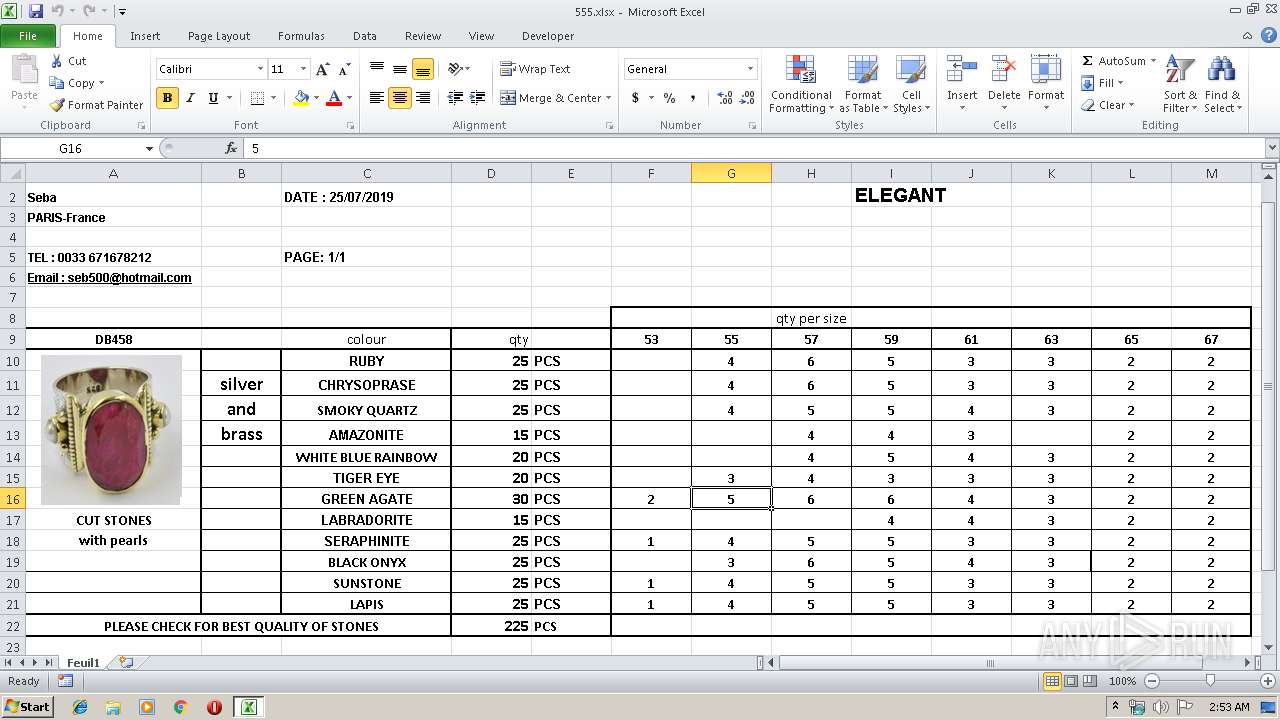
| File name: | 555.xlsx |
| Full analysis: | https://app.any.run/tasks/86b8728f-5832-45dc-901c-93ef362511cb |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2019, 01:52:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | FA9B4801240CB4F70F0A810452E652BA |
| SHA1: | B9745E884270E4A0B15CBACCFE9AF186D4224C68 |
| SHA256: | 32935F7F01BD3BDA0D9AB3AF495B02367AD5DDB1DAE559F17C38BA371046D05E |
| SSDEEP: | 384:4NRyWJMpDA6jv2z603n+0YwmVWmGXaZHo0Bg13kjwxZ0zcqW4DtSXYe74vu:4N9SDhY603n+hjVWmGUHCy+0zTIY+Wu |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3368)
Application was dropped or rewritten from another process
- chigocryp.exe (PID: 3332)
Actions looks like stealing of personal data
- vbc.exe (PID: 2916)
Loads dropped or rewritten executable
- vbc.exe (PID: 2916)
SUSPICIOUS
Creates files in the user directory
- EQNEDT32.EXE (PID: 3368)
- chigocryp.exe (PID: 3332)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3368)
- chigocryp.exe (PID: 3332)
- vbc.exe (PID: 2916)
Executed via COM
- EQNEDT32.EXE (PID: 3368)
Executes scripts
- chigocryp.exe (PID: 3332)
Reads the cookies of Google Chrome
- vbc.exe (PID: 2916)
Reads the cookies of Mozilla Firefox
- vbc.exe (PID: 2916)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:26 00:19:20 |
| ZipCRC: | 0x96c115fe |
| ZipCompressedSize: | 424 |
| ZipUncompressedSize: | 1805 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | hp |
|---|
XML
| LastModifiedBy: | hp |
|---|---|
| CreateDate: | 2019:07:22 18:46:12Z |
| ModifyDate: | 2019:07:24 20:26:54Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | Feuil1 |
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
Total processes
36
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2916 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | chigocryp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3332 | C:\Users\admin\AppData\Roaming\chigocryp.exe | C:\Users\admin\AppData\Roaming\chigocryp.exe | EQNEDT32.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3368 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
656
Read events
574
Write events
75
Delete events
7
Modification events
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | ;s# |
Value: 3B732300340D0000010000000000000000000000 | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 340D000060E27EF6B05BD50100000000 | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | ;s# |
Value: 3B732300340D0000010000000000000000000000 | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3380) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\169FFF |
| Operation: | write | Name: | 169FFF |
Value: 04000000340D00002A00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C003500350035002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000080B7A1F7B05BD501FF9F1600FF9F160000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
51
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B3B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3368 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\chigocryp[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3368 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\chigocryp.exe | executable | |
MD5:— | SHA256:— | |||
| 3332 | chigocryp.exe | C:\Users\admin\AppData\Roaming\filename.exe | executable | |
MD5:— | SHA256:— | |||
| 2916 | vbc.exe | C:\Users\admin\AppData\Local\Temp\2fda\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:502263C56F931DF8440D7FD2FA7B7C00 | SHA256:94A5DF1227818EDBFD0D5091C6A48F86B4117C38550343F780C604EEE1CD6231 | |||
| 2916 | vbc.exe | C:\Users\admin\AppData\Local\Temp\2fda\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:E2F648AE40D234A3892E1455B4DBBE05 | SHA256:C8C499B012D0D63B7AFC8B4CA42D6D996B2FCF2E8B5F94CACFBEC9E6F33E8A03 | |||
| 2916 | vbc.exe | C:\Users\admin\AppData\Local\Temp\2fda\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:88FF191FD8648099592ED28EE6C442A5 | SHA256:C310CC91464C9431AB0902A561AF947FA5C973925FF70482D3DE017ED3F73B7D | |||
| 2916 | vbc.exe | C:\Users\admin\AppData\Local\Temp\2fda\api-ms-win-core-localization-l1-2-0.dll | executable | |
MD5:EFF11130BFE0D9C90C0026BF2FB219AE | SHA256:03AD57C24FF2CF895B5F533F0ECBD10266FD8634C6B9053CC9CB33B814AD5D97 | |||
| 2916 | vbc.exe | C:\Users\admin\AppData\Local\Temp\2fda\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:E479444BDD4AE4577FD32314A68F5D28 | SHA256:C85DC081B1964B77D289AAC43CC64746E7B141D036F248A731601EB98F827719 | |||
| 2916 | vbc.exe | C:\Users\admin\AppData\Local\Temp\2fda\api-ms-win-core-libraryloader-l1-1-0.dll | executable | |
MD5:D0873E21721D04E20B6FFB038ACCF2F1 | SHA256:BB25CCF8694D1FCFCE85A7159DCF6985FDB54728D29B021CB3D14242F65909CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2916 | vbc.exe | 185.50.196.212:443 | losjardinesdejavier.com | Comvive Servidores S.L. | ES | malicious |
3368 | EQNEDT32.EXE | 69.89.31.230:443 | earadat.com | Unified Layer | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
earadat.com |
| suspicious |
losjardinesdejavier.com |
| malicious |