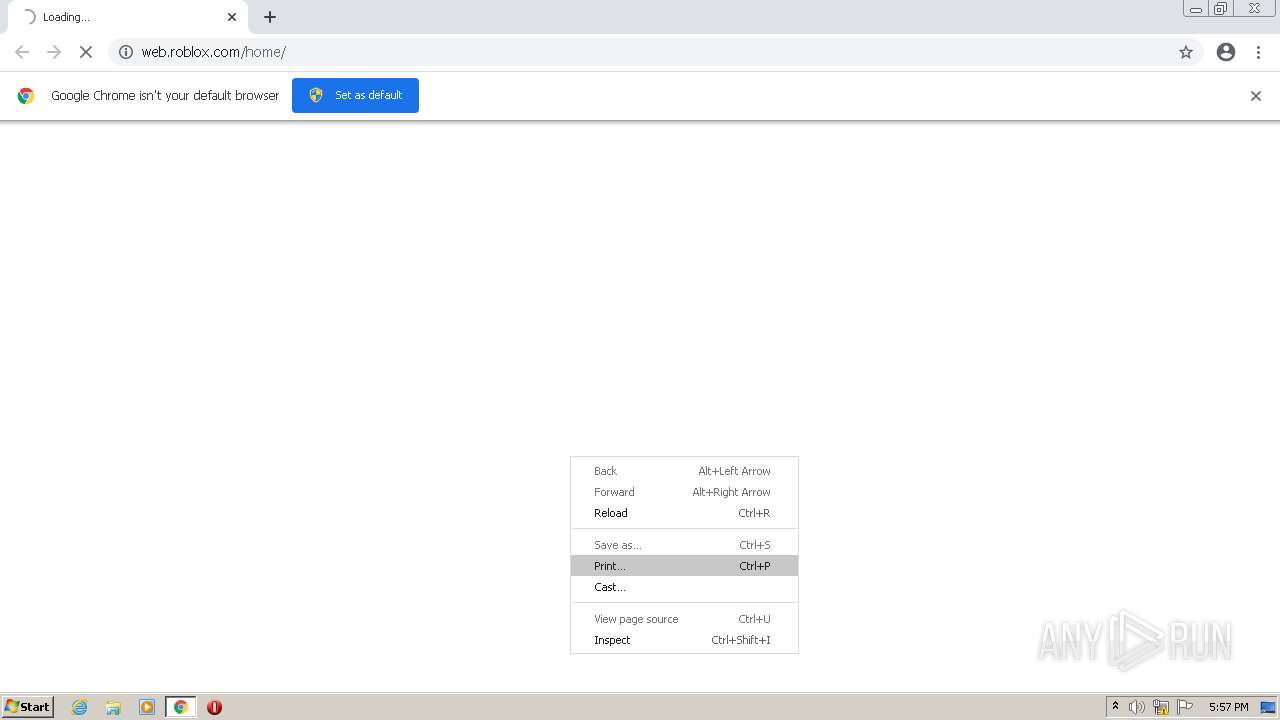
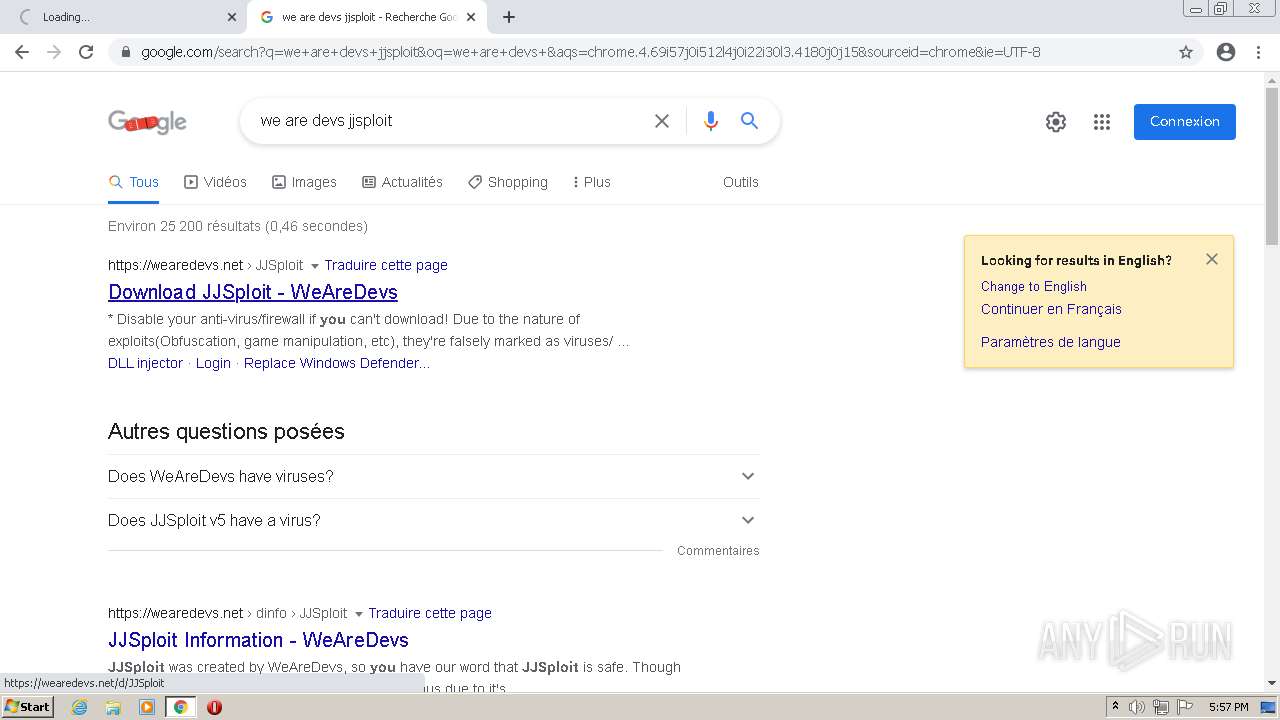
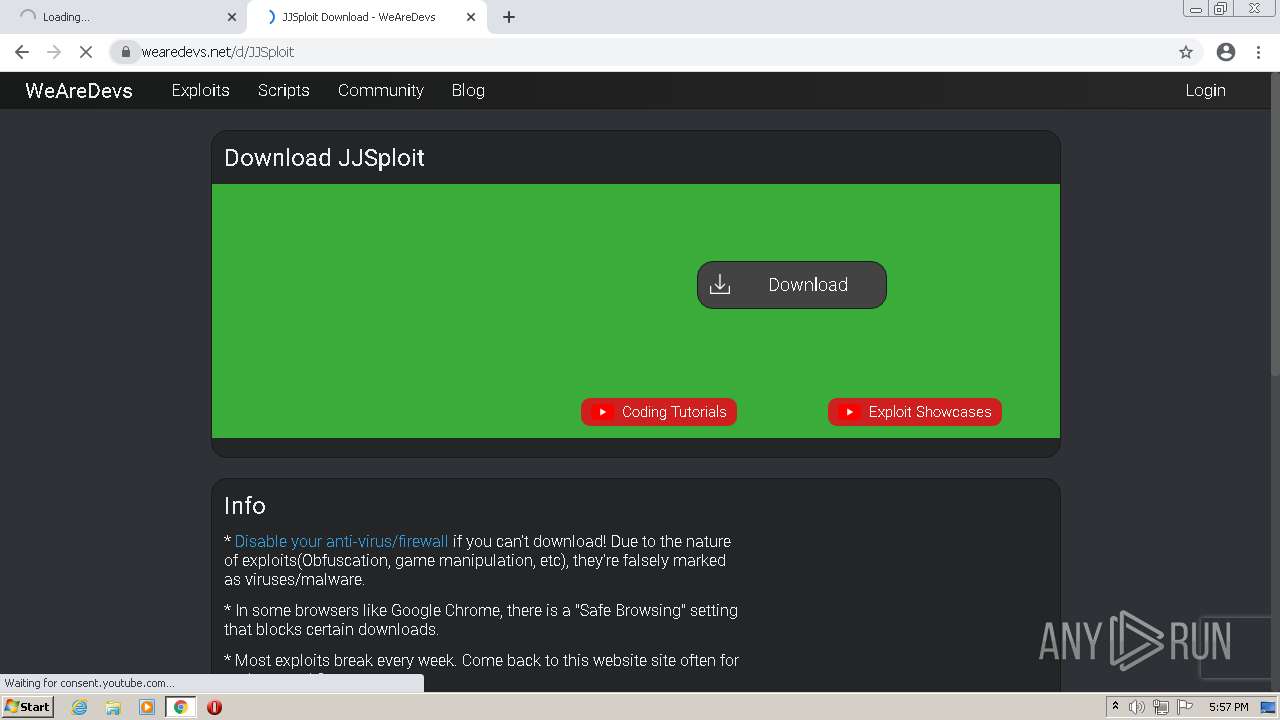
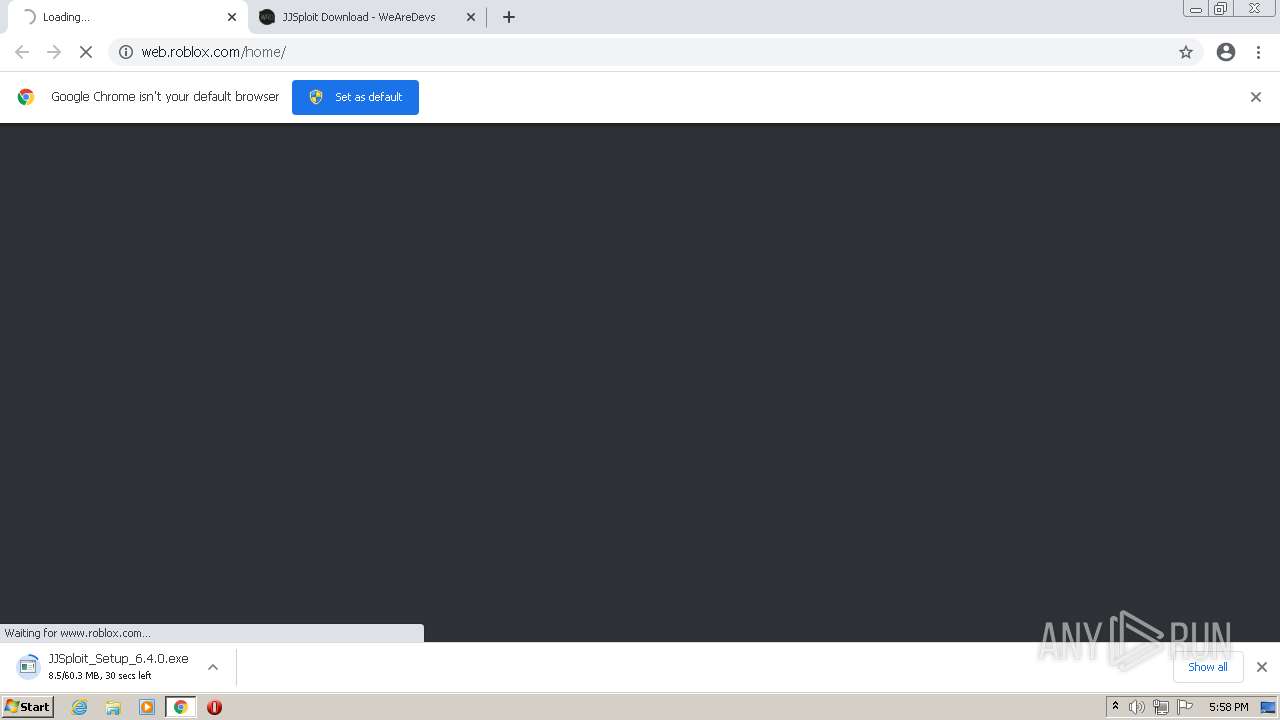
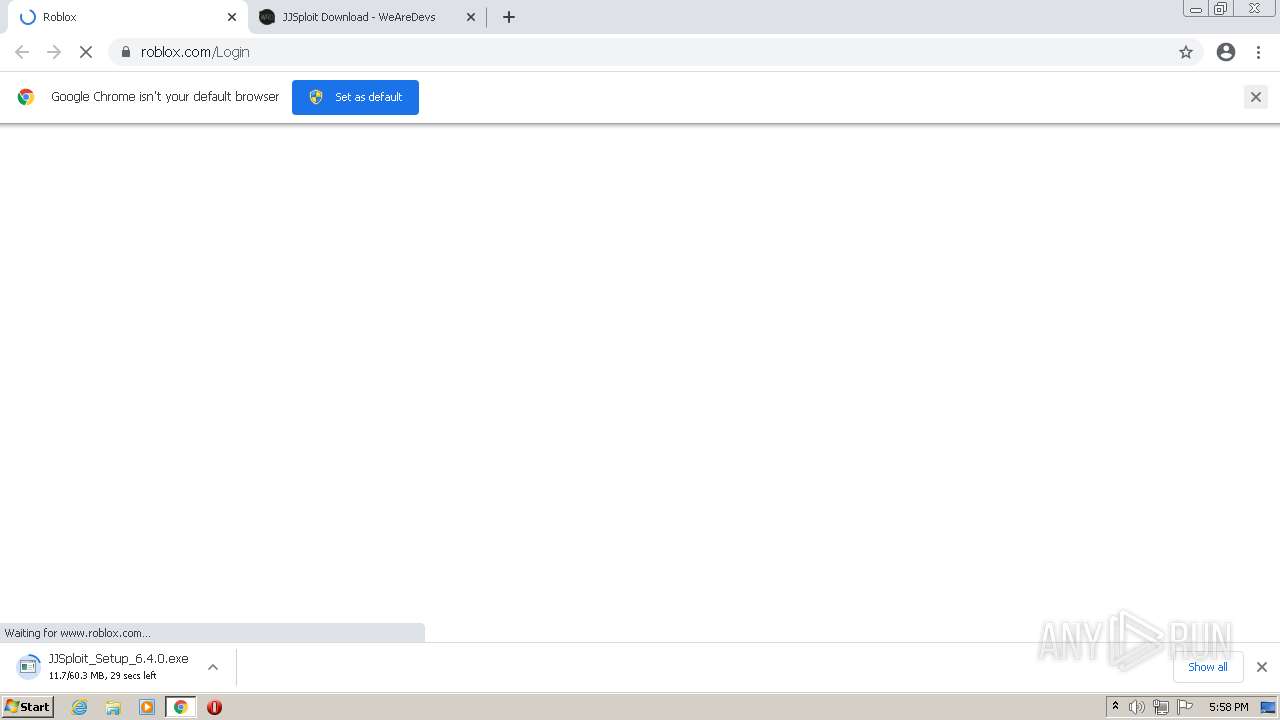
