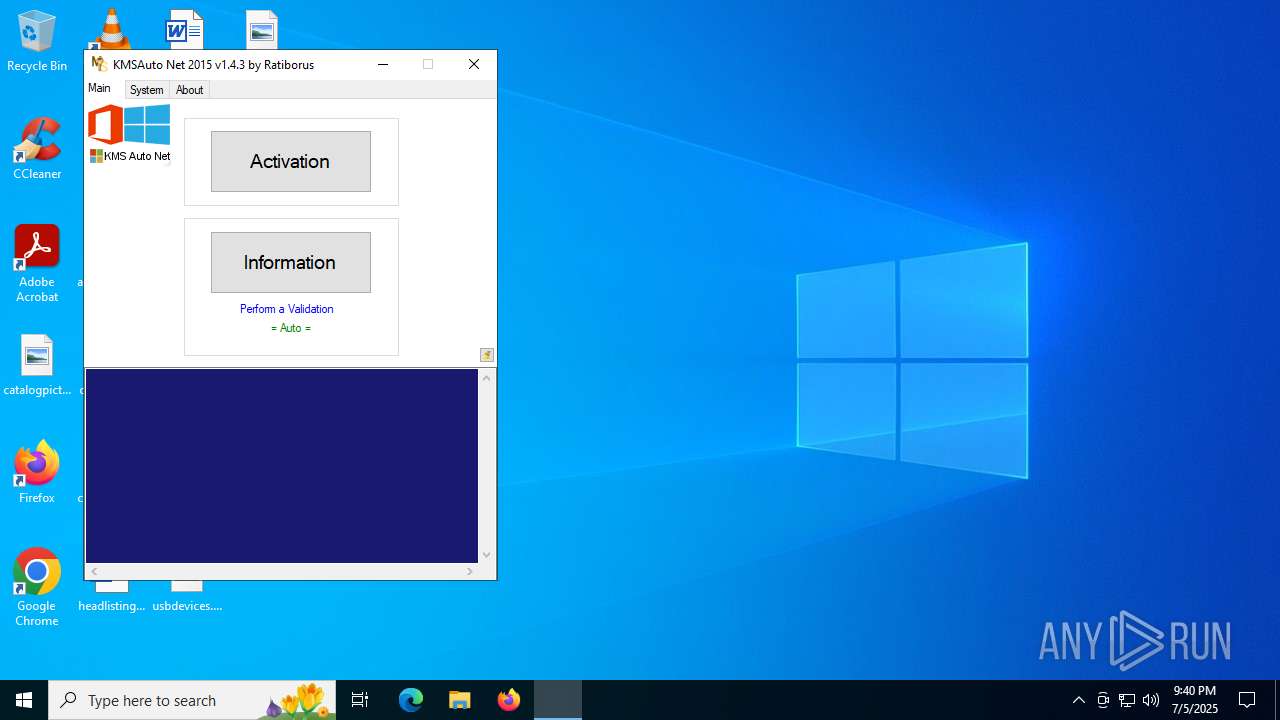
| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/8265dc89-4383-4432-b7cf-2b814641399e |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2025, 21:40:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2AFE64A6DE98AB97C4EC2462A9AE323A |
| SHA1: | CB3F696F24548E9F688AE1C9AD15F1BC73B41227 |
| SHA256: | 3310F1A7A7BFC43B356BE28F7791D16B449D1E796069D0A856C21B10EB2453C5 |
| SSDEEP: | 98304:pQacMiy8cWEv9E01DwQDYpveEzROLQs29E0ZrsK5sdEtzVeOlp7NFEO3WLf9E0I0:nWmV9D |
MALICIOUS
Executing a file with an untrusted certificate
- KMSAuto Net.exe (PID: 4412)
- KMSAuto Net.exe (PID: 2040)
- certmgr.exe (PID: 4664)
- certmgr.exe (PID: 6140)
- KMSSS.exe (PID: 856)
- FakeClient.exe (PID: 3620)
- certmgr.exe (PID: 6376)
- certmgr.exe (PID: 5724)
Opens a text file (SCRIPT)
- cscript.exe (PID: 2128)
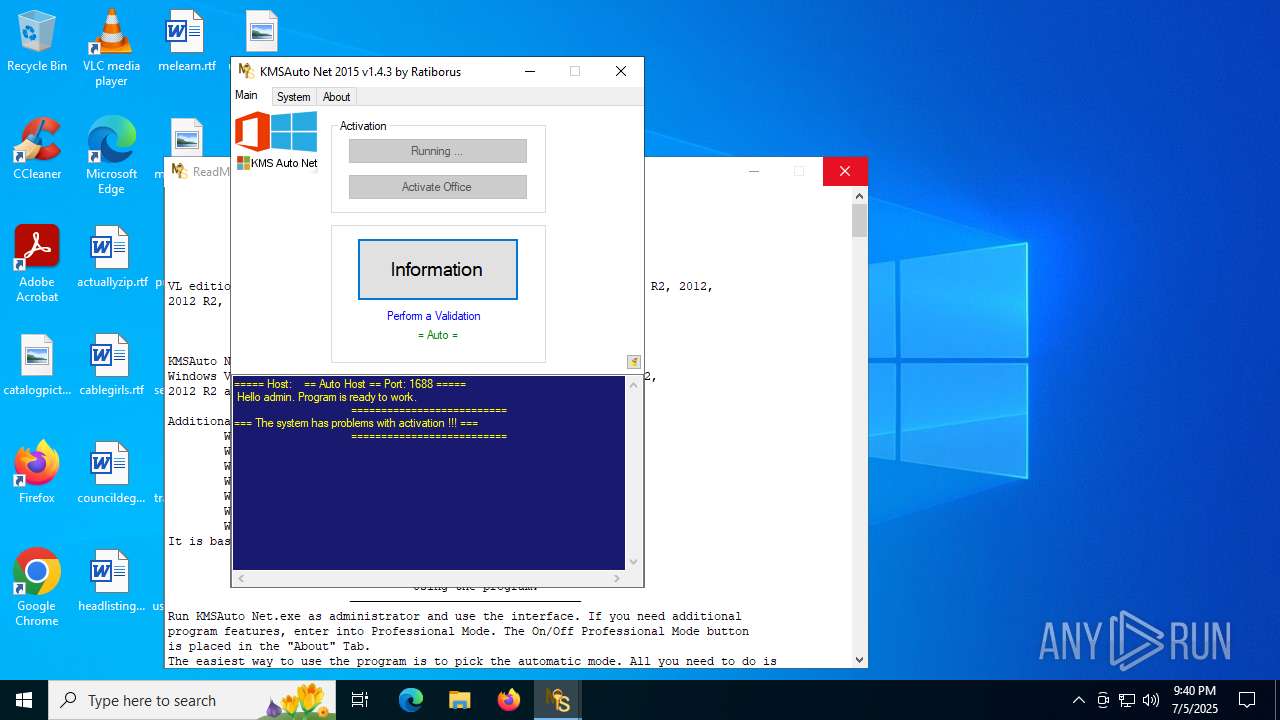
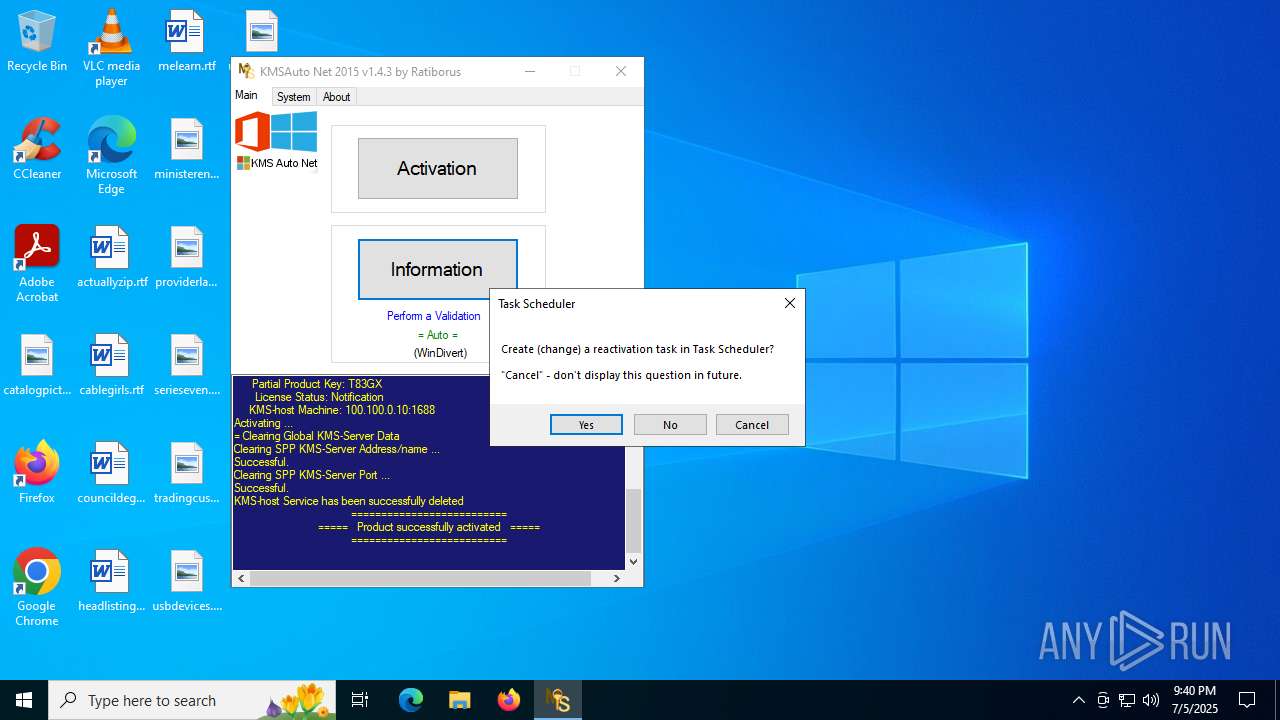
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2508)
SUSPICIOUS
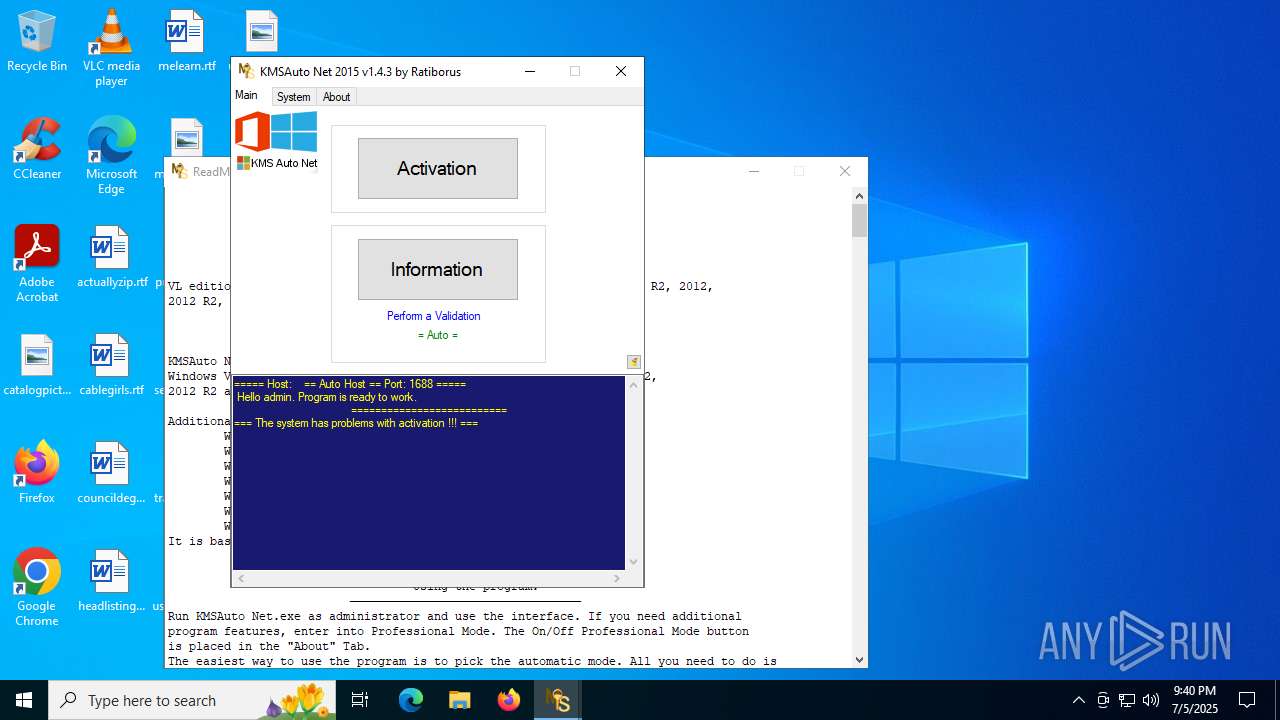
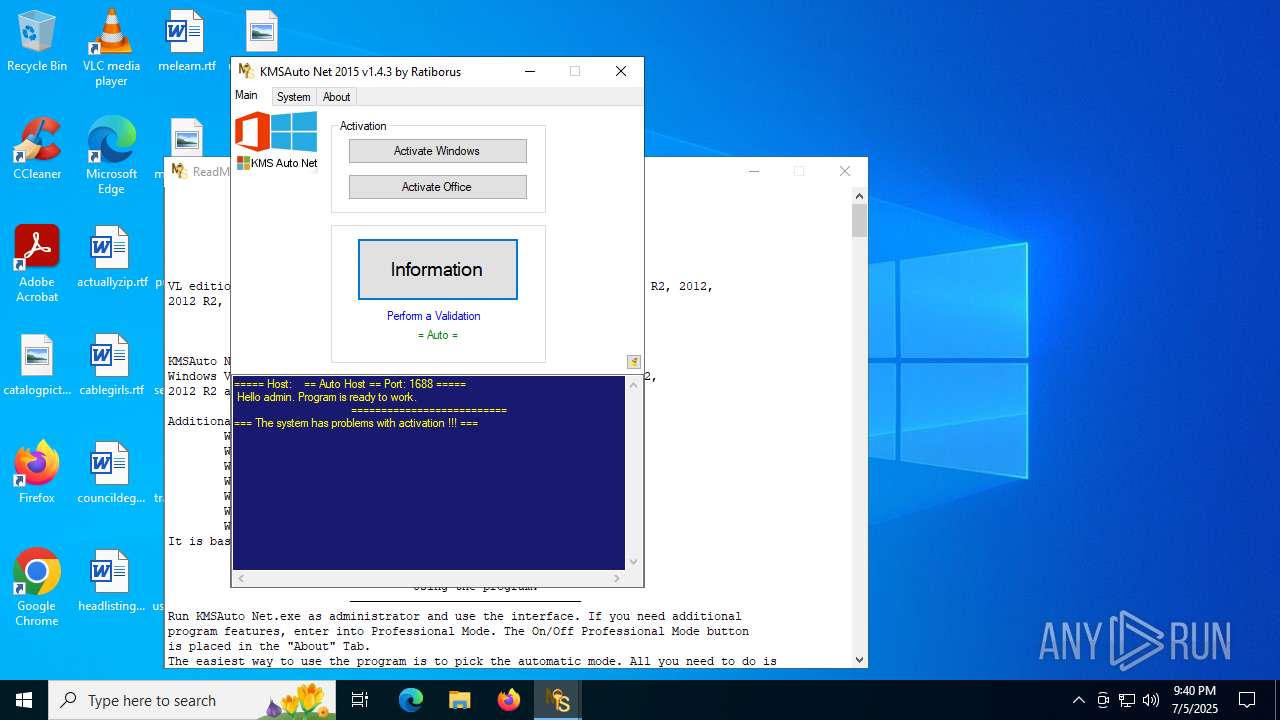
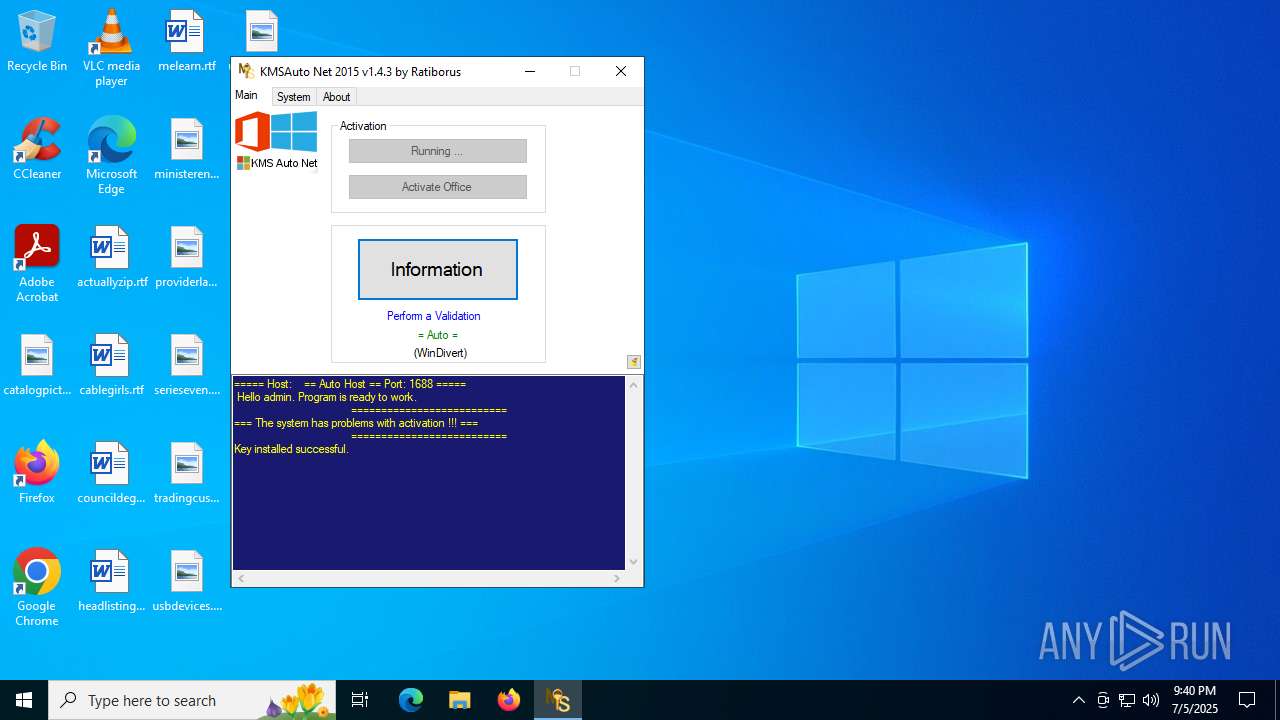
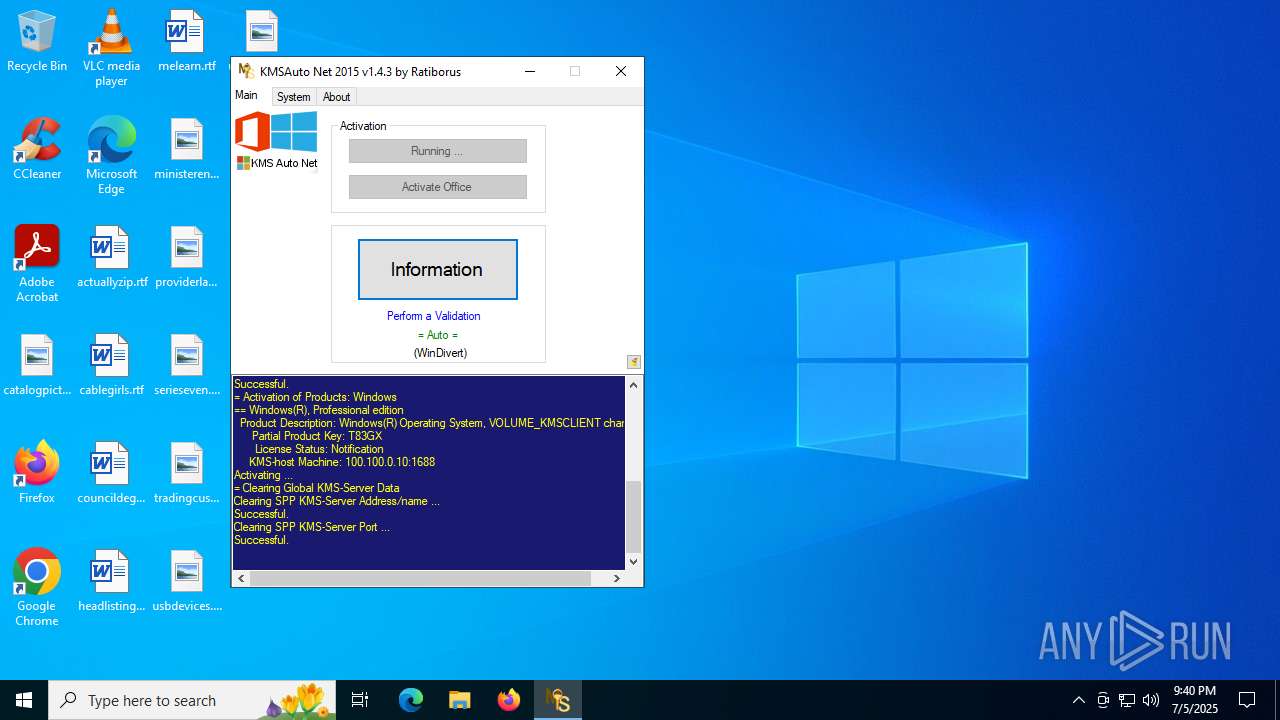
KMS tool has been detected
- KMSAuto Net.exe (PID: 4412)
- KMSAuto Net.exe (PID: 2040)
- KMSAuto Net.exe (PID: 2040)
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 2040)
The process executes VB scripts
- KMSAuto Net.exe (PID: 2040)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 2128)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2128)
There is functionality for taking screenshot (YARA)
