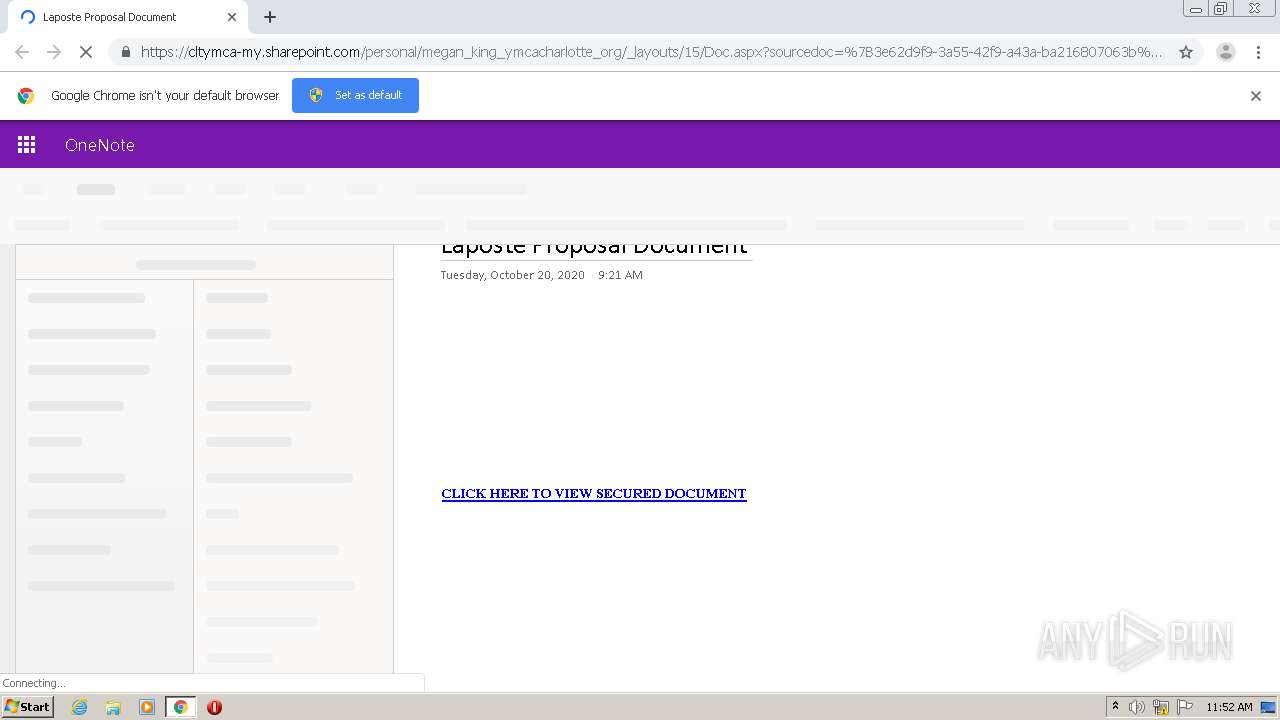
| URL: | http://cltymca-my.sharepoint.com/:o:/g/personal/megan_king_ymcacharlotte_org/EvnZYj5VOvlCpDq6IWgHBjsBzQ7pZTvhAjiYQRtq0CsJZg |
| Full analysis: | https://app.any.run/tasks/8e29280e-2a4a-42c8-8dea-be901be0bd41 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 10:52:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 143D0B48D9EEBE420B52ECDEC38F8B12 |
| SHA1: | 5039BBCBCA0E079A3EA43382B134C4440B227D9F |
| SHA256: | 32F8C9A6096274E1D5C2F11F96EB3ACA16079C17EABB7AFA15A779787B505D9A |
| SSDEEP: | 3:N1KdJRc3iQArL5+KVFSIEL6y6YEPX4NKEIisuoRnb80WmoK:ClcSQAfNKL6iuX4Y0suYnb8zK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2688)