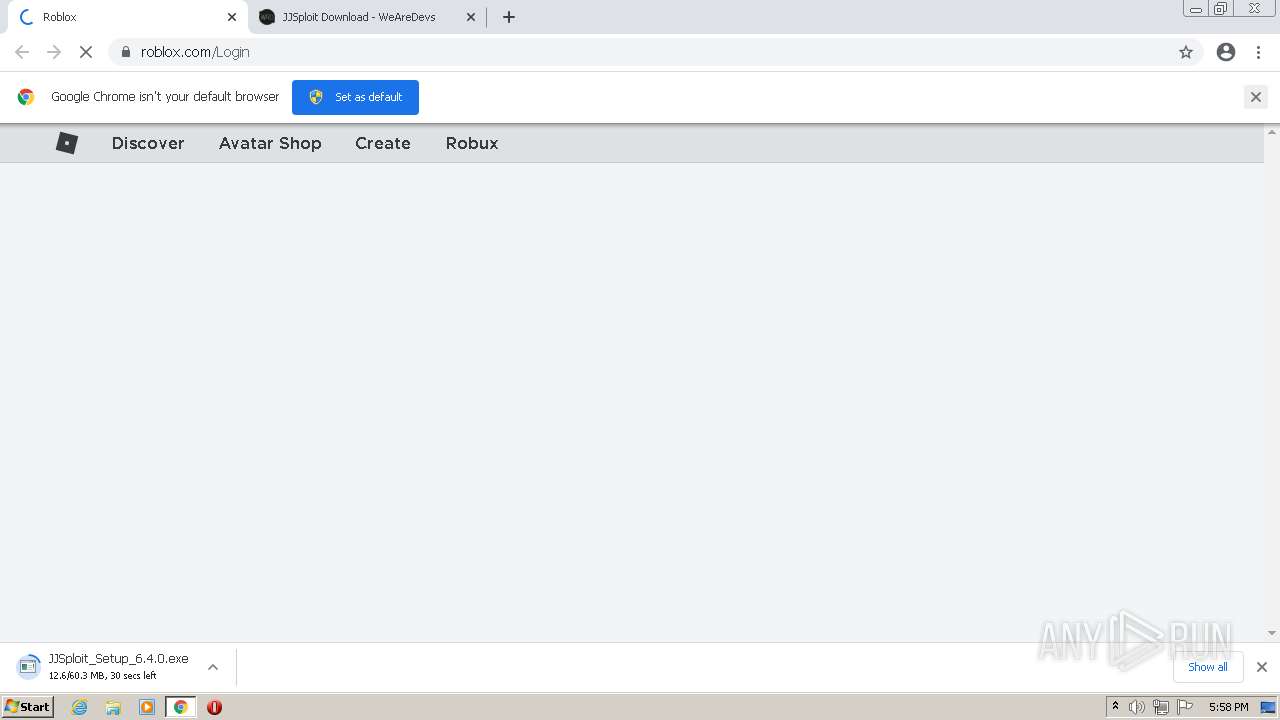
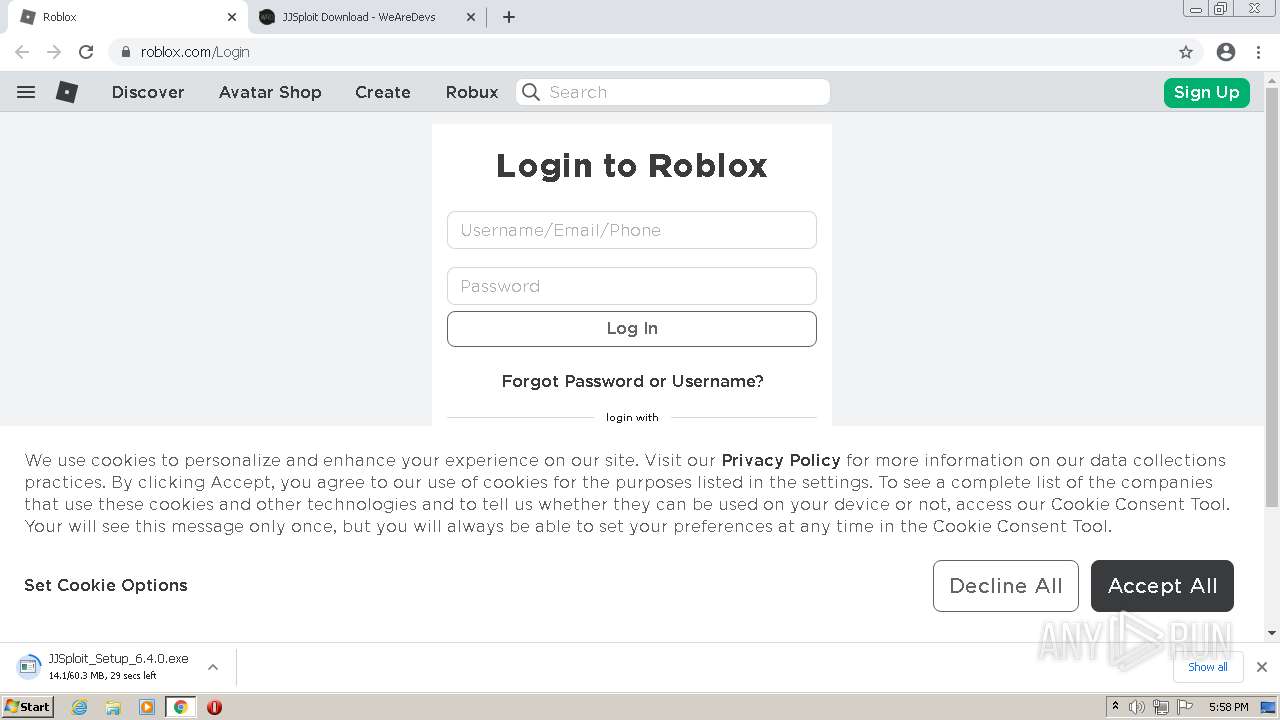
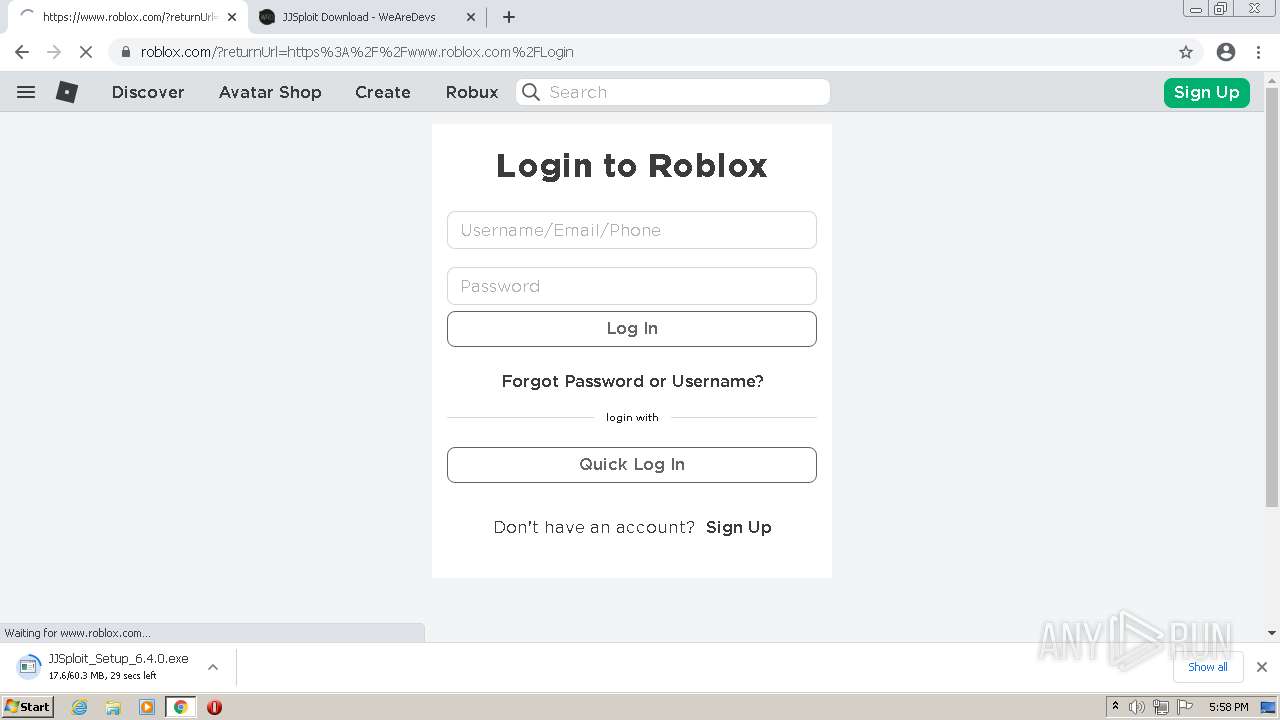
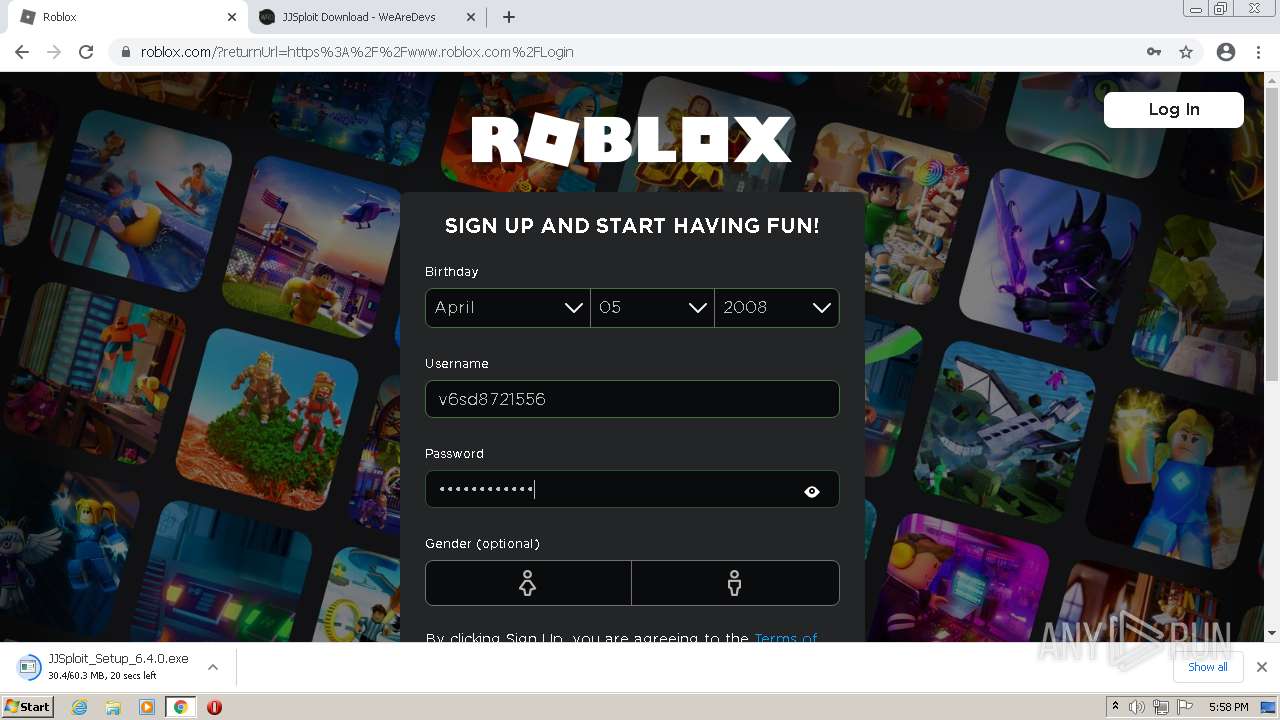
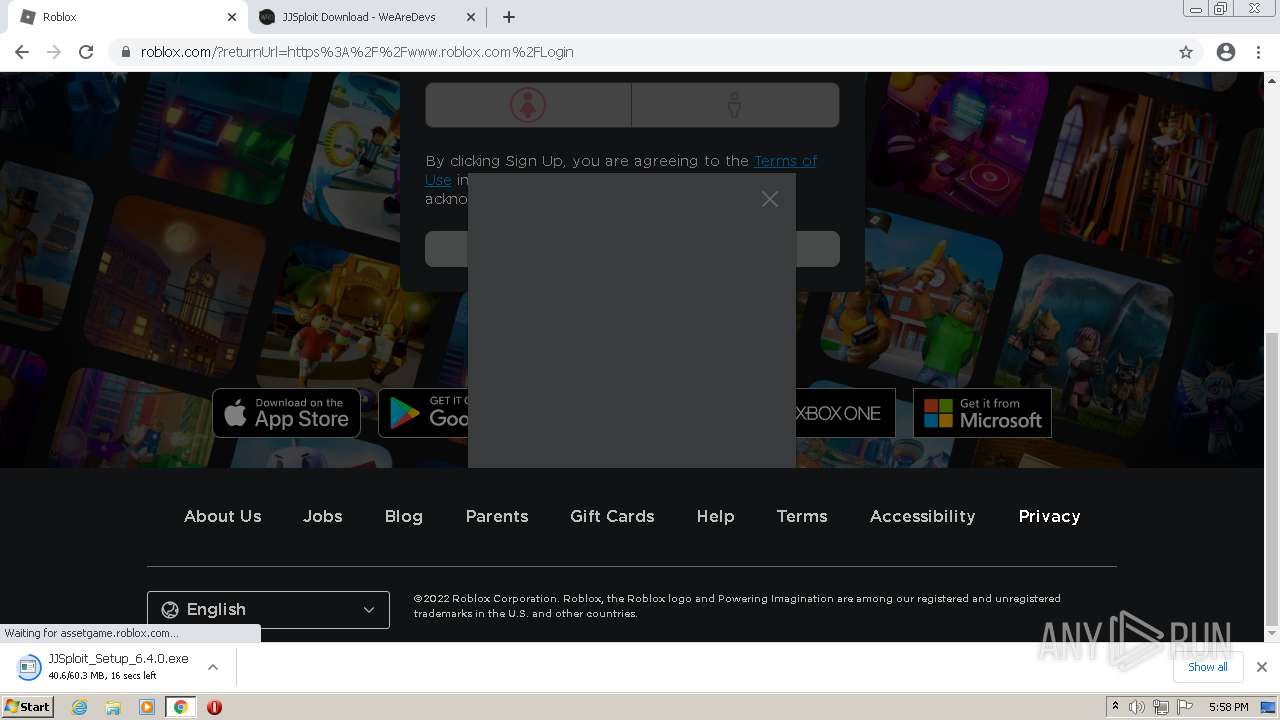