- KMSAuto Net.exe (PID: 2040)
Starts application with an unusual extension
- cmd.exe (PID: 5444)
- cmd.exe (PID: 7008)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 6720)
- cmd.exe (PID: 1180)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2128)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2040)
- cmd.exe (PID: 3720)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 2128)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 2128)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2128)
Adds/modifies Windows certificates
- certmgr.exe (PID: 4664)
- certmgr.exe (PID: 6140)
- certmgr.exe (PID: 6376)
- certmgr.exe (PID: 5724)
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 2040)
Executable content was dropped or overwritten
- bin.dat (PID: 6268)
- AESDecoder.exe (PID: 4132)
- wzt.dat (PID: 5896)
- KMSAuto Net.exe (PID: 2040)
- bin_x64.dat (PID: 2692)
- wzt.dat (PID: 3820)
- bin_x64.dat (PID: 6780)
- AESDecoder.exe (PID: 6292)
- bin.dat (PID: 1976)
Process drops legitimate windows executable
- wzt.dat (PID: 5896)
- bin_x64.dat (PID: 2692)
- wzt.dat (PID: 3820)
- bin_x64.dat (PID: 6780)
Drops a system driver (possible attempt to evade defenses)
- bin_x64.dat (PID: 2692)
- bin_x64.dat (PID: 6780)
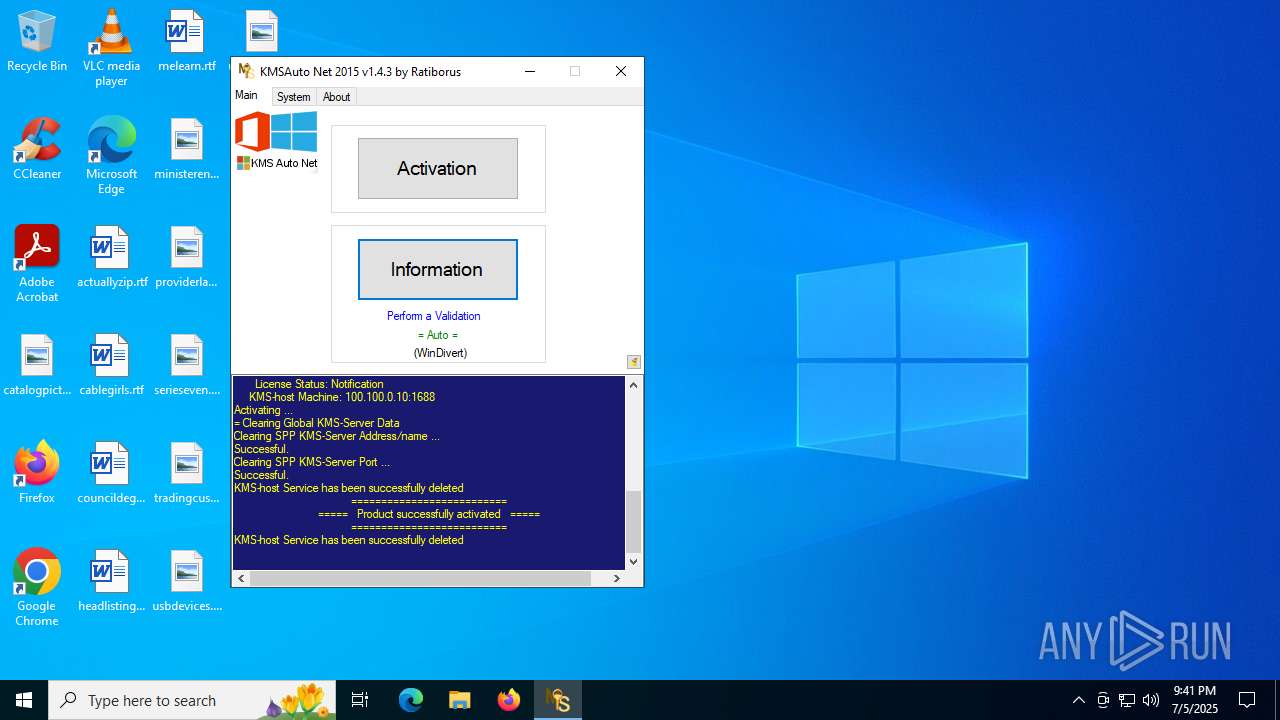
Creates a new Windows service
- sc.exe (PID: 5352)
Application launched itself
- cmd.exe (PID: 3720)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 2040)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 2040)
