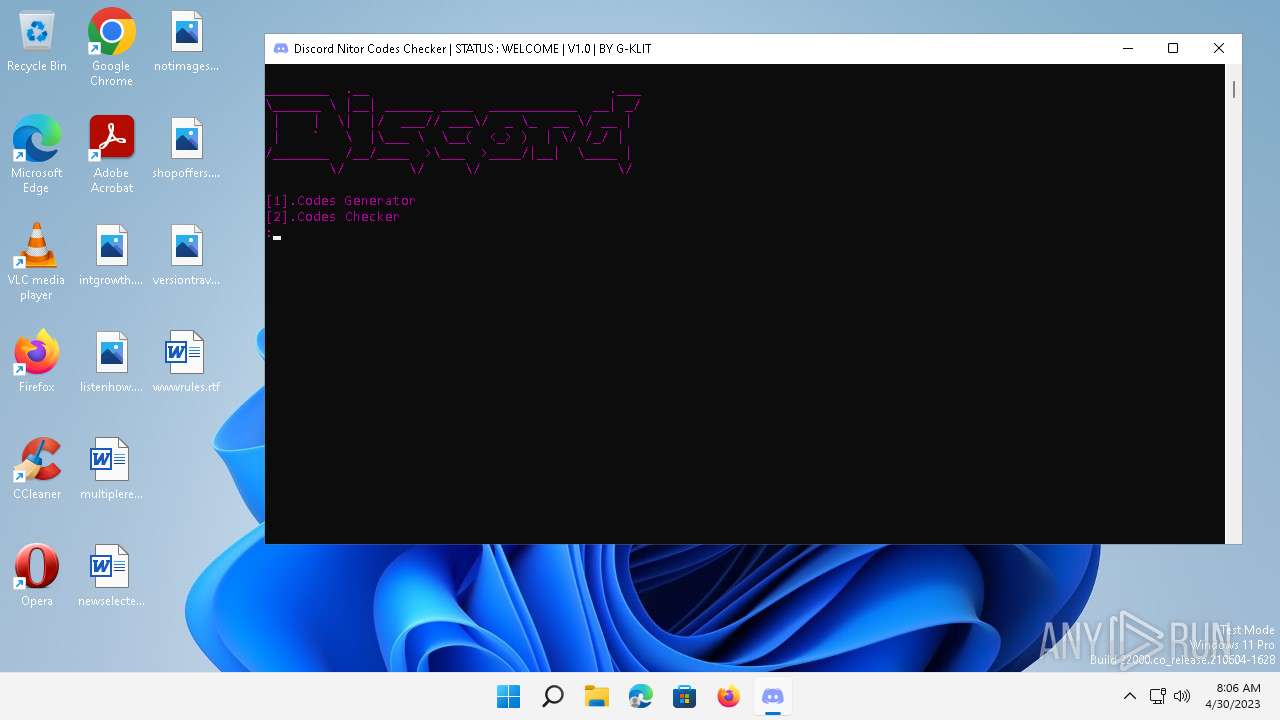
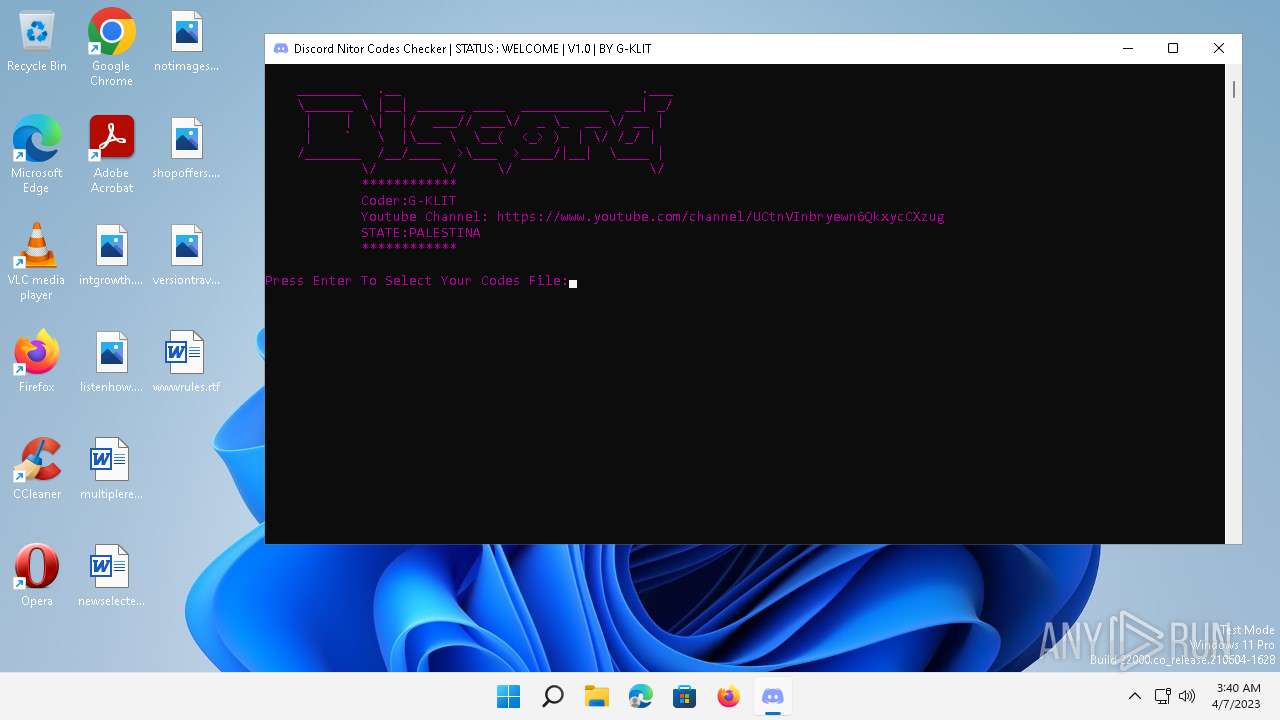
| File name: | Discord Nitro Gift Codes Checker By G-KLIT.exe |
| Full analysis: | https://app.any.run/tasks/dfd60f90-58ad-4a81-9372-e3a219be7921 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2023, 15:06:04 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 2CA4BAE5697C9BBB0DA41E4D0D5603CC |
| SHA1: | 24FF7967EF6F419A562B8F78A5F75555261FCF55 |
| SHA256: | 32F85AF353D33125CEEB6FAC3B99DE3F46666BE6DC2E6C4938E2679CD4AE341E |
| SSDEEP: | 196608:fvmHiAor3TDpYpmeuPF8yh431CQeUpg176GtbYPvbJQlHqLG8CiNcFicMI2DNX:ZfTySFvYcVMg1OGkJQlKLk4cMD |
MALICIOUS
No malicious indicators.SUSPICIOUS
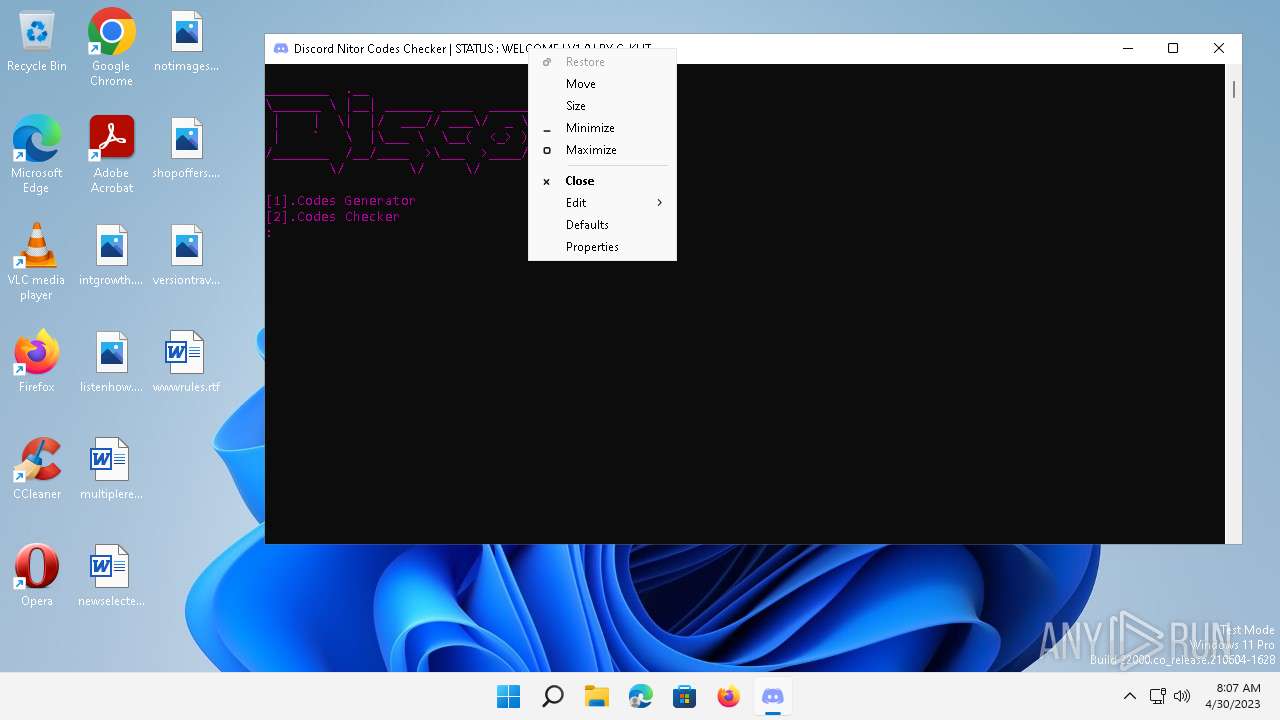
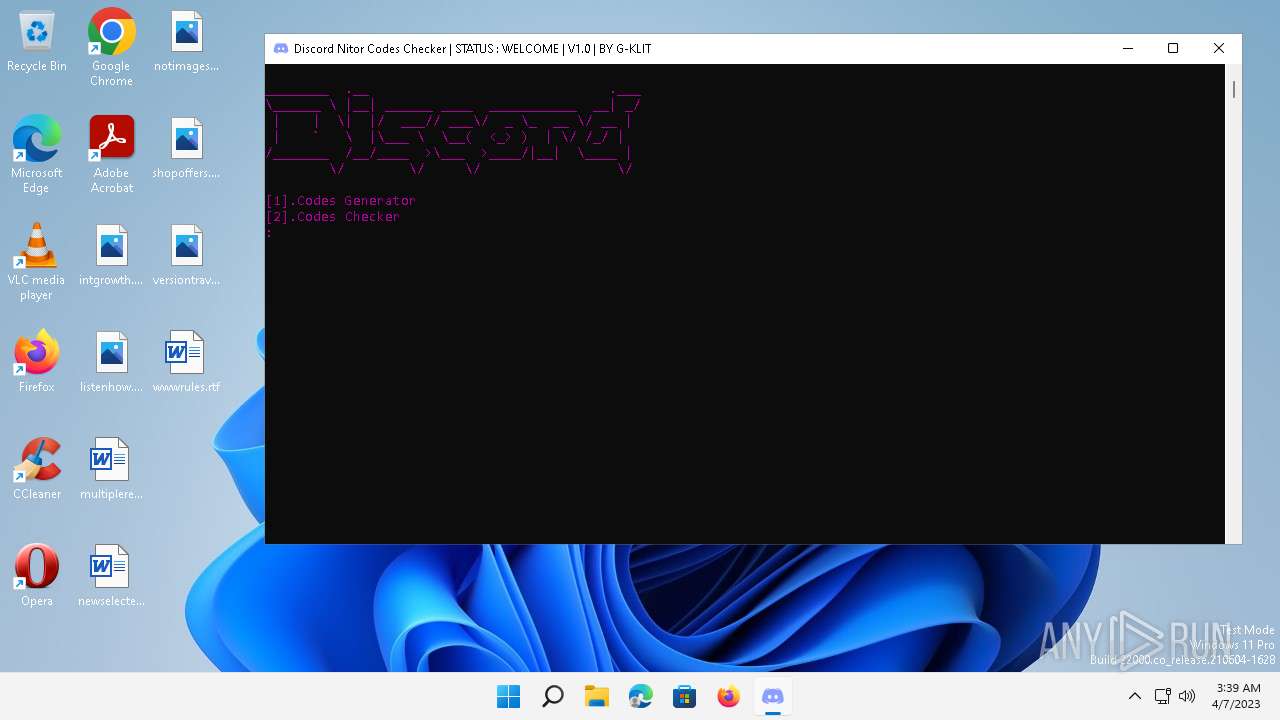
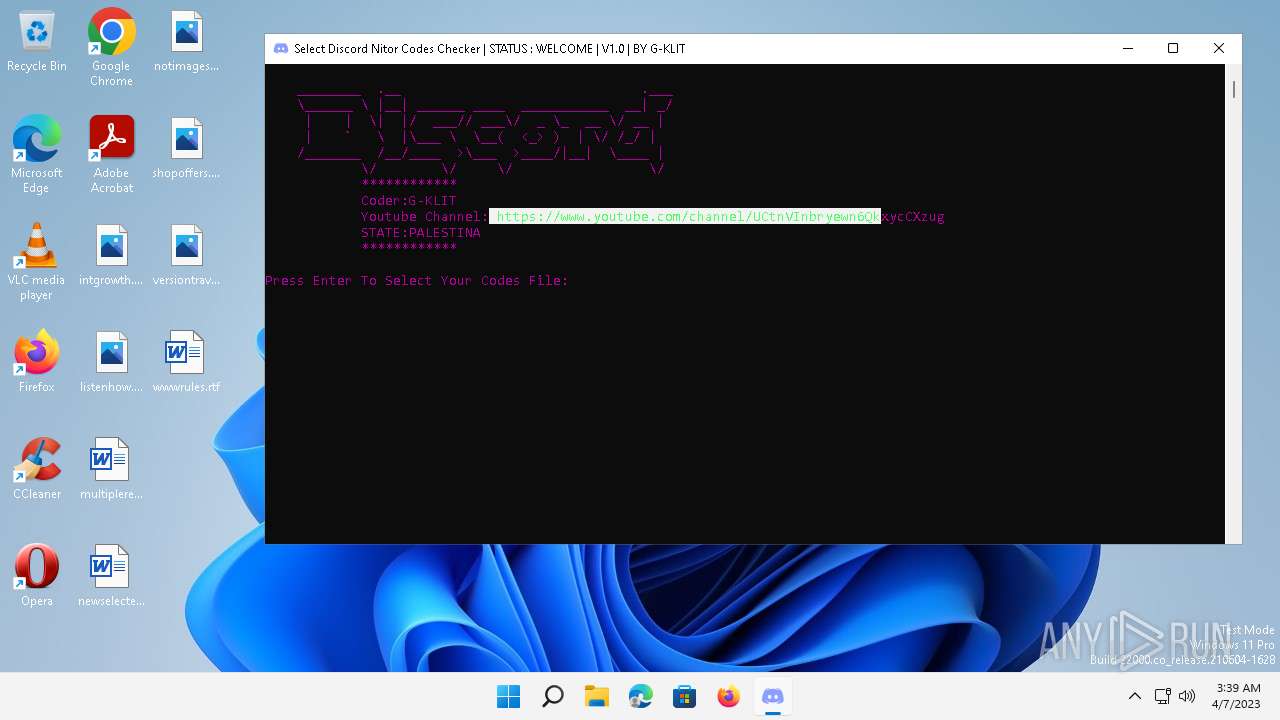
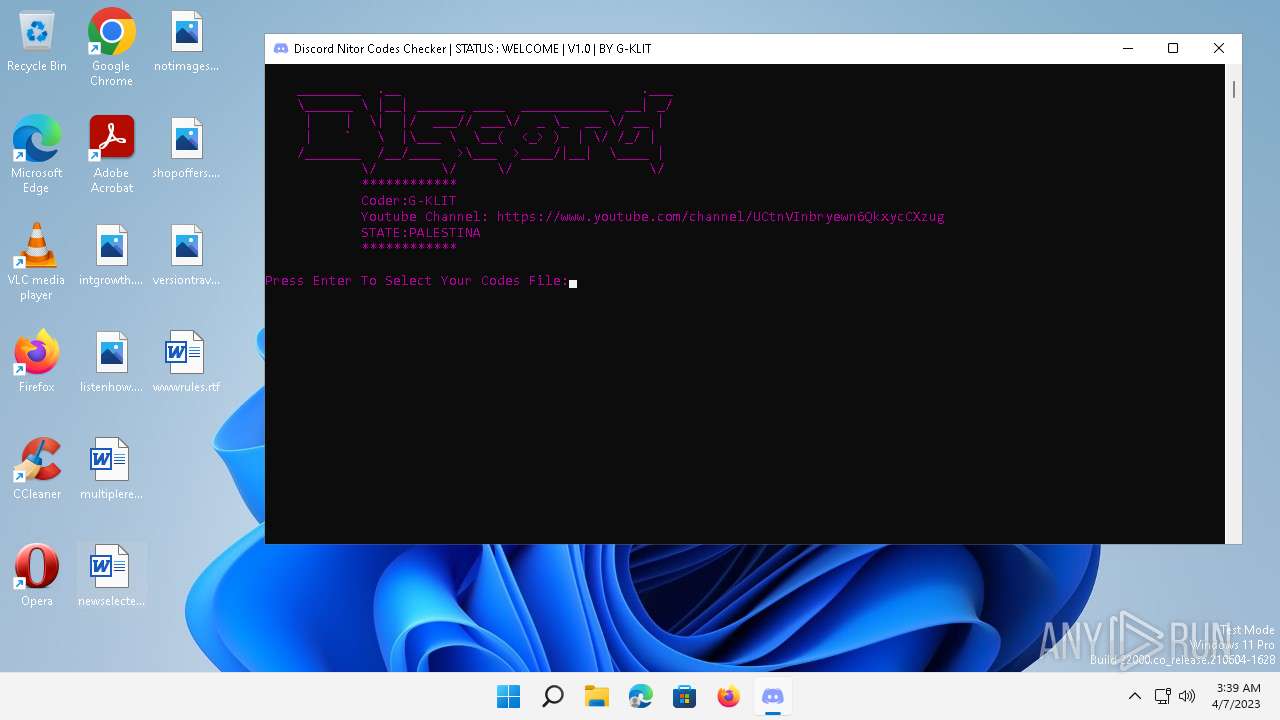
Application launched itself
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 6360)
Loads Python modules
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
Executable content was dropped or overwritten
