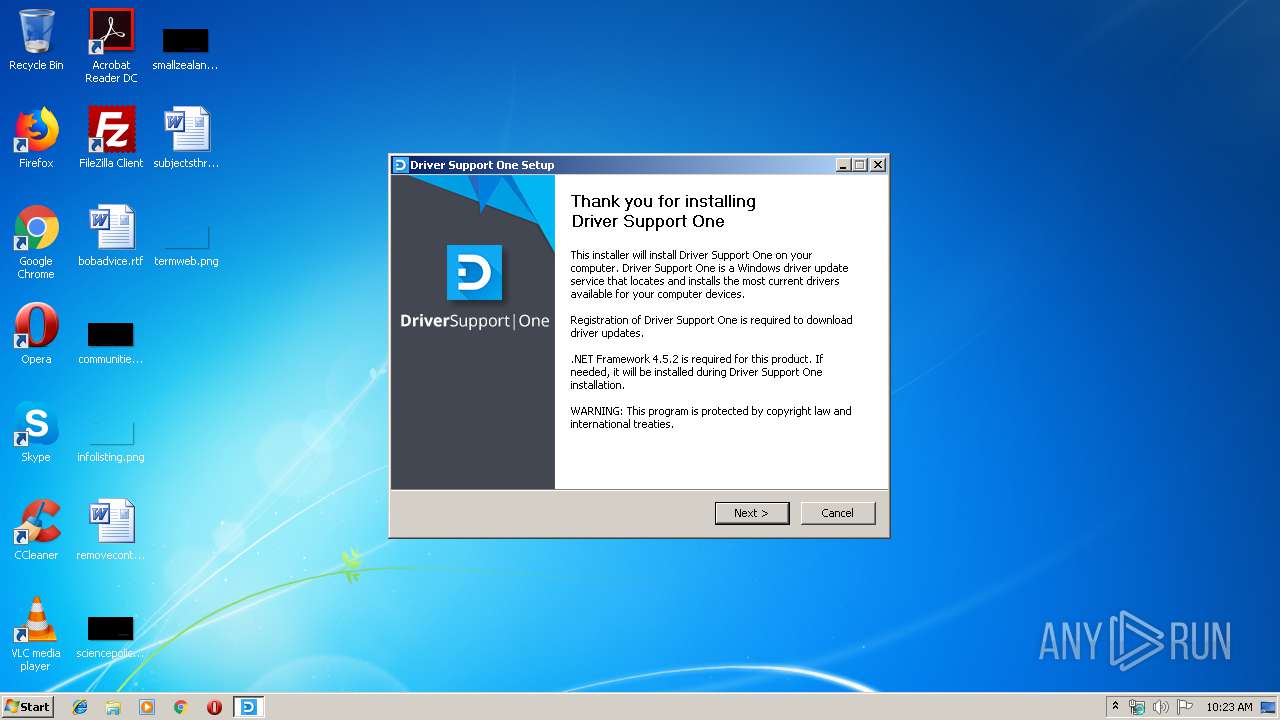
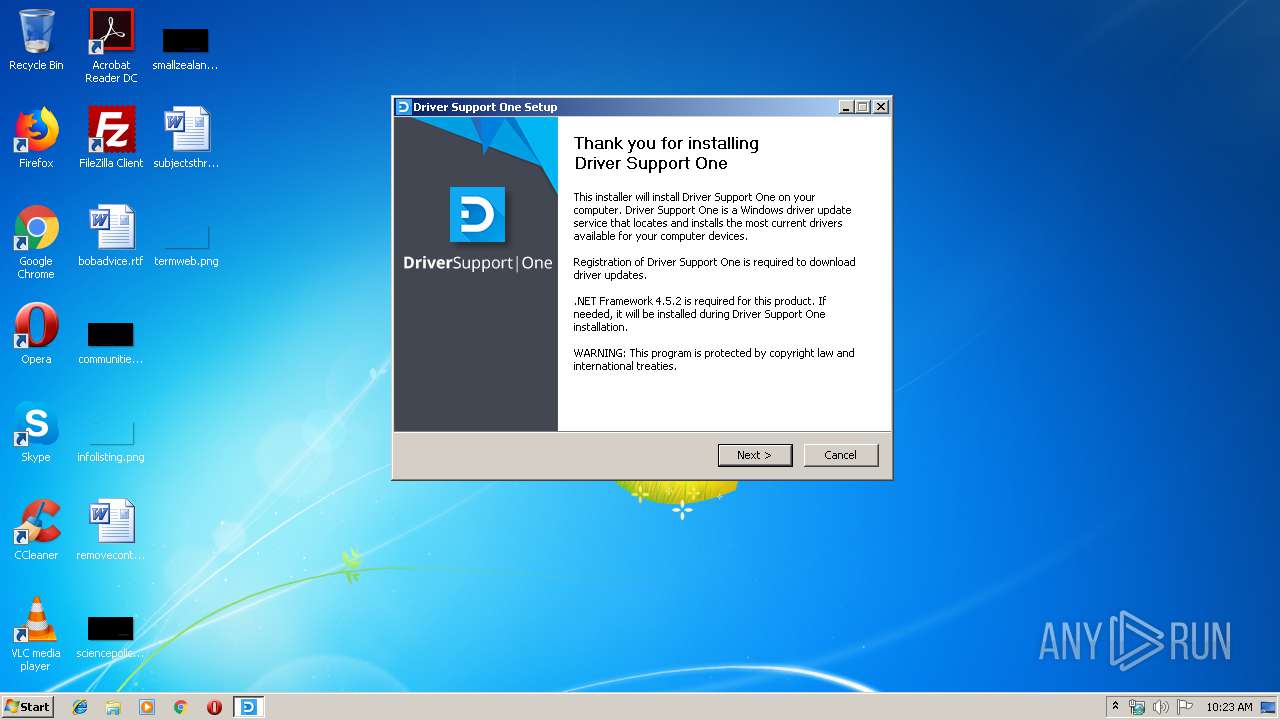
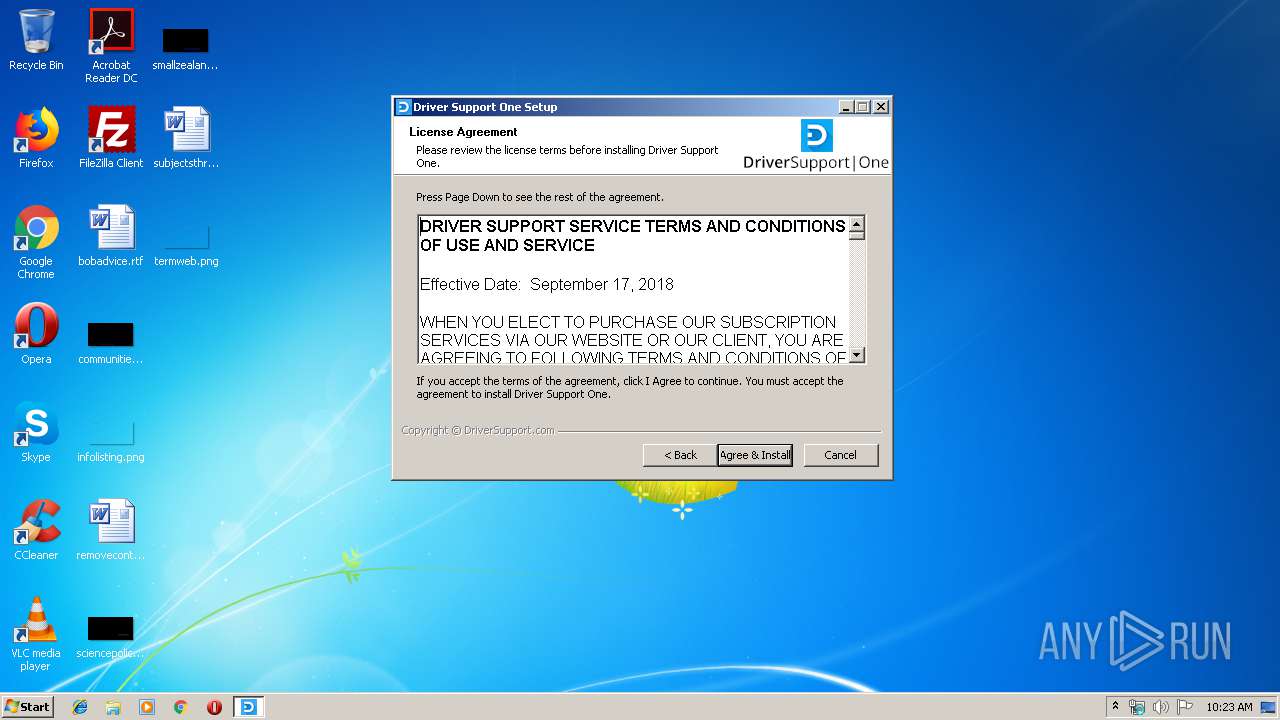
| File name: | DSOne.exe |
| Full analysis: | https://app.any.run/tasks/12e77b9f-5f68-4821-a118-44bfa0cdb293 |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2020, 10:23:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 92DA323AB59BDC61213B734DB0B40BFF |
| SHA1: | C81D93482BEACE09337CF40AF1F8B5E3DD29A3D3 |
| SHA256: | 3363D896903978A9AB10E3A24406E15701E1E2832160D95DF4F8C739455D8789 |
| SSDEEP: | 3072:aNzPHk9MpcMUBzGjkN2RzUN9vwP+iG55sKmHHqzGdX1fW5mLIyPBoEDnjx:ahRZhU3vTiwsKAugfLIyPmQjx |
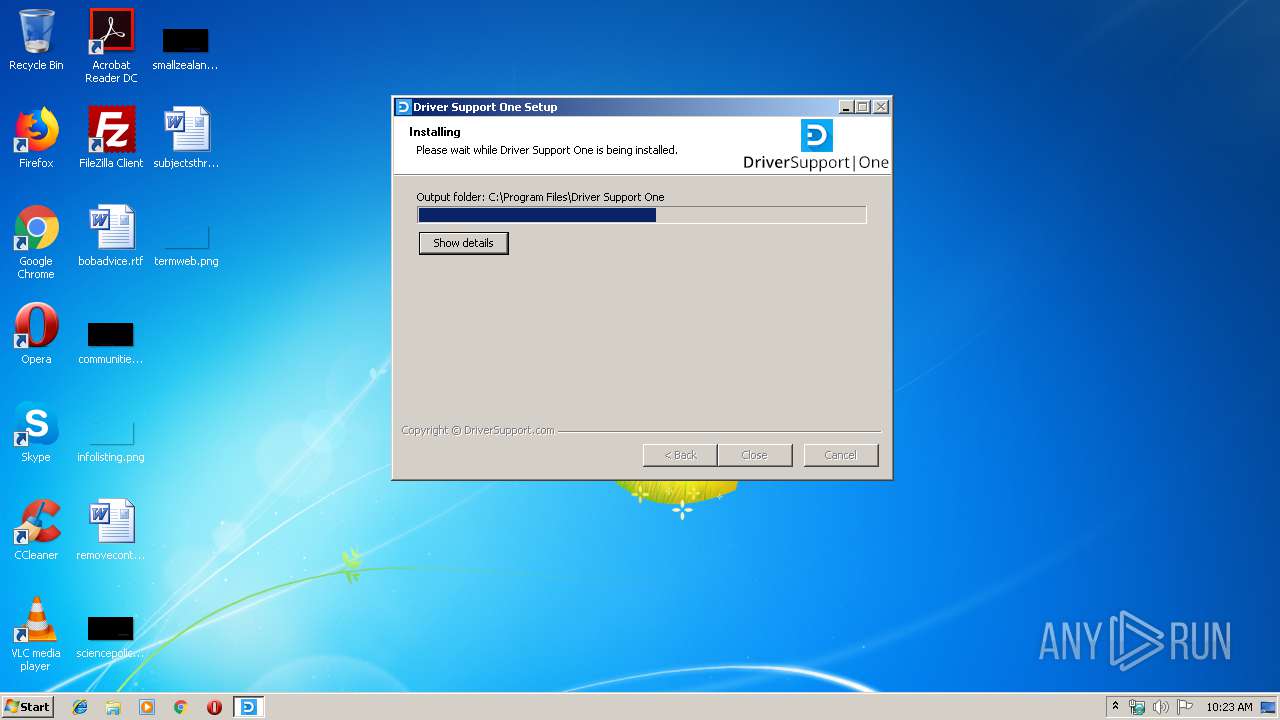
MALICIOUS
Loads dropped or rewritten executable
- DSOne.exe (PID: 1876)
Application was dropped or rewritten from another process
- nsC939.tmp (PID: 2692)
- ns6D74.tmp (PID: 3908)
SUSPICIOUS
Starts CMD.EXE for commands execution
- nsC939.tmp (PID: 2692)
- ns6D74.tmp (PID: 3908)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3796)
- cmd.exe (PID: 436)
Executable content was dropped or overwritten
- DSOne.exe (PID: 1876)
- wusa.exe (PID: 3664)
Starts application with an unusual extension
- DSOne.exe (PID: 1876)
Creates files in the Windows directory
- wusa.exe (PID: 3664)
Executed as Windows Service
- vssvc.exe (PID: 2588)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:33:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x330d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.7285.28324 |
| ProductVersionNumber: | 1.2.7285.28324 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Asurvio, LP |
| FileDescription: | Driver Support One |
| FileVersion: | 1.2.7285.28324 |
| LegalCopyright: | Asurvio, LP |
| OriginalFileName: | DSOne.exe |
| ProductName: | Driver Support One |
| ProductVersion: | 1.2.7285.28324 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:33:55 |
| Detected languages: |
|
| CompanyName: | Asurvio, LP |
| FileDescription: | Driver Support One |
| FileVersion: | 1.2.7285.28324 |
| LegalCopyright: | Asurvio, LP |
| OriginalFilename: | DSOne.exe |
| ProductName: | Driver Support One |
| ProductVersion: | 1.2.7285.28324 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:33:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000603C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39362 |
.rdata | 0x00008000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22313 |
.ndata | 0x00025000 | 0x00019000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003E000 | 0x000193D8 | 0x00019400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.6642 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30695 | 1130 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.61494 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 4.82474 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.06278 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.33593 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.80283 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
55
Monitored processes
12
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | cmd /Q /C "C:\Windows\System32\wbem\wmic.exe qfe get hotfixid | C:\Windows\System32\findstr.exe "^KB2506143"" | C:\Windows\system32\cmd.exe | — | ns6D74.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 640 | C:\Windows\System32\wbem\wmic.exe qfe get hotfixid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 736 | C:\Windows\System32\findstr.exe "^KB3033929" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | C:\Windows\System32\wbem\wmic.exe qfe get hotfixid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | C:\Windows\System32\findstr.exe "^KB2506143" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Temp\DSOne.exe" | C:\Users\admin\AppData\Local\Temp\DSOne.exe | — | explorer.exe | |||||||||||
User: admin Company: Asurvio, LP Integrity Level: MEDIUM Description: Driver Support One Exit code: 3221226540 Version: 1.2.7285.28324 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\DSOne.exe" | C:\Users\admin\AppData\Local\Temp\DSOne.exe | explorer.exe | ||||||||||||
User: admin Company: Asurvio, LP Integrity Level: HIGH Description: Driver Support One Exit code: 88 Version: 1.2.7285.28324 Modules
| |||||||||||||||
| 2588 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Temp\nshA5E1.tmp\nsC939.tmp" cmd /Q /C "C:\Windows\System32\wbem\wmic.exe qfe get hotfixid | C:\Windows\System32\findstr.exe "^KB3033929"" | C:\Users\admin\AppData\Local\Temp\nshA5E1.tmp\nsC939.tmp | — | DSOne.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
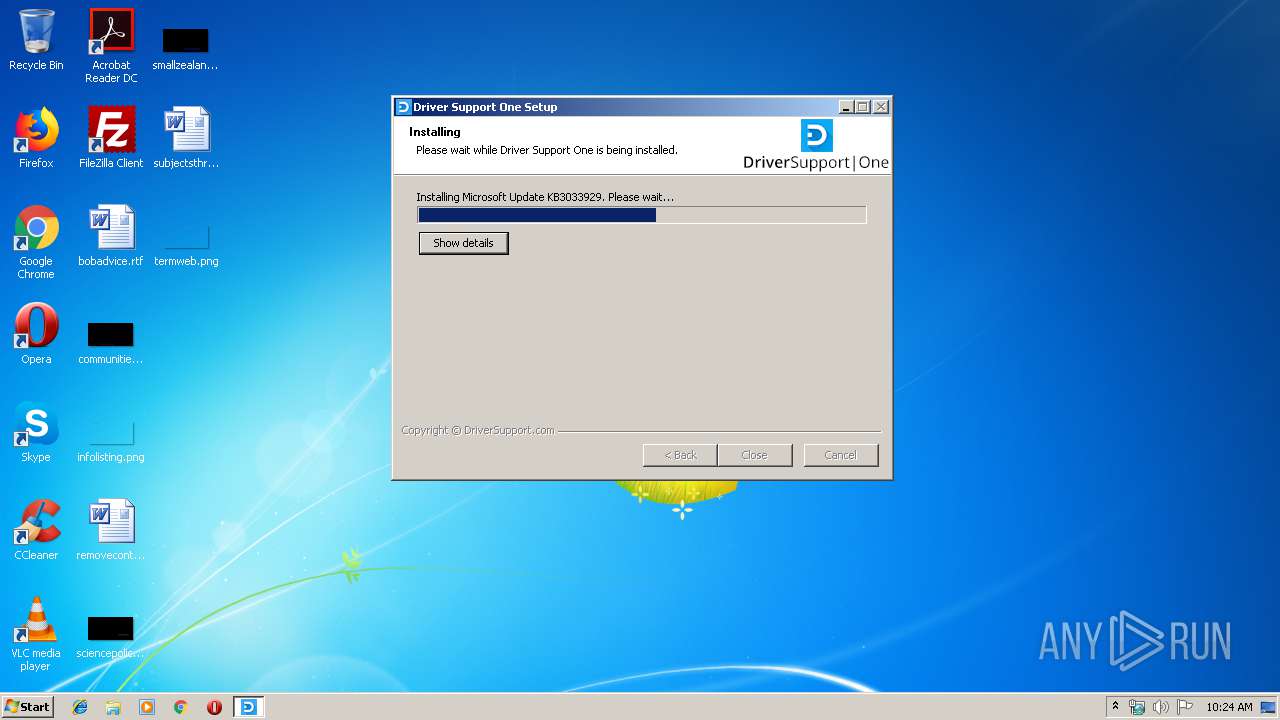
| 3664 | "C:\Windows\System32\wusa.exe" "C:\Users\admin\AppData\Local\Temp\microsoft_win_patch_for_dsone1.msu" /quiet /norestart | C:\Windows\System32\wusa.exe | DSOne.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 3010 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
612
Read events
491
Write events
120
Delete events
1
Modification events
| (PID) Process: | (3664) wusa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WUSA |
| Operation: | write | Name: | WUSACommandLine |
Value: /quiet | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F06E491657CCD5011C0A000018040000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F06E491657CCD5011C0A0000600F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F06E491657CCD5011C0A000030090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F06E491657CCD5011C0A0000980F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000000CBD571657CCD5011C0A000030090000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000661F5A1657CCD5011C0A0000980F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000661F5A1657CCD5011C0A000018040000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000C0815C1657CCD5011C0A0000600F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2588) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Enter) |
Value: 4000000000000000A64B9C1C57CCD5011C0A0000600F000001040000010000000000000000000000946A72246B061843B1972F38E8616B6D0000000000000000 | |||
Executable files
11
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | DSOne.exe | C:\Users\admin\AppData\Local\Temp\microsoft_win_patch_for_dsone1.msu | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\$dpx$.tmp\8738363849327b4e87d72c385be14492.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\Windows6.1-KB3033929-x86.cab | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\$dpx$.tmp\096da57ca2d2f64185fabf84547e6870.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\$dpx$.tmp\2d2502ebab80f74c8fe6fa650a091765.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\$dpx$.tmp\bda69cbb9d99754d8bc143b26938754f.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\$dpx$.tmp\0576e610b9abbf4492115a886b903819.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\9c1d1af55368248dd90deb36d2\$dpx$.tmp\6280136b486d1b47978c900e596a3bb4.tmp | — | |
MD5:— | SHA256:— | |||
| 2588 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3664 | wusa.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
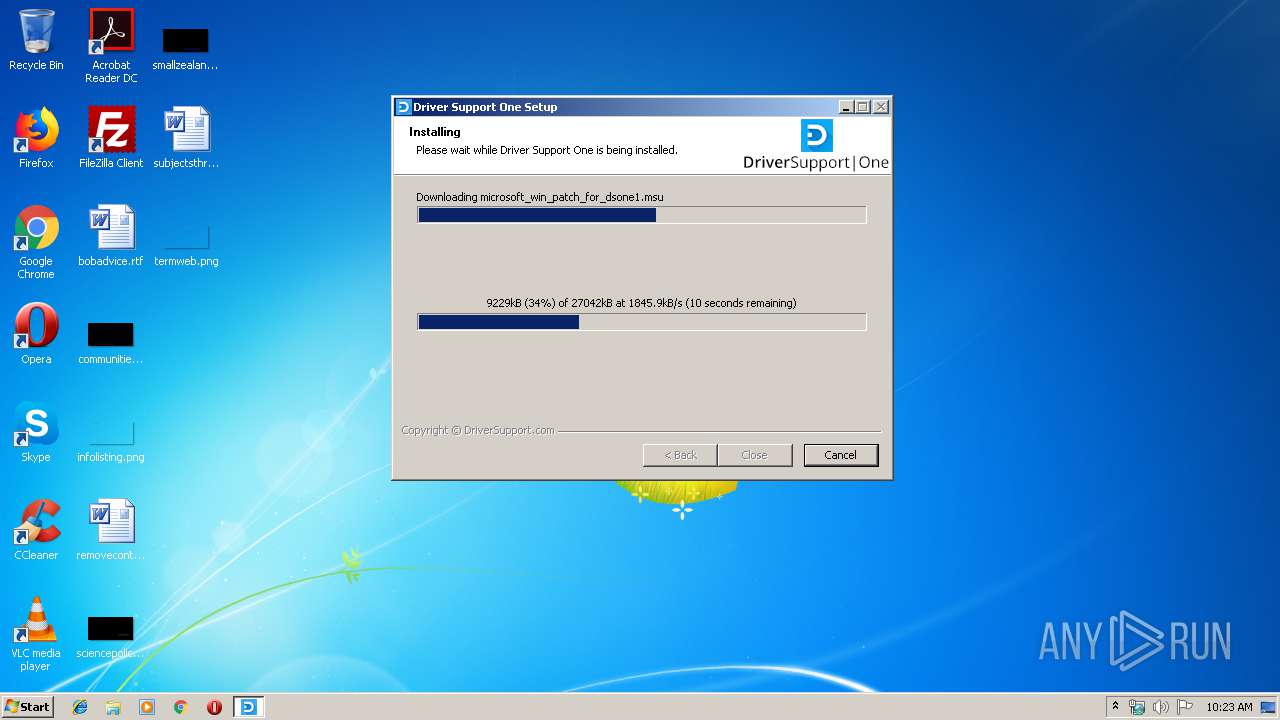
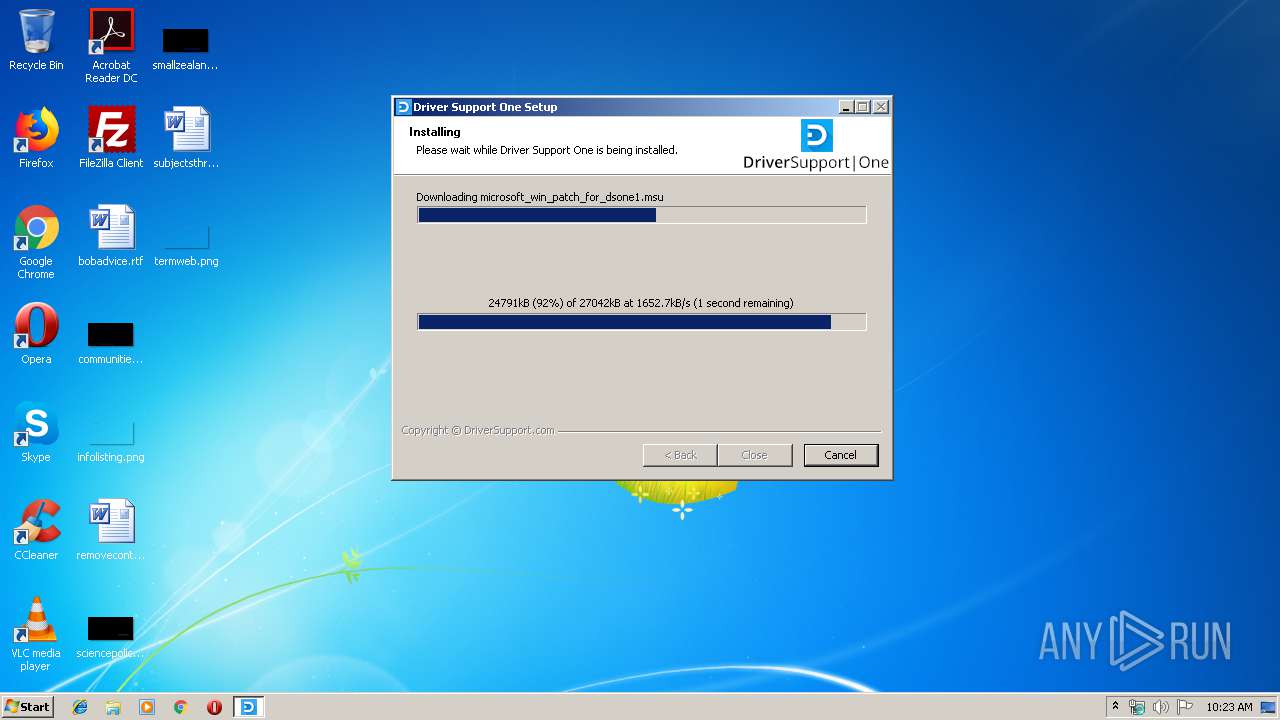
1876 | DSOne.exe | GET | 200 | 2.21.36.168:80 | http://download.microsoft.com/download/3/7/4/37473F39-5728-4153-9A25-64C09DE9ED52/Windows6.1-KB3033929-x86.msu | FR | compressed | 26.4 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1876 | DSOne.exe | 2.21.36.168:80 | download.microsoft.com | GTT Communications Inc. | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report