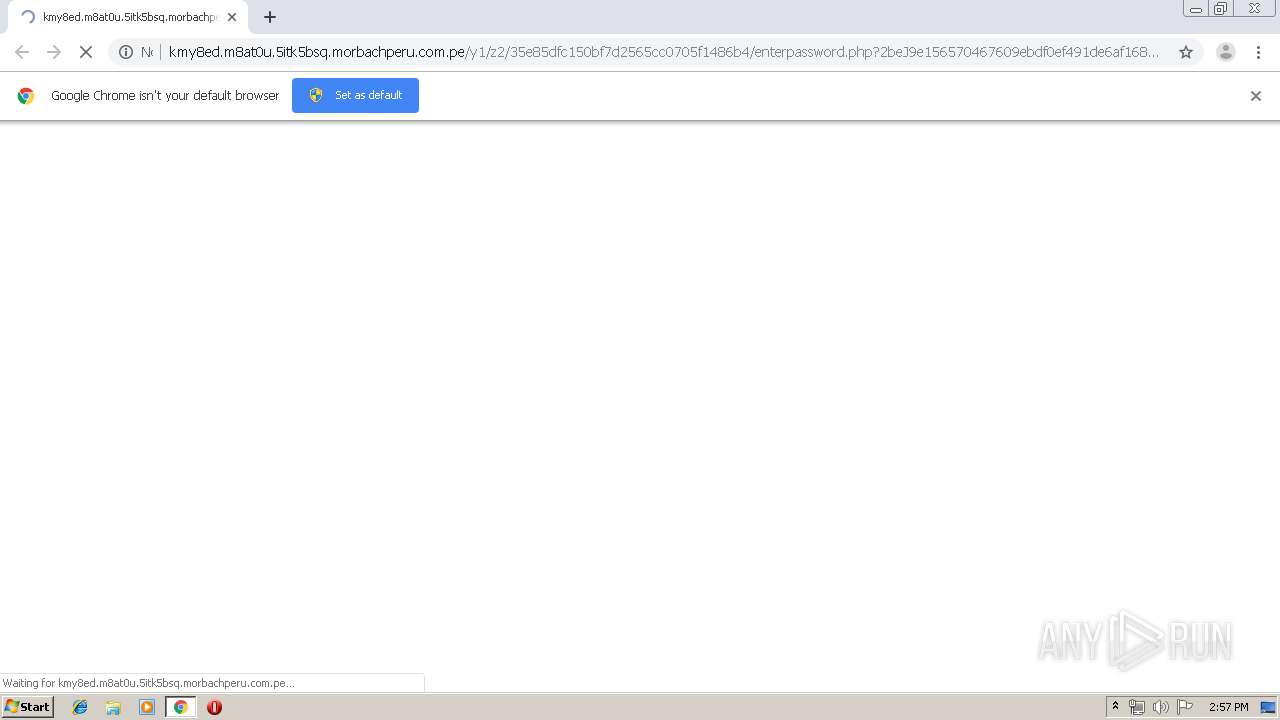
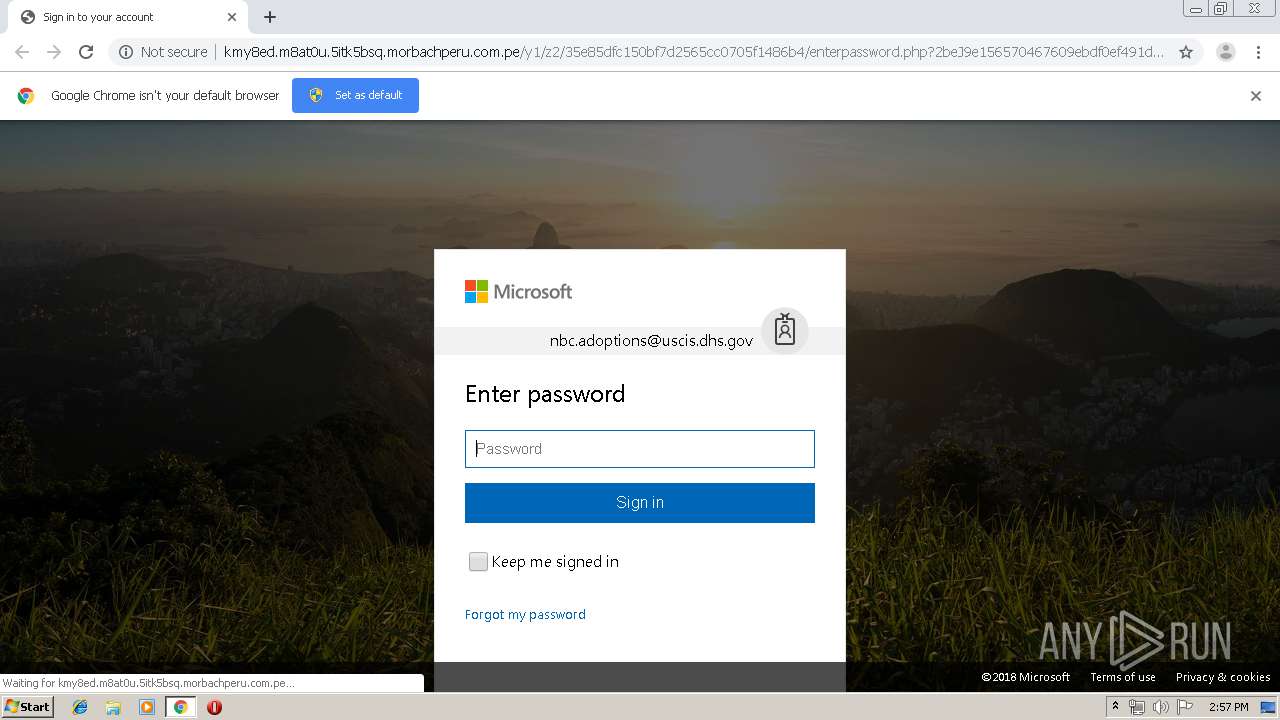
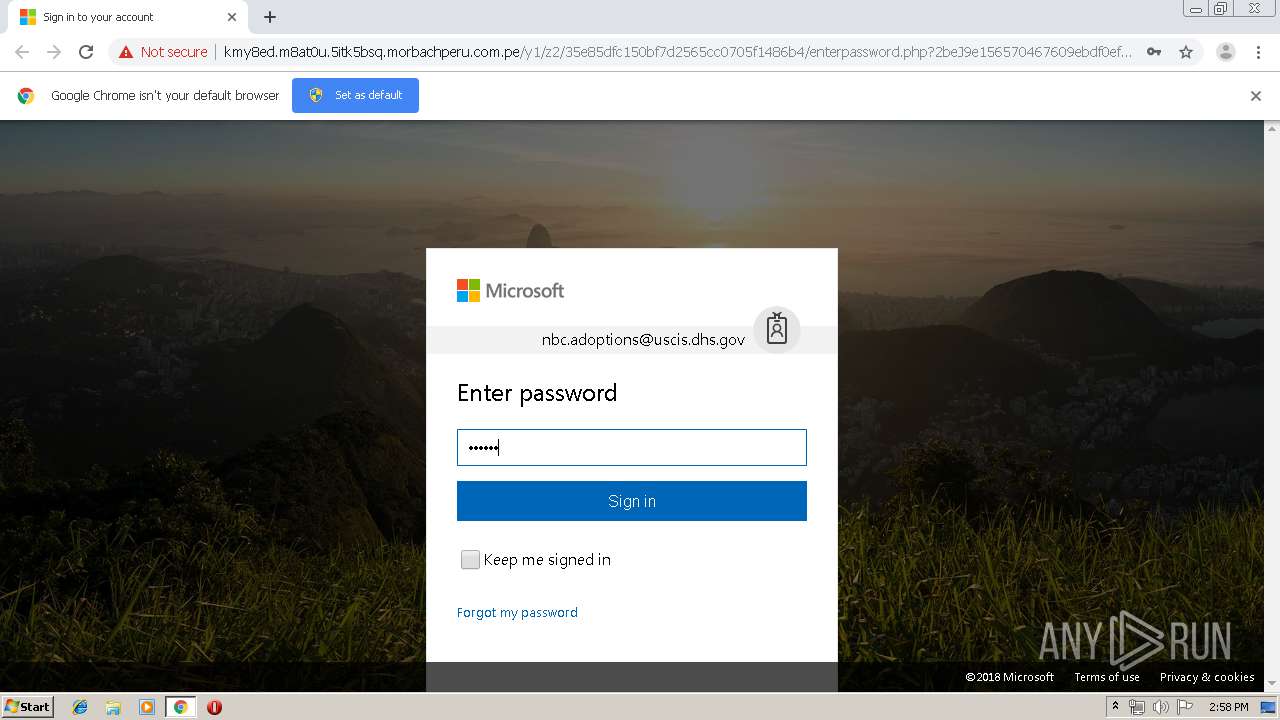
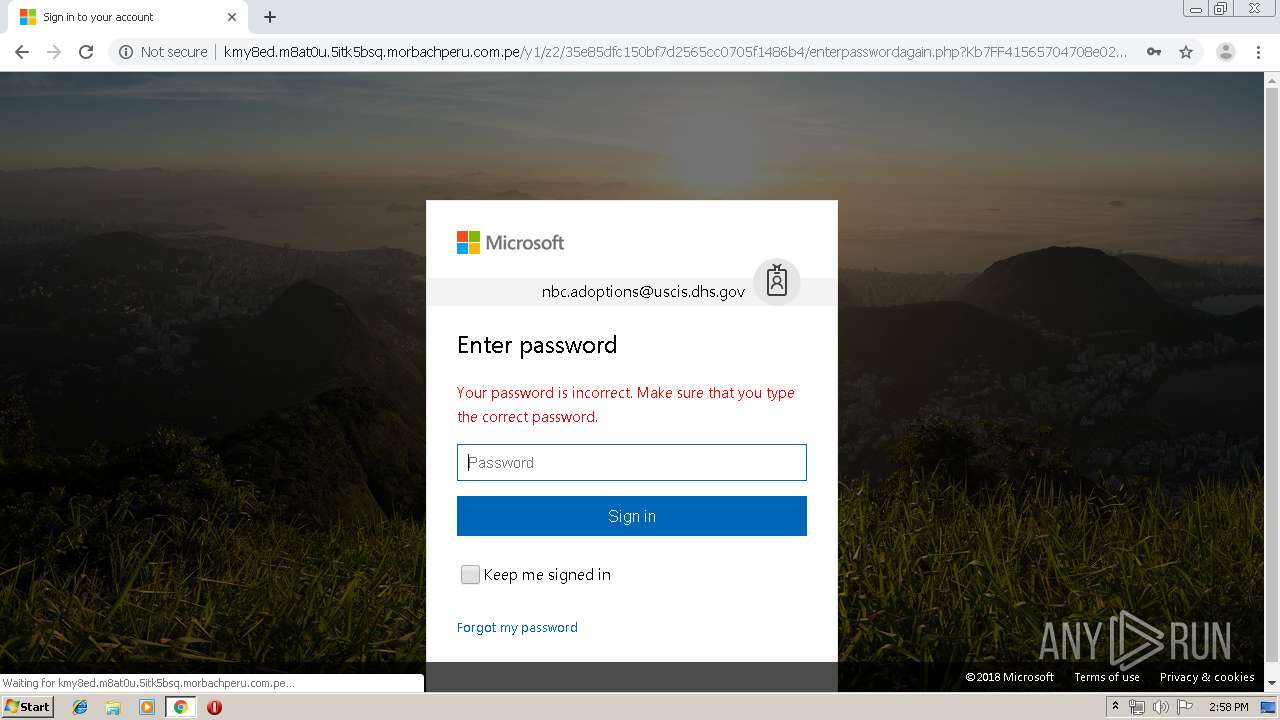
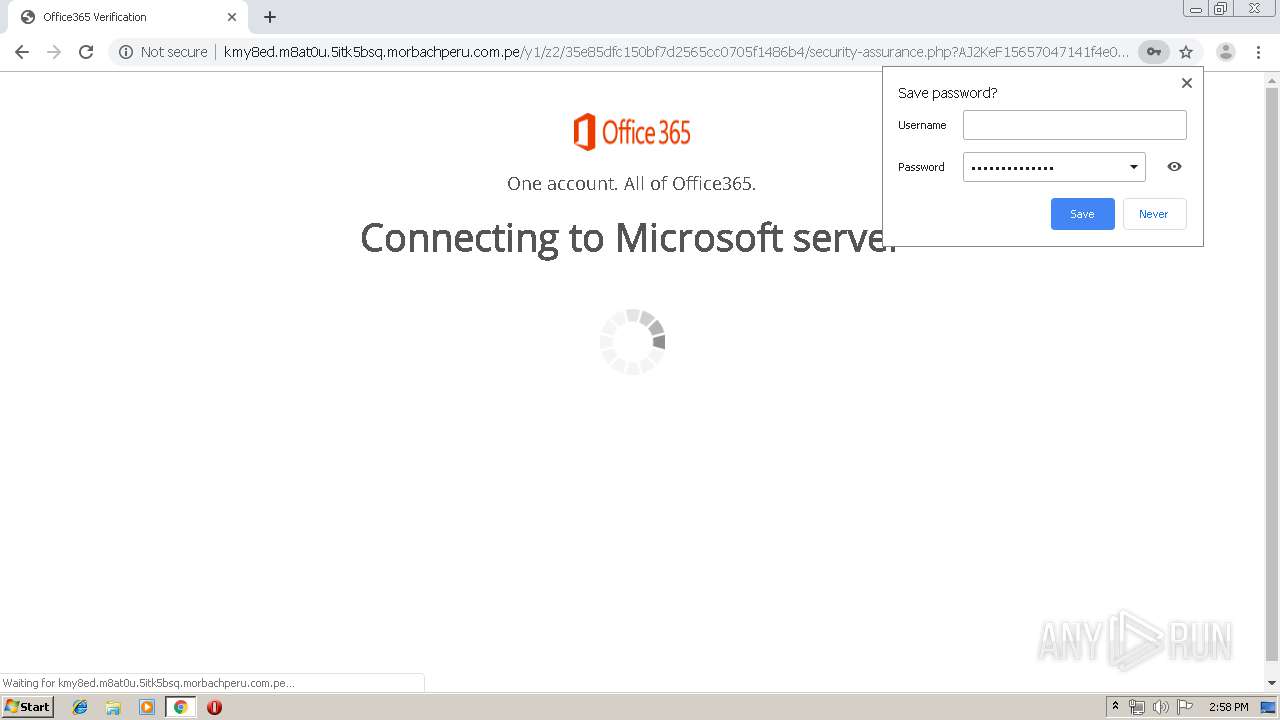
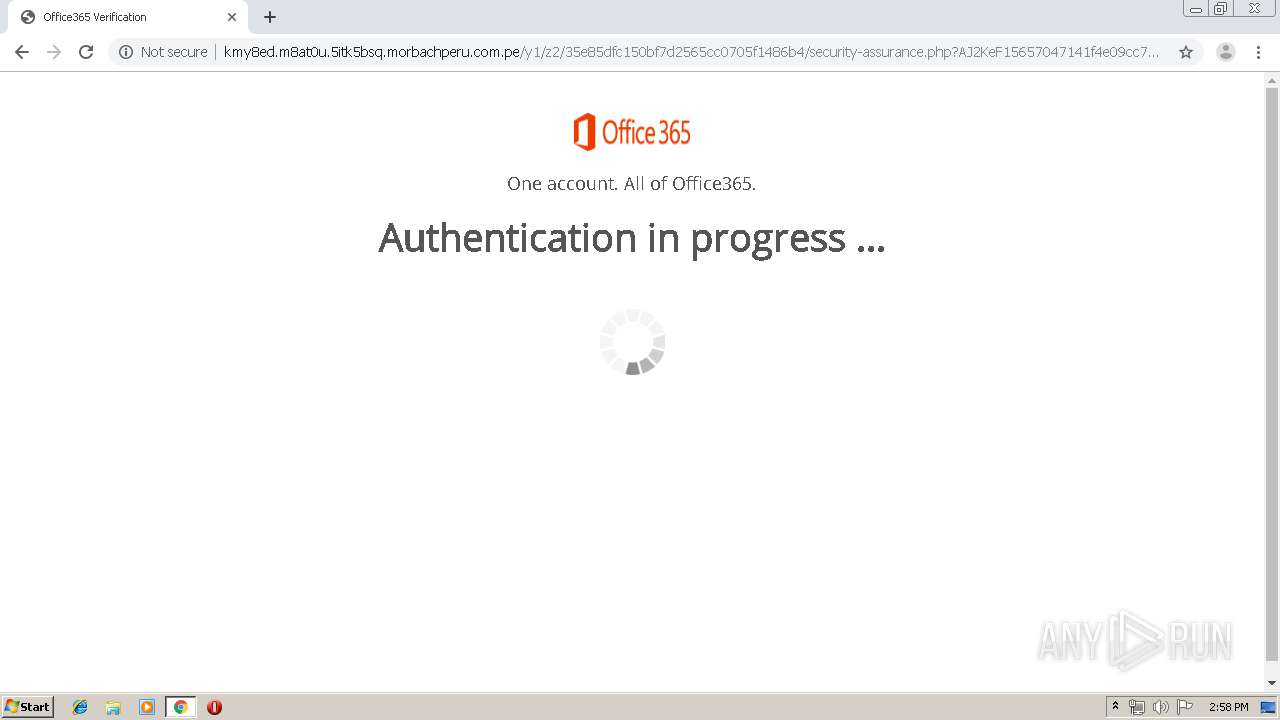
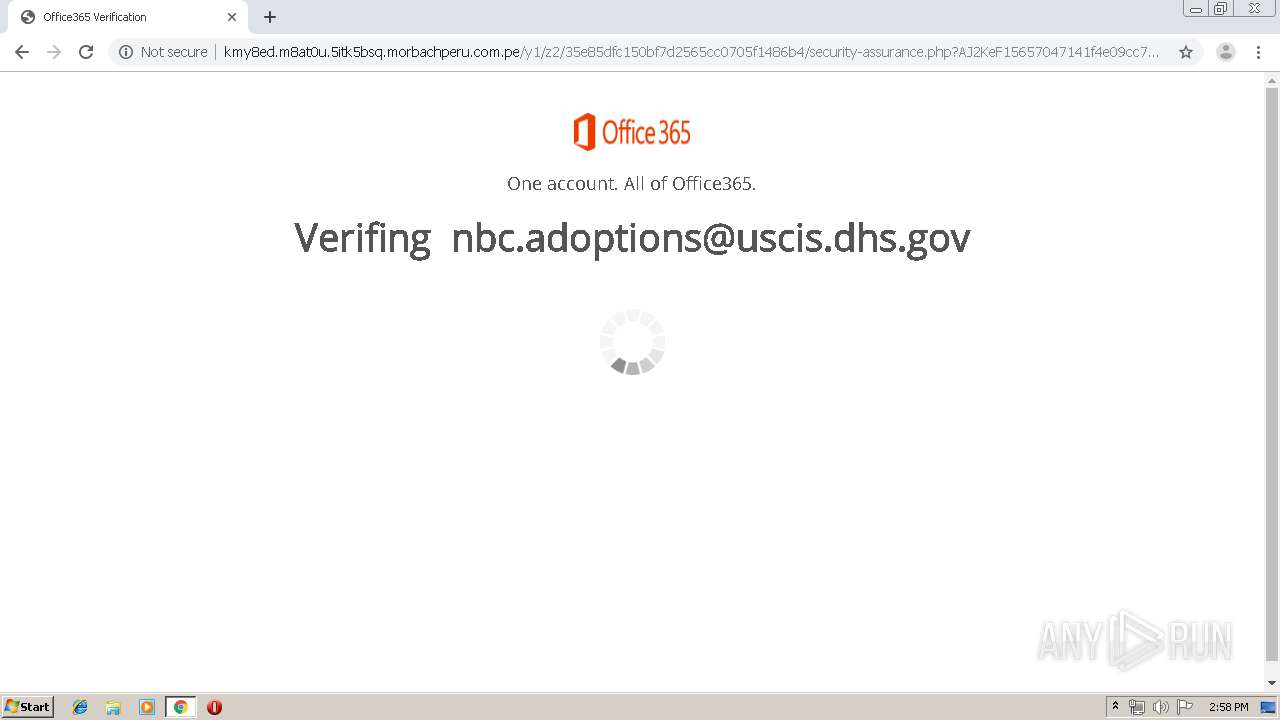
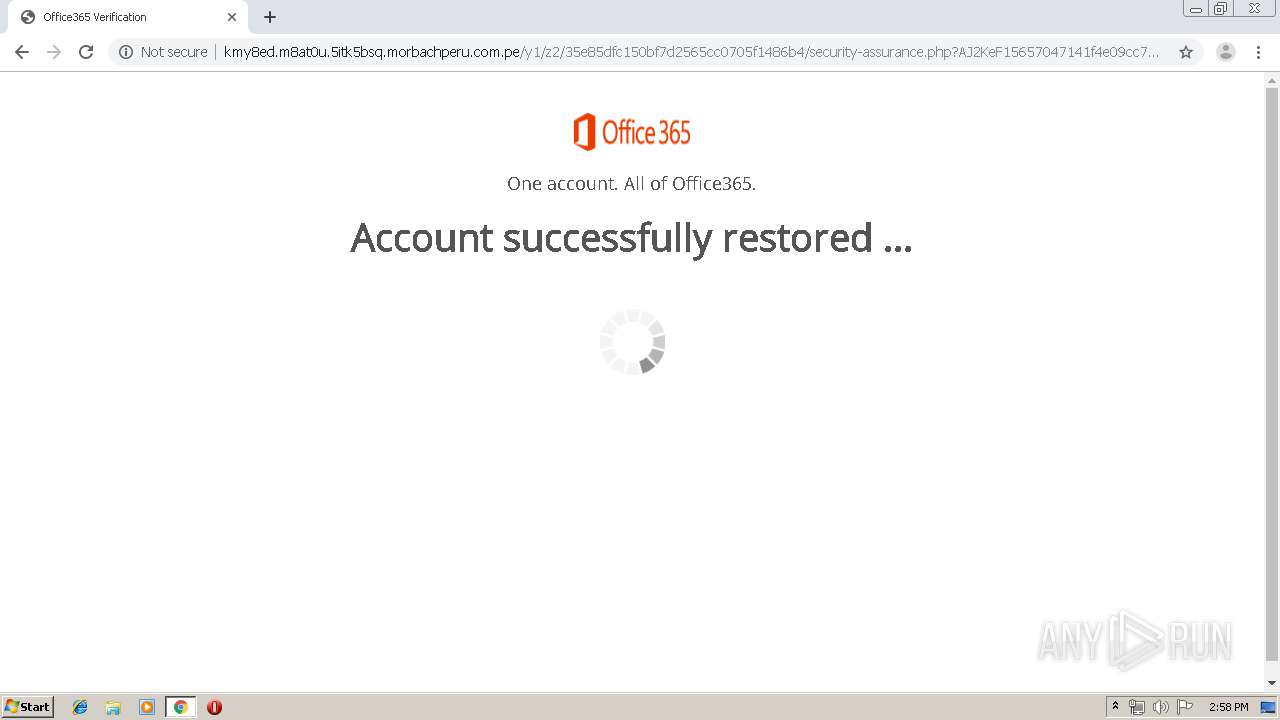
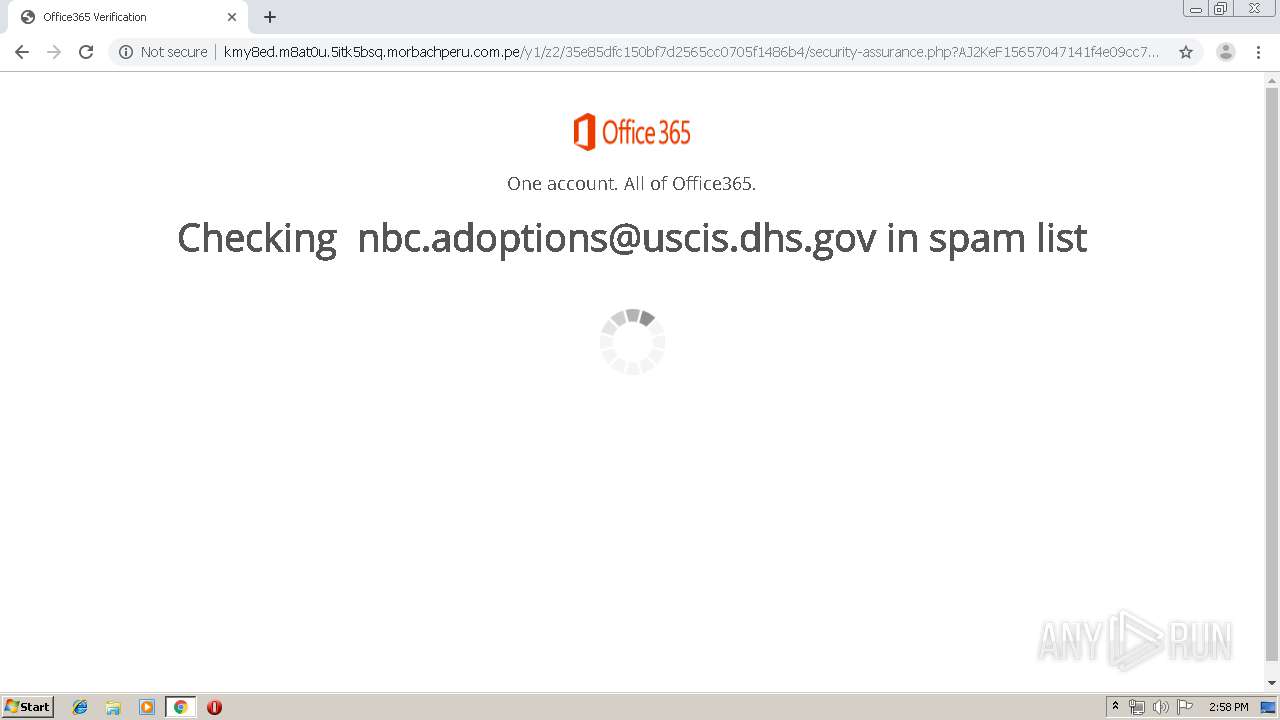
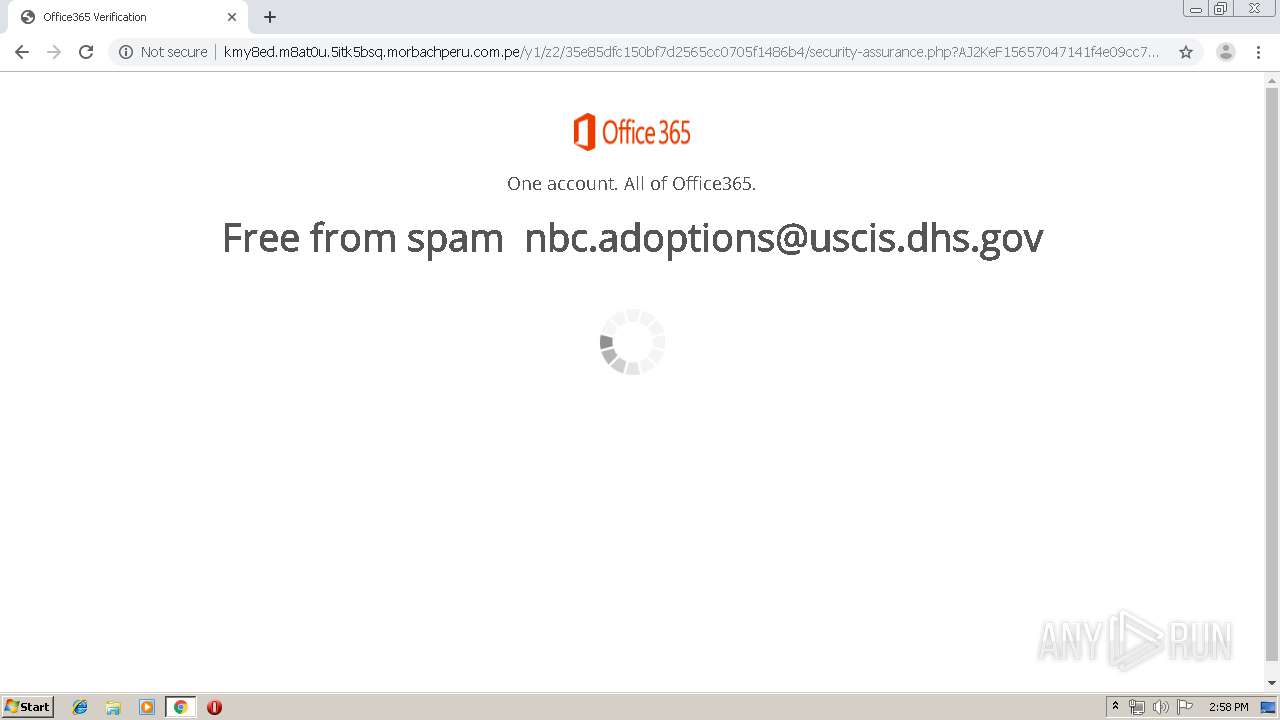
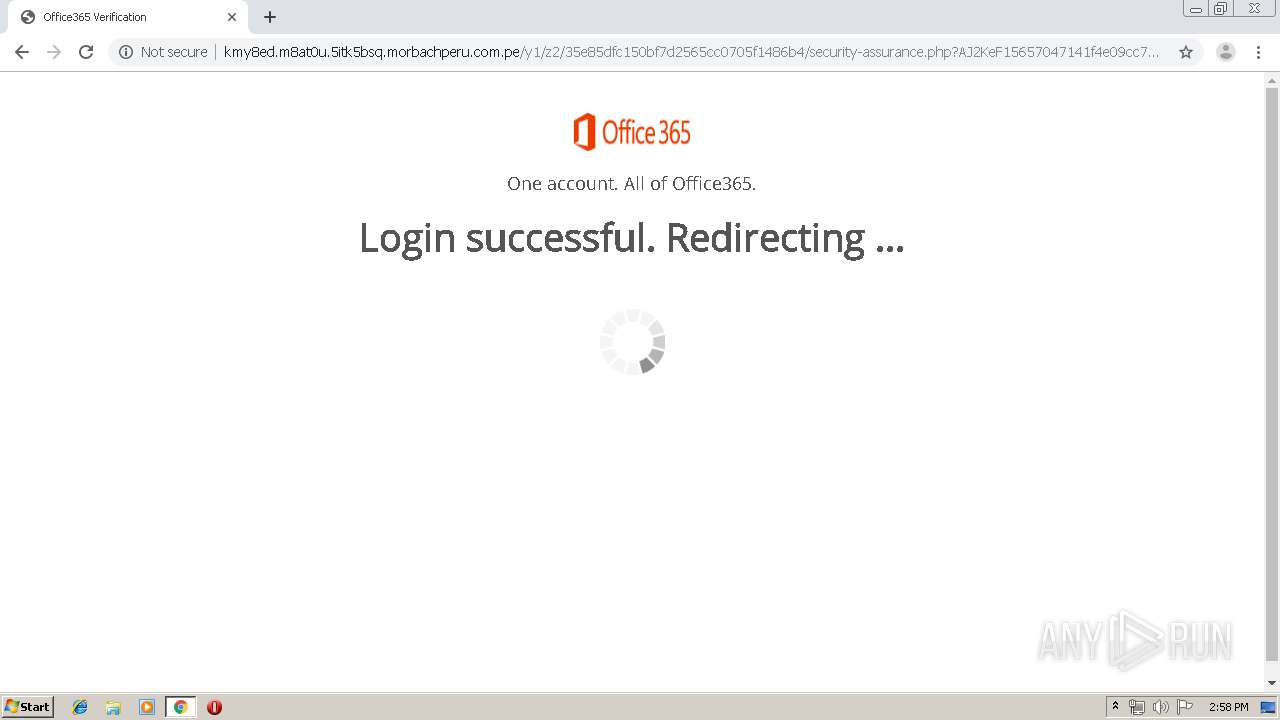
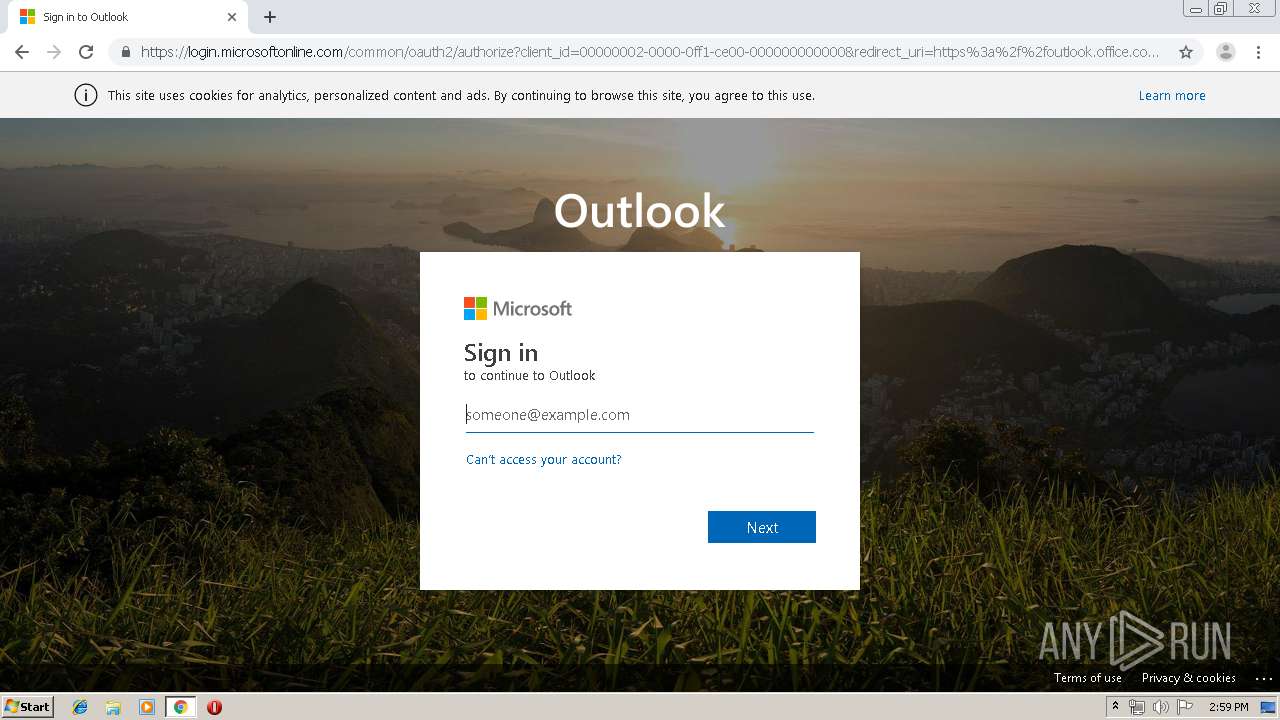
| URL: | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/?84363899237&Yerima=NLA&onowu=nbc.adoptions@uscis.dhs.gov |
| Full analysis: | https://app.any.run/tasks/5008abf9-9f89-43e5-bf53-bff0fe2e51de |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 13:57:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7539F81E43D5542A9A3EE353FC4B8918 |
| SHA1: | A01B53A5EF5C139E26FD575F6BDD0EC199D5931A |
| SHA256: | 33165FBCF05D6AC75CDF732806CB2FFB78151D106CE6D8E7808B83E6797F09C7 |
| SSDEEP: | 3:N1KVIsjuuNqXeG1vlEVlch7Y9KQew14LhGh:Cisjuu21vlEVGh7W |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3416)
INFO
Application launched itself
- chrome.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11494731625534190925 --mojo-platform-channel-handle=4100 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5554905960749912162 --mojo-platform-channel-handle=3672 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16075381496207785961 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2467362893657902033 --mojo-platform-channel-handle=3292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10382408194890243809 --mojo-platform-channel-handle=3912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8110239598509038510 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9427860086362053464 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3458582966222021710 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x70fea9d0,0x70fea9e0,0x70fea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,2711083331668239575,8213410749563523969,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2951046430728361007 --mojo-platform-channel-handle=3208 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
613
Read events
522
Write events
86
Delete events
5
Modification events
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3416-13210178274077625 |
Value: 259 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
28
Text files
183
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2890c7bd-5b8c-4bb0-8c2b-a85b107321c9.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF36e8b3.TMP | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF36e8f2.TMP | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF36e8b3.TMP | text | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
39
DNS requests
24
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3840 | chrome.exe | GET | 304 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/images/ms-logo-v1.svg | CA | — | — | suspicious |
3840 | chrome.exe | GET | 304 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/images/ms-logo-v2.jpg | CA | — | — | suspicious |
3840 | chrome.exe | GET | 200 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/enterpassword.php?2beJ9e156570467609ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf&AP___=nbc.adoptions@uscis.dhs.gov&error= | CA | html | 769 b | suspicious |
3840 | chrome.exe | GET | 200 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/style.css | CA | text | 5.87 Kb | suspicious |
3840 | chrome.exe | GET | 302 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/313oeo1wtfbqfupn1wvk91u4.php?A43e9H156570467609ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf09ebdf0ef491de6af168ed2fc695f1cf&AP___=nbc.adoptions@uscis.dhs.gov&error= | CA | html | 1.09 Kb | suspicious |
3840 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3840 | chrome.exe | GET | 302 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/retry.php?D21A391565704707baa21e150378a3e30269c17cc2cce112baa21e150378a3e30269c17cc2cce112baa21e150378a3e30269c17cc2cce112baa21e150378a3e30269c17cc2cce112baa21e150378a3e30269c17cc2cce112&AP___=nbc.adoptions@uscis.dhs.gov&error=2 | CA | html | 1.13 Kb | suspicious |
3840 | chrome.exe | GET | 200 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/enterpasswordagain.php?Kb7FF41565704708e02687d84577b607eb648db6ca3be441e02687d84577b607eb648db6ca3be441e02687d84577b607eb648db6ca3be441e02687d84577b607eb648db6ca3be441e02687d84577b607eb648db6ca3be441&AP___=nbc.adoptions@uscis.dhs.gov&error=2 | CA | html | 808 b | suspicious |
3840 | chrome.exe | GET | 304 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/style.css | CA | compressed | 808 b | suspicious |
3840 | chrome.exe | GET | 302 | 149.56.240.114:80 | http://kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe/y1/z2/35e85dfc150bf7d2565cc0705f1486b4/?Yerima=NLA&AP___=nbc.adoptions@uscis.dhs.gov | CA | binary | 20 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3840 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 149.56.240.114:80 | kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe | OVH SAS | CA | suspicious |
— | — | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.16.195:443 | www.google.it | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 184.31.91.84:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | whitelisted |
— | — | 13.107.18.11:443 | outlook.office.com | Microsoft Corporation | US | whitelisted |
3840 | chrome.exe | 74.125.4.216:80 | r2---sn-aigzrney.gvt1.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.18.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kmy8ed.m8at0u.5itk5bsq.morbachperu.com.pe |
| suspicious |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-aigzrney.gvt1.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report