Windows service management via SC.EXE
- sc.exe (PID: 6664)
- sc.exe (PID: 2324)
- sc.exe (PID: 2432)
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 2040)
Executes as Windows Service
- KMSSS.exe (PID: 856)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 5540)
Stops a currently running service
- sc.exe (PID: 2292)
- sc.exe (PID: 3960)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 2388)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6220)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 2040)
- cmd.exe (PID: 2180)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 3100)
Modifies existing scheduled task
- schtasks.exe (PID: 1720)
INFO
Checks supported languages
- KMSAuto Net.exe (PID: 2040)
- certmgr.exe (PID: 4664)
- certmgr.exe (PID: 6140)
- bin.dat (PID: 6268)
- wzt.dat (PID: 5896)
- AESDecoder.exe (PID: 4132)
- bin_x64.dat (PID: 2692)
- KMSSS.exe (PID: 856)
- FakeClient.exe (PID: 3620)
- certmgr.exe (PID: 6376)
- certmgr.exe (PID: 5724)
- bin.dat (PID: 1976)
- wzt.dat (PID: 3820)
- bin_x64.dat (PID: 6780)
- AESDecoder.exe (PID: 6292)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 2040)
- KMSSS.exe (PID: 856)
Reads the computer name
- KMSAuto Net.exe (PID: 2040)
- FakeClient.exe (PID: 3620)
- KMSSS.exe (PID: 856)
Creates a new folder
- cmd.exe (PID: 6320)
- cmd.exe (PID: 4788)
- cmd.exe (PID: 6164)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 2040)
Reads Environment values
- KMSAuto Net.exe (PID: 2040)
Reads product name
- KMSAuto Net.exe (PID: 2040)
Creates files in the program directory
- KMSAuto Net.exe (PID: 2040)
- bin.dat (PID: 6268)
- cmd.exe (PID: 4788)
- wzt.dat (PID: 5896)
- AESDecoder.exe (PID: 4132)
- bin_x64.dat (PID: 2692)
- KMSSS.exe (PID: 856)
- wzt.dat (PID: 3820)
- cmd.exe (PID: 6164)
- bin_x64.dat (PID: 6780)
- AESDecoder.exe (PID: 6292)
- bin.dat (PID: 1976)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2128)
The sample compiled with english language support
- KMSAuto Net.exe (PID: 2040)
- wzt.dat (PID: 5896)
- AESDecoder.exe (PID: 4132)
- bin_x64.dat (PID: 2692)
- wzt.dat (PID: 3820)
- AESDecoder.exe (PID: 6292)
- bin_x64.dat (PID: 6780)
Adds a route via ROUTE.EXE
- ROUTE.EXE (PID: 6260)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 2528)
Create files in a temporary directory
- KMSAuto Net.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (16) |
|---|---|---|
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:01 07:21:28+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 9008128 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x899212 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.3.0 |
| ProductVersionNumber: | 1.4.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.4.3 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.4.3 |
| AssemblyVersion: | 1.4.3.0 |
Total processes
285
Monitored processes
147
Malicious processes
6
