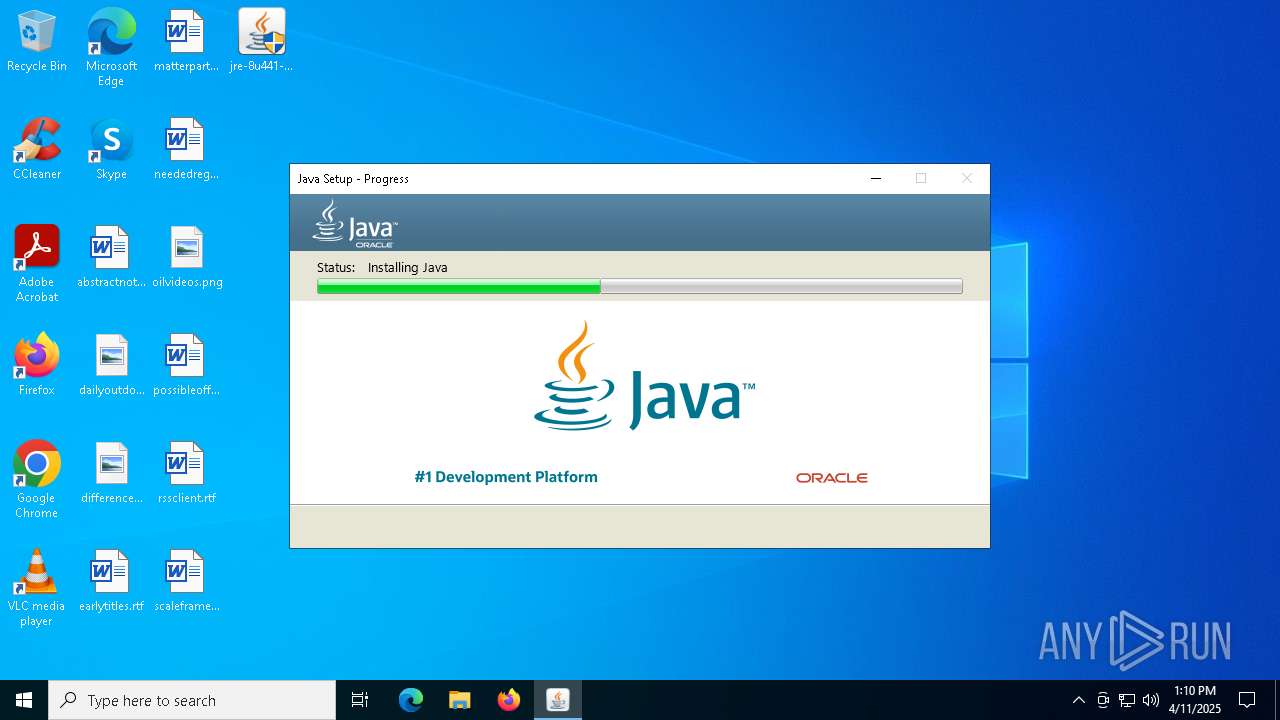
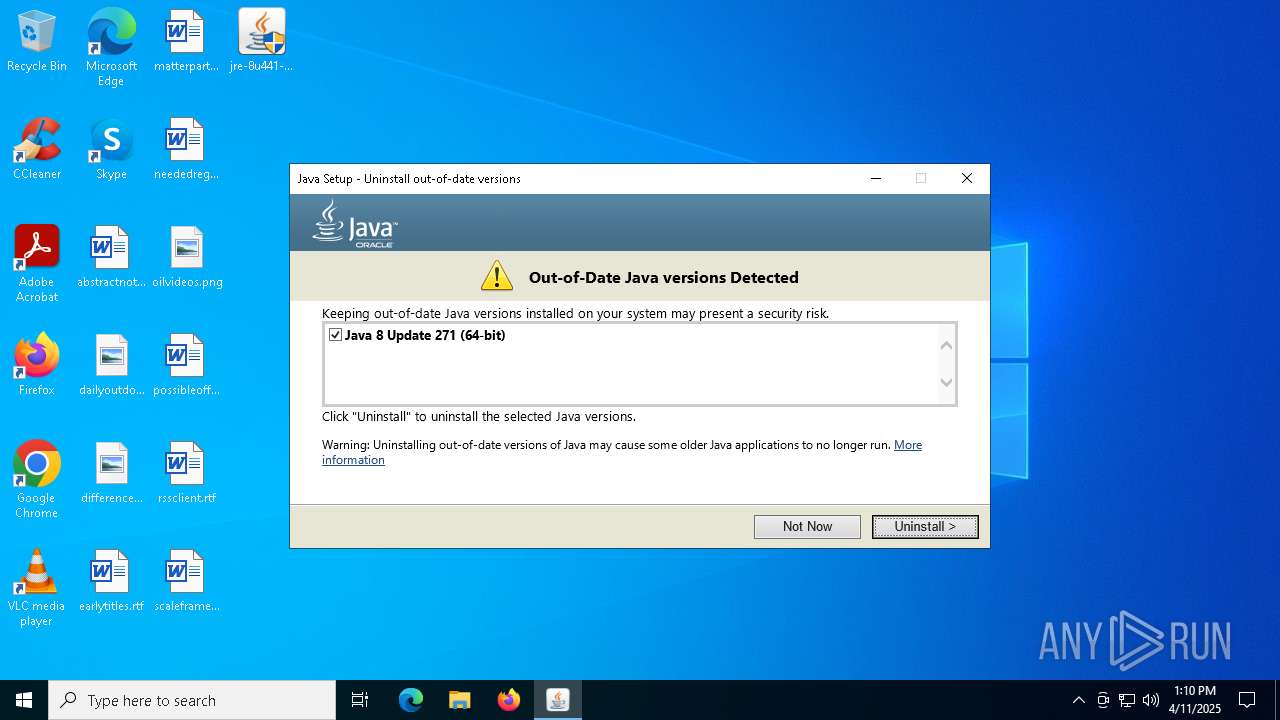
| File name: | jre-8u441-windows-i586-iftw.exe |
| Full analysis: | https://app.any.run/tasks/63a63052-7a23-4cfe-97f6-f71f98259874 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 13:09:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | E0D3BAA99BBB61108D75EE30EA614D6F |
| SHA1: | 7B32110EC4F8F23237F98A57F804A24E1EF0B262 |
| SHA256: | 32EB651FB600C4A008E0B2B66488E15F459AE1741B3D5835697F5D8471F779C4 |
| SSDEEP: | 98304:UElcske/5ZB35TYwmwJUaOqP7R/hTwMqfZeW3nTZ8aj3:w |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- jre-8u441-windows-i586-iftw.exe (PID: 7520)
- LZMA_EXE (PID: 8172)
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- installer.exe (PID: 5968)
Checks for Java to be installed
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- installer.exe (PID: 5968)
- msiexec.exe (PID: 3304)
- ssvagent.exe (PID: 6724)
- jp2launcher.exe (PID: 7996)
- msiexec.exe (PID: 5244)
- jp2launcher.exe (PID: 7656)
- msiexec.exe (PID: 6592)
Reads security settings of Internet Explorer
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- installer.exe (PID: 5968)
- jp2launcher.exe (PID: 7656)
- jp2launcher.exe (PID: 7996)
Reads Microsoft Outlook installation path
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
Starts application with an unusual extension
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
Reads Internet Explorer settings
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
Process drops legitimate windows executable
- msiexec.exe (PID: 3304)
The process drops C-runtime libraries
- msiexec.exe (PID: 3304)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3304)
Creates/Modifies COM task schedule object
- installer.exe (PID: 5968)
- ssvagent.exe (PID: 6724)
INFO
The sample compiled with english language support
- jre-8u441-windows-i586-iftw.exe (PID: 7520)
- LZMA_EXE (PID: 8172)
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- msiexec.exe (PID: 3304)
- installer.exe (PID: 5968)
Java executable
- jre-8u441-windows-i586-iftw.exe (PID: 7404)
- jre-8u441-windows-i586-iftw.exe (PID: 7520)
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- installer.exe (PID: 5968)
Create files in a temporary directory
- jre-8u441-windows-i586-iftw.exe (PID: 7520)
- javaw.exe (PID: 6132)
- installer.exe (PID: 5968)
- jp2launcher.exe (PID: 7656)
Checks supported languages
- jre-8u441-windows-i586-iftw.exe (PID: 7520)
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- LZMA_EXE (PID: 8172)
- LZMA_EXE (PID: 6668)
- installer.exe (PID: 5968)
- javaw.exe (PID: 6132)
- msiexec.exe (PID: 3304)
- msiexec.exe (PID: 5892)
- ssvagent.exe (PID: 6724)
- javaws.exe (PID: 7652)
- jp2launcher.exe (PID: 7656)
- jp2launcher.exe (PID: 7996)
- msiexec.exe (PID: 5244)
- msiexec.exe (PID: 5400)
- javaws.exe (PID: 7992)
- msiexec.exe (PID: 5408)
- javaw.exe (PID: 7612)
- msiexec.exe (PID: 6592)
Reads the machine GUID from the registry
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- msiexec.exe (PID: 3304)
Reads the computer name
- jre-8u441-windows-i586-iftw.exe (PID: 7520)
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- msiexec.exe (PID: 5892)
- msiexec.exe (PID: 3304)
- installer.exe (PID: 5968)
- javaws.exe (PID: 7652)
- msiexec.exe (PID: 5400)
- jp2launcher.exe (PID: 7656)
- javaws.exe (PID: 7992)
- msiexec.exe (PID: 5244)
- msiexec.exe (PID: 6592)
- msiexec.exe (PID: 5408)
- javaw.exe (PID: 7612)
Creates files or folders in the user directory
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- LZMA_EXE (PID: 8172)
- LZMA_EXE (PID: 6668)
Checks proxy server information
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
Reads the software policy settings
- jre-8u441-windows-i586-iftw.exe (PID: 7540)
- msiexec.exe (PID: 3304)
Reads CPU info
- msiexec.exe (PID: 3304)
Creates a software uninstall entry
- msiexec.exe (PID: 3304)
Creates files in the program directory
- javaw.exe (PID: 6132)
- installer.exe (PID: 5968)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3304)
Local mutex for internet shortcut management
- installer.exe (PID: 5968)
JAVA mutex has been found
- jp2launcher.exe (PID: 7996)
- jp2launcher.exe (PID: 7656)
- msiexec.exe (PID: 8140)
- msiexec.exe (PID: 5400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:04 08:53:22+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.36 |
| CodeSize: | 200192 |
| InitializedDataSize: | 2157568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1046b |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.4410.7 |
| ProductVersionNumber: | 8.0.4410.7 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Oracle Corporation |
| FileDescription: | Java Platform SE binary |
| FileVersion: | 8.0.4410.7 |
| FullVersion: | 1.8.0_441-b07 |
| InternalName: | Setup Launcher |
| LegalCopyright: | Copyright © 2025 |
| OriginalFileName: | online_wrapper-iftw.exe |
| ProductName: | Java Platform SE 8 U441 |
| ProductVersion: | 8.0.4410.7 |
Total processes
153
Monitored processes
24
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3304 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3956 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | LZMA_EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | C:\Windows\syswow64\MsiExec.exe -Embedding D90025EDF903E6206A40C076AAF46F86 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | C:\Windows\syswow64\MsiExec.exe -Embedding 8D3F0F4E9D70CFE8907E9CFE3D344888 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | C:\Windows\syswow64\MsiExec.exe -Embedding EA58B936470A18B4399EA3092AEB1B4A E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | C:\Windows\syswow64\MsiExec.exe -Embedding CAA91586255968CB9A577F09CCDE17B6 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5968 | "C:\Program Files (x86)\Java\jre1.8.0_441\installer.exe" /s INSTALLDIR="C:\Program Files (x86)\Java\jre1.8.0_441\\" INSTALL_SILENT=1 AUTO_UPDATE=0 SPONSORS=0 REPAIRMODE=0 ProductCode={77724AE4-039E-4CA4-87B4-2F32180441F0} | C:\Program Files (x86)\Java\jre1.8.0_441\installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.4410.7 Modules
| |||||||||||||||
| 6132 | "C:\Program Files (x86)\Java\jre1.8.0_441\bin\javaw.exe" -Xshare:dump -Djdk.disableLastUsageTracking | C:\Program Files (x86)\Java\jre1.8.0_441\bin\javaw.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.4410.7 Modules
| |||||||||||||||
| 6592 | C:\Windows\syswow64\MsiExec.exe -Embedding C6672C3A85D50FAFB44FA9E6EB03FCEE E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\LZMA_EXE" d "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\jre1.8.0_441.msi" "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\msi.tmp" | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\LZMA_EXE | — | jre-8u441-windows-i586-iftw.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
34 627
Read events
13 429
Write events
12 863
Delete events
8 335
Modification events
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft |
| Operation: | delete value | Name: | InstallStatus |
Value: | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Country |
Value: DE | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Method |
Value: jother | |||
| (PID) Process: | (7540) jre-8u441-windows-i586-iftw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | PostStatusUrl |
Value: https://sjremetrics.java.com/b/ss//6 | |||
| (PID) Process: | (3304) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E80C0000D32B7517E3AADB01 | |||
Executable files
205
Suspicious files
78
Text files
109
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\jds1100406.tmp | — | |
MD5:— | SHA256:— | |||
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\jre1.8.0_441.msi | — | |
MD5:— | SHA256:— | |||
| 6668 | LZMA_EXE | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\msi.tmp | — | |
MD5:— | SHA256:— | |||
| 3304 | msiexec.exe | C:\Windows\Installer\112400.msi | — | |
MD5:— | SHA256:— | |||
| 7520 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\Local\Temp\jusched.log | text | |
MD5:B36DA5EABCAA72DDC3DFBC5C4D1DE8C9 | SHA256:1A1E2EEB3CEC19F825A756E4907CB960703B12A1232EC048689B9F68DACD0C72 | |||
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:0AA457C5CE9ECD63D99FDE08ADDB7014 | SHA256:09ABC516E7F0DE66B9F180FE3963743D16EE0540EA8780D1A4BE06A66C911989 | |||
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\au.msi | compressed | |
MD5:3B7F9FC63D1878D91B74D0D8F52AD126 | SHA256:9158B014B2D780DE2F931AA44A518E030E04DE2F67123F6C47B1DBB8DB103110 | |||
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:6BE10D8290BD2B60A08953A0EEF4DCFB | SHA256:AEA6A404B5AB1C527729A46B337A67119AB5FC6E2BE7737EAEBA7CE07FC8601E | |||
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\jds1100407.tmp | compressed | |
MD5:3B7F9FC63D1878D91B74D0D8F52AD126 | SHA256:9158B014B2D780DE2F931AA44A518E030E04DE2F67123F6C47B1DBB8DB103110 | |||
| 7540 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\LZMA_EXE | executable | |
MD5:3842C46F2FBC7522EF625F1833530804 | SHA256:17CB7CF185355B60D6ED5138A86C78B9FD5A7D6D3C0DD90F2224246E823166E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7540 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4880 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4880 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAYOL4%2BeG4vlGNX%2BK2nPzLE%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | 23.197.134.132:443 | javadl-esd-secure.oracle.com | Akamai International B.V. | US | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | 104.102.53.139:443 | javadl.oracle.com | AKAMAI-AS | DE | whitelisted |
7540 | jre-8u441-windows-i586-iftw.exe | 2.18.160.86:443 | sdlc-esd.oracle.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |
login.live.com |
| whitelisted |
rps-svcs.oracle.com |
| whitelisted |