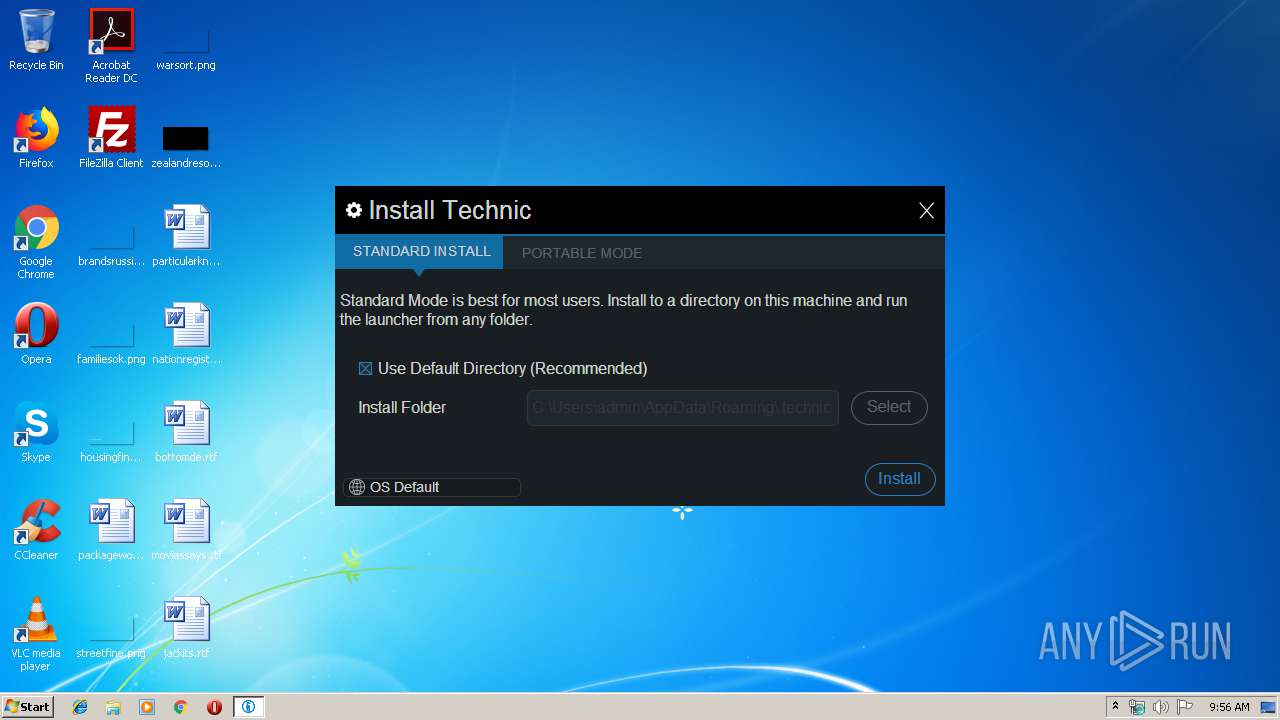
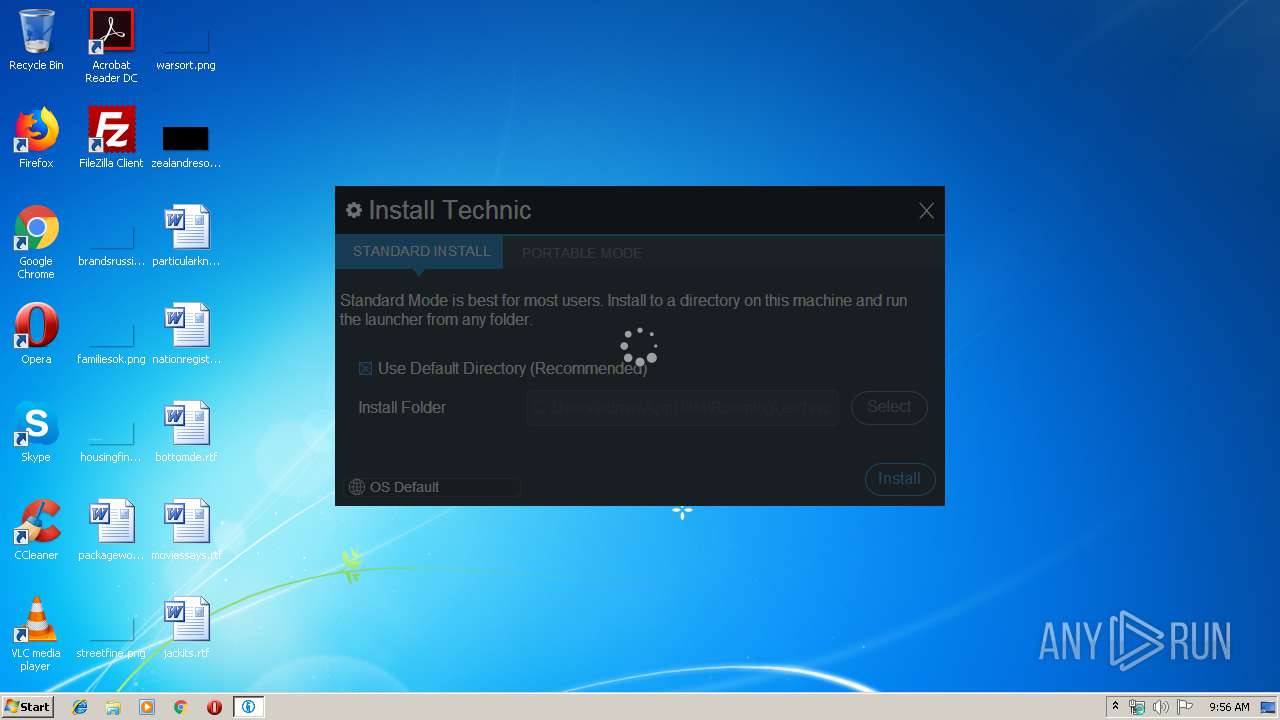
| File name: | TechnicLauncher.exe |
| Full analysis: | https://app.any.run/tasks/f9bfceb8-8dd0-4428-a572-f8f7fea7c5e0 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 08:56:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 40A33D3F104EAFFCEFE03D93CED526AD |
| SHA1: | B5C94F19DD5FE71EB85C6AD8AB25D9FA5AF8928F |
| SHA256: | 32A96AA5E51E058B2A1A4B7BA25D8989C11109D06B84A5C6AD714ADD3176A258 |
| SSDEEP: | 98304:kVRrLJmFxcTdrbC4aaRVID/+QT4xeN8mCzx/:kVRZxTJm4aQ+D/EG8mCzx/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Check for Java to be installed
- reg.exe (PID: 2872)
- reg.exe (PID: 4084)
Creates files in the user directory
- javaw.exe (PID: 3988)
- javaw.exe (PID: 3224)
Executes JAVA applets
- TechnicLauncher.exe (PID: 2744)
- TechnicLauncher.exe (PID: 3284)
- javaw.exe (PID: 3224)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3224)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:08:23 13:25:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.26 |
| CodeSize: | 19968 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.450 |
| ProductVersionNumber: | 4.0.0.450 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | Technic Launcher |
| FileVersion: | 4.0.0.450 |
| InternalName: | launcher |
| LegalCopyright: | Syndicate, LLC, https://www.technicpack.net |
| LegalTrademarks: | - |
| OriginalFileName: | launcher.exe |
| ProductName: | Technic Launcher |
| ProductVersion: | 4.0.0.450 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Aug-2019 11:25:32 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | Technic Launcher |
| FileVersion: | 4.0.0.450 |
| InternalName: | launcher |
| LegalCopyright: | Syndicate, LLC, https://www.technicpack.net |
| LegalTrademarks: | - |
