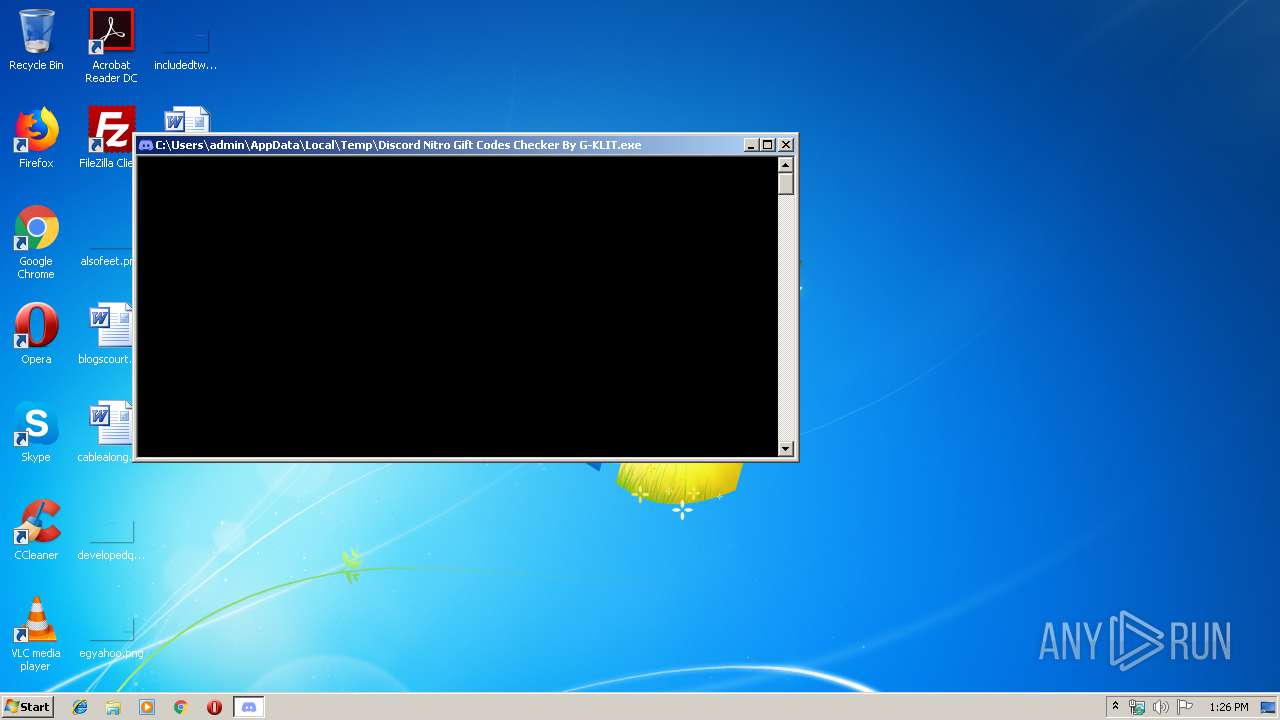
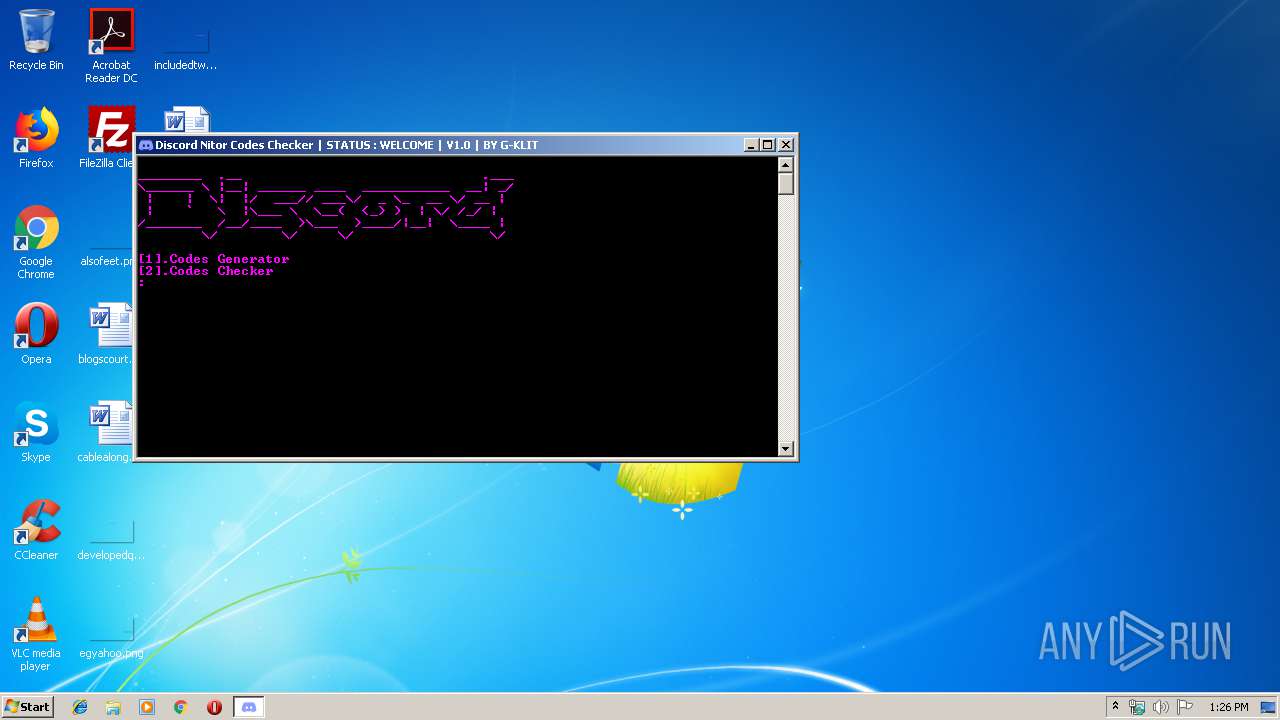
| File name: | Discord Nitro Gift Codes Checker By G-KLIT.exe |
| Full analysis: | https://app.any.run/tasks/9bb0f0b1-5465-4a7b-a1df-8ff7ac4b5163 |
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2019, 13:26:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 2CA4BAE5697C9BBB0DA41E4D0D5603CC |
| SHA1: | 24FF7967EF6F419A562B8F78A5F75555261FCF55 |
| SHA256: | 32F85AF353D33125CEEB6FAC3B99DE3F46666BE6DC2E6C4938E2679CD4AE341E |
| SSDEEP: | 196608:fvmHiAor3TDpYpmeuPF8yh431CQeUpg176GtbYPvbJQlHqLG8CiNcFicMI2DNX:ZfTySFvYcVMg1OGkJQlKLk4cMD |
MALICIOUS
Loads dropped or rewritten executable
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 3976)
SUSPICIOUS
Loads Python modules
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 3976)
Application launched itself
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 2496)
Executable content was dropped or overwritten
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 2496)
INFO
Dropped object may contain Bitcoin addresses
- Discord Nitro Gift Codes Checker By G-KLIT.exe (PID: 2496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:09 16:22:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 219136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x790a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jul-2019 14:22:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:22:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F3B4 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66635 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10031 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86637 |
.rsrc | 0x0003D000 | 0x0001A376 | 0x0001A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.6715 |
.reloc | 0x00058000 | 0x000017D0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.86138 | 7299 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 1.88072 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.06834 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.20199 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.3577 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.67095 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2496 | "C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe" | C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe" | C:\Users\admin\AppData\Local\Temp\Discord Nitro Gift Codes Checker By G-KLIT.exe | — | Discord Nitro Gift Codes Checker By G-KLIT.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3
Read events
3
Write events
0
Delete events
0
Modification events
Executable files
24
Suspicious files
1
Text files
922
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\_bz2.pyd | executable | |
MD5:FF5AC8FB724EDB1635E2AD985F98EE5B | SHA256:B94F64FCB49F40682ED794FA1940A1DC0C8A28F24A1768D3BFE774CF75F59B62 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\Discord.exe.manifest | xml | |
MD5:C70E9748DD5C4686AE9E3864D083366F | SHA256:FEF6F04896F0099D64A2A2EE5582FA6FB24A91FD5350E26EC989719EE28058B6 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\libssl-1_1.dll | executable | |
MD5:5ADB49CC84ABD6D3C8F959CA5A146AD7 | SHA256:F4D5DF50BDF3E7304C67C81ACE83263C8D0F0E28087C6104C21150BFEDA86B8D | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\_cffi_backend.cp37-win32.pyd | executable | |
MD5:9C57FA6BD22B8DCA861E767384E428E4 | SHA256:2DBA673A4701D68FB85054F64A22C4C249C4FB8C7BA0B8CAE8383BBCC9F8D762 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\cryptography\hazmat\bindings\_constant_time.cp37-win32.pyd | executable | |
MD5:F217E40FD967C5DA98C27EEBA10711D6 | SHA256:D86E08F86E1095BBFEE98E1816D489D0A7F57B9CDD3BE0AE2FAE10F40E9BDDB6 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\_ssl.pyd | executable | |
MD5:CC5C8EB32ACB2261C42A7285D436CCA9 | SHA256:07EA50E536886F68473635FFEFCFCAA7266E63C478EF039BA100DDF02F88CE61 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\_tkinter.pyd | executable | |
MD5:E46970E8EB0061DF01347A3723140E77 | SHA256:71C4545CEE713F26CF2F910A08340DD519C4713B8416479F74B0B9E2683C85D5 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\lxml\_elementpath.cp37-win32.pyd | executable | |
MD5:D250D9FC72ECB0485BB95E72E18E7603 | SHA256:19129CAE206DE6155CD7355A9790181A2FDE5B09FE5B1C51F7186E3156C942C6 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\pyexpat.pyd | executable | |
MD5:F4AC522E0A04829BBA2B8FCA878F560E | SHA256:87A1D8B94668C55AC0B67E05A9505031E38510CFD2A47979697C05B7C7B375A2 | |||
| 2496 | Discord Nitro Gift Codes Checker By G-KLIT.exe | C:\Users\admin\AppData\Local\Temp\_MEI24962\_queue.pyd | executable | |
MD5:8807DC228BB761439DC6525A2966E27E | SHA256:B7ED6DFB6882E8EC4267D9F80CD5B1DC0A43519382FCB72AB5E74C47875C209D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report