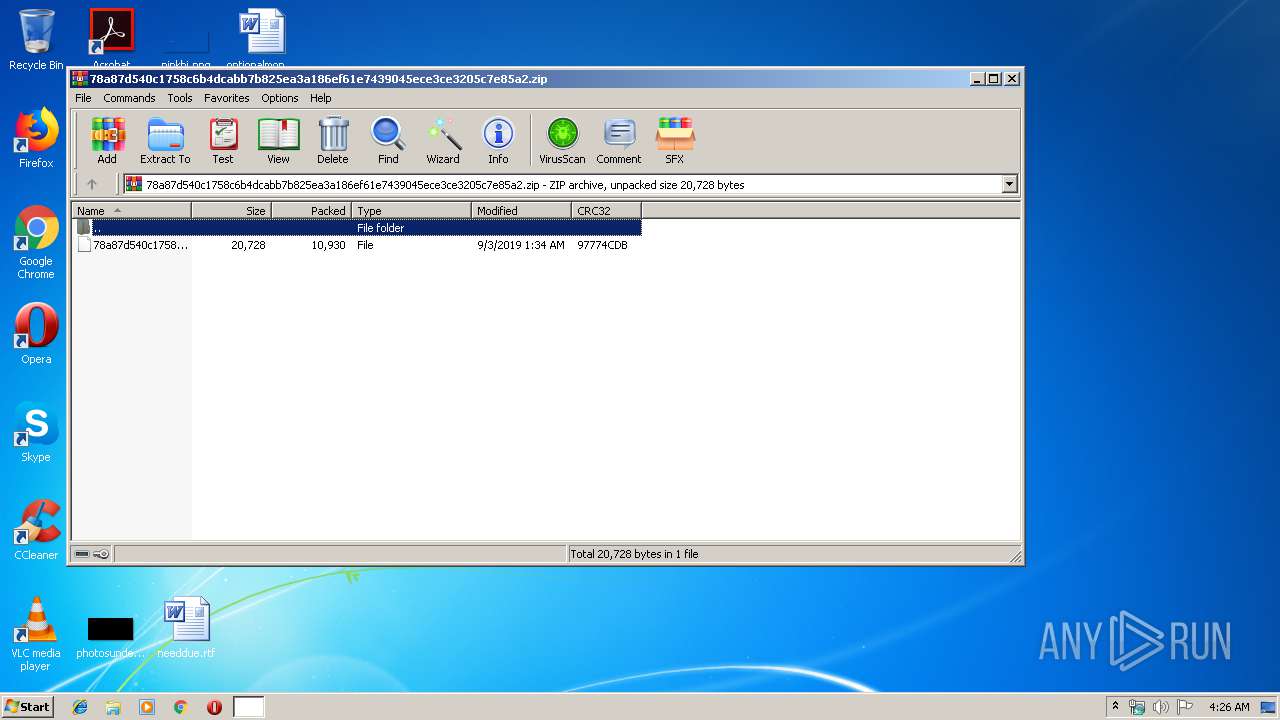
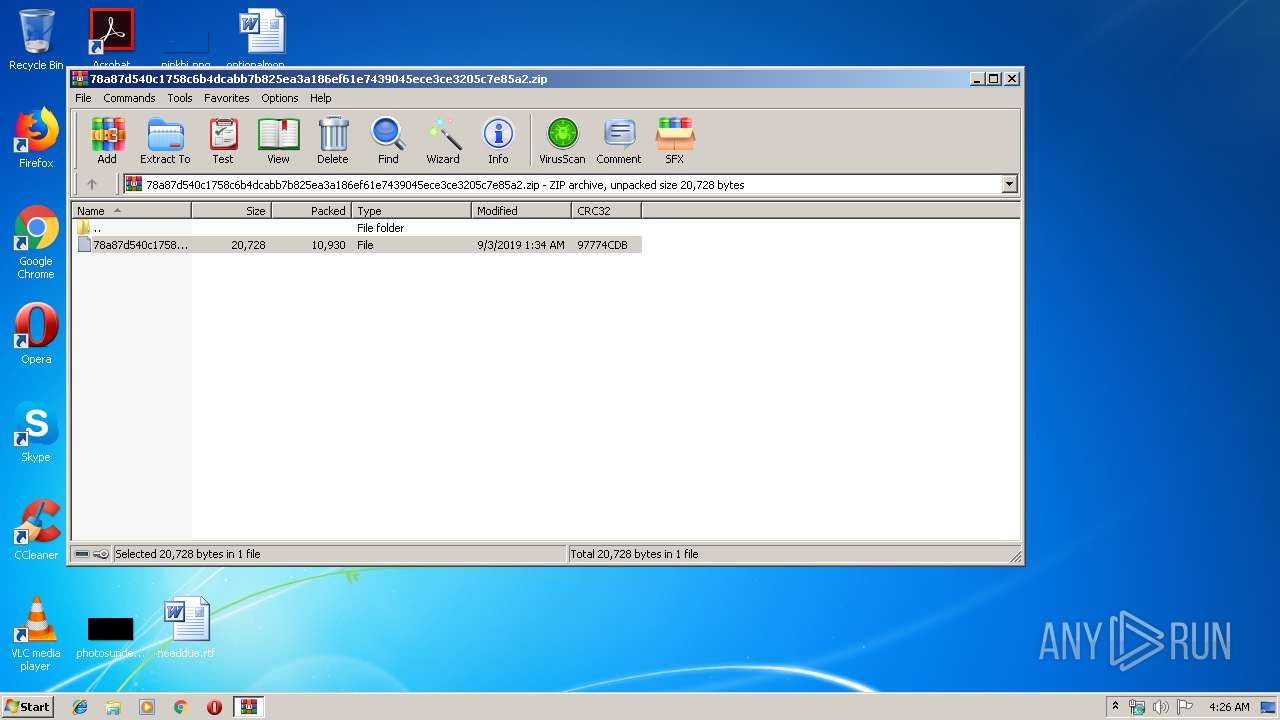
| File name: | 78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2.zip |
| Full analysis: | https://app.any.run/tasks/af35c7be-1fb1-4930-9667-56aeb1540bf9 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 03:26:15 |
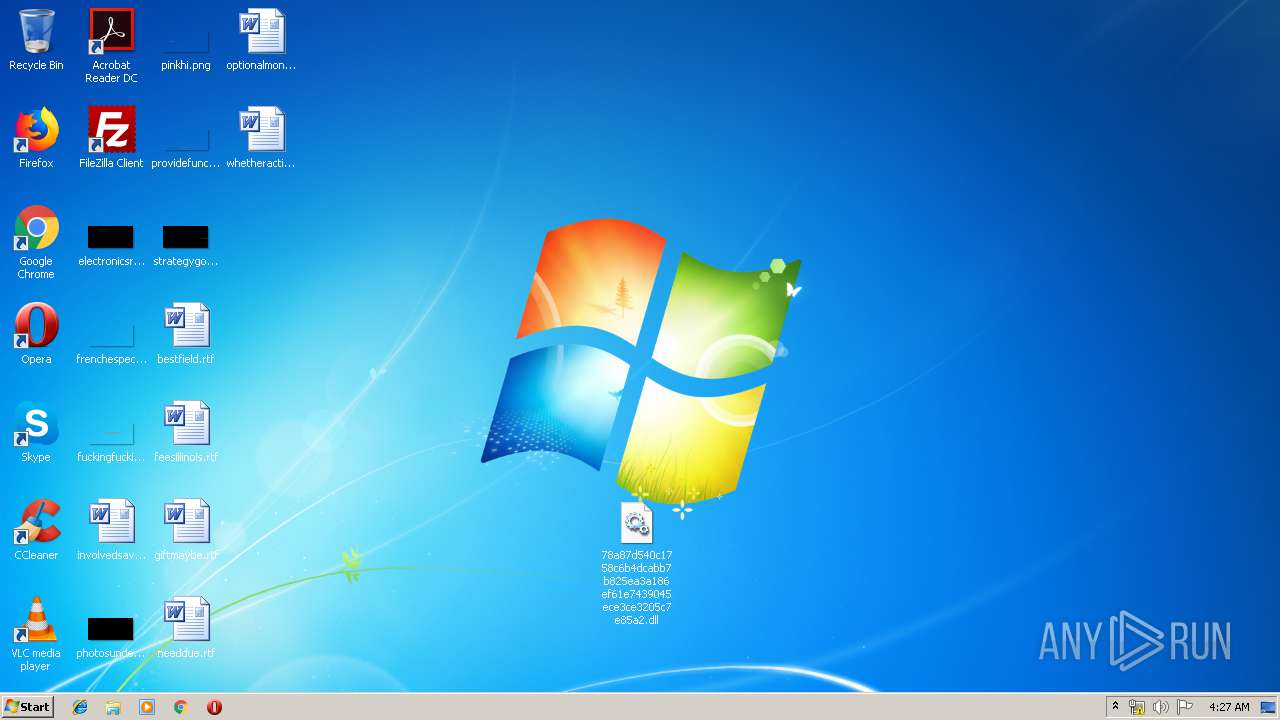
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 60E08DD1B0BECC08954920B6EEE3CB22 |
| SHA1: | 0229A8580CAA122D390F43B21977B7B979DBAB5E |
| SHA256: | 332B978E23B6EF33BBB905F2C6DCBB86A7F9D350B818132516EBF4CE54D4B41B |
| SSDEEP: | 192:e4w9NQywZuo9mZu01NKg9RCKFVjDnV/NUc1MASfEMijM0cuKADDHpBu8uKwfAZy:a9N1a99017TzVt1+NfEMIMBA/JI8udA4 |
MALICIOUS
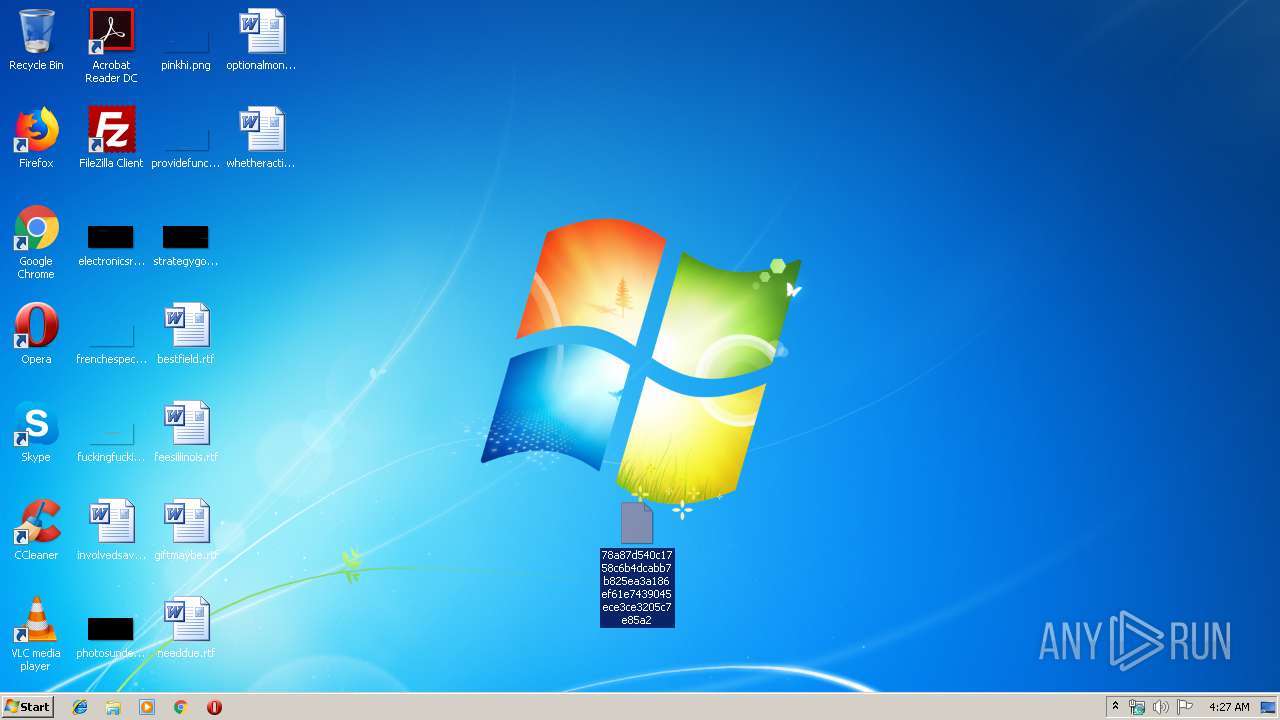
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 752)
- explorer.exe (PID: 276)
- svchost.exe (PID: 852)
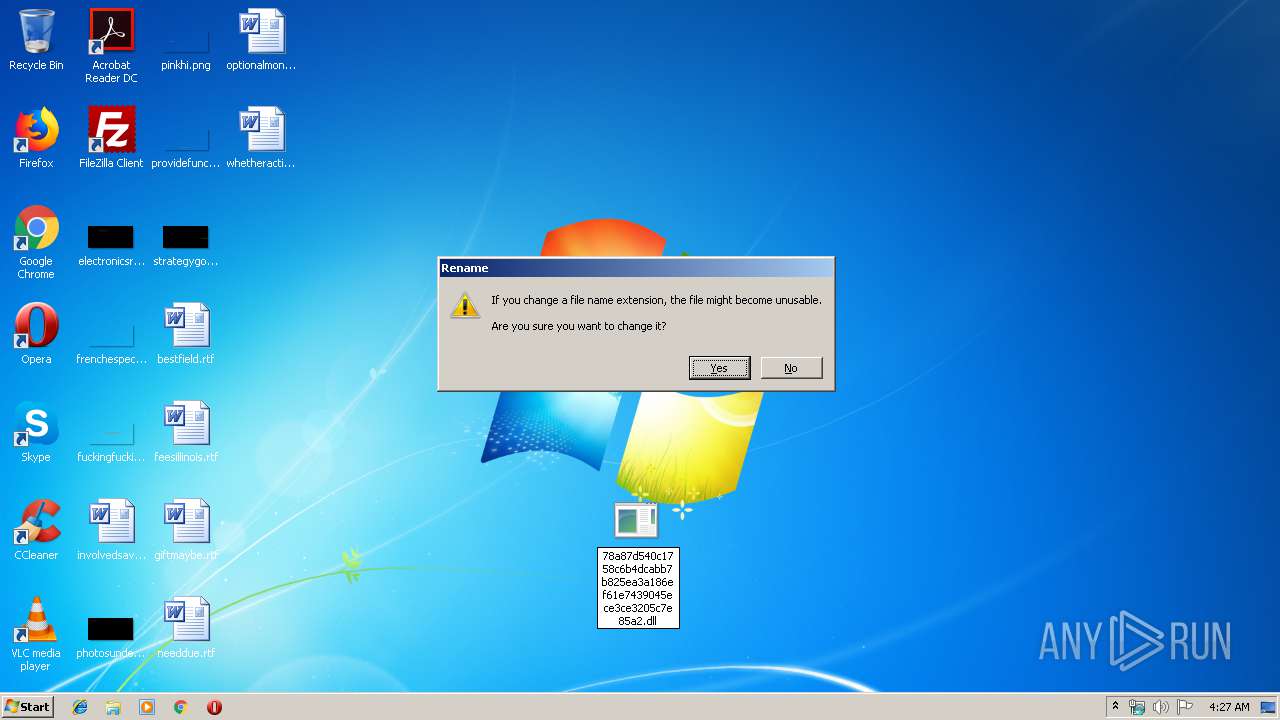
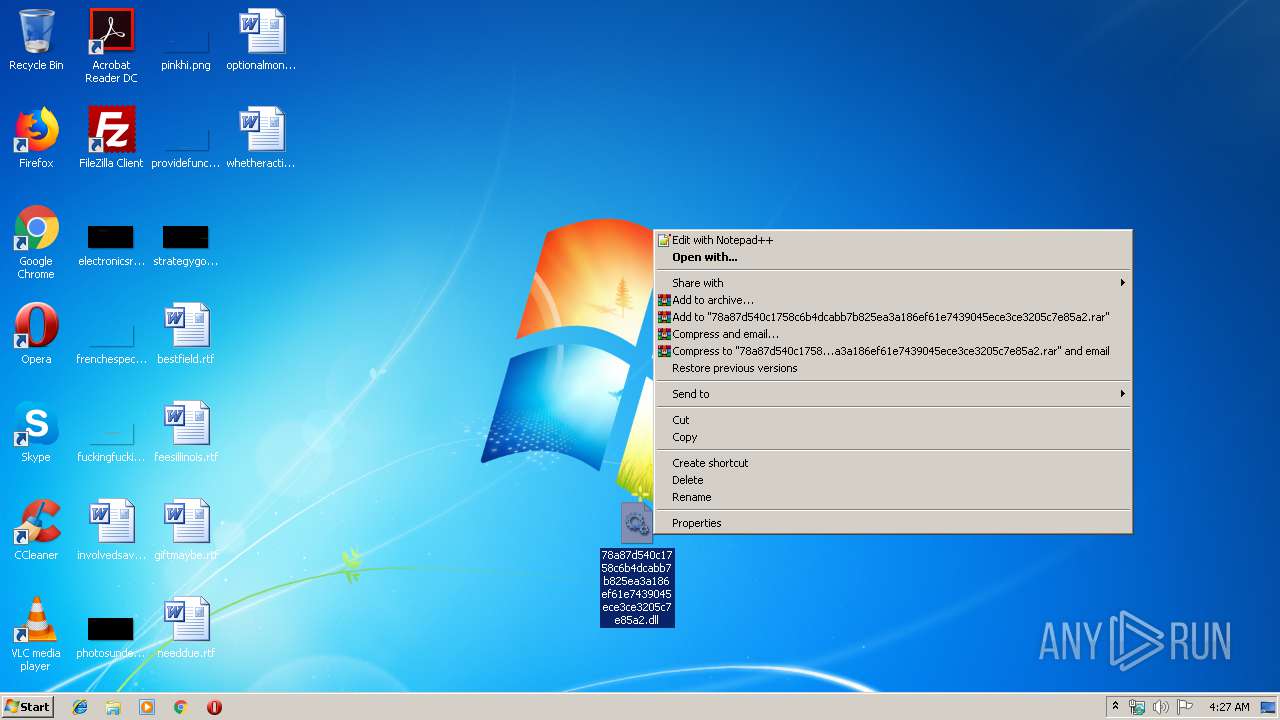
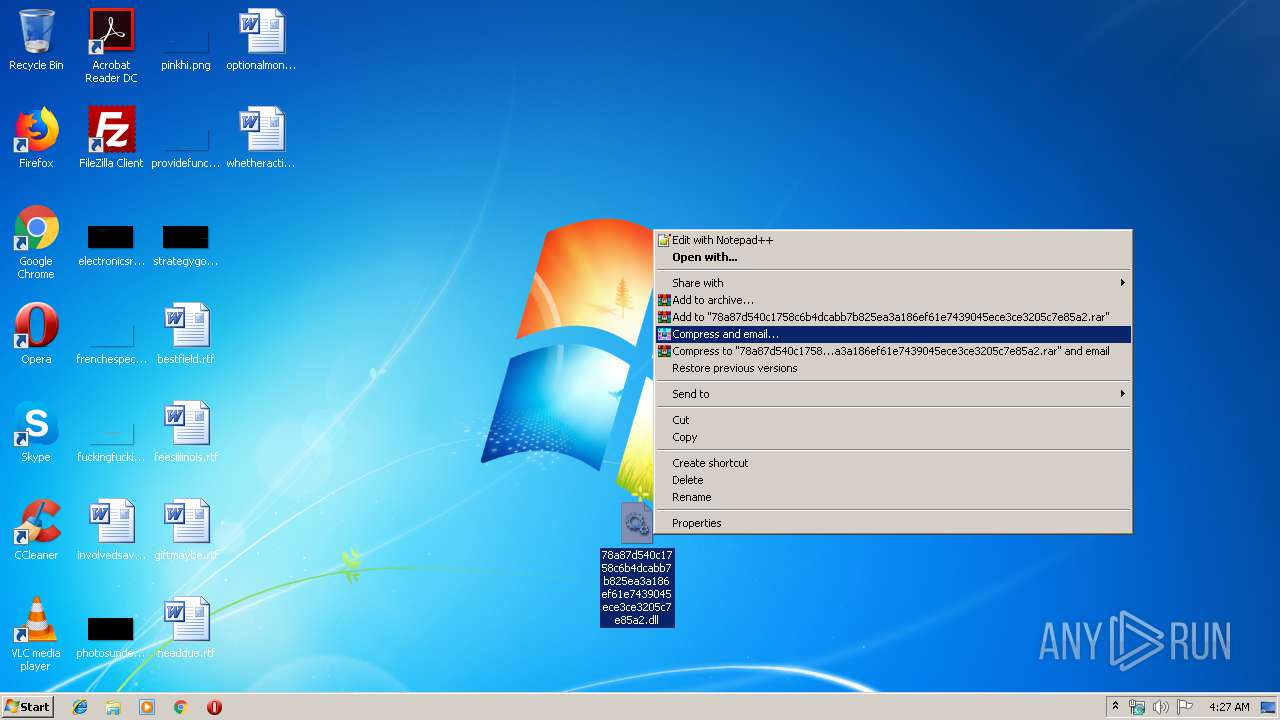
Renames files like Ransomware
- explorer.exe (PID: 276)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3388)
- explorer.exe (PID: 276)
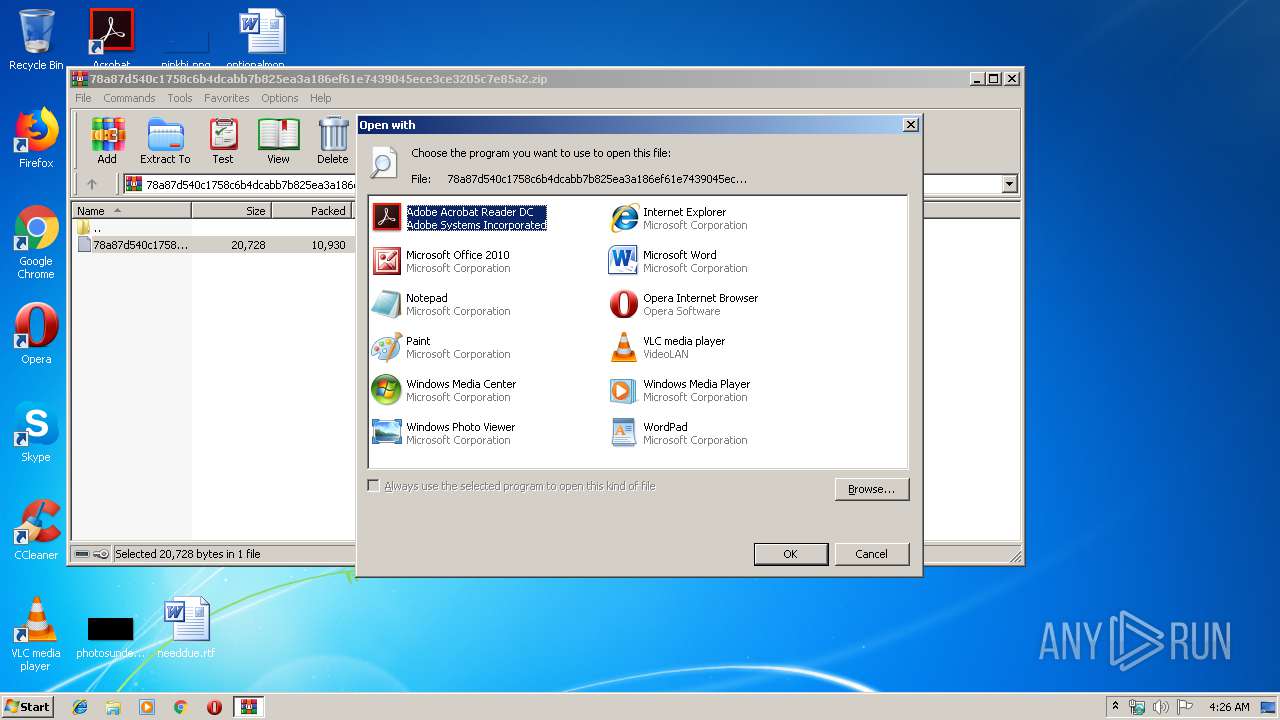
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3388)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
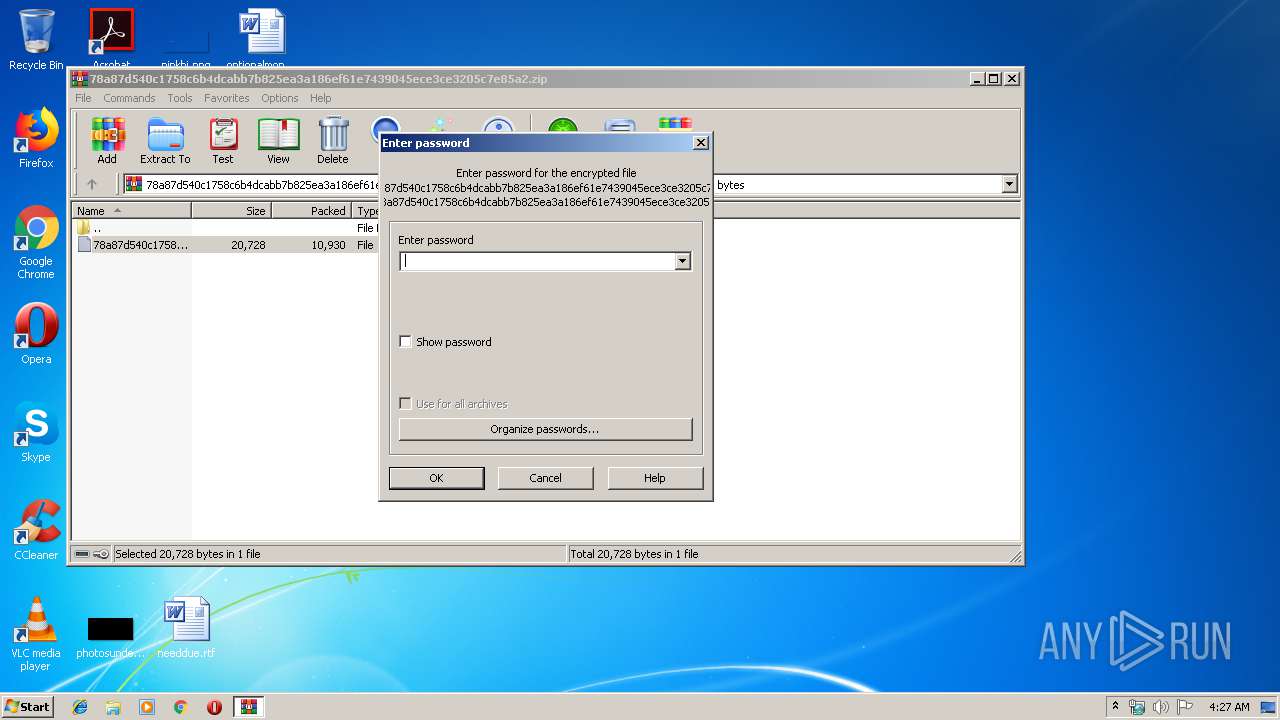
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:03 02:34:27 |
| ZipCRC: | 0x97774cdb |
| ZipCompressedSize: | 10930 |
| ZipUncompressedSize: | 20728 |
| ZipFileName: | 78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2 |
Total processes
36
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
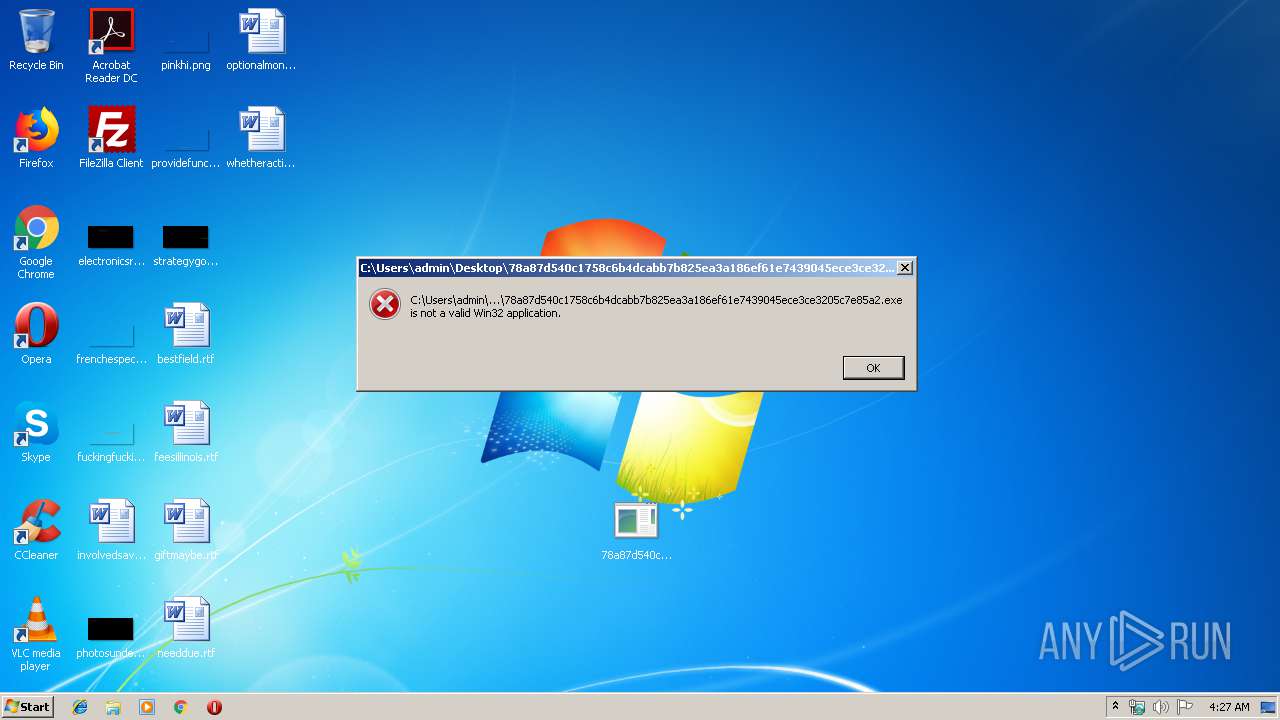
| 2216 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb3388.41297\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
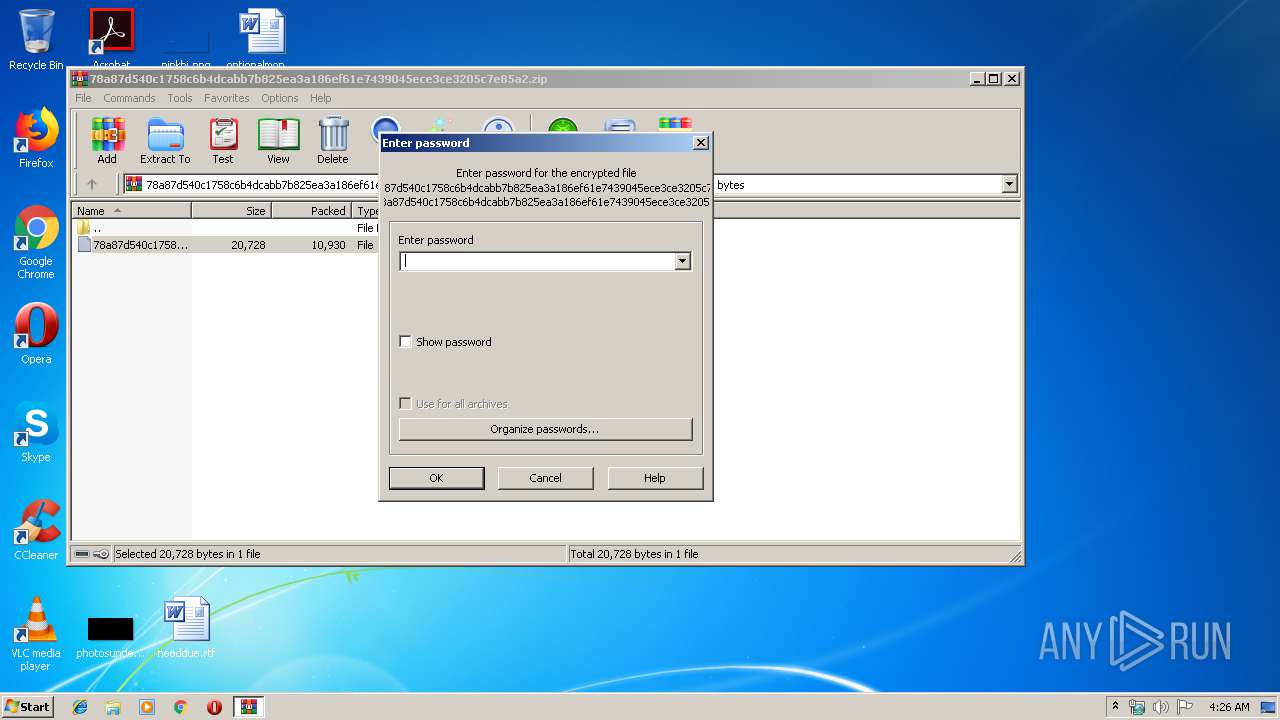
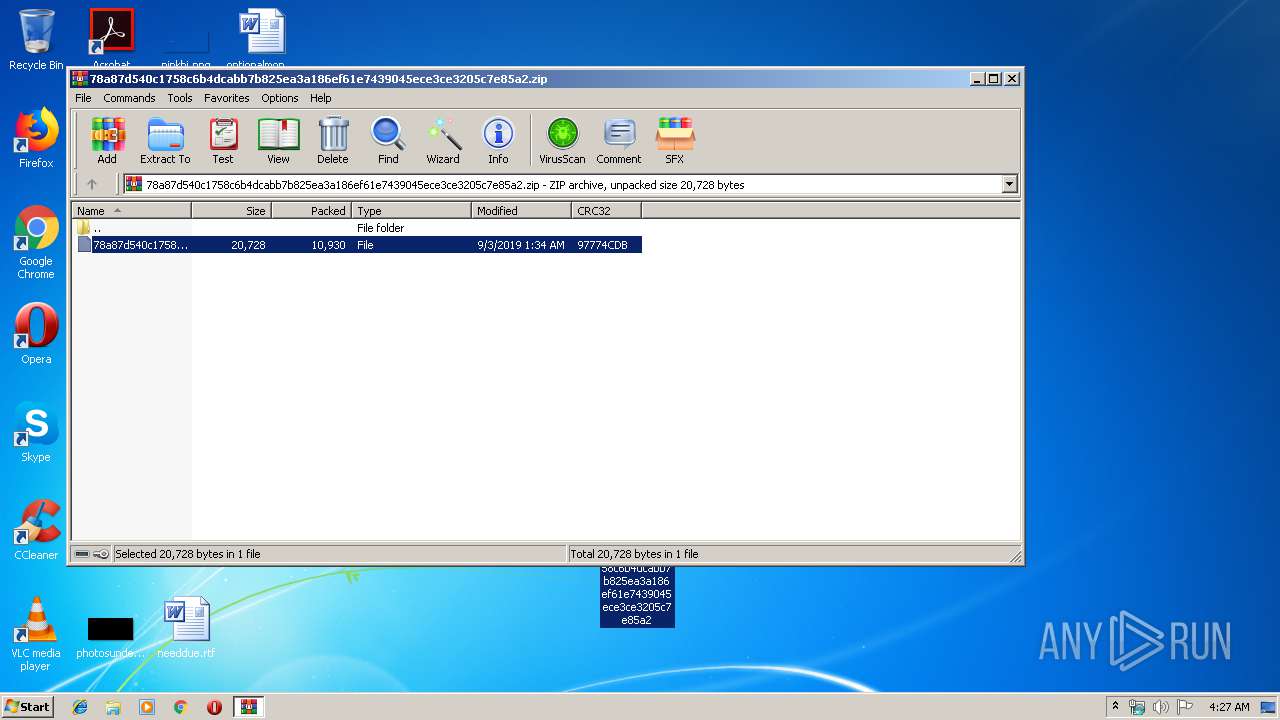
| 3388 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 045
Read events
2 992
Write events
53
Delete events
0
Modification events
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2.zip | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3388) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
1
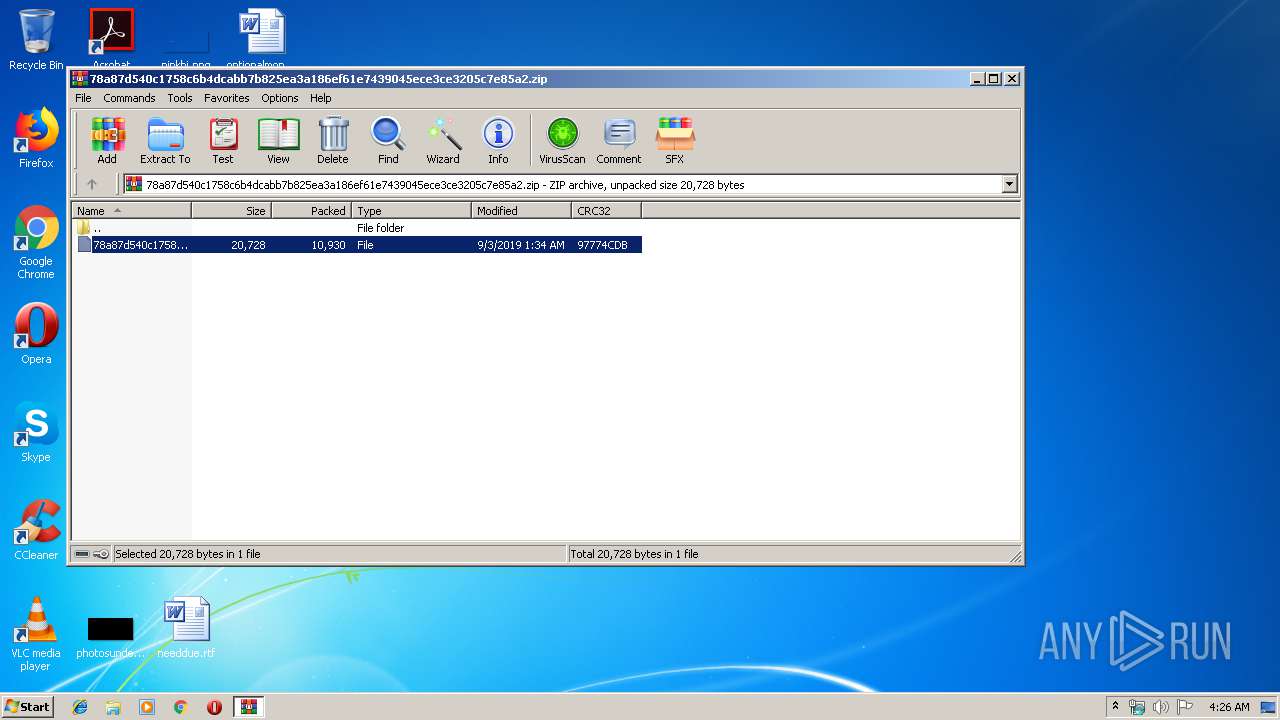
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3388.42223\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2 | — | |
MD5:— | SHA256:— | |||
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
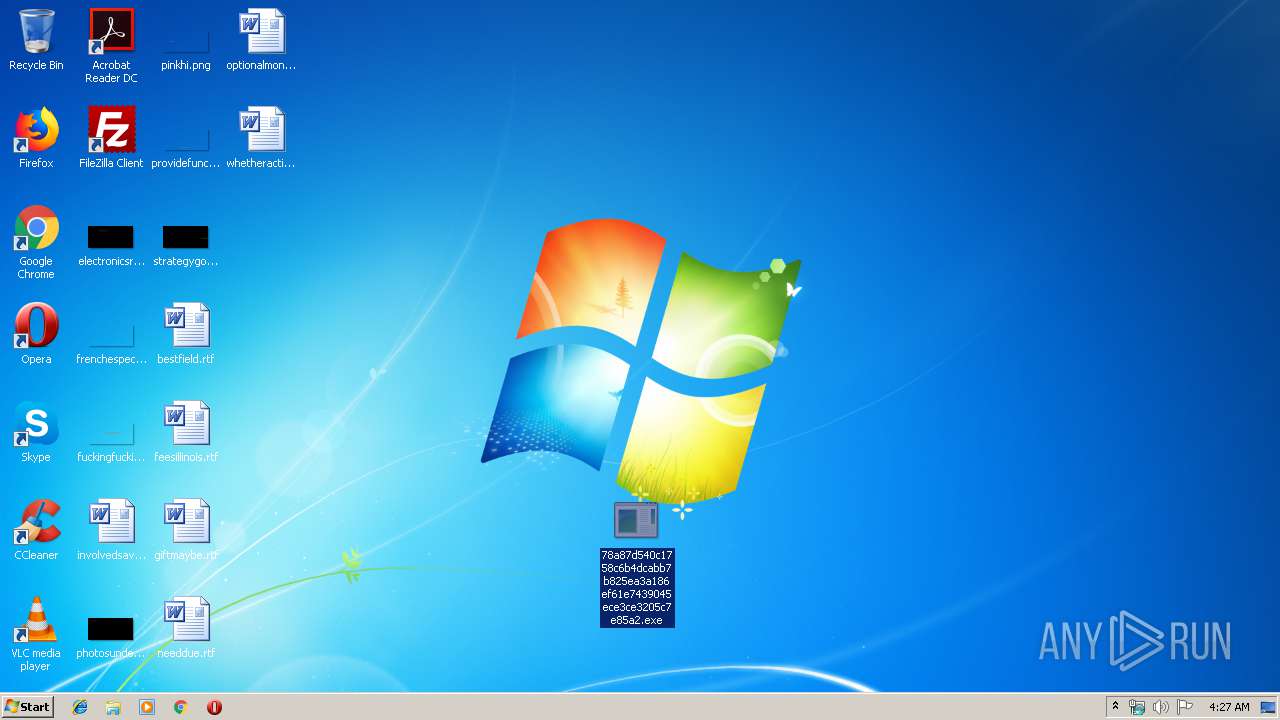
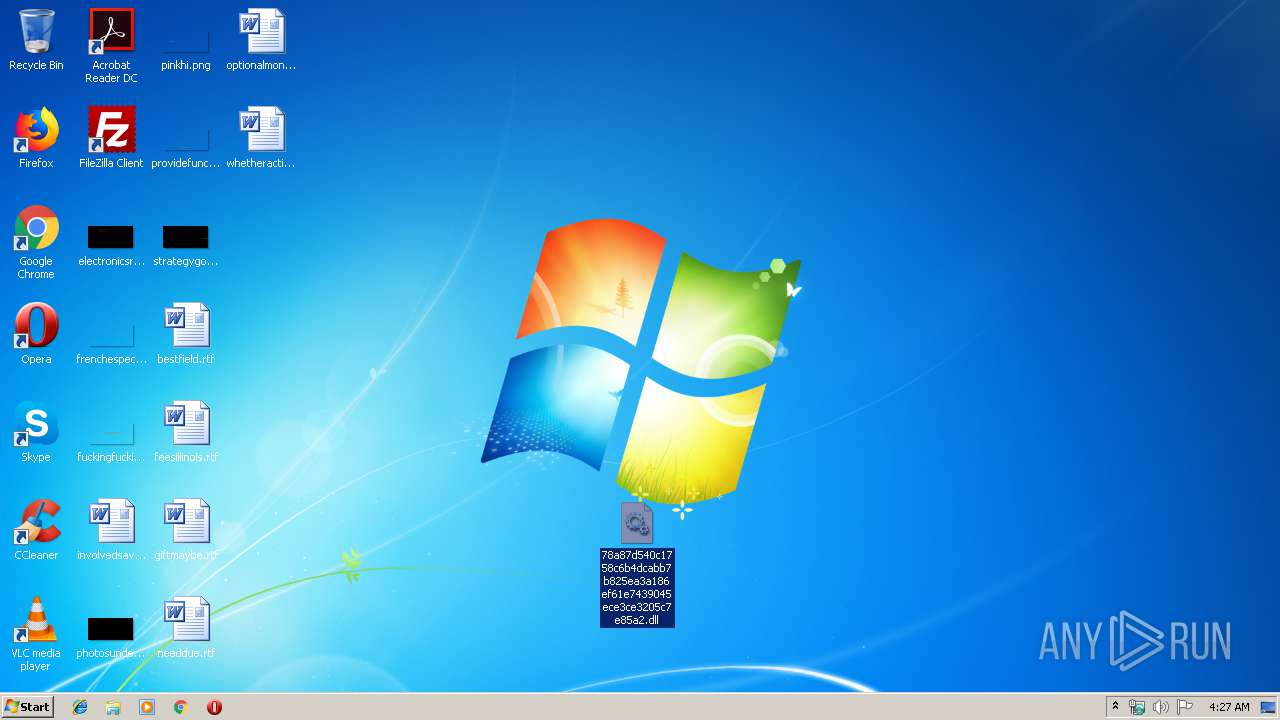
| 276 | explorer.exe | C:\Users\admin\Desktop\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2.exe | executable | |
MD5:3B9646BF2D791E5EF4633E802F23E305 | SHA256:78A87D540C1758C6B4DCABB7B825EA3A186EF61E7439045ECE3CE3205C7E85A2 | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2.dll | executable | |
MD5:3B9646BF2D791E5EF4633E802F23E305 | SHA256:78A87D540C1758C6B4DCABB7B825EA3A186EF61E7439045ECE3CE3205C7E85A2 | |||
| 3388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3388.41297\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2 | executable | |
MD5:3B9646BF2D791E5EF4633E802F23E305 | SHA256:78A87D540C1758C6B4DCABB7B825EA3A186EF61E7439045ECE3CE3205C7E85A2 | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\78a87d540c1758c6b4dcabb7b825ea3a186ef61e7439045ece3ce3205c7e85a2 | executable | |
MD5:3B9646BF2D791E5EF4633E802F23E305 | SHA256:78A87D540C1758C6B4DCABB7B825EA3A186EF61E7439045ECE3CE3205C7E85A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report