Reads the hosts file
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2688)
Reads settings of System Certificates
- chrome.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16159536773426805149 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14691896244018989295 --mojo-platform-channel-handle=916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5342883275827663278 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15928806898072533874 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15906723605730538465 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2740 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13786892049585917843 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13252538860193826839 --mojo-platform-channel-handle=3724 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9491551829394184423 --mojo-platform-channel-handle=4104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://cltymca-my.sharepoint.com/:o:/g/personal/megan_king_ymcacharlotte_org/EvnZYj5VOvlCpDq6IWgHBjsBzQ7pZTvhAjiYQRtq0CsJZg" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
825
Read events
744
Write events
77
Delete events
4
Modification events
| (PID) Process: | (2128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2688-13247664740336500 |
Value: 259 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2688-13247664740336500 |
Value: 259 | |||
Executable files
0
Suspicious files
104
Text files
90
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EC164-A80.pma | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d3e85.TMP | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b165a834-b712-4fe4-a6fb-58aebb458f14.tmp | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d3e46.TMP | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
85
DNS requests
43
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
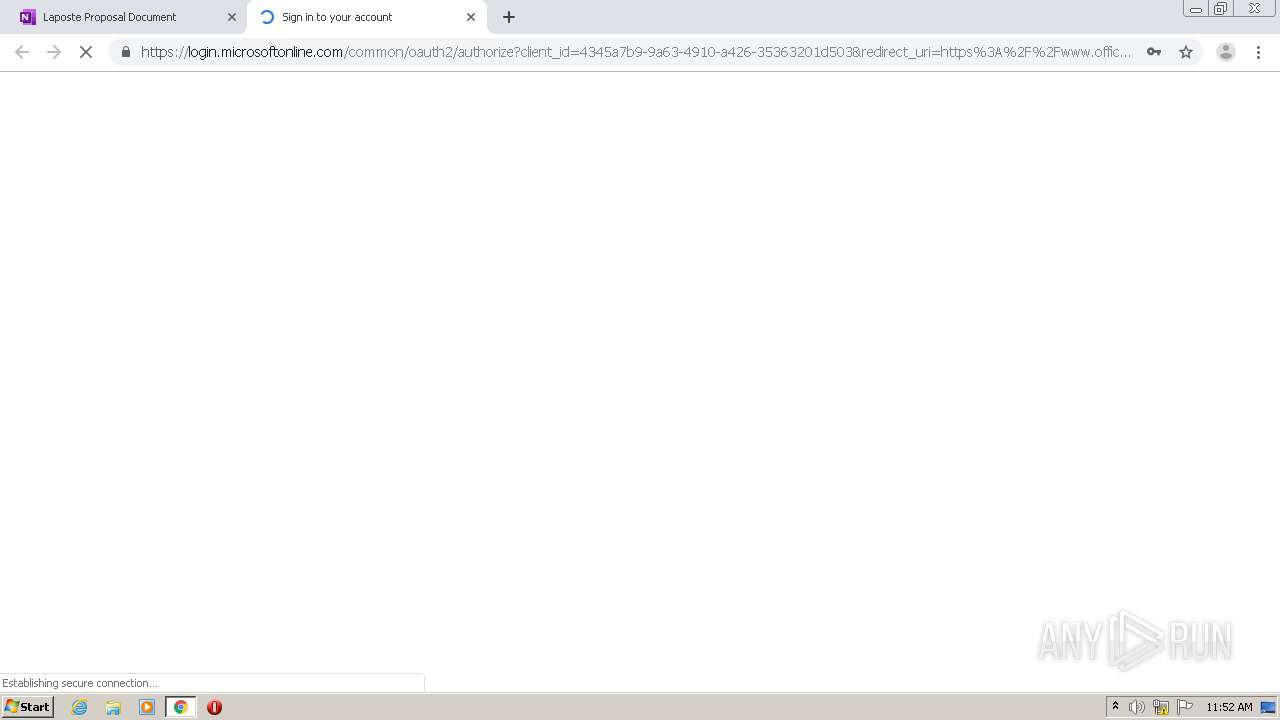
3496 | chrome.exe | GET | 301 | 13.107.136.9:80 | http://cltymca-my.sharepoint.com/:o:/g/personal/megan_king_ymcacharlotte_org/EvnZYj5VOvlCpDq6IWgHBjsBzQ7pZTvhAjiYQRtq0CsJZg | US | — | — | suspicious |
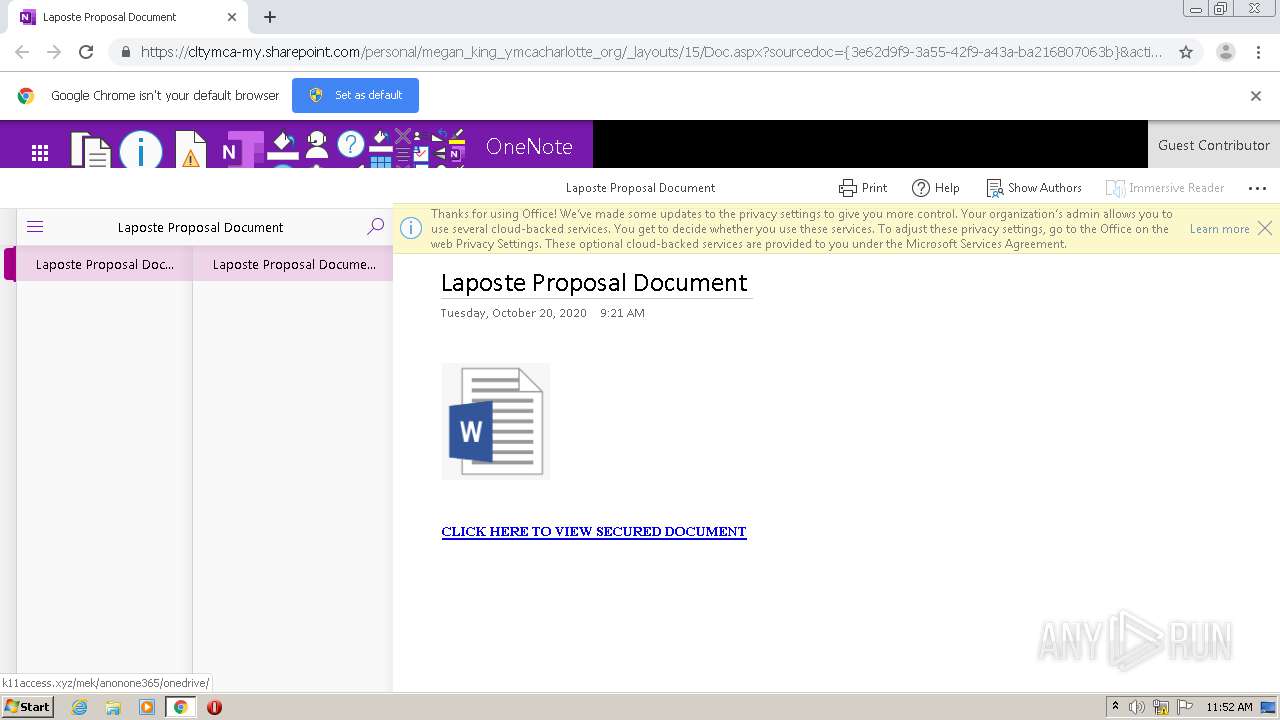
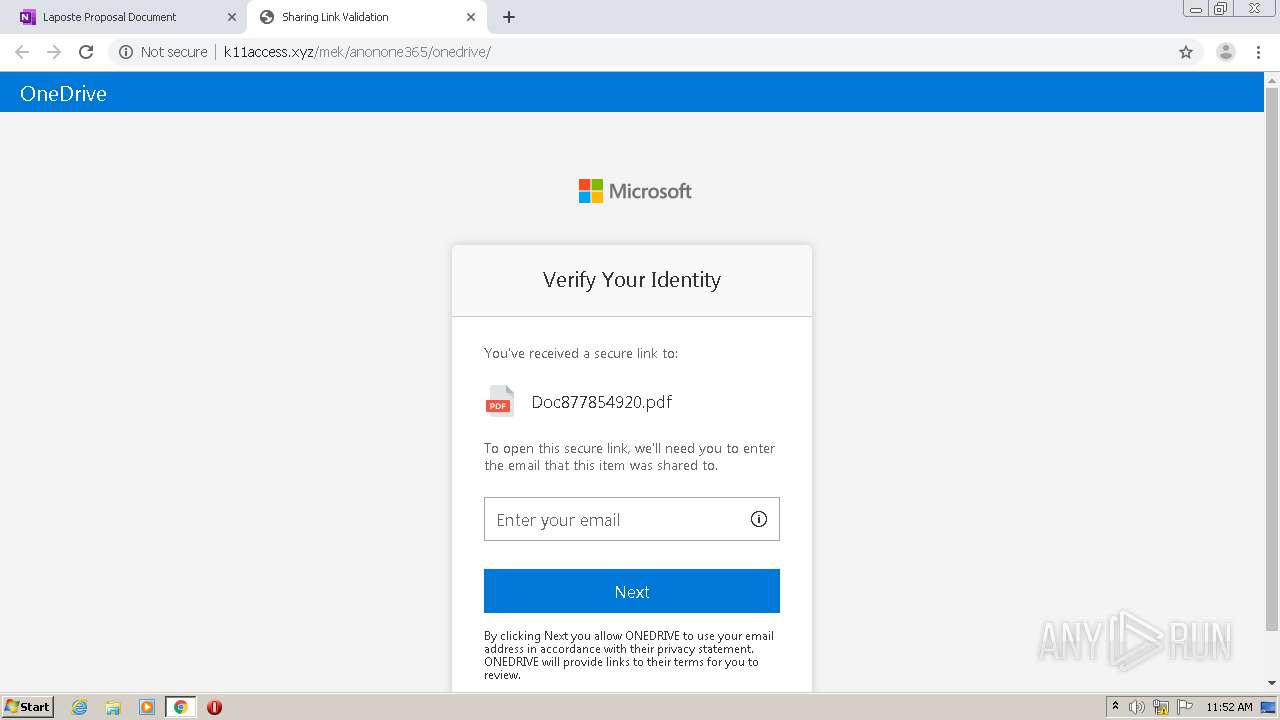
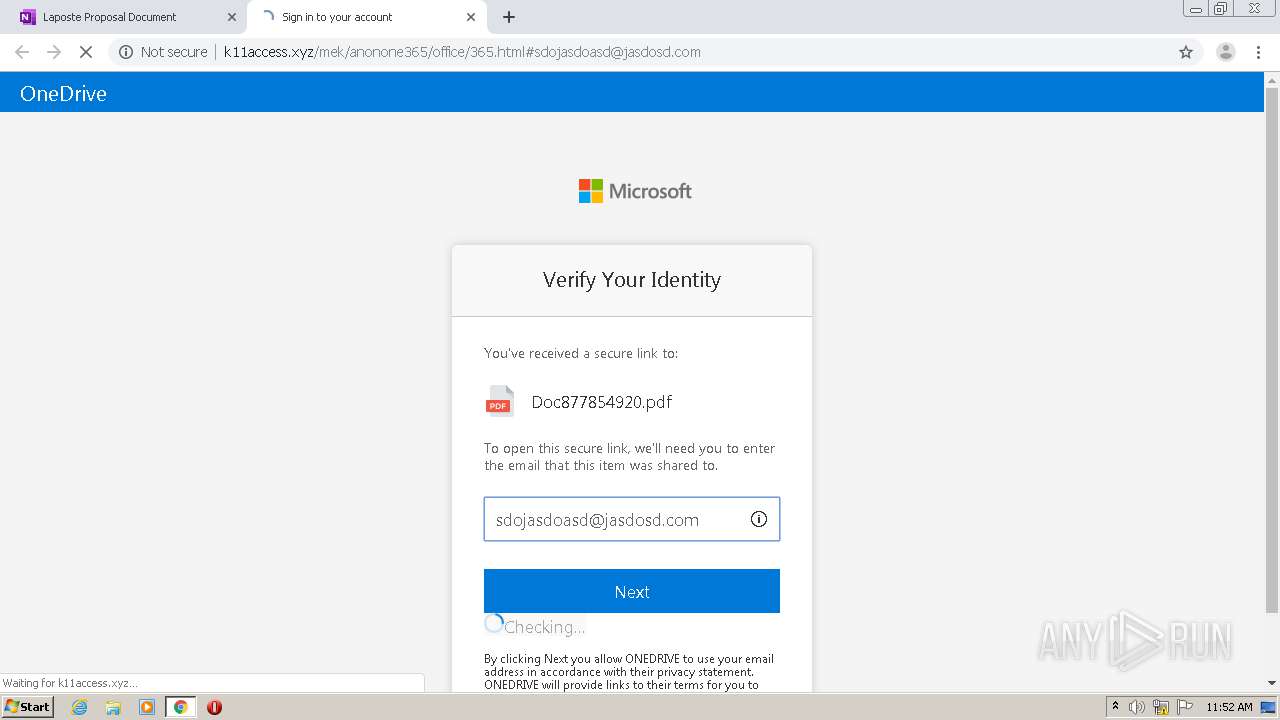
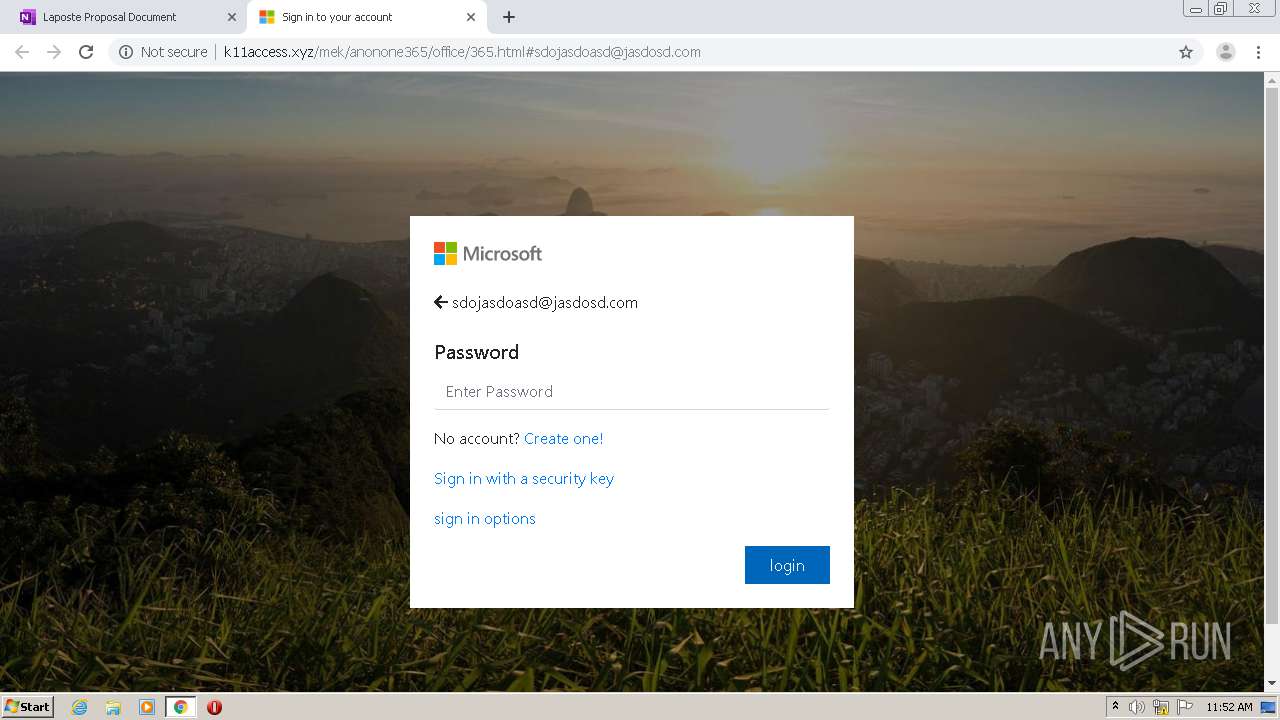
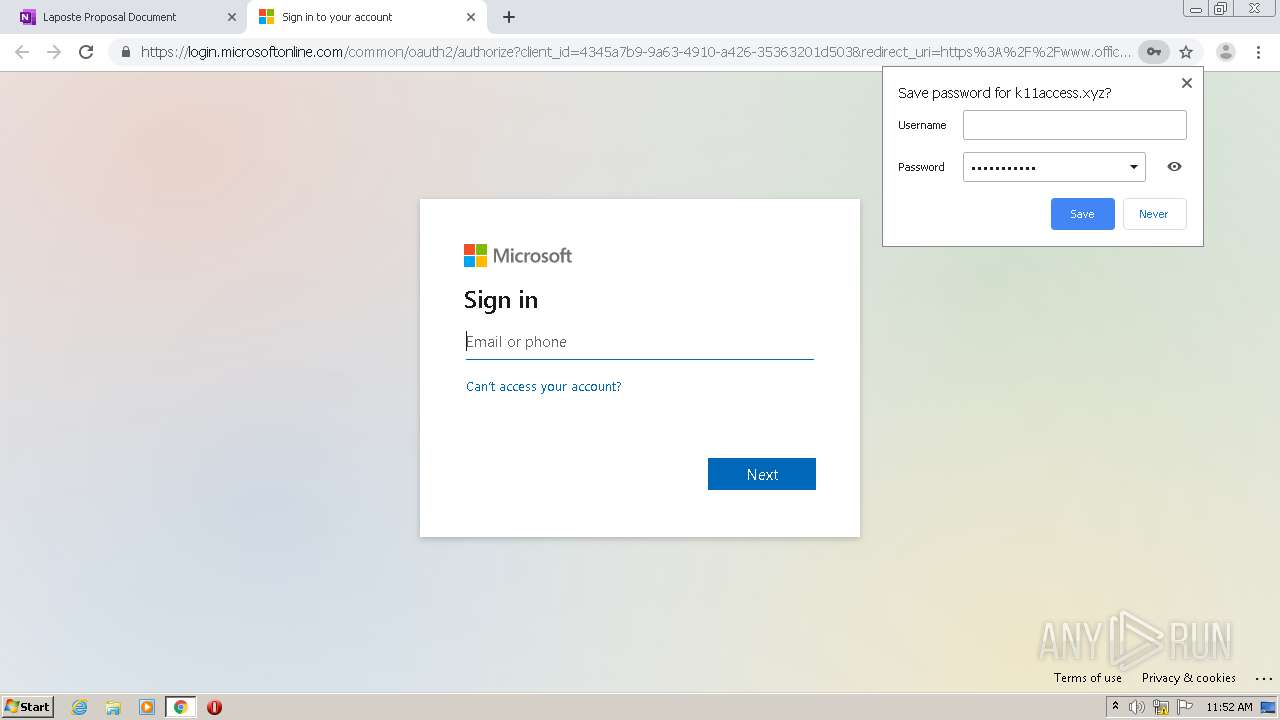
3496 | chrome.exe | GET | 200 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/office/365.html | CA | html | 167 Kb | suspicious |
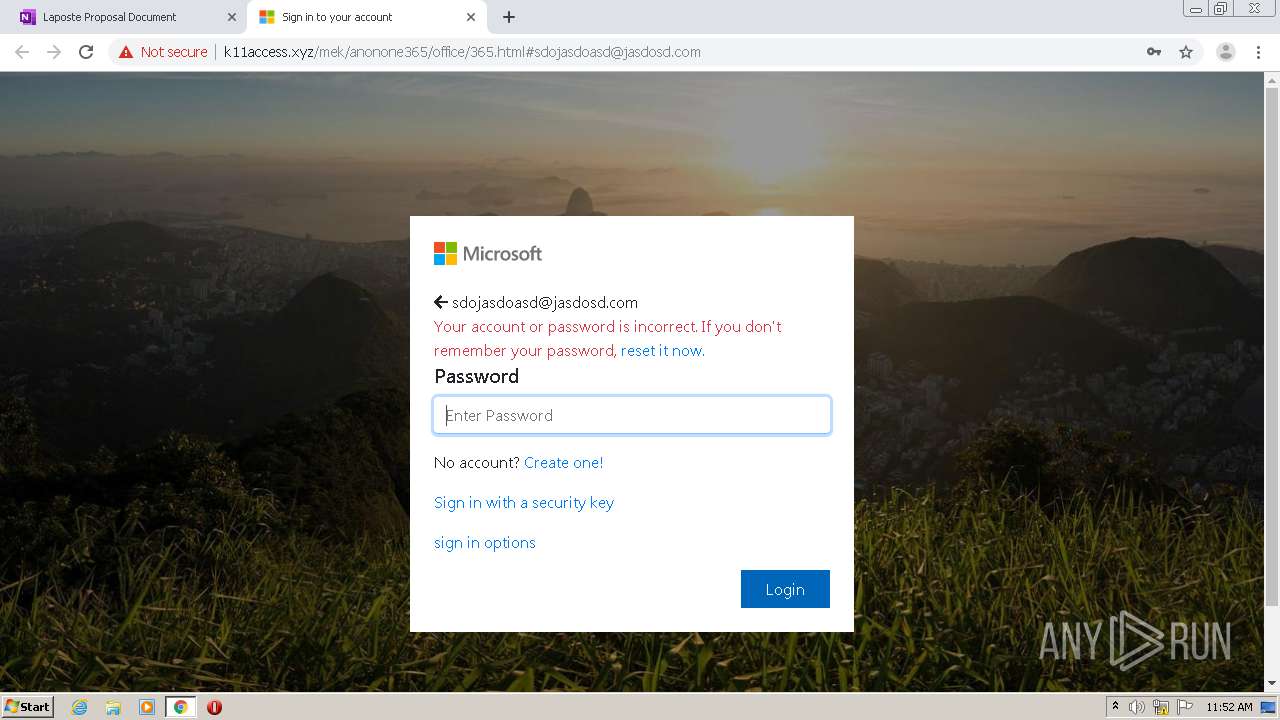
3496 | chrome.exe | POST | 200 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/office/submit.php | CA | html | 131 b | suspicious |
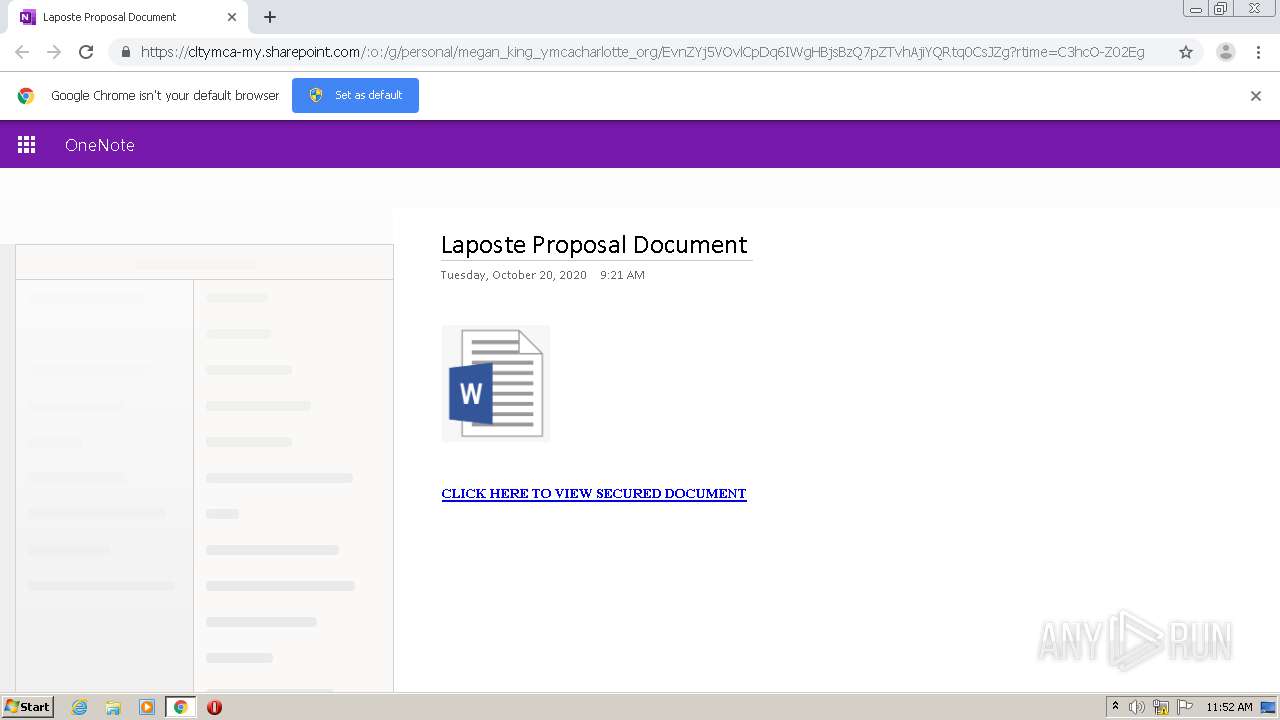
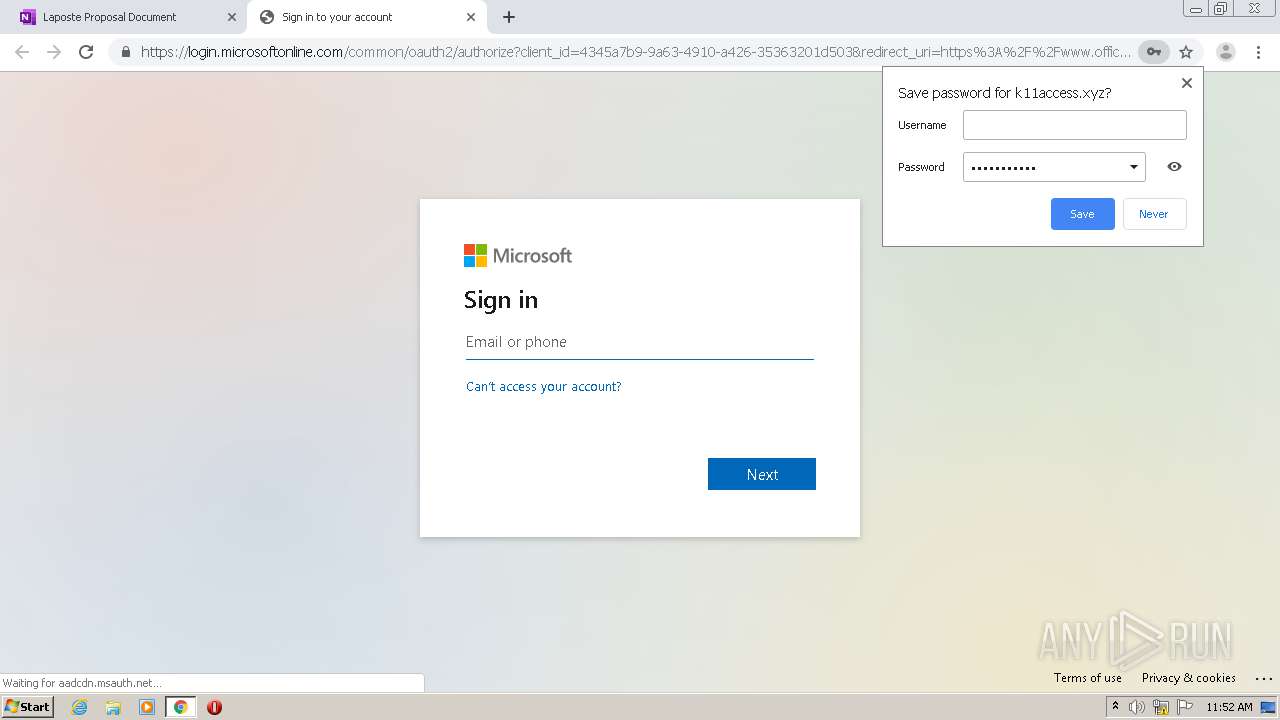
3496 | chrome.exe | GET | 200 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/onedrive/ | CA | html | 7.91 Kb | suspicious |
3496 | chrome.exe | POST | 200 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/office/submit.php | CA | html | 131 b | suspicious |
3496 | chrome.exe | GET | 200 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/onedrive/files/mssoft.png | CA | image | 2.16 Kb | suspicious |
3496 | chrome.exe | GET | 404 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/onedrive/images/favicon.ico | CA | html | 315 b | suspicious |
3496 | chrome.exe | GET | 200 | 162.0.235.49:80 | http://k11access.xyz/mek/anonone365/onedrive/files/pdf.png | CA | image | 7.99 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3496 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3496 | chrome.exe | 13.107.136.9:80 | cltymca-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
3496 | chrome.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
3496 | chrome.exe | 13.107.136.9:443 | cltymca-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
3496 | chrome.exe | 104.111.249.245:443 | c1-onenote-15.cdn.office.net | Akamai International B.V. | NL | unknown |
3496 | chrome.exe | 52.108.79.17:443 | usc-onenote.officeapps.live.com | Microsoft Corporation | US | unknown |
3496 | chrome.exe | 52.109.88.115:443 | onenoteonlinesync.onenote.com | Microsoft Corporation | NL | unknown |
3496 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3496 | chrome.exe | 104.111.214.95:443 | fs.microsoft.com | Akamai International B.V. | NL | whitelisted |
3496 | chrome.exe | 52.114.159.112:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
cltymca-my.sharepoint.com |
| suspicious |
accounts.google.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
c1-onenote-15.cdn.office.net |
| whitelisted |
c1-officeapps-15.cdn.office.net |
| whitelisted |
usc-onenote.officeapps.live.com |
| whitelisted |
onenoteonlinesync.onenote.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3496 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2 ETPRO signatures available at the full report