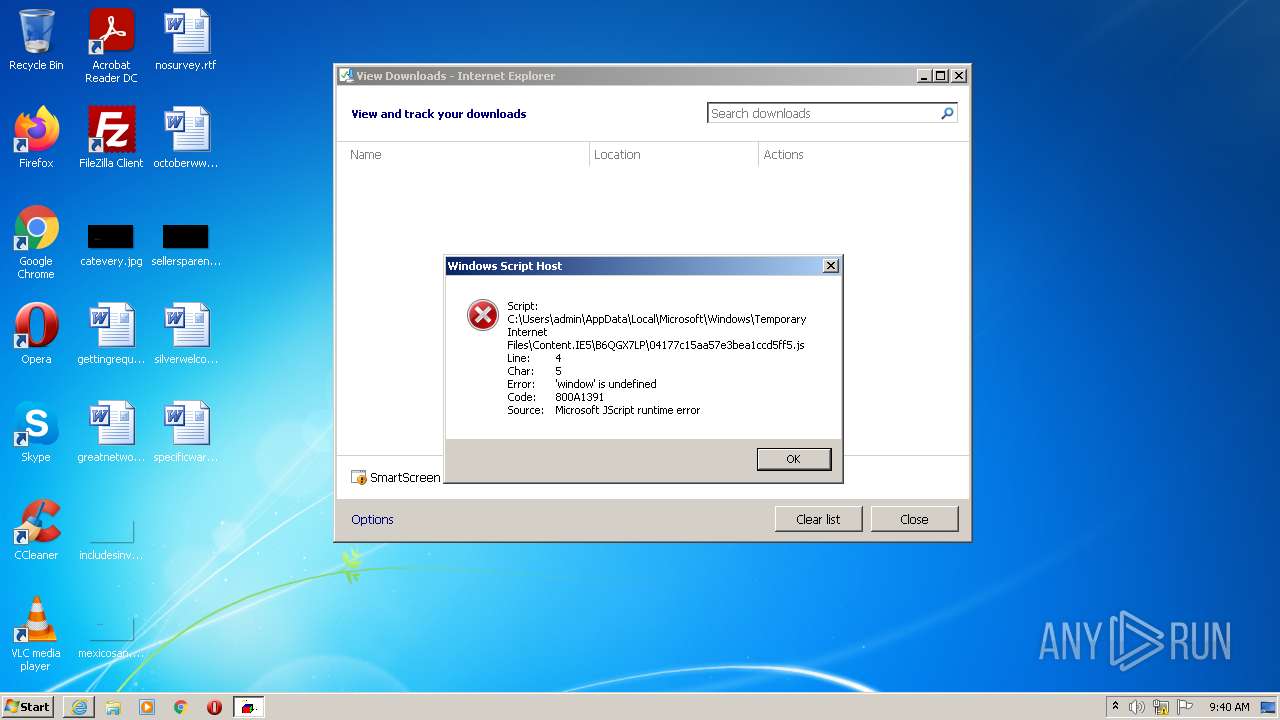
| URL: | https://chimpstatic.com/mcjs-connected/js/users/7ae0d7371fd5f95f76804c2b0/04177c15aa57e3bea1ccd5ff5.js |
| Full analysis: | https://app.any.run/tasks/c02bd1d1-e004-4122-8637-7fe418087e54 |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2022, 08:39:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 925C2023D56A324DF1826AF4FC05D6D1 |
| SHA1: | 4DA75CE9C21F44C402D290F83ABA5E6F50699898 |
| SHA256: | 32852B168C4D91079963E40C47CA70FC8087D0B81EF1FEF4A4726C401B25B10E |
| SSDEEP: | 3:N8QbDpdCQ/HnprSWnDYYVRGwVBSDiHzHAkWWM7W:2QJdCuHpGWn8YRyDYA5WM7W |
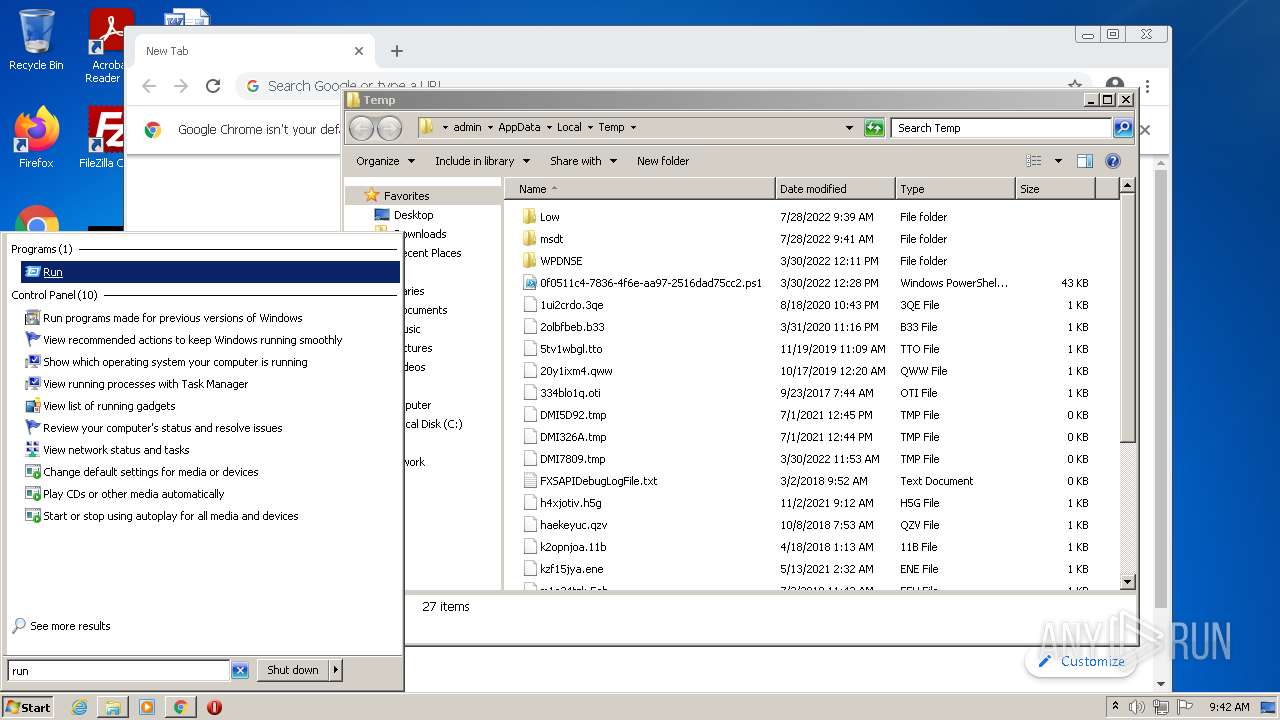
MALICIOUS
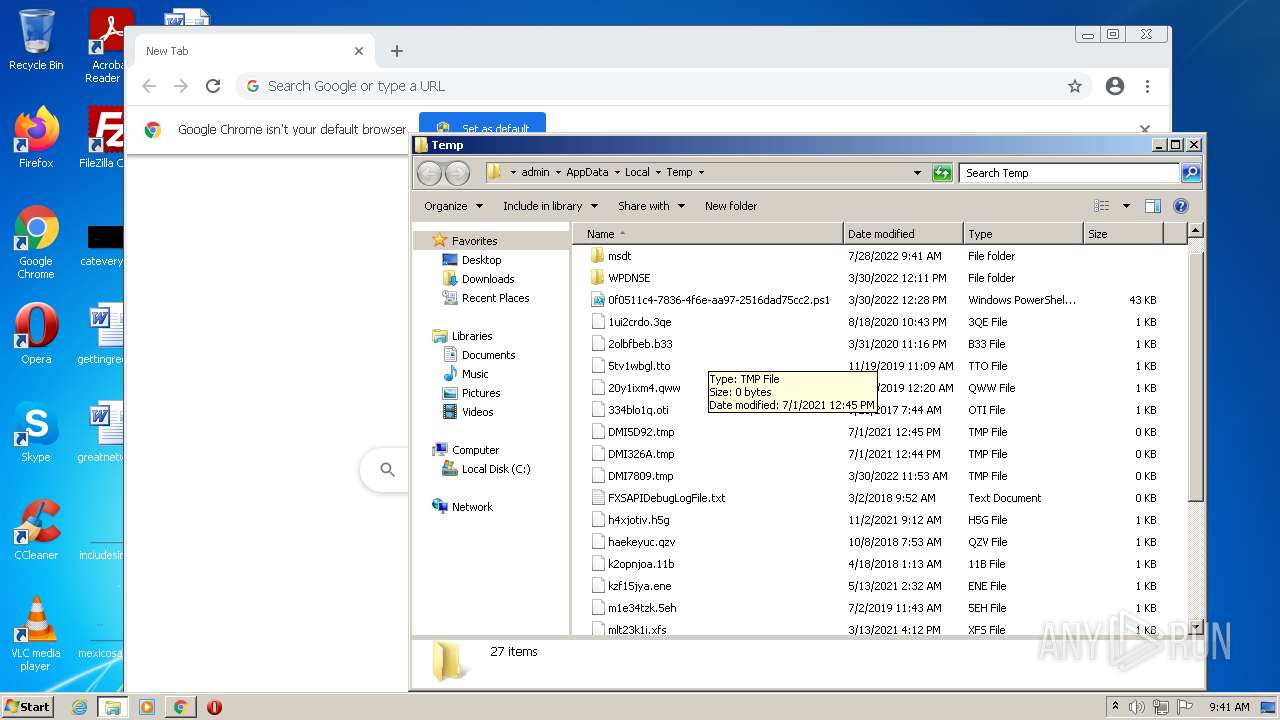
Drops executable file immediately after starts
- msdt.exe (PID: 3532)
- csc.exe (PID: 2660)
- csc.exe (PID: 3092)
- csc.exe (PID: 2176)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 1108)
