| File name: | Digital_Viewer_3.1.07.exe |
| Full analysis: | https://app.any.run/tasks/25f510dc-d0b7-4e2b-8516-bfa57dc039c9 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2018, 22:02:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 821B37E3F8A9DDB36FF21026651A467B |
| SHA1: | FC0BE6EC62ACE14332E711BD6BBB57D083201338 |
| SHA256: | 32D2967C69D4115BC196AFB6ADE22FA45EC6C49B0CC705265F3DFEF3FFF357CC |
| SSDEEP: | 196608:rIC/C6oEHVQNbvshf0cDVZSSSbr46pEORI+tJEiVPsIypRBEb6c2:rICArNba8cCDbU6pdR7HGHEv2 |
MALICIOUS
Loads dropped or rewritten executable
- Digital_Viewer_3.1.07.exe (PID: 2612)
- Xvid-1.3.3-20141019.exe (PID: 3592)
Changes the autorun value in the registry
- rundll32.exe (PID: 1716)
Application was dropped or rewritten from another process
- SETPRI~1.EXE (PID: 2908)
- Xvid-1.3.3-20141019.exe (PID: 3592)
- setavi32.exe (PID: 3392)
Registers / Runs the DLL via REGSVR32.EXE
- Xvid-1.3.3-20141019.exe (PID: 3592)
SUSPICIOUS
Executable content was dropped or overwritten
- Digital_Viewer_3.1.07.exe (PID: 2612)
- Xvid-1.3.3-20141019.exe (PID: 3592)
- rundll32.exe (PID: 1716)
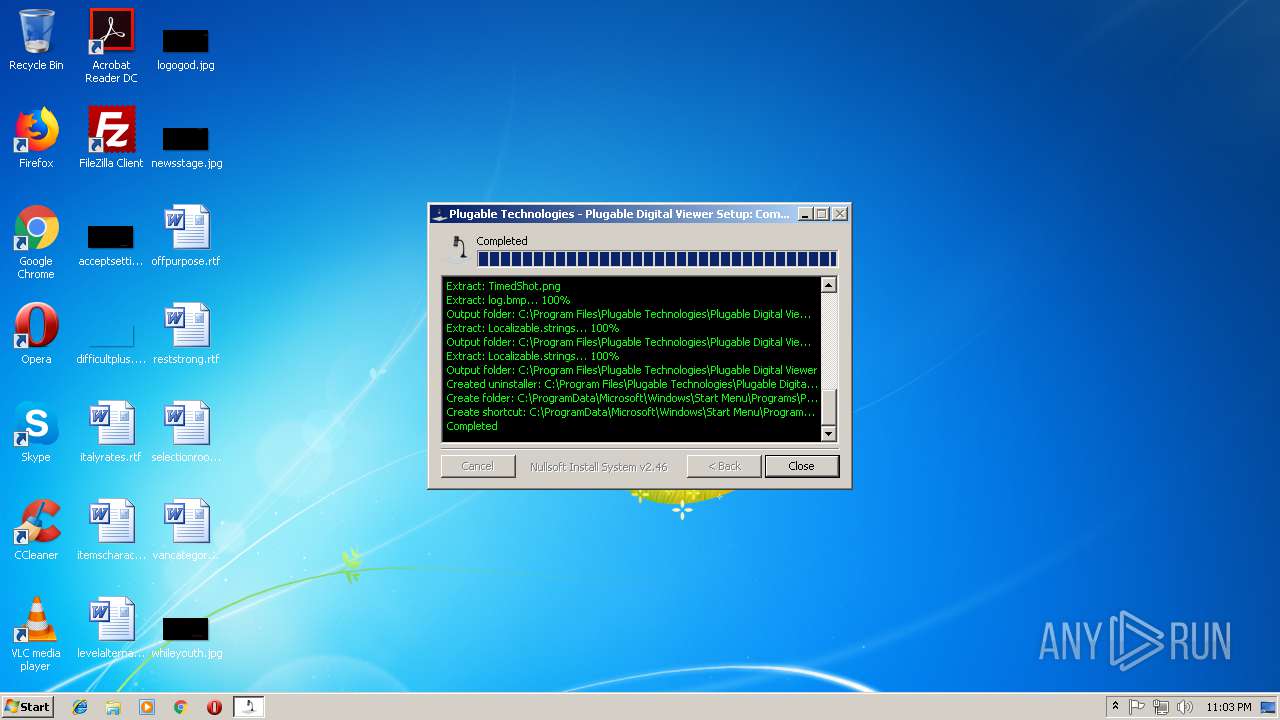
Creates files in the program directory
- Xvid-1.3.3-20141019.exe (PID: 3592)
- Digital_Viewer_3.1.07.exe (PID: 2612)
Creates files in the Windows directory
- rundll32.exe (PID: 1716)
Removes files from Windows directory
- rundll32.exe (PID: 1716)
Creates a software uninstall entry
- Digital_Viewer_3.1.07.exe (PID: 2612)
- Xvid-1.3.3-20141019.exe (PID: 3592)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x0005AEE0 | 0x0005B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.46904 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.68295 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.17025 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 3.40445 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.97665 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.67603 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.76511 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