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\Sysnative\cmd.exe /D /c del /F /Q "AESDecoder.exe" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\Sysnative\cmd.exe /D /c bin_x64.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | C:\WINDOWS\Sysnative\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59A52881-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\system32\cmd.exe /c netstat -ano | find ":1688 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 554
Read events
7 538
Write events
8
Delete events
8
Modification events
| (PID) Process: | (4664) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | F81F111D0E5AB58D396F7BF525577FD30FDC95AA |
Value: | |||
| (PID) Process: | (4664) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\F81F111D0E5AB58D396F7BF525577FD30FDC95AA |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000F81F111D0E5AB58D396F7BF525577FD30FDC95AA2000000001000000E8010000308201E43082014DA003020102021008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D0101040500300E310C300A06035504031303575A54301E170D3135313130383038313534395A170D3339313233313233353935395A300E310C300A06035504031303575A5430819F300D06092A864886F70D010101050003818D0030818902818100A3B38E6E8CD01F282D0872986D29BF5F0EAAD61A32C045D9B23DB1C221C3679770C401DE98695E88CAD621B319730DCABEDF4C4709EEBE8126DD567A9AB387DAB7EA13B3665166464D1B8EFFFED8BC4225515A9AAA170E595EB348A496309110C8EB66D0490F113A3C79A508058448B0398BE6F9D34F84C60E694C472C72F9B70203010001A3433041303F0603551D01043830368010E4E11038D29FC50F20A0C1914BBEFF0BA110300E310C300A06035504031303575A54821008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D01010405000381810054C251E1B9CDCA11ADE10887278347C178233BFFB85A6D692CA235D68AFE76D59F2113E7C3016AC0347E7131D590047A877083536F61D90FCB2BF95856952ABD4F63DACCFCCC840950667CC68F7513F8AE72DC7676E94B61FA169158457EA2B8531A593671E79D886743E24EDDF7141E0443E22F1F6B16B0A76D720466E4B8E8 | |||
| (PID) Process: | (6140) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates |
| Operation: | delete value | Name: | F81F111D0E5AB58D396F7BF525577FD30FDC95AA |
Value: | |||
| (PID) Process: | (6140) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\F81F111D0E5AB58D396F7BF525577FD30FDC95AA |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000F81F111D0E5AB58D396F7BF525577FD30FDC95AA2000000001000000E8010000308201E43082014DA003020102021008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D0101040500300E310C300A06035504031303575A54301E170D3135313130383038313534395A170D3339313233313233353935395A300E310C300A06035504031303575A5430819F300D06092A864886F70D010101050003818D0030818902818100A3B38E6E8CD01F282D0872986D29BF5F0EAAD61A32C045D9B23DB1C221C3679770C401DE98695E88CAD621B319730DCABEDF4C4709EEBE8126DD567A9AB387DAB7EA13B3665166464D1B8EFFFED8BC4225515A9AAA170E595EB348A496309110C8EB66D0490F113A3C79A508058448B0398BE6F9D34F84C60E694C472C72F9B70203010001A3433041303F0603551D01043830368010E4E11038D29FC50F20A0C1914BBEFF0BA110300E310C300A06035504031303575A54821008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D01010405000381810054C251E1B9CDCA11ADE10887278347C178233BFFB85A6D692CA235D68AFE76D59F2113E7C3016AC0347E7131D590047A877083536F61D90FCB2BF95856952ABD4F63DACCFCCC840950667CC68F7513F8AE72DC7676E94B61FA169158457EA2B8531A593671E79D886743E24EDDF7141E0443E22F1F6B16B0A76D720466E4B8E8 | |||
| (PID) Process: | (3860) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (2040) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | ImagePath |
Value: "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | |||
| (PID) Process: | (2040) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | Description |
Value: KMS-host for all Microsoft VL Products | |||
| (PID) Process: | (2040) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | DisplayName |
Value: KMS-host Service | |||
| (PID) Process: | (6016) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f\2de67392-b7a7-462a-b1ca-108dd189f588 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6016) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
36
Suspicious files
20
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:B22721ECC7249380EF3032685ED19A5A | SHA256:2AC517A3388939951E5BC81489A251193C4BCB4620A9968BA0EC8F34594952D8 | |||
| 7060 | cmd.exe | C:\Users\admin\Desktop\test.test | text | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
| 5896 | wzt.dat | C:\ProgramData\KMSAuto\wzt\wzt.cer | binary | |
MD5:4BF5BFBB3CAF16C6125DF0E10EE60D18 | SHA256:B3DB601B90499D6D5D7CD954CA36A907ABB6AE649B5439AB2BCA93E2E026FE9F | |||
| 6268 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe.aes | binary | |
MD5:A59C42386E14D73EC83CC01A4AF1551B | SHA256:8751A3C6CF2E3A1CD8E9C7B63BB3CBA177476319A67AA766F317151C9CA83AEC | |||
| 2040 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | executable | |
MD5:918C19F788457AC6B7973835BFAFF2EB | SHA256:A756452BC96B77BE8661183425F50ACA3D2658DE7CF9E1F2279EBD905CB2618C | |||
| 6268 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe.aes | binary | |
MD5:61D01B472C1B2FB783AA45A317CC4BC4 | SHA256:CBD17860AF5DD667C9CEBF3FDBD96790B887CFCC7884282A254867D8CFCE9853 | |||
| 6268 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe.aes | binary | |
MD5:DCDB16BB53846BBE61EEBA0887E8D2F0 | SHA256:B85899BB189B43367E5C4172BD345BFEEA45DB3086772C4D3B81DB5C6E63DB6C | |||
| 5896 | wzt.dat | C:\ProgramData\KMSAuto\wzt\certmgr.exe | executable | |
MD5:9D4F1124B2D870583268D19317D564AE | SHA256:EBAD2237B3E7CDF65385CCCE5099E82C7EC5080E737C97CE4E542CDBEA8D418D | |||
| 2040 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\wzt.dat | executable | |
MD5:B41540F62BDE758F2FBB8BD9372CC417 | SHA256:21B5828E9B324690B1AF6352B44C4F668621EE659AB22D525D9AD175F652CB8C | |||
| 2692 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\tap0901.cer | binary | |
MD5:3D5FFD53BE77C32CBB147F32423C0A86 | SHA256:669C56DB590C0308EA25C4508375BB88611B06B1AE689A895DC6B19F4DF5619C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7156 | WmiPrvSE.exe | 20.83.72.98:443 | validation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
validation-v2.sls.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [07/05/2025 21:40.36.439] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [07/05/2025 21:40.36.439] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [07/05/2025 21:40.36.439] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|