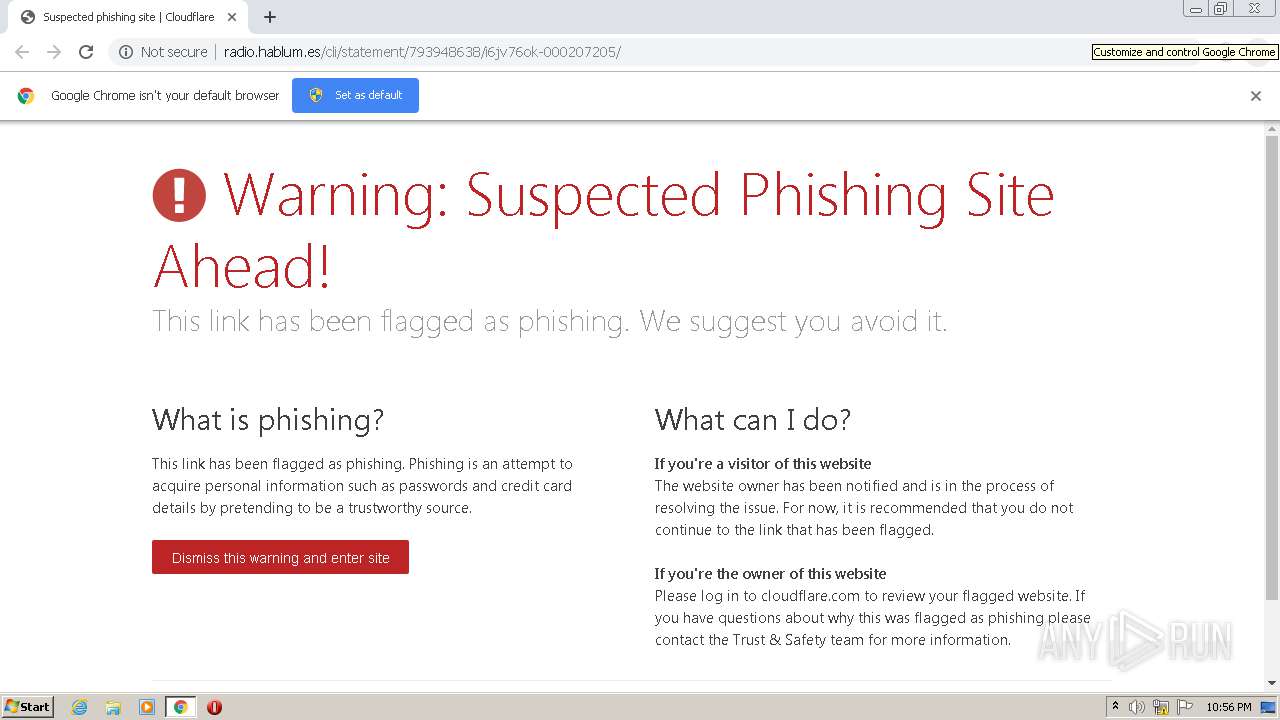
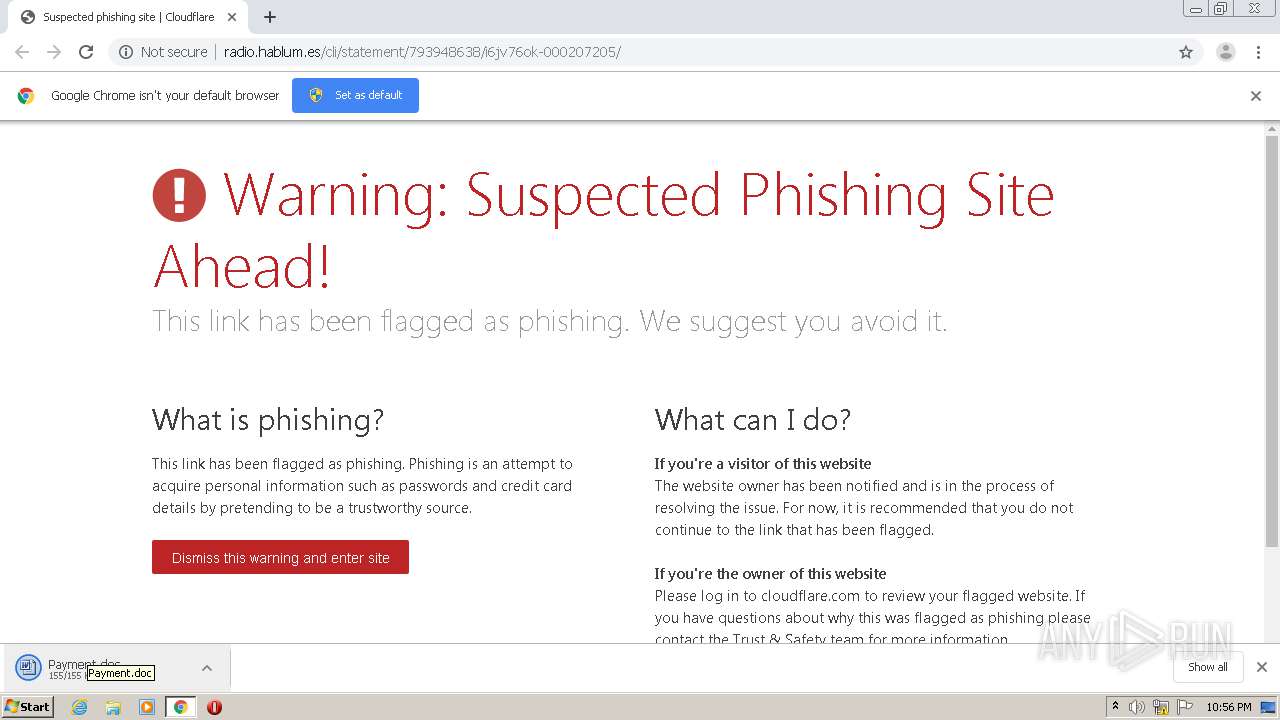
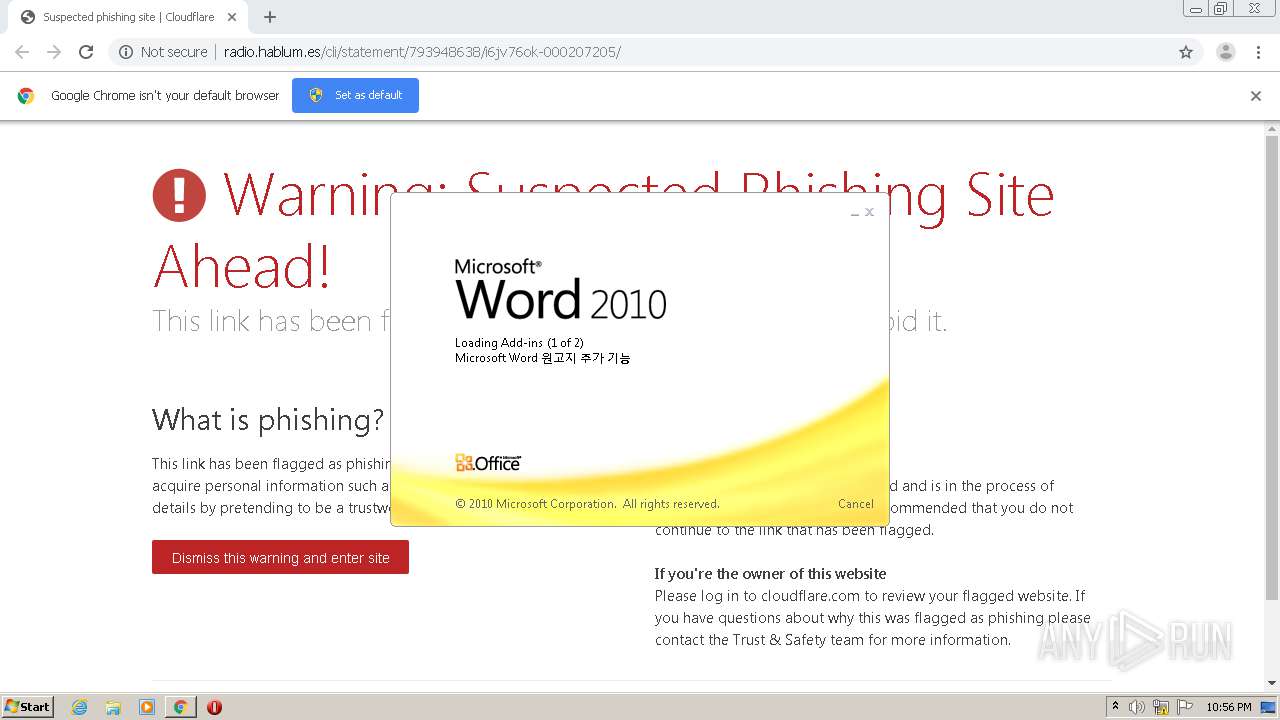
| URL: | http://radio.hablum.es/cli/statement/793948638/i6jv76ok-000207205/ |
| Full analysis: | https://app.any.run/tasks/c60ddb89-7a25-4604-9eb2-e7aef7bac152 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 21:56:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 24B5A47EE11461C6F5B8C9672A6FB6FF |
| SHA1: | 26FE43697E3857148E1D66CA502A85C6BDB5343E |
| SHA256: | 3332B9307FF486C673D9D2A799532B11369E1781AFCE8C151C47A93F9D83D6F1 |
| SSDEEP: | 3:N1KMRK5ubAWLMNR4tuRSWcGVrPOIdC:CMr4NR4YRSWcorPOH |
MALICIOUS
Application was dropped or rewritten from another process
- Stwk31v.exe (PID: 3696)
- dhcpcore6.exe (PID: 2096)
EMOTET was detected
- dhcpcore6.exe (PID: 2096)
Changes the autorun value in the registry
- dhcpcore6.exe (PID: 2096)
Connects to CnC server
- dhcpcore6.exe (PID: 2096)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3528)
SUSPICIOUS
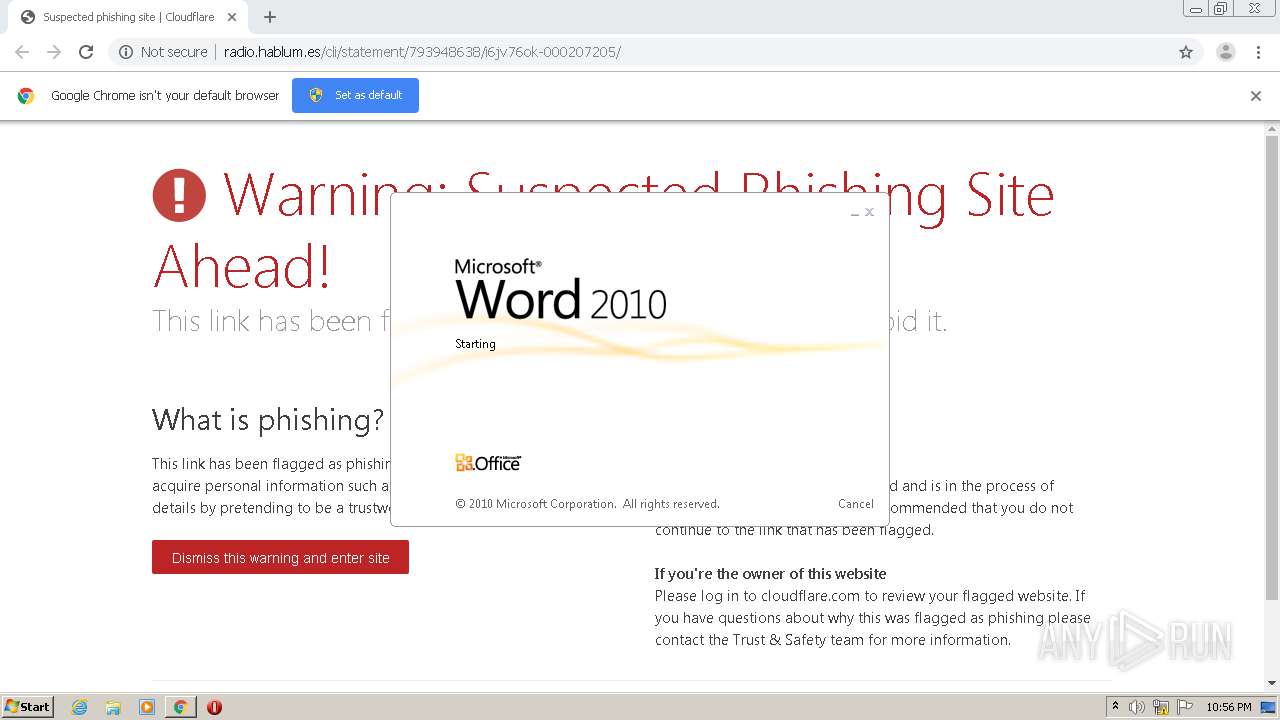
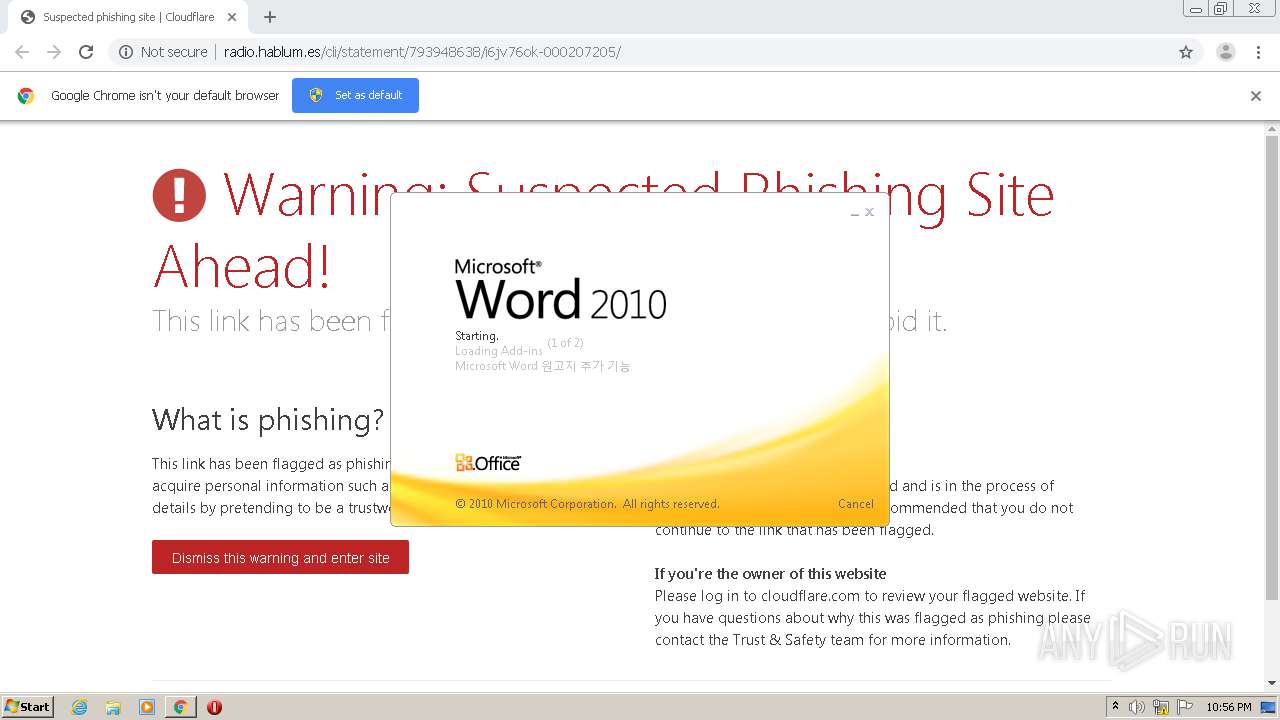
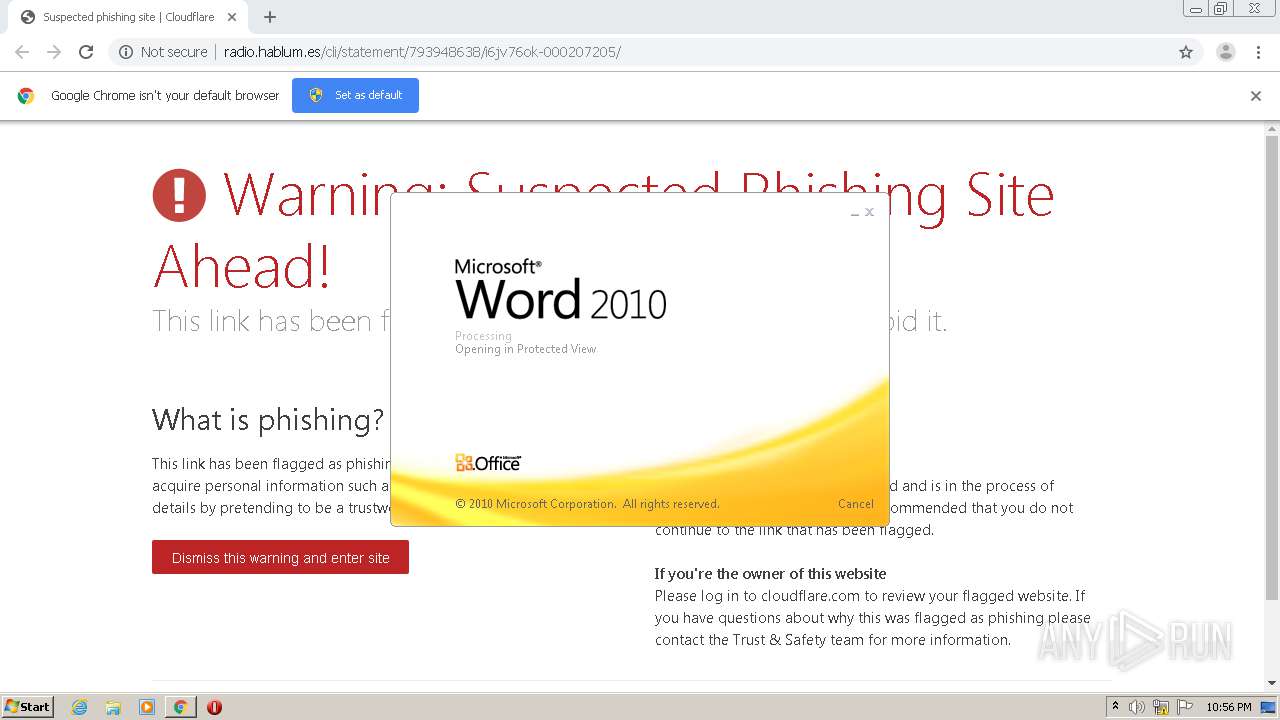
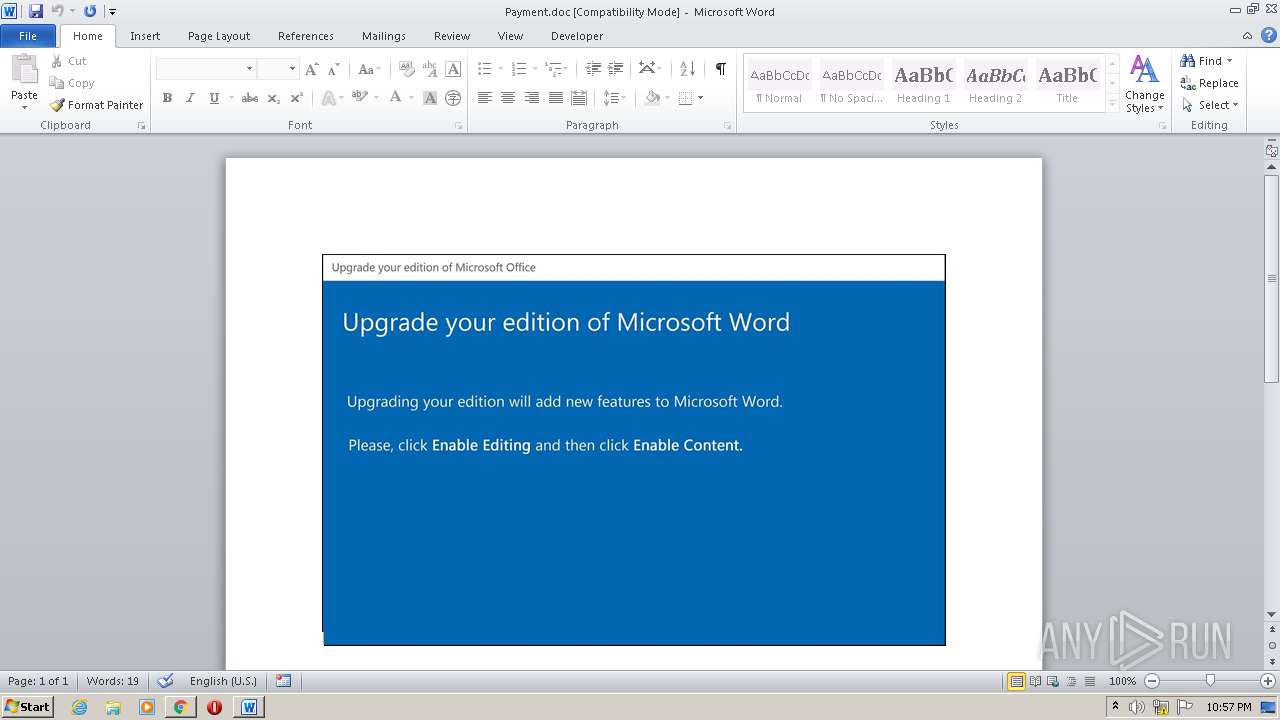
Starts Microsoft Office Application
- chrome.exe (PID: 2516)
- WINWORD.EXE (PID: 2944)
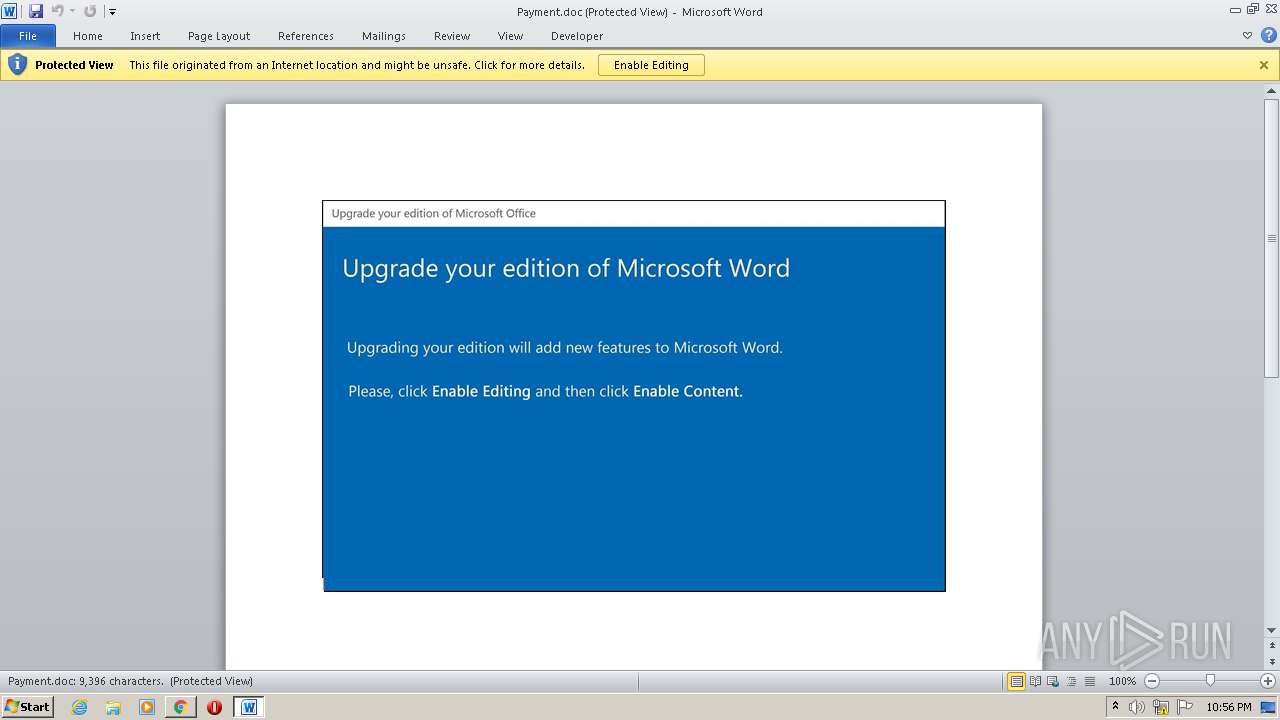
Application launched itself
- WINWORD.EXE (PID: 2944)
Executed via WMI
- POwersheLL.exe (PID: 3528)
- Stwk31v.exe (PID: 3696)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3528)
- Stwk31v.exe (PID: 3696)
PowerShell script executed
- POwersheLL.exe (PID: 3528)
Creates files in the user directory
- POwersheLL.exe (PID: 3528)
Starts itself from another location
- Stwk31v.exe (PID: 3696)
Reads Internet Cache Settings
- dhcpcore6.exe (PID: 2096)
INFO
Reads the hosts file
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3948)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3948)
- chrome.exe (PID: 2516)
- WINWORD.EXE (PID: 2944)
Application launched itself
- chrome.exe (PID: 2516)
Reads Internet Cache Settings
- chrome.exe (PID: 2516)
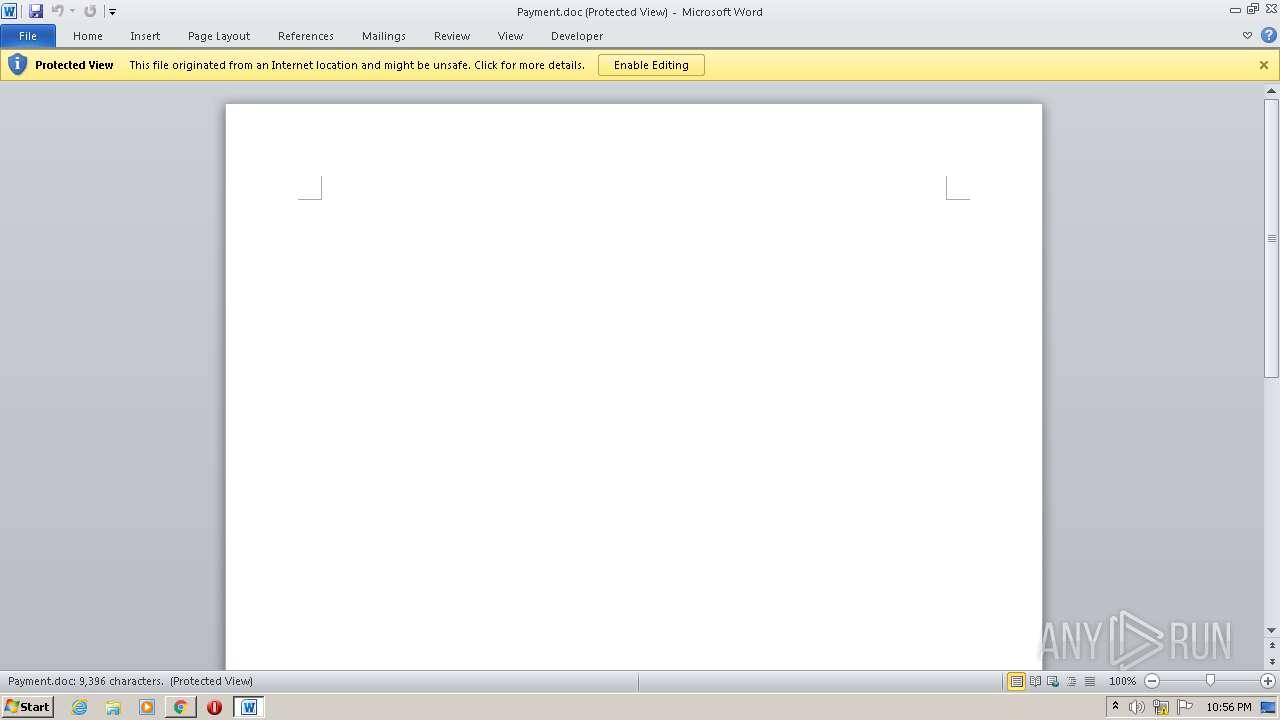
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2944)
- WINWORD.EXE (PID: 3844)
Reads settings of System Certificates
- chrome.exe (PID: 3948)
Creates files in the user directory
- WINWORD.EXE (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
18
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,7384063098447445365,18019515117784430353,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1319971005825396164 --mojo-platform-channel-handle=3776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,7384063098447445365,18019515117784430353,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12945254381967942877 --mojo-platform-channel-handle=3876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,7384063098447445365,18019515117784430353,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12139630962042390345 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,7384063098447445365,18019515117784430353,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12684245026856694615 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\at\dhcpcore6.exe" | C:\Users\admin\AppData\Local\at\dhcpcore6.exe | Stwk31v.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2504 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://radio.hablum.es/cli/statement/793948638/i6jv76ok-000207205/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Payment.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,7384063098447445365,18019515117784430353,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5565388727181752166 --mojo-platform-channel-handle=4004 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 754
Read events
2 767
Write events
785
Delete events
202
Modification events
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2516-13247618201039250 |
Value: 259 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2516-13247618201039250 |
Value: 259 | |||
Executable files
2
Suspicious files
16
Text files
80
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E0B99-9D4.pma | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\122fa0de-f7e3-47fe-879d-ac1017296712.tmp | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d4153.TMP | text | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2d41a1.TMP | text | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
23
DNS requests
14
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3948 | chrome.exe | GET | 200 | 172.67.72.250:80 | http://radio.hablum.es/cdn-cgi/styles/cf.errors.css | US | text | 4.32 Kb | suspicious |
3528 | POwersheLL.exe | GET | 200 | 172.67.151.128:80 | http://dp-womenbasket.com/wp-admin/Li/ | US | html | 4.18 Kb | suspicious |
3528 | POwersheLL.exe | GET | 200 | 172.67.192.55:80 | http://tudorinvest.com/wp-admin/rGtnUb5f/ | US | html | 4.19 Kb | malicious |
2096 | dhcpcore6.exe | POST | — | 91.121.87.90:8080 | http://91.121.87.90:8080/IuFVTBOPnMiF4c/584dY94LoHG0O/HEk3Pz2/FG6kw1/W2iAjO8lnVhTFC5POjm/ | FR | — | — | malicious |
3528 | POwersheLL.exe | GET | 200 | 35.189.10.17:80 | http://stylefix.co/guillotine-cross/CTRNOQ/ | US | executable | 578 Kb | malicious |
3948 | chrome.exe | GET | 200 | 172.67.72.250:80 | http://radio.hablum.es/cdn-cgi/images/icon-exclamation.png?1376755637 | US | image | 452 b | suspicious |
3948 | chrome.exe | GET | 301 | 172.67.72.250:80 | http://radio.hablum.es/favicon.ico | US | image | 452 b | suspicious |
3948 | chrome.exe | GET | 301 | 172.67.72.250:80 | http://radio.hablum.es/cli/statement/793948638/i6jv76ok-000207205/ | US | html | 167 b | suspicious |
2096 | dhcpcore6.exe | POST | — | 177.130.51.198:80 | http://177.130.51.198/jXI1KTV/F54nmMHInkw2ch/8txaKwvmXmAeiZa/nye9NOeRjfoYwzurc/ | BR | — | — | malicious |
2096 | dhcpcore6.exe | POST | 200 | 104.131.144.215:8080 | http://104.131.144.215:8080/r2LaPxSlHTn4ErtF/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3948 | chrome.exe | 172.67.72.250:80 | radio.hablum.es | — | US | suspicious |
3948 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
3948 | chrome.exe | 216.58.208.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3948 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3948 | chrome.exe | 104.26.13.30:443 | radio.hablum.es | Cloudflare Inc | US | unknown |
3528 | POwersheLL.exe | 172.67.192.55:80 | tudorinvest.com | — | US | suspicious |
3528 | POwersheLL.exe | 172.67.151.128:80 | dp-womenbasket.com | — | US | suspicious |
3528 | POwersheLL.exe | 35.189.10.17:80 | stylefix.co | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
radio.hablum.es |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.cloudflare.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
tudorinvest.com |
| malicious |
dp-womenbasket.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3948 | chrome.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
3528 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3528 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3528 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2096 | dhcpcore6.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2096 | dhcpcore6.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3528 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
2 ETPRO signatures available at the full report