44
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | "C:\Users\admin\AppData\Local\Temp\Digital_Viewer_3.1.07.exe" | C:\Users\admin\AppData\Local\Temp\Digital_Viewer_3.1.07.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1716 | C:\Windows\System32\rundll32.exe setupapi.dll,InstallHinfSection DefaultInstall 0 C:\Users\admin\AppData\Local\Temp/xvid_x86/xvid.inf | C:\Windows\System32\rundll32.exe | Xvid-1.3.3-20141019.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | C:\Windows\System32\regsvr32.exe /s C:\Windows\system32/xvid.ax | C:\Windows\System32\regsvr32.exe | — | Xvid-1.3.3-20141019.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\Digital_Viewer_3.1.07.exe" | C:\Users\admin\AppData\Local\Temp\Digital_Viewer_3.1.07.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | C:\Users\admin\AppData\Local\Temp\xvid_x86\SETPRI~1.EXE | C:\Users\admin\AppData\Local\Temp\xvid_x86\SETPRI~1.EXE | Xvid-1.3.3-20141019.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3392 | C:\Users\admin\AppData\Local\Temp\xvid_x86\setavi32.exe | C:\Users\admin\AppData\Local\Temp\xvid_x86\setavi32.exe | Xvid-1.3.3-20141019.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
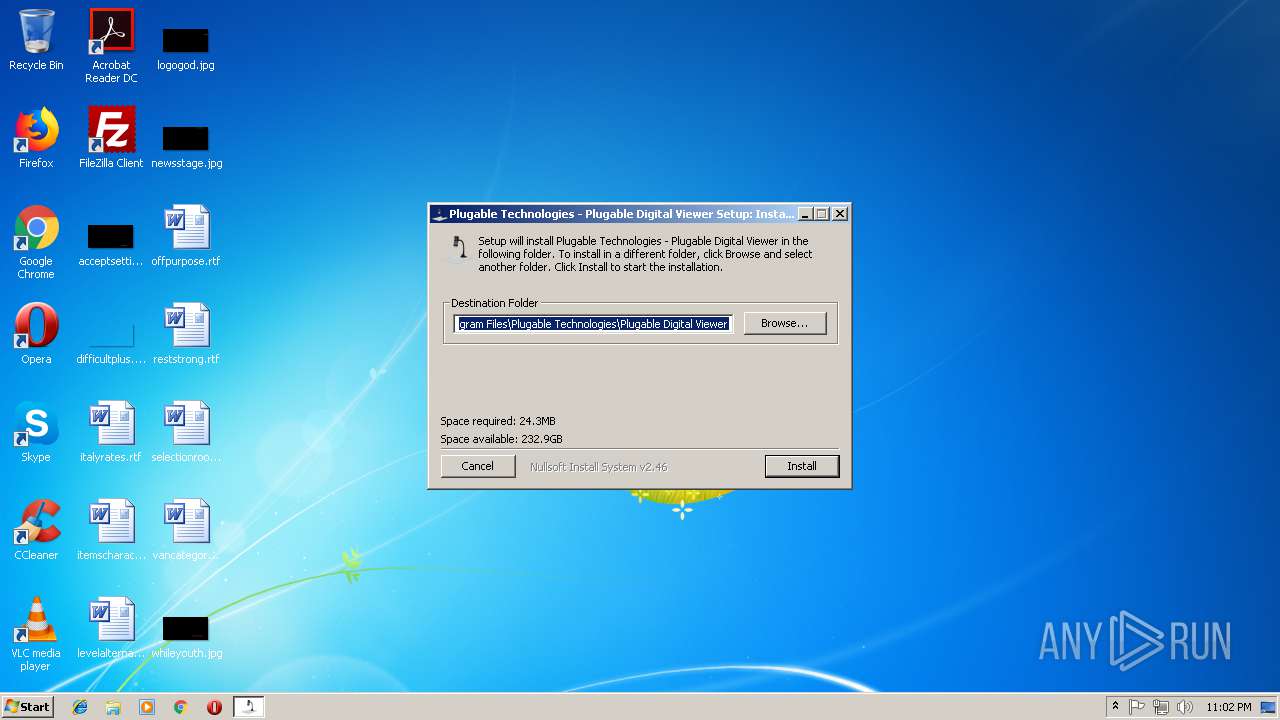
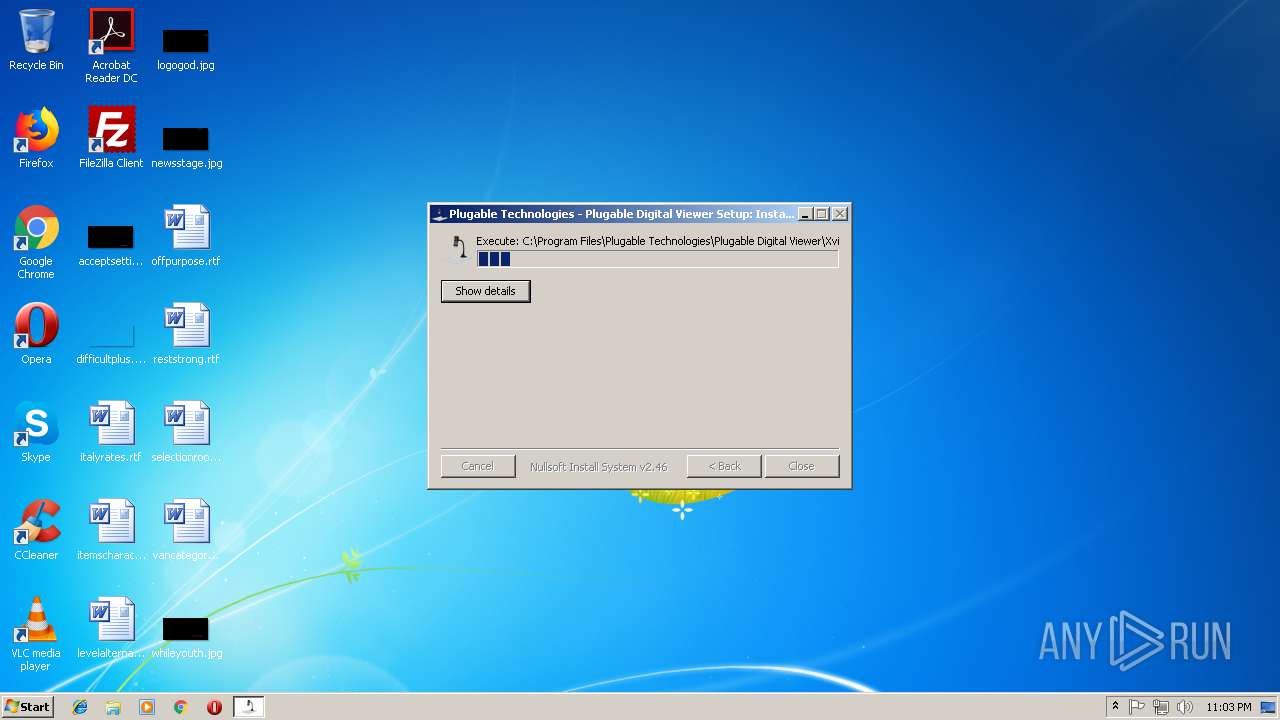
| 3592 | "C:\Program Files\Plugable Technologies\Plugable Digital Viewer\Xvid-1.3.3-20141019.exe" --mode unattended --AutoUpdater no --unattendedmodeui none --decode_divx no --decode_3ivx no --decode_other no | C:\Program Files\Plugable Technologies\Plugable Digital Viewer\Xvid-1.3.3-20141019.exe | Digital_Viewer_3.1.07.exe | ||||||||||||
User: admin Company: Xvid Team Integrity Level: HIGH Exit code: 0 Version: 1.3.3.0 Modules
| |||||||||||||||
| 3644 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
622
Read events
558
Write events
59
Delete events
5
Modification events
| (PID) Process: | (3592) Xvid-1.3.3-20141019.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | BitRock |
Value: 1 | |||
| (PID) Process: | (3592) Xvid-1.3.3-20141019.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | delete value | Name: | BitRock |
Value: 1 | |||
| (PID) Process: | (2896) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (2896) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2896) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1716) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (1716) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\drivers.desc |
| Operation: | write | Name: | xvidvfw.dll |
Value: Xvid MPEG-4 Video Codec | |||
| (PID) Process: | (1716) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Drivers32 |
| Operation: | write | Name: | vidc.XVID |
Value: xvidvfw.dll | |||
| (PID) Process: | (1716) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | GrpConv |
Value: grpconv -o | |||
| (PID) Process: | (1716) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 52 | |||
Executable files
35
Suspicious files
6
Text files
28
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3592 | Xvid-1.3.3-20141019.exe | C:\Users\admin\AppData\Local\Temp\be29e7f1-71ae-4703-50cb-1d52be512f51\twapi-be29e7f1-71ae-4703-50cb-1d52be512f51.dll | executable | |
MD5:A210F1AC135E5331C314CE5F394FB5A5 | SHA256:65B32EA2982078FB9A18E88FEEC238CB76ED2AE6C2BB4DDB0F6A9C4F57B1D62B | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Users\admin\AppData\Local\Temp\BR46B3.tmp | executable | |
MD5:B4EB1E7438DC099078CE8FE6E5A2C99D | SHA256:F9AB62A357A9D964CEE9E078EF5C6A66D3AFE9B27C57D01D8B4FE1D7930C630B | |||
| 2612 | Digital_Viewer_3.1.07.exe | C:\Users\admin\AppData\Local\Temp\nsy20D7.tmp\UserInfo.dll | executable | |
MD5:7579ADE7AE1747A31960A228CE02E666 | SHA256:564C80DEC62D76C53497C40094DB360FF8A36E0DC1BDA8383D0F9583138997F5 | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Program Files\Xvid\MiniConvert.exe | executable | |
MD5:A40C3DB74E5FE589863DCB9158962DEE | SHA256:69865C71A865E4E4CDA721D7CF22D6E792137643125437D2E3BE4DA8FB52B849 | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Program Files\Xvid\xvid.ico | image | |
MD5:231017665B6869CB6762B09E15F1A8ED | SHA256:B5735768B9E283578094EF05A2FEEC921BDCF5230B662D0F21956470D190DC0E | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Users\admin\AppData\Local\Temp\BR4327.tmp | executable | |
MD5:027491B39A7B16B116E780F55ABC288E | SHA256:EEF69D005BF1C0B715C8D6205400D4755C261DD38DDFBBFE918E6EE91F21F1F0 | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Users\admin\AppData\Local\Temp\BR4326.tmp | executable | |
MD5:D33EE6D856350F321189138134745388 | SHA256:9EB5405449BE0D43FEE145B5B6D5FE01799C6F635389A44F58A0AF2793A1B737 | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Program Files\Xvid\OGMCalc.exe | executable | |
MD5:95CAEF9DA6E9AEE1ECD627527CFA0F38 | SHA256:422CCA5E2E3C51E39DC0C6279306EEB68FC261C2EA6E677D38FA5F376176B2E0 | |||
| 2612 | Digital_Viewer_3.1.07.exe | C:\Program Files\Plugable Technologies\Plugable Digital Viewer\Xvid-1.3.3-20141019.exe | executable | |
MD5:542BB1E4393255C16F03583727320812 | SHA256:23ACF6354A07C28DF537144BF9290586C4A9FFB3A373142CC5FC66D3BE9AF39D | |||
| 3592 | Xvid-1.3.3-20141019.exe | C:\Program Files\Xvid\AviC.exe | executable | |
MD5:C39AD6299E0E1F7AA3F5B51AC9B5CD0E | SHA256:8DC1D99199D4A85A852E245B81DBCB82CC14E2DF58AFB3C30A537FABA8C1C756 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
SETPRI~1.EXE | Successfully changed DACL
|
SETPRI~1.EXE | Successfully changed DACL
|
setavi32.exe | Successfully changed DACL
|