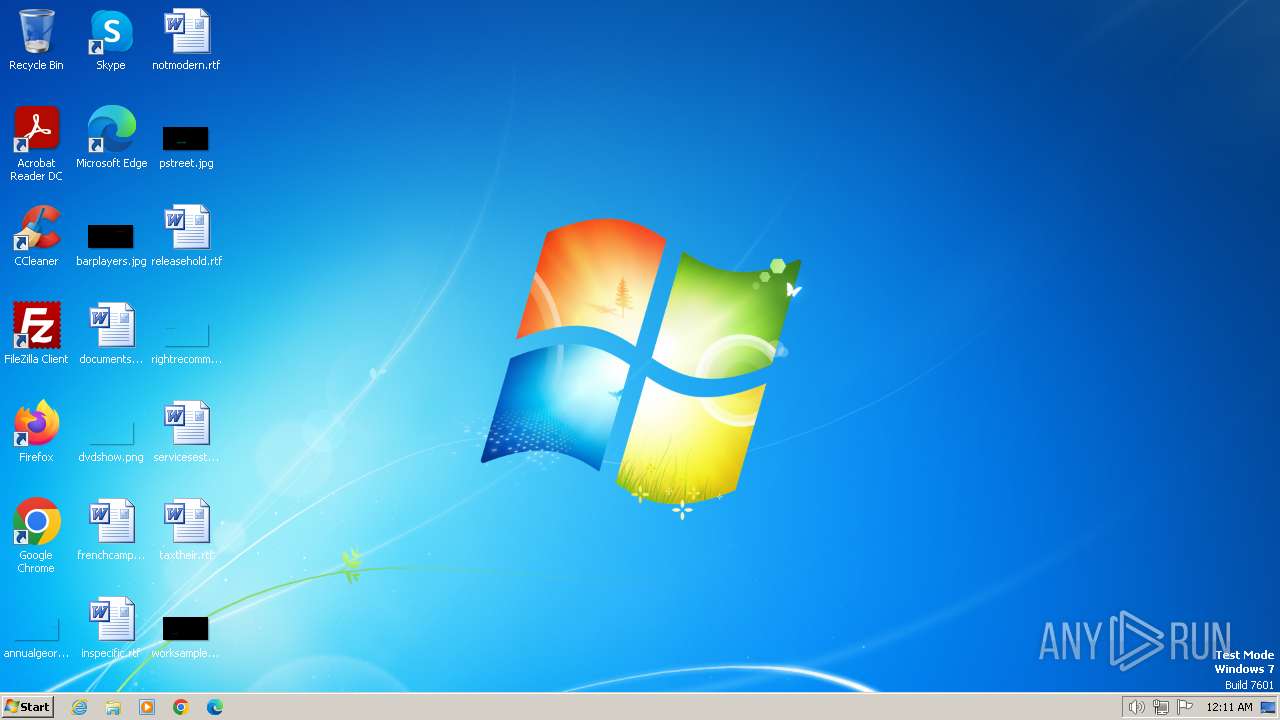
| File name: | HorrorTrojan6.exe |
| Full analysis: | https://app.any.run/tasks/7b1688fc-b53b-4ee1-98b2-fe7d9a20e9b8 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 00:11:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | ABB3A2F1580A738C96716509A0D9121D |
| SHA1: | 9843ED4836E3D08DE2A7F73A9ADF382DCBDDEA34 |
| SHA256: | 32D2D9331DA7F7745E9031538997CC1129B28AF533DCB3DDCC81230F48B89226 |
| SSDEEP: | 98304:9E4dwtudIWr5+tvTQu5YDr3BDmDoqlEmfZhQ7kU/9oCGyXwKjKwWm3oWEBEHU1Xg:h2jG3BBFq |
MALICIOUS
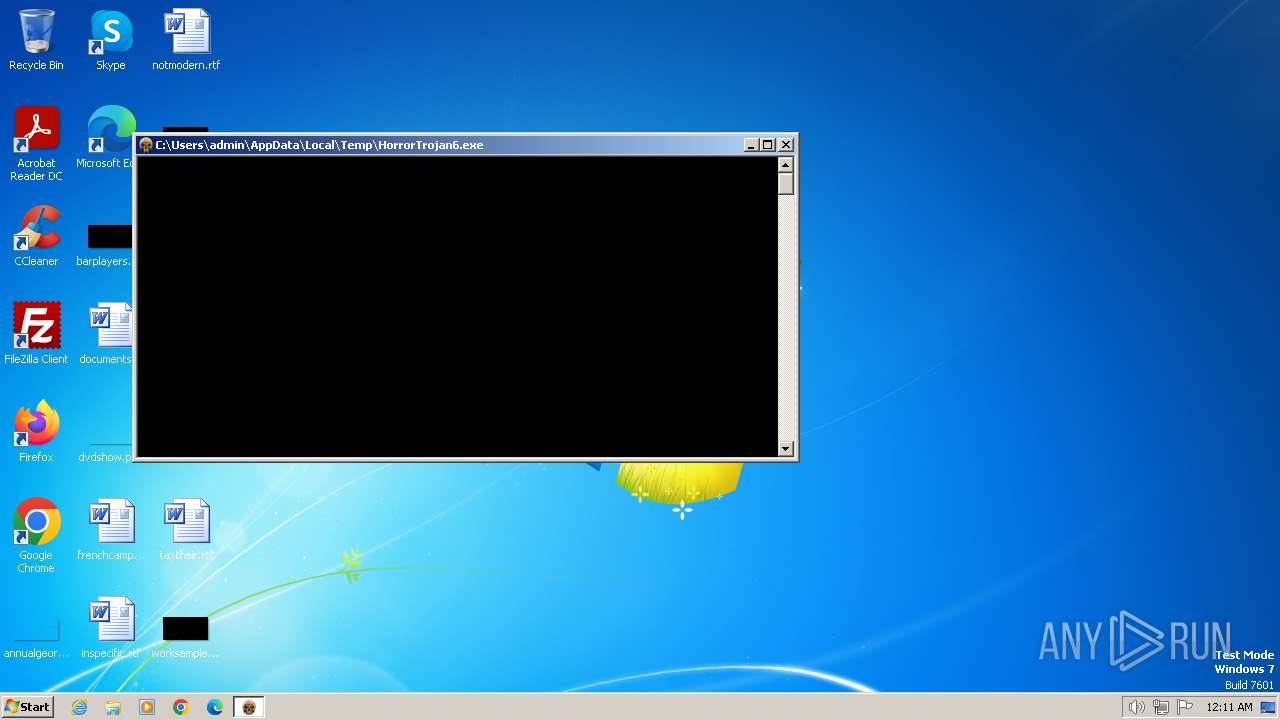
Drops the executable file immediately after the start
- HorrorTrojan6.exe (PID: 3660)
- cmd.exe (PID: 2840)
UAC/LUA settings modification
- reg.exe (PID: 3304)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2840)
- net.exe (PID: 3428)
Disables Windows Defender
- reg.exe (PID: 1040)
Create files in the Startup directory
- cmd.exe (PID: 2840)
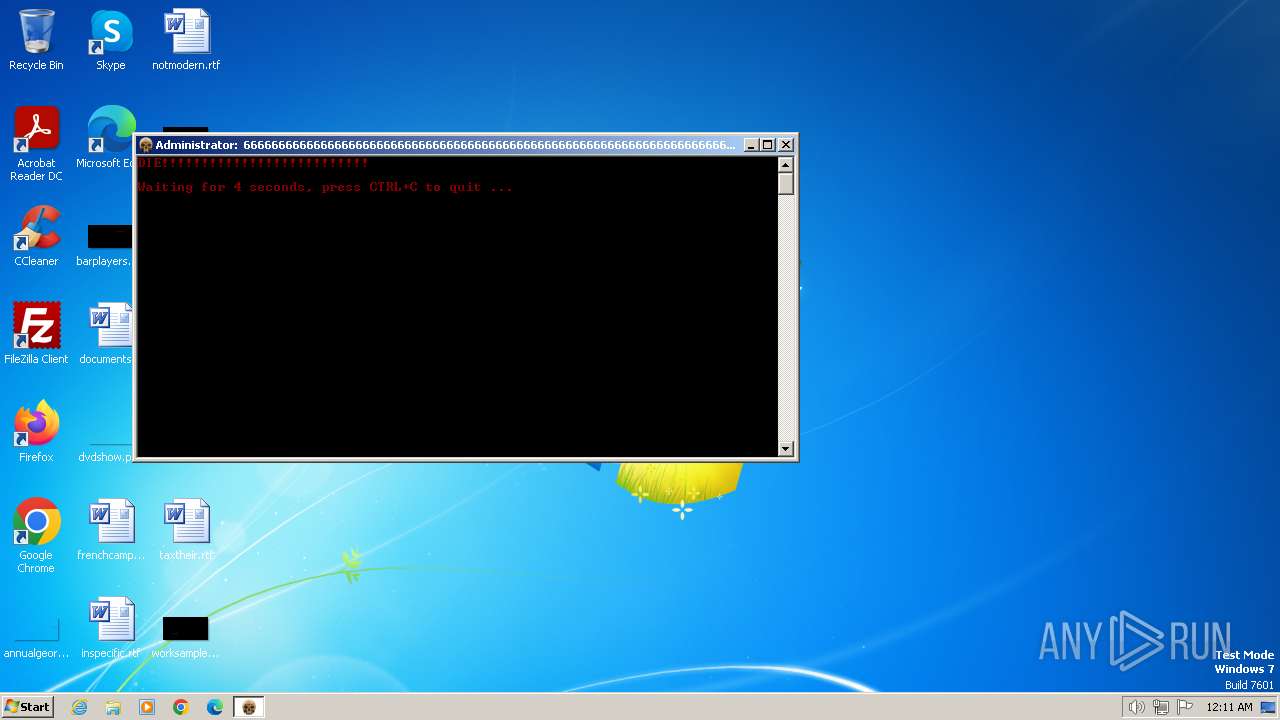
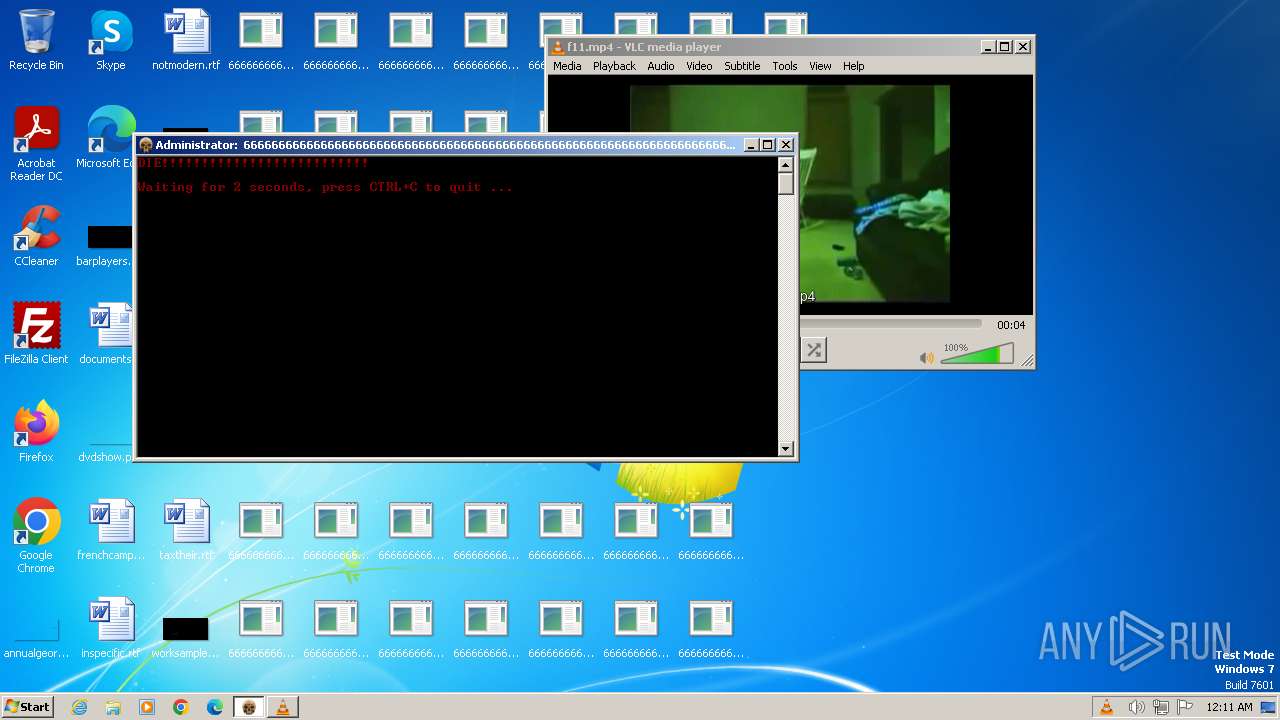
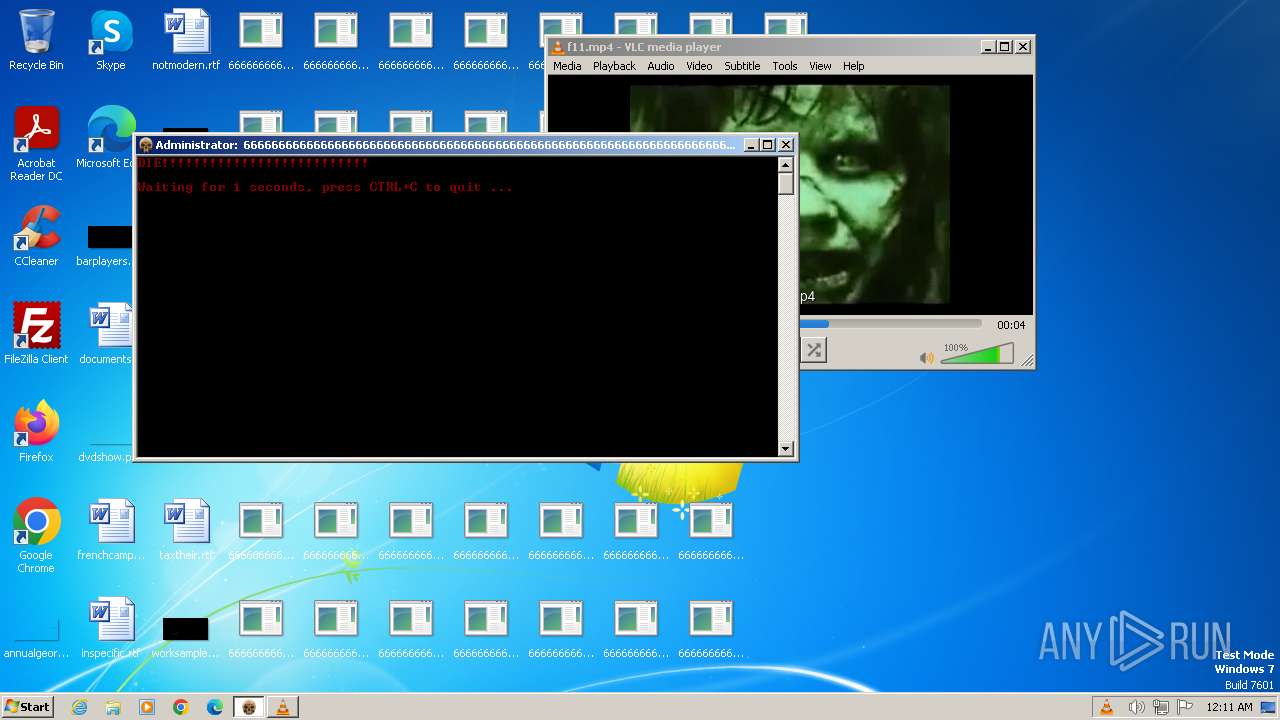
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2644)
- wscript.exe (PID: 2100)
SUSPICIOUS
Executing commands from ".cmd" file
- HorrorTrojan6.exe (PID: 3660)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2840)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2840)
Executable content was dropped or overwritten
- HorrorTrojan6.exe (PID: 3660)
- cmd.exe (PID: 2840)
Starts CMD.EXE for commands execution
- HorrorTrojan6.exe (PID: 3660)
- cmd.exe (PID: 2840)
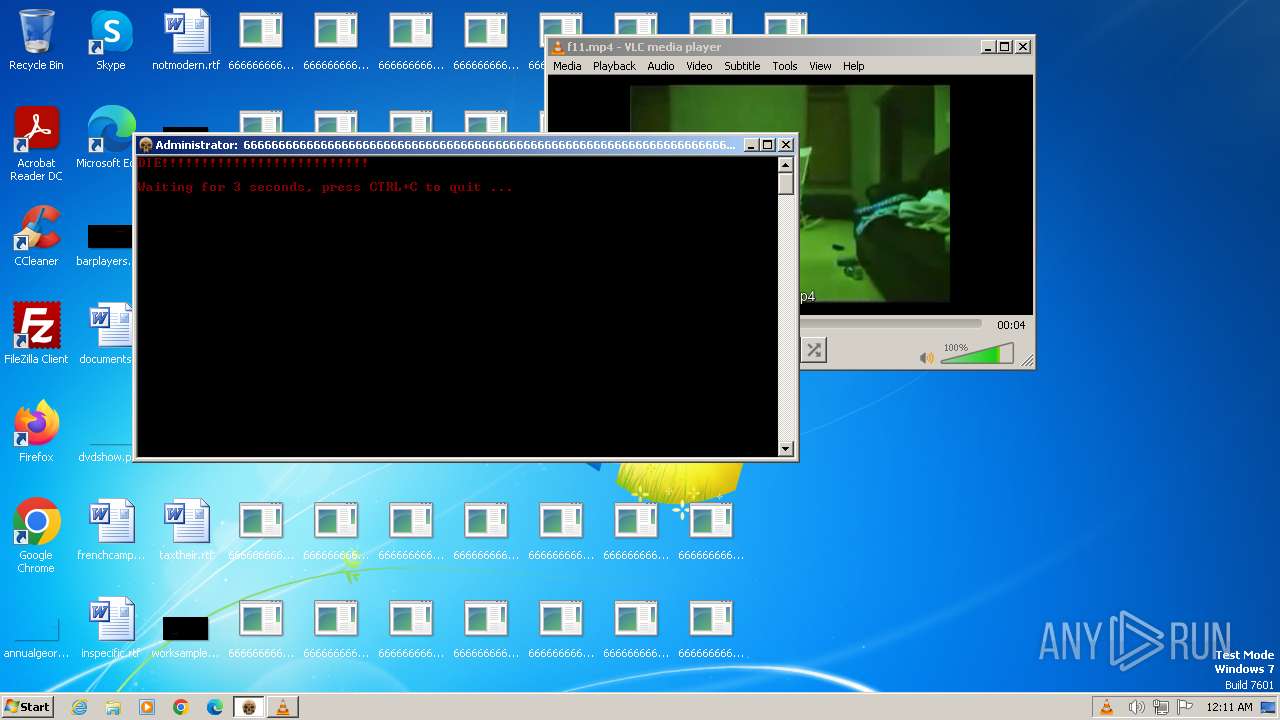
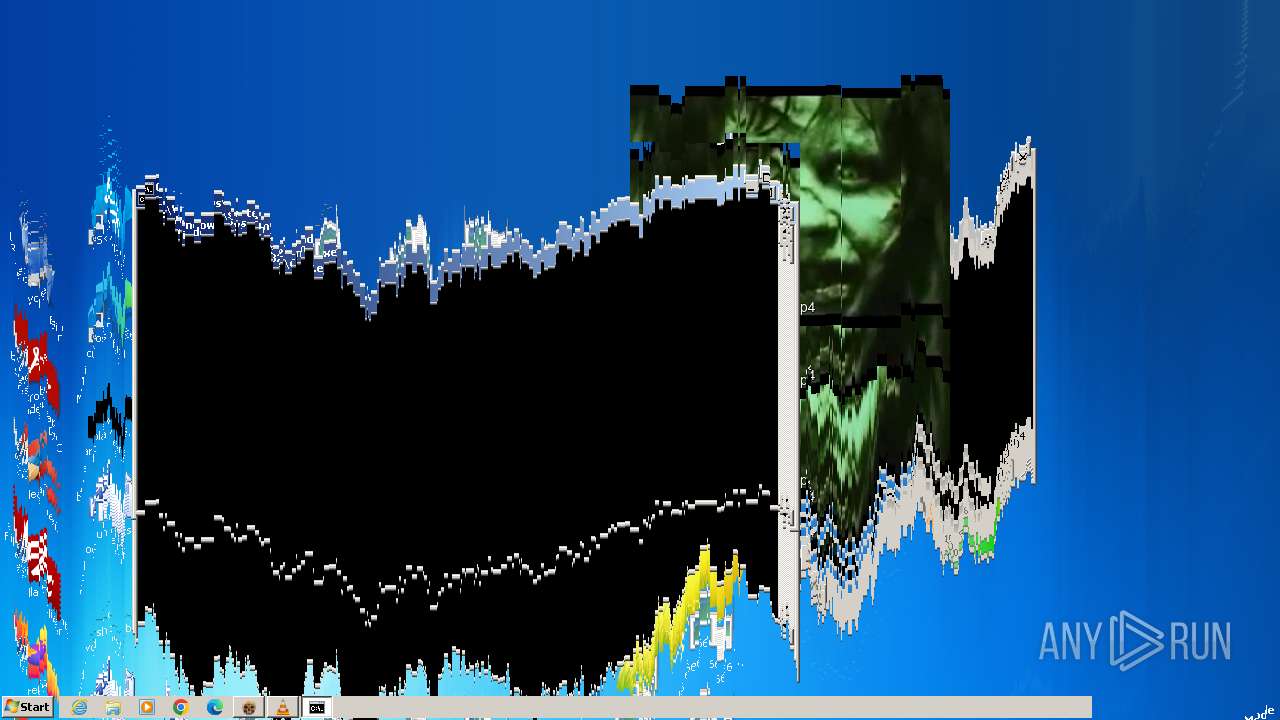
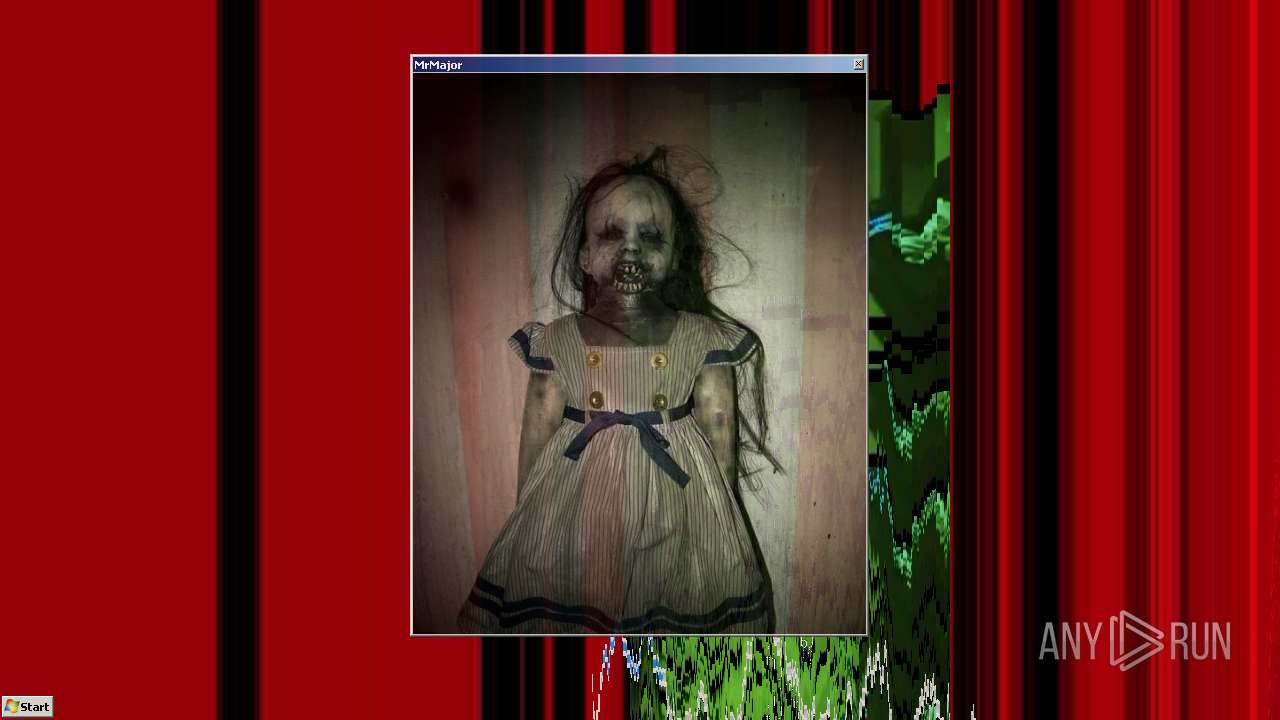
Changes the desktop background image
- reg.exe (PID: 3944)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2840)
Reads the Internet Settings
- cmd.exe (PID: 2840)
- wscript.exe (PID: 2644)
- sipnotify.exe (PID: 1476)
- wscript.exe (PID: 2100)
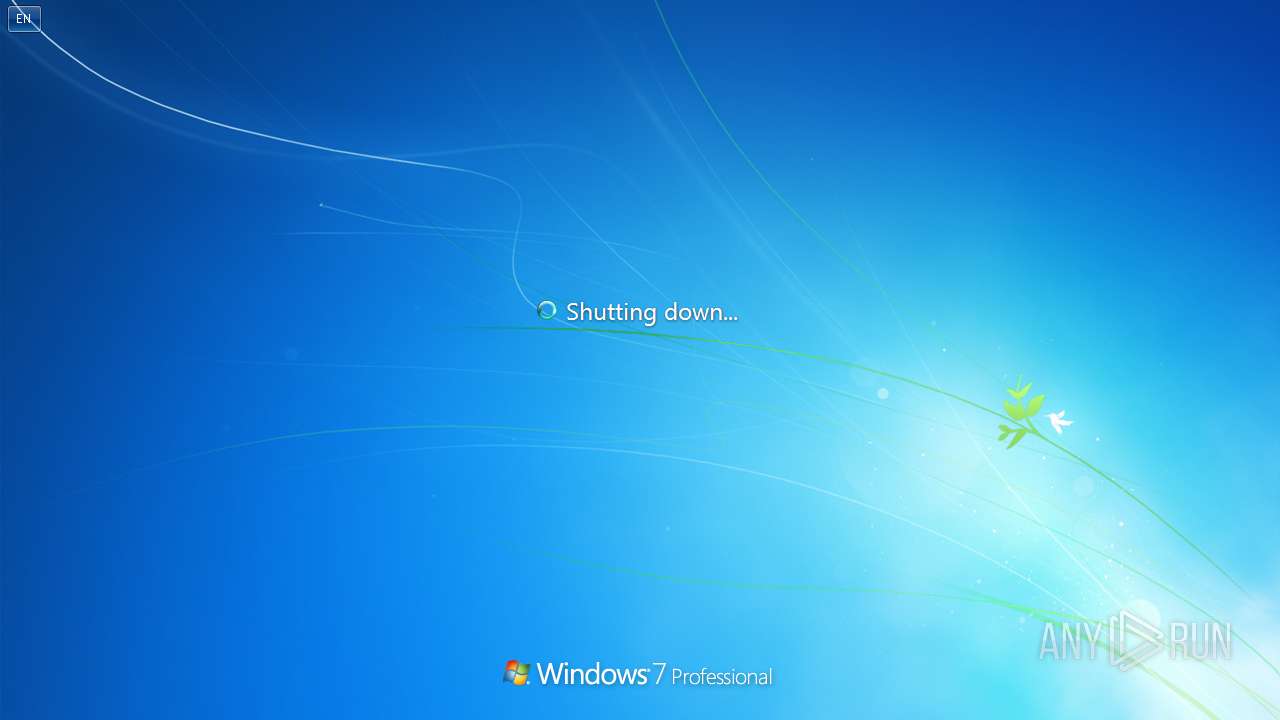
The system shut down or reboot
- cmd.exe (PID: 2840)
The process executes VB scripts
- cmd.exe (PID: 2840)
Executing commands from a ".bat" file
- cmd.exe (PID: 2840)
The executable file from the user directory is run by the CMD process
- ScreenMelter.exe (PID: 2596)
- Scream.exe (PID: 1644)
Application launched itself
- cmd.exe (PID: 2840)
The process executes via Task Scheduler
- ctfmon.exe (PID: 348)
- sipnotify.exe (PID: 1476)
Reads settings of System Certificates
- sipnotify.exe (PID: 1476)
INFO
Create files in a temporary directory
- HorrorTrojan6.exe (PID: 3660)
Checks supported languages
- HorrorTrojan6.exe (PID: 3660)
- vlc.exe (PID: 1696)
- ScreenMelter.exe (PID: 2596)
- Scream.exe (PID: 1644)
- MrsMjrGui.exe (PID: 1336)
- MrsMjrGui.exe (PID: 3036)
- MrsMjrGui.exe (PID: 128)
- IMEKLMG.EXE (PID: 1944)
- IMEKLMG.EXE (PID: 1400)
- vlc.exe (PID: 2064)
- wmpnscfg.exe (PID: 2736)
- Scream.exe (PID: 2124)
- ScreenMelter.exe (PID: 2136)
- MrsMjrGui.exe (PID: 2148)
- wmpnscfg.exe (PID: 2776)
Reads the time zone
- net1.exe (PID: 4060)
Creates files in the program directory
- cmd.exe (PID: 2840)
Checks proxy server information
- wscript.exe (PID: 2644)
- wscript.exe (PID: 2100)
Reads the computer name
- MrsMjrGui.exe (PID: 1336)
- vlc.exe (PID: 1696)
- IMEKLMG.EXE (PID: 1944)
- IMEKLMG.EXE (PID: 1400)
- vlc.exe (PID: 2064)
- MrsMjrGui.exe (PID: 2148)
- wmpnscfg.exe (PID: 2736)
- wmpnscfg.exe (PID: 2776)
Reads the machine GUID from the registry
- MrsMjrGui.exe (PID: 1336)
- MrsMjrGui.exe (PID: 2148)
Manual execution by a user
- IMEKLMG.EXE (PID: 1944)
- cmd.exe (PID: 2080)
- IMEKLMG.EXE (PID: 1400)
- vlc.exe (PID: 2064)
- wscript.exe (PID: 2100)
- Scream.exe (PID: 2124)
- wmpnscfg.exe (PID: 2736)
- wmpnscfg.exe (PID: 2776)
- ScreenMelter.exe (PID: 2136)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1476)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 1944)
- IMEKLMG.EXE (PID: 1400)
Reads the software policy settings
- sipnotify.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:08 13:12:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 6295552 |
| InitializedDataSize: | 253952 |
| UninitializedDataSize: | 3002368 |
| EntryPoint: | 0x8de2d0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 6.6.6.6 |
| ProductVersionNumber: | 6.6.6.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | HorrorTrojans |
| FileDescription: | ZGVhdGg= |
| FileVersion: | 6,6,6,6 |
| ProductName: | HorrorTrojan 6.666 |
| InternalName: | ZGVhdGg= |
| ProductVersion: | 6,6,6,6 |
| LegalCopyright: | 2022 |
Total processes
119
Monitored processes
33
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\mrsmjrgui.exe" | C:\MrsMjrGui.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221226091 Version: 1.0.0.0 Modules
| |||||||||||||||
| 348 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | Reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender" /v DisableAntiSpyware /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\mrsmjrgui.exe" | C:\MrsMjrGui.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1476 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1492 | reg.exe ADD HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop /v NoChangingWallPaper /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1644 | scream.exe | C:\Users\admin\AppData\Local\Temp\FF8E.tmp\Scream.exe | — | cmd.exe | |||||||||||
User: admin Company: HorrorTrojans Integrity Level: HIGH Exit code: 1073807364 Version: 6.06.0006 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\FF8E.tmp\f11.mp4" | C:\Program Files\VideoLAN\VLC\vlc.exe | cmd.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: HIGH Description: VLC media player Exit code: 1073807364 Version: 3.0.11 Modules
| |||||||||||||||
| 1860 | C:\Windows\system32\cmd.exe /K MrsMjrGuiLauncher.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1073807364 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
16 311
Read events
16 241
Write events
57
Delete events
13
Modification events
| (PID) Process: | (3944) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: c:\blood.bmp | |||
| (PID) Process: | (1492) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop |
| Operation: | write | Name: | NoChangingWallPaper |
Value: 1 | |||
| (PID) Process: | (3304) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (1040) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2624) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (1696) vlc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vlc.exe | |||
| (PID) Process: | (1696) vlc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vlc.exe | |||
| (PID) Process: | (1696) vlc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 817180846 | |||
| (PID) Process: | (2840) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2840) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
11
Suspicious files
2
Text files
16
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | HorrorTrojan6.exe | C:\Users\admin\AppData\Local\Temp\FF8E.tmp\deephaze.mp3 | — | |
MD5:— | SHA256:— | |||
| 2840 | cmd.exe | C:\deephaze.mp3 | — | |
MD5:— | SHA256:— | |||
| 3660 | HorrorTrojan6.exe | C:\Users\admin\AppData\Local\Temp\FF8E.tmp\MrsMjrGuiLauncher.bat | text | |
MD5:539FE923A0AB920FB0E9D1972E3D20B3 | SHA256:CA21A371F16D4D426819B91F22BE1A53E74DB5C154059DEBC11CD05CD0E9703F | |||
| 2840 | cmd.exe | C:\blood.bmp | image | |
MD5:791971D5FF9CB22B491194D3B743CEA9 | SHA256:BBB1BFF656AE882AD39606EDF38FF7693CE884BE1CFCCCF894769DE43685BC67 | |||
| 3660 | HorrorTrojan6.exe | C:\Users\admin\AppData\Local\Temp\FF8E.tmp\musicplayer2.vbs | text | |
MD5:4CD6EA340444F2C259FCCC0E14598FCD | SHA256:F10B0178B85A421CDCD1E87B12264294C6770064C3A12E9928186AC77F10FBDA | |||
| 2840 | cmd.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\Scream.exe | executable | |
MD5:A674B637ACB2103EE505318E79FACA4E | SHA256:4D0E3EB3955B1334F70AE9C71E7E9F338660570048F01633AAE0403AAE3791A6 | |||
| 3660 | HorrorTrojan6.exe | C:\Users\admin\AppData\Local\Temp\FF8E.tmp\blood.bmp | image | |
MD5:791971D5FF9CB22B491194D3B743CEA9 | SHA256:BBB1BFF656AE882AD39606EDF38FF7693CE884BE1CFCCCF894769DE43685BC67 | |||
| 2840 | cmd.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\f11.mp4 | m4v | |
MD5:17042B9E5FC04A571311CD484F17B9EB | SHA256:A9B0F1F849E0B41924F5E80B0C4948E63FC4B4F335BBDF0F997B03A3AFF55424 | |||
| 3660 | HorrorTrojan6.exe | C:\Users\admin\AppData\Local\Temp\FF8E.tmp\MrsMjrGui.exe | executable | |
MD5:450F49426B4519ECAAC8CD04814C03A4 | SHA256:087FCA40E079746B9C1DFAF777D3994C0321EA8F69D08238CDFC02FB109ADD1D | |||
| 2064 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | text | |
MD5:D605705DACB3E5764B232AD484C8304F | SHA256:8B35736956AD042630D6F4A0A17A2AE9FDF6425AD8F8F4CD9EF372428FD6CAEA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1476 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133525159077650000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1128 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1476 | sipnotify.exe | 23.197.138.118:80 | query.prod.cms.rt.microsoft.com | Akamai International B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|