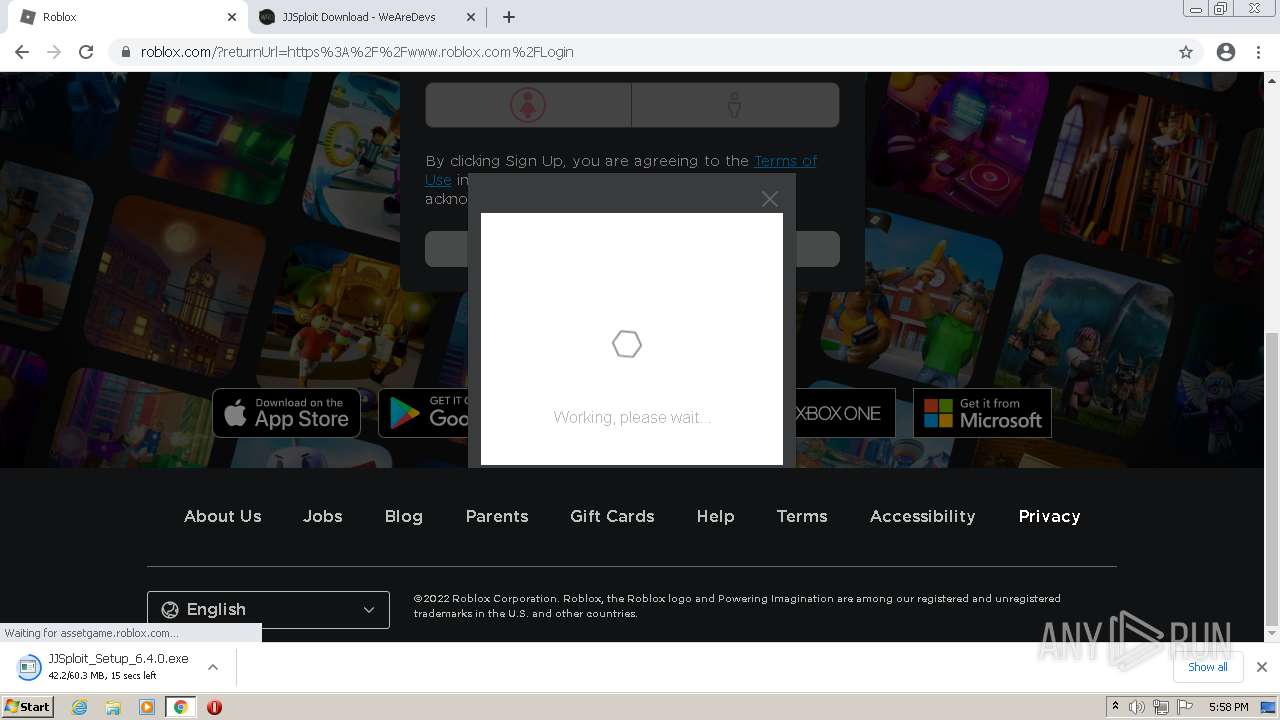
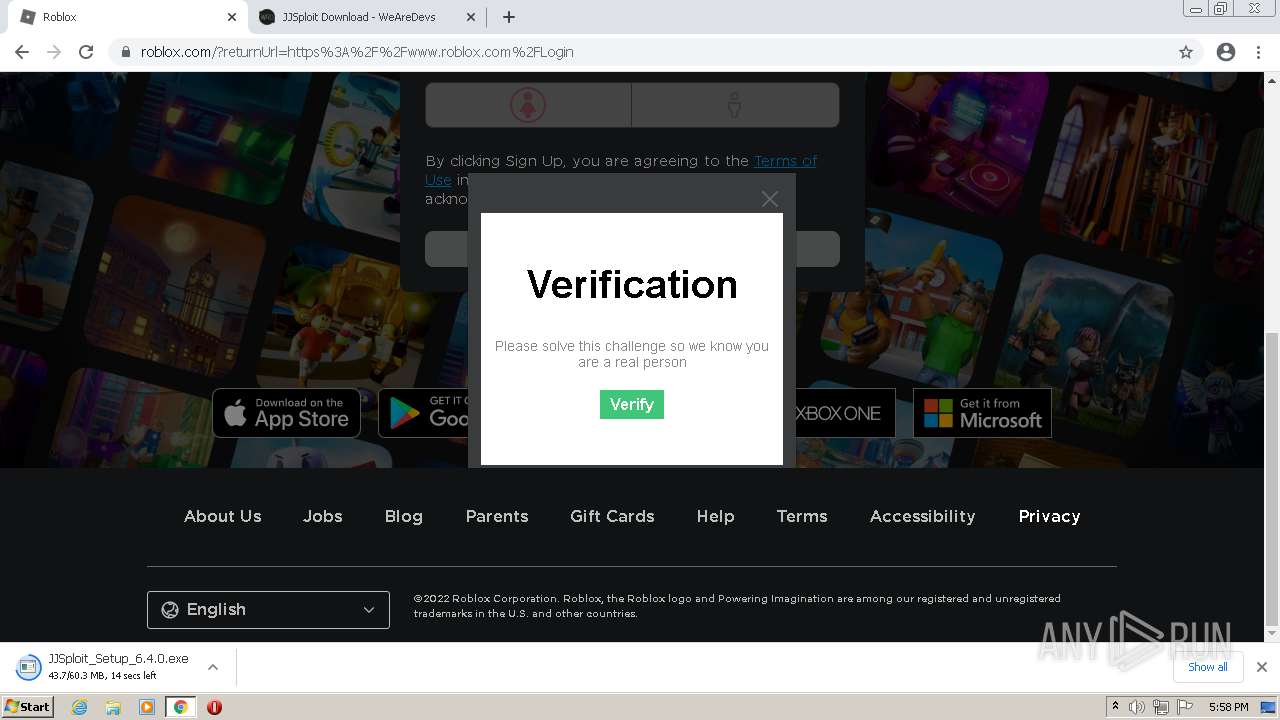
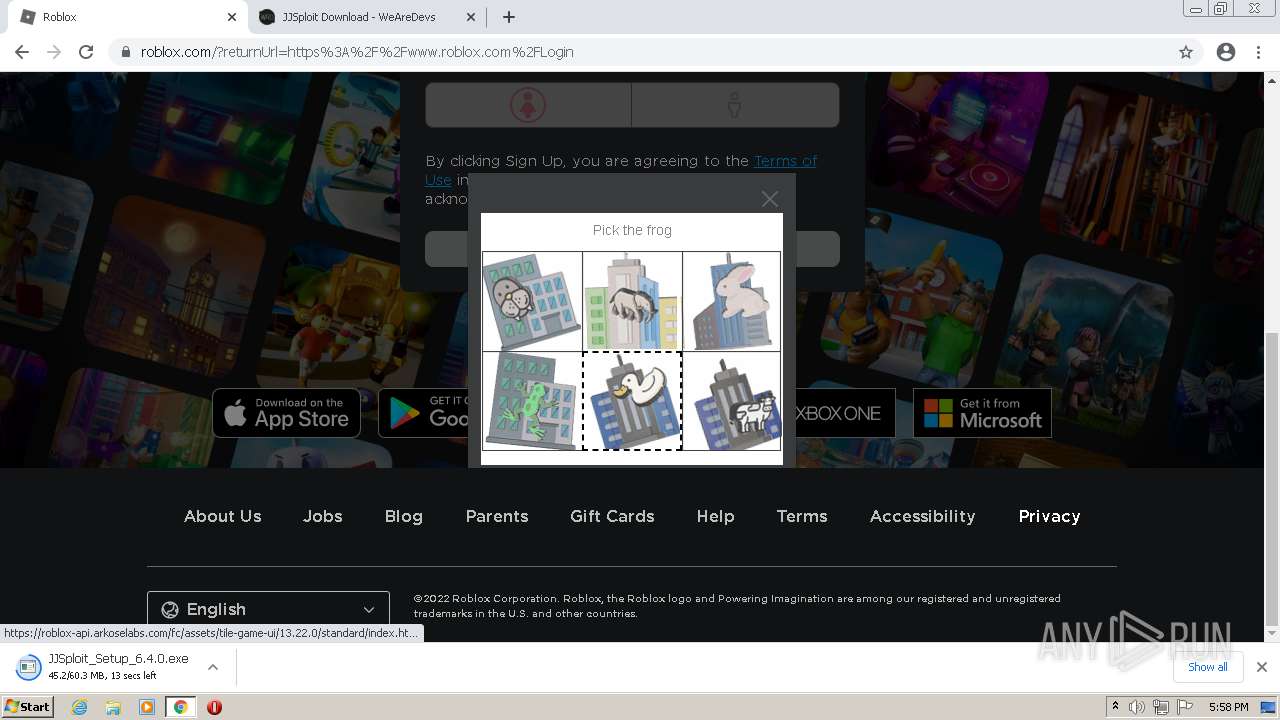
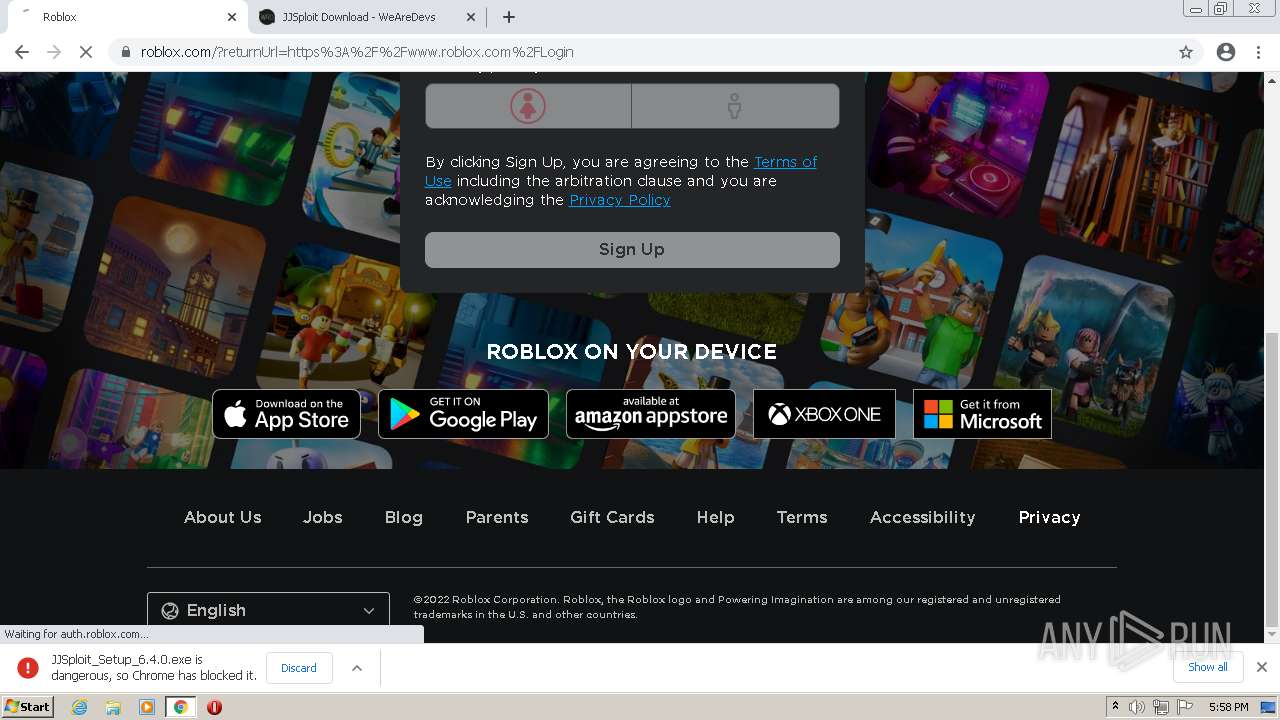
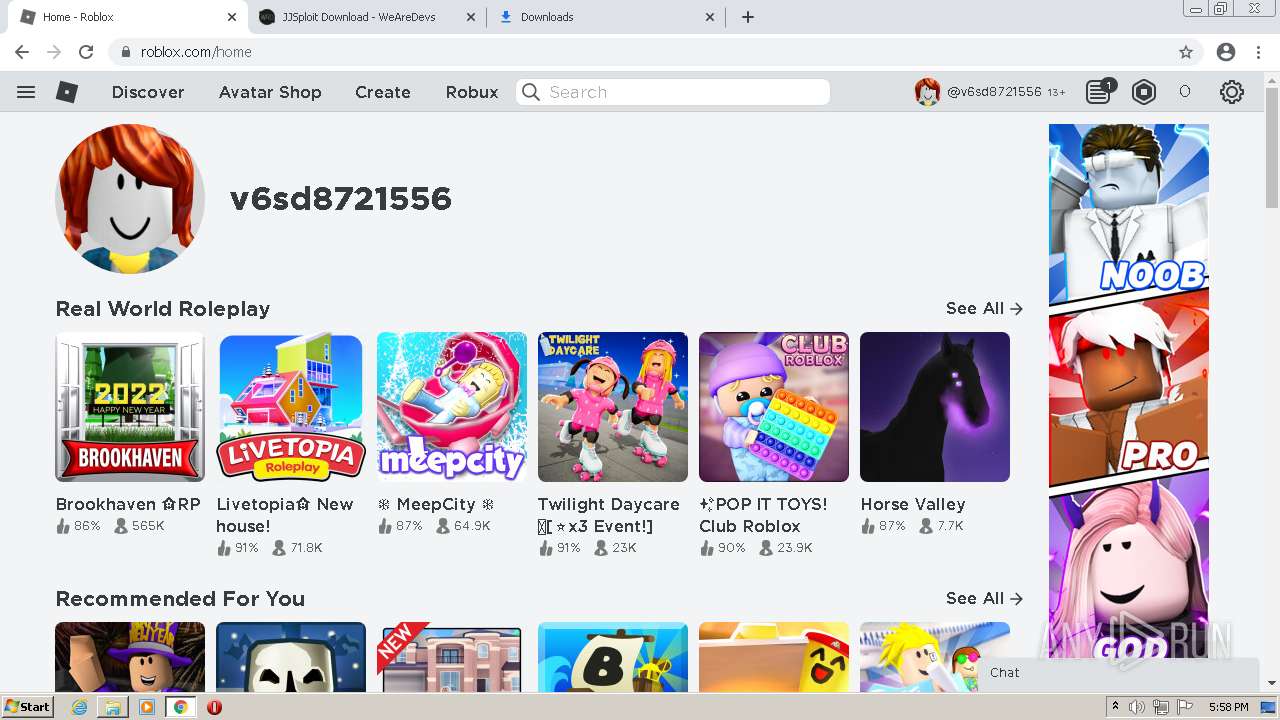
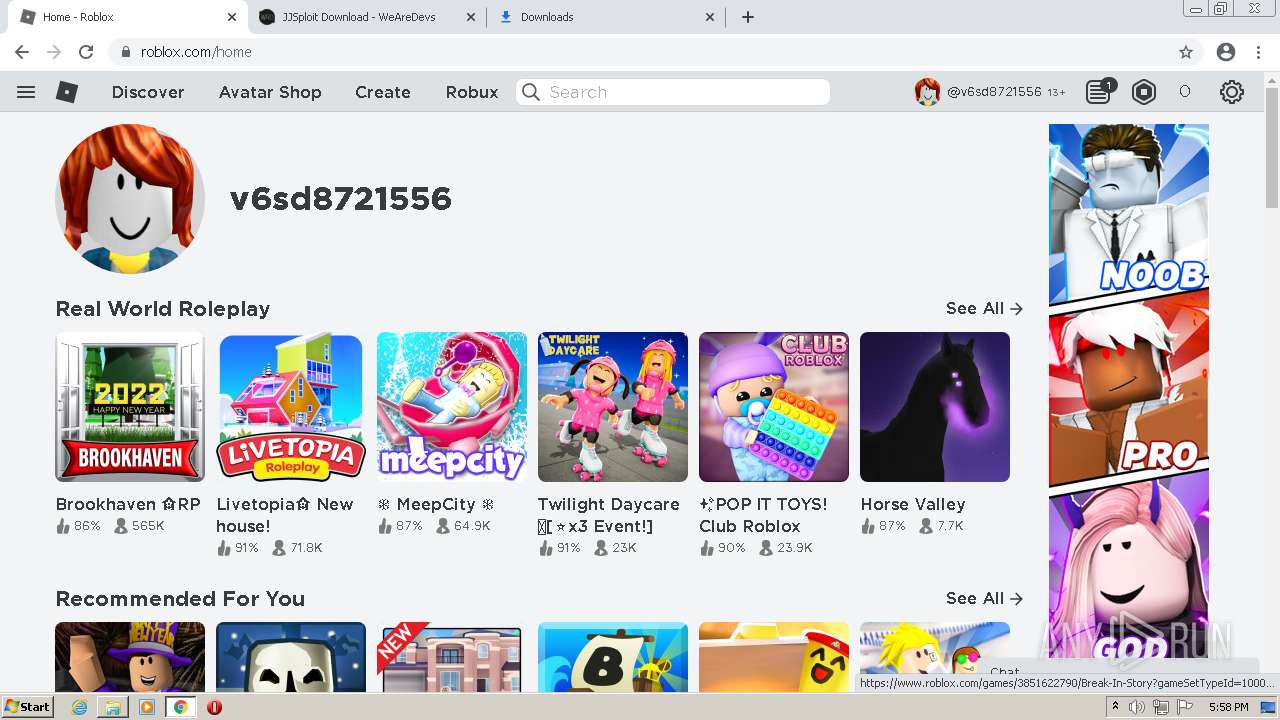
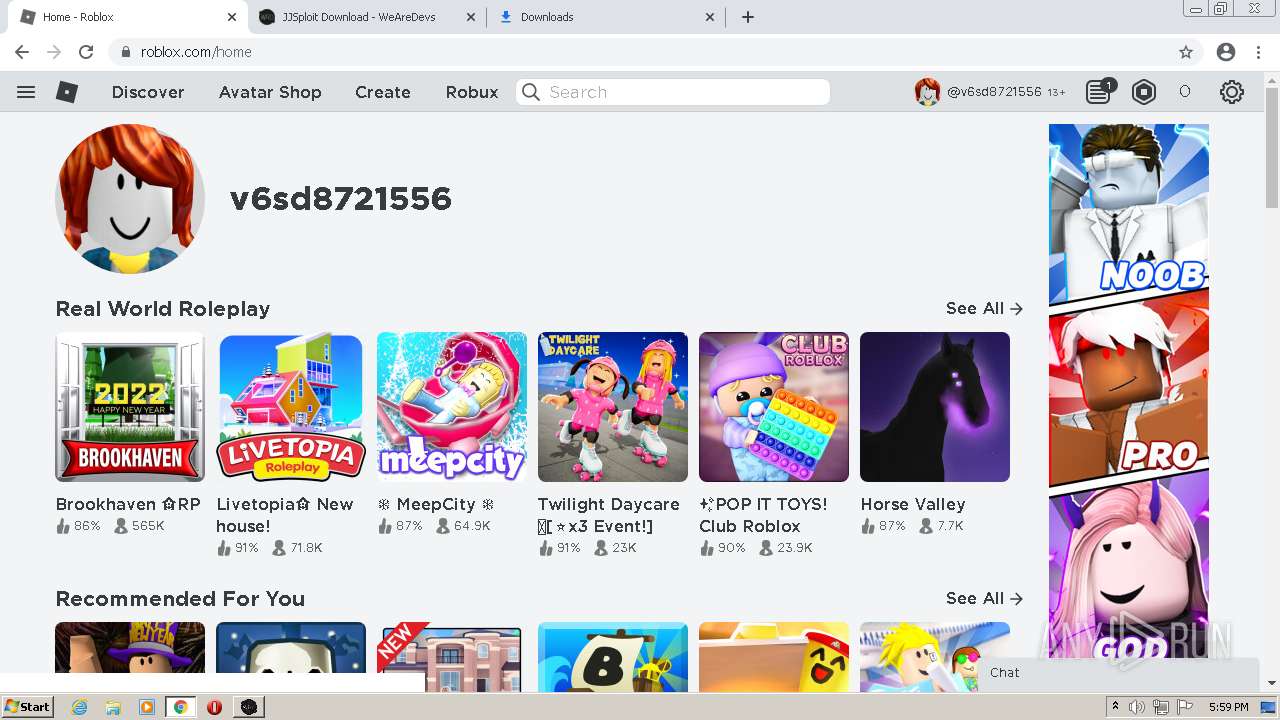
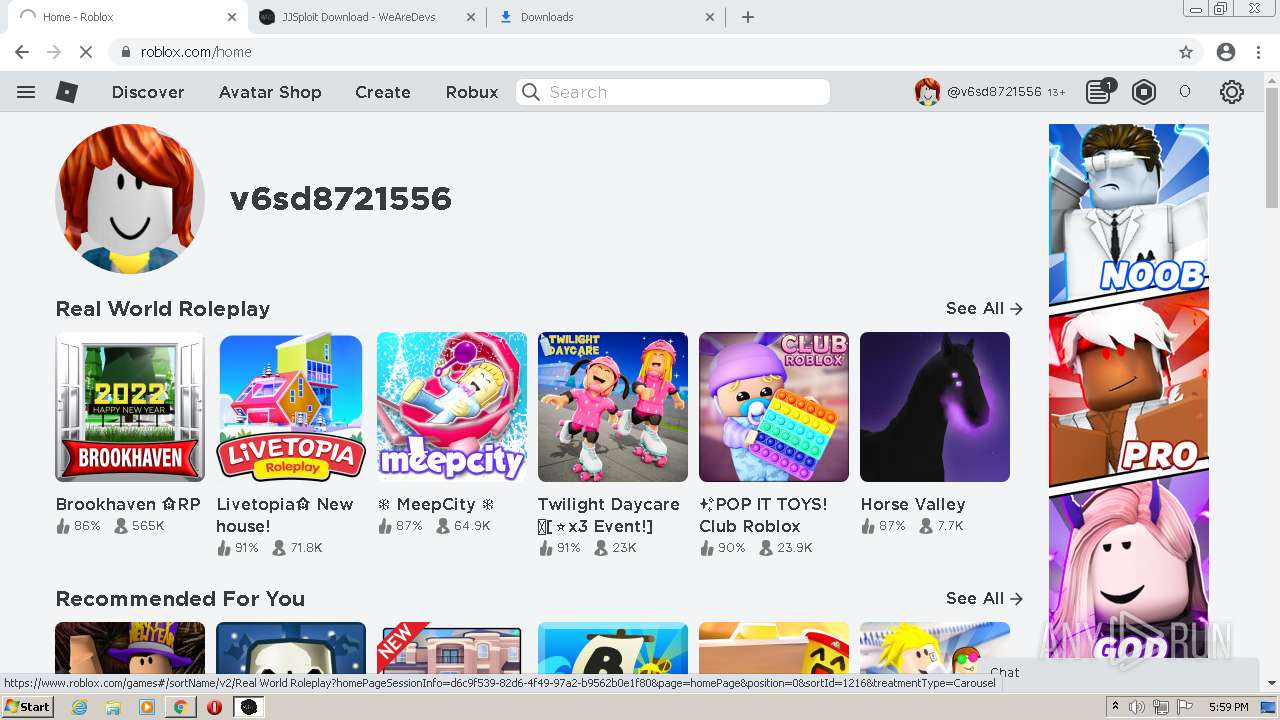
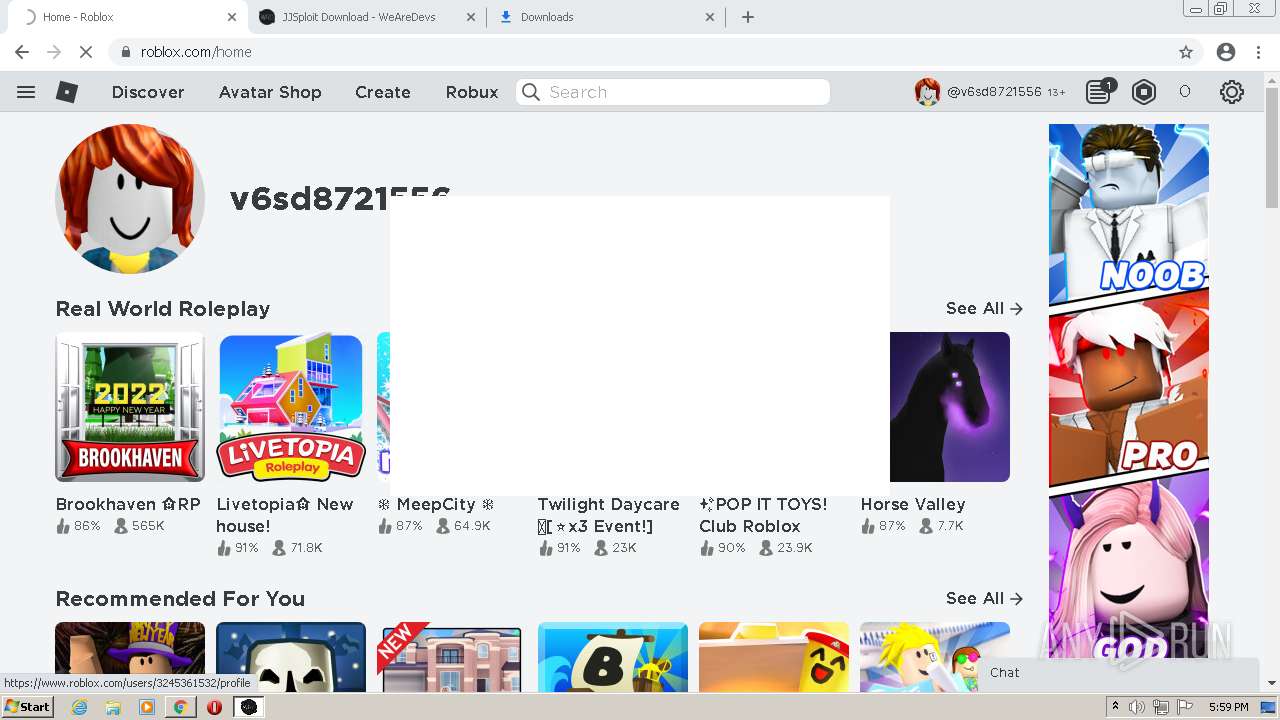