SUSPICIOUS
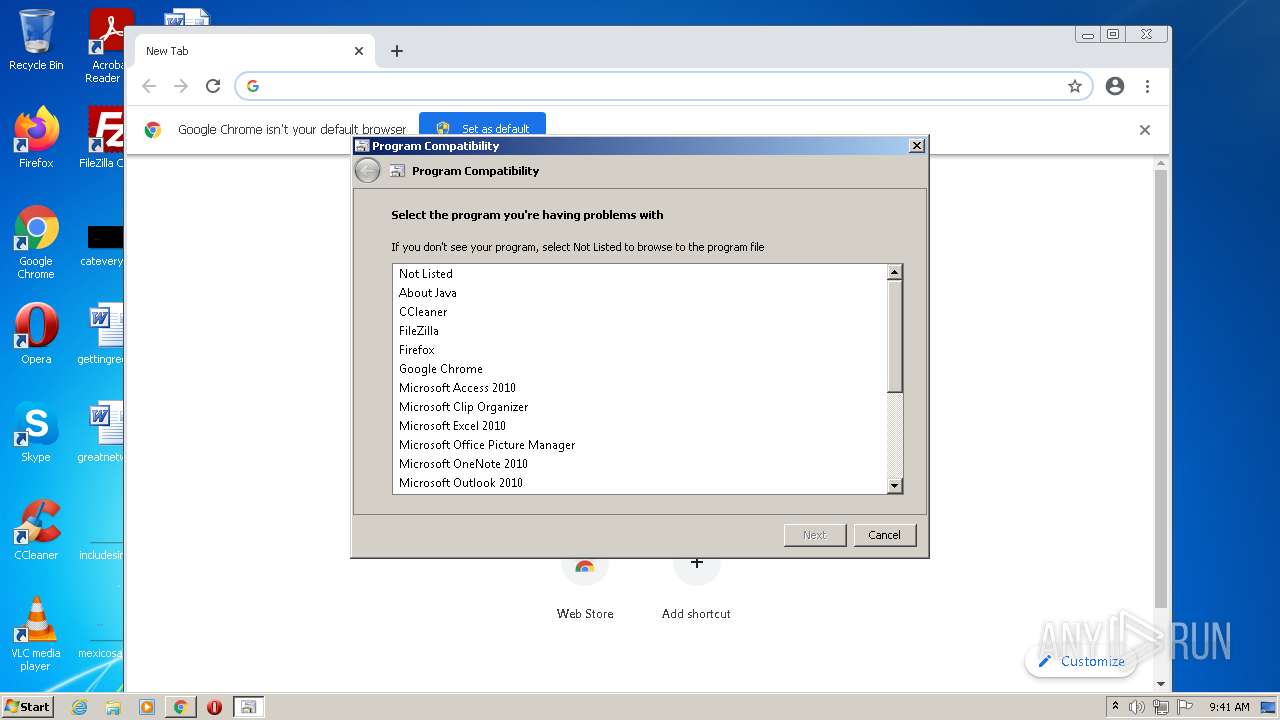
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2736)
Reads the computer name
- WScript.exe (PID: 3940)
Checks supported languages
- WScript.exe (PID: 3940)
- csc.exe (PID: 2660)
- cvtres.exe (PID: 2824)
- csc.exe (PID: 3092)
- cvtres.exe (PID: 3484)
- csc.exe (PID: 2176)
- cvtres.exe (PID: 3608)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1996)
Executable content was dropped or overwritten
- msdt.exe (PID: 3532)
- csc.exe (PID: 2660)
- csc.exe (PID: 3092)
- csc.exe (PID: 2176)
Executed via COM
- sdiagnhost.exe (PID: 1108)
Drops a file with a compile date too recent
- msdt.exe (PID: 3532)
- csc.exe (PID: 2660)
- csc.exe (PID: 3092)
- csc.exe (PID: 2176)
INFO
Checks supported languages
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 2736)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 1740)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 1312)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 3396)
- msdt.exe (PID: 3532)
- sdiagnhost.exe (PID: 1108)
- chrome.exe (PID: 1316)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 884)
Reads the computer name
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 2736)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 3644)
- msdt.exe (PID: 3532)
- sdiagnhost.exe (PID: 1108)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 1316)
- chrome.exe (PID: 884)
Application launched itself
- iexplore.exe (PID: 2548)
- chrome.exe (PID: 1996)
Changes internet zones settings
- iexplore.exe (PID: 2548)
Reads settings of System Certificates
- iexplore.exe (PID: 2736)
- iexplore.exe (PID: 2548)
- chrome.exe (PID: 4044)
- msdt.exe (PID: 3532)
Checks Windows Trust Settings
- iexplore.exe (PID: 2736)
- iexplore.exe (PID: 2548)
- WScript.exe (PID: 3940)
- msdt.exe (PID: 3532)
- sdiagnhost.exe (PID: 1108)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2548)
Changes settings of System certificates
- iexplore.exe (PID: 2548)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2548)
Reads the date of Windows installation
- iexplore.exe (PID: 2548)
- chrome.exe (PID: 1316)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2548)
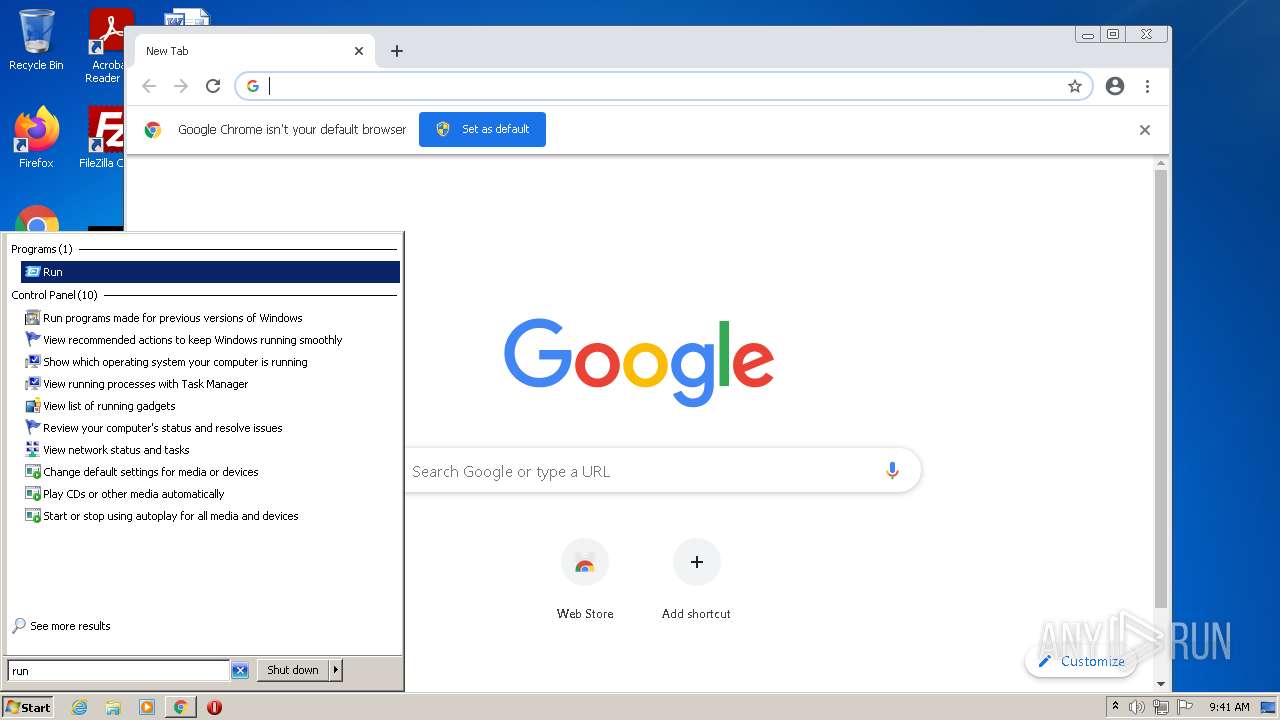
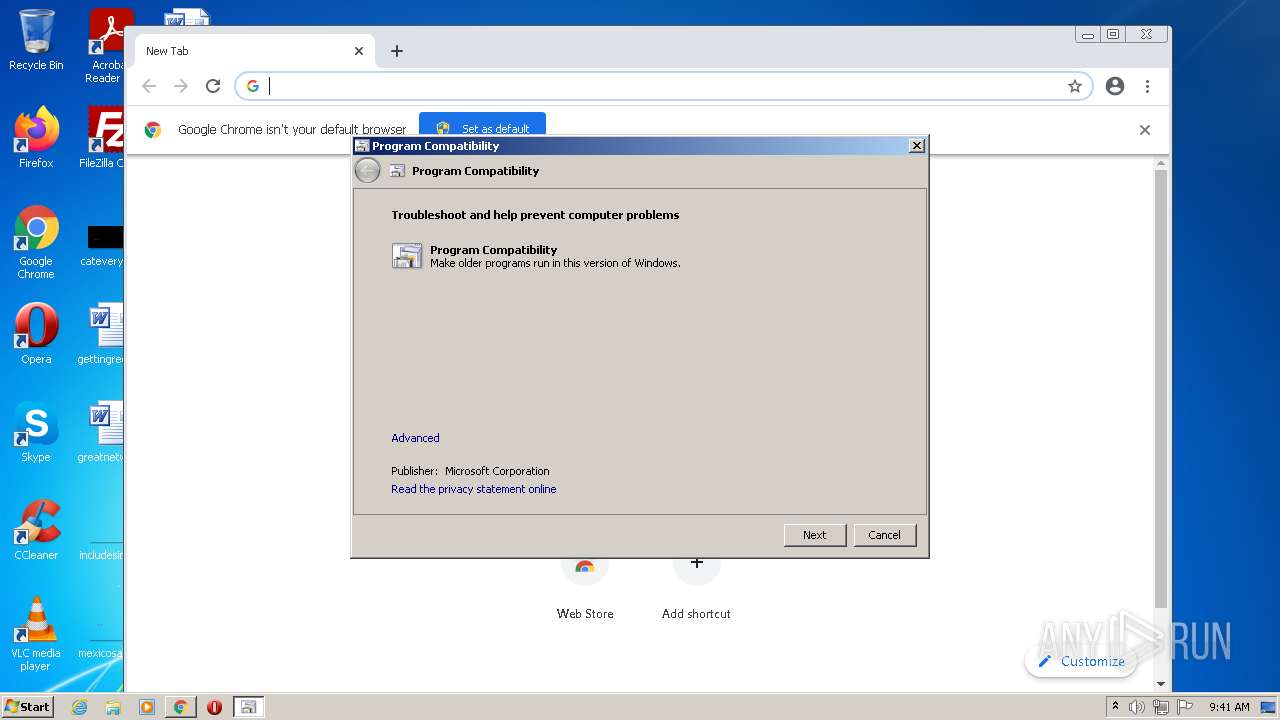
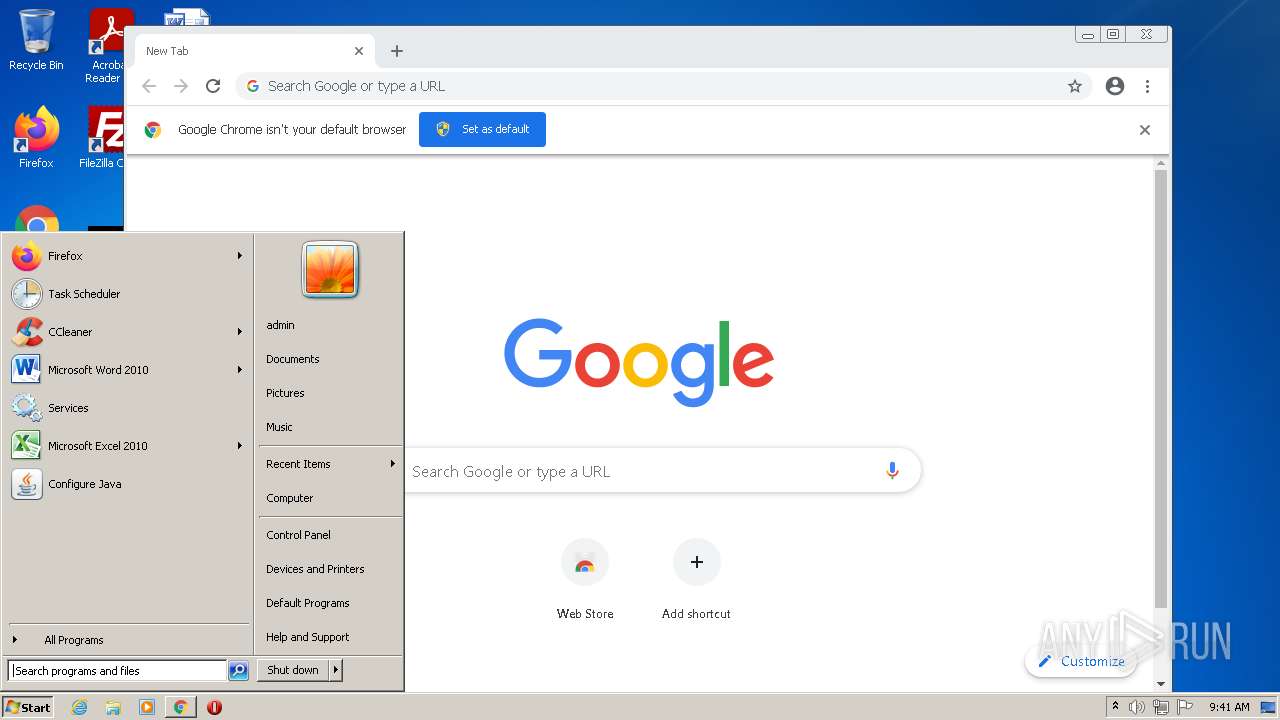
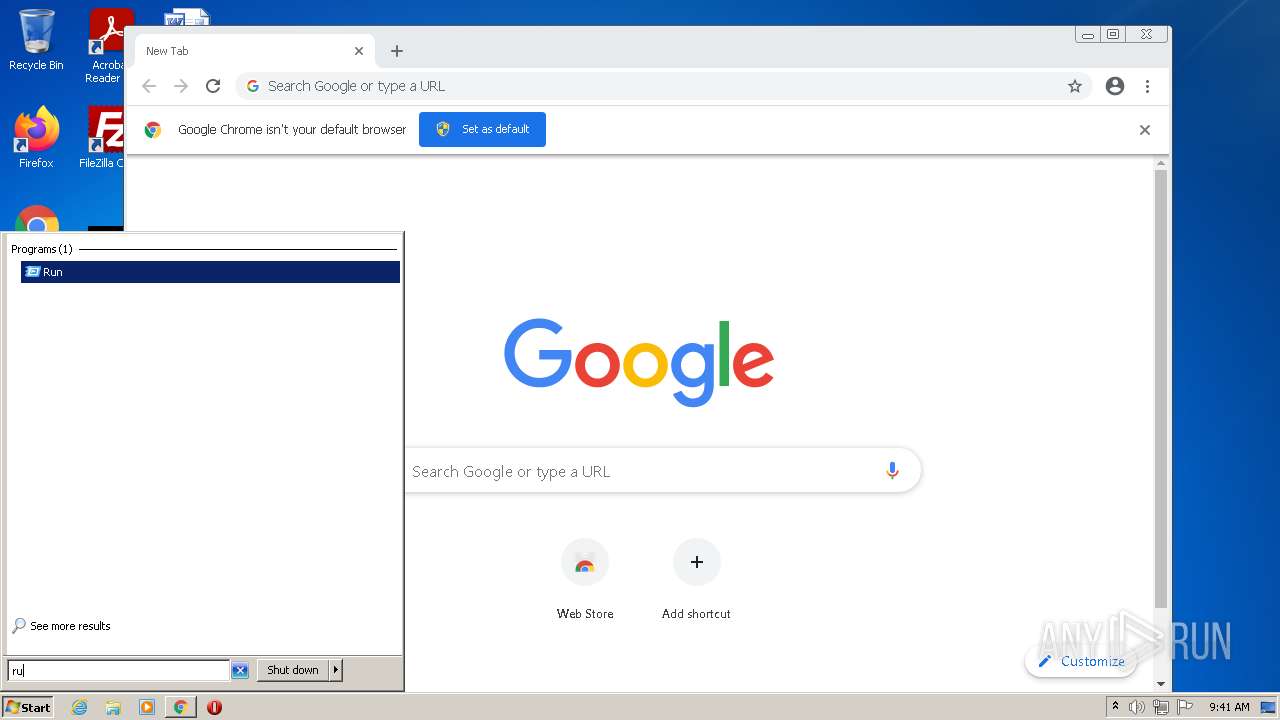
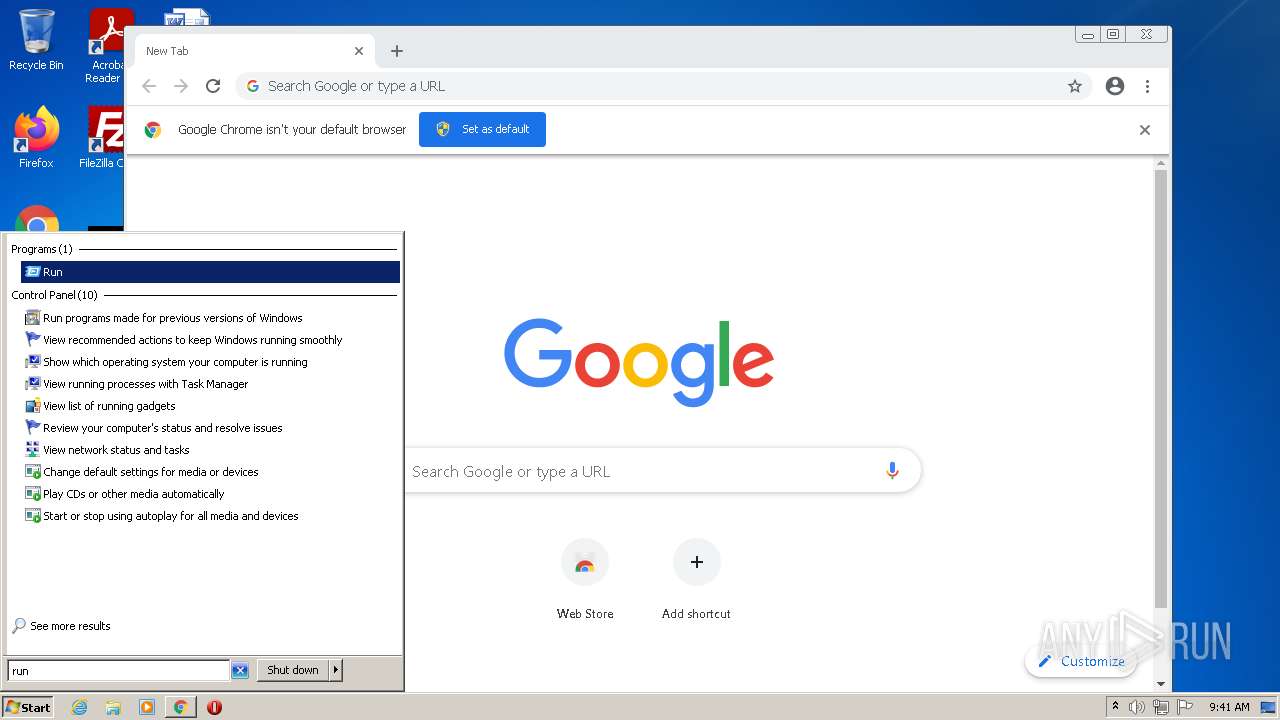
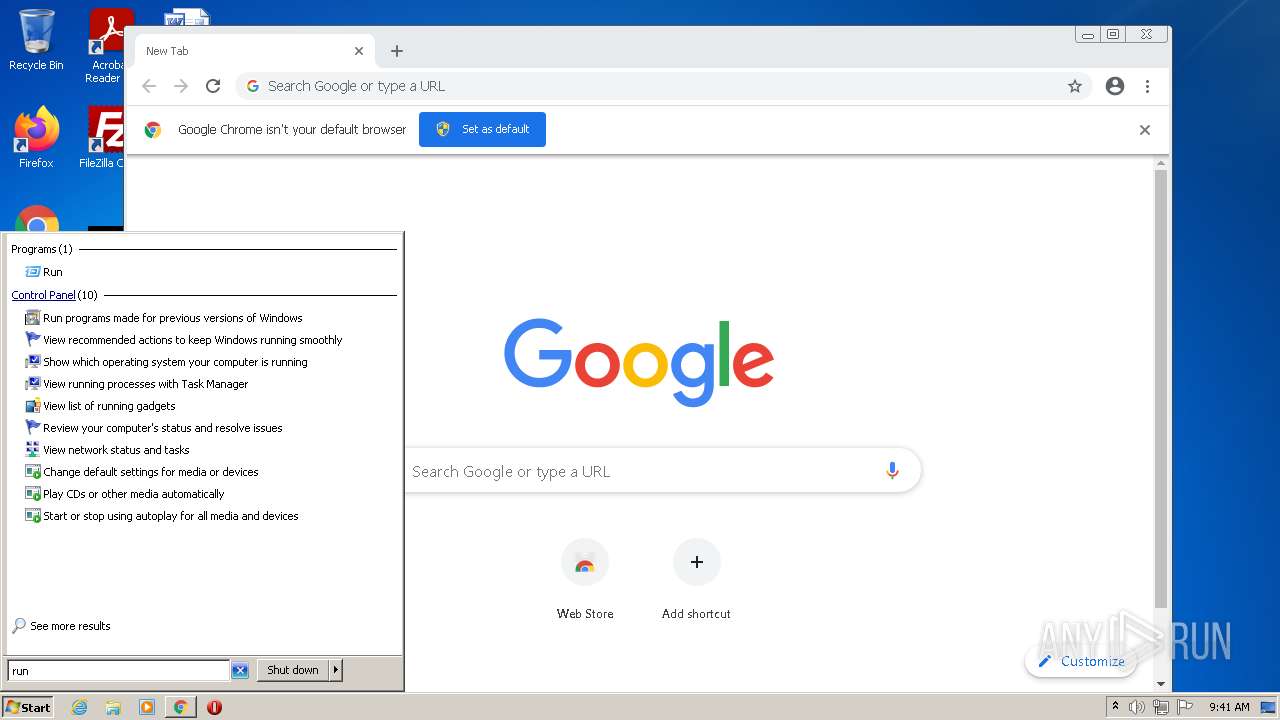
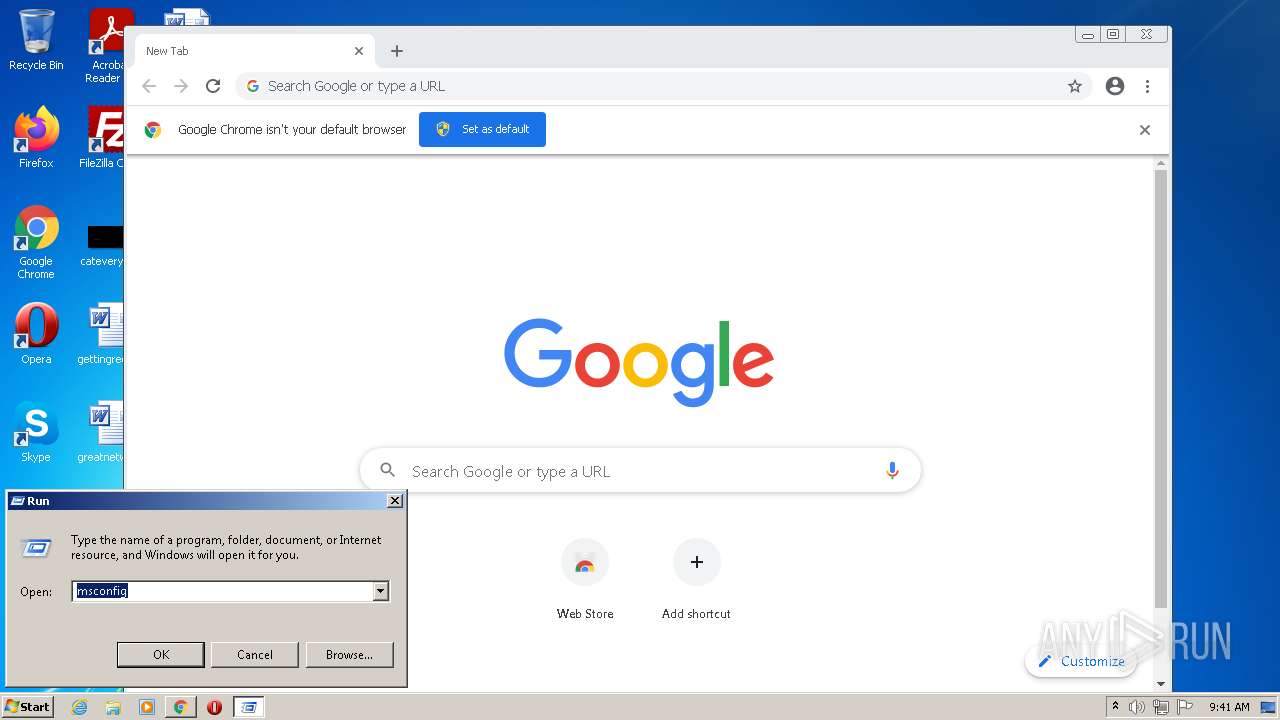
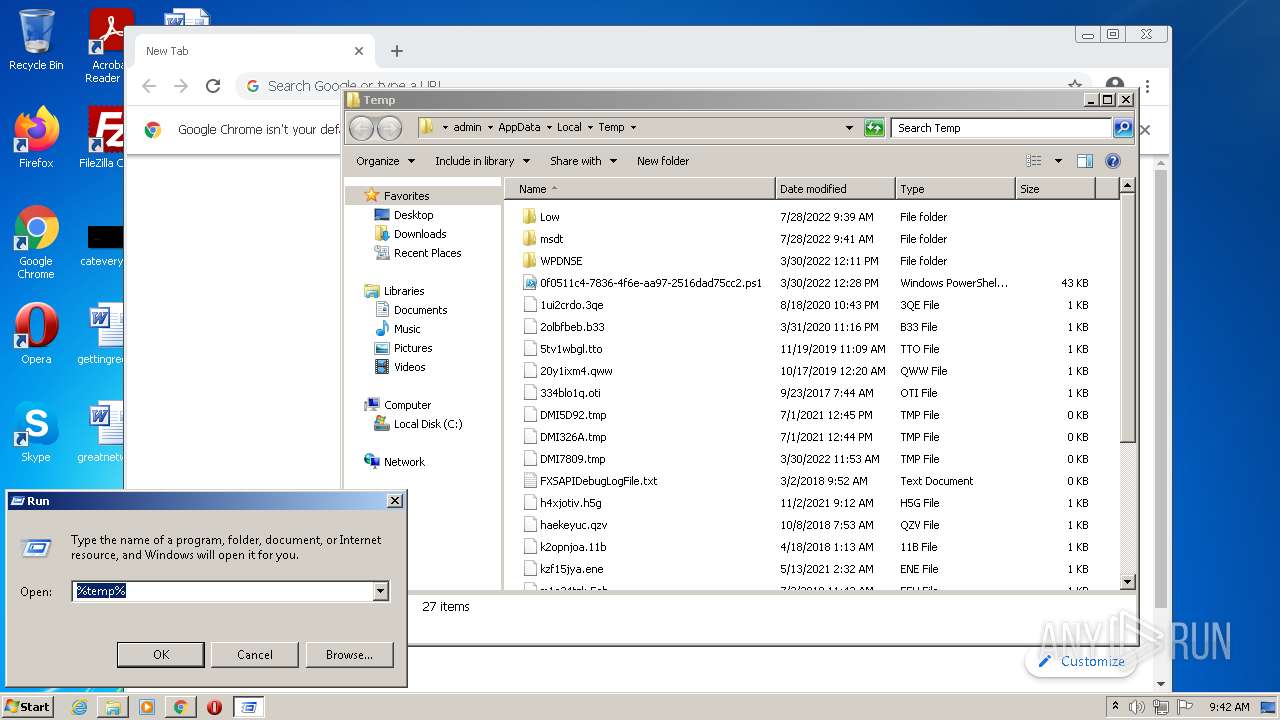
Manual execution by user
- chrome.exe (PID: 1996)
- msdt.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
27
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1072,11707681441962494001,6879226271775986138,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3428 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1072,11707681441962494001,6879226271775986138,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1072,11707681441962494001,6879226271775986138,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1072,11707681441962494001,6879226271775986138,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2176 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\tdvkyxsh.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://chimpstatic.com/mcjs-connected/js/users/7ae0d7371fd5f95f76804c2b0/04177c15aa57e3bea1ccd5ff5.js" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2660 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\m4bq5uo5.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1072,11707681441962494001,6879226271775986138,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
26 789
Read events
26 547
Write events
237
Delete events
5
Modification events
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30974557 | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30974557 | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2548) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
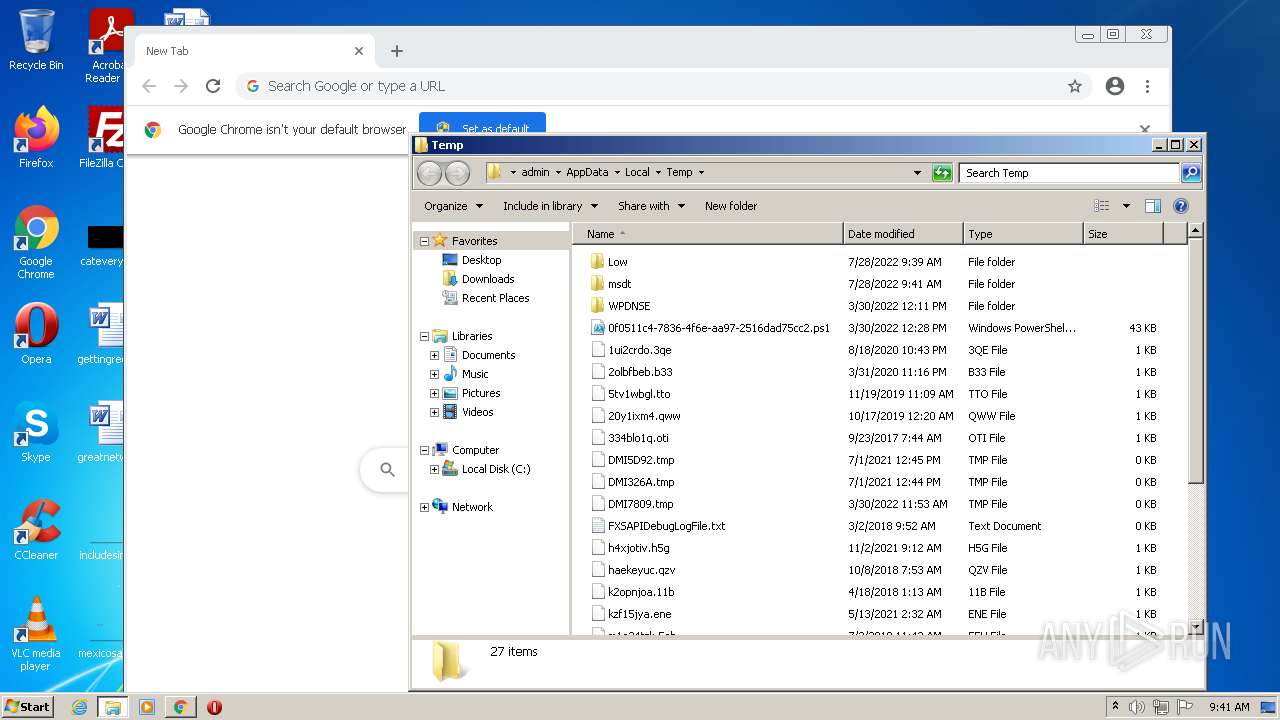
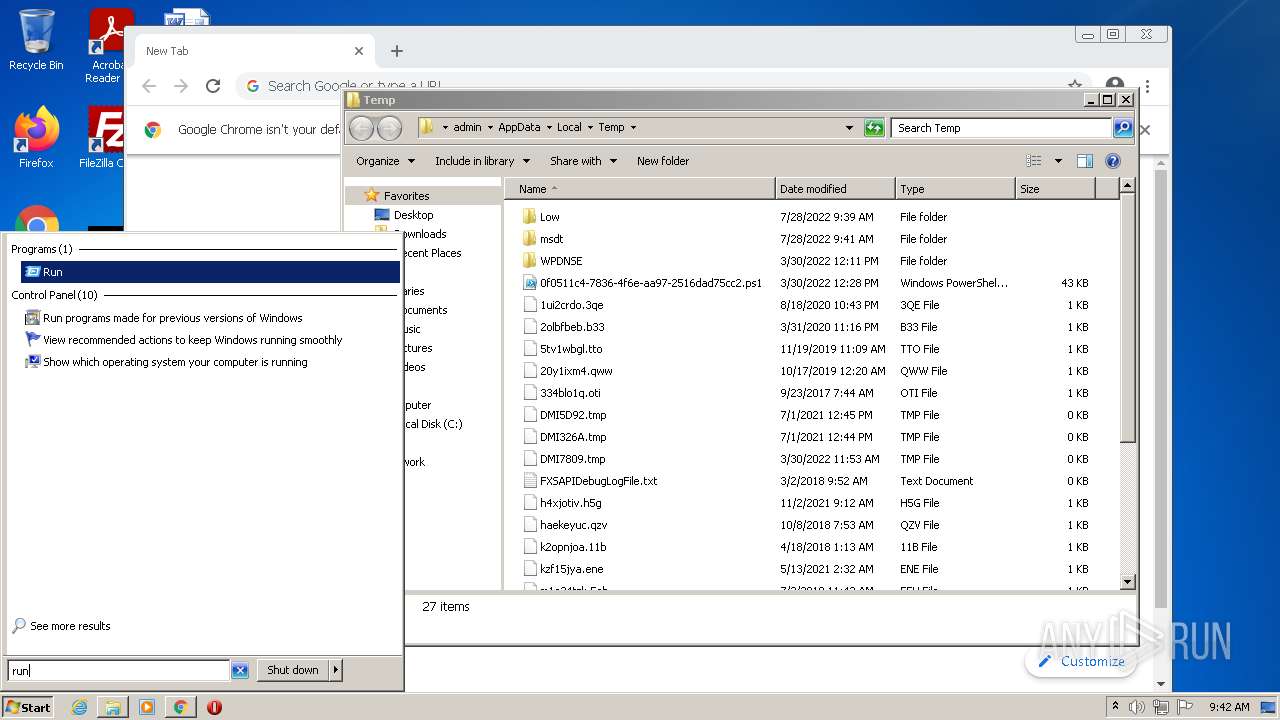
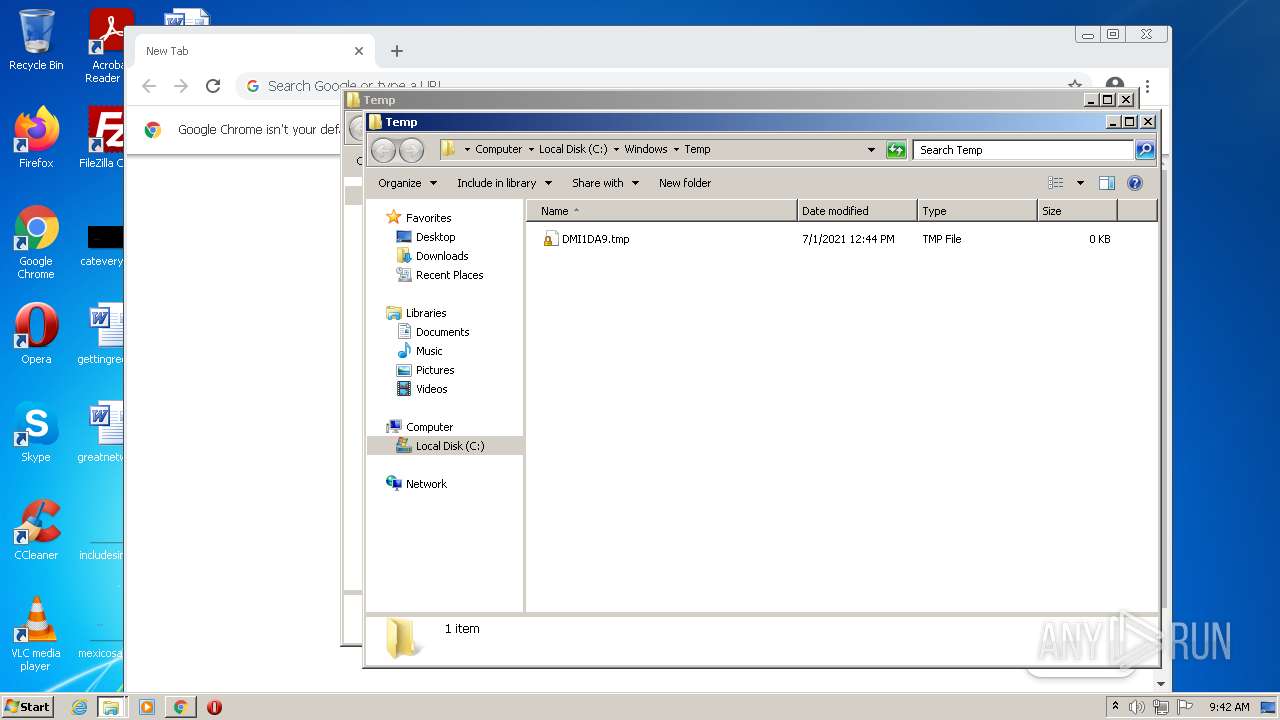
Executable files
5
Suspicious files
123
Text files
136
Unknown types
19
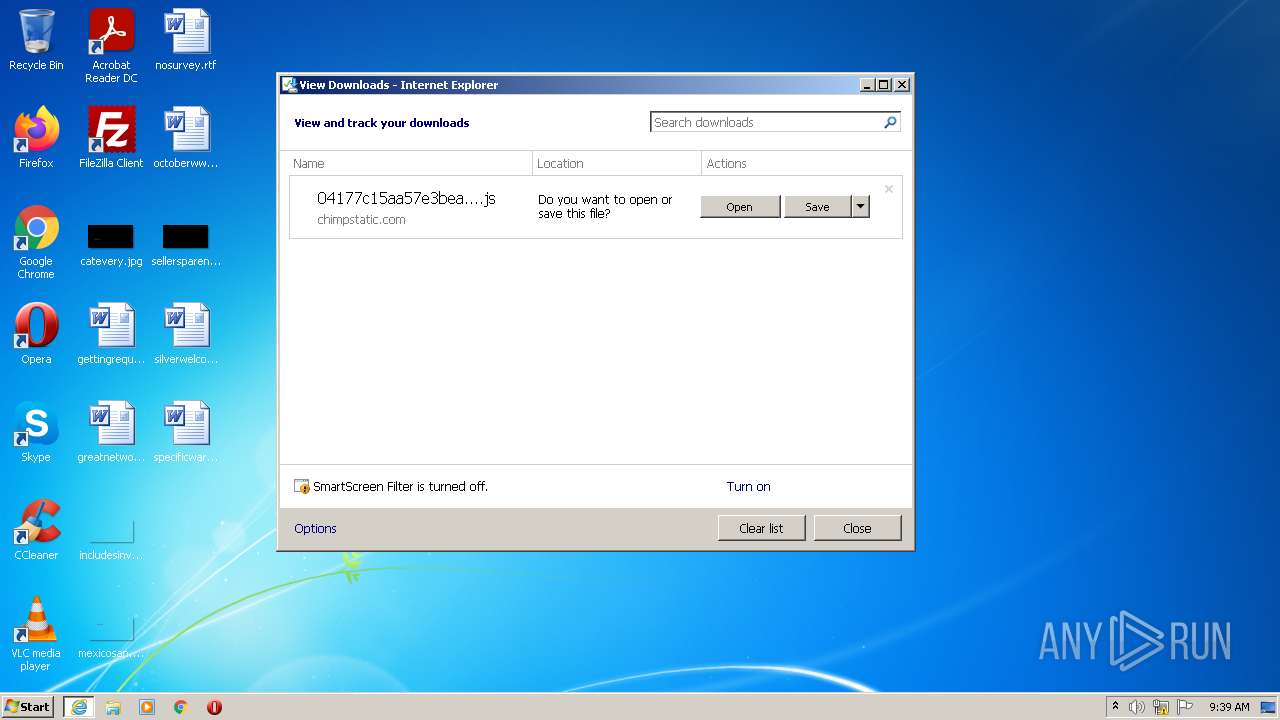
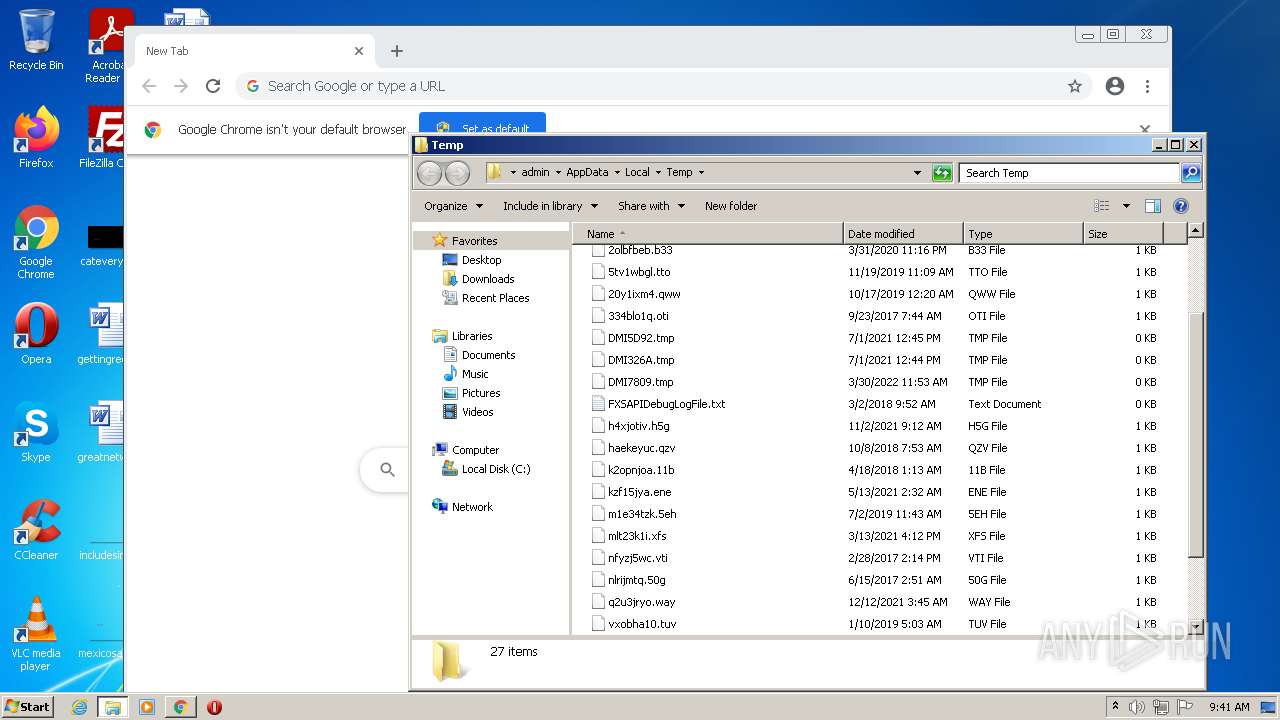
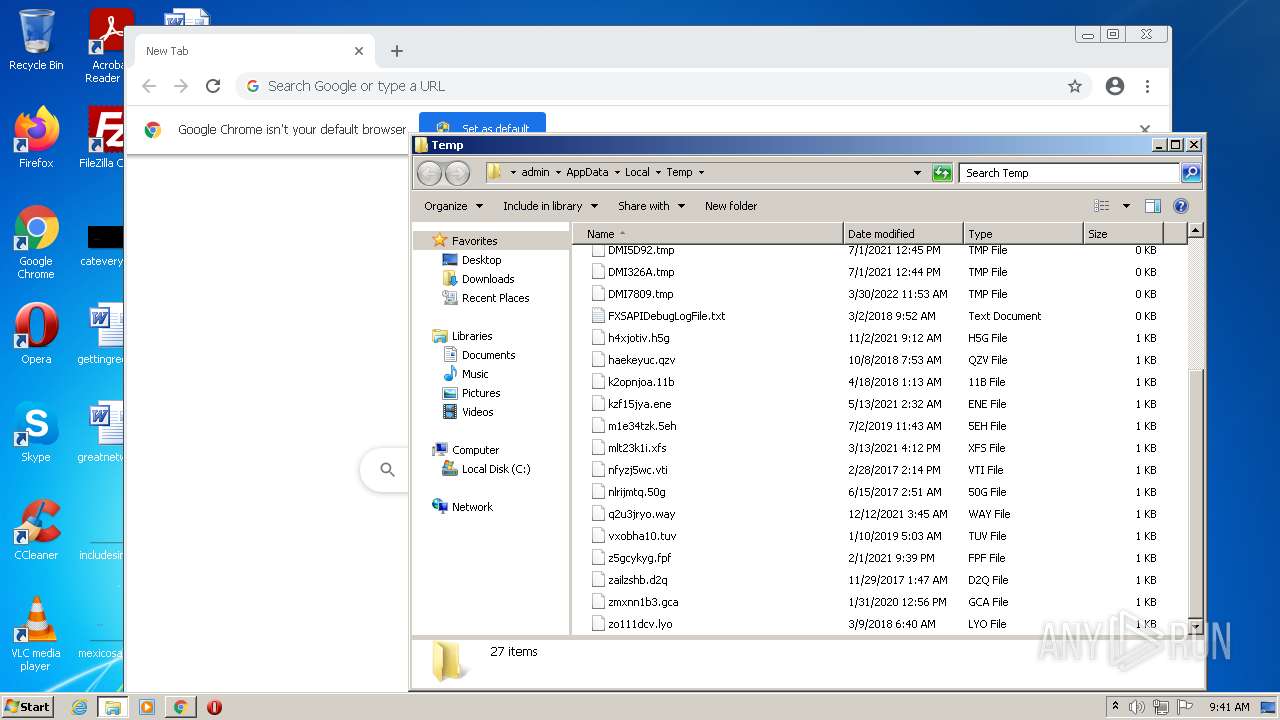
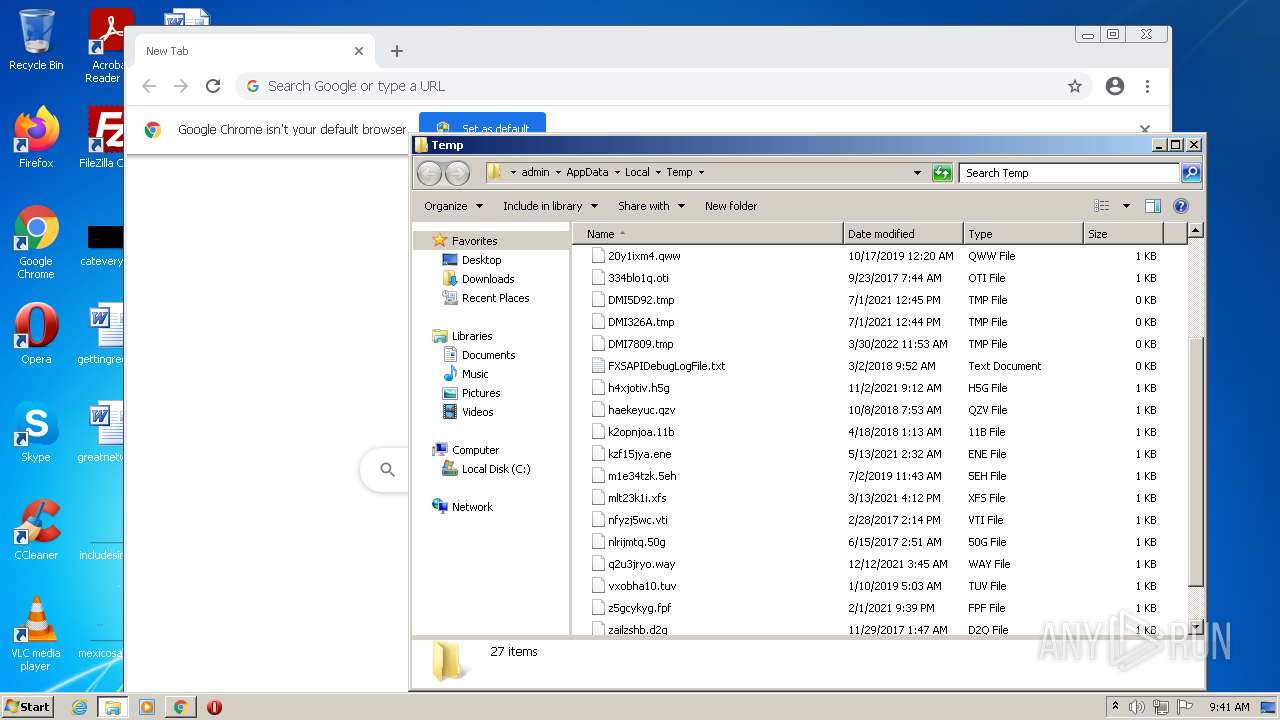
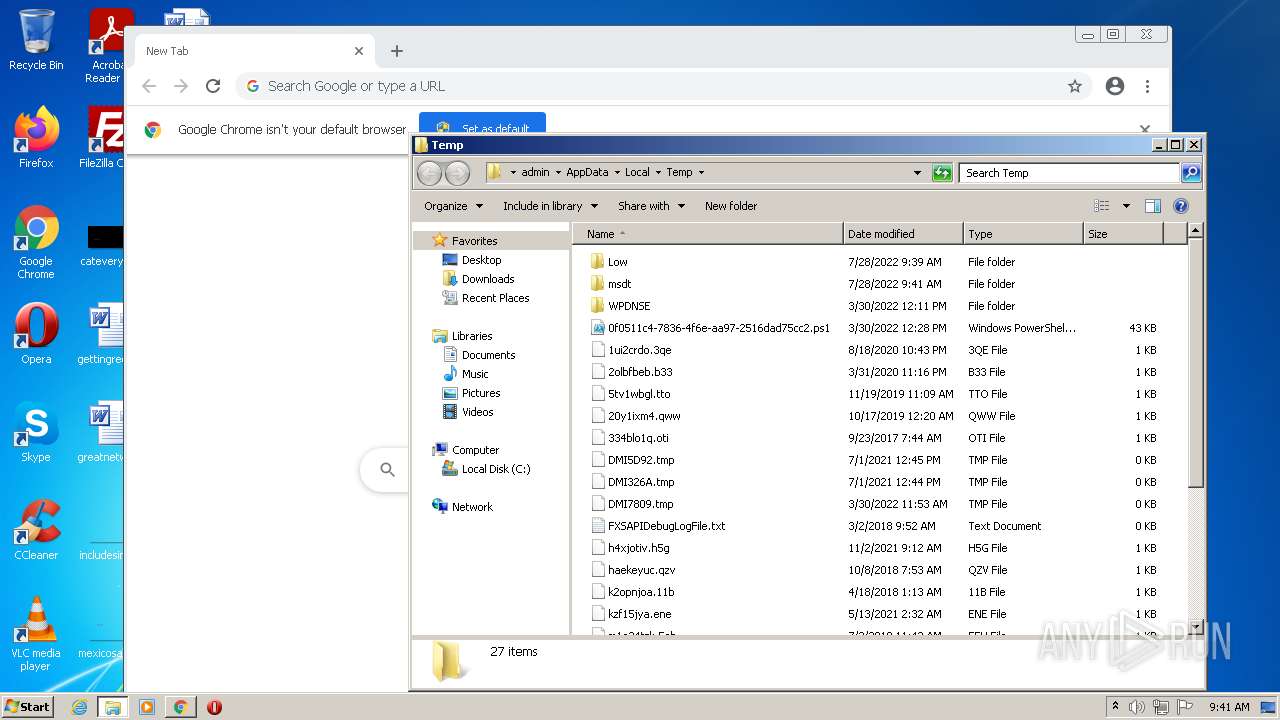
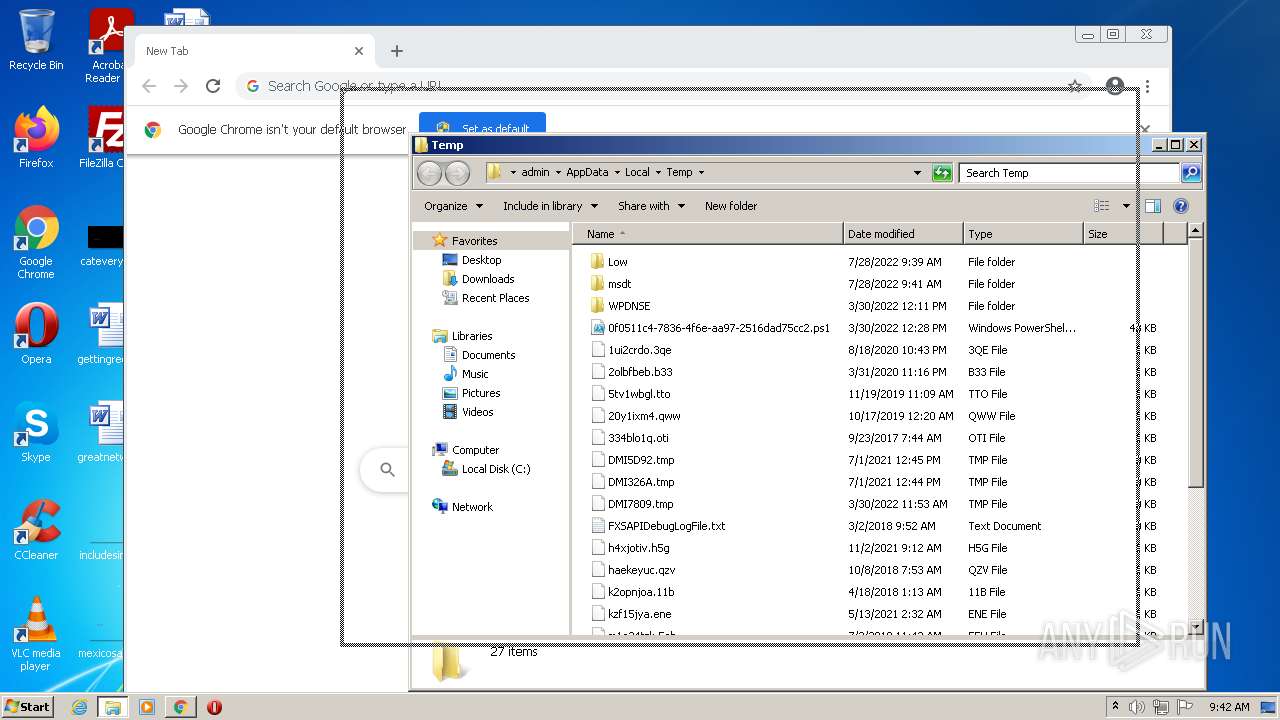
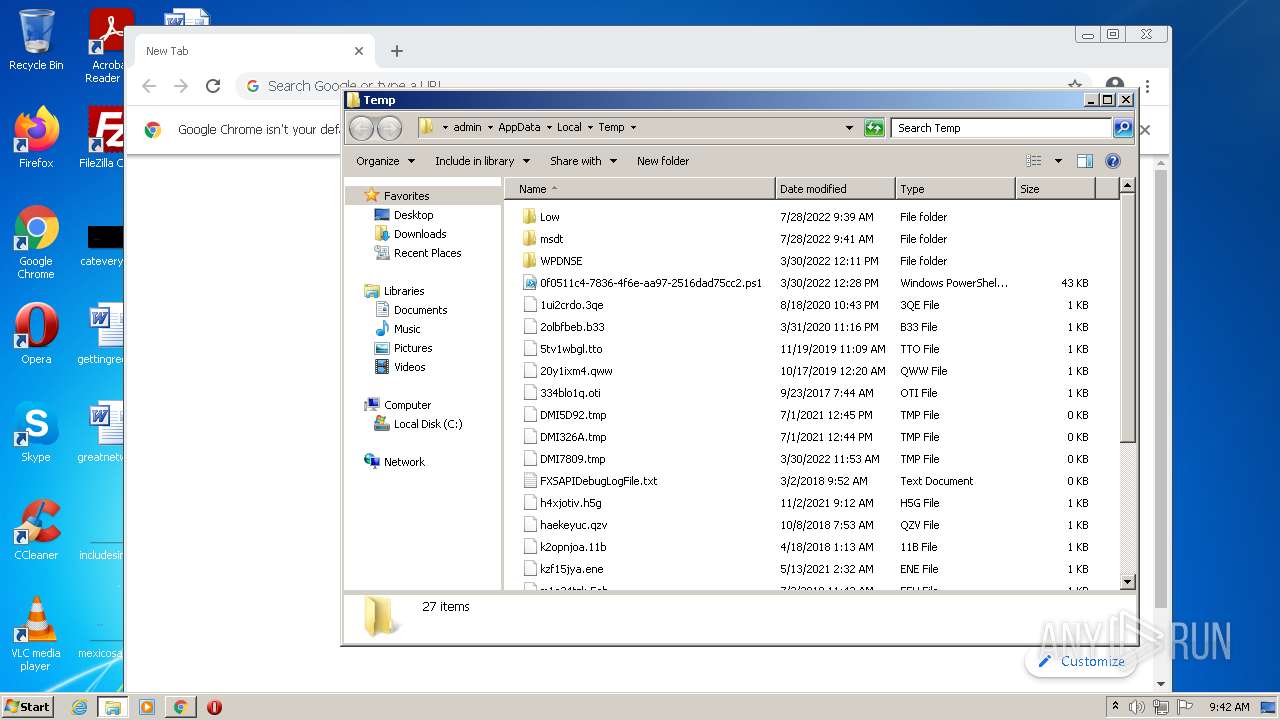
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\69C6F6EC64E114822DF688DC12CDD86C | der | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\04177c15aa57e3bea1ccd5ff5[1].js | text | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\69C6F6EC64E114822DF688DC12CDD86C | binary | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{BBD0DE59-0E50-11ED-AE3F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7DEA676BDA97D5B3.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\76ALHY0I.txt | text | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\04177c15aa57e3bea1ccd5ff5.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
38
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
2548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2548 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e23a1cf438697d91 | US | compressed | 4.70 Kb | whitelisted |
4044 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl2/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
2736 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?684e7b3ad5972330 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2736 | iexplore.exe | 92.123.22.86:443 | chimpstatic.com | Telia Company AB | FR | unknown |
2736 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2548 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2736 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2548 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2548 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2548 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2548 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
2548 | iexplore.exe | 131.253.33.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chimpstatic.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|