| File name: | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader |
| Full analysis: | https://app.any.run/tasks/74758dff-e167-4074-bac6-61f687ba6c8f |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 02:26:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 09662EA83E8C5896452A70BF1D537FA5 |
| SHA1: | 5D3D368CAFED93A6949C397C0F946A9C664B9310 |
| SHA256: | 32A0A17A354982238108485424AADF0BADD83DD98990763FF524779D2B9F32FA |
| SSDEEP: | 98304:iefUuZuKAuf5jTFPkOefUuZuKAuf5jTFziy9/W10abzzpQXPJP0jjiGHaGx/LOLs:JySbzzdr0ijelYl |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
- UpdatAuto.exe (PID: 7828)
Starts a Microsoft application from unusual location
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7532)
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
Starts itself from another location
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
Executing commands from a ".bat" file
- UpdatAuto.exe (PID: 7828)
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
Starts CMD.EXE for commands execution
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
- UpdatAuto.exe (PID: 7828)
Creates file in the systems drive root
- UpdatAuto.exe (PID: 7828)
Executable content was dropped or overwritten
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
- UpdatAuto.exe (PID: 7828)
INFO
The sample compiled with chinese language support
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 7684)
- UpdatAuto.exe (PID: 7828)
Checks supported languages
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 7992)
Reads the computer name
- 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 7992)
Creates files in the program directory
- UpdatAuto.exe (PID: 7828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (63.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (24.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.1) |
| .exe | | | Win32 Executable (generic) (3.5) |
| .exe | | | Generic Win/DOS Executable (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:12 04:30:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 102400 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dc |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Windows Update Manager for NT |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Update Manager for NT |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| FileVersion: | 6.01 |
| ProductVersion: | 6.01 |
| InternalName: | INCUBUS |
| OriginalFileName: | INCUBUS.exe |
Total processes
140
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7360 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7532 | "C:\Users\admin\Desktop\2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe" | C:\Users\admin\Desktop\2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Manager for NT Exit code: 3221226540 Version: 6.01 Modules
| |||||||||||||||
| 7684 | "C:\Users\admin\Desktop\2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe" | C:\Users\admin\Desktop\2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Manager for NT Version: 6.01 | |||||||||||||||
| 7700 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 7828 | C:\WINDOWS\system32\UpdatAuto.exe | C:\Windows\SysWOW64\UpdatAuto.exe | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Manager for NT Version: 6.01 | |||||||||||||||
| 7844 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | UpdatAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 7852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
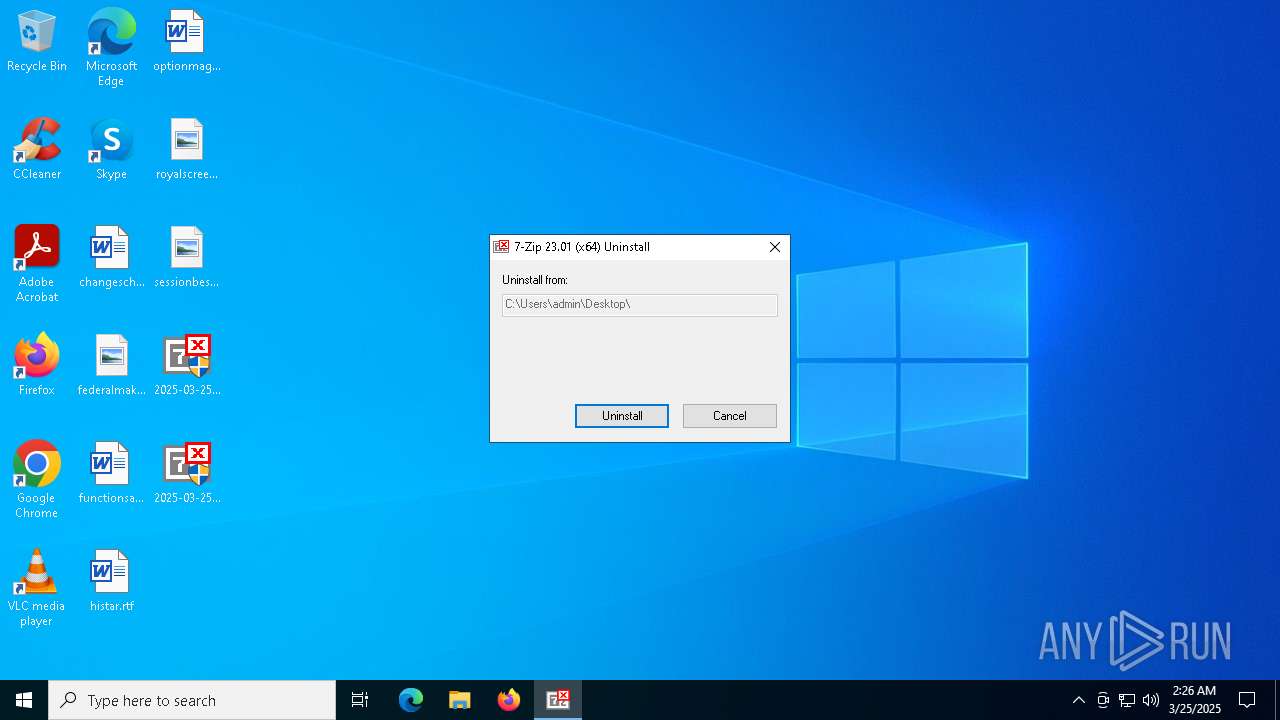
| 7992 | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | C:\Users\admin\Desktop\2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | — | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Uninstaller Version: 23.01 Modules
| |||||||||||||||
Total events
113
Read events
113
Write events
0
Delete events
0
Modification events
Executable files
11
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7828 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRLogTransport.exe | — | |
MD5:— | SHA256:— | |||
| 7828 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRWindowsClientService.exe | — | |
MD5:— | SHA256:— | |||
| 7828 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Eula.exe | — | |
MD5:— | SHA256:— | |||
| 7684 | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\Option.bat | text | |
MD5:1D04ABF39E9DF55EED1D04430CC21EB8 | SHA256:0BC485263CF8A962E64DB0B88F156F2A9AF1B81ECFDB1CF9111D497E85DF70F3 | |||
| 7684 | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\ntldr~6 | executable | |
MD5:7CB5FD1C4B3EA199674575AE237948AC | SHA256:A2116870500C34CB1135EFAB305ABA72AB0738F31B894A1FAC840CF1E10B571D | |||
| 7684 | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\Users\admin\Desktop\2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | executable | |
MD5:1612E7F47EBB6852FE9B8622FAAA24DF | SHA256:029702B79942FB75423C298DF07BF7DF562E8B8F28635D1B7B11AF39907CC1DF | |||
| 7828 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\ADelRCP.exe | executable | |
MD5:7147EC838CFAFBF36419BF4AB0A01B97 | SHA256:17D103CF6A6C1355E56FD5A081B4FA584AD0E9F071D805A8859930D49AF62FB1 | |||
| 7684 | 2025-03-25_09662ea83e8c5896452a70bf1d537fa5_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\ntldr~8 | executable | |
MD5:7CB5FD1C4B3EA199674575AE237948AC | SHA256:A2116870500C34CB1135EFAB305ABA72AB0738F31B894A1FAC840CF1E10B571D | |||
| 7828 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcrobatInfo.exe | executable | |
MD5:2B3D7D9F74DE650086763B2BF3CCDC74 | SHA256:DF420FB544B426961829CA812E7FC5612266144E7CA00067BB49B0DDACBDF1ED | |||
| 7828 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat_sl.exe | executable | |
MD5:92979CE227CDC12EF47D705A94E189C1 | SHA256:8E81977ED3D62987B4E1B4A7132715FB5D3CFF36C23C973A458FE3EF2E1FD1E4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
59
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
8188 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4628 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |