| File name: | Ssp2mk.exe |
| Full analysis: | https://app.any.run/tasks/ea8e0d3a-81b5-4662-bd84-e35e63f082b6 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2024, 00:24:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable PE32 executable (GUI) Intel 80386, for MS Windows, MZ for MS-DOS |
| MD5: | 7A9BEF390A529FFCF25A9853E8118D0A |
| SHA1: | 1062AF123878B7A345E31EBFFC3F18A48633DA9A |
| SHA256: | 33390316291F844A351591D5763ACE398076EE0CCA6F0E32C8103791993C39BE |
| SSDEEP: | 24576:5cPNsBWzSTX5rfQQ42euti4uf56boXbCQ4NDEtn5a+D692xO:5cKBWzSTX5rfQQ42euti4uf56boXbCTB |
MALICIOUS
Drops the executable file immediately after the start
- Ssp2mk.exe (PID: 3660)
- icsys.icn.exe (PID: 2964)
- explorer.exe (PID: 2752)
- spoolsv.exe (PID: 3848)
Changes the autorun value in the registry
- svchost.exe (PID: 3948)
- explorer.exe (PID: 2752)
Changes appearance of the Explorer extensions
- explorer.exe (PID: 2752)
- svchost.exe (PID: 3948)
SUSPICIOUS
Executable content was dropped or overwritten
- Ssp2mk.exe (PID: 3660)
- icsys.icn.exe (PID: 2964)
- explorer.exe (PID: 2752)
- spoolsv.exe (PID: 3848)
Starts application with an unusual extension
- Ssp2mk.exe (PID: 3660)
Starts itself from another location
- Ssp2mk.exe (PID: 3660)
- icsys.icn.exe (PID: 2964)
- explorer.exe (PID: 2752)
- spoolsv.exe (PID: 3848)
- svchost.exe (PID: 3948)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 2964)
- spoolsv.exe (PID: 3848)
Creates or modifies Windows services
- svchost.exe (PID: 3948)
INFO
Checks supported languages
- Ssp2mk.exe (PID: 3660)
- ssp2mk.exe (PID: 2852)
- icsys.icn.exe (PID: 2964)
- explorer.exe (PID: 2752)
- spoolsv.exe (PID: 3848)
- spoolsv.exe (PID: 3464)
- svchost.exe (PID: 3948)
Reads the computer name
- ssp2mk.exe (PID: 2852)
- svchost.exe (PID: 3948)
Reads the machine GUID from the registry
- Ssp2mk.exe (PID: 3660)
- icsys.icn.exe (PID: 2964)
- explorer.exe (PID: 2752)
- spoolsv.exe (PID: 3848)
- svchost.exe (PID: 3948)
- spoolsv.exe (PID: 3464)
Create files in a temporary directory
- Ssp2mk.exe (PID: 3660)
- icsys.icn.exe (PID: 2964)
- explorer.exe (PID: 2752)
- svchost.exe (PID: 3948)
- spoolsv.exe (PID: 3848)
- spoolsv.exe (PID: 3464)
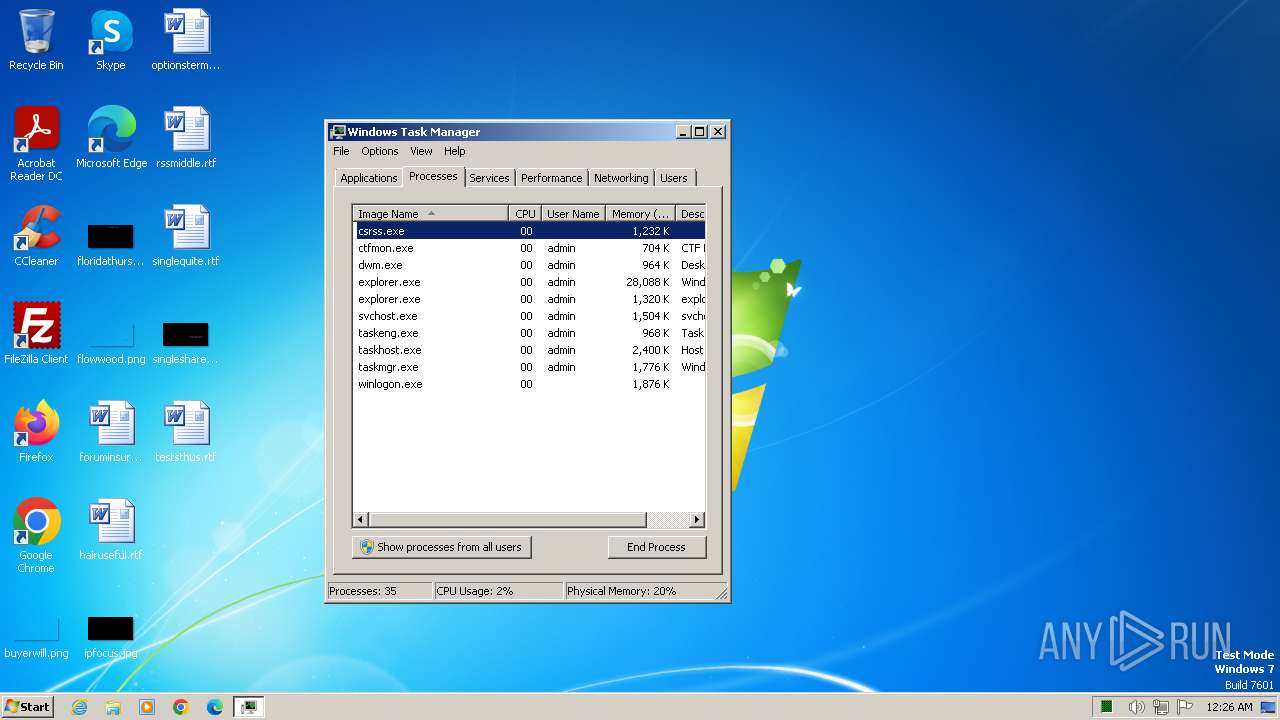
Manual execution by a user
- taskmgr.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
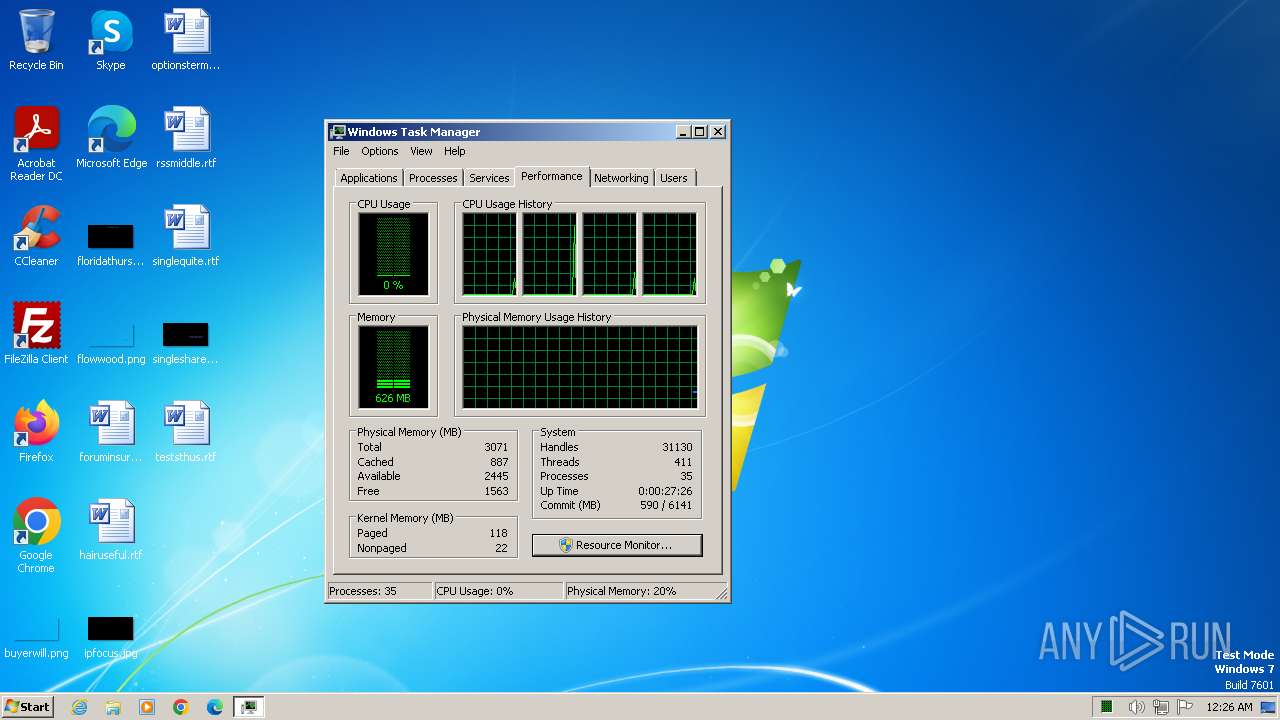
Total processes
53
Monitored processes
12
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2444 | schtasks /create /tn "svchost" /tr "c:\windows\resources\svchost.exe" /sc daily /st 00:26 /f | C:\Windows\System32\schtasks.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2752 | c:\windows\resources\themes\explorer.exe | C:\Windows\resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2852 | c:\users\admin\appdata\local\temp\ssp2mk.exe | C:\Users\admin\AppData\Local\Temp\ssp2mk.exe | — | Ssp2mk.exe | |||||||||||
User: admin Company: Don't mess with concrete Integrity Level: HIGH Description: Sentinel SuperPro Dumper/Solver for Multikey Exit code: 2 Version: 1.2.0.1 Modules
| |||||||||||||||
| 2964 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | Ssp2mk.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3464 | c:\windows\resources\spoolsv.exe PR | C:\Windows\resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\Ssp2mk.exe" | C:\Users\admin\AppData\Local\Temp\Ssp2mk.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3684 | schtasks /create /tn "svchost" /tr "c:\windows\resources\svchost.exe" /sc daily /st 00:28 /f | C:\Windows\System32\schtasks.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\Ssp2mk.exe" | C:\Users\admin\AppData\Local\Temp\Ssp2mk.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 3848 | c:\windows\resources\spoolsv.exe SE | C:\Windows\resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
1 018
Read events
989
Write events
25
Delete events
4
Modification events
| (PID) Process: | (3660) Ssp2mk.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (2964) icsys.icn.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (2752) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (2752) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (2752) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (2752) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (3948) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (3948) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (3948) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (3948) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF662A9B9EB5012B38.TMP | binary | |
MD5:7FD486CF6039BB673CC249ABE9BF0286 | SHA256:3C9340B399120070AFBF21B3A97FAD6FA31F6227F6D558AF82AC2FC447F8F64E | |||
| 3464 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFB382354C4C9013AE.TMP | binary | |
MD5:7FD486CF6039BB673CC249ABE9BF0286 | SHA256:3C9340B399120070AFBF21B3A97FAD6FA31F6227F6D558AF82AC2FC447F8F64E | |||
| 3660 | Ssp2mk.exe | C:\users\admin\appdata\local\temp\ssp2mk.exe | executable | |
MD5:6404E8BFB745C31179B97238B21514D1 | SHA256:E96CF212CC8A0E6C950D90D3123A24AB43A477351577B8DBA72F4FB6D2668D02 | |||
| 2964 | icsys.icn.exe | C:\windows\resources\themes\explorer.exe | executable | |
MD5:07A06DD7714AF9E1E70F6F7490BE8633 | SHA256:365491A252504219B190B82855E06ED5EFDFDE7F981E09A363276C34C7A6FCBF | |||
| 2964 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF32C9D8F78D6A2B96.TMP | binary | |
MD5:D798DE7BC9295855835F6119AB6D0B4A | SHA256:BD2D67220ED17B2D2FE38857349D9D6164C29BD6FC0DBC83DCFC1CE0C10E9753 | |||
| 3848 | spoolsv.exe | C:\windows\resources\svchost.exe | executable | |
MD5:DD05AA7A86E9B16D73096A17990BFA26 | SHA256:9E63FD975AE820AB78EA39AB4596BBCABA7B7E8278295918BDBE010F72BC301A | |||
| 2752 | explorer.exe | C:\windows\resources\spoolsv.exe | executable | |
MD5:FA9B286C2F7C71AFE220964A57FE384F | SHA256:81BEABB8F61BA14B5ABC8B14283D0BD8E0E96DAD63271FC5BB14F401BD8C6C06 | |||
| 3660 | Ssp2mk.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:3DCE746009DFB480A35E3FEF45C3CE09 | SHA256:D302351FA72FB8BA8BC28AB5FDA6387807E3D743CAD5BD388AD79F453654C2D8 | |||
| 3660 | Ssp2mk.exe | C:\Users\admin\AppData\Local\Temp\~DFBA42CF71360750DF.TMP | binary | |
MD5:4DD8AD2CB18451BE0AFED090CE4DD1AB | SHA256:8E6ECF264ECE941E7FD35D777179A92C5049687918E3DBDC6D84E7C78E4C4EAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |