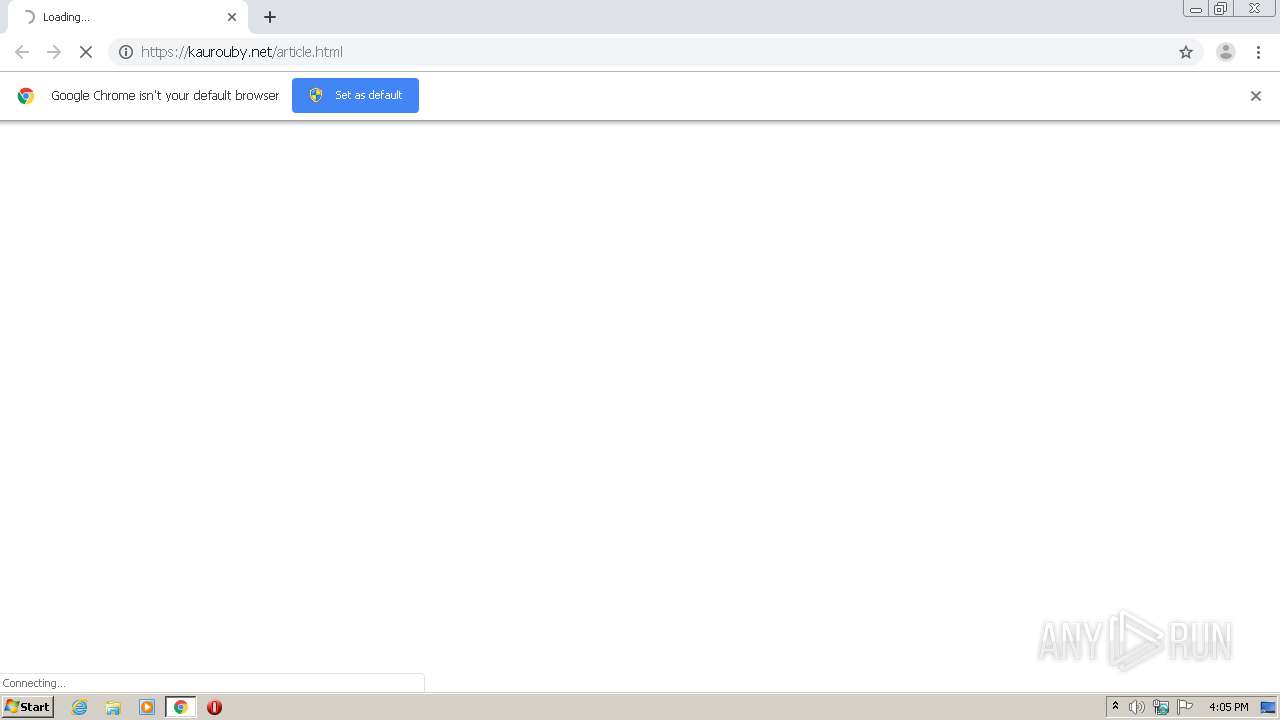
| URL: | https://kaurouby.net/article.html |
| Full analysis: | https://app.any.run/tasks/ec72a9fd-1dfe-47f9-a1ff-0c70e74c7f9b |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2021, 16:05:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 375837136ACA30F6B39F448FA288344C |
| SHA1: | 643D50E24B15B4DDC6E389F12121D7BC7C5A642E |
| SHA256: | 331BFBADDFC1B3B7CE3E815BF9DFAE51FF7C4E8930C0425B5C3B083EF56A55A4 |
| SSDEEP: | 3:N8BC+LKuLQ:2g00 |
MALICIOUS
No malicious indicators.SUSPICIOUS
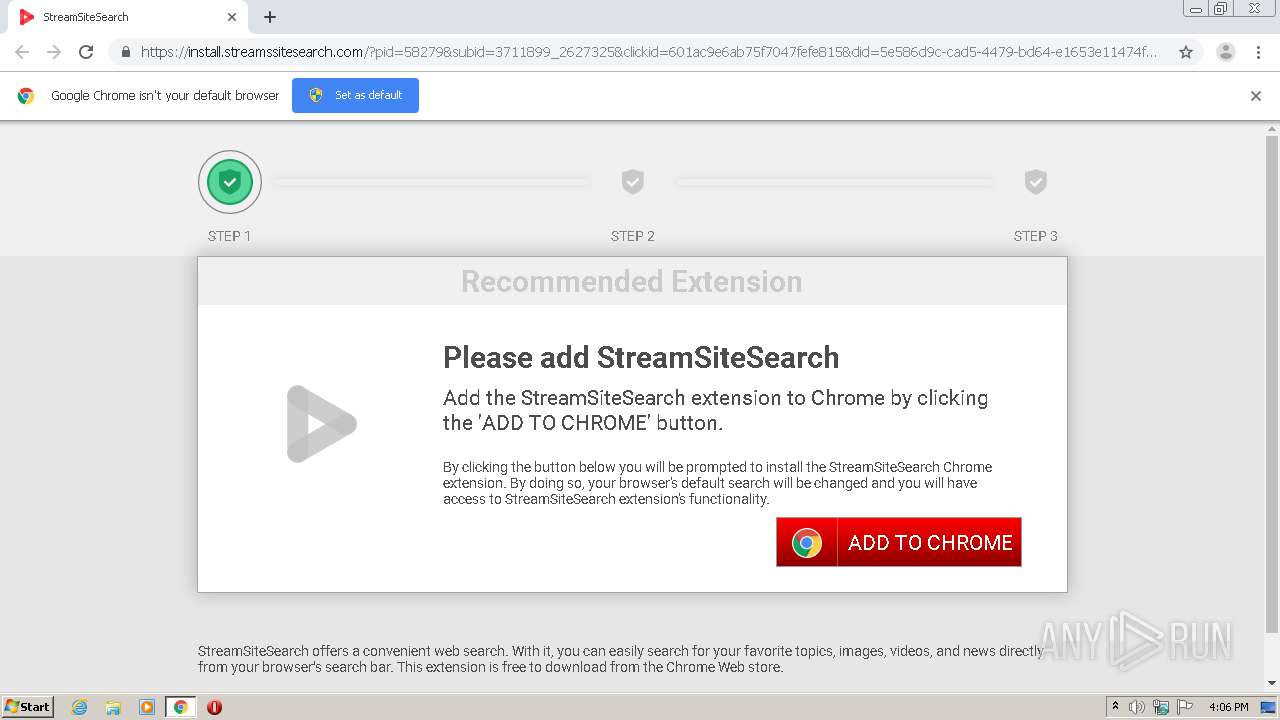
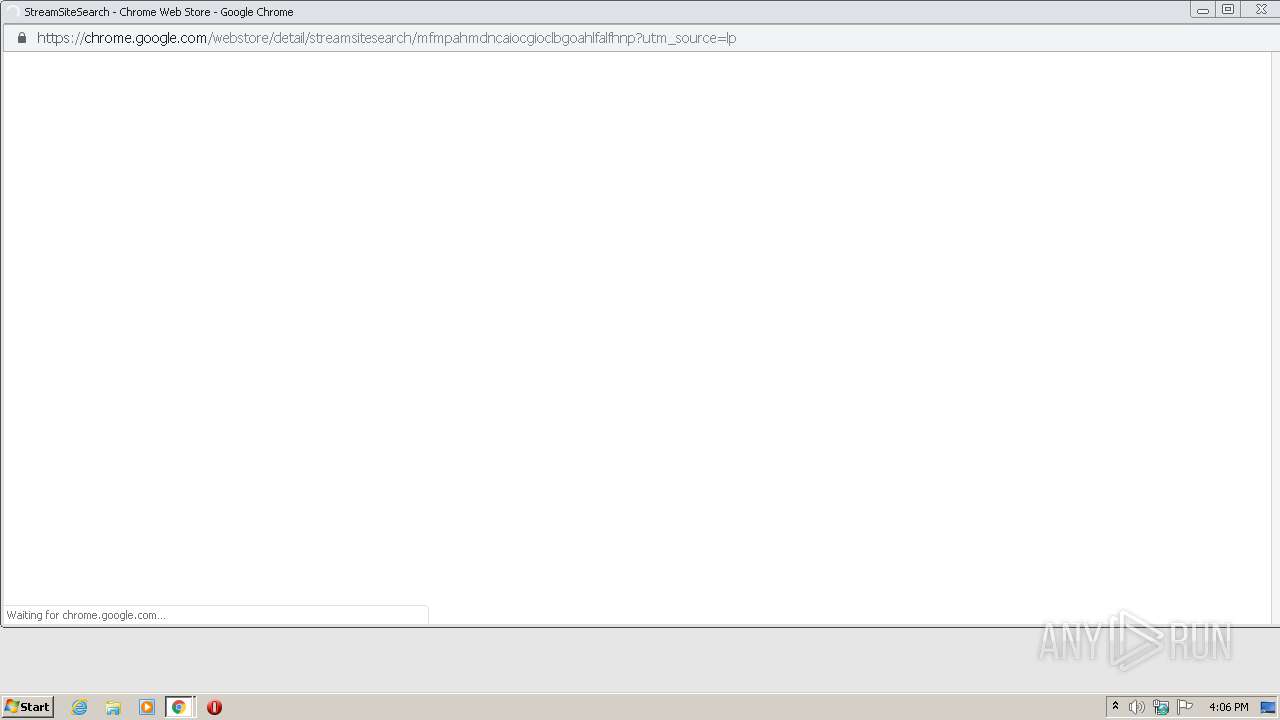
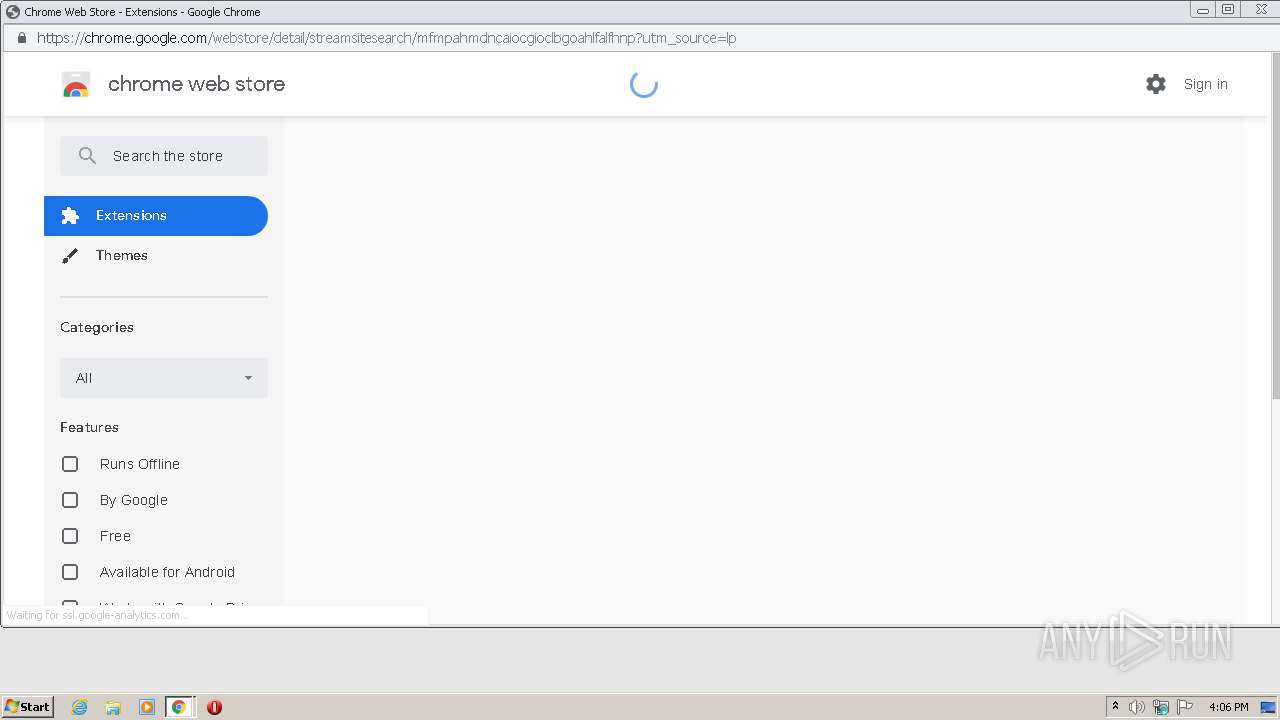
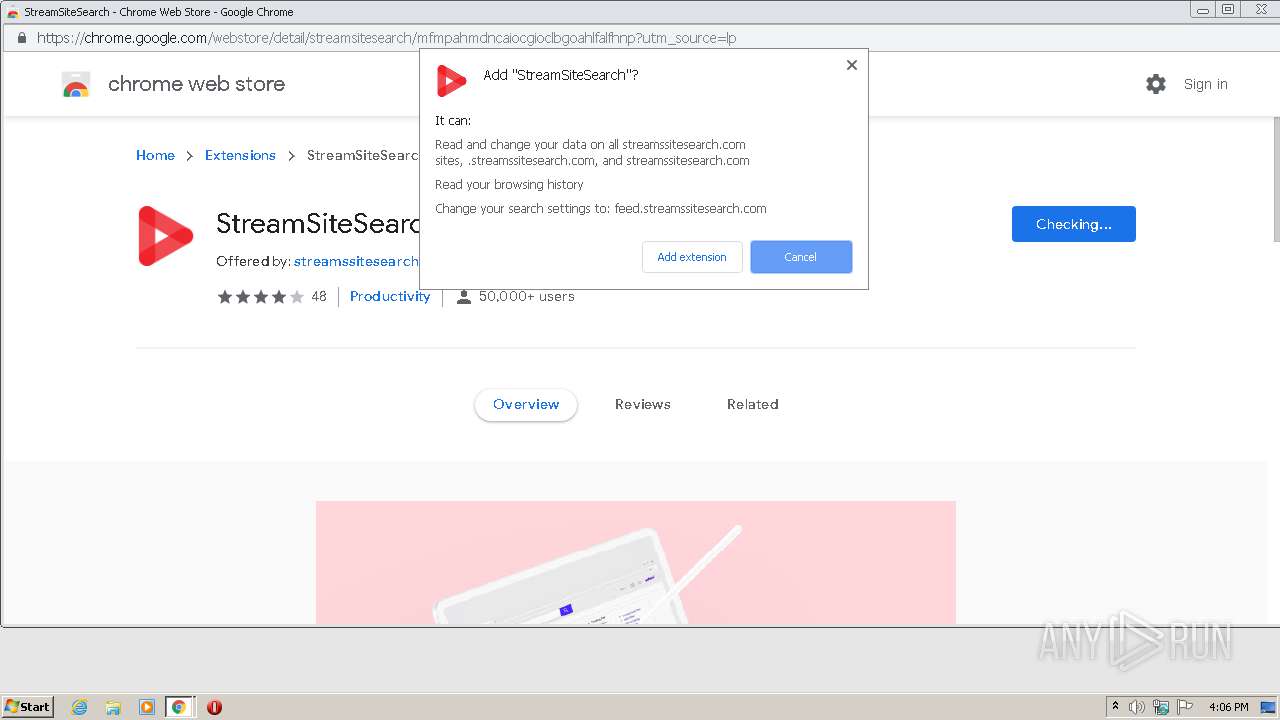
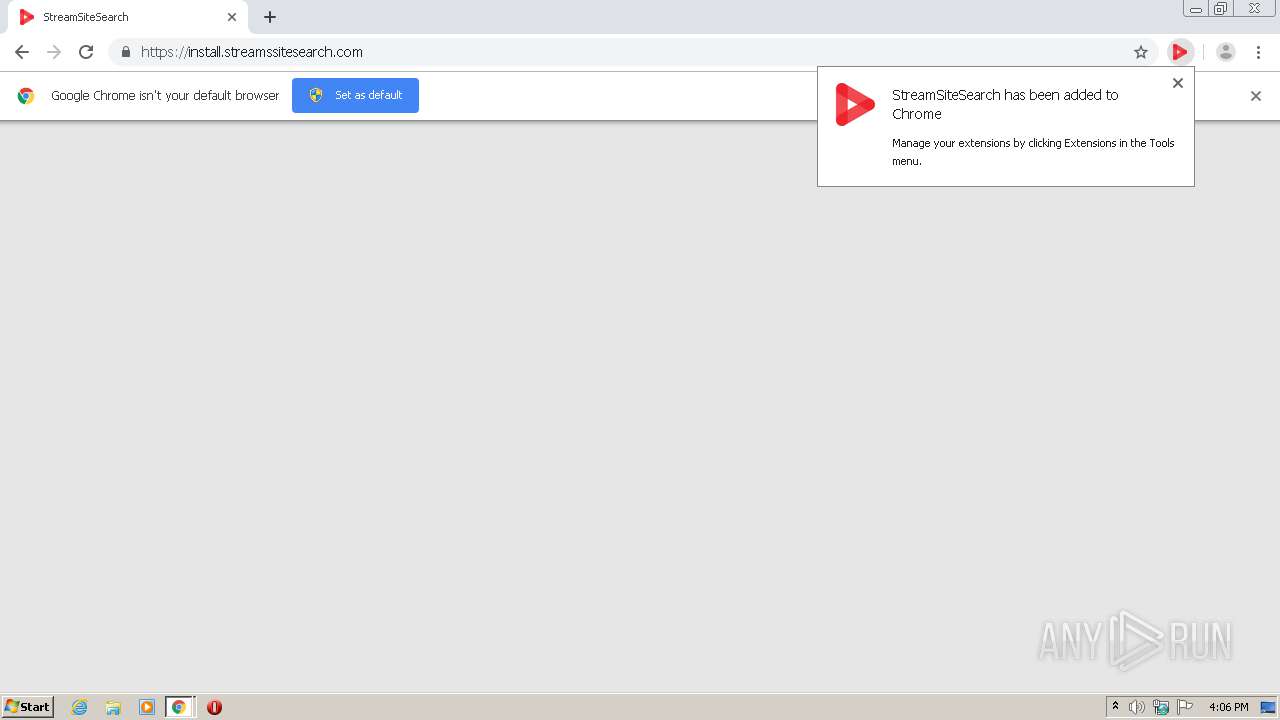
Modifies files in Chrome extension folder
- chrome.exe (PID: 1912)
INFO
Reads the hosts file
- chrome.exe (PID: 1912)
- chrome.exe (PID: 3960)
Reads settings of System Certificates
- chrome.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 1912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12920387395051645146 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1318947314978585066 --mojo-platform-channel-handle=4152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10559163654062070952 --mojo-platform-channel-handle=3928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8321141064927732448 --mojo-platform-channel-handle=3728 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13681871031167587761 --mojo-platform-channel-handle=4148 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3383344151469928314 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16585390018339639148 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1104 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://kaurouby.net/article.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1052248781967246627,10366756393470079322,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11487731610852766117 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
840
Read events
753
Write events
83
Delete events
4
Modification events
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1912-13256841951588625 |
Value: 259 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1912-13256841951588625 |
Value: 259 | |||
Executable files
0
Suspicious files
49
Text files
95
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-601AC9E0-778.pma | — | |
MD5:— | SHA256:— | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6e91b9a3-4001-4419-88f9-8f9caec62466.tmp | — | |
MD5:— | SHA256:— | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | gmc | |
MD5:B6D81B360A5672D80C27430F39153E2C | SHA256:30E14955EBF1352266DC2FF8067E68104607E750ABB9D3B36582B8AF909FCB58 | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF129f74.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12a262.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
135
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=178c706091aac579cfe4d81c16ba638f34914c173a0d691d25004121b1724ce62055ef942f48b0d8ad8073df4406660445c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3da22af232a4fd60c0&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fc7c1459ea808c01d7c20567570c10fbaedcb505a8c1c7434c42743cf6cf737dfab1f92b2e999c0fa6a65755993fbc343d610b55c51bbd8c2fce3b348246312becd56638641e5e79bb79bde9ca233b17a8cce4cd333bc43fdae563f23408093183a269e0652f4f163485f09ee47f0de625fd9e80076b9f3e3ecaf87ccf061d22f48afa4f59de6add54a92006370d45768&ccd=ca&stc=d&cin=dublin&mcd=0&cic=35590&kw=qldummy | US | — | — | suspicious |
3960 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=178c706091aac579cfe4d81c16ba638f34914c173a0d691d25004121b1724ce62055ef942f48b0d8c11a4539c265514945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d4bbe255383aa7b45&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fb5f699f8cc057105fda4ffb03e2e498b3984d1e2aa099e2f1dc7dcf252b1921591d90ed781805f38824842ffccfc48f7d23f8e46553d633551b0412facce7ec9d6dad81cb778684a7766c84bcf21b41304cddf388ddad42a7b4ef47730eb85395054acb0dfab4b9eea11109c30114169d22e547a286d311c4689915f106675dc65e9d1f7c9312c1ae21eac1bd8a776419cc5b9cb68379767&ccd=ca&stc=d&cin=dublin&mcd=0&cic=35590&kw=qldummy | US | — | — | suspicious |
3960 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=178c706091aac579cfe4d81c16ba638f34914c173a0d691d25004121b1724ce62055ef942f48b0d85ca71983e786eab145c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3da385ad8fbb8b36a4&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fb5f699f8cc0571050fab8330d0a7dad3a0368ff548236c5d1dc7dcf252b1921591d90ed781805f38824842ffccfc48f7ad94079e0f681acd51b0412facce7ec9d6dad81cb778684a7766c84bcf21b41304cddf388ddad42a7b4ef47730eb85395054acb0dfab4b9eea11109c30114169d22e547a286d311c4689915f106675dc65e9d1f7c9312c1adcec19b4a434f1889cc5b9cb68379767&ccd=ca&stc=d&cin=dublin&mcd=0&cic=35590&kw=qldummy | US | — | — | suspicious |
3960 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=178c706091aac579cfe4d81c16ba638f34914c173a0d691d25004121b1724ce62055ef942f48b0d814a4fbe71a3cbaf945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d4c13c1e79bc2d95b&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fc27bb95ba7e6b3f8919e674a8f6c928a0570dfb134a2be1963379820cb1253f4e0bff2601b0861cc7b6acc51a7f1a44cdb5494d8ef1b0ca299c2de81911618465c9697bf149461b7582ca870a3e3eaf7627e6f7bc39727eee307c3d28962303a45328cf5d85b75c7468f093cc21f6471f0cf57a0b46eef52783b8bb2b66375fca653c4ac3dc9378d108d314d4504e39d&ccd=ca&stc=d&cin=dublin&mcd=0&cic=35590&kw=qldummy | US | — | — | suspicious |
3960 | chrome.exe | GET | 200 | 34.96.99.173:80 | http://imptrk.siteplug.com/impTrk.php?enk1=178c706091aac579cfe4d81c16ba638f34914c173a0d691d25004121b1724ce62055ef942f48b0d8d4957f757577a62345c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3dda2dc0d03867010d&enk2=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272f128da8d35cc4be68008a47d668a3c44a0dc51ff94657b6381dc7dcf252b1921591d90ed781805f38824842ffccfc48f7d2307c77b3e9034c51b0412facce7ec9d6dad81cb778684a7766c84bcf21b41304cddf388ddad42a7b4ef47730eb85395054acb0dfab4b9eea11109c30114169d22e547a286d311c4689915f106675dc65e9d1f7c9312c1af6780a864c5392319cc5b9cb68379767&ccd=ca&stc=d&cin=dublin&mcd=0&cic=35590&kw=qldummy | US | — | — | suspicious |
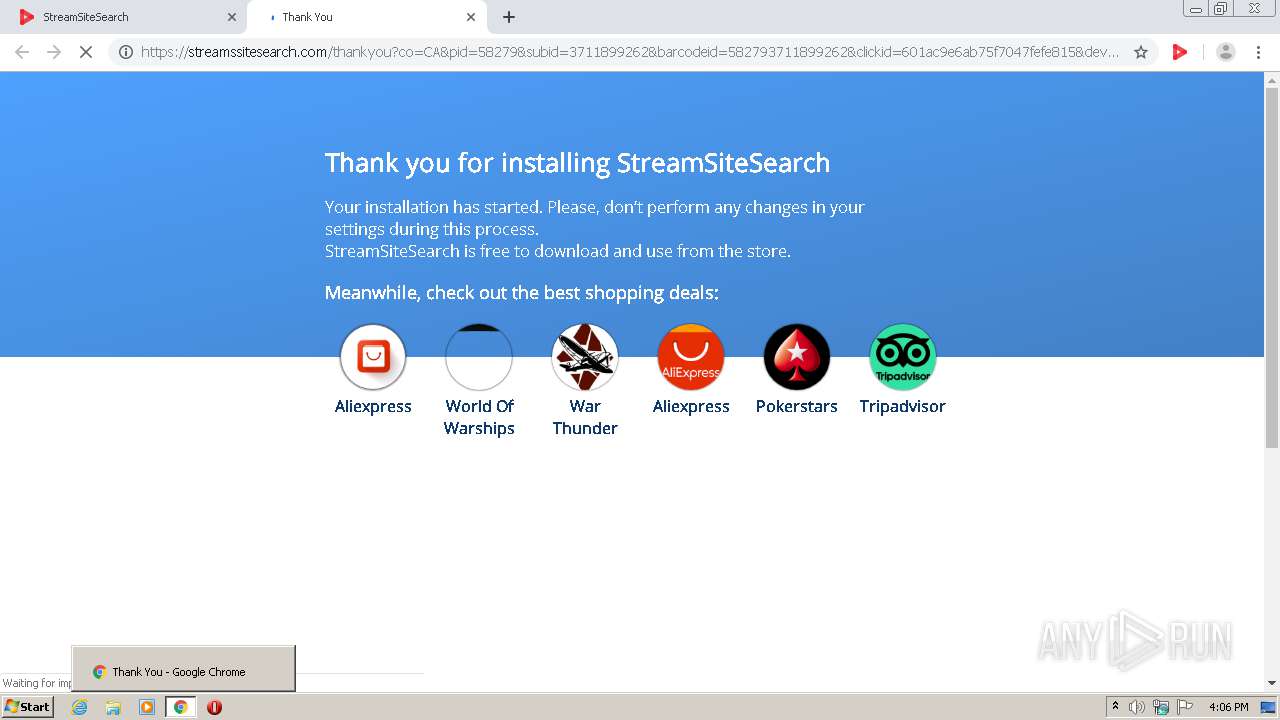
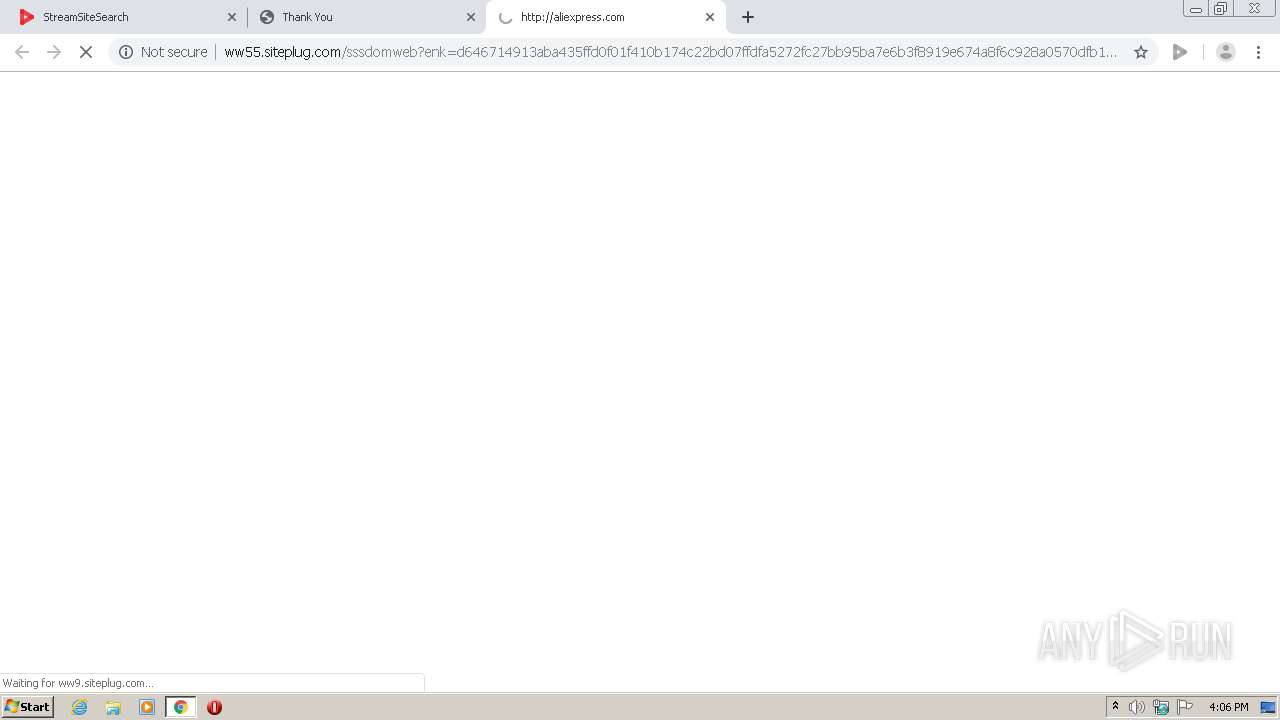
3960 | chrome.exe | GET | 302 | 35.244.152.255:80 | http://ww9.siteplug.com/fly1?q=&rf=&enk=RsEnyY%2BRBqGPiY%2BJBsknyY%2BJxolGmcbBZskn4ybjJuPm&qxcli=fdcfc611773a2be3&qxsi=eb9c042db8532198&sx=1280&sy=720&bx=1280&by=620&mx=0&my=0&ifm=0&ol=ee93acfb469601d8f1192f423edd3e19&tm=1612368399.4399&etm=1612368399.4466&ls=0&kdbbh=0&cskey=odc96&test_flag_for_click=&v6=&v4=3116371973&vip=3116371973&iv6=0 | US | text | 2 b | unknown |
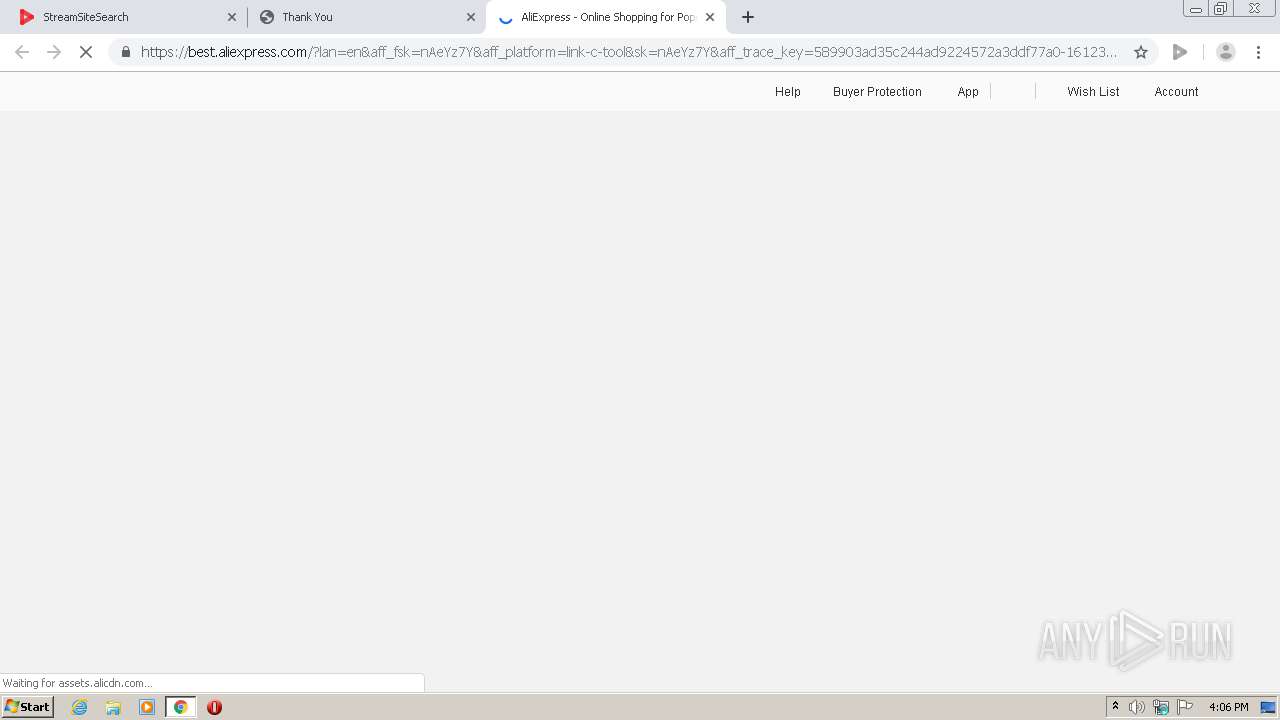
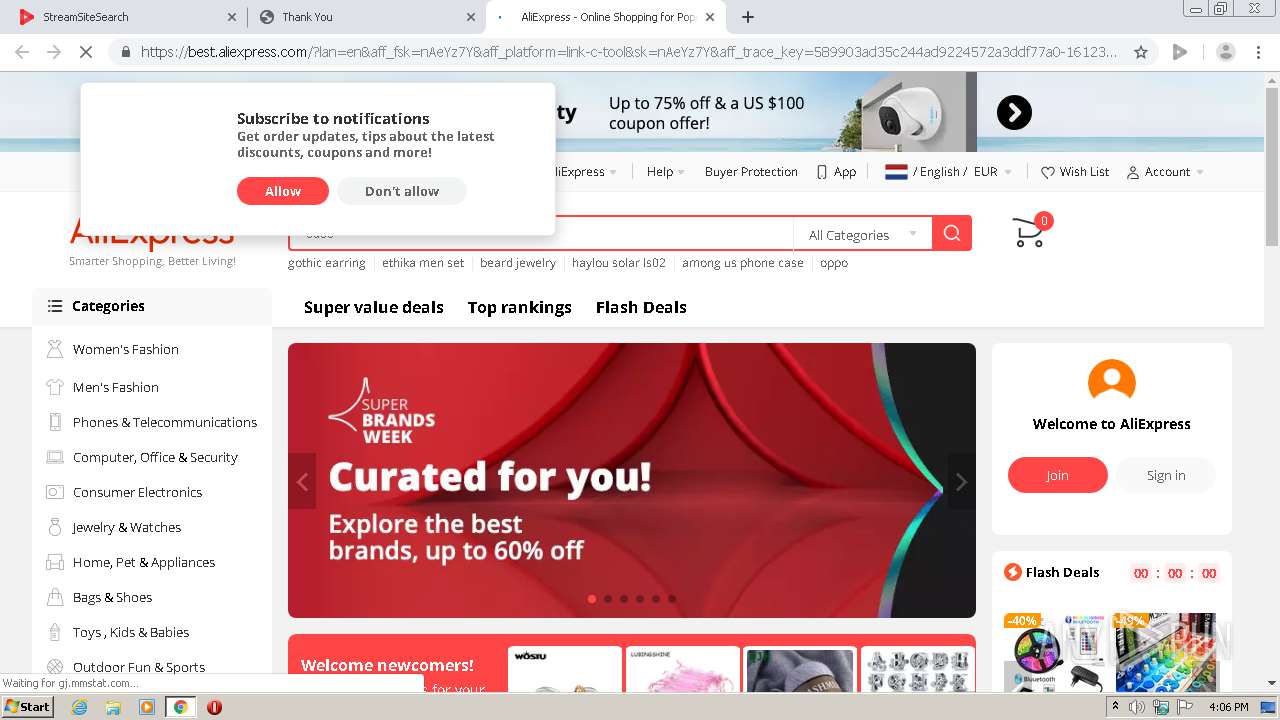
3960 | chrome.exe | GET | 301 | 23.32.59.171:80 | http://s.click.aliexpress.com/e/nAeYz7Y?dp=08ac3772931b07ffb8952397fbf23630 | US | html | 357 b | whitelisted |
3960 | chrome.exe | GET | 200 | 130.211.44.187:80 | http://ww55.siteplug.com/sssdomweb?enk=d646714913aba435ffd0f01f410b174c22bd07ffdfa5272fc27bb95ba7e6b3f8919e674a8f6c928a0570dfb134a2be1963379820cb1253f4e0bff2601b0861cc7b6acc51a7f1a44cdb5494d8ef1b0ca299c2de81911618465c9697bf149461b7582ca870a3e3eaf7627e6f7bc39727eee307c3d28962303a45328cf5d85b75c7468f093cc21f6471f0cf57a0b46eef52783b8bb2b66375fca653c4ac3dc9378d108d314d4504e39d&ccd=ca&stc=d&cin=dublin&mcd=0&cic=35590&kw=qldummy&renk=178c706091aac579cfe4d81c16ba638f34914c173a0d691d25004121b1724ce62055ef942f48b0d814a4fbe71a3cbaf945c886fb5f7184fc6845bb452e760f1e4212c2ca210f16d5d996f34ca7d3c4a40ce3e92c0ff59c3d4c13c1e79bc2d95b | US | html | 5.76 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | chrome.exe | 139.45.197.64:443 | kaurouby.net | — | US | unknown |
3960 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
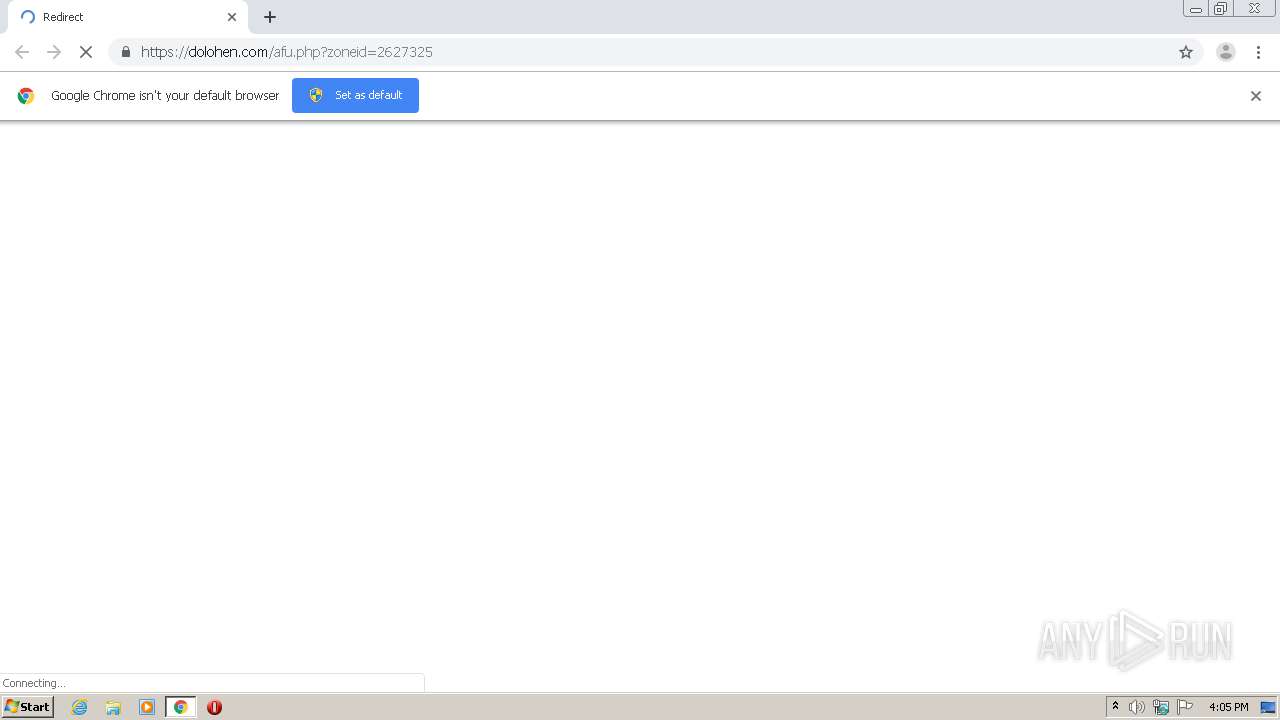
3960 | chrome.exe | 139.45.195.162:443 | dolohen.com | — | US | suspicious |
3960 | chrome.exe | 139.45.197.31:443 | propeller-tracking.com | — | US | unknown |
3960 | chrome.exe | 95.217.204.250:443 | adtrackingflow.pro | Hetzner Online GmbH | DE | unknown |
3960 | chrome.exe | 139.45.197.8:443 | my.rtmark.net | — | US | unknown |
3960 | chrome.exe | 139.45.195.161:443 | bainushe.com | — | US | unknown |
3960 | chrome.exe | 64.233.177.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
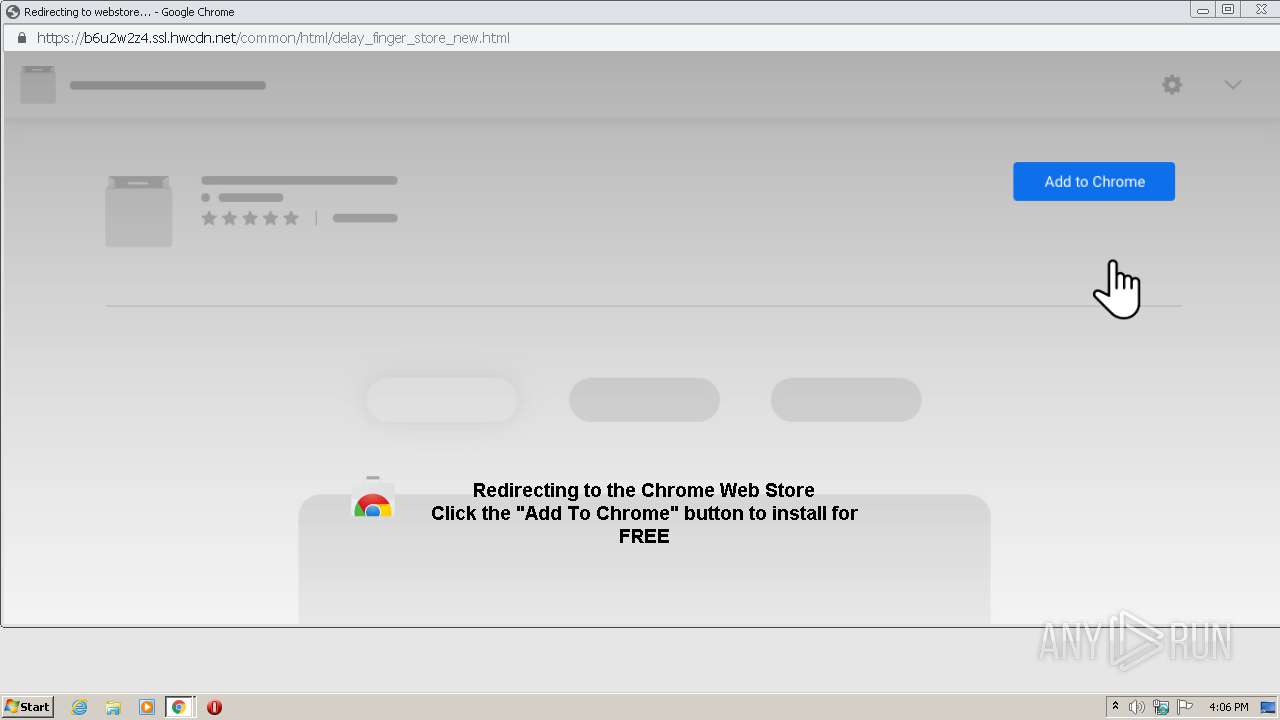
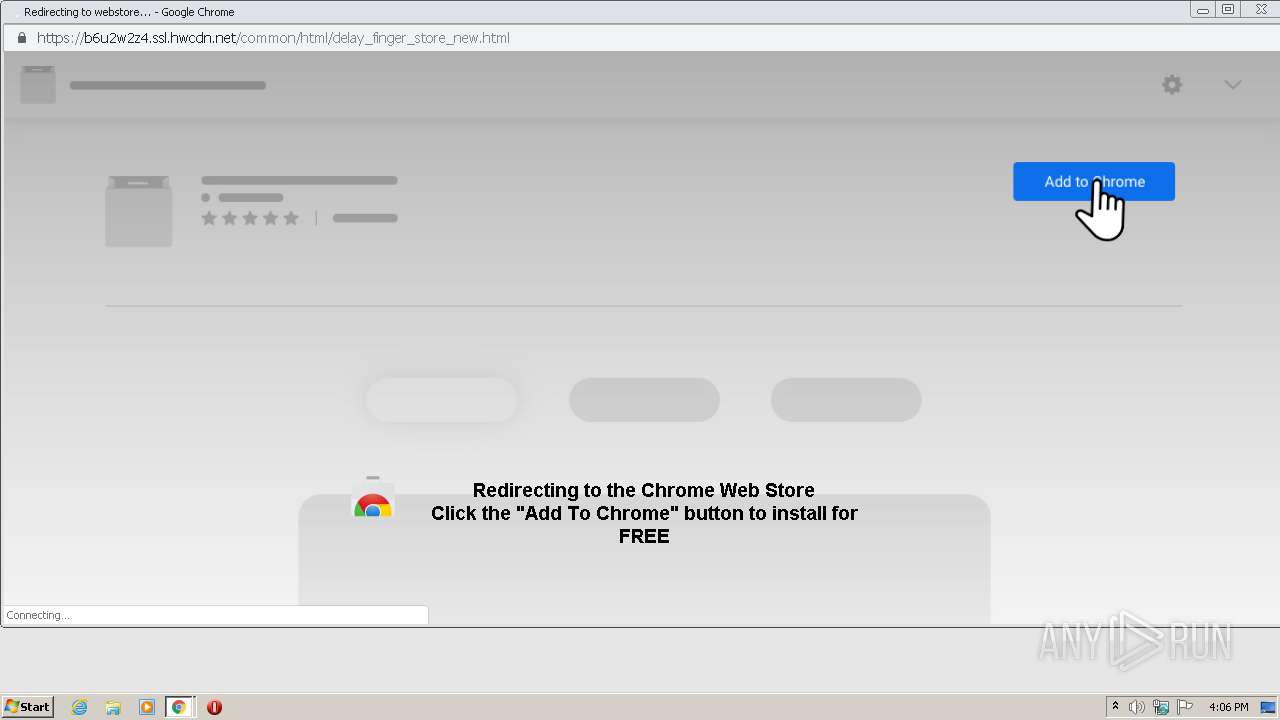
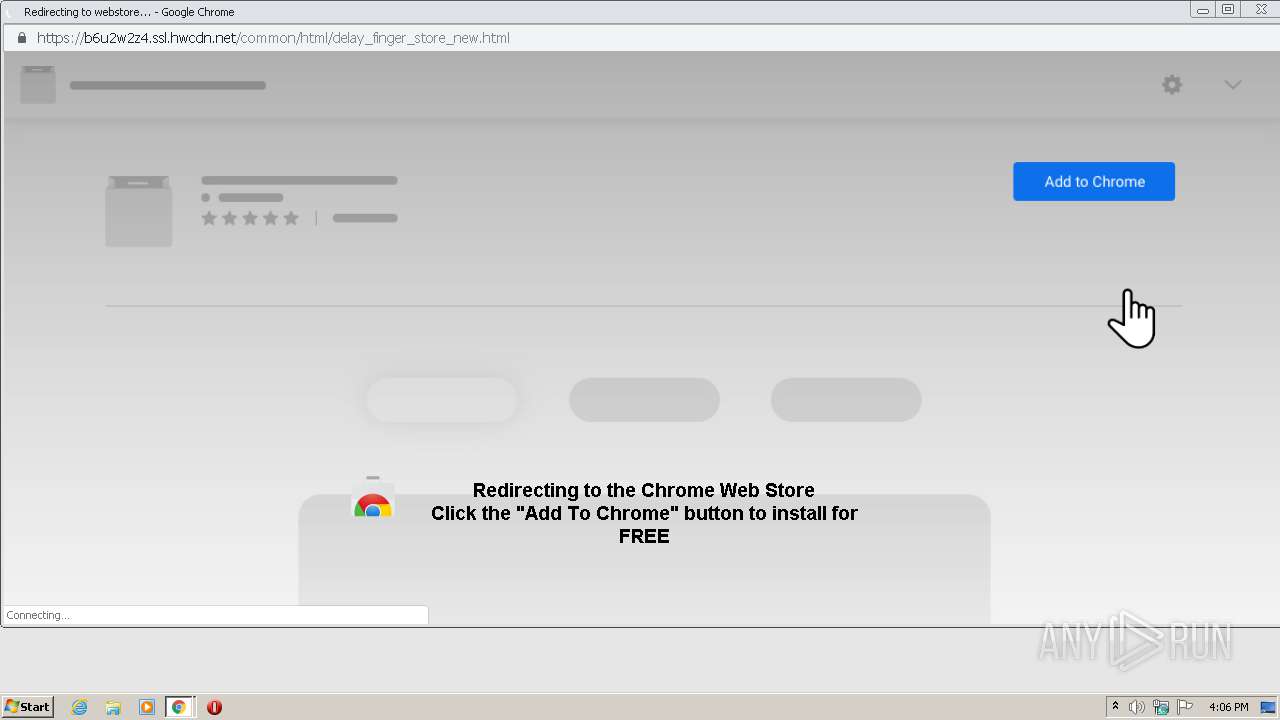
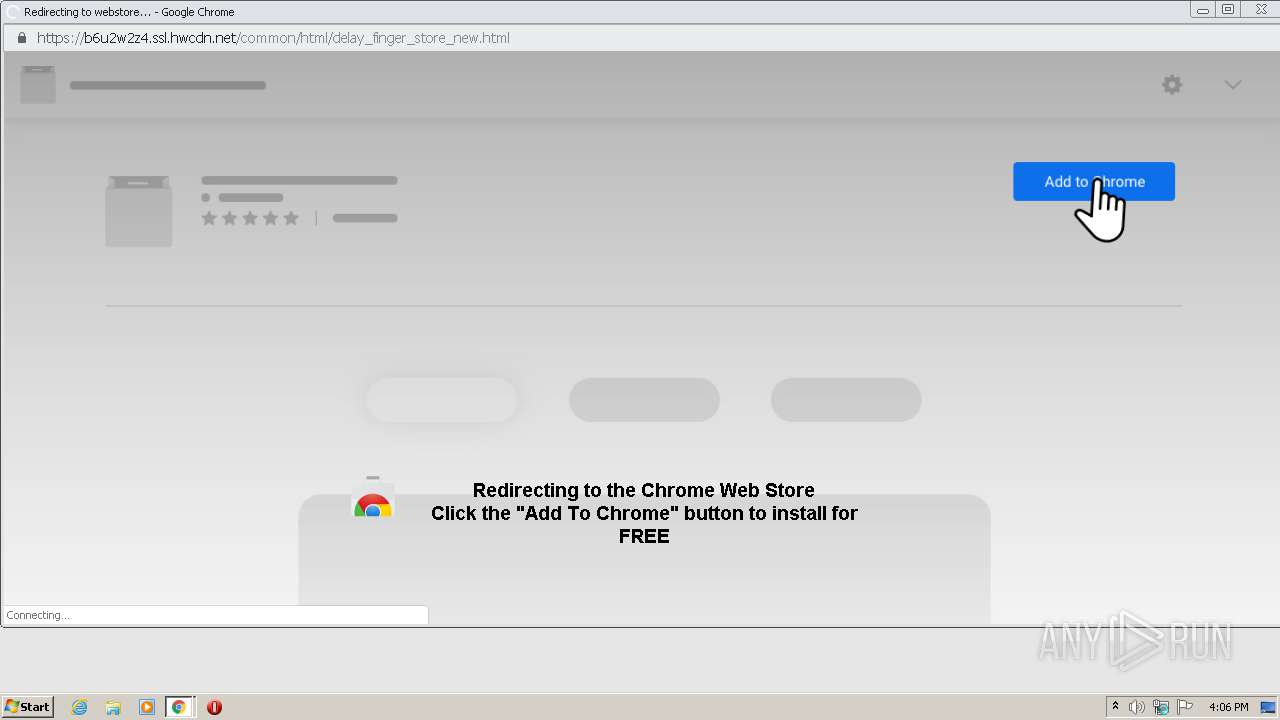
3960 | chrome.exe | 69.16.175.10:443 | b6u2w2z4.ssl.hwcdn.net | Highwinds Network Group, Inc. | US | malicious |
3960 | chrome.exe | 142.250.185.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kaurouby.net |
| suspicious |
accounts.google.com |
| shared |
dolohen.com |
| malicious |
propeller-tracking.com |
| whitelisted |
my.rtmark.net |
| whitelisted |
adtrackingflow.pro |
| unknown |
bainushe.com |
| suspicious |
vashoot.gotrackier.com |
| unknown |
get.keamp.com |
| unknown |
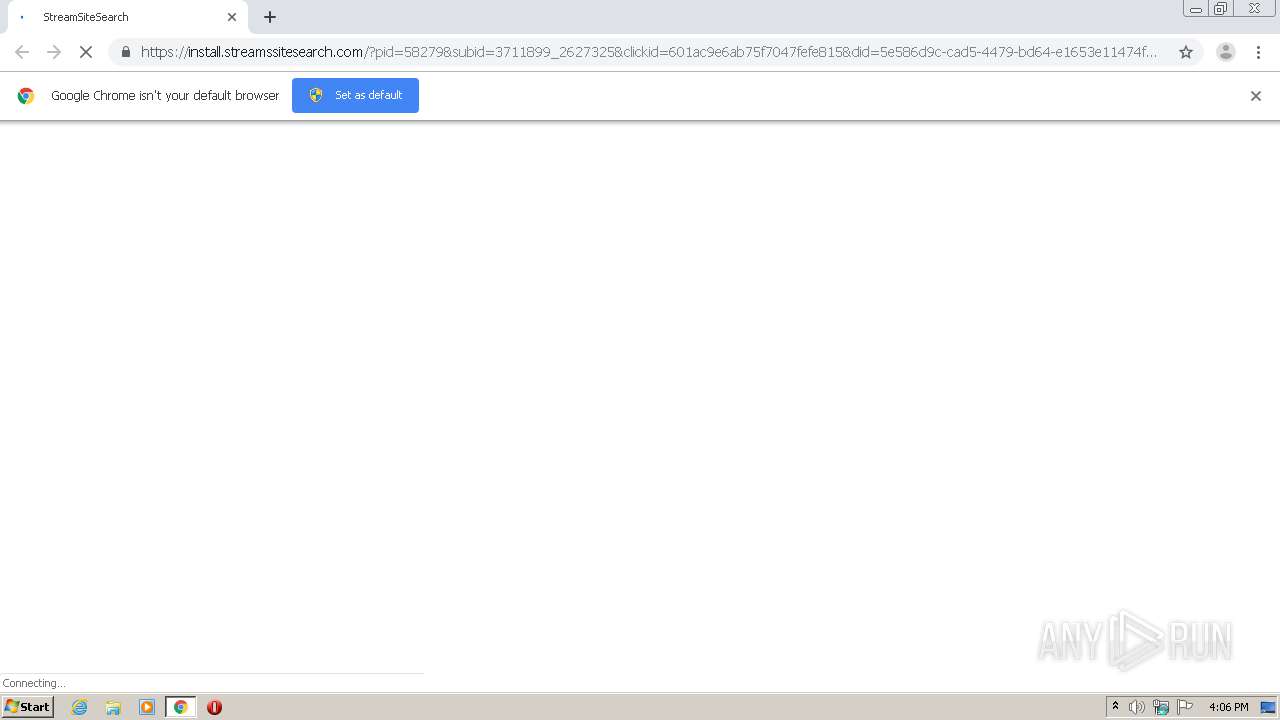
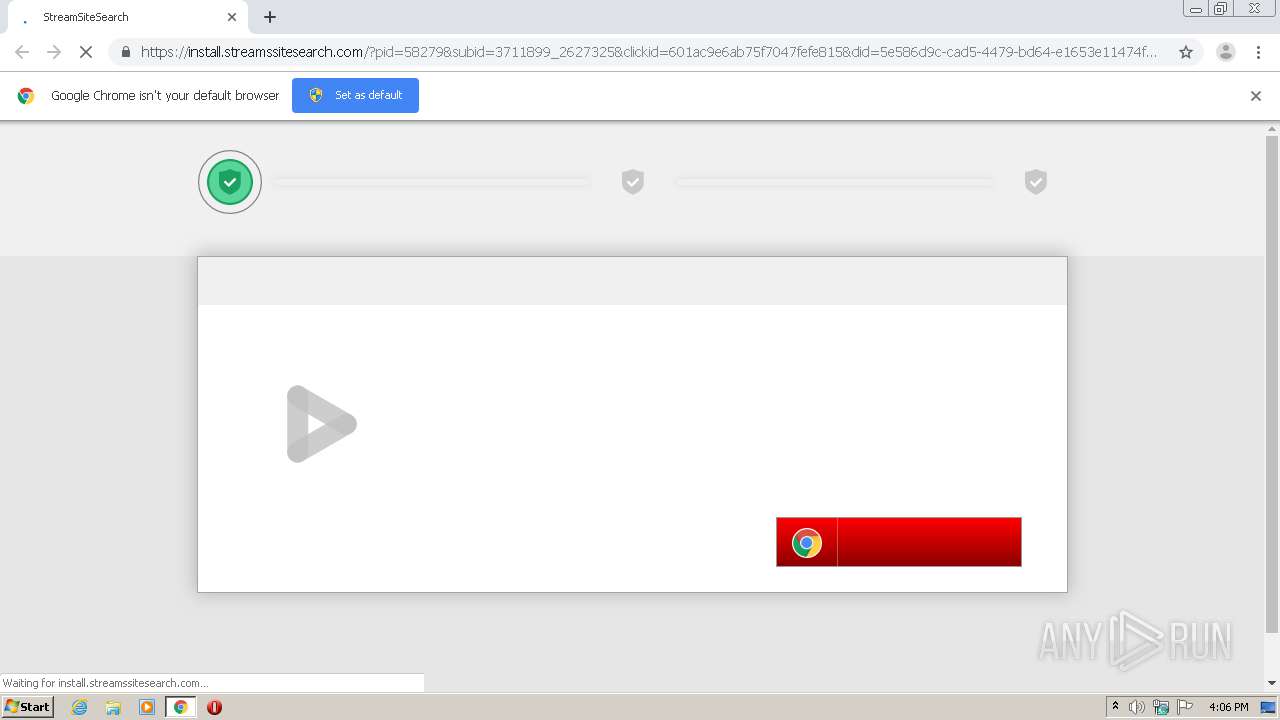
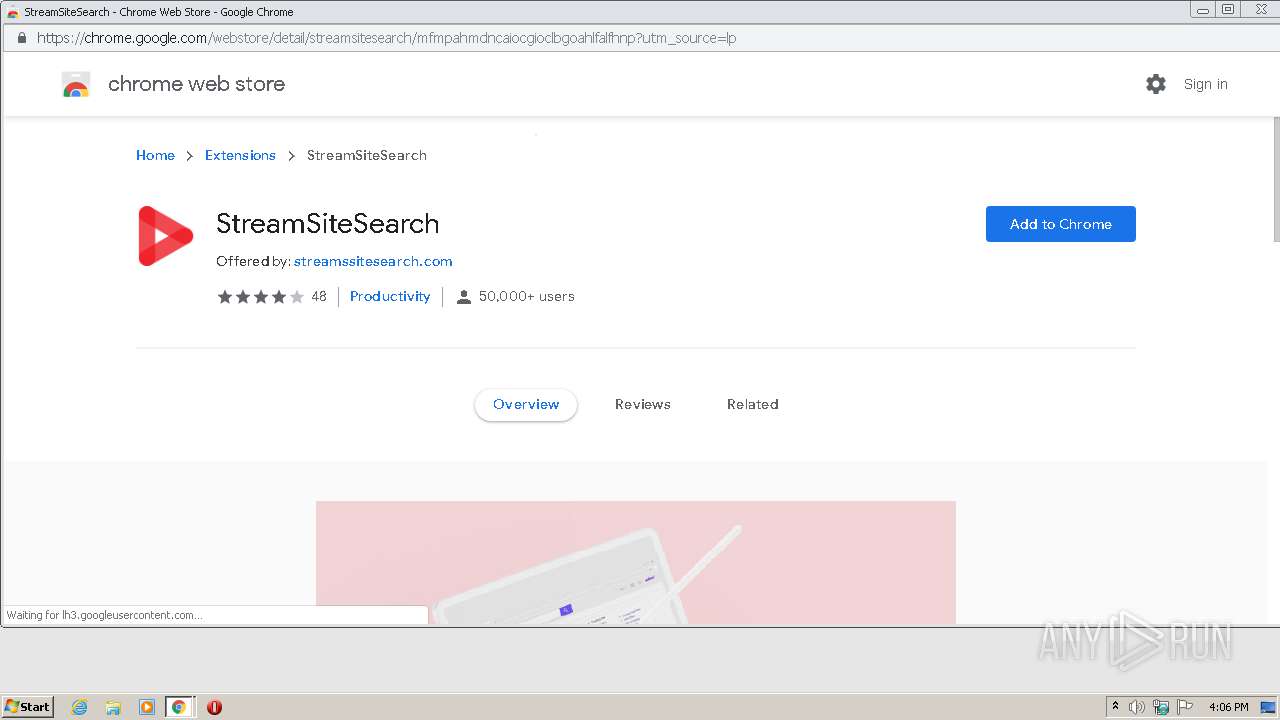
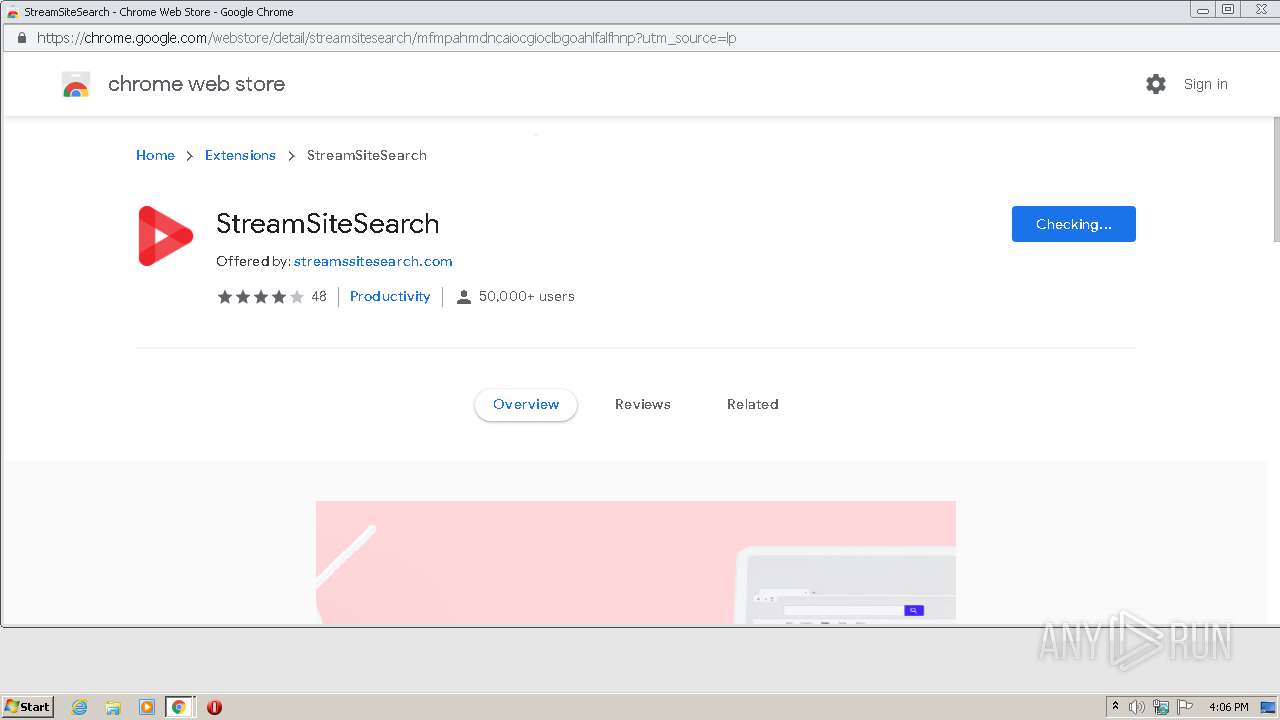
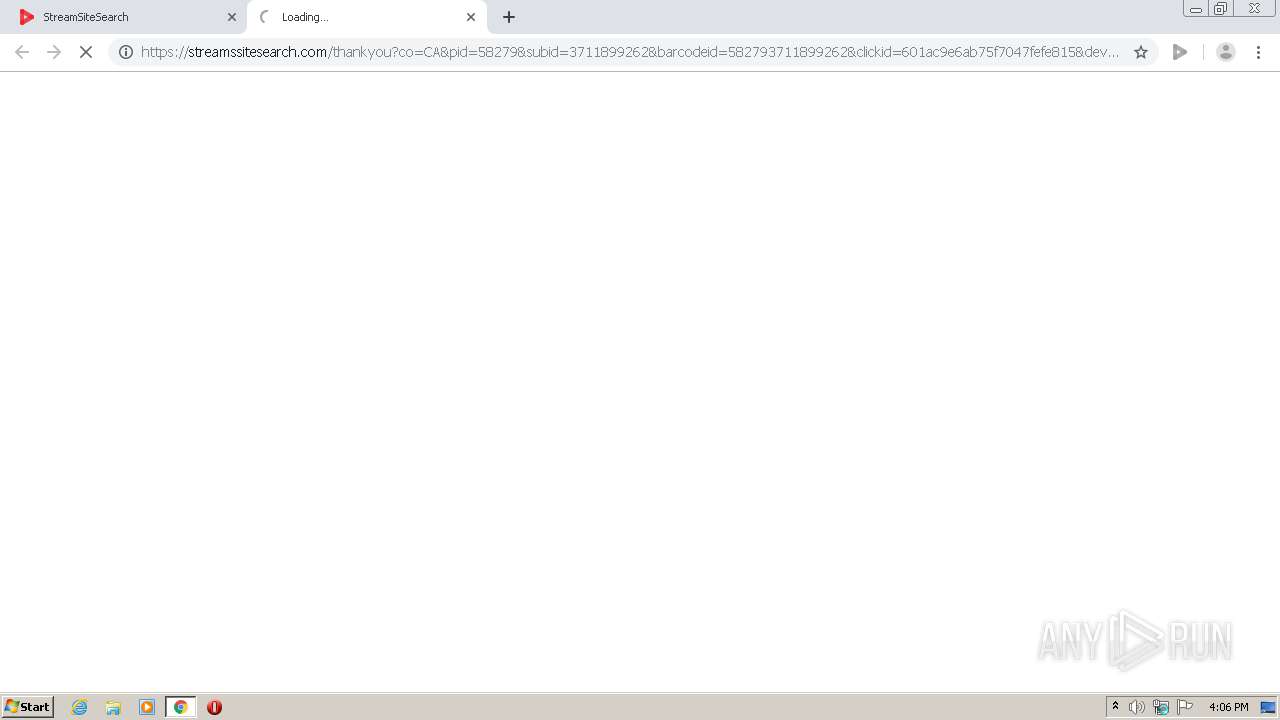
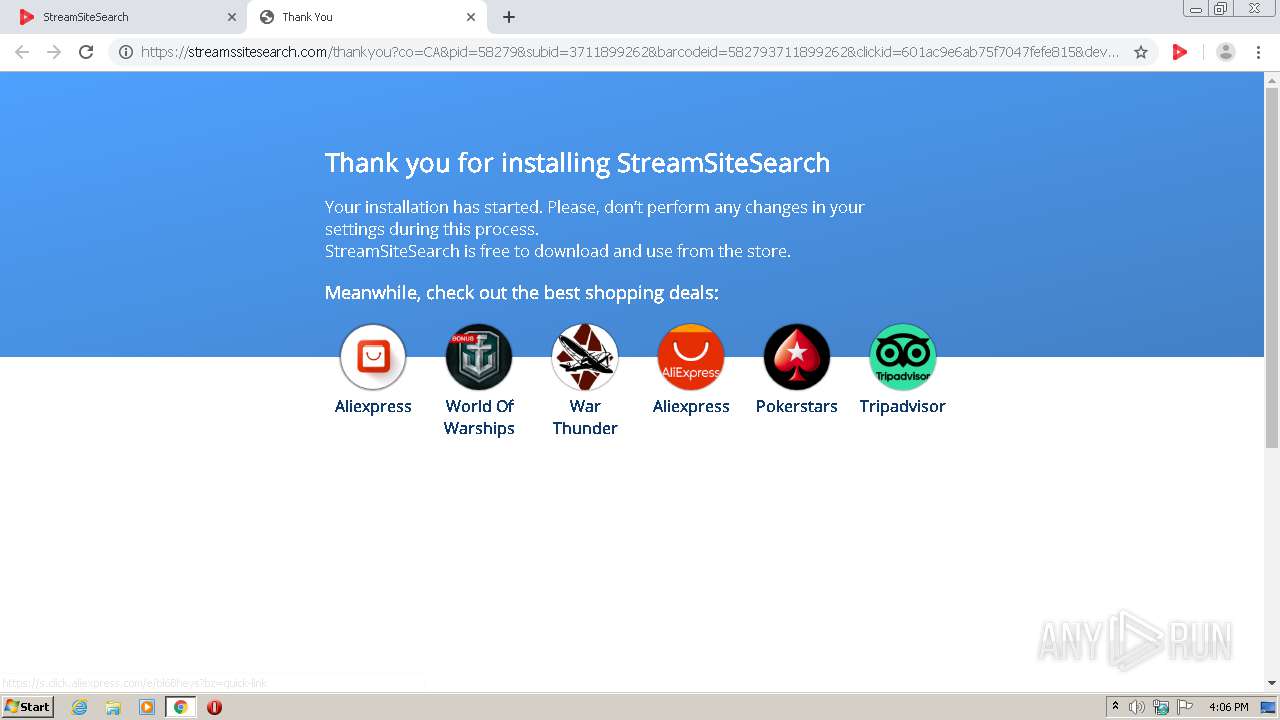
install.streamssitesearch.com |
| suspicious |