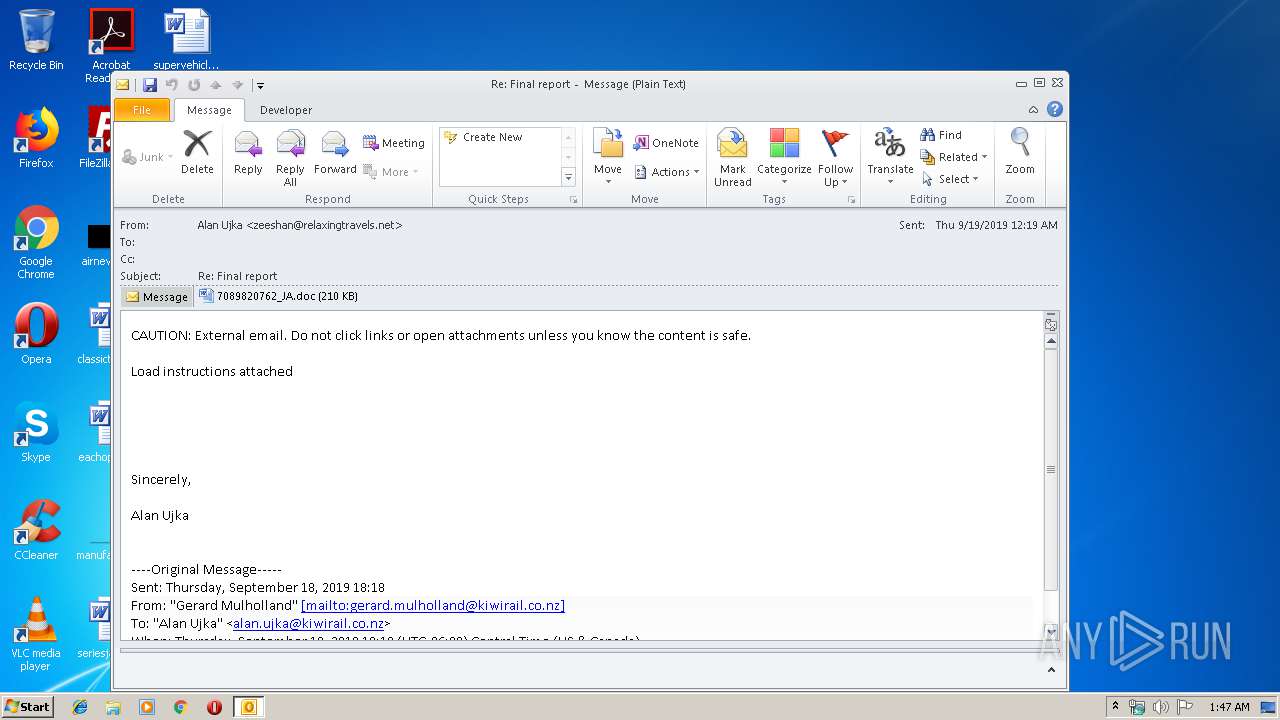
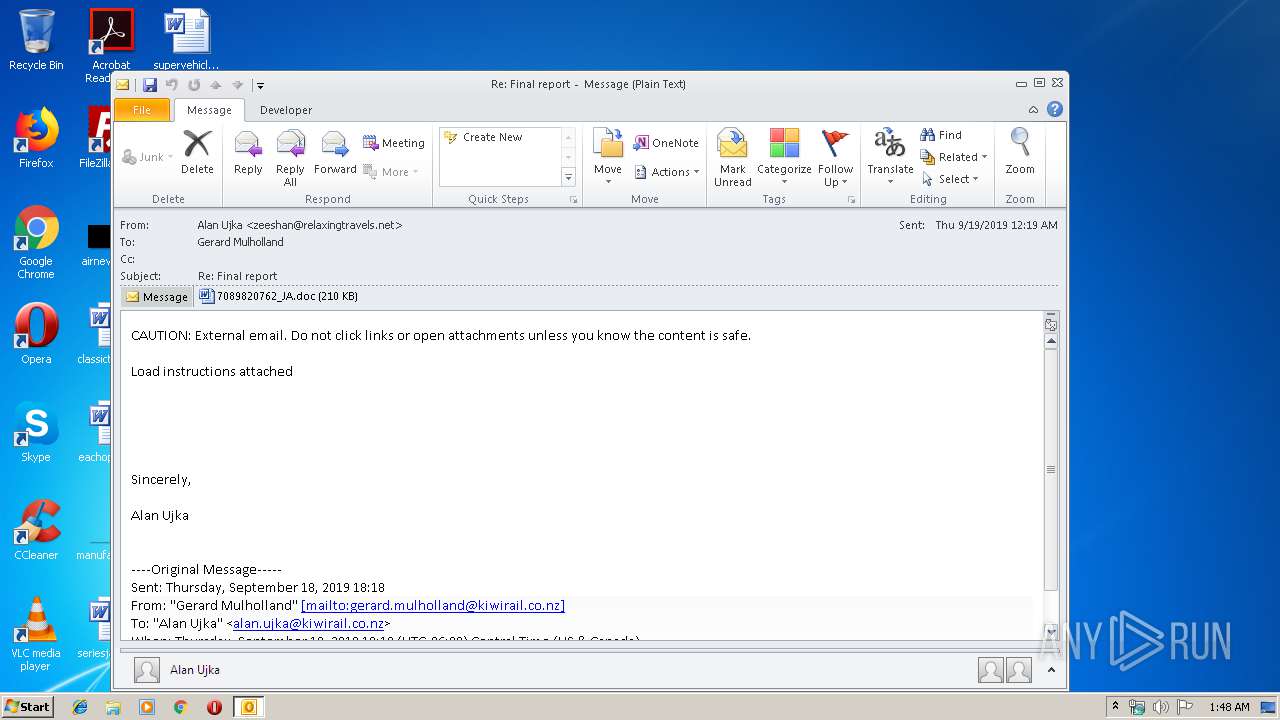
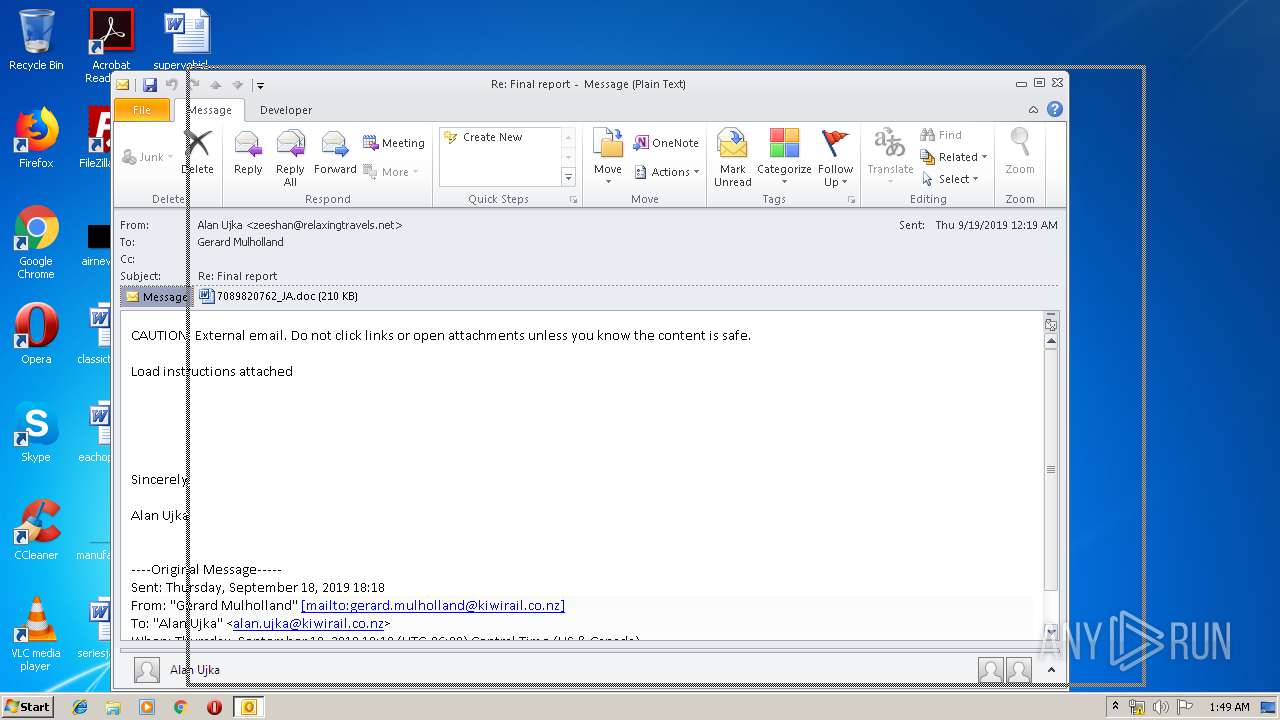
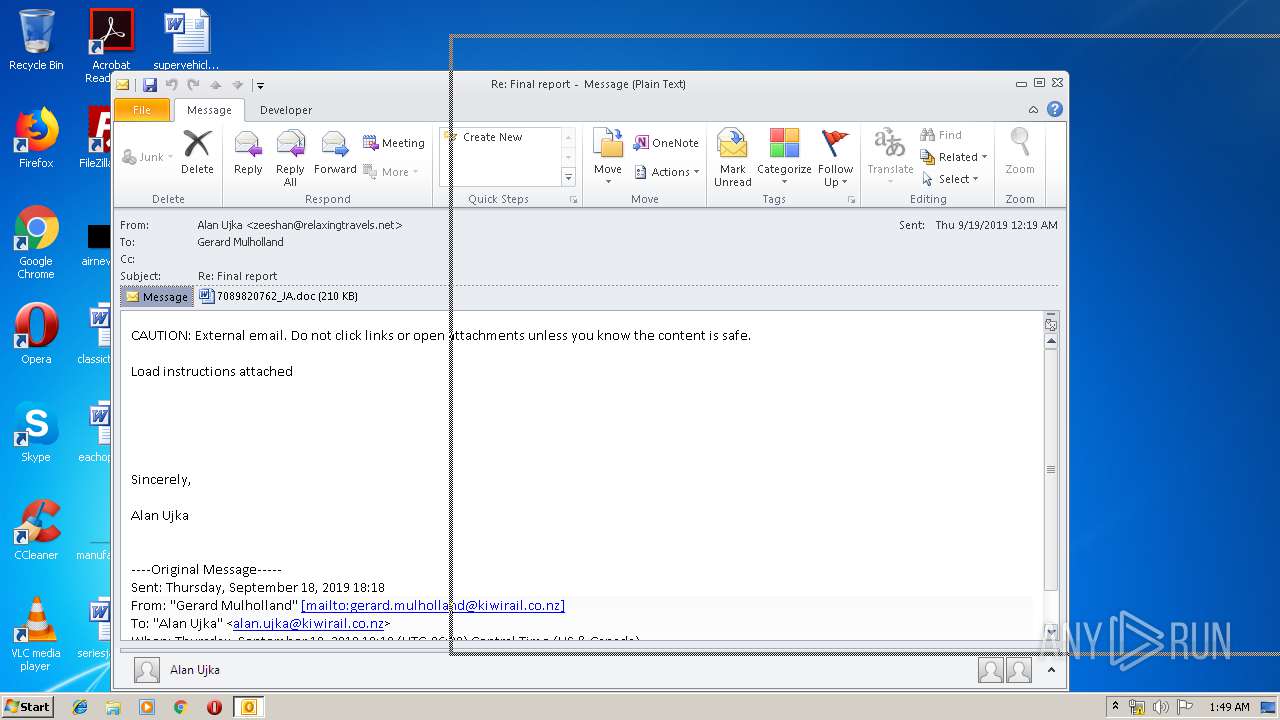
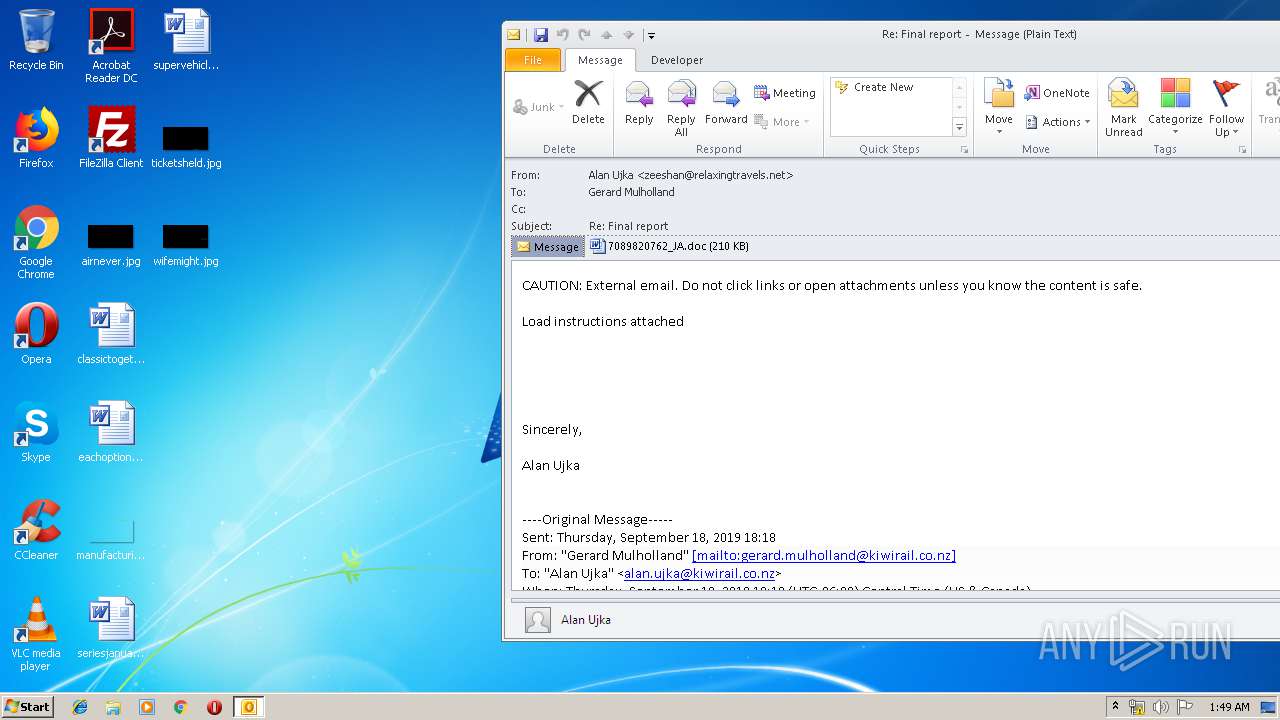
| File name: | Re_ Final report.eml |
| Full analysis: | https://app.any.run/tasks/d20cd8f6-0ac2-4439-9a94-199bdb05794f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 00:47:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | 3077A324864E5D62E5959BF760975A9B |
| SHA1: | C0BAC049019719C601D56414BE2ADB30280B5C7C |
| SHA256: | 32D80A86D33D82D0D570E872C97DE70DF63310A117D727A97B18E4B0F17A3B9E |
| SSDEEP: | 6144:QwTEt+pf20YMhE375zmeQRZGh6vme/gwjBTsZfkcInOW7LzKPHRcl90wsYLbrjIt:gme2We//ZGZ1WLKH |
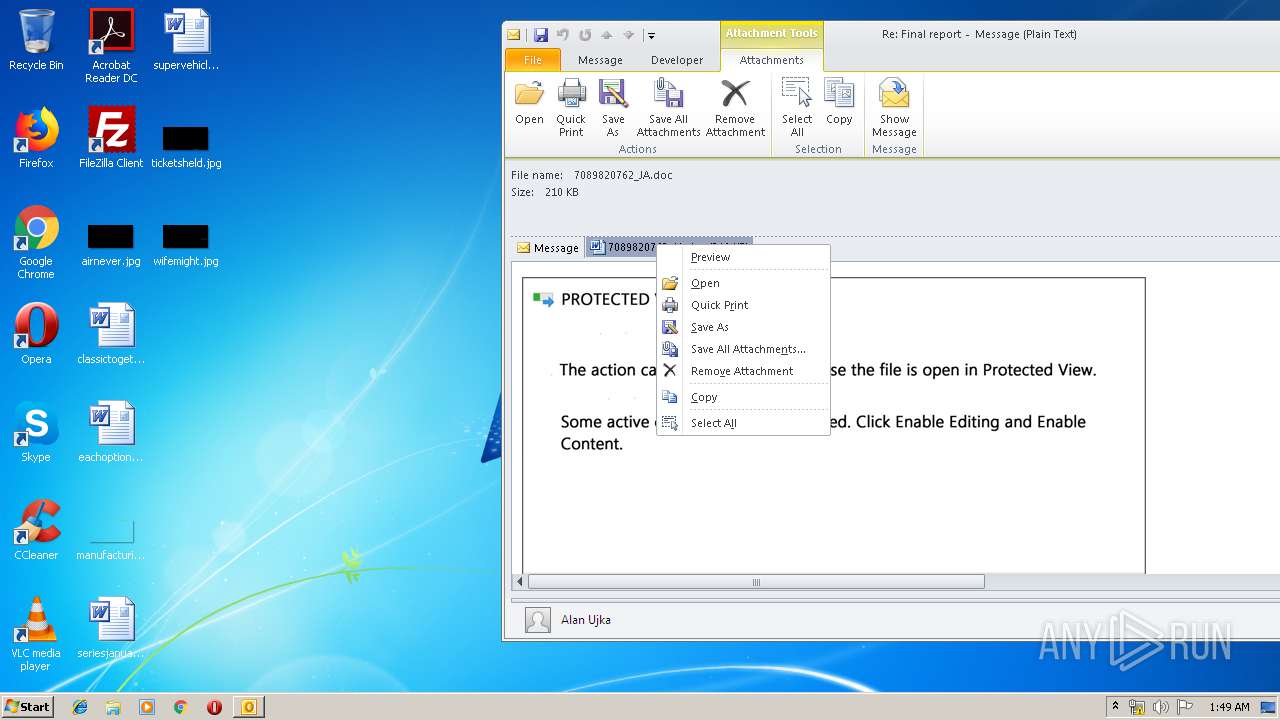
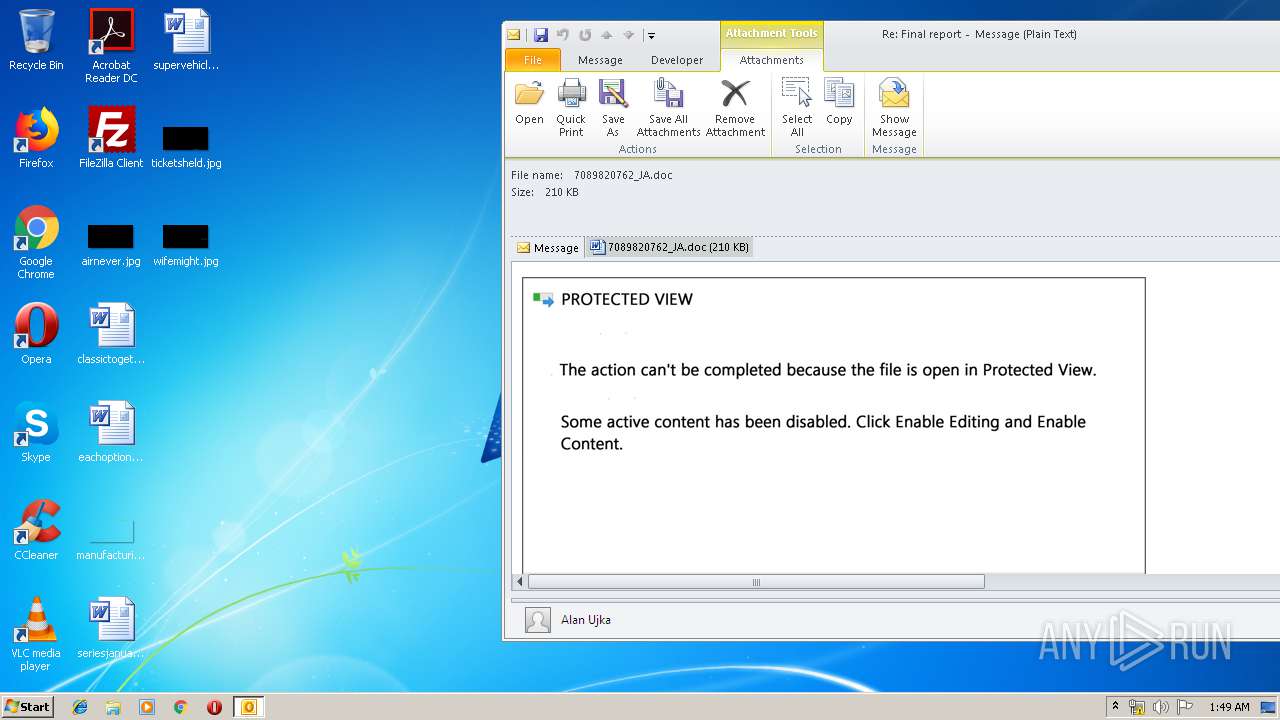
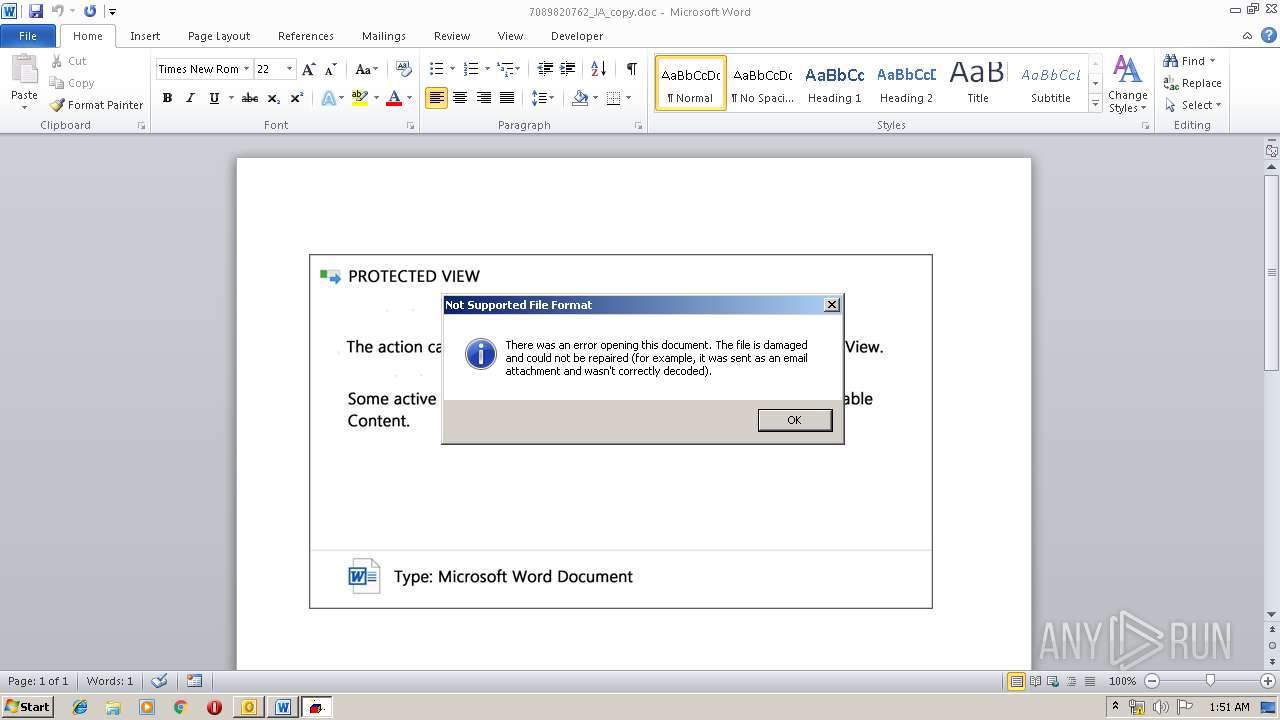
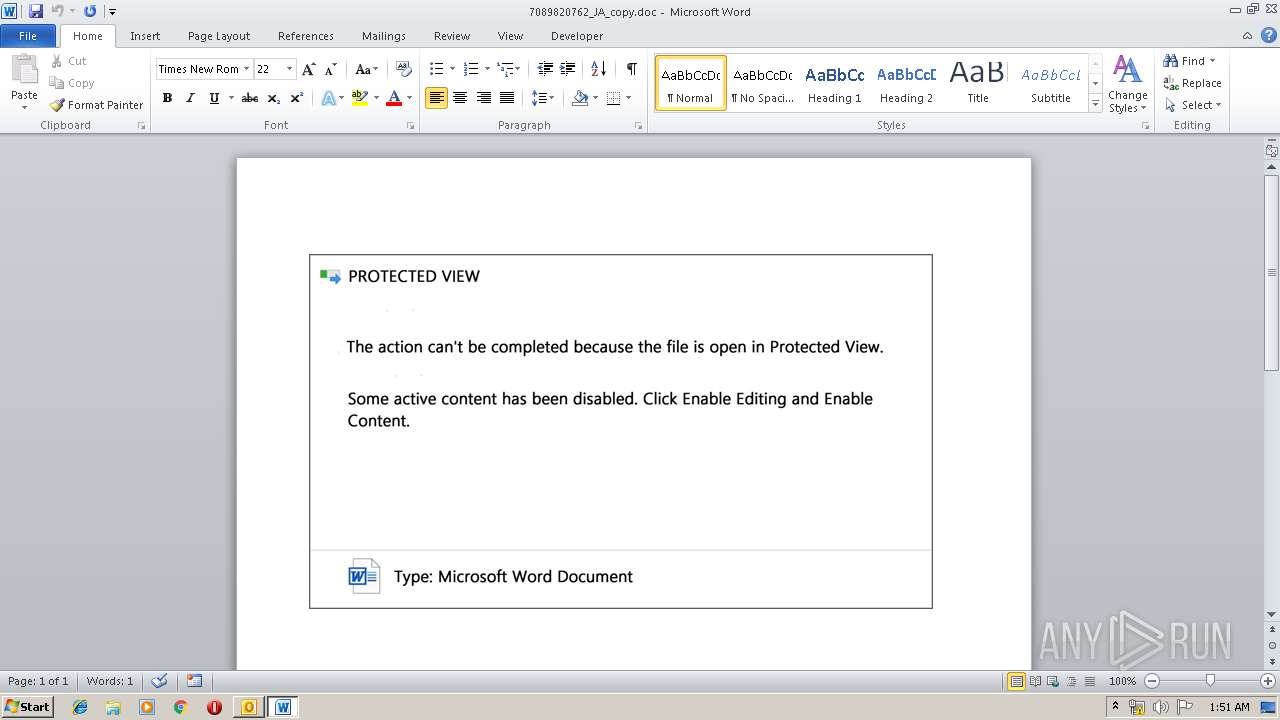
MALICIOUS
Executes scripts
- WINWORD.EXE (PID: 2516)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2516)
Application was dropped or rewritten from another process
- 6giixoryu.exe (PID: 3948)
- 6giixoryu.exe (PID: 2996)
- 6giixoryu.exe (PID: 2760)
- 6giixoryu.exe (PID: 3880)
- easywindow.exe (PID: 2736)
- easywindow.exe (PID: 2228)
- easywindow.exe (PID: 3864)
- easywindow.exe (PID: 2068)
EMOTET was detected
- easywindow.exe (PID: 2068)
Emotet process was detected
- 6giixoryu.exe (PID: 3880)
Changes the autorun value in the registry
- easywindow.exe (PID: 2068)
Connects to CnC server
- easywindow.exe (PID: 2068)
SUSPICIOUS
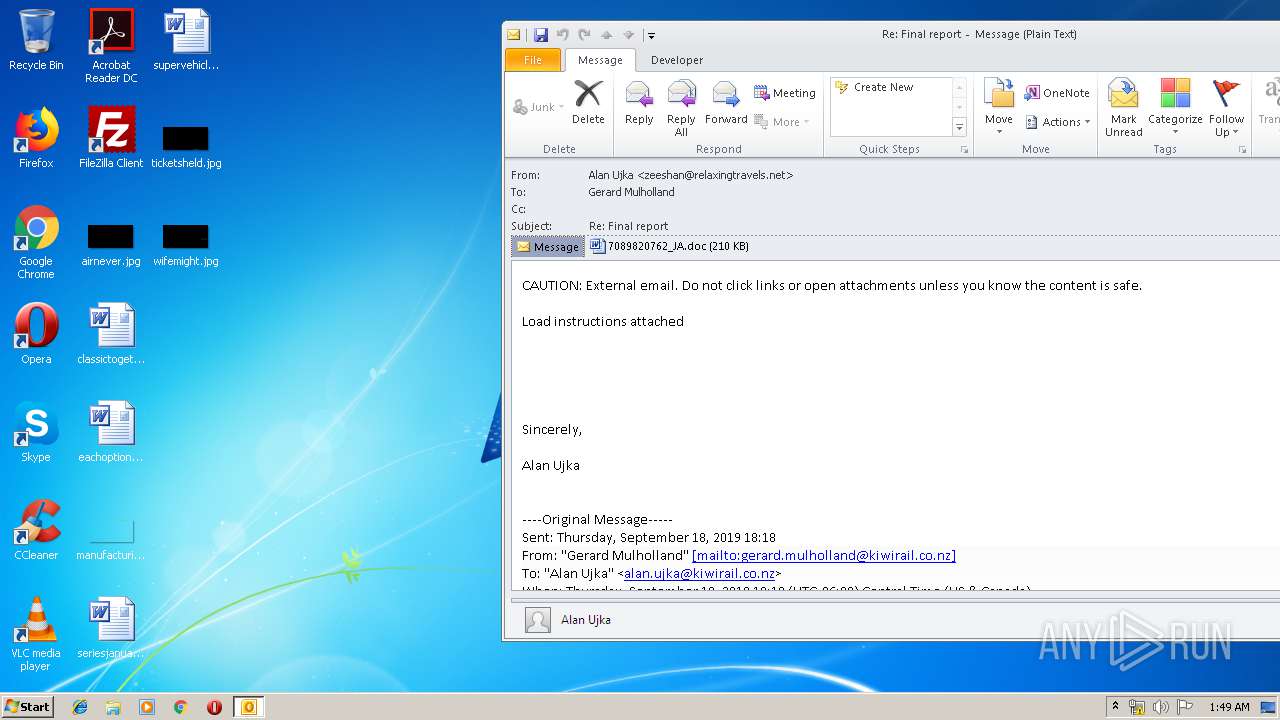
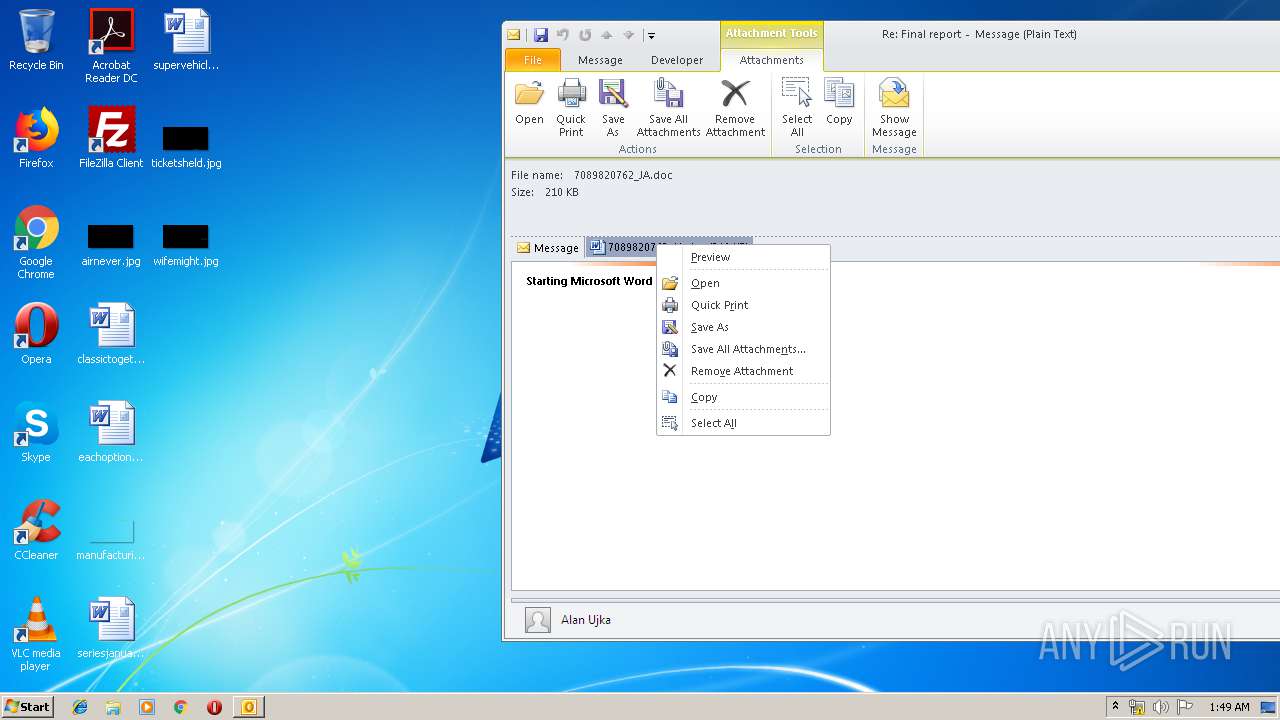
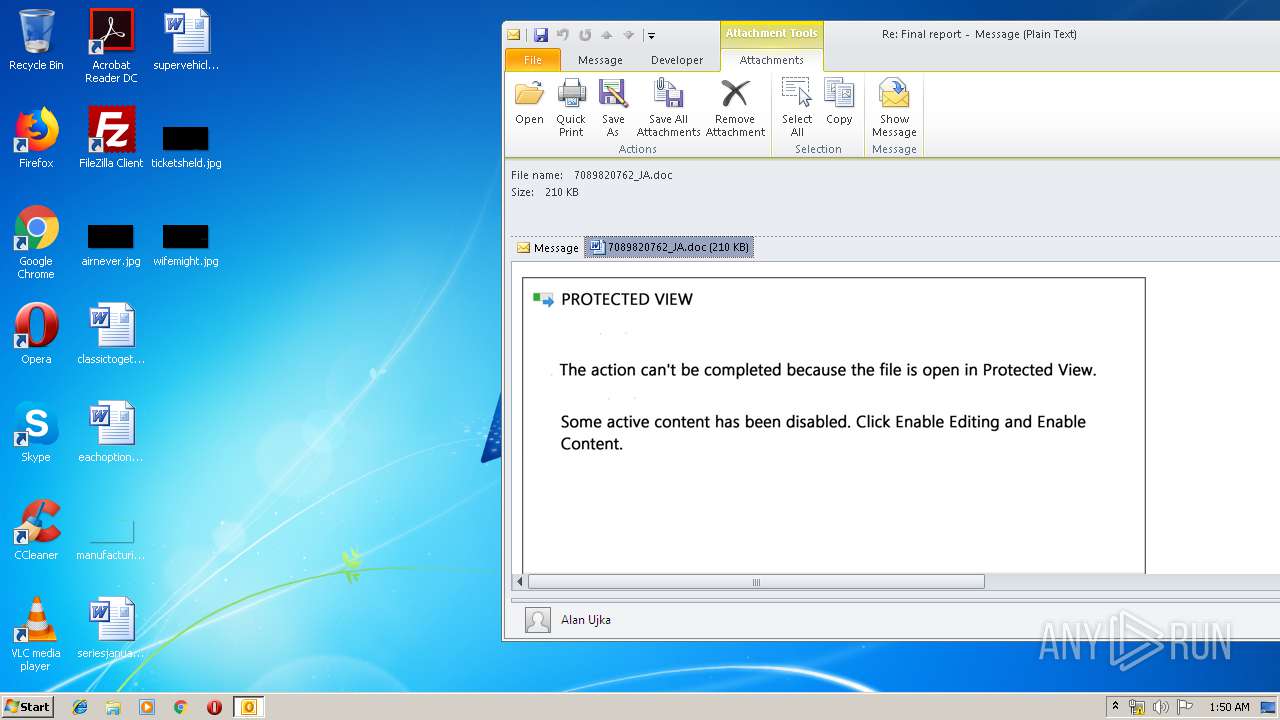
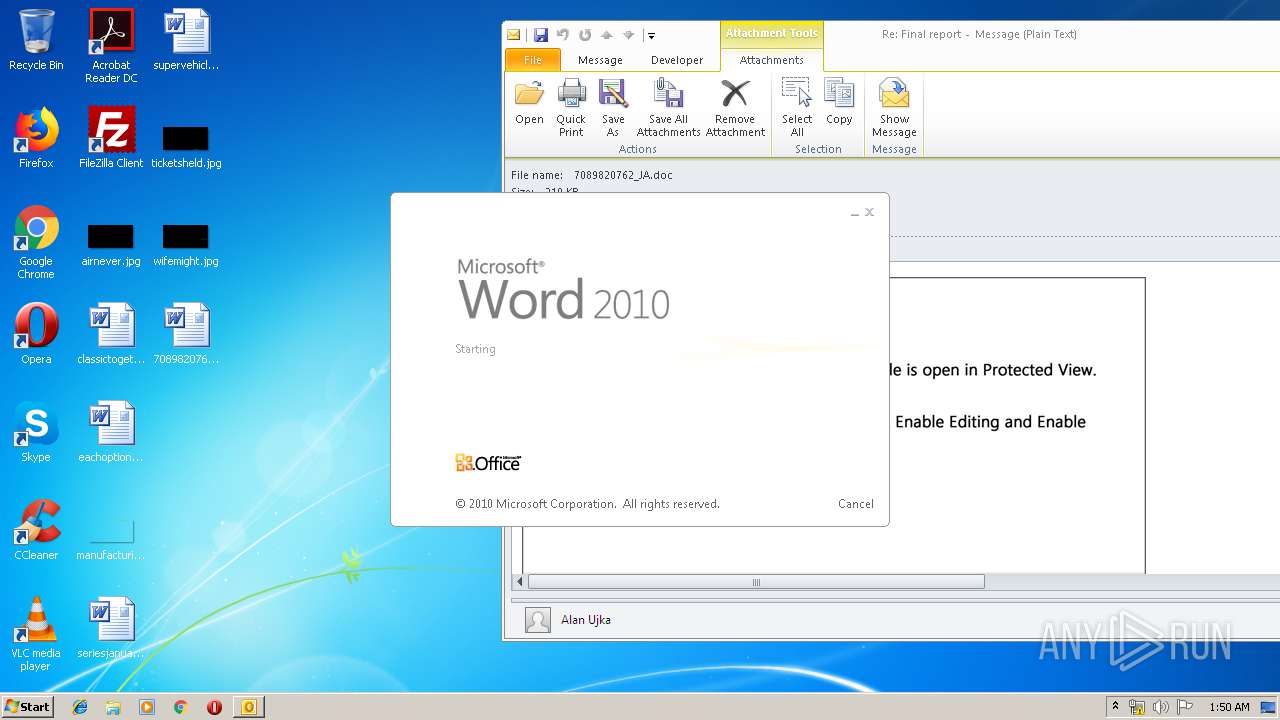
Starts Microsoft Office Application
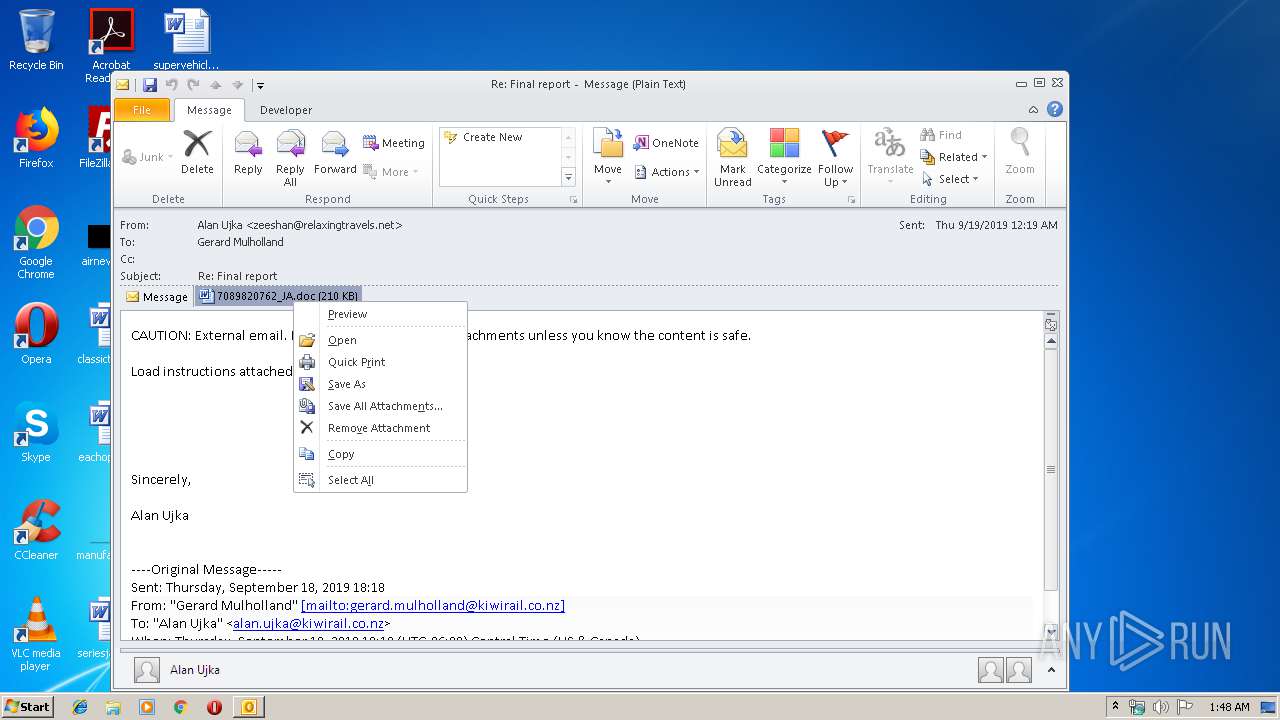
- WINWORD.EXE (PID: 2516)
- OUTLOOK.EXE (PID: 2808)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2808)
Application launched itself
- WINWORD.EXE (PID: 2516)
- easywindow.exe (PID: 2736)
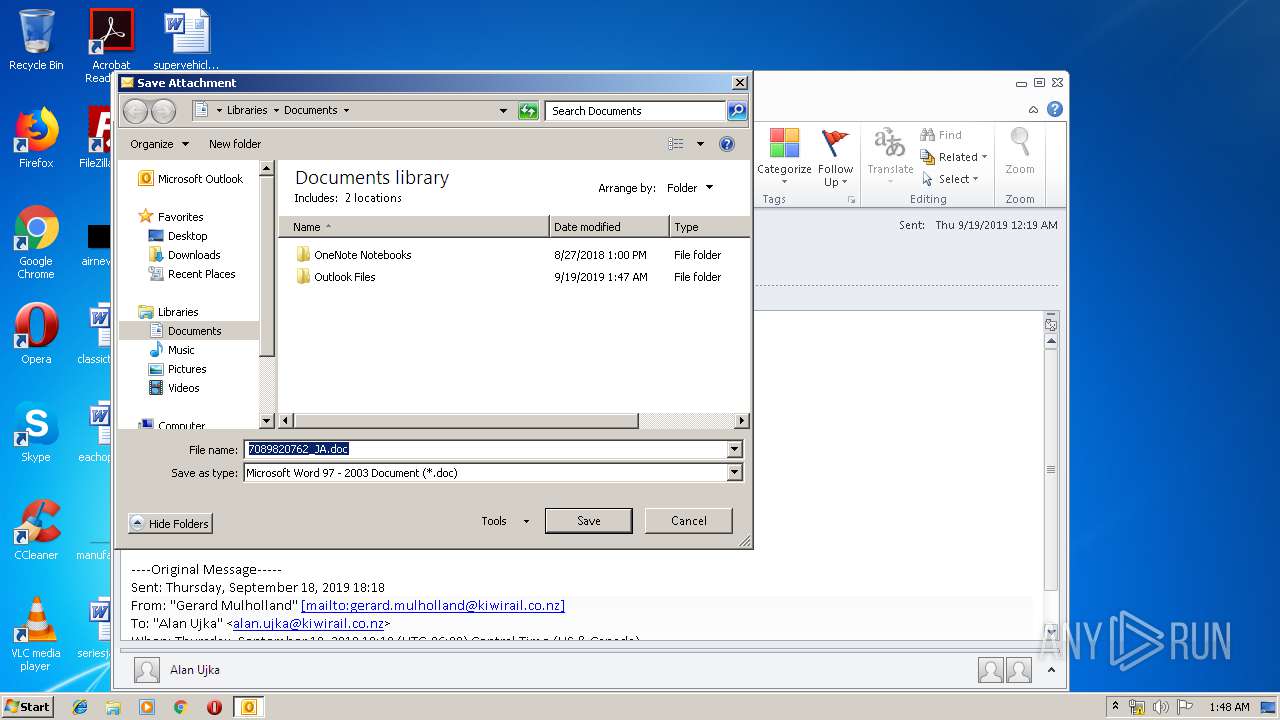
Creates files in the user directory
- OUTLOOK.EXE (PID: 2808)
- WScript.exe (PID: 2768)
Executable content was dropped or overwritten
- WScript.exe (PID: 2768)
- 6giixoryu.exe (PID: 3880)
Starts itself from another location
- 6giixoryu.exe (PID: 3880)
Connects to server without host name
- easywindow.exe (PID: 2068)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2808)
- WINWORD.EXE (PID: 3180)
- WINWORD.EXE (PID: 3728)
- WINWORD.EXE (PID: 2516)
Manual execution by user
- WINWORD.EXE (PID: 2516)
Creates files in the user directory
- WINWORD.EXE (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
51
Monitored processes
13
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2068 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2228 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\7089820762_JA_copy.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 6giixoryu.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2760 | --55a553aa | C:\Users\admin\AppData\Local\Temp\6giixoryu.exe | — | 6giixoryu.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2768 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\0.7055475.jse" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2808 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Re_ Final report.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\6giixoryu.exe" | C:\Users\admin\AppData\Local\Temp\6giixoryu.exe | — | 6giixoryu.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 890
Read events
3 622
Write events
1 231
Delete events
37
Modification events
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | %(! |
Value: 25282100F80A0000010000000000000000000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: F80A00009ADF21DC836ED50100000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220222080 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328742421 | |||
Executable files
2
Suspicious files
16
Text files
30
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8C85.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp8EC8.tmp | — | |
MD5:— | SHA256:— | |||
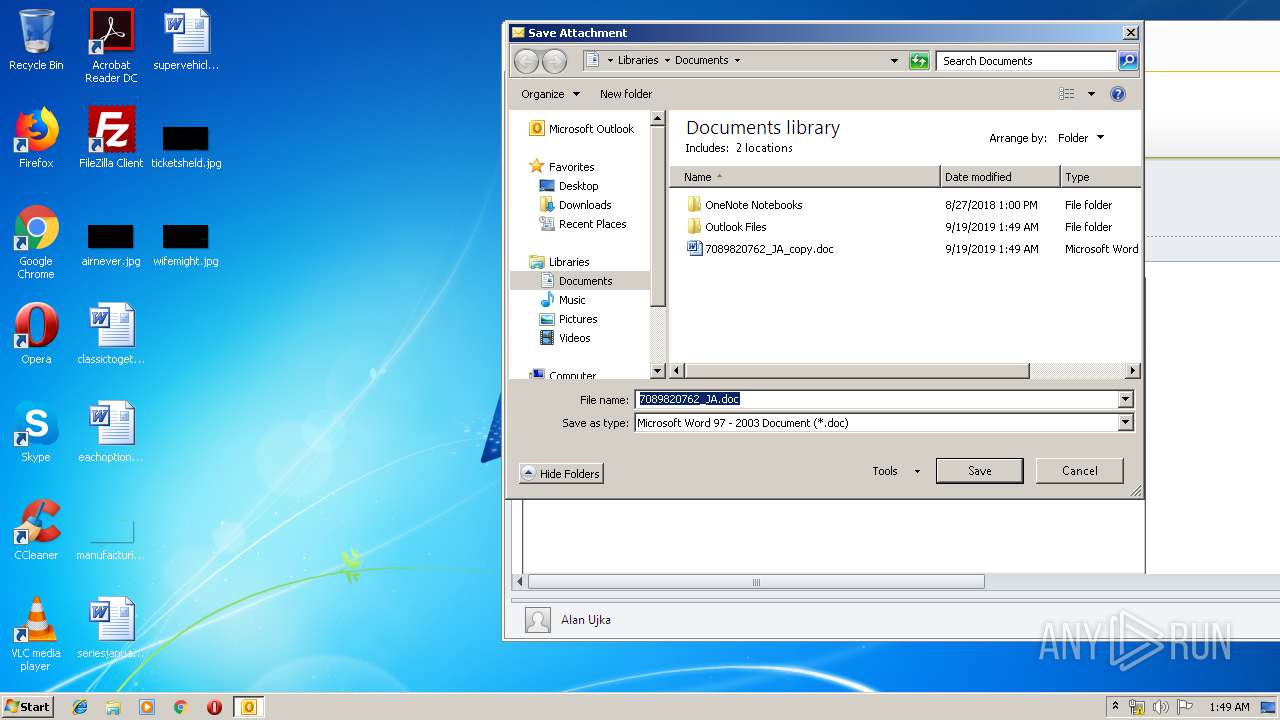
| 2808 | OUTLOOK.EXE | C:\Users\admin\Documents\7089820762_JA_copy.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\1VPA75AJ\7089820762_JA (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C8479BDD-03A7-4333-9A60-C2EE0552BA2E.0\6E37F462.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
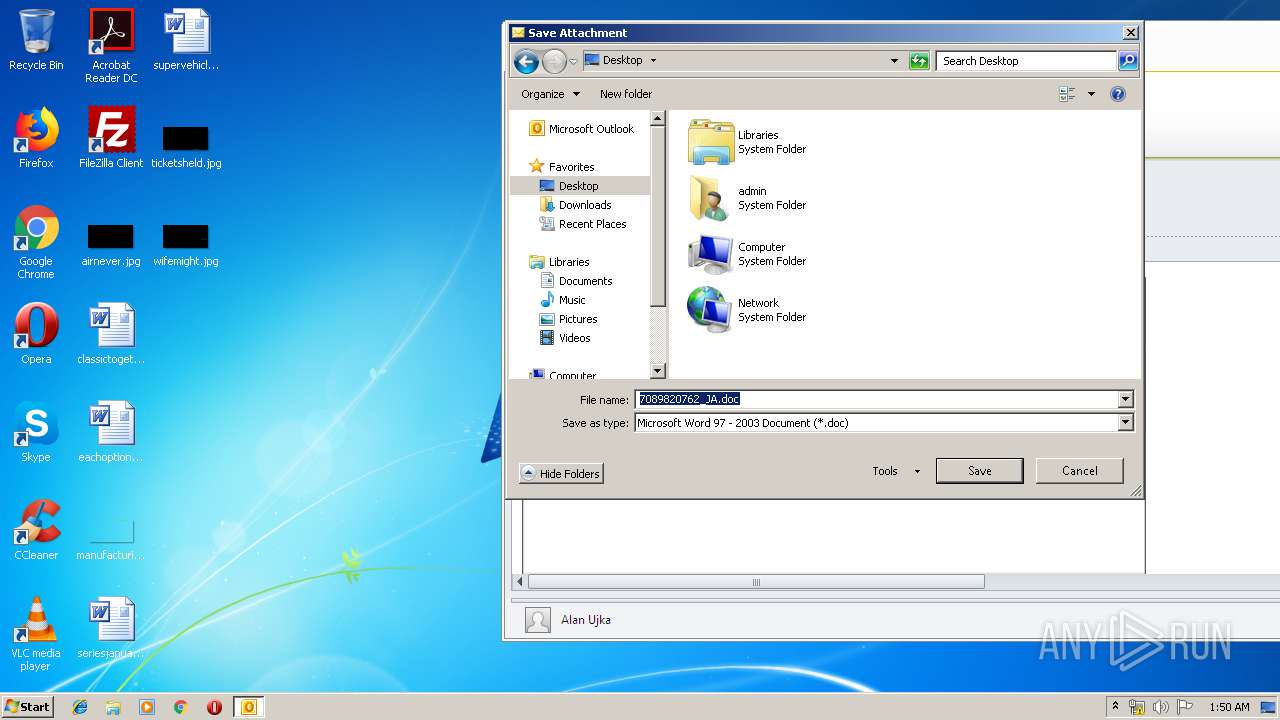
| 2808 | OUTLOOK.EXE | C:\Users\admin\Desktop\7089820762_JA_copy.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD8A8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{9787244D-7266-43D1-A71F-6994D8923EC9}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 2516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_5B19754D-1242-4AAF-94D3-57CEEDE9DE4A.0\3C37D30B.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2068 | easywindow.exe | POST | 200 | 190.18.146.70:80 | http://190.18.146.70/prep/ | AR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
— | — | 190.18.146.70:80 | — | CABLEVISION S.A. | AR | malicious |
2768 | WScript.exe | 47.101.216.114:443 | www.wuus.org.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.wuus.org.cn |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2068 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2068 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report