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 6360)
Starts CMD.EXE for commands execution
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
INFO
The process checks LSA protection
- conhost.exe (PID: 2988)
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
Checks supported languages
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 6360)
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
Reads the machine GUID from the registry
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
Reads the computer name
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
Create files in a temporary directory
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 880)
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 6360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x790a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 219136 |
| CodeSize: | 128000 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| TimeStamp: | 2019:07:09 14:22:19+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jul-2019 14:22:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:22:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F3B4 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66635 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10031 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86637 |
.rsrc | 0x0003D000 | 0x0001A376 | 0x0001A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.6715 |
.reloc | 0x00058000 | 0x000017D0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.86138 | 7299 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 1.88072 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.06834 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.20199 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.3577 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.67095 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
130
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | "C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe" | C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe | — | Discord Nitro Gift Codes Checker By G-KLIT.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2988 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Discord Nitro Gift Codes Checker By G-KLIT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3308 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\SysWOW64\cmd.exe | — | Discord Nitro Gift Codes Checker By G-KLIT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6360 | "C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe" | C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6680 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\SysWOW64\cmd.exe | — | Discord Nitro Gift Codes Checker By G-KLIT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
920
Read events
920
Write events
0
Delete events
0
Modification events
Executable files
48
Suspicious files
6
Text files
1 846
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_ctypes.pyd | executable | |
MD5:9DB2D9962CBD754E91B40F91CBC49542 | SHA256:6A6DF7D77B7A5552D8443BD1B98F681AD2E6B5A8ACF7ADE542DD369BEAB7E439 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_hashlib.pyd | executable | |
MD5:E84E1BA269371E439C2D52024ACA6535 | SHA256:2FCB297733E6080480AC24CF073FF5E239FB02A1CE9694313C5047F9C58D781B | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_cffi_backend.cp37-win32.pyd | executable | |
MD5:9C57FA6BD22B8DCA861E767384E428E4 | SHA256:2DBA673A4701D68FB85054F64A22C4C249C4FB8C7BA0B8CAE8383BBCC9F8D762 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_tkinter.pyd | executable | |
MD5:E46970E8EB0061DF01347A3723140E77 | SHA256:71C4545CEE713F26CF2F910A08340DD519C4713B8416479F74B0B9E2683C85D5 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_queue.pyd | executable | |
MD5:8807DC228BB761439DC6525A2966E27E | SHA256:B7ED6DFB6882E8EC4267D9F80CD5B1DC0A43519382FCB72AB5E74C47875C209D | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\Discord.exe.manifest | xml | |
MD5:C70E9748DD5C4686AE9E3864D083366F | SHA256:FEF6F04896F0099D64A2A2EE5582FA6FB24A91FD5350E26EC989719EE28058B6 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_bz2.pyd | executable | |
MD5:FF5AC8FB724EDB1635E2AD985F98EE5B | SHA256:B94F64FCB49F40682ED794FA1940A1DC0C8A28F24A1768D3BFE774CF75F59B62 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\cryptography\hazmat\bindings\_openssl.cp37-win32.pyd | executable | |
MD5:6060B0D2596BFBEC7C2E3C16D5237686 | SHA256:0B192A88494F19C5D099C2F7937534830DDDDE40745C30A0B1A0F24A96A2AA04 | |||
| 6360 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI63602\_multiprocessing.pyd | executable | |
MD5:42A5EC2E2EC56DCA18E7221C1858A7DE | SHA256:C22D475ADA5E8D7EA37124892B4A3D8315E6E66594A2237DCB0BBDF160B053DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
37
DNS requests
49
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | svchost.exe | GET | 304 | 8.248.147.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e3d87e03e02a0d69 | US | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://crl4.digicert.com/DigiCertGlobalRootCA.crl | US | binary | 779 b | whitelisted |
1480 | svchost.exe | GET | 200 | 13.107.4.52:80 | http://www.msftconnecttest.com/connecttest.txt | US | text | 22 b | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | binary | 242 Kb | whitelisted |
— | — | GET | 304 | 8.248.117.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4c9e687b8c32f98b | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1480 | svchost.exe | 13.107.4.52:80 | www.msftconnecttest.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 8.248.117.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | malicious |
— | — | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | suspicious |
— | — | 142.250.184.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.46:443 | clients2.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
— | — | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
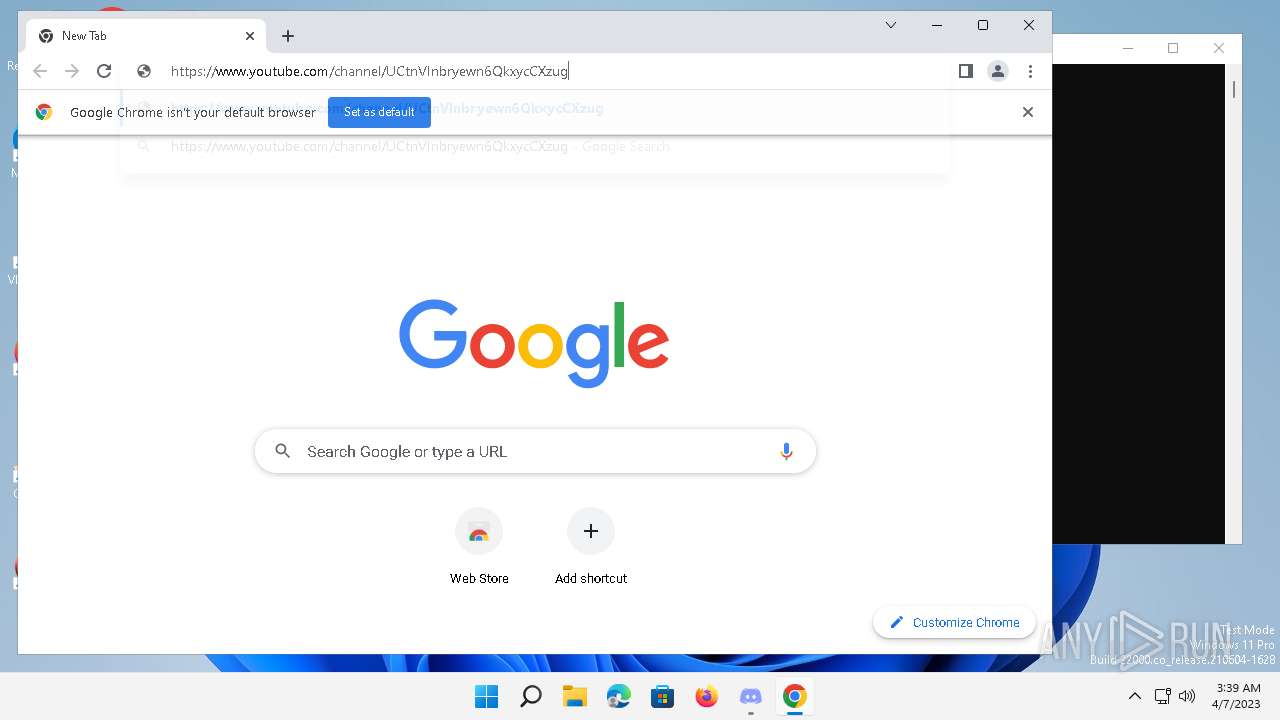
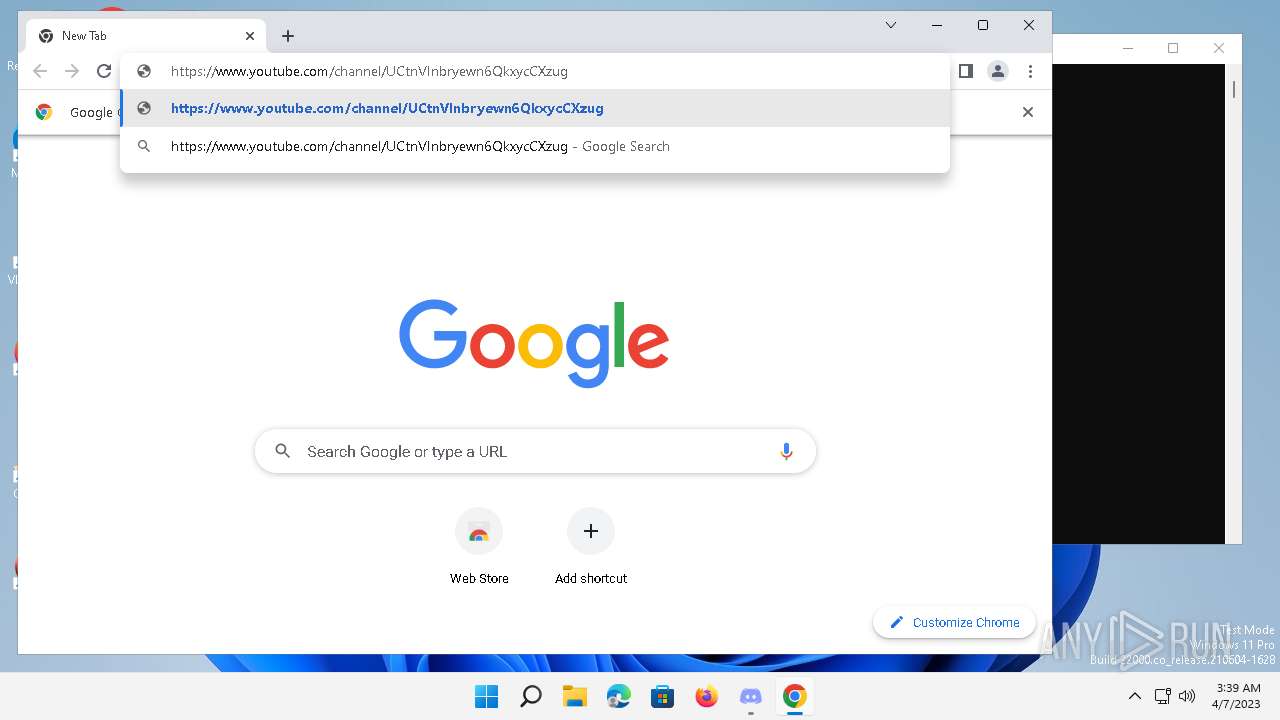
— | — | 142.250.186.142:443 | www.youtube.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
time.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1480 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |