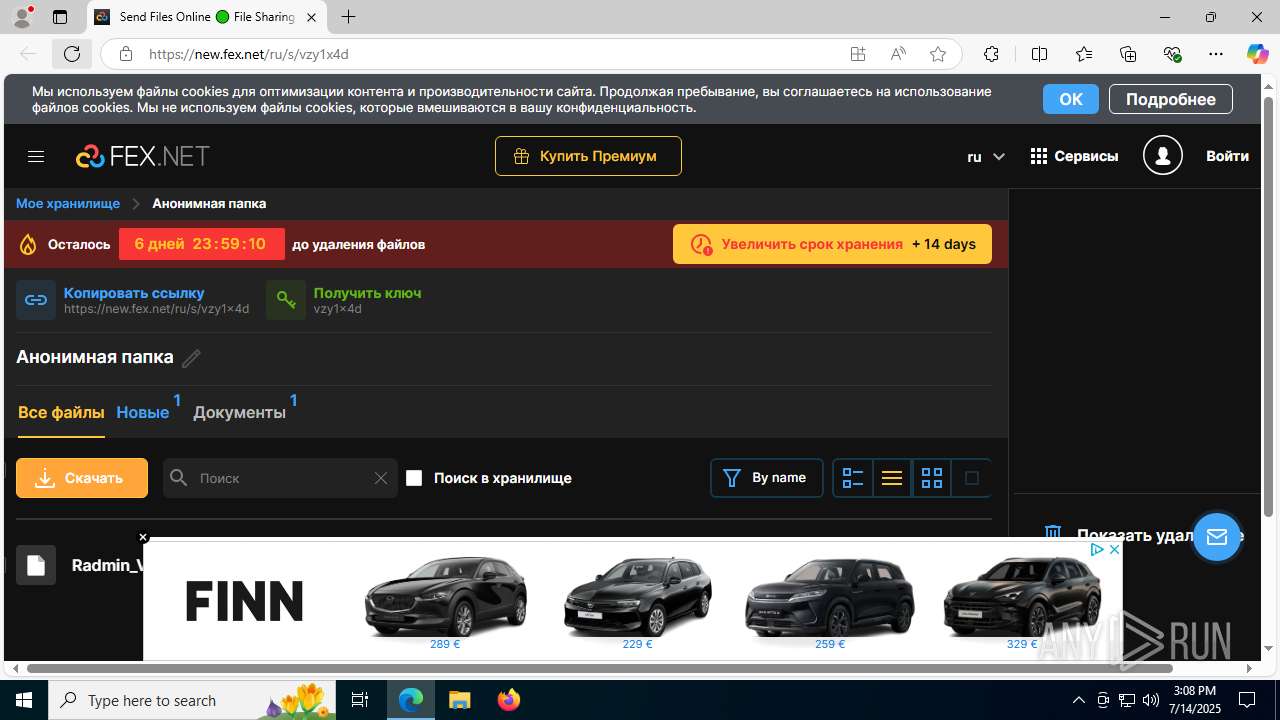
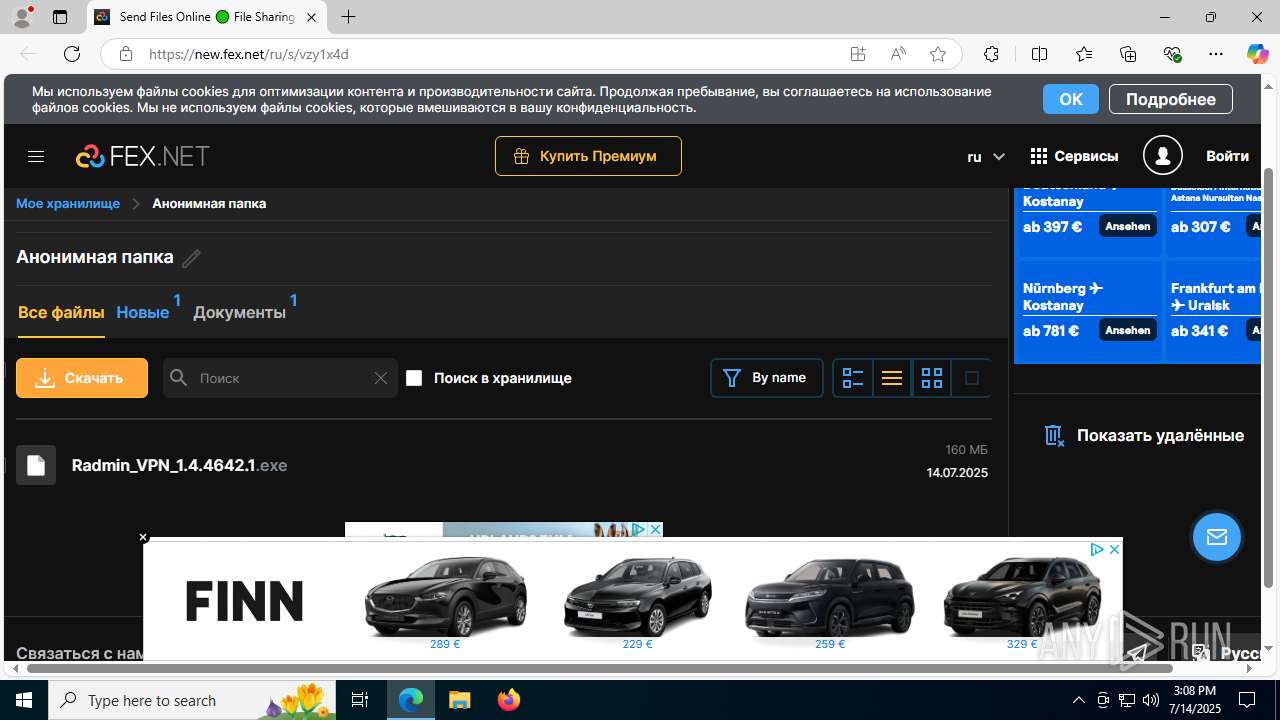
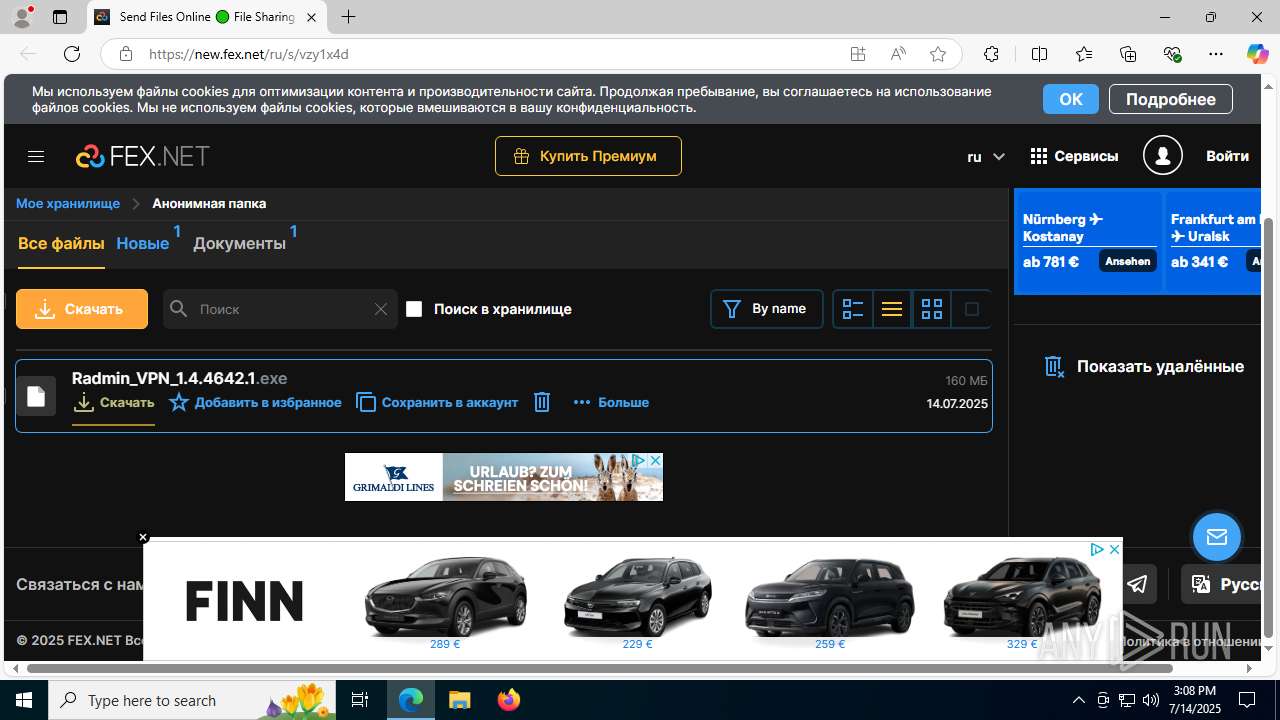
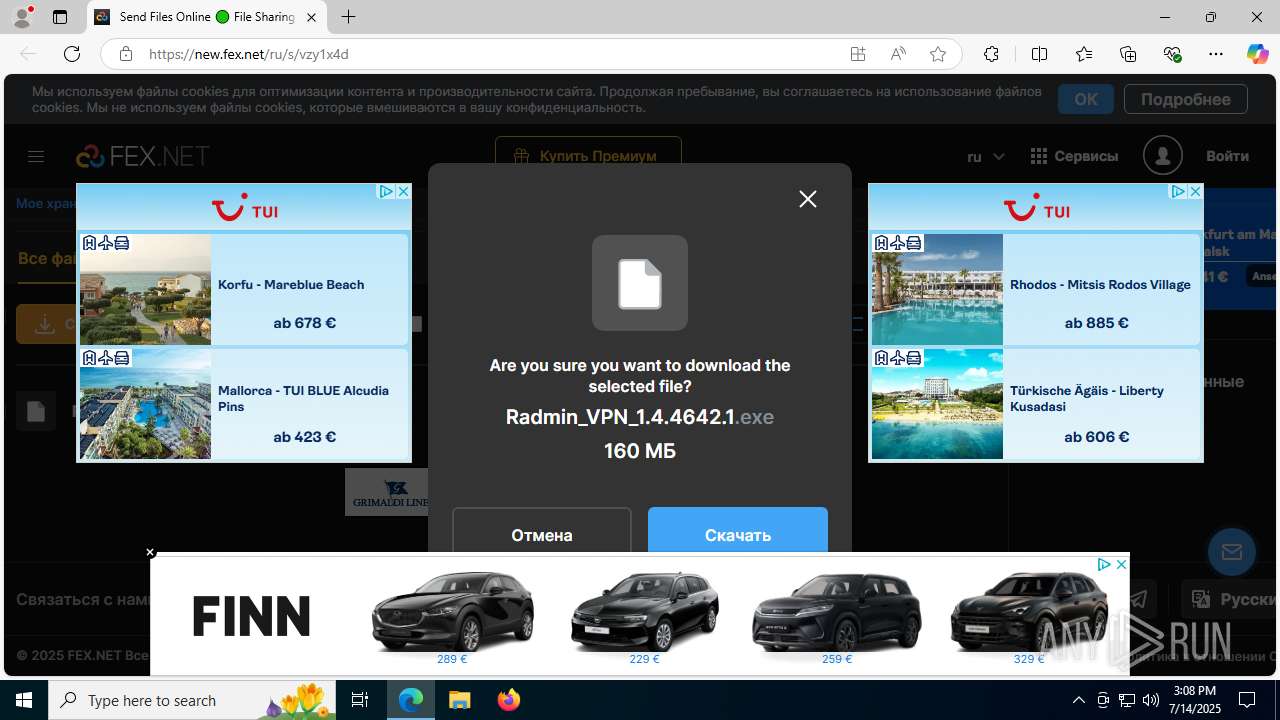
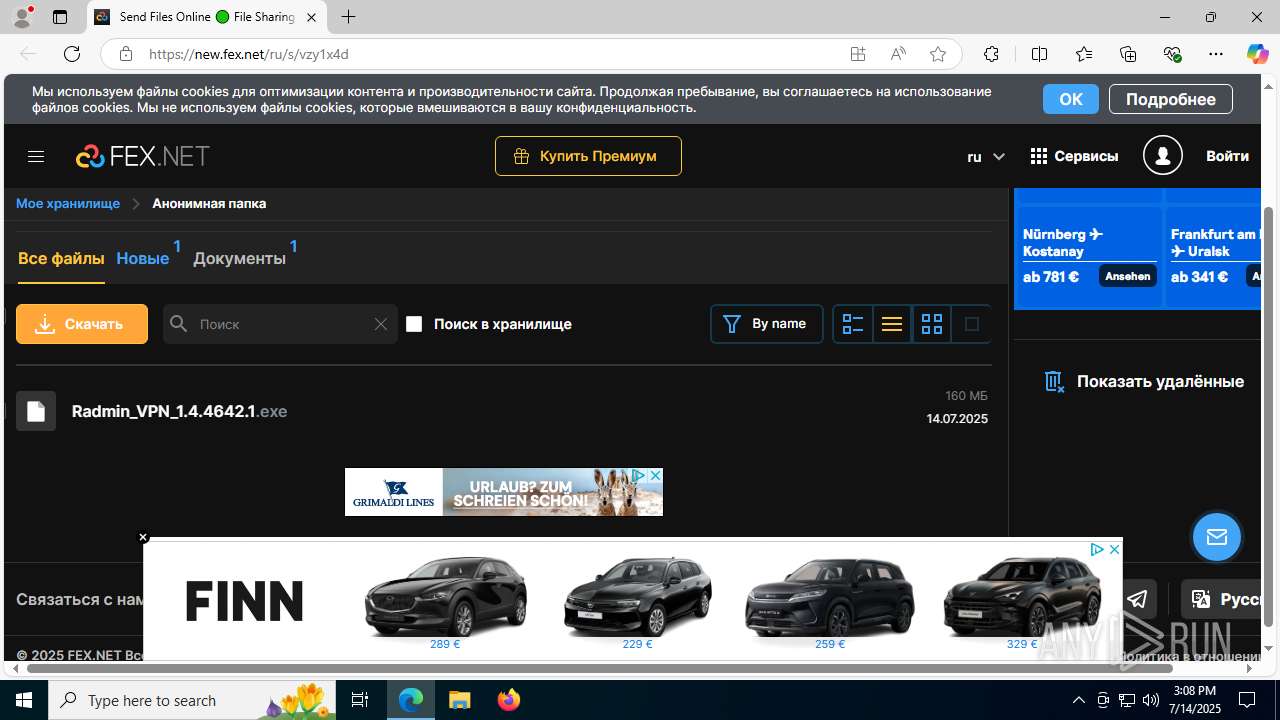
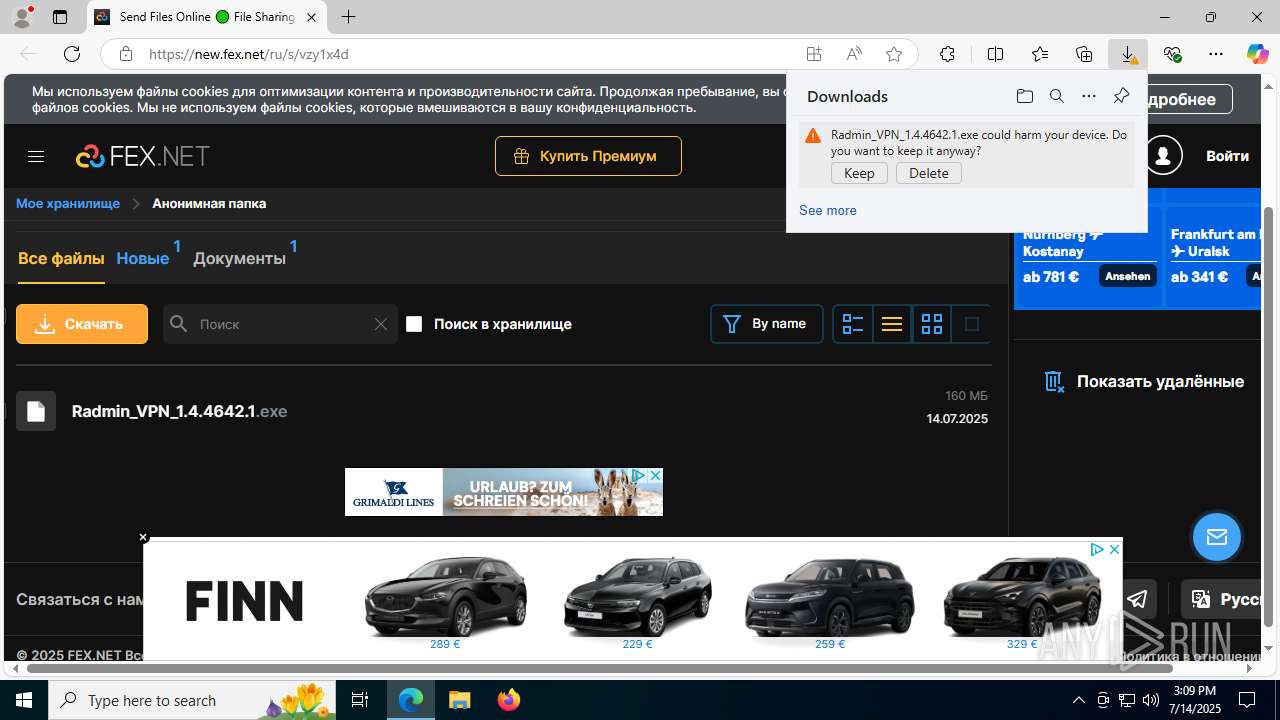
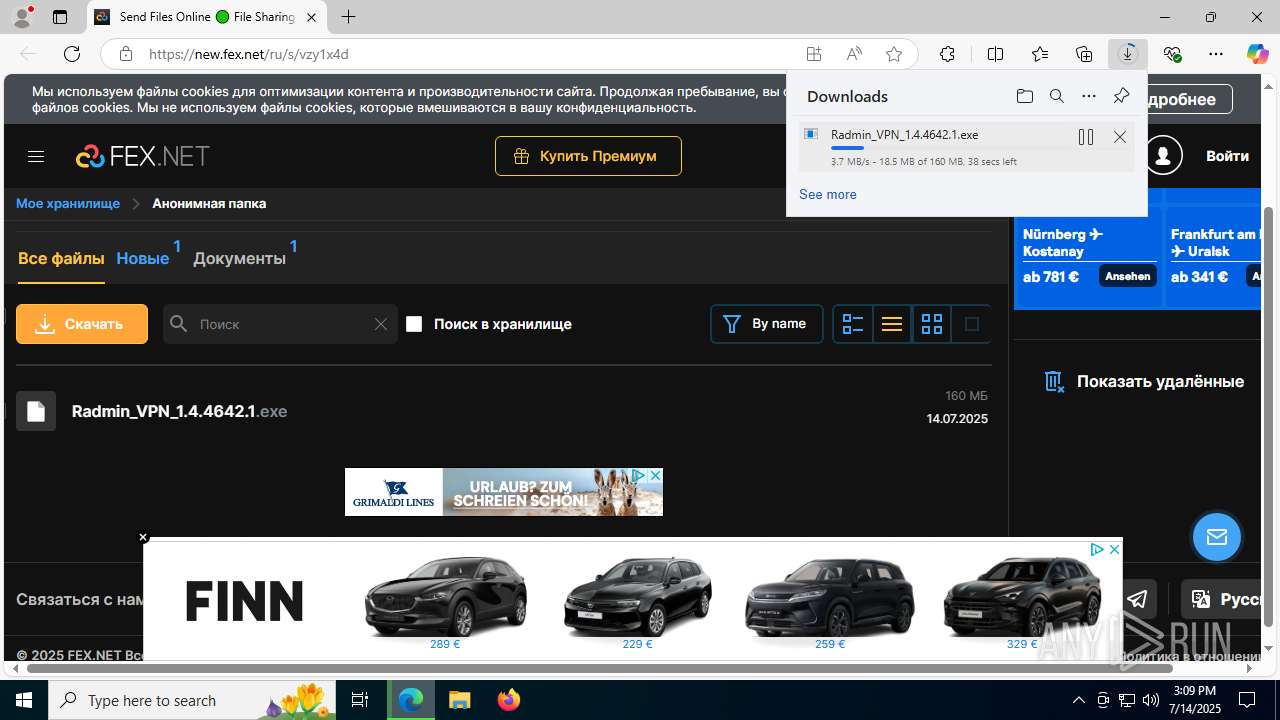
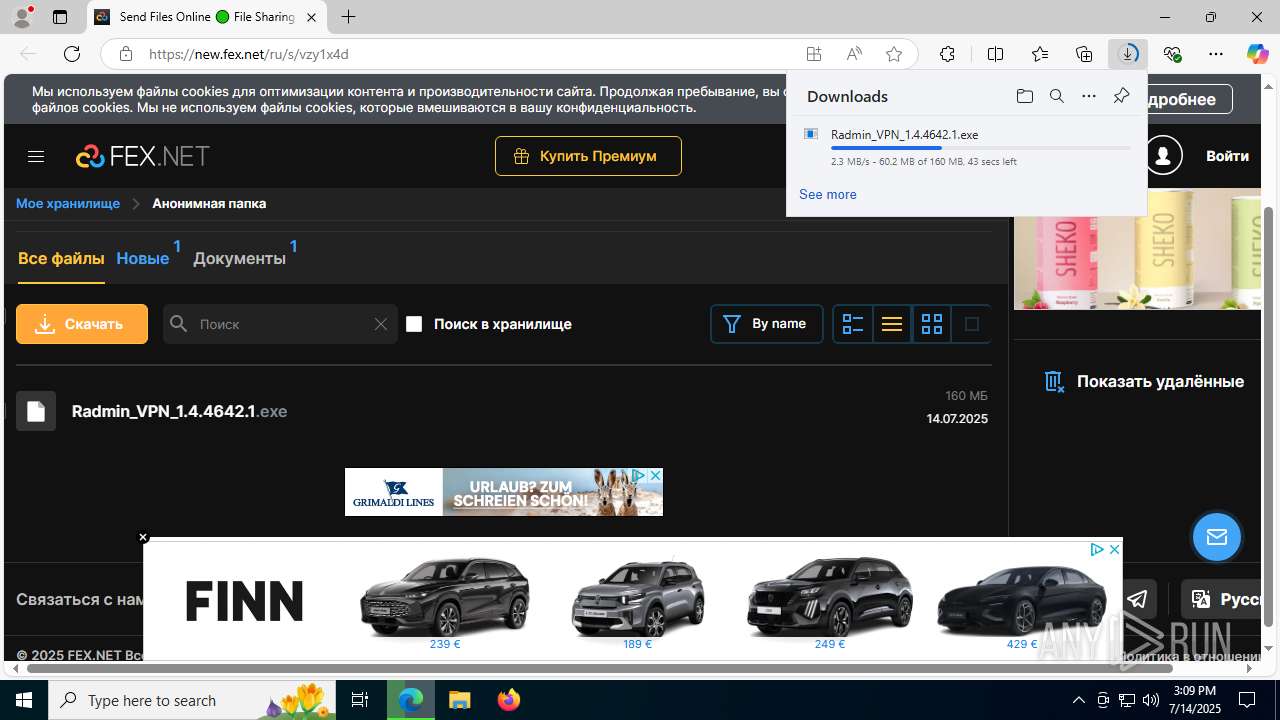
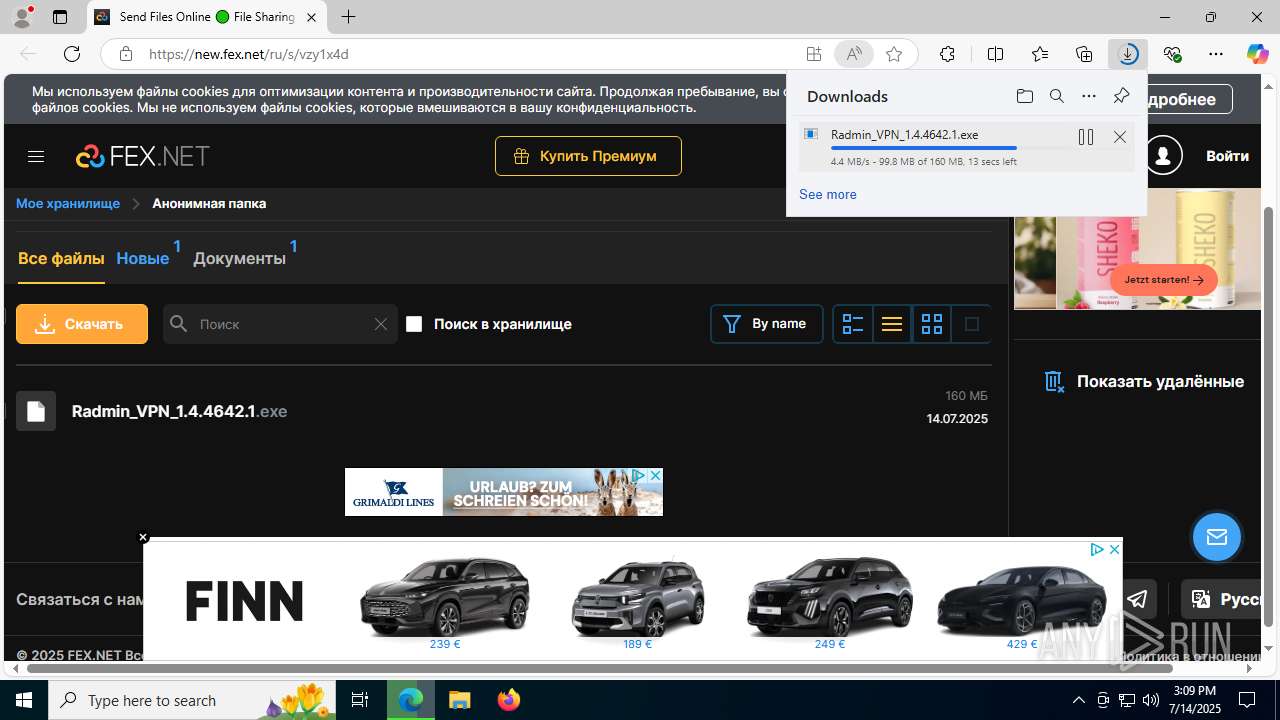
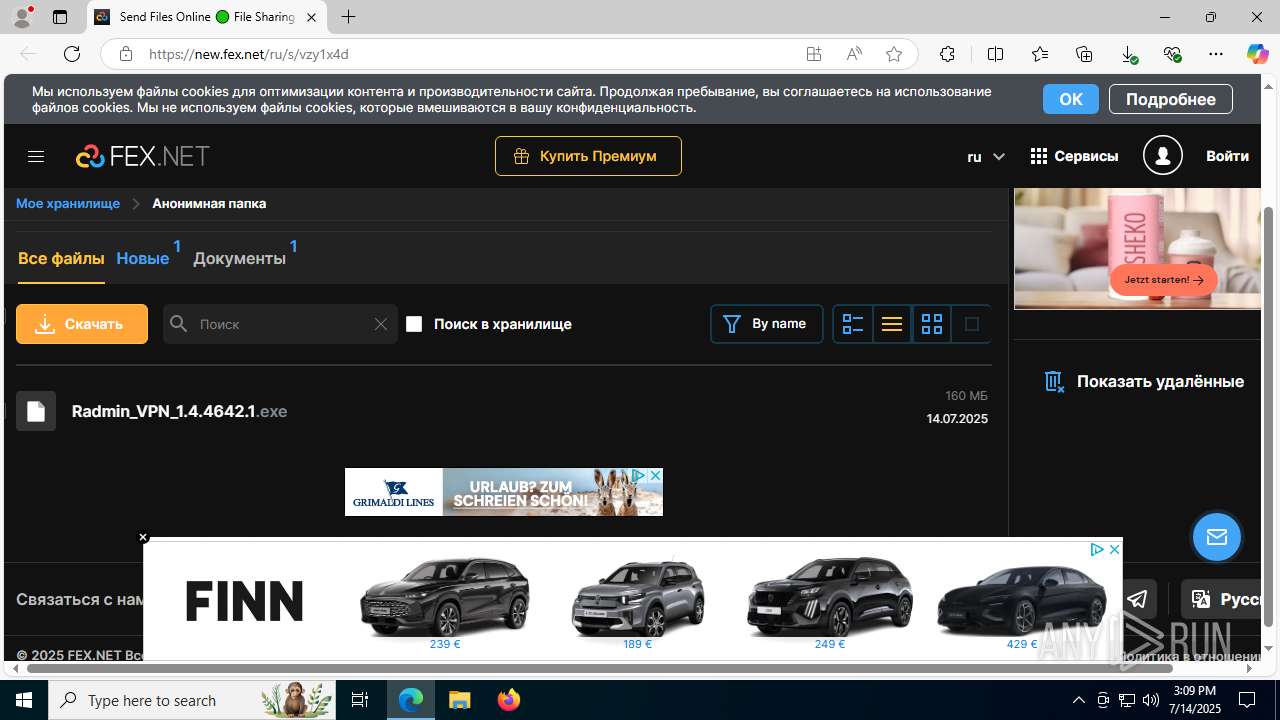
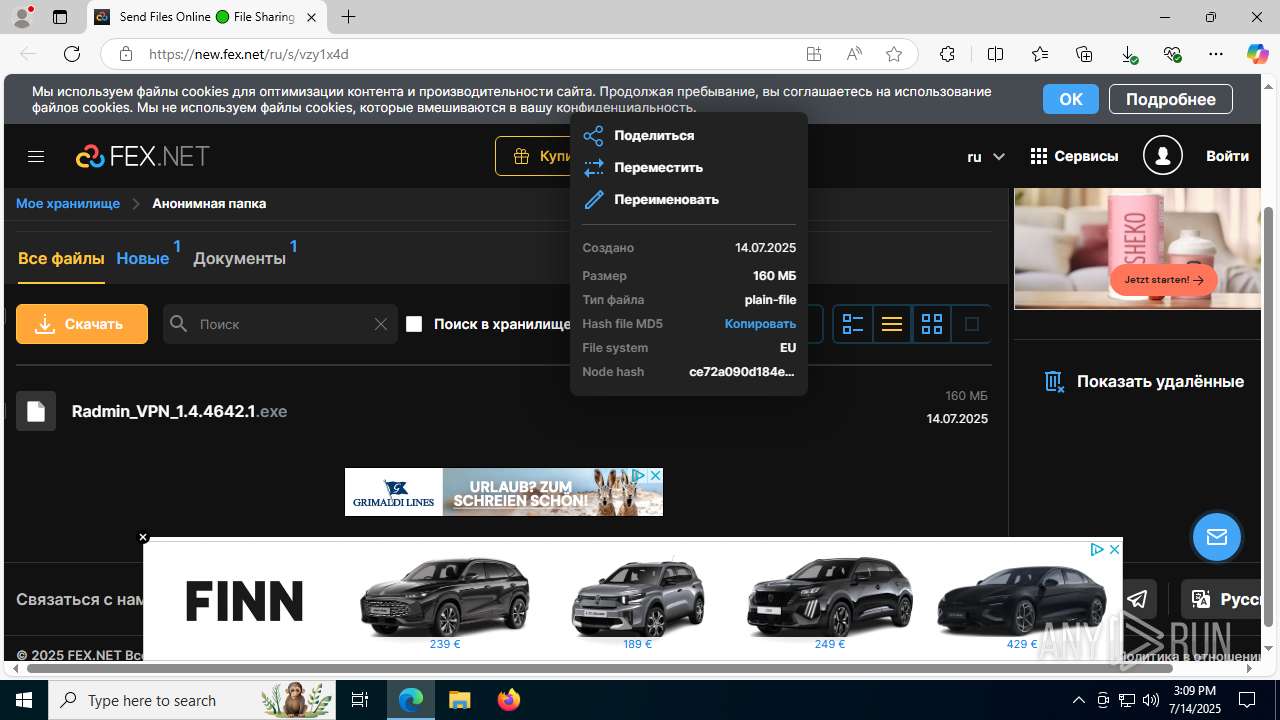
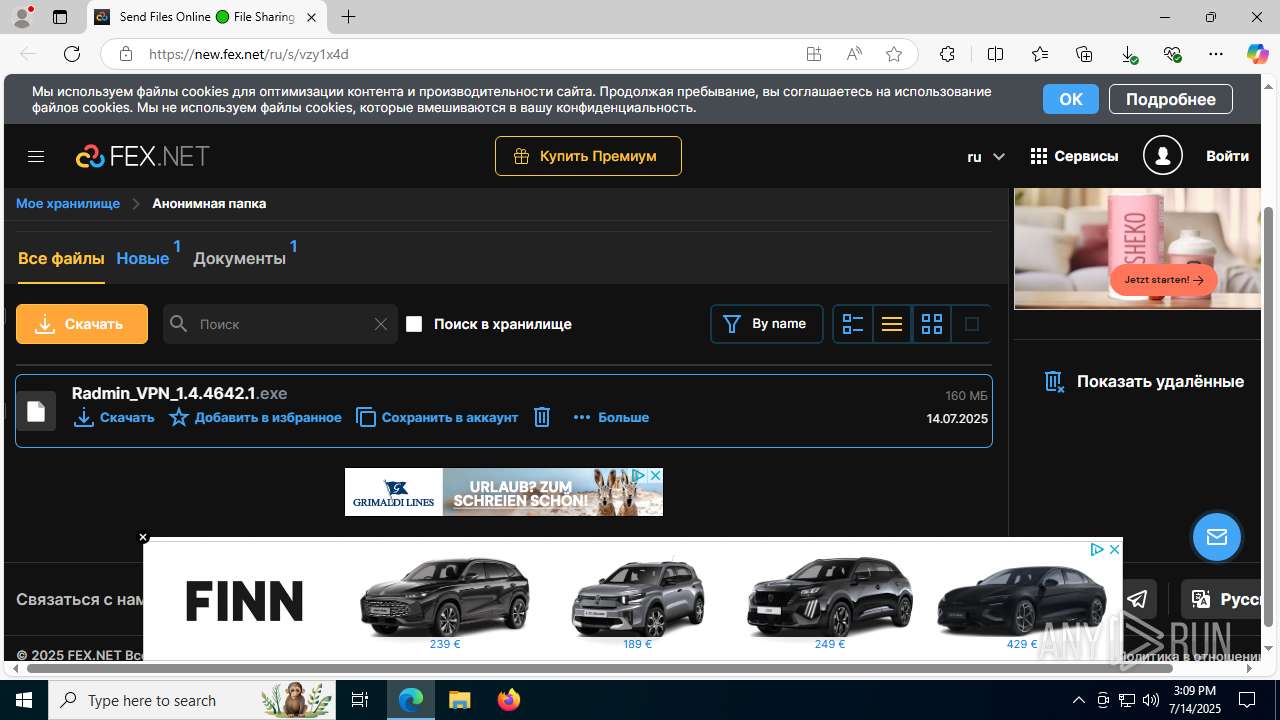
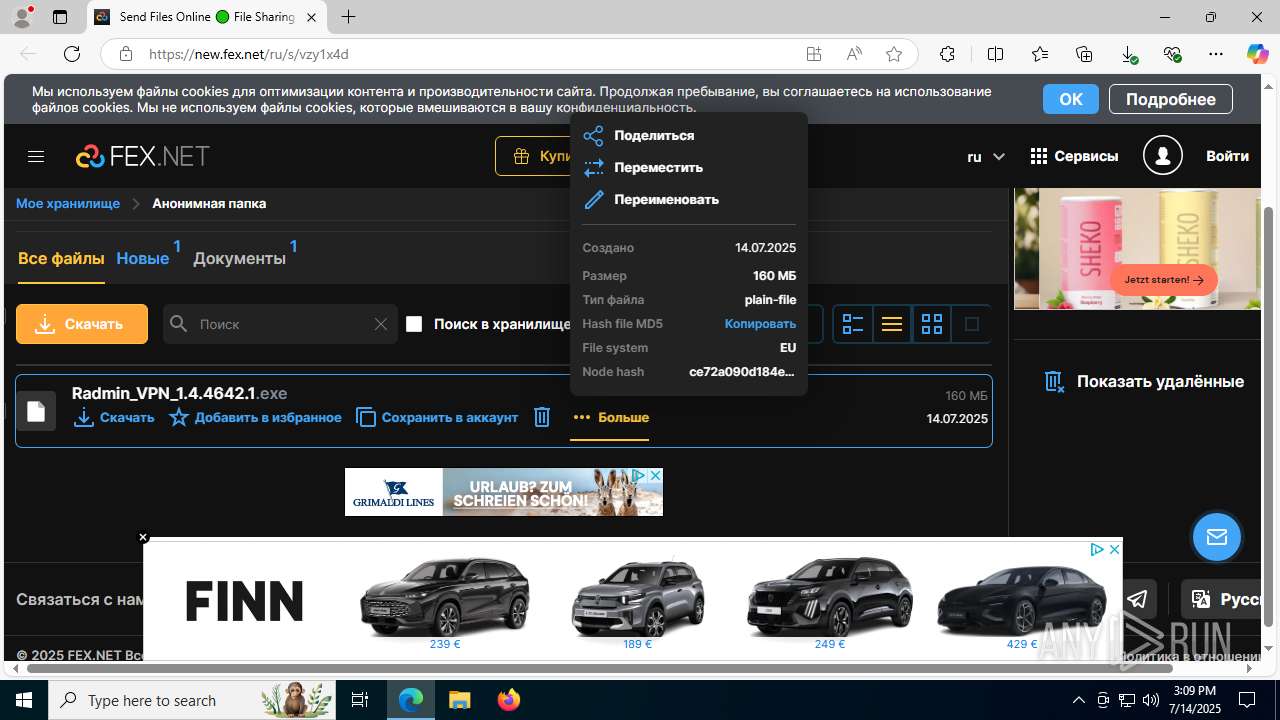
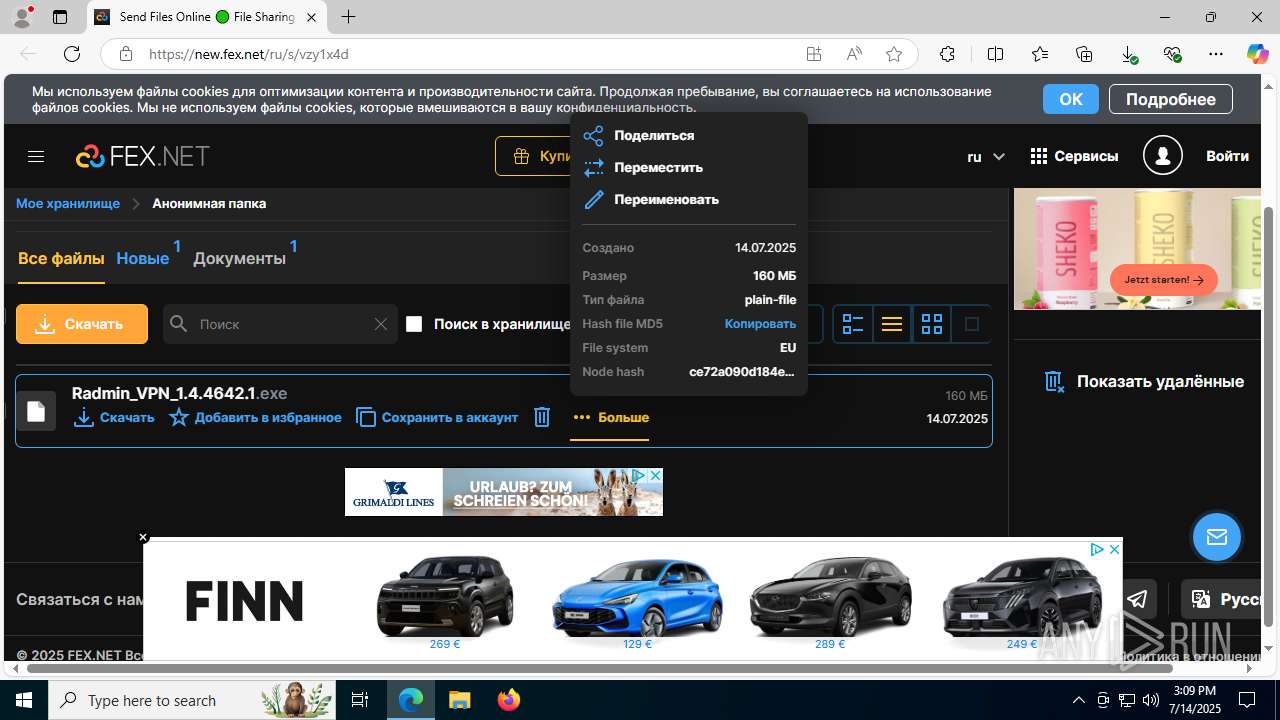
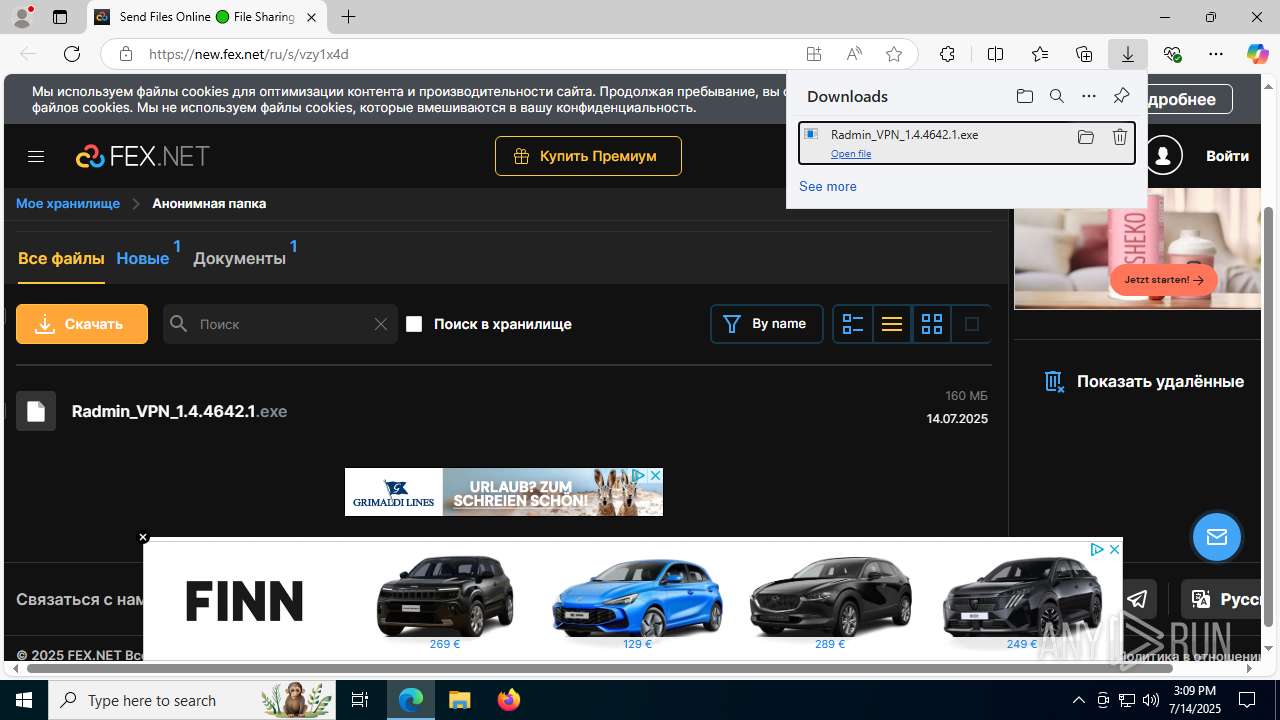
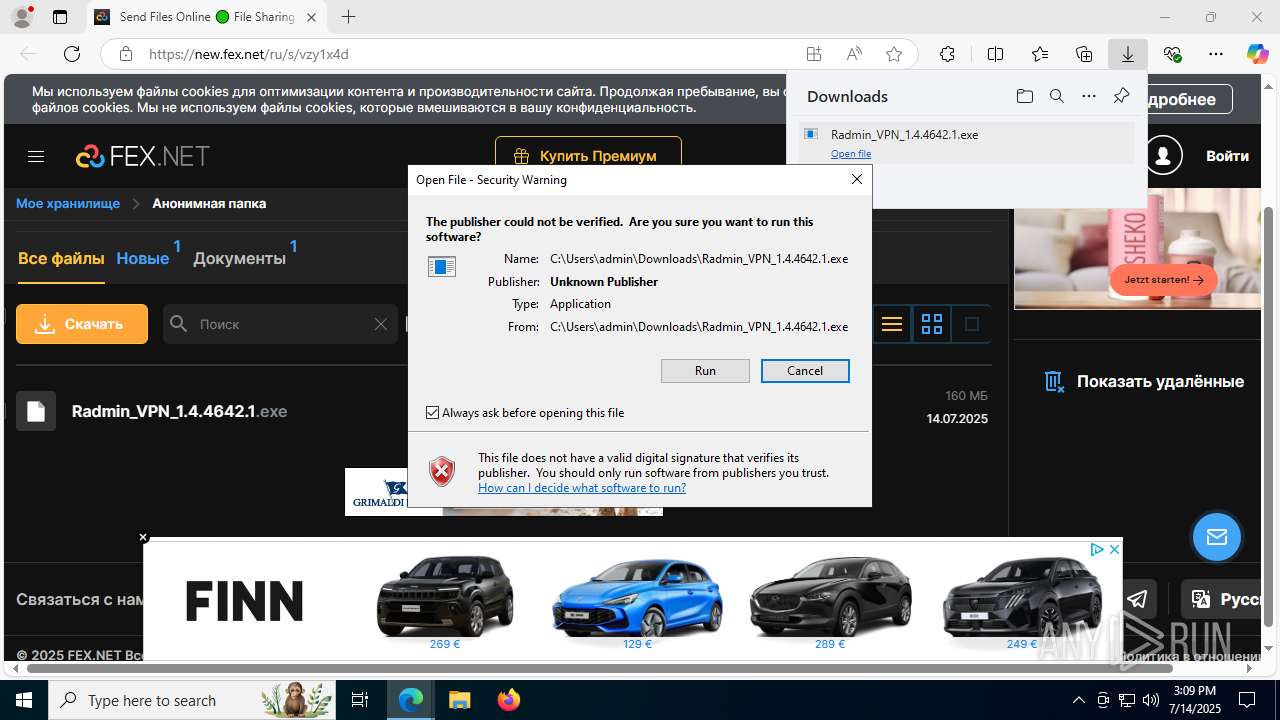
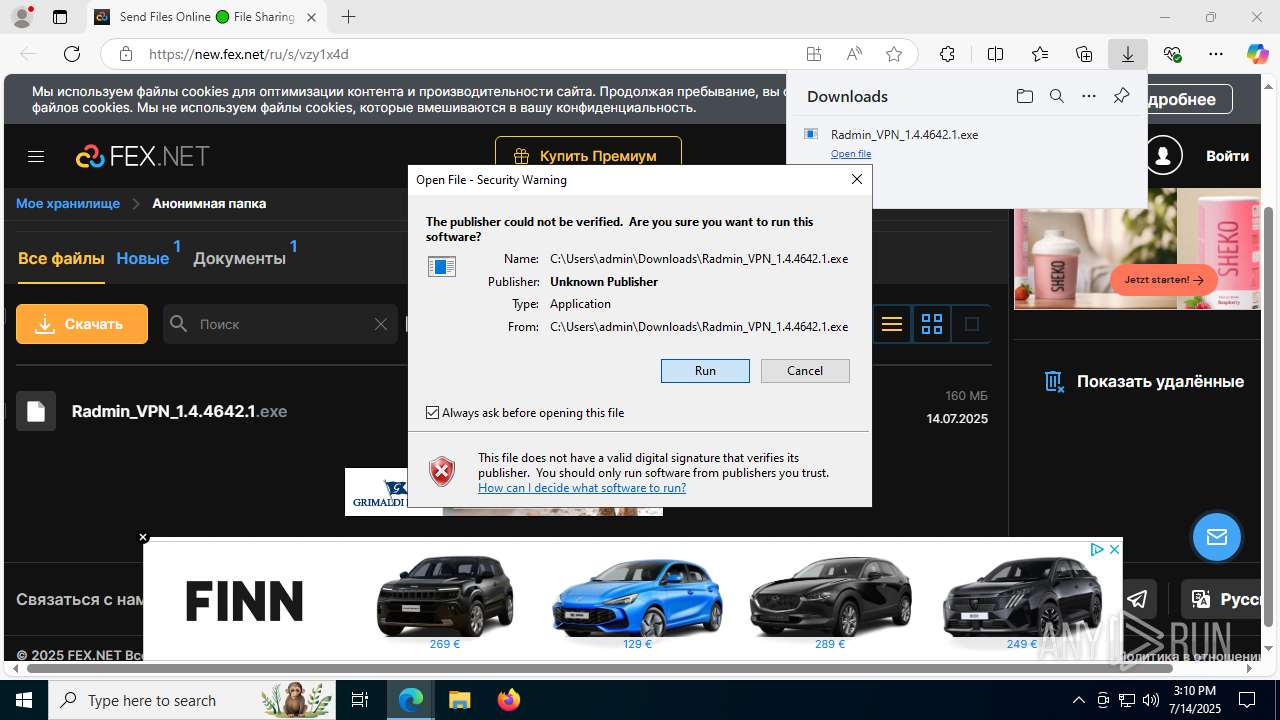
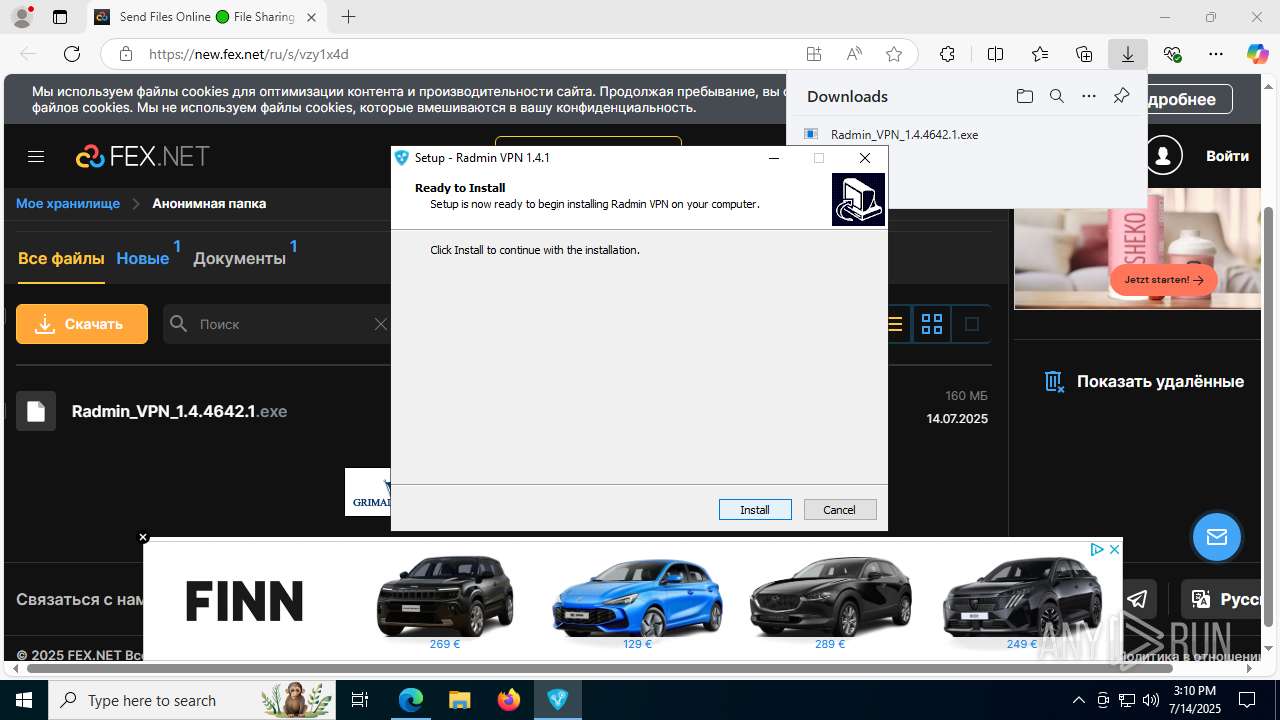
| URL: | https://new.fex.net/ru/s/vzy1x4d |
| Full analysis: | https://app.any.run/tasks/e17e7295-817b-4b1a-a890-4a218f77565b |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | July 14, 2025, 15:08:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 89018E13CC214634C5BE5F62BAA725DE |
| SHA1: | C9C9F04F8EF05A5E31D5BADAA14ACE2906D7B099 |
| SHA256: | 3294655830BBD96D42650ECFB22D2A6EBE71FDCE2D996E8A8747752D25D85492 |
| SSDEEP: | 3:N8JGvNn:2YvNn |
MALICIOUS
Uses Task Scheduler to run other applications
- Setup_RadminVPN.exe (PID: 7372)
- XClient.exe (PID: 4308)
Create files in the Startup directory
- Setup_RadminVPN.exe (PID: 7372)
Changes the autorun value in the registry
- Setup_RadminVPN.exe (PID: 7372)
- msiexec.exe (PID: 6836)
- XClient.exe (PID: 4308)
XWORM has been detected (YARA)
- Setup_RadminVPN.exe (PID: 7372)
XWORM has been detected (SURICATA)
- Setup_RadminVPN.exe (PID: 7372)
- XClient.exe (PID: 4308)
Generic malware mutex has been detected
- Setup_RadminVPN.exe (PID: 7372)
SUSPICIOUS
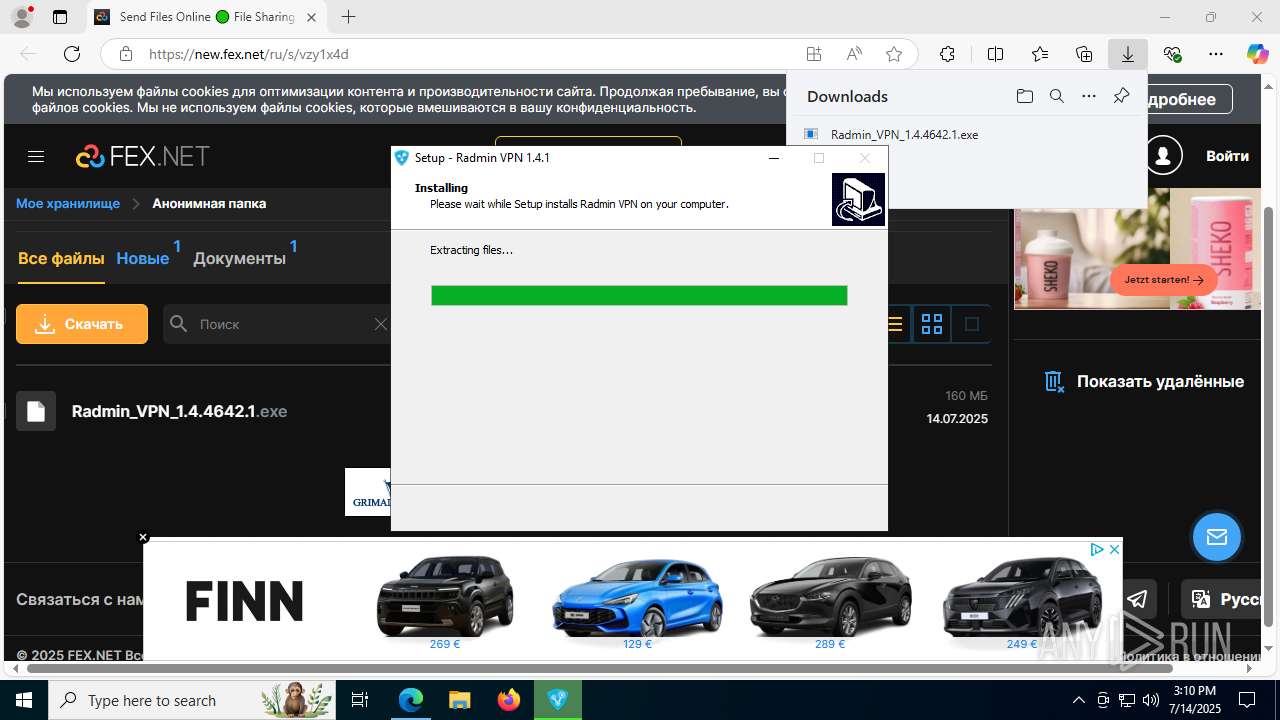
Executable content was dropped or overwritten
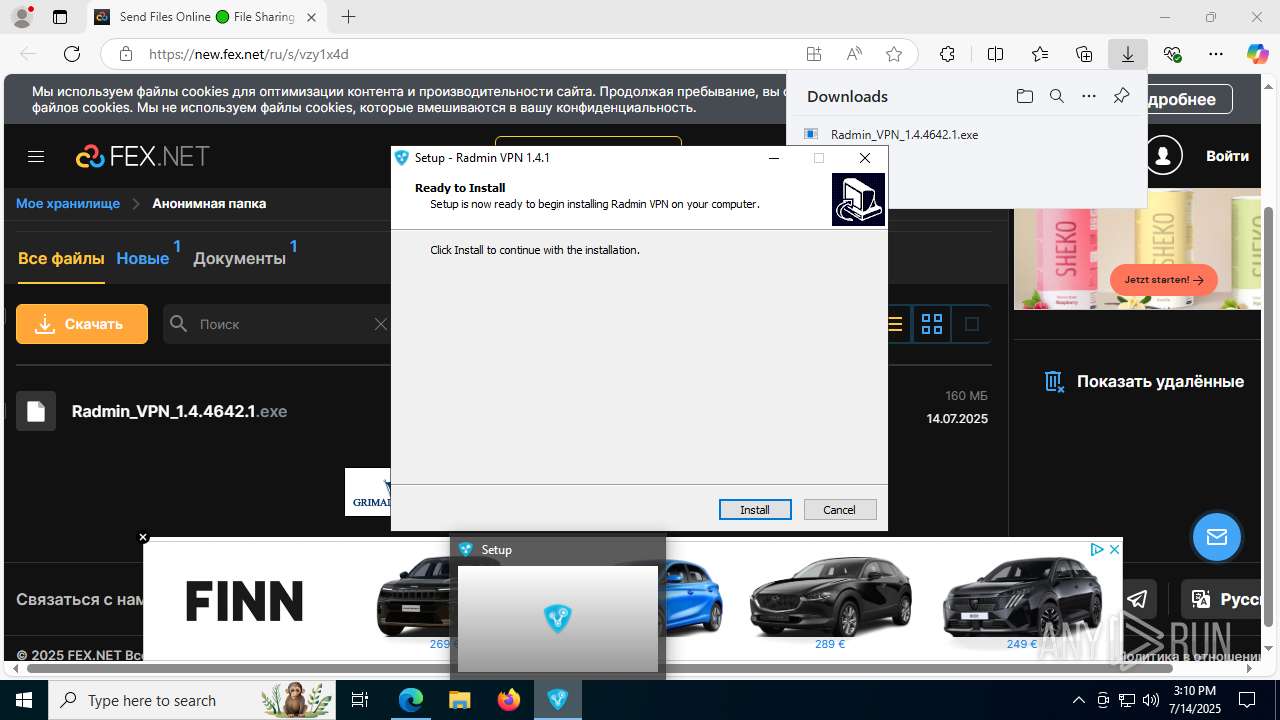
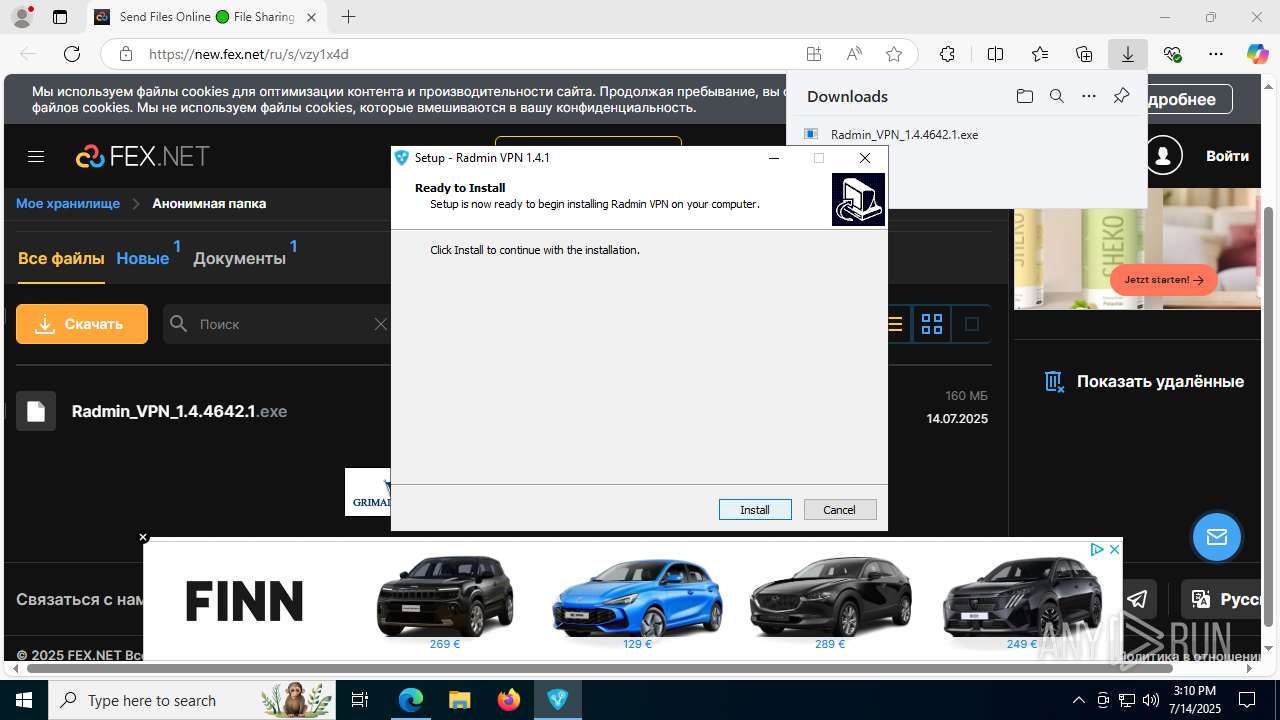
- Radmin_VPN_1.4.4642.1.exe (PID: 5960)
- Radmin_VPN_1.4.4642.1 (1).exe (PID: 7608)
- Radmin_VPN_1.4.4642.1 (1).exe (PID: 2348)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- Setup_RadminVPN.exe (PID: 7372)
- drvinst.exe (PID: 7196)
- drvinst.exe (PID: 7448)
Reads security settings of Internet Explorer
- Radmin_VPN_1.4.4642.1.exe (PID: 5960)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 3148)
- Setup_RadminVPN.exe (PID: 7372)
- XClient.exe (PID: 4308)
Reads the Windows owner or organization settings
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- msiexec.exe (PID: 6836)
Checks for external IP
- Setup_RadminVPN.exe (PID: 7372)
- svchost.exe (PID: 2200)
- XClient.exe (PID: 4308)
Reads the date of Windows installation
- Setup_RadminVPN.exe (PID: 7372)
- XClient.exe (PID: 4308)
Adds/modifies Windows certificates
- msiexec.exe (PID: 6836)
Process drops legitimate windows executable
- msiexec.exe (PID: 6836)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6836)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6836)
- drvinst.exe (PID: 7196)
- drvinst.exe (PID: 7448)
The process drops C-runtime libraries
- msiexec.exe (PID: 6836)
Creates files in the driver directory
- drvinst.exe (PID: 7196)
- drvinst.exe (PID: 7448)
- MSIBFD.tmp (PID: 6828)
Connects to unusual port
- Setup_RadminVPN.exe (PID: 7372)
- RvControlSvc.exe (PID: 2148)
- XClient.exe (PID: 4308)
Creates or modifies Windows services
- drvinst.exe (PID: 7448)
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 6180)
Contacting a server suspected of hosting an CnC
- Setup_RadminVPN.exe (PID: 7372)
- XClient.exe (PID: 4308)
Executes as Windows Service
- RvControlSvc.exe (PID: 2148)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 8108)
Starts CMD.EXE for commands execution
- RvControlSvc.exe (PID: 2148)
Process requests binary or script from the Internet
- svchost.exe (PID: 7332)
Potential Corporate Privacy Violation
- svchost.exe (PID: 7332)
The process executes via Task Scheduler
- XClient.exe (PID: 5028)
- XClient.exe (PID: 4308)
- XClient.exe (PID: 7868)
There is functionality for taking screenshot (YARA)
- RvRvpnGui.exe (PID: 2136)
INFO
Checks supported languages
- identity_helper.exe (PID: 8032)
- Radmin_VPN_1.4.4642.1.exe (PID: 5960)
- Setup_RadminVPN.exe (PID: 7372)
- Radmin_VPN_1.4.4642.1 (1).exe (PID: 7608)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 3148)
- Radmin_VPN_1.4.4642.1 (1).exe (PID: 2348)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- msiexec.exe (PID: 6836)
- msiexec.exe (PID: 7736)
- identity_helper.exe (PID: 5008)
- MSIBFD.tmp (PID: 6828)
- drvinst.exe (PID: 7196)
- drvinst.exe (PID: 7448)
- msiexec.exe (PID: 6180)
- RvControlSvc.exe (PID: 2148)
- RvRvpnGui.exe (PID: 2136)
- XClient.exe (PID: 5028)
- XClient.exe (PID: 4308)
- XClient.exe (PID: 7868)
Reads Environment values
- identity_helper.exe (PID: 8032)
- Setup_RadminVPN.exe (PID: 7372)
- identity_helper.exe (PID: 5008)
- XClient.exe (PID: 4308)
Application launched itself
- msedge.exe (PID: 4372)
- msedge.exe (PID: 5556)
- firefox.exe (PID: 5548)
- firefox.exe (PID: 5020)
Create files in a temporary directory
- svchost.exe (PID: 7332)
- Radmin_VPN_1.4.4642.1.exe (PID: 5960)
- Radmin_VPN_1.4.4642.1 (1).exe (PID: 7608)
- Radmin_VPN_1.4.4642.1 (1).exe (PID: 2348)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- Setup_RadminVPN.exe (PID: 7372)
Reads the computer name
- identity_helper.exe (PID: 8032)
- Radmin_VPN_1.4.4642.1.exe (PID: 5960)
- Setup_RadminVPN.exe (PID: 7372)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 3148)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- msiexec.exe (PID: 6836)
- msiexec.exe (PID: 7736)
- identity_helper.exe (PID: 5008)
- MSIBFD.tmp (PID: 6828)
- drvinst.exe (PID: 7196)
- drvinst.exe (PID: 7448)
- msiexec.exe (PID: 6180)
- RvControlSvc.exe (PID: 2148)
- RvRvpnGui.exe (PID: 2136)
- XClient.exe (PID: 5028)
- XClient.exe (PID: 4308)
- XClient.exe (PID: 7868)
Executable content was dropped or overwritten
- msedge.exe (PID: 4372)
- msiexec.exe (PID: 6836)
Reads the machine GUID from the registry
- Setup_RadminVPN.exe (PID: 7372)
- msiexec.exe (PID: 6836)
- MSIBFD.tmp (PID: 6828)
- drvinst.exe (PID: 7196)
- RvControlSvc.exe (PID: 2148)
- RvRvpnGui.exe (PID: 2136)
- XClient.exe (PID: 7868)
- XClient.exe (PID: 5028)
- XClient.exe (PID: 4308)
Process checks computer location settings
- Radmin_VPN_1.4.4642.1.exe (PID: 5960)
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 3148)
- Setup_RadminVPN.exe (PID: 7372)
- XClient.exe (PID: 4308)
Disables trace logs
- Setup_RadminVPN.exe (PID: 7372)
- netsh.exe (PID: 7388)
- netsh.exe (PID: 6360)
- netsh.exe (PID: 1128)
- netsh.exe (PID: 1532)
- netsh.exe (PID: 7832)
- XClient.exe (PID: 4308)
The sample compiled with english language support
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- msiexec.exe (PID: 6836)
- drvinst.exe (PID: 7196)
- drvinst.exe (PID: 7448)
RADMINVPN mutex has been found
- Radmin_VPN_1.4.4642.1 (1).tmp (PID: 7616)
- RvControlSvc.exe (PID: 2148)
- RvRvpnGui.exe (PID: 2136)
Checks proxy server information
- Setup_RadminVPN.exe (PID: 7372)
- slui.exe (PID: 2128)
- slui.exe (PID: 9112)
- XClient.exe (PID: 4308)
Creates files or folders in the user directory
- Setup_RadminVPN.exe (PID: 7372)
- msiexec.exe (PID: 6836)
Launching a file from a Registry key
- Setup_RadminVPN.exe (PID: 7372)
- msiexec.exe (PID: 6836)
- XClient.exe (PID: 4308)
Launching a file from the Startup directory
- Setup_RadminVPN.exe (PID: 7372)
Reads the software policy settings
- msiexec.exe (PID: 6836)
- slui.exe (PID: 2128)
- drvinst.exe (PID: 7196)
- MSIBFD.tmp (PID: 6828)
- slui.exe (PID: 9112)
The sample compiled with russian language support
- msiexec.exe (PID: 6836)
Starts application with an unusual extension
- msiexec.exe (PID: 6836)
Creates files in the program directory
- RvControlSvc.exe (PID: 2148)
Creates a software uninstall entry
- msiexec.exe (PID: 6836)
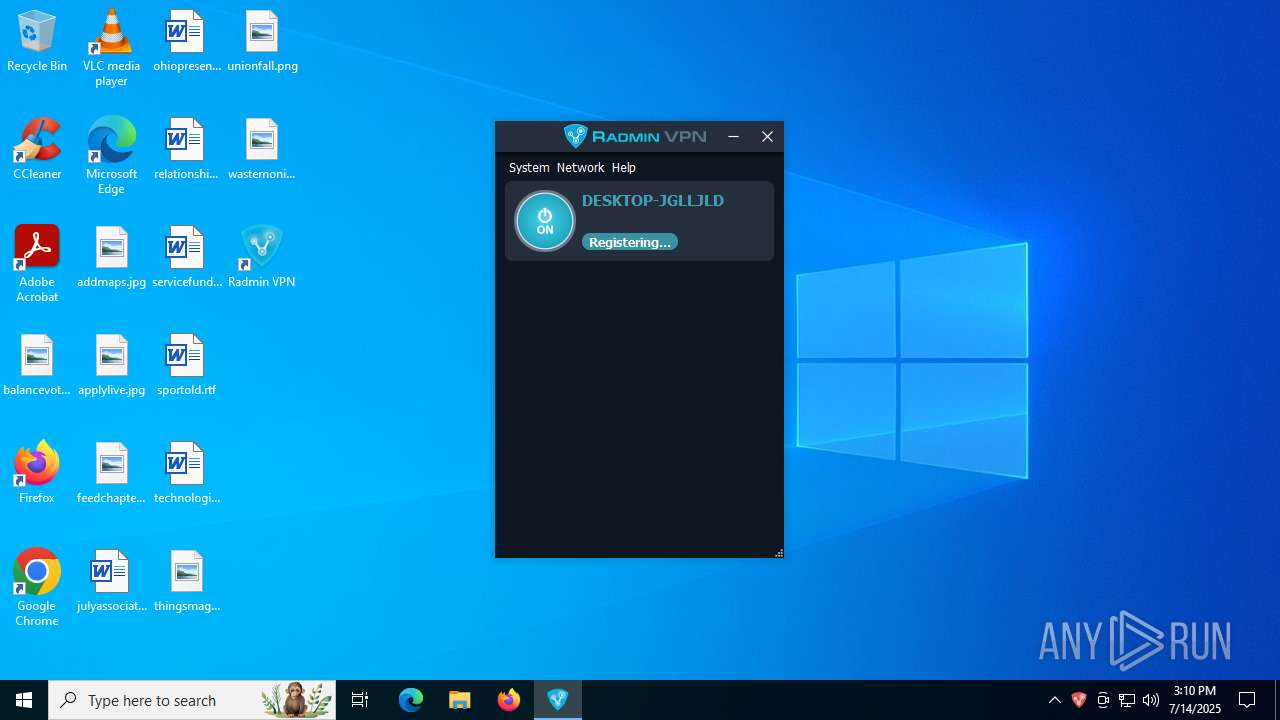
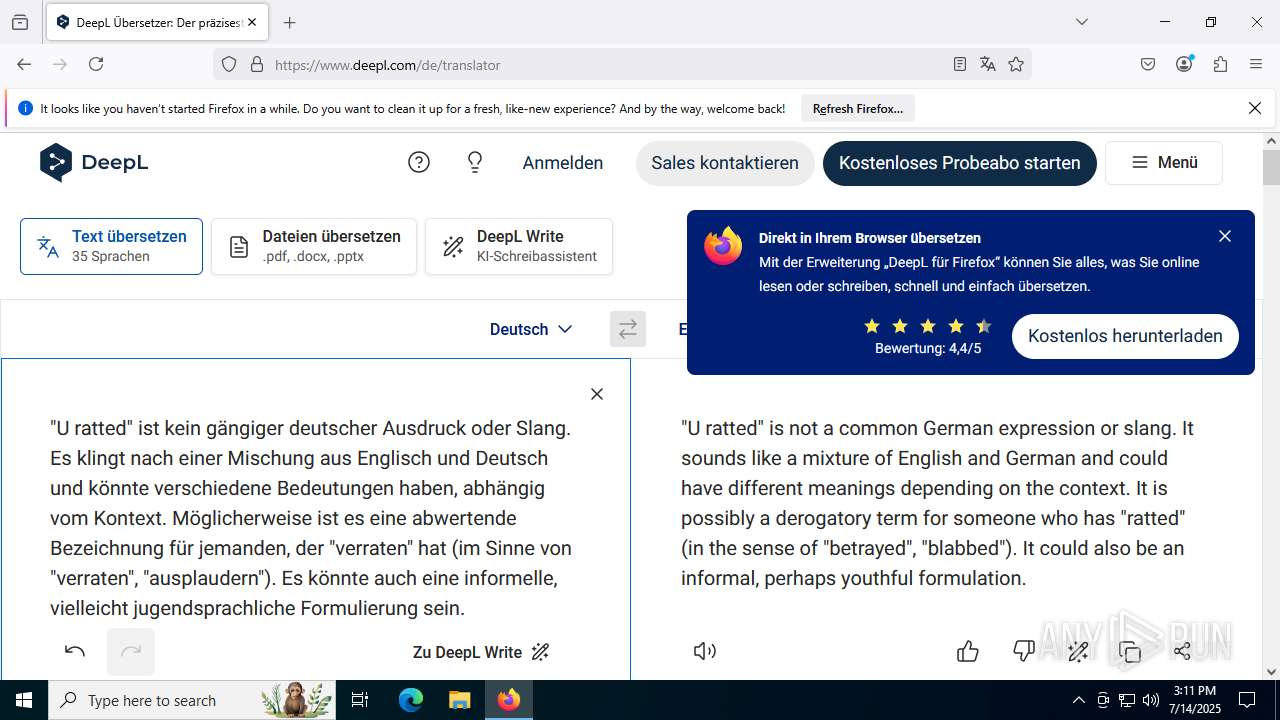
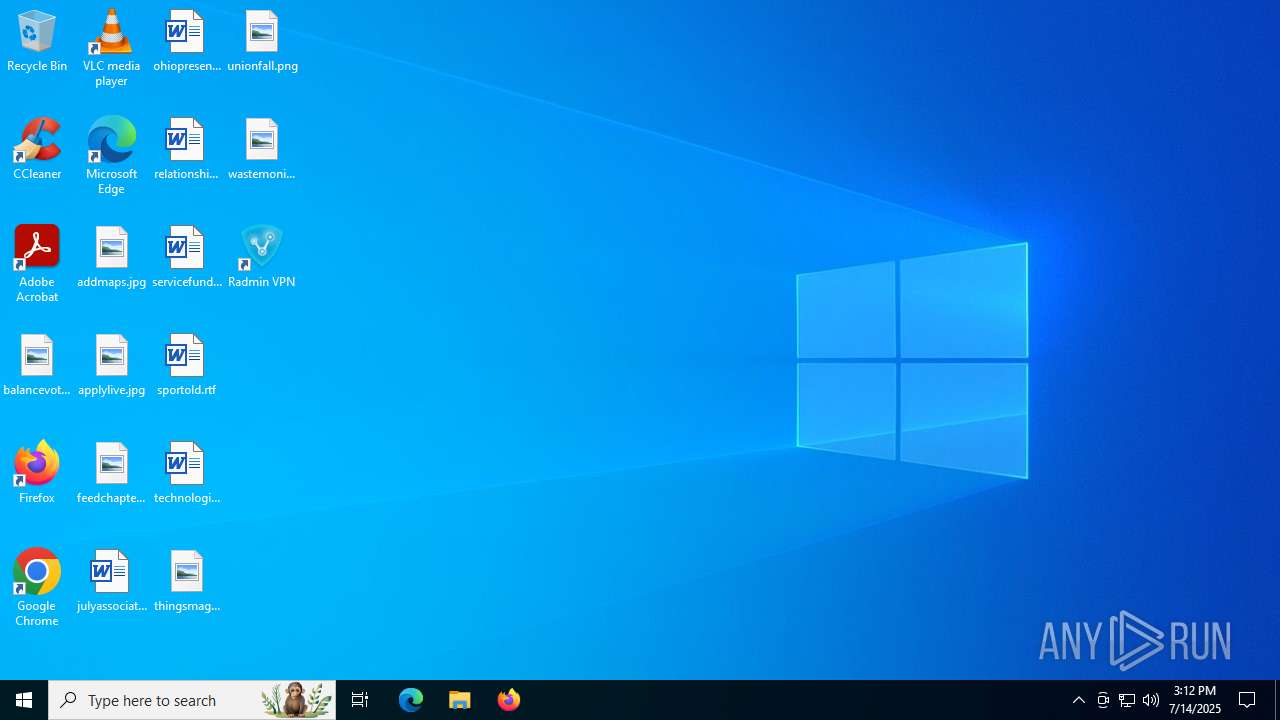
Manual execution by a user
- RvRvpnGui.exe (PID: 2136)
- firefox.exe (PID: 5548)
Reads Microsoft Office registry keys
- firefox.exe (PID: 5020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
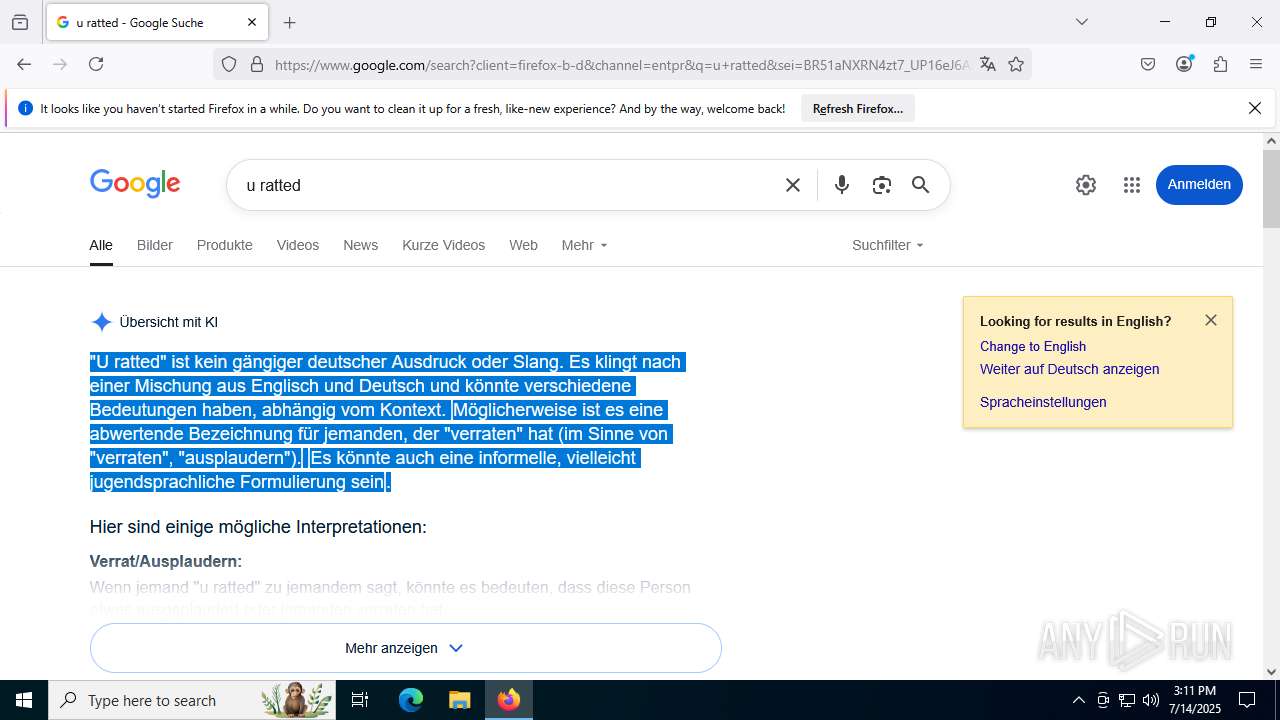
XWorm
(PID) Process(7372) Setup_RadminVPN.exe
C2york-pavilion.gl.at.ply.gg:11126
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V6.0
Mutex3BUJFKqQL7j5Sv5R
Total processes
277
Monitored processes
117
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4912,i,5966153895184939303,7534227902283829341,262144 --variations-seed-version --mojo-platform-channel-handle=4968 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2604,i,3388507784917763837,13996892609768223109,262144 --variations-seed-version --mojo-platform-channel-handle=2800 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 892 | netsh advfirewall firewall add rule name="Radmin VPN Control Service" dir=in action=allow program="C:\Program Files (x86)\Radmin VPN\RvControlSvc.exe" enable=yes profile=any edge=yes | C:\Windows\SysWOW64\netsh.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --always-read-main-dll --field-trial-handle=7748,i,3388507784917763837,13996892609768223109,262144 --variations-seed-version --mojo-platform-channel-handle=7756 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\system32\netsh.exe interface ip add address name="Radmin VPN" addr=26.23.18.146 mask=255.0.0.0 gateway=26.0.0.1 gwmetric=9256 | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5232,i,5966153895184939303,7534227902283829341,262144 --variations-seed-version --mojo-platform-channel-handle=5236 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://new.fex.net/ru/s/vzy1x4d" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | C:\WINDOWS\system32\netsh.exe interface ipv6 add address interface="Radmin VPN" address=fdfd::1a17:1292 | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4600 -prefsLen 39068 -prefMapHandle 4604 -prefMapSize 272997 -jsInitHandle 4608 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5104 -initialChannelId {03f3fe86-83a8-45a0-b2c5-c021f3caa9a1} -parentPid 5020 -crashReporter "\\.\pipe\gecko-crash-server-pipe.5020" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
Total events
72 952
Read events
72 238
Write events
490
Delete events
224
Modification events
| (PID) Process: | (4372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 844514521 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31192273 | |||
| (PID) Process: | (1356) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
123
Suspicious files
451
Text files
203
Unknown types
380
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1755f0.TMP | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1755f0.TMP | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1755f0.TMP | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1755ff.TMP | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17561f.TMP | — | |
MD5:— | SHA256:— | |||
| 4372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
93
TCP/UDP connections
382
DNS requests
383
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4412 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ZmItUh-FWXylq6B5z_EEPE05vtMGiZUScgPA87pHhW8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2288 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7332 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752554056&P2=404&P3=2&P4=bWtItdM%2bfx6AA96I%2buhCD%2fRdHZ8jBcGpEtUErl0RQsWMNL8iCDd0k%2bXo4fQNMgO90DFAZf658rdV3SFmEUBvsQ%3d%3d | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7332 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752554056&P2=404&P3=2&P4=bWtItdM%2bfx6AA96I%2buhCD%2fRdHZ8jBcGpEtUErl0RQsWMNL8iCDd0k%2bXo4fQNMgO90DFAZf658rdV3SFmEUBvsQ%3d%3d | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7332 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752554056&P2=404&P3=2&P4=bWtItdM%2bfx6AA96I%2buhCD%2fRdHZ8jBcGpEtUErl0RQsWMNL8iCDd0k%2bXo4fQNMgO90DFAZf658rdV3SFmEUBvsQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6260 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4412 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4412 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4412 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
4412 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4412 | msedge.exe | 104.21.90.161:443 | new.fex.net | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
new.fex.net |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
player.bidmatic.io |
| unknown |
securepubads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|
Setup_RadminVPN.exe | Conversion from string "" to type 'Integer' is not valid.
|