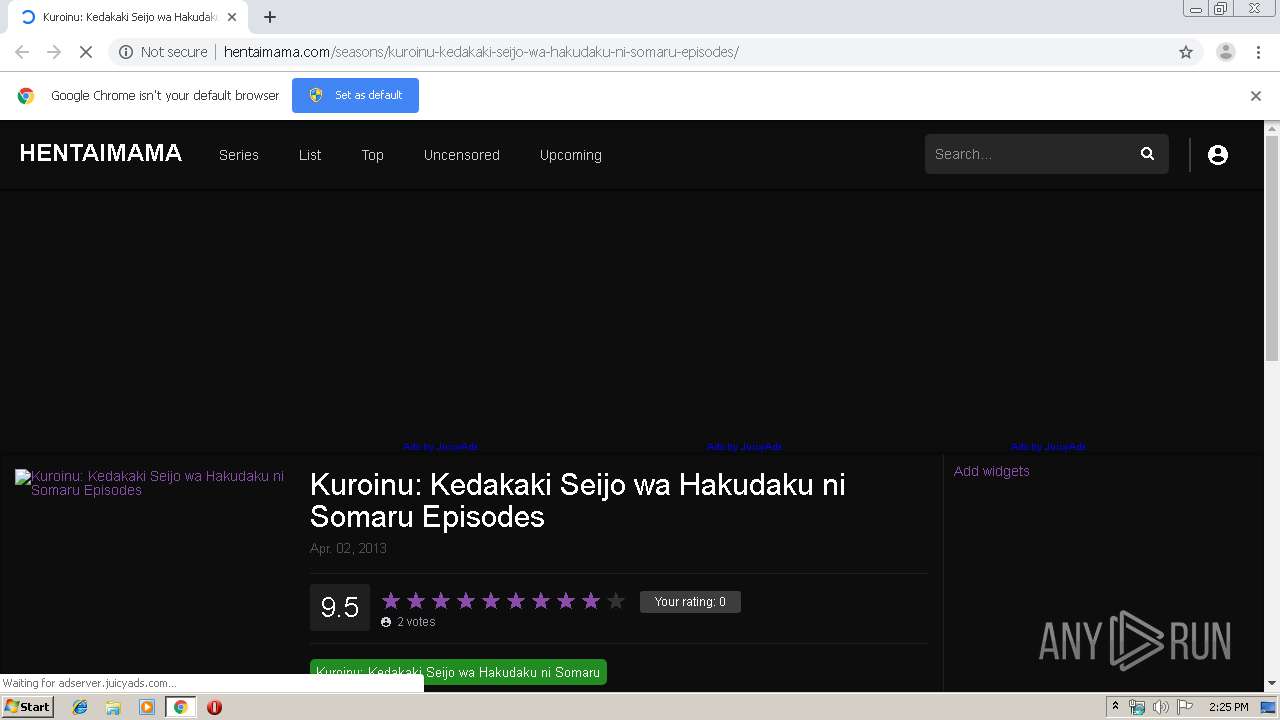
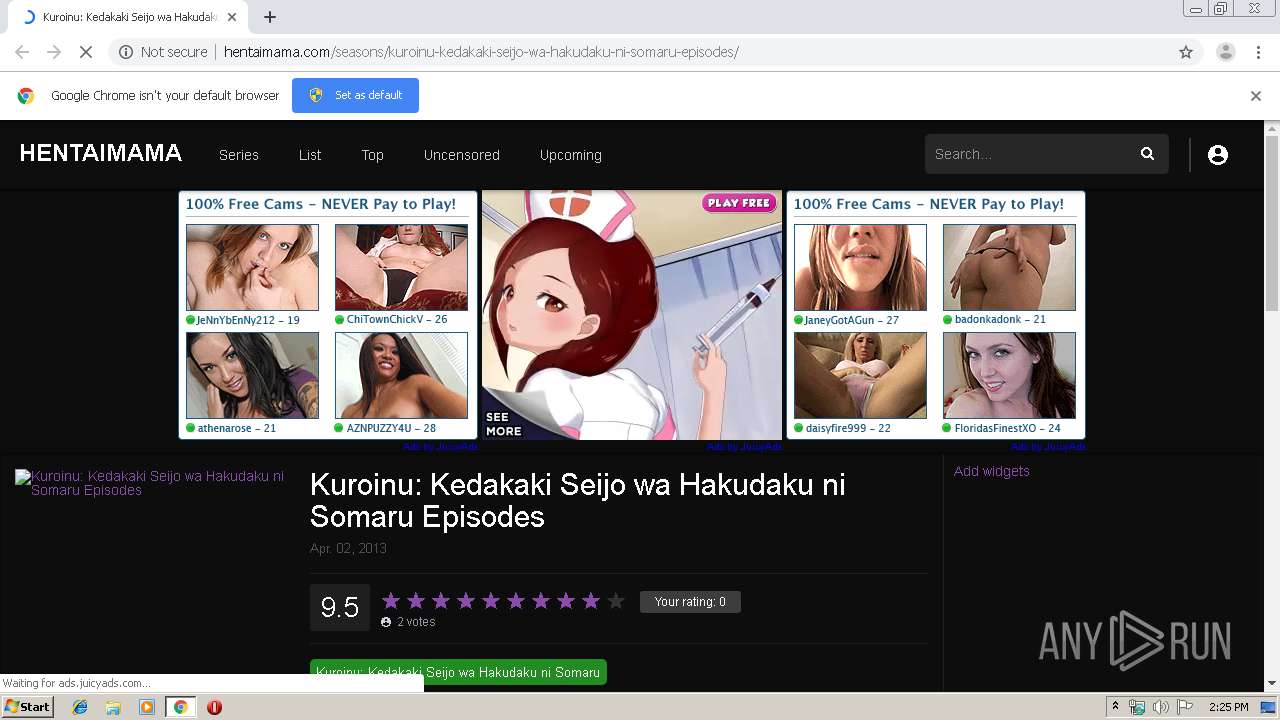
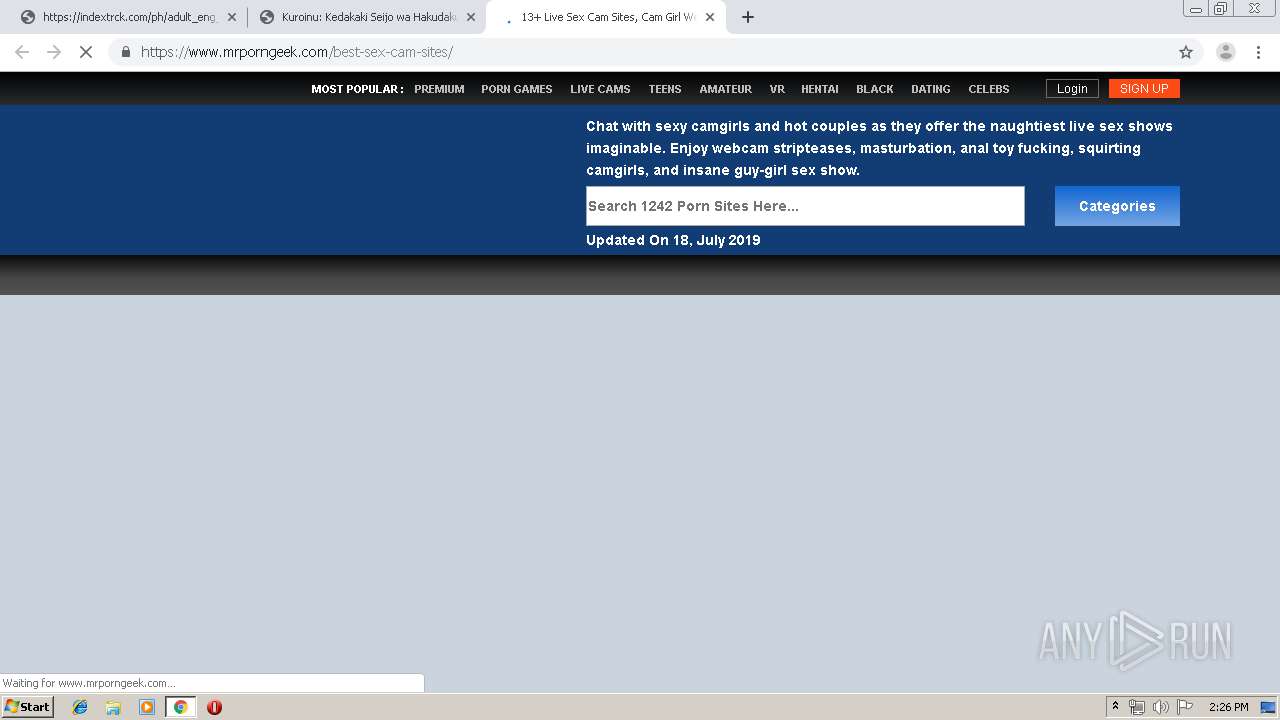
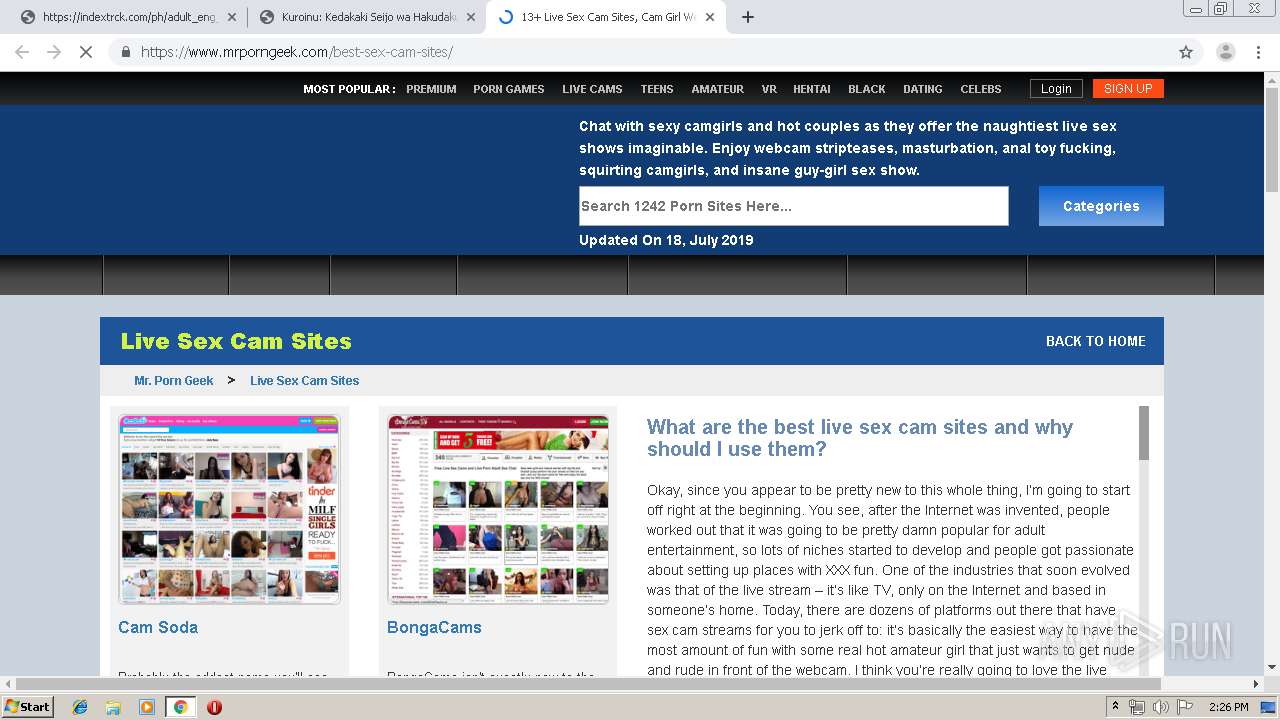
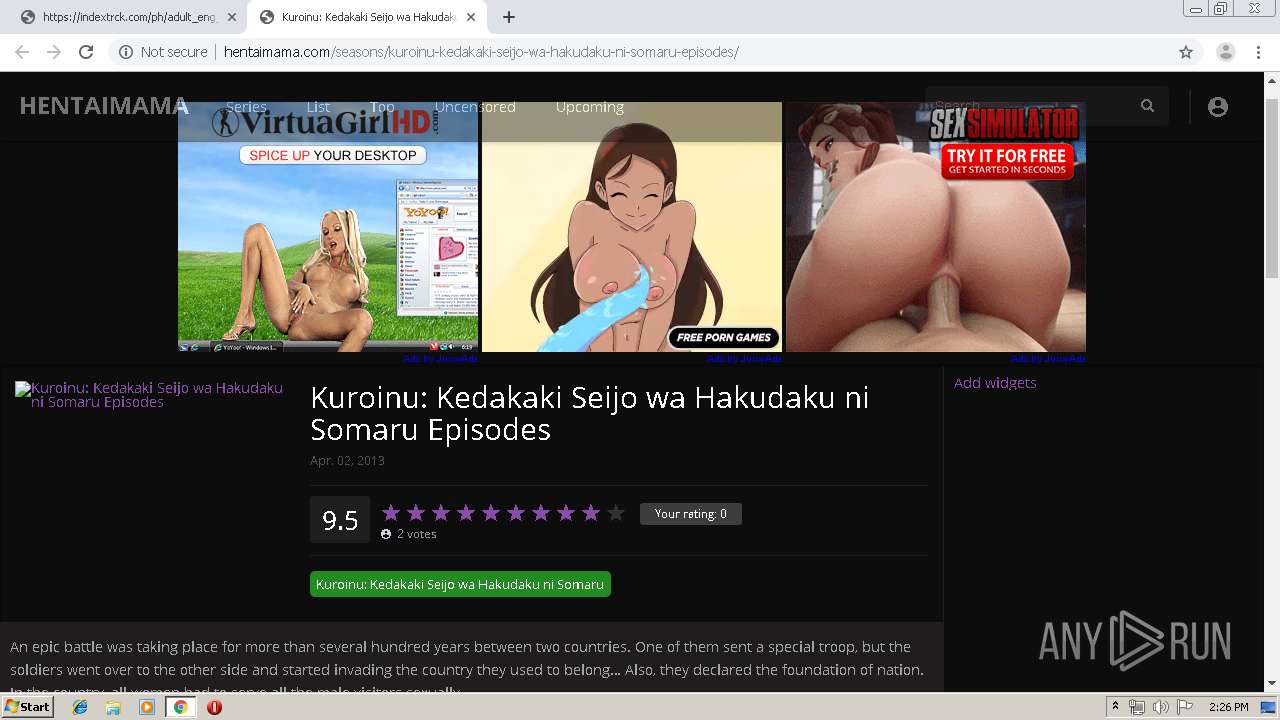
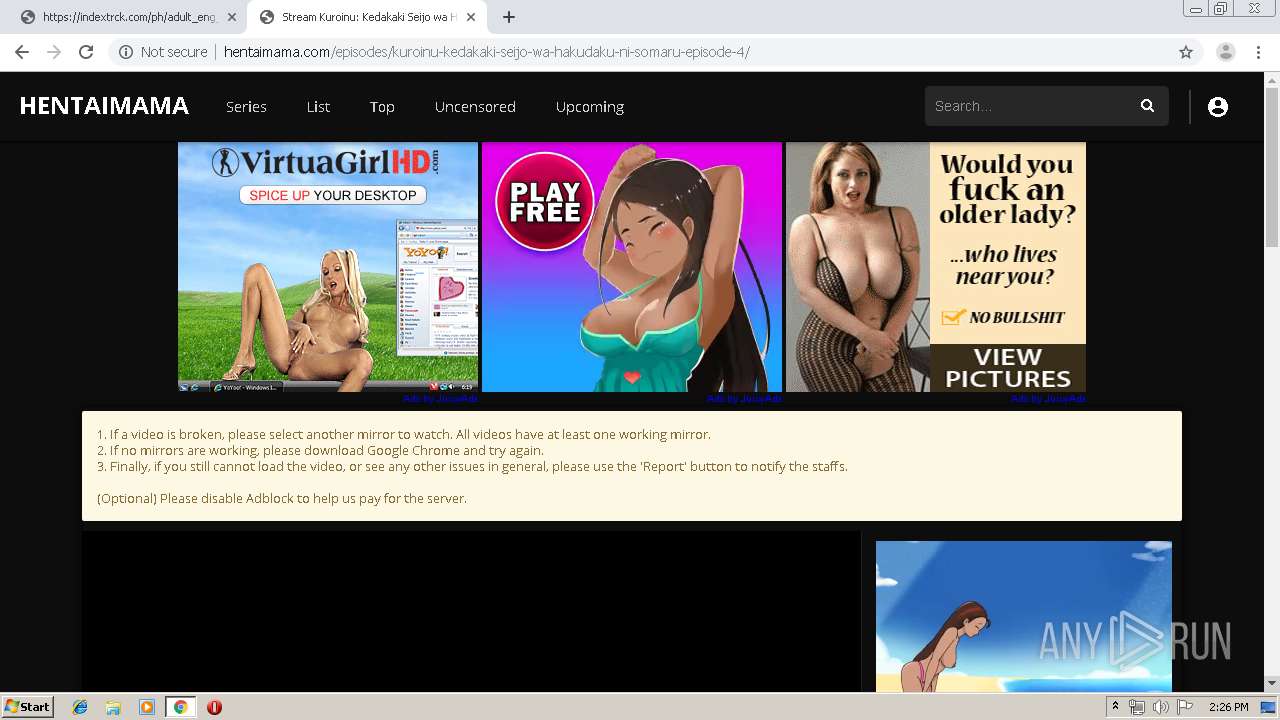
| URL: | http://hentaimama.com/seasons/kuroinu-kedakaki-seijo-wa-hakudaku-ni-somaru-episodes/ |
| Full analysis: | https://app.any.run/tasks/6c514aa7-640c-4763-8bc6-476b10e068d0 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 13:25:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4678AFACE7AAE92EEC9BD7494FCAE041 |
| SHA1: | A0446F3F01538E8734F0F6A5583F09A06C577197 |
| SHA256: | 32A4E448709FADE8E8215511126249C8AADADE21958D78A105C17A864DC6CC39 |
| SSDEEP: | 3:N1KWAllN3HEWJCK8OABE0s2gJnCIaEymWKM:CWetJ8O1UgJCXVcM |