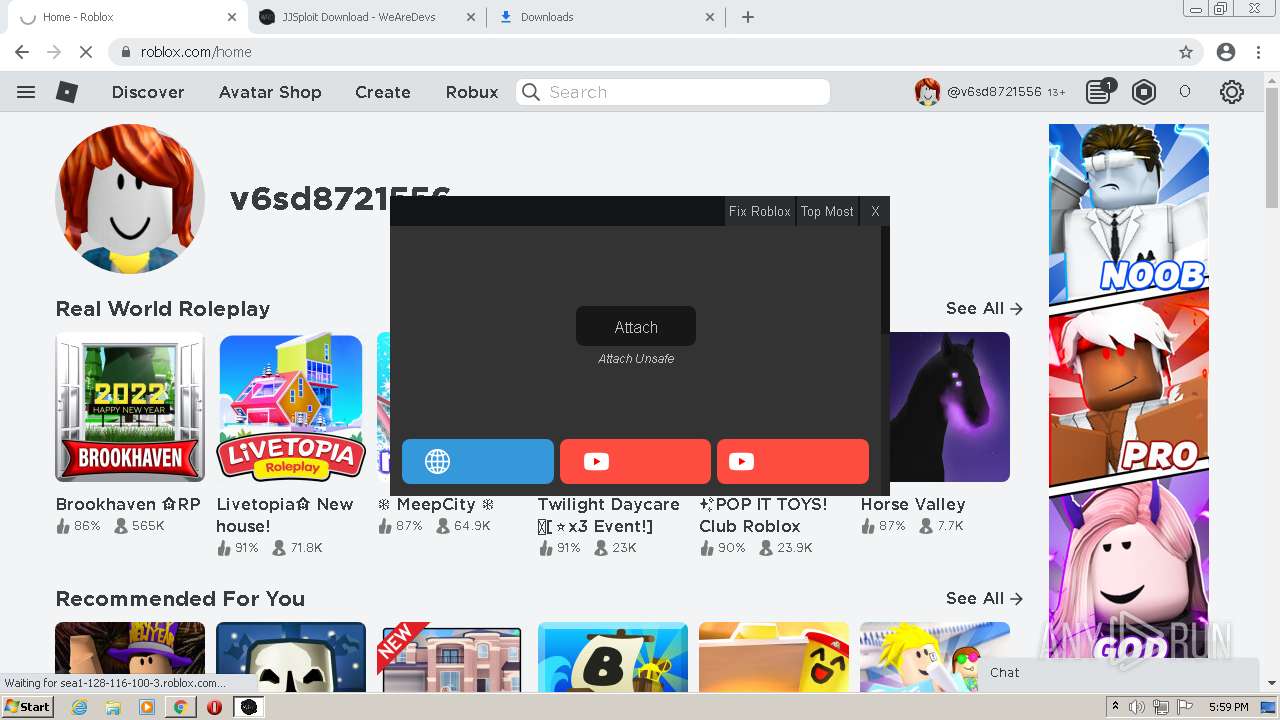
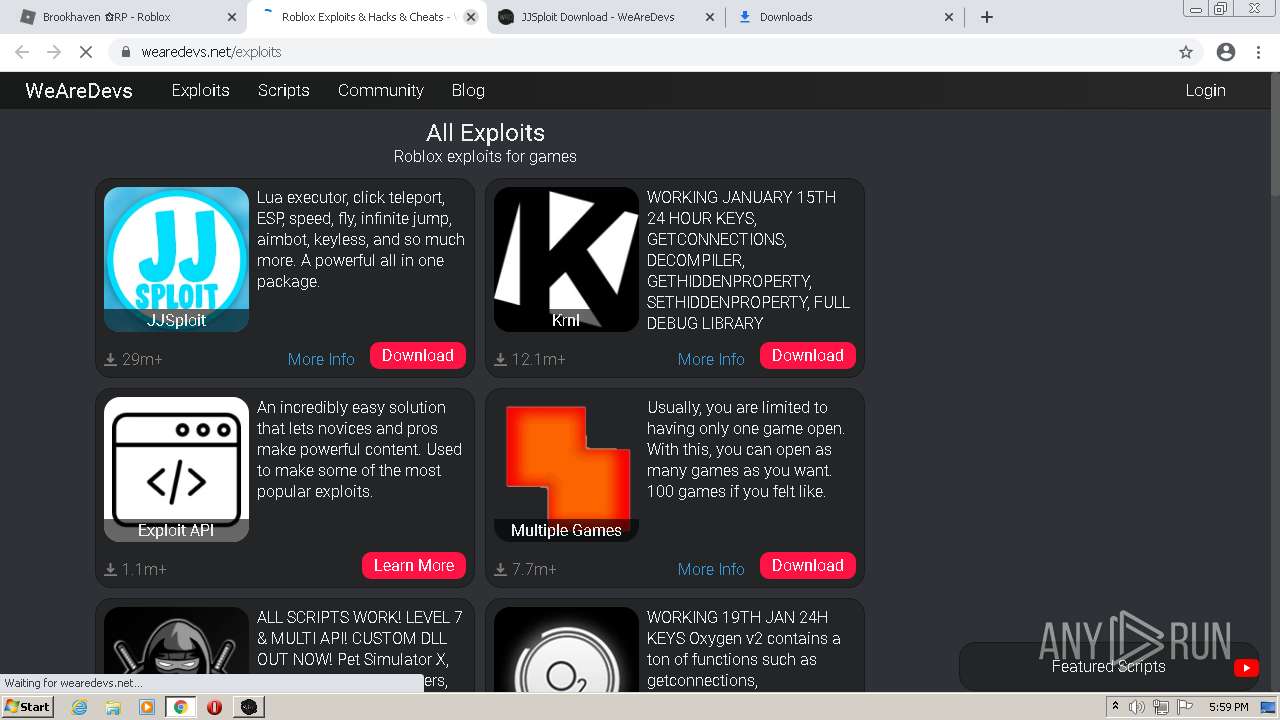
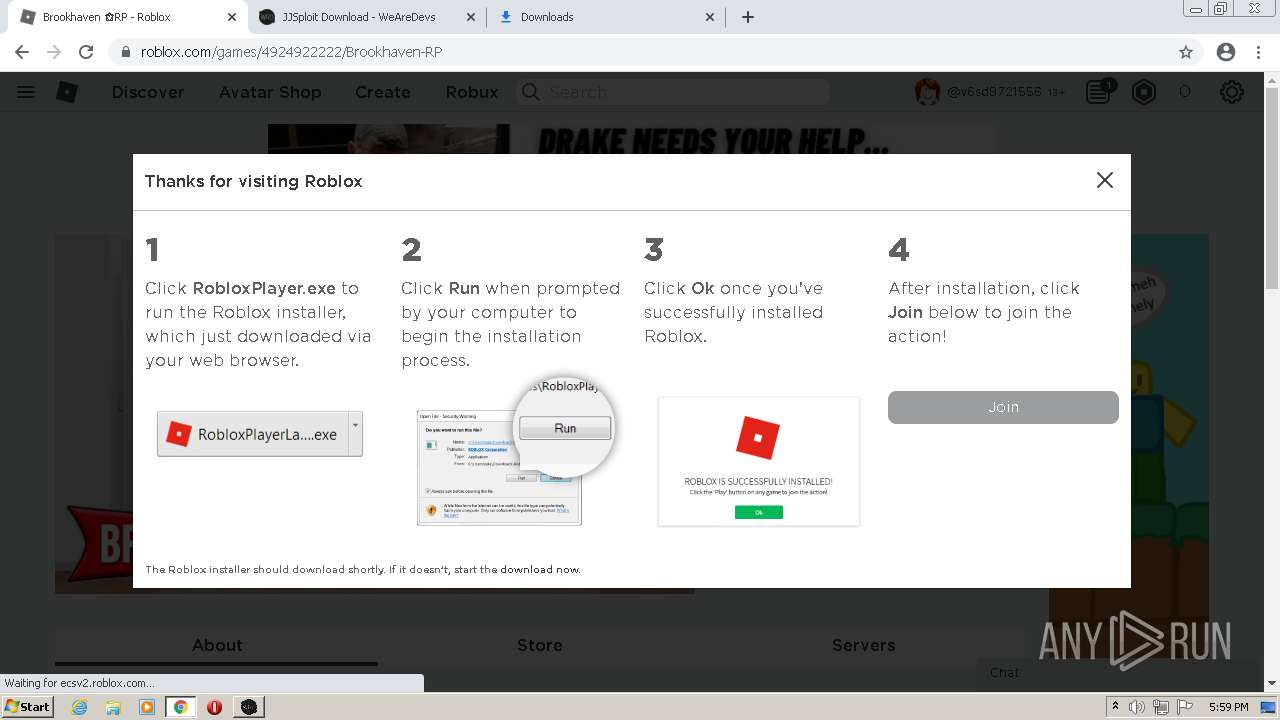
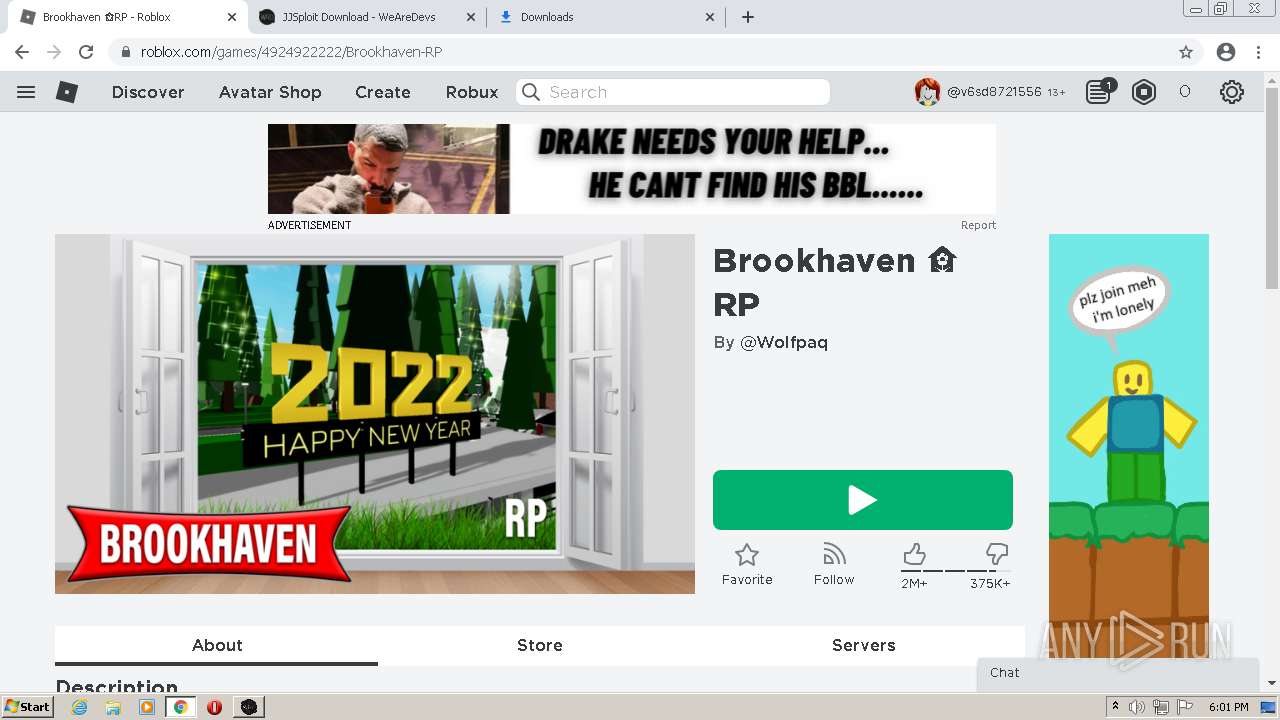
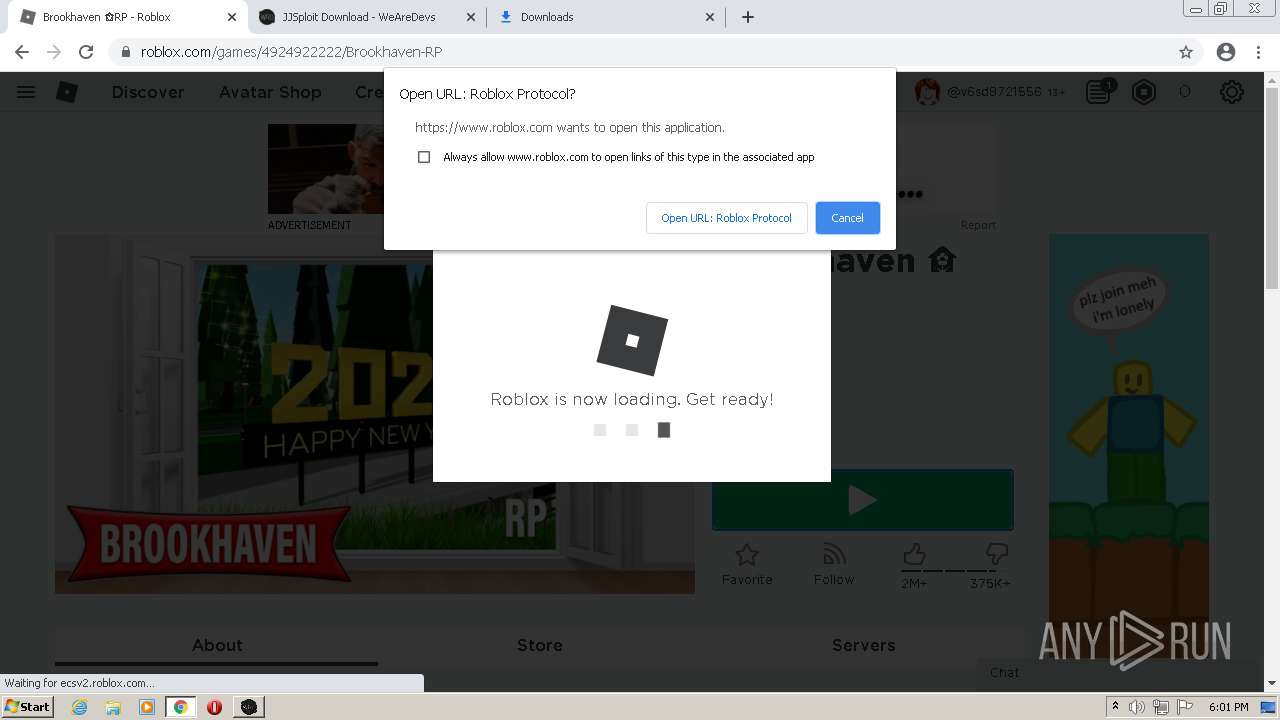
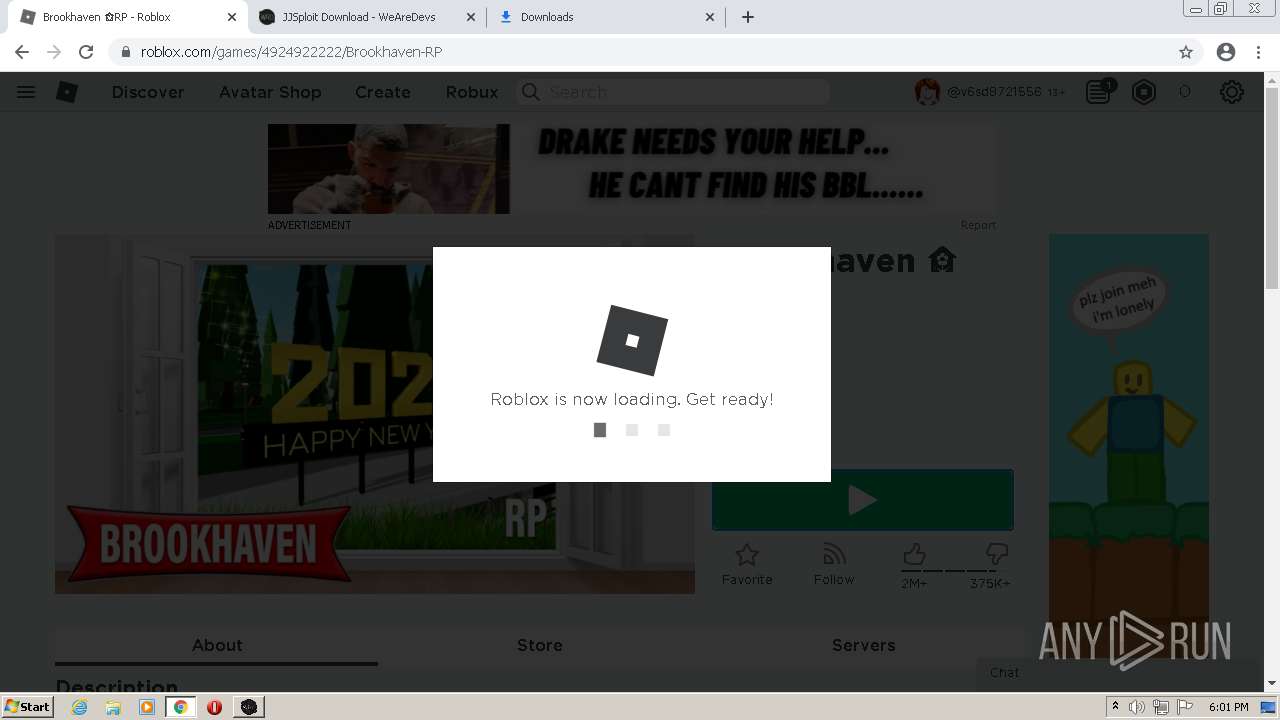
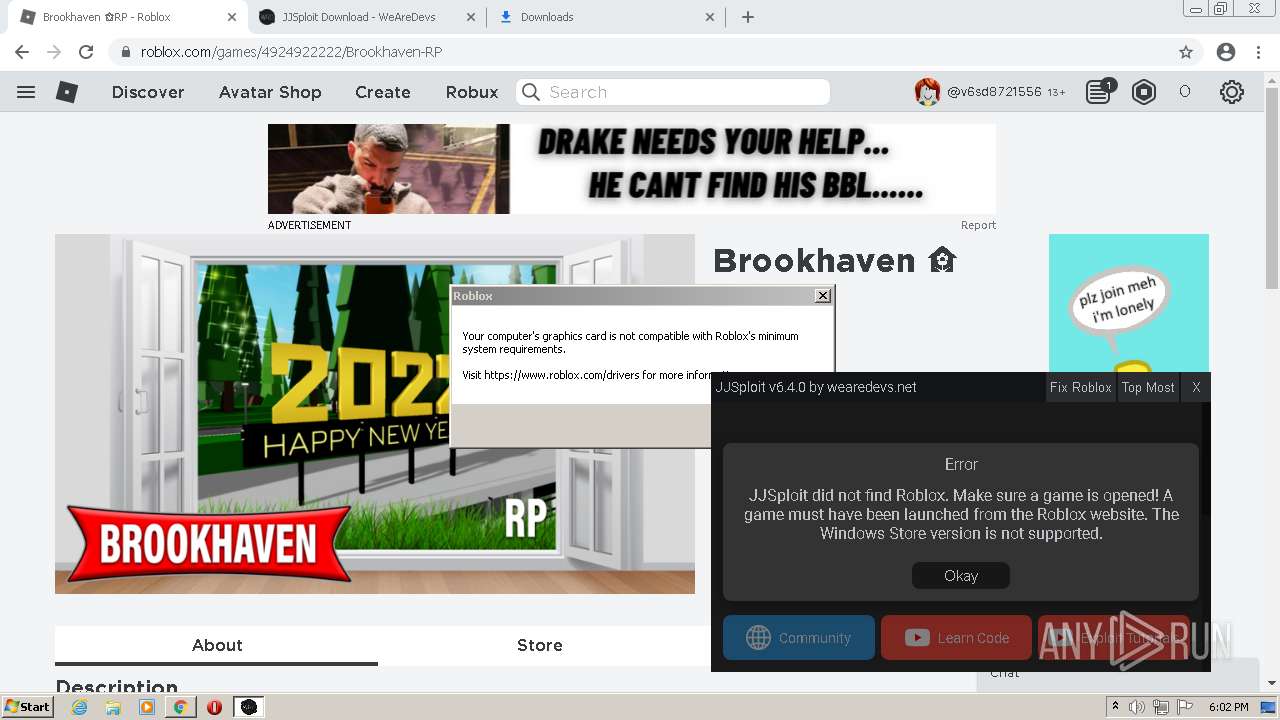
| URL: | https://web.roblox.com/home/ |
| Full analysis: | https://app.any.run/tasks/3c54d778-817e-4708-bfc1-6f2379ea2e89 |
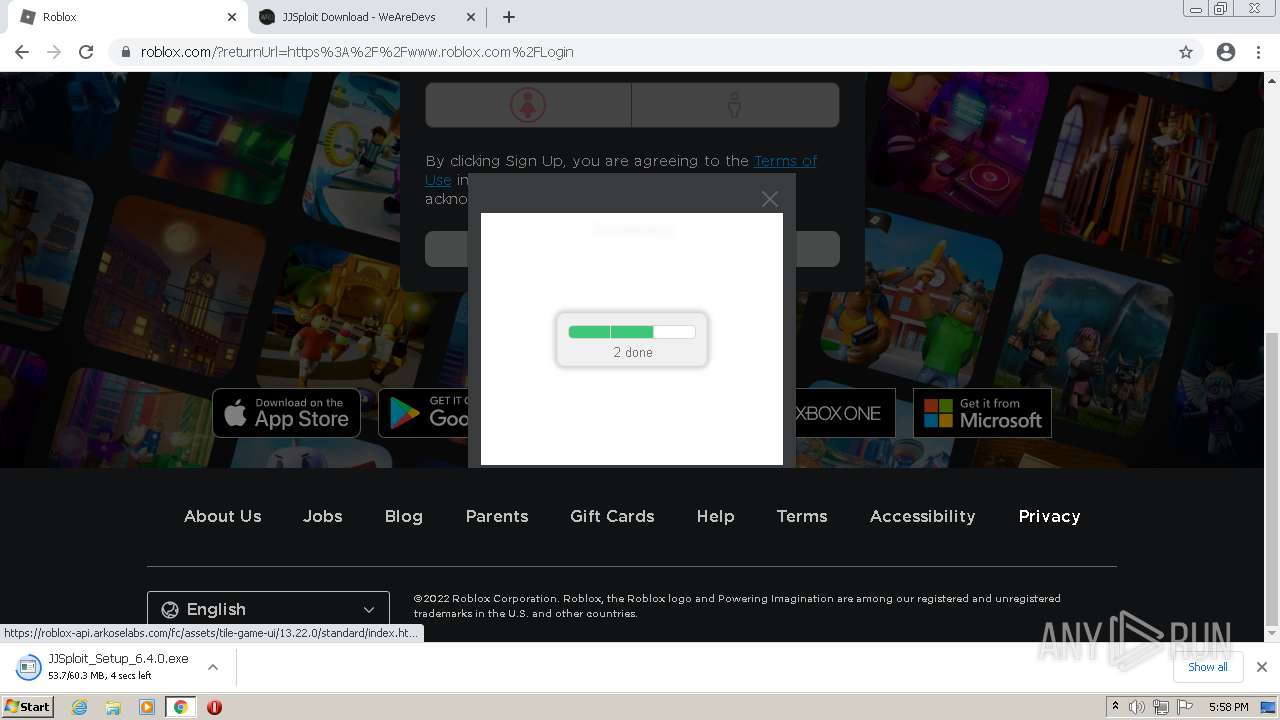
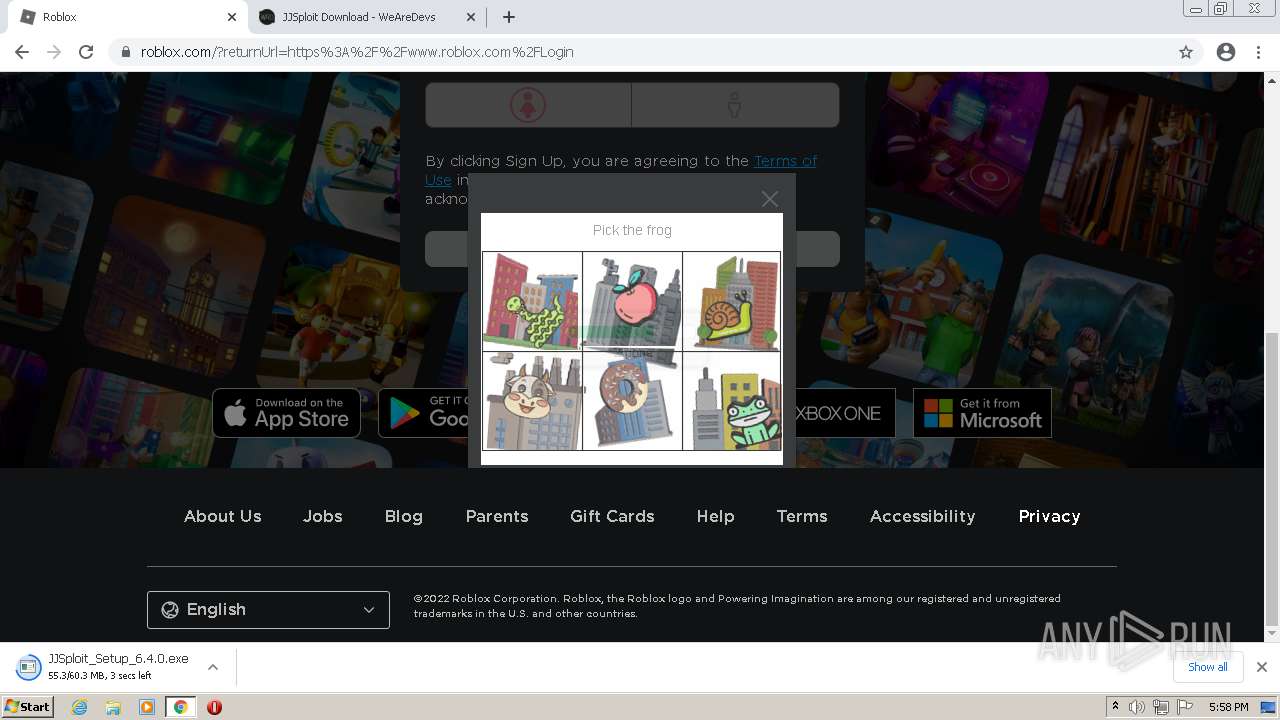
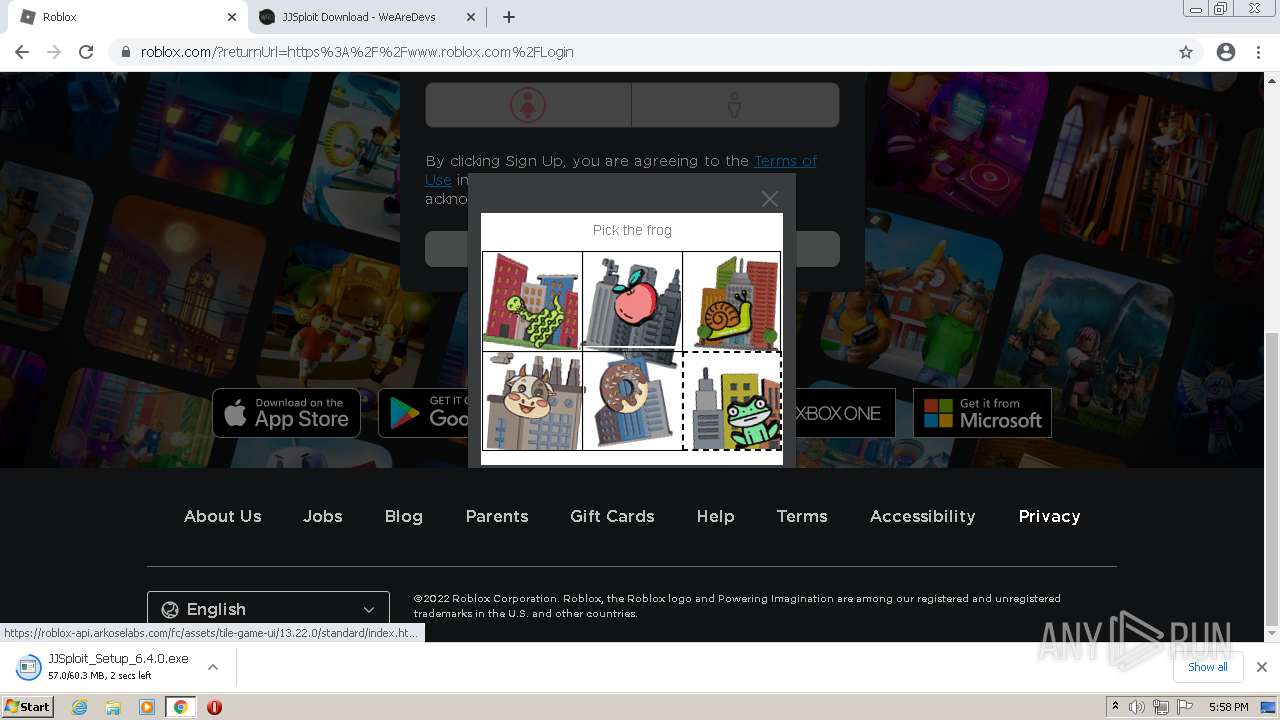
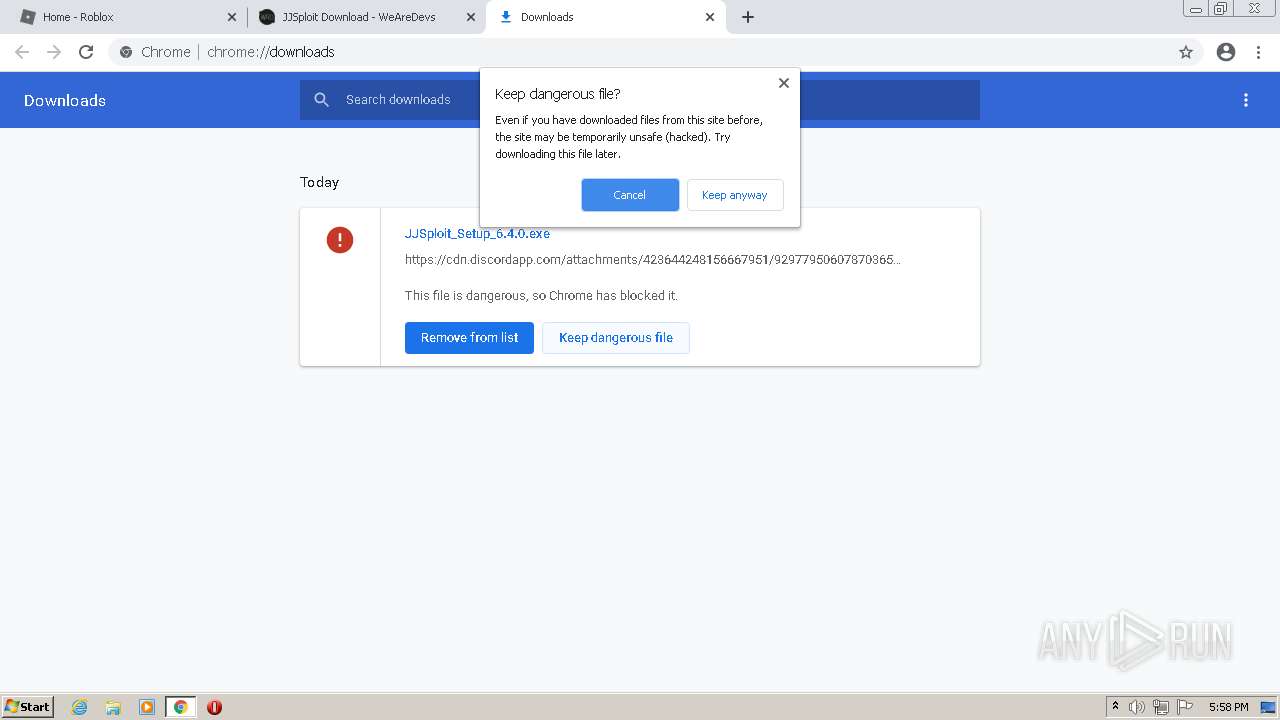
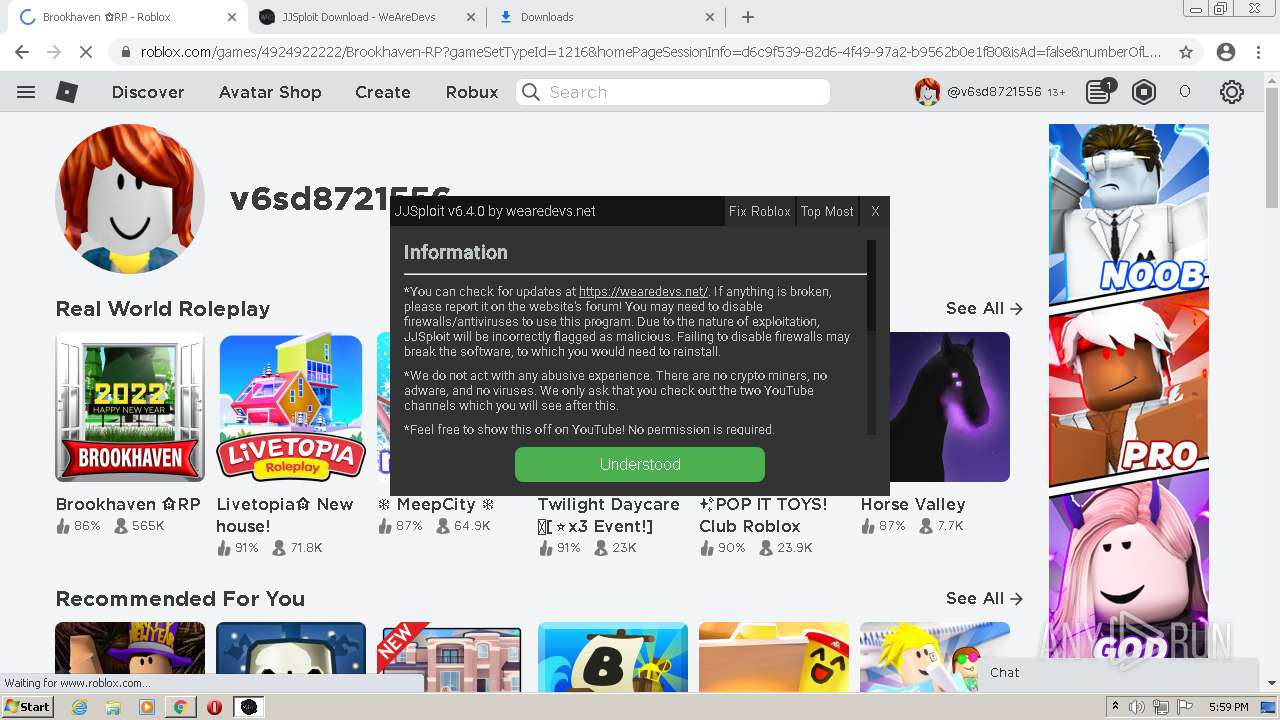
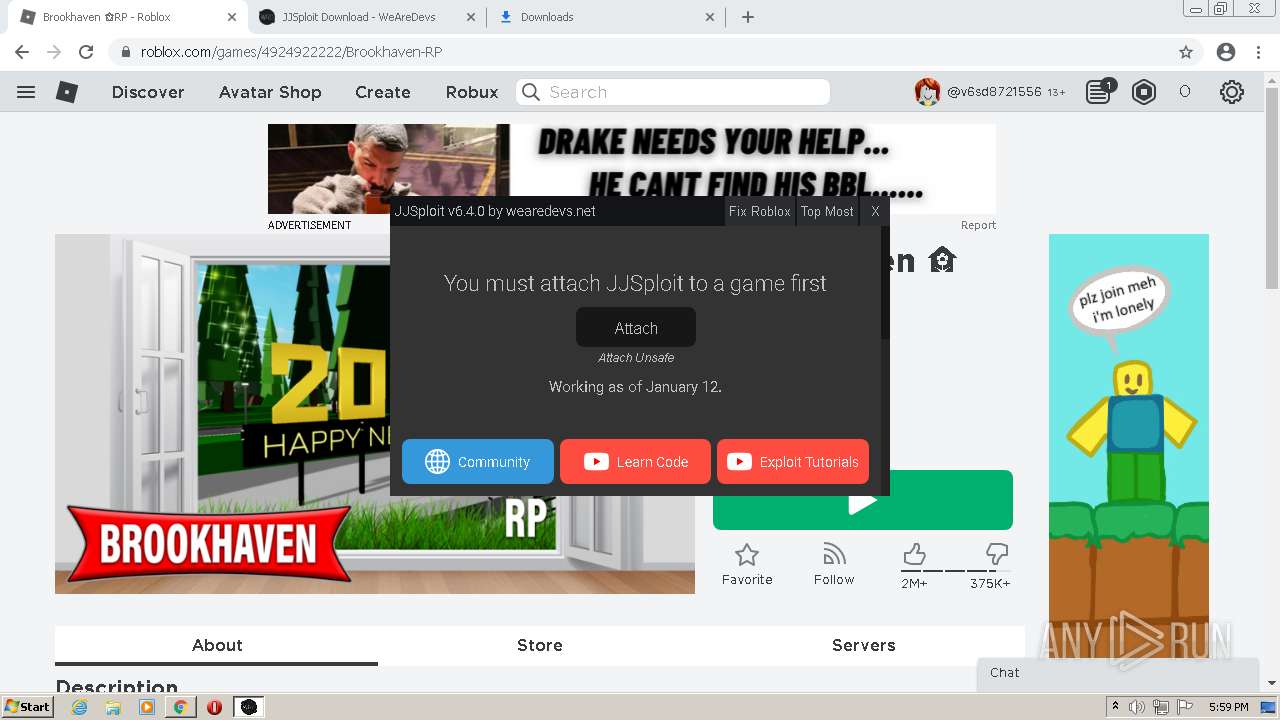
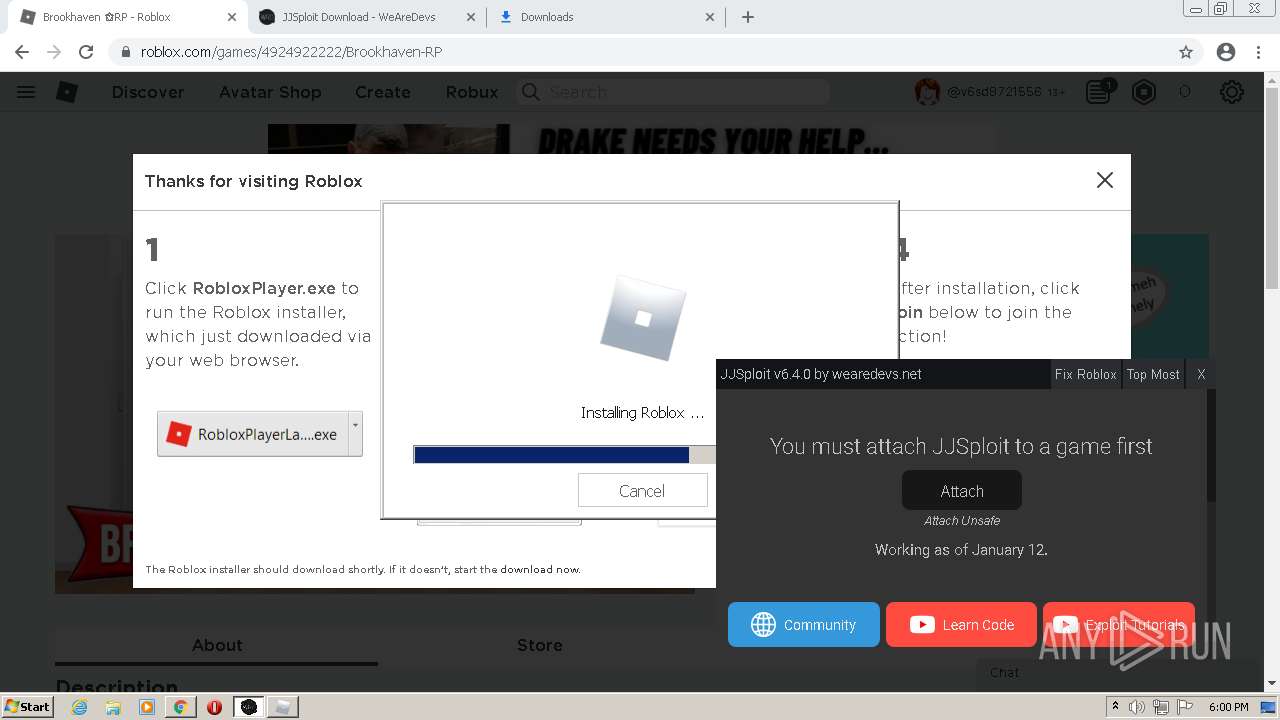
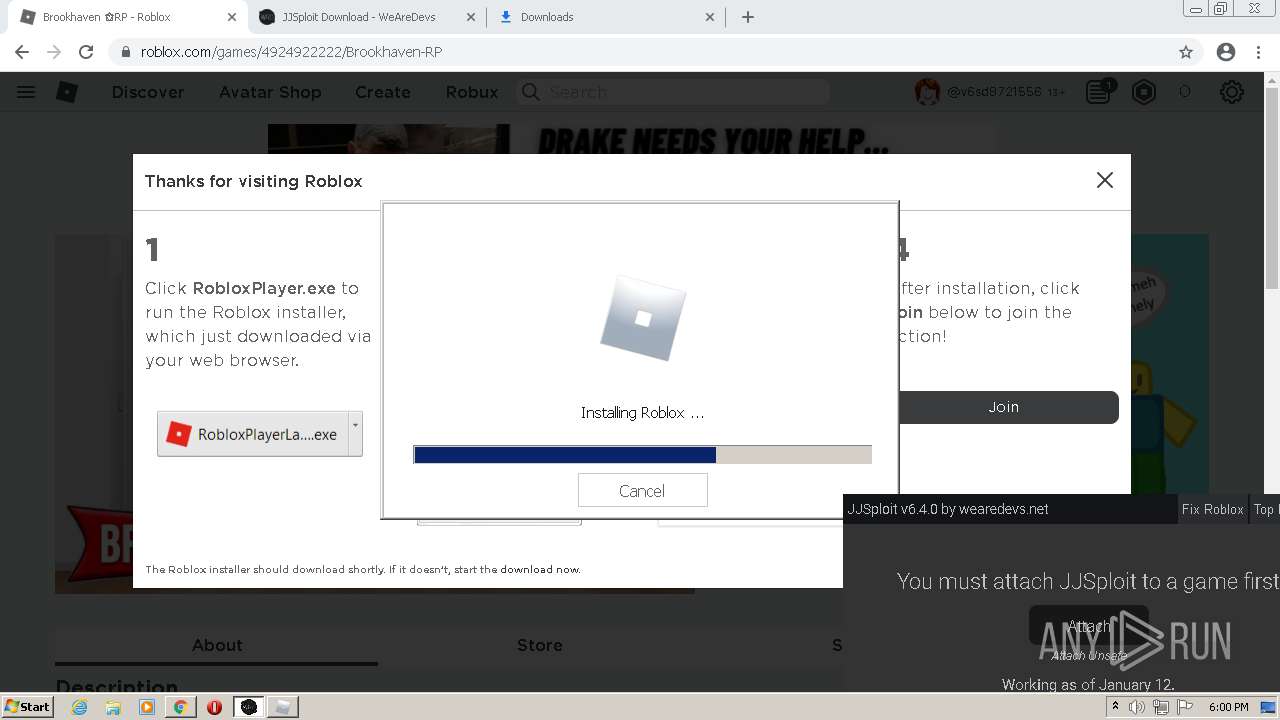
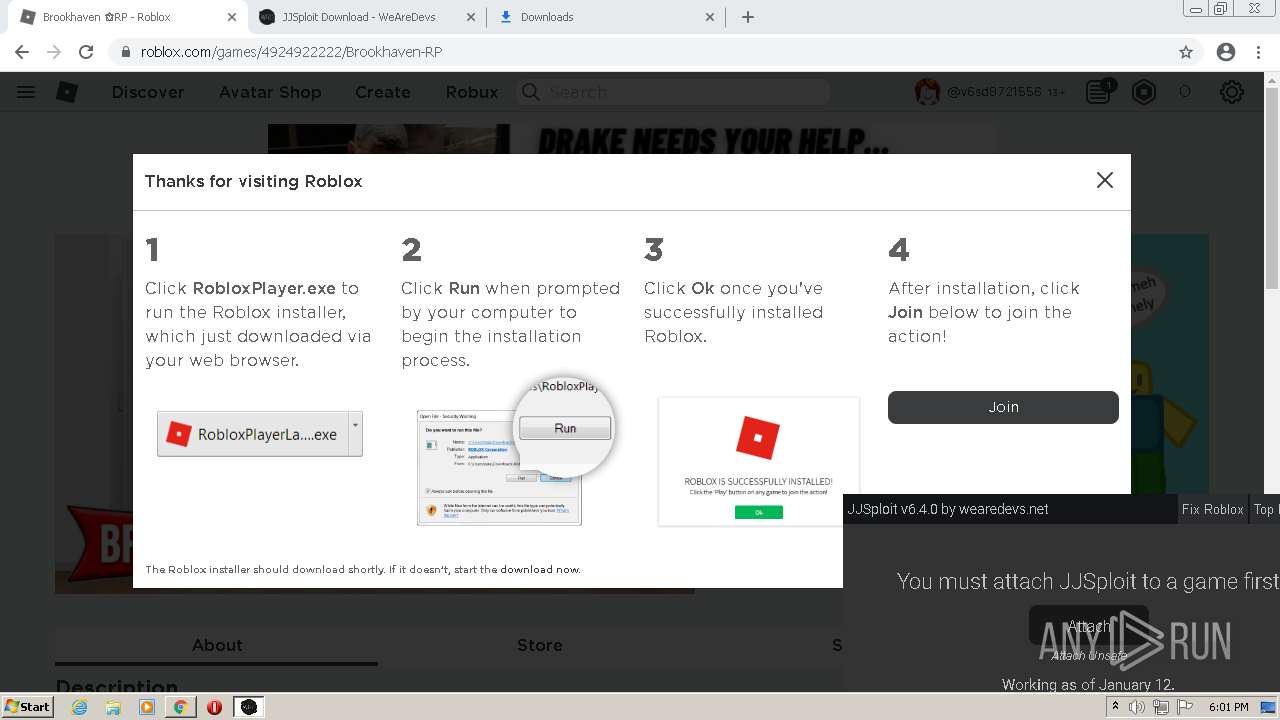
