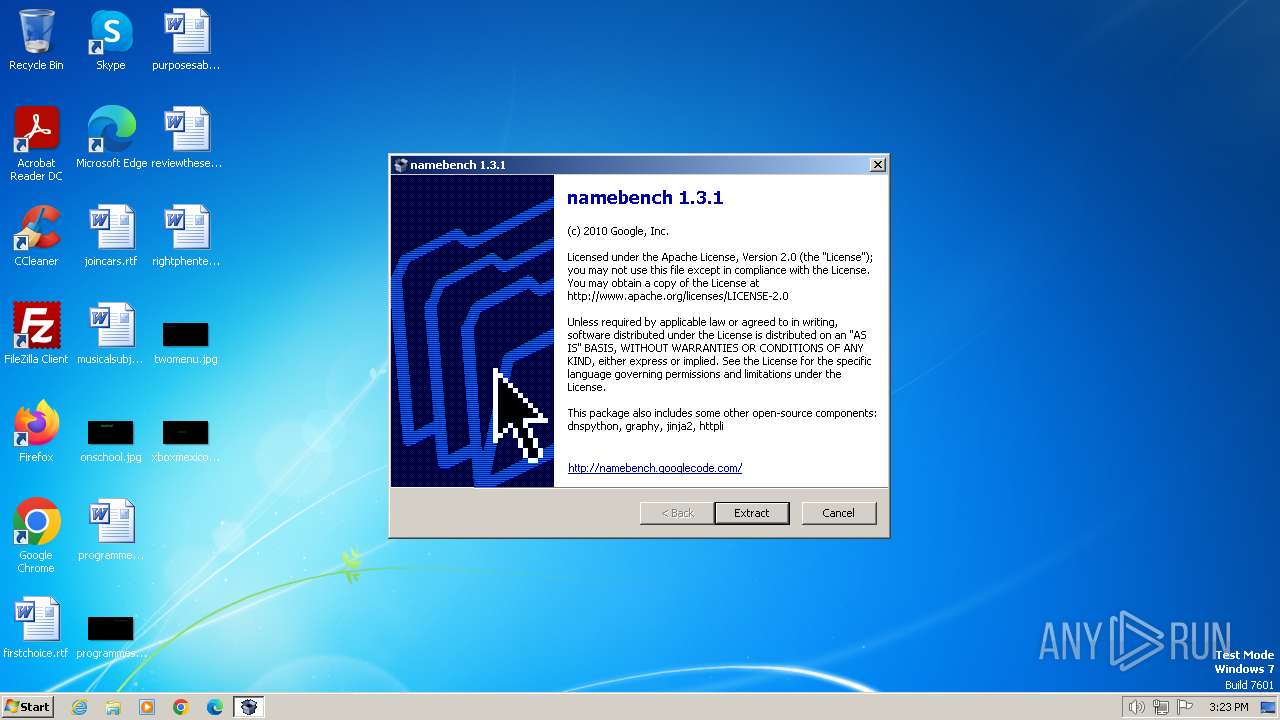
| File name: | namebench-1.3.1-Windows.exe |
| Full analysis: | https://app.any.run/tasks/ea545dcd-6e29-4ec6-8798-7d2865e44057 |
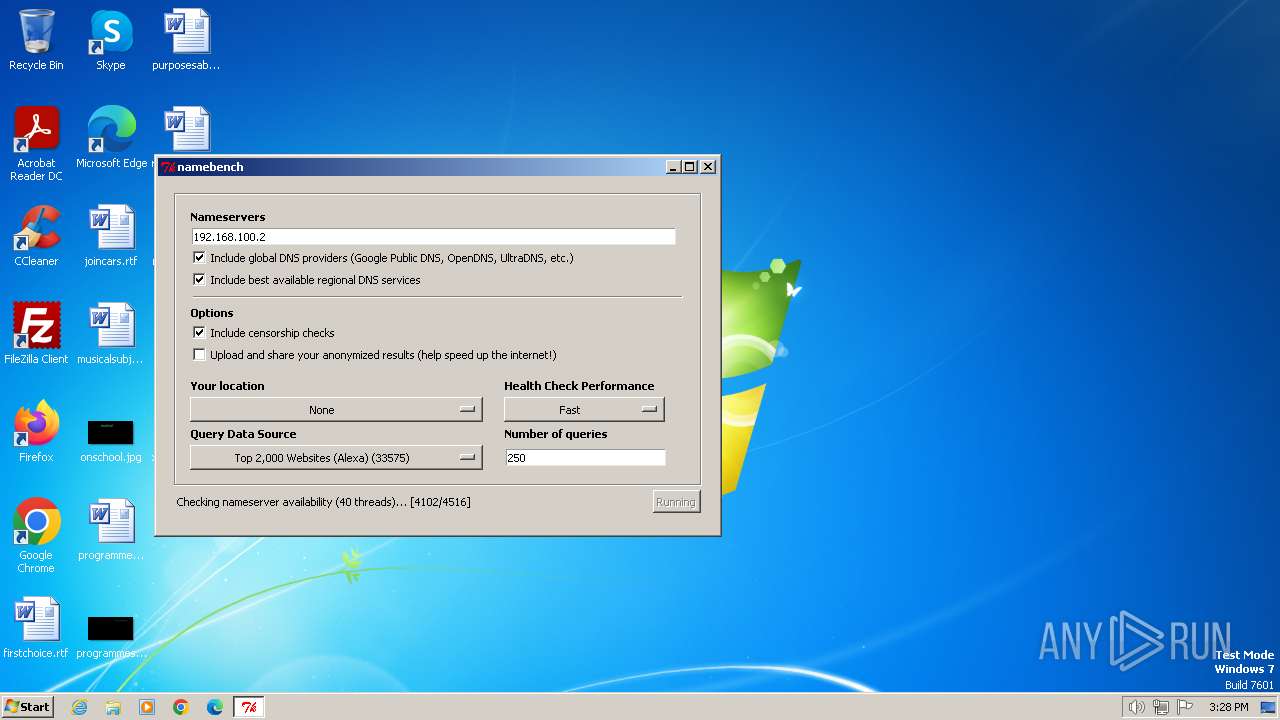
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2024, 14:23:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2A26C182BCC0AFEE88434E64B7B633BE |
| SHA1: | B33778303D37BB6A2E6FE4861C72390A41F3AB7A |
| SHA256: | 32DEBD21DBE46268E2305271FD63B96AFA4284FFA3CF7AE005F1B70E79699FF1 |
| SSDEEP: | 98304:VPHA10B6kNeZ9gYwsxLCknBRSF5SPJYsU+Ry02krJqZCFJJePx6c7g+MhgEdF2OX:wm3reevC |
MALICIOUS
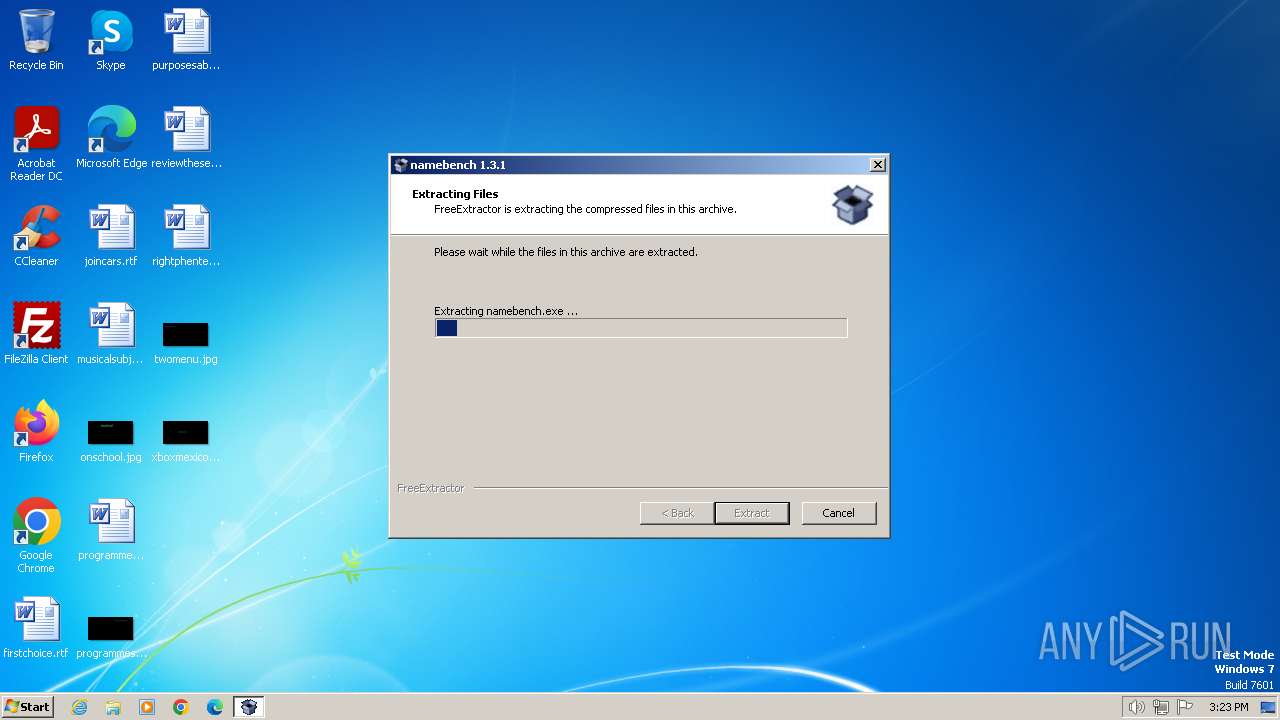
Drops the executable file immediately after the start
- namebench-1.3.1-Windows.exe (PID: 3348)
Actions looks like stealing of personal data
- namebench.exe (PID: 3416)
Steals credentials from Web Browsers
- namebench.exe (PID: 3416)
SUSPICIOUS
Executable content was dropped or overwritten
- namebench-1.3.1-Windows.exe (PID: 3348)
Process drops python dynamic module
- namebench-1.3.1-Windows.exe (PID: 3348)
INFO
Checks supported languages
- namebench-1.3.1-Windows.exe (PID: 3348)
- namebench.exe (PID: 3416)
UPX packer has been detected
- namebench-1.3.1-Windows.exe (PID: 3348)
Create files in a temporary directory
- namebench-1.3.1-Windows.exe (PID: 3348)
- namebench.exe (PID: 3416)
Reads the computer name
- namebench.exe (PID: 3416)
Reads the machine GUID from the registry
- namebench.exe (PID: 3416)
Reads Environment values
- namebench.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:03:20 06:35:57+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Aggressive working-set trim, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 77824 |
| EntryPoint: | 0x19200 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
39
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3348 | "C:\Users\admin\AppData\Local\Temp\namebench-1.3.1-Windows.exe" | C:\Users\admin\AppData\Local\Temp\namebench-1.3.1-Windows.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3416 | namebench.exe | C:\Users\admin\AppData\Local\Temp\namebench.exe | namebench-1.3.1-Windows.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
407
Read events
407
Write events
0
Delete events
0
Modification events
Executable files
12
Suspicious files
1
Text files
312
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench.exe | executable | |
MD5:1A1814781C8E85F9AD8FF8E2F8D9781E | SHA256:E6AA34EAD07078E64F47A3BDDCAB27B1E7A8EAE8363B75405D87E7D756D27B17 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\data\cache-hit.txt | text | |
MD5:8028068E0CAF8A729136AEE4F4F6F3FE | SHA256:0AC200D16A46774D3E23B2C2D185092D82DF08A6363F31CAAE3B2939EC5AC925 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench.zip | compressed | |
MD5:6AB90E72B14D25FDF7AF02A10449D23A | SHA256:0FD1215BE93B89677B7F97A4BD2E7C3FF0512AC08B5B3BDEC853FFA3B042A0B3 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\data\cache-miss.txt | text | |
MD5:155E14DCE644B7D5AC4D800BEFA112E7 | SHA256:88D908CDC046F05348E08C1A8C3C8733AFC4EB62BD8F26F9BEEEDB2A1DD69417 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\config\data_sources.cfg | text | |
MD5:3B5F3956FFA9C0D94B3DFD3421EFF9E7 | SHA256:0CA4CBCD3A98608710ED5AB63FF67AA2D786C1EB7284E330B4EE5A33B89E36EE | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\templates\ascii.tmpl | text | |
MD5:7ED235066BABBE7F293B2C105F3E31BE | SHA256:1F49501C78865D8EC50CFC3B730AFD0E2596EE1893EB12A8B3CAED5BF45509A3 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\templates\html.tmpl | html | |
MD5:386307DEC2B56FACCCBE866E8F4A055E | SHA256:88B78F90C820C5B73FBBAEEF94CB9B8646A0871ACE03E05F676E4623FFAC370A | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\templates\resolv.conf.tmpl | text | |
MD5:4C5143CD43F31C9A4E18A777BFC65D83 | SHA256:614119FE7FD68038BCE4815E5FD24B2E83EAA7543E83ED511781EF7C4841CF49 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\namebench\config\namebench.cfg | text | |
MD5:D4F014F675FB072687BAC68087324F92 | SHA256:96A2F8D67FDBA8E0AE6C37763A7F4FA60FC481B1B27F084B1A1B5F15518B34F9 | |||
| 3348 | namebench-1.3.1-Windows.exe | C:\Users\admin\AppData\Local\Temp\bz2.pyd | executable | |
MD5:3825D4803887FD7905094127F5208035 | SHA256:975F06897191DEBE3408EE23F9D972D69A54B1823645987DF6690FD4F85DD1DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
15
DNS requests
4 144
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | namebench.exe | POST | 404 | 216.58.206.68:80 | http://www.google.com/loc/json | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.18.79.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11acddbe1ebd82b3 | unknown | — | — | unknown |
3416 | namebench.exe | GET | 404 | 142.251.31.82:80 | http://namebench.googlecode.com/svn/trunk/config/hostname_reference.cfg | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3416 | namebench.exe | 216.58.206.68:80 | www.google.com | GOOGLE | US | whitelisted |
3416 | namebench.exe | 49.13.77.253:80 | j.maxmind.com | Hetzner Online GmbH | DE | unknown |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 2.18.79.138:80 | crl.microsoft.com | Akamai International B.V. | AT | unknown |
1372 | svchost.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
j.maxmind.com |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
220.220.67.208.in-addr.arpa |
| unknown |
which.opendns.com |
| unknown |
test.nb0.0422430702551.google.com |
| unknown |
test.nb0.625251210726.google.com |
| unknown |
Threats
2 ETPRO signatures available at the full report