| OriginalFilename: | launcher.exe |
| ProductName: | Technic Launcher |
| ProductVersion: | 4.0.0.450 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 23-Aug-2019 11:25:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03203 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x000086A0 | 0x00008800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.37783 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34111 | 796 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
4 | 2.84454 | 16936 | UNKNOWN | Process Default Language | RT_ICON |
12 | 4.66037 | 86 | UNKNOWN | Process Default Language | RT_RCDATA |
15 | 3.75506 | 38 | UNKNOWN | Process Default Language | RT_RCDATA |
16 | 2.9477 | 9 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
51
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2324 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2744 | C:\Users\admin\AppData\Local\Temp\TechnicLauncher.exe | C:\Users\admin\AppData\Local\Temp\TechnicLauncher.exe | — | javaw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Technic Launcher Exit code: 0 Version: 4.0.0.450 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2872 | reg query HKEY_LOCAL_MACHINE\Software\JavaSoft\ /f Home /t REG_SZ /s /reg:32 | C:\Windows\system32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Djava.net.preferIPv4Stack=true -Dawt.useSystemAAFontSettings=lcd -Dswing.aatext=true -classpath "C:\Users\admin\AppData\Local\Temp\TechnicLauncher.exe;anything" net.technicpack.launcher.LauncherMain | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | TechnicLauncher.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3284 | "C:\Users\admin\AppData\Local\Temp\TechnicLauncher.exe" | C:\Users\admin\AppData\Local\Temp\TechnicLauncher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Technic Launcher Exit code: 0 Version: 4.0.0.450 Modules
| |||||||||||||||
| 3592 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
65
Read events
63
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3988) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3224) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
1
Text files
28
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5164537452598287479.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio450314106292332640.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio4478663264253016772.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3727824232492642283.tmp | — | |
MD5:— | SHA256:— | |||
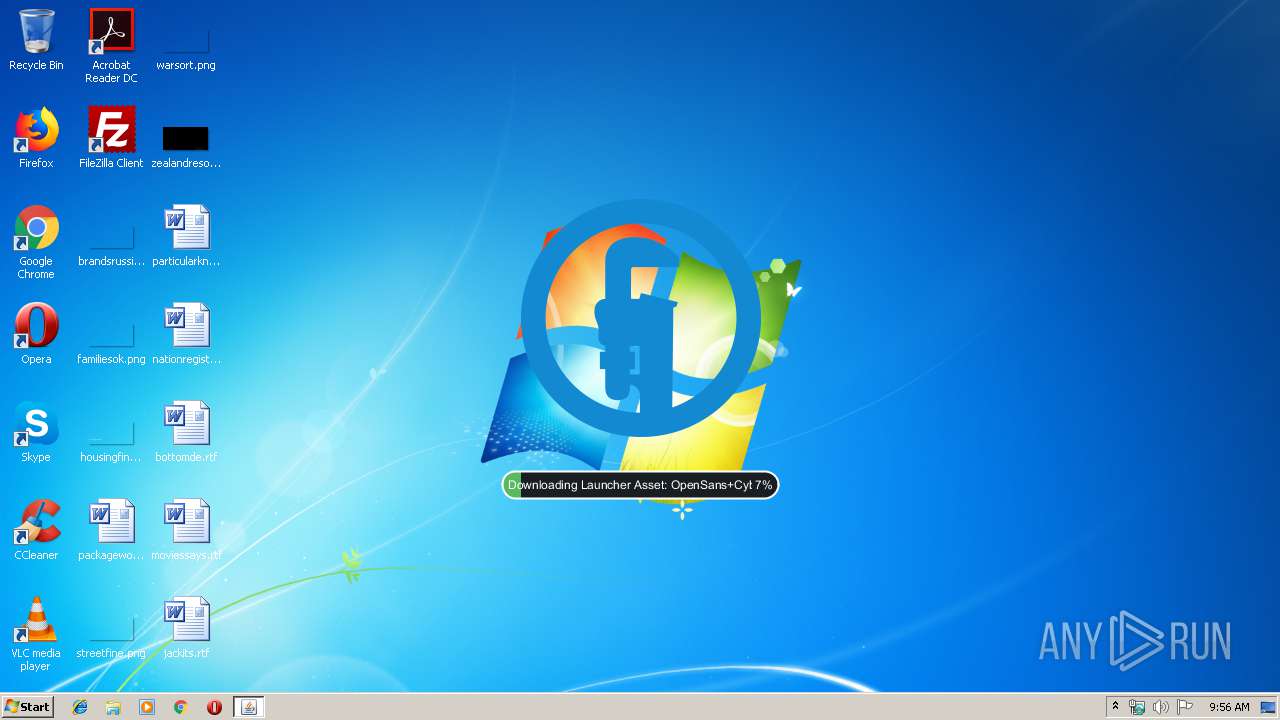
| 3224 | javaw.exe | C:\Users\admin\AppData\Roaming\.technic\assets\launcher\OpenSans+Cyberbit.ttf | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Roaming\.technic\assets\launcher\Raleway+FireflySung.ttf | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5579952649959190669.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio7987059379723364972.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio7186103383203424524.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio8037507404914152987.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
8
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | javaw.exe | GET | 200 | 75.126.196.169:80 | http://launcher.technicpack.net/resources/OpenSans+Cyberbit.ttf | US | ttf | 12.9 Mb | suspicious |
3224 | javaw.exe | GET | 200 | 104.25.34.11:80 | http://api.technicpack.net/launcher/version/stable4 | US | text | 701 b | suspicious |
3224 | javaw.exe | GET | 200 | 75.126.196.169:80 | http://launcher.technicpack.net/resources/Raleway+FireflySung.ttf | US | ttf | 12.1 Mb | suspicious |
3224 | javaw.exe | GET | 200 | 104.25.34.11:80 | http://api.technicpack.net/news?build=450 | US | html | 43.2 Kb | suspicious |
3224 | javaw.exe | GET | 200 | 104.25.34.11:80 | http://api.technicpack.net/news?build=450 | US | html | 43.2 Kb | suspicious |
3224 | javaw.exe | GET | 200 | 172.217.21.234:80 | http://fonts.googleapis.com/css?family=Raleway:400,300,100|Open+Sans:400,700 | US | text | 1.14 Kb | whitelisted |
3224 | javaw.exe | GET | 200 | 75.126.196.169:80 | http://mirror.technicpack.net/resources/aether-dep.jar | US | compressed | 2.66 Mb | suspicious |
3224 | javaw.exe | GET | 200 | 104.25.34.11:80 | http://api.technicpack.net/discover/ | US | html | 2.81 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3988 | javaw.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3224 | javaw.exe | 104.25.34.11:80 | api.technicpack.net | Cloudflare Inc | US | shared |
3224 | javaw.exe | 75.126.196.169:80 | launcher.technicpack.net | SoftLayer Technologies Inc. | US | suspicious |
3224 | javaw.exe | 192.0.73.2:443 | www.gravatar.com | Automattic, Inc | US | whitelisted |
3224 | javaw.exe | 104.25.34.11:443 | api.technicpack.net | Cloudflare Inc | US | shared |
3224 | javaw.exe | 172.217.21.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3224 | javaw.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
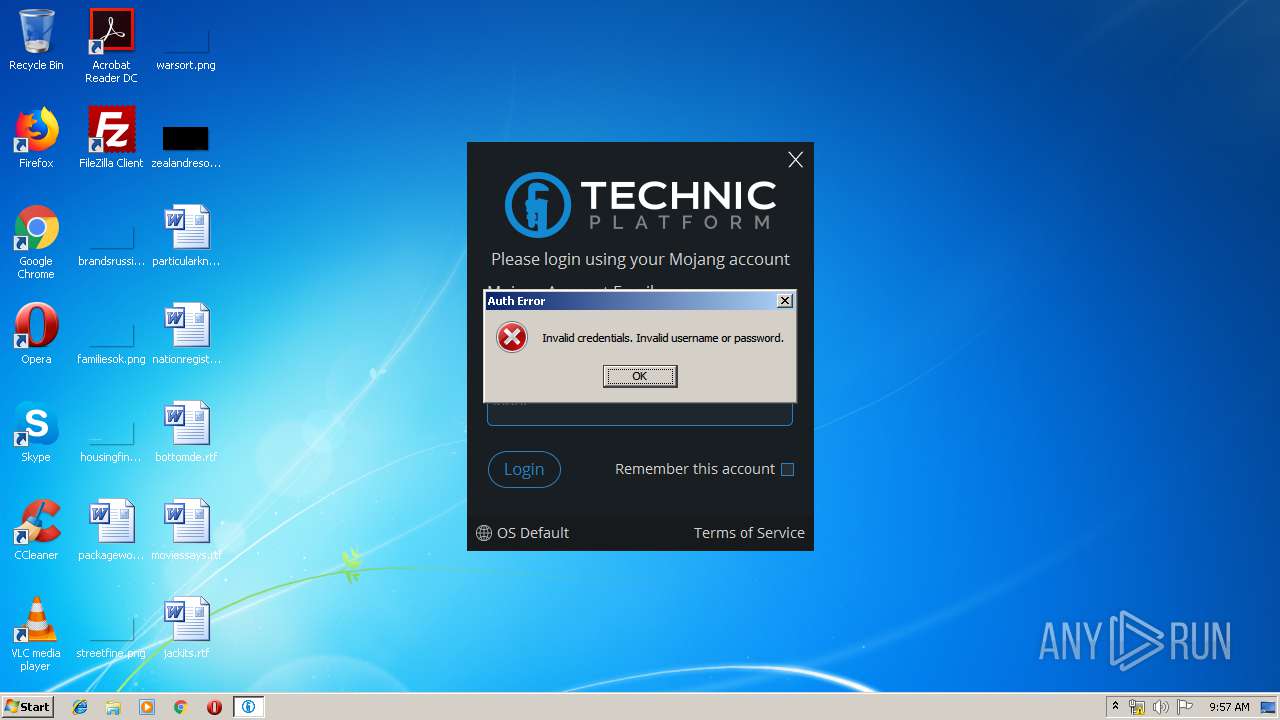
3224 | javaw.exe | 13.224.187.68:443 | authserver.mojang.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
api.technicpack.net |
| suspicious |
launcher.technicpack.net |
| suspicious |
mirror.technicpack.net |
| suspicious |
www.gravatar.com |
| whitelisted |
www.technicpack.net |
| suspicious |
fonts.googleapis.com |
| whitelisted |
authserver.mojang.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3224 | javaw.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |