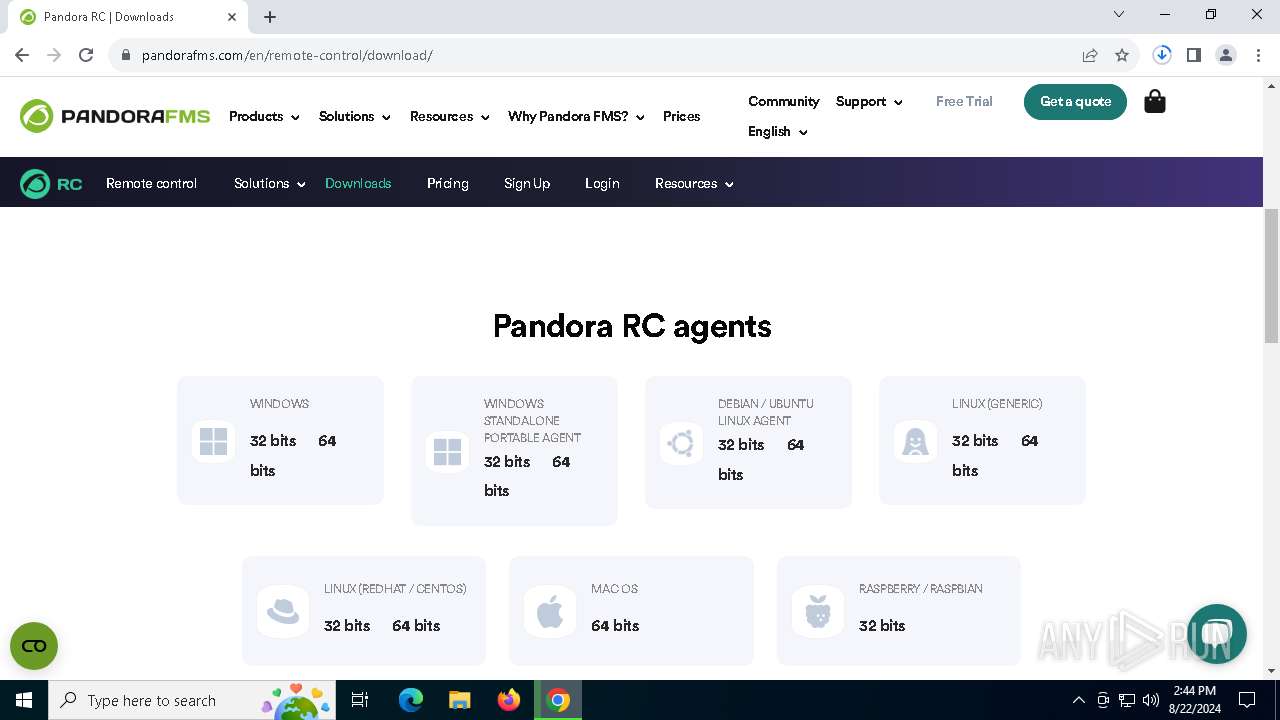
| URL: | ehorus.com |
| Full analysis: | https://app.any.run/tasks/44cd682d-ab3a-4d5b-a763-a67743226d45 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 14:44:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 1CCAD42ADD096FCFF650492D1E6B146F |
| SHA1: | 8D63647F0664041CEF3B5DA8D2F518490812B7FF |
| SHA256: | 335E457C6485BBA5A1B527829B9EF3E16D5E226EE3D3FE2F613274BEF51BB38F |
| SSDEEP: | 3:oRWLGKIn:oRMGKIn |
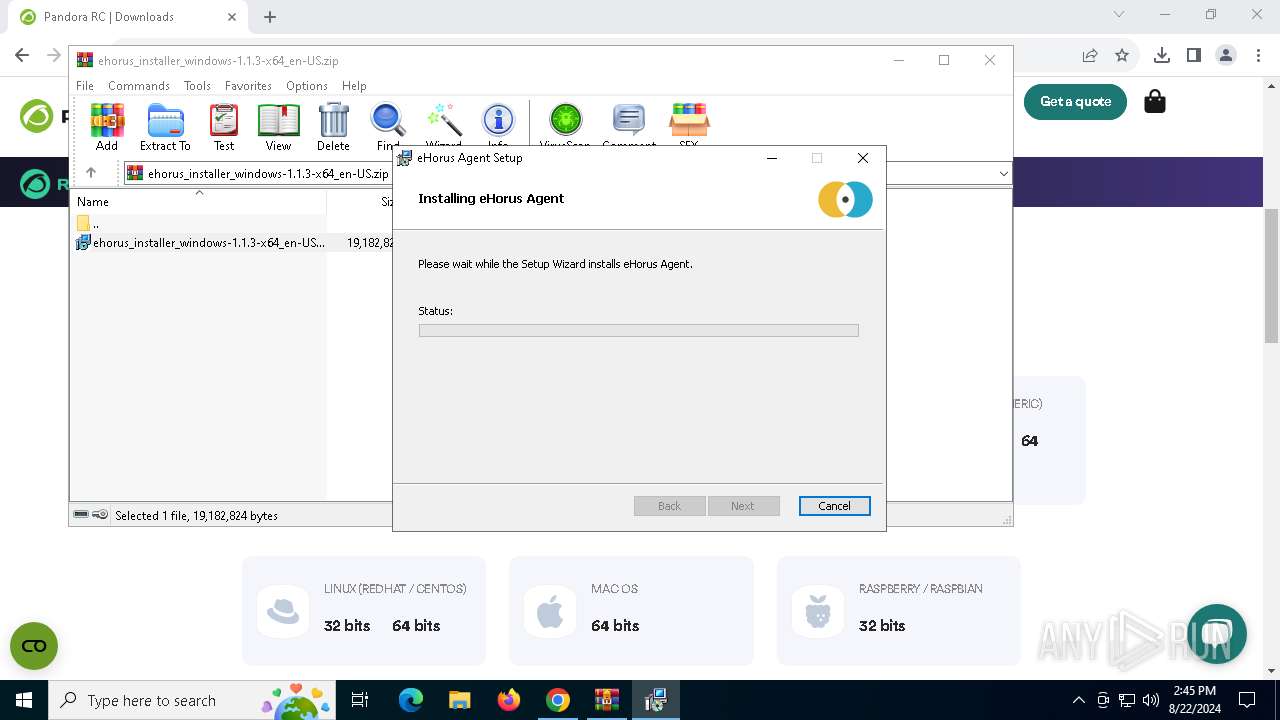
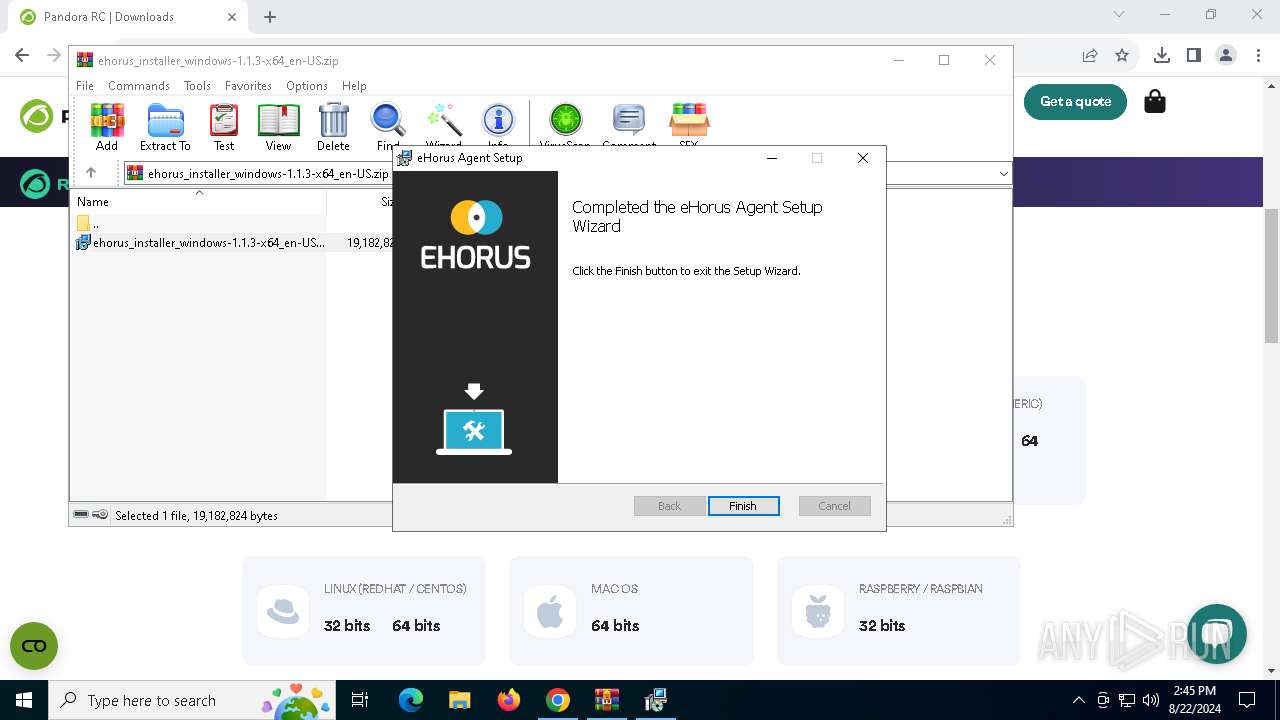
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 1344)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2268)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6388)
- rundll32.exe (PID: 7752)
- rundll32.exe (PID: 7860)
- rundll32.exe (PID: 6164)
- rundll32.exe (PID: 1640)
- rundll32.exe (PID: 4592)
- rundll32.exe (PID: 7416)
- rundll32.exe (PID: 7484)
- ehorus_agent.exe (PID: 7720)
- rundll32.exe (PID: 6348)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 2388)
- msiexec.exe (PID: 1432)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1344)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 7416)
Drops the executable file immediately after the start
- msiexec.exe (PID: 1344)
- ehorus_agent.exe (PID: 7720)
The process creates files with name similar to system file names
- msiexec.exe (PID: 1344)
Executes as Windows Service
- VSSVC.exe (PID: 4076)
- ehorus_launcher.exe (PID: 7728)
Detected use of alternative data streams (AltDS)
- ehorus_agent.exe (PID: 1752)
- ehorus_agent.exe (PID: 7720)
Uses TASKKILL.EXE to kill process
- ehorus_launcher.exe (PID: 7728)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6540)
- WinRAR.exe (PID: 2268)
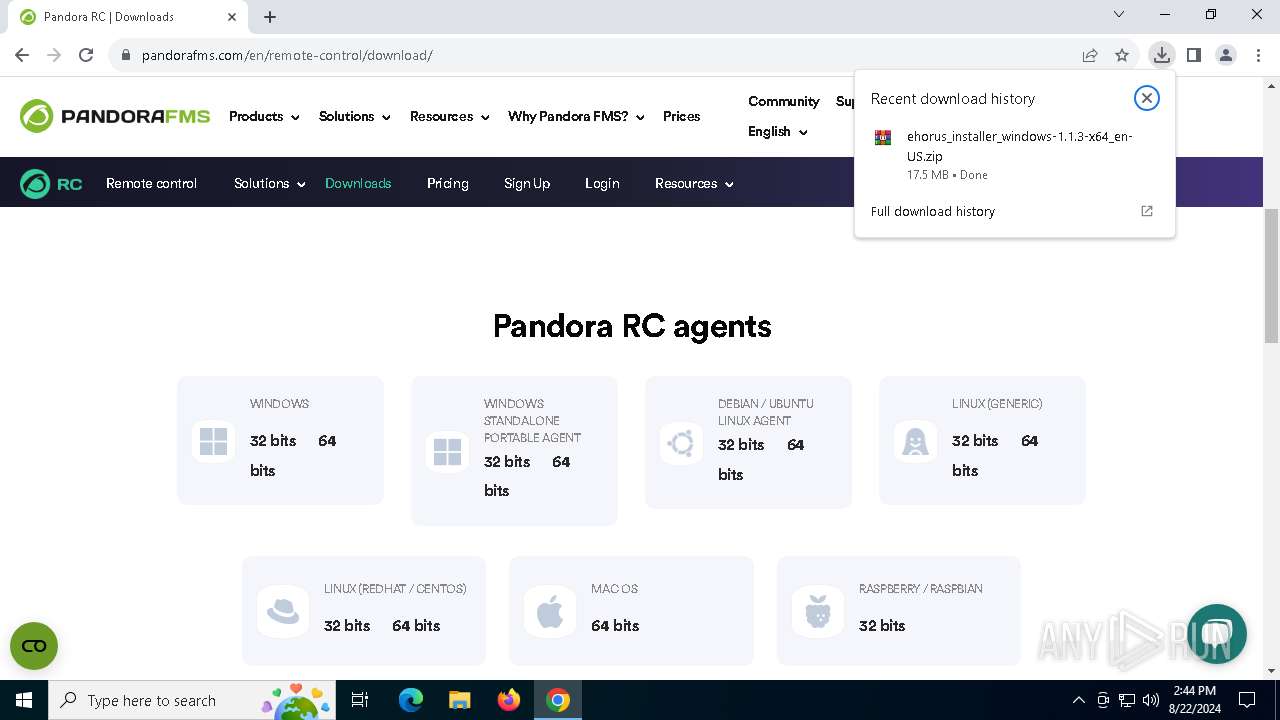
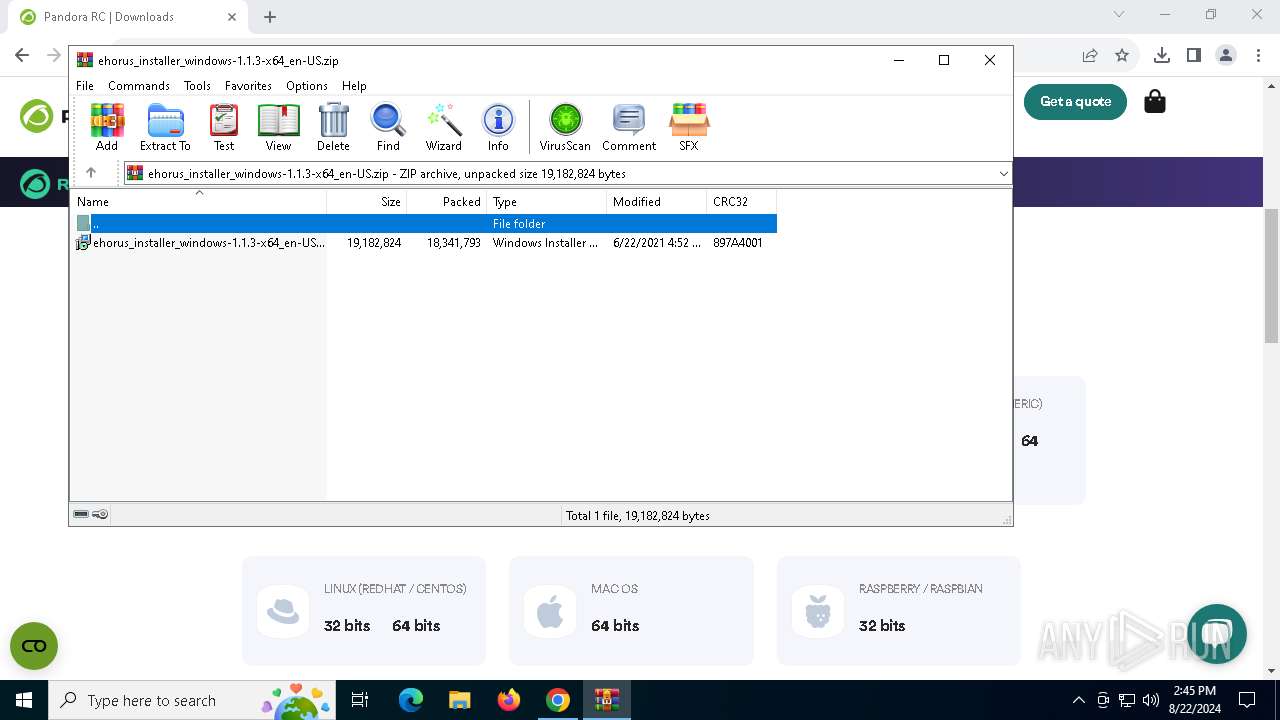
The process uses the downloaded file
- chrome.exe (PID: 6540)
- WinRAR.exe (PID: 2268)
- chrome.exe (PID: 7912)
Application launched itself
- chrome.exe (PID: 6540)
- msiexec.exe (PID: 1344)
Reads the computer name
- msiexec.exe (PID: 1344)
- msiexec.exe (PID: 2388)
- msiexec.exe (PID: 1432)
- ehorus_launcher.exe (PID: 7728)
- ehorus_agent.exe (PID: 1752)
- msiexec.exe (PID: 4168)
- ehorus_agent.exe (PID: 7720)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7332)
- msiexec.exe (PID: 1344)
- msiexec.exe (PID: 7680)
- chrome.exe (PID: 5852)
Checks supported languages
- msiexec.exe (PID: 1344)
- msiexec.exe (PID: 2388)
- msiexec.exe (PID: 1432)
- ehorus_launcher.exe (PID: 7728)
- ehorus_agent.exe (PID: 1752)
- msiexec.exe (PID: 4168)
- ehorus_agent.exe (PID: 7720)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 6388)
Create files in a temporary directory
- rundll32.exe (PID: 7752)
- rundll32.exe (PID: 6164)
- rundll32.exe (PID: 7860)
- rundll32.exe (PID: 6388)
Creates files in the program directory
- ehorus_agent.exe (PID: 7720)
- ehorus_agent.exe (PID: 1752)
Creates a software uninstall entry
- msiexec.exe (PID: 1344)
Reads the machine GUID from the registry
- ehorus_agent.exe (PID: 1752)
- ehorus_agent.exe (PID: 7720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
61
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ehorus_agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5416 --field-trial-handle=1896,i,13313085942244210596,15579556267139612857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
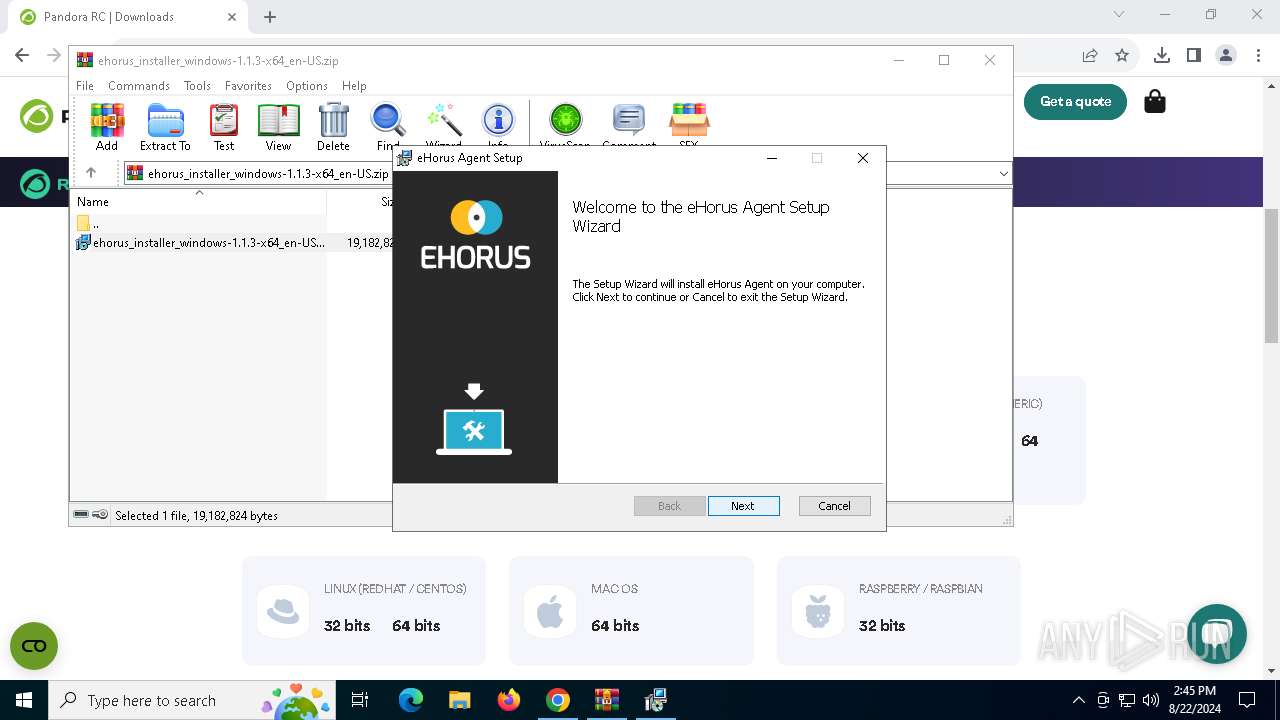
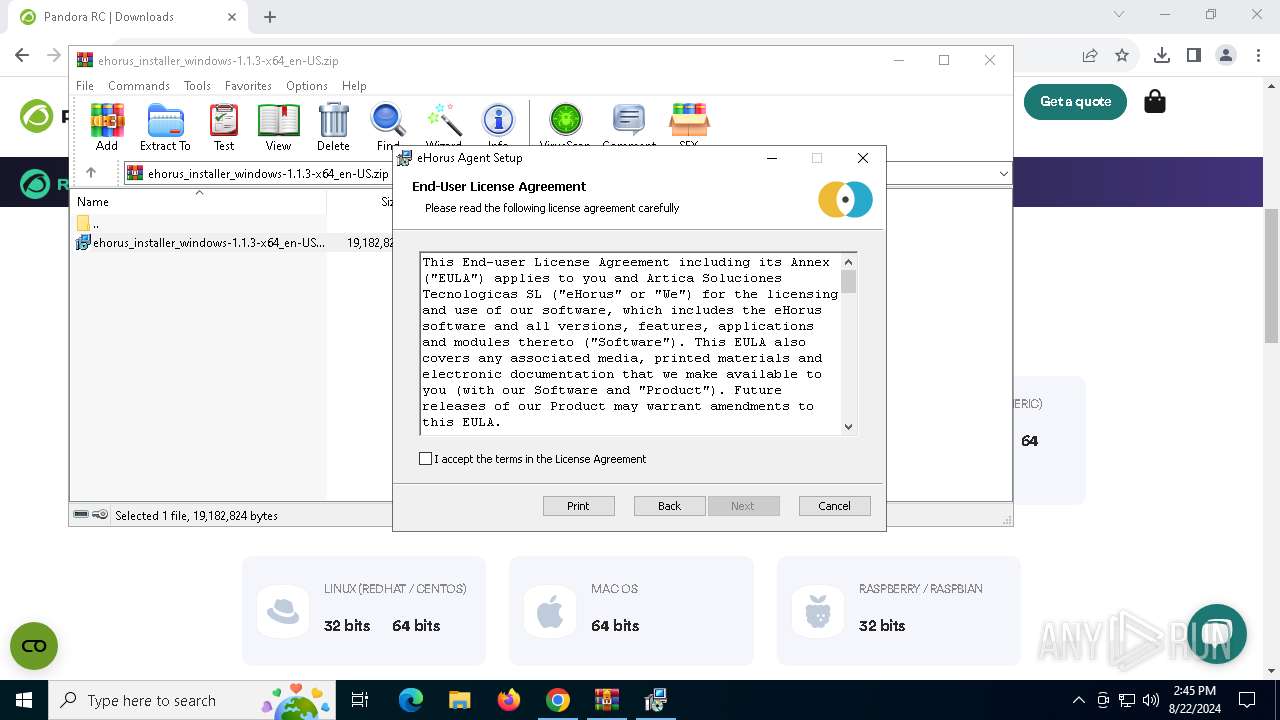
| 1344 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | C:\Windows\System32\MsiExec.exe -Embedding 7684017D8264E8F0250312DFF9D11A56 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | taskkill /F /IM "ehorus_display.exe" | C:\Windows\SysWOW64\taskkill.exe | — | ehorus_launcher.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1640 | rundll32.exe "C:\WINDOWS\Installer\MSI4D39.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1265531 2 eHorusMsiCustomActions!eHorusMsiCustomActions.CustomActions.ExecuteNsisUninstaller | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Program Files\ehorus_agent\ehorus_agent.exe" -f "C:\Program Files\ehorus_agent\ehorus_agent.conf" -d | C:\Program Files\ehorus_agent\ehorus_agent.exe | — | ehorus_launcher.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 1.1.3.0 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5212 --field-trial-handle=1896,i,13313085942244210596,15579556267139612857,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
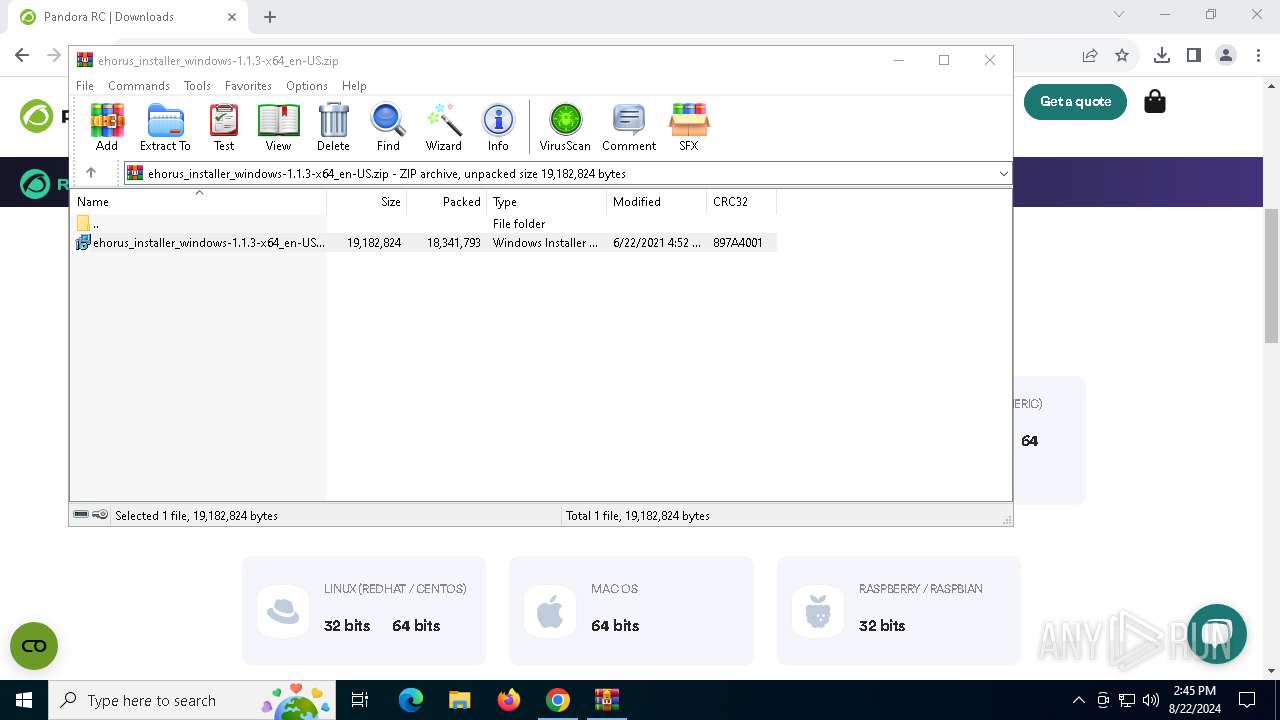
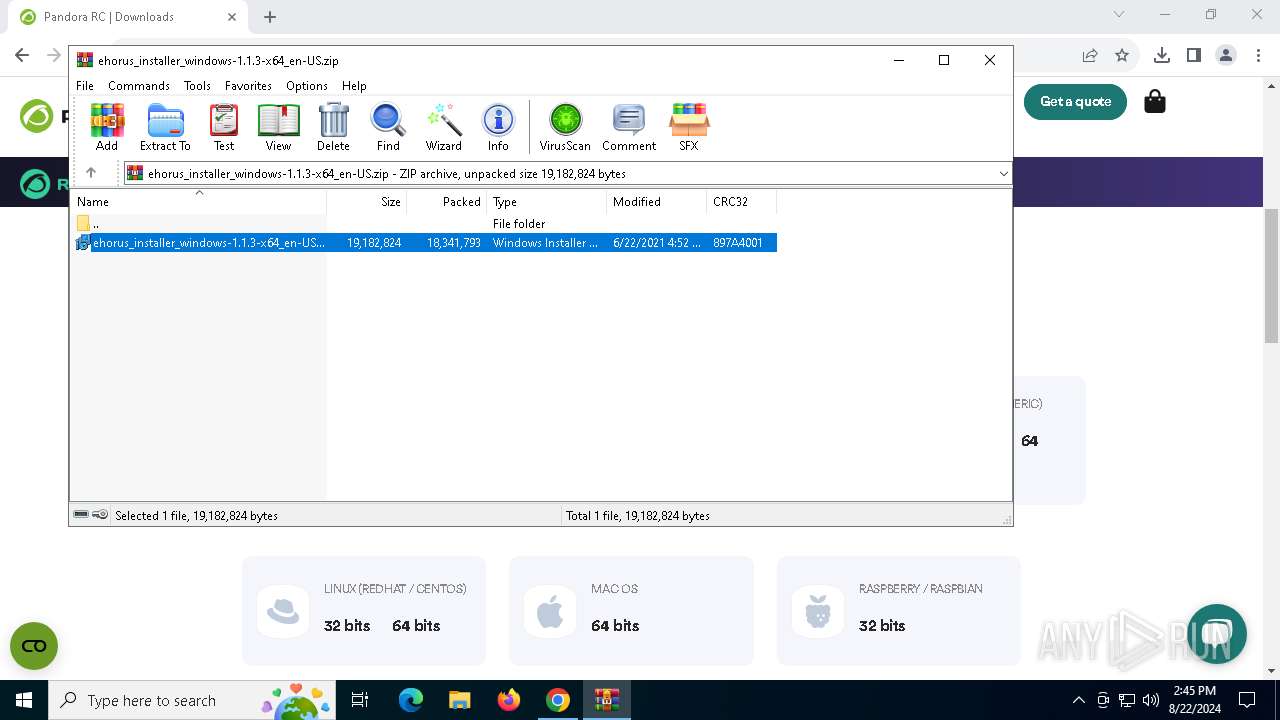
| 2268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ehorus_installer_windows-1.1.3-x64_en-US.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2388 | C:\Windows\System32\MsiExec.exe -Embedding 4BD1DFF0C2F8B149A77F7A2222606BC1 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 408
Read events
29 007
Write events
376
Delete events
25
Modification events
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
82
Suspicious files
432
Text files
56
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF11e471.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11e471.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11e462.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:FCE53E052E5CF7C20819320F374DEA88 | SHA256:CD95DE277E746E92CC2C53D9FC92A8F6F0C3EDFB7F1AD9A4E9259F927065BC89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
91
DNS requests
108
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6356 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7988 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nd7vu5lglswh3vpwf4lswivh4u_2024.8.21.1/jflhchccmppkfebkiaminageehmchikm_2024.08.21.01_all_ackxrq2vkwy5u5364idlfp6aj7nq.crx3 | unknown | — | — | whitelisted |
3980 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7792 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7988 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
7988 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
7988 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
7988 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | unknown | — | — | whitelisted |
7988 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nd7vu5lglswh3vpwf4lswivh4u_2024.8.21.1/jflhchccmppkfebkiaminageehmchikm_2024.08.21.01_all_ackxrq2vkwy5u5364idlfp6aj7nq.crx3 | unknown | — | — | whitelisted |
7988 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nd7vu5lglswh3vpwf4lswivh4u_2024.8.21.1/jflhchccmppkfebkiaminageehmchikm_2024.08.21.01_all_ackxrq2vkwy5u5364idlfp6aj7nq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4704 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3992 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6540 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6792 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
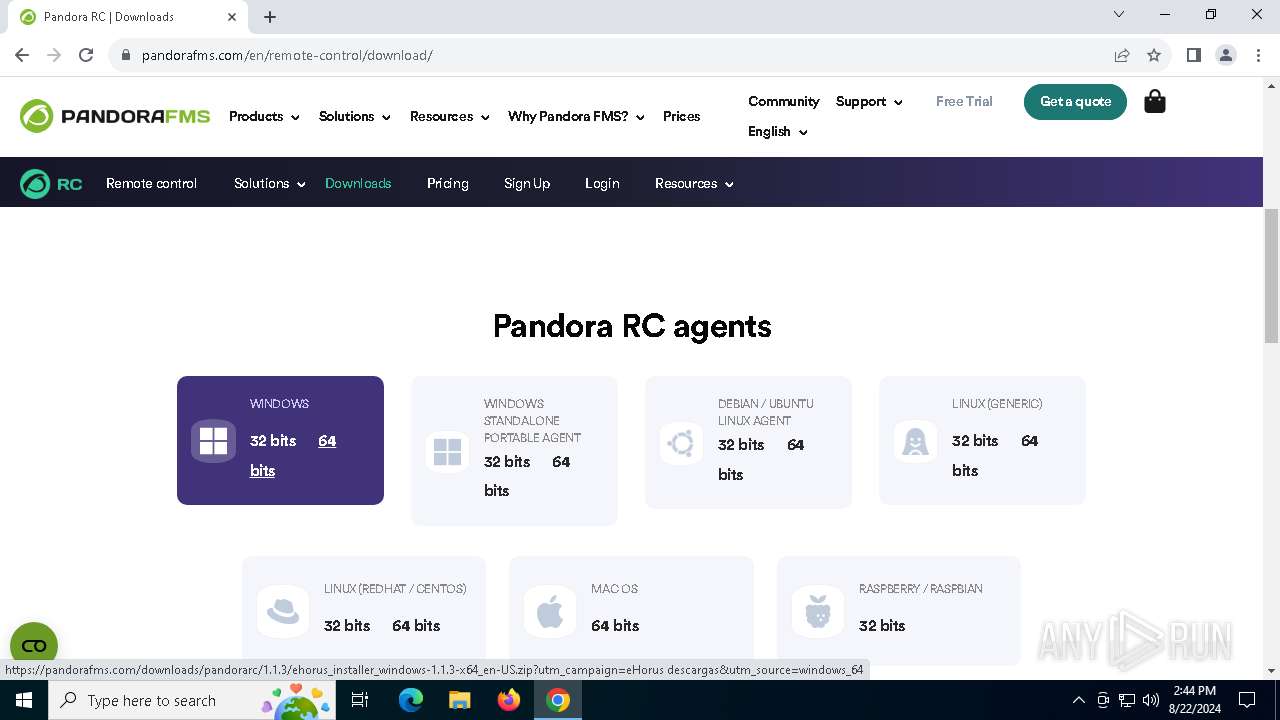
6792 | chrome.exe | 172.67.181.250:443 | ehorus.com | CLOUDFLARENET | US | unknown |
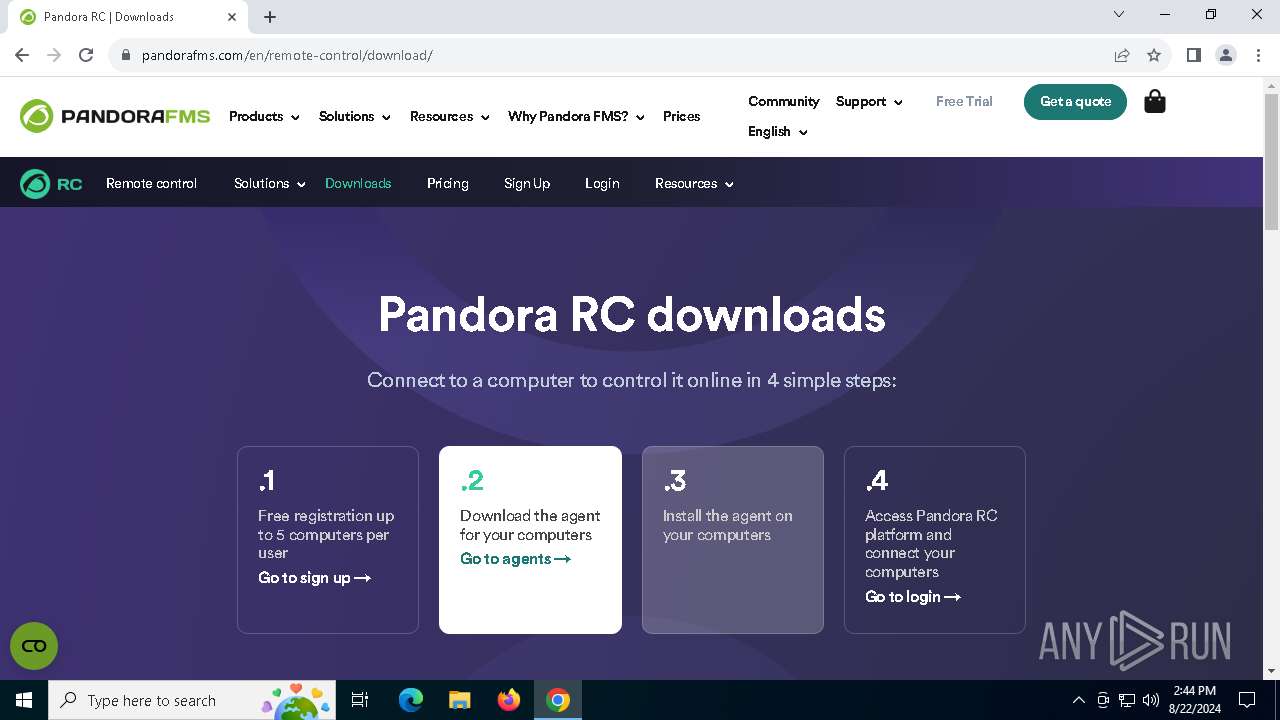
6792 | chrome.exe | 172.66.40.150:443 | pandorafms.com | CLOUDFLARENET | US | unknown |
6792 | chrome.exe | 2.18.64.31:443 | consent.cookiebot.com | Administracion Nacional de Telecomunicaciones | UY | unknown |
6792 | chrome.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ehorus.com |
| malicious |
accounts.google.com |
| whitelisted |
pandorafms.com |
| unknown |
consent.cookiebot.com |
| whitelisted |
stats.wp.com |
| whitelisted |
js.hs-scripts.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pixel.wp.com |
| whitelisted |
b.sf-syn.com |
| unknown |