MALICIOUS
No malicious indicators.SUSPICIOUS
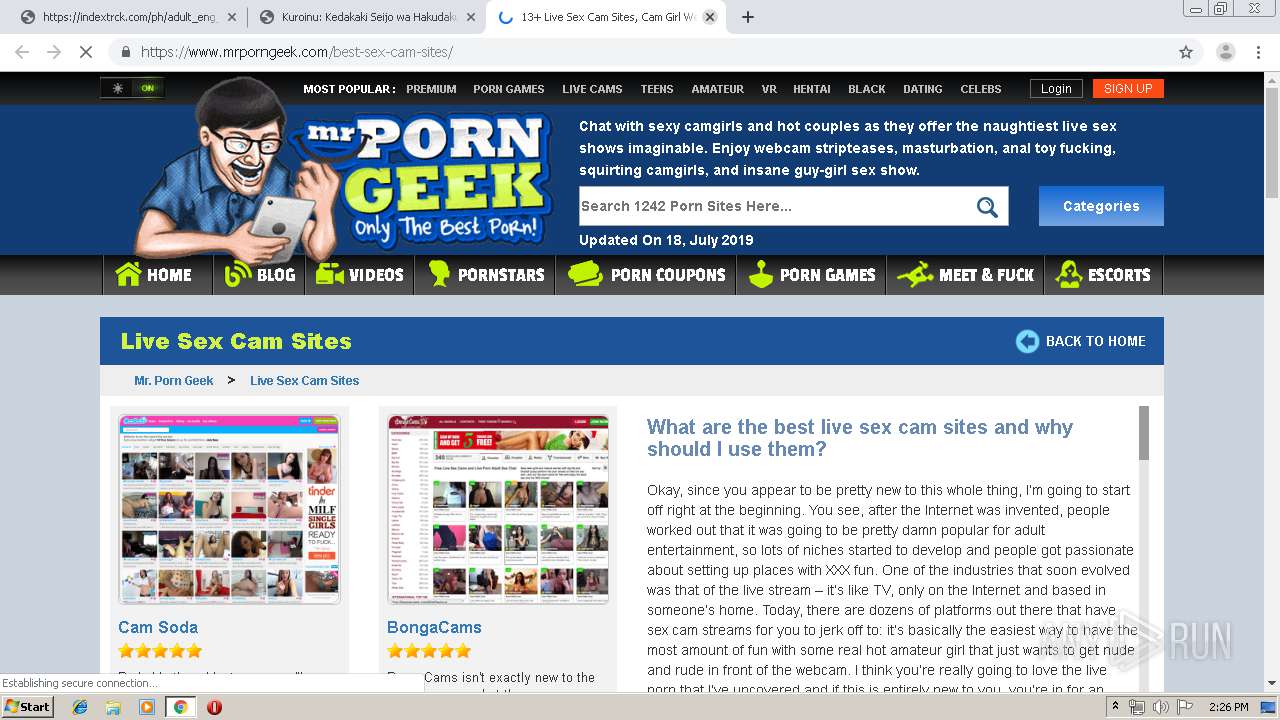
Modifies files in Chrome extension folder
- chrome.exe (PID: 2896)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 396)
Application launched itself
- chrome.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7532055610834368170 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3657428834988071264 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3746213530148131674 --mojo-platform-channel-handle=3680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2183554963820035138 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2026860071380066463 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13638013479066405201 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3115482184489655155 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=194654200388266167 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4292975776019780693 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,5968936814125096855,6652012705170661122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3090246801616829554 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
696
Read events
595
Write events
97
Delete events
4
Modification events
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2896-13207929925674375 |
Value: 259 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
208
Text files
314
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eb16209f-77ea-4127-9419-8cd61bca935f.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17a7d8.TMP | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF17a846.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
147
TCP/UDP connections
191
DNS requests
73
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/jquery.multiselect.css?ver=2.1 | US | text | 818 b | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/icons.21.css?ver=2.1 | US | text | 1.44 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/seasons/kuroinu-kedakaki-seijo-wa-hakudaku-ni-somaru-episodes/ | US | html | 10.6 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 94.31.29.128:80 | http://cdn.popcash.net/pop.js | GB | text | 27.7 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/scrollbar.21.css?ver=2.1 | US | text | 1.24 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/dark.21.css?ver=2.1 | US | text | 7.18 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/main.21.css?ver=2.111 | US | text | 15.8 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/gallery.21.css?ver=2.1 | US | text | 1.12 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/css/responsive.21.css?ver=2.13 | US | text | 1.96 Kb | whitelisted |
396 | chrome.exe | GET | 200 | 104.27.168.79:80 | http://hentaimama.com/wp-content/themes/dooplay/assets/js/jquery.multiselect.js?ver=2.1 | US | text | 6.93 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
396 | chrome.exe | 104.27.168.79:80 | hentaimama.com | Cloudflare Inc | US | shared |
396 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
396 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
396 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
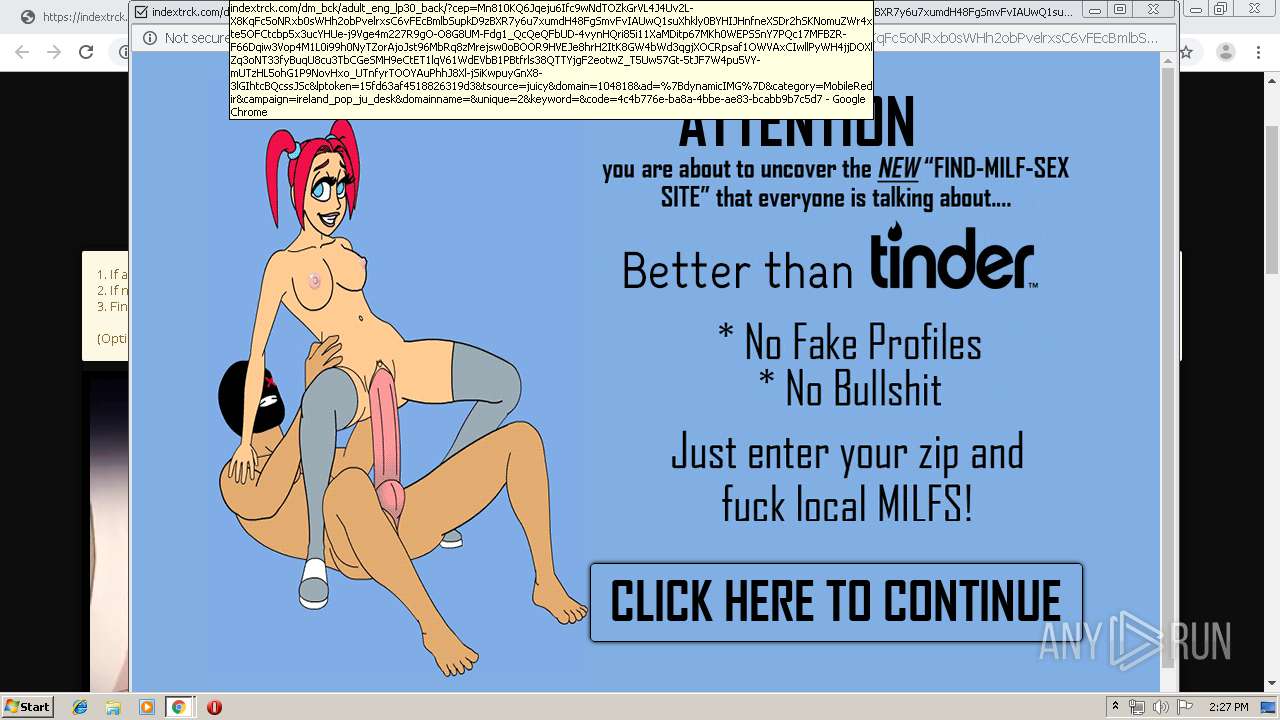
396 | chrome.exe | 94.31.29.128:80 | cdn.popcash.net | netDNA | GB | malicious |
396 | chrome.exe | 151.139.128.10:443 | js.juicyads.com | Highwinds Network Group, Inc. | US | malicious |
396 | chrome.exe | 99.192.193.3:80 | adserver.juicyads.com | MOJOHOST | US | unknown |
396 | chrome.exe | 104.16.57.155:443 | image.tmdb.org | Cloudflare Inc | US | shared |
396 | chrome.exe | 151.139.128.10:80 | js.juicyads.com | Highwinds Network Group, Inc. | US | malicious |
396 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
hentaimama.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
js.juicyads.com |
| whitelisted |
cdn.popcash.net |
| whitelisted |
adserver.juicyads.com |
| suspicious |
image.tmdb.org |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
396 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
396 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
396 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
396 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
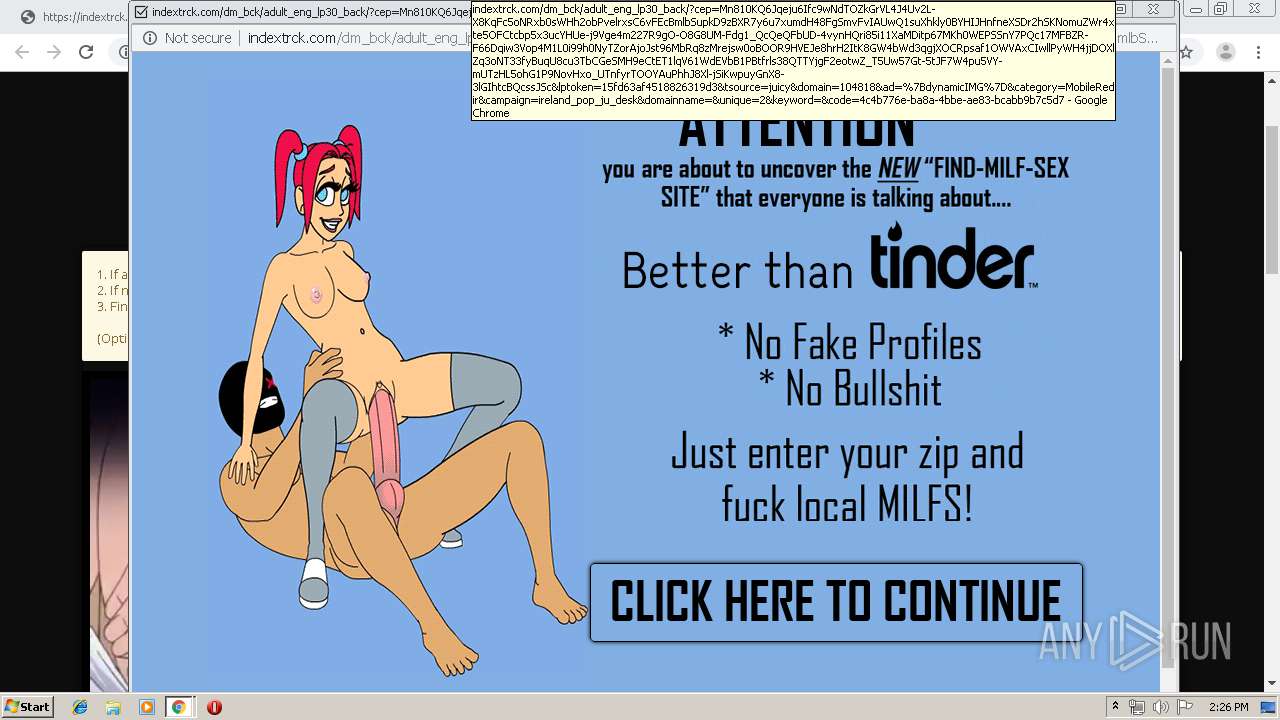
396 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - request in.cgi |
396 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS TDS Sutra - HTTP header redirecting to a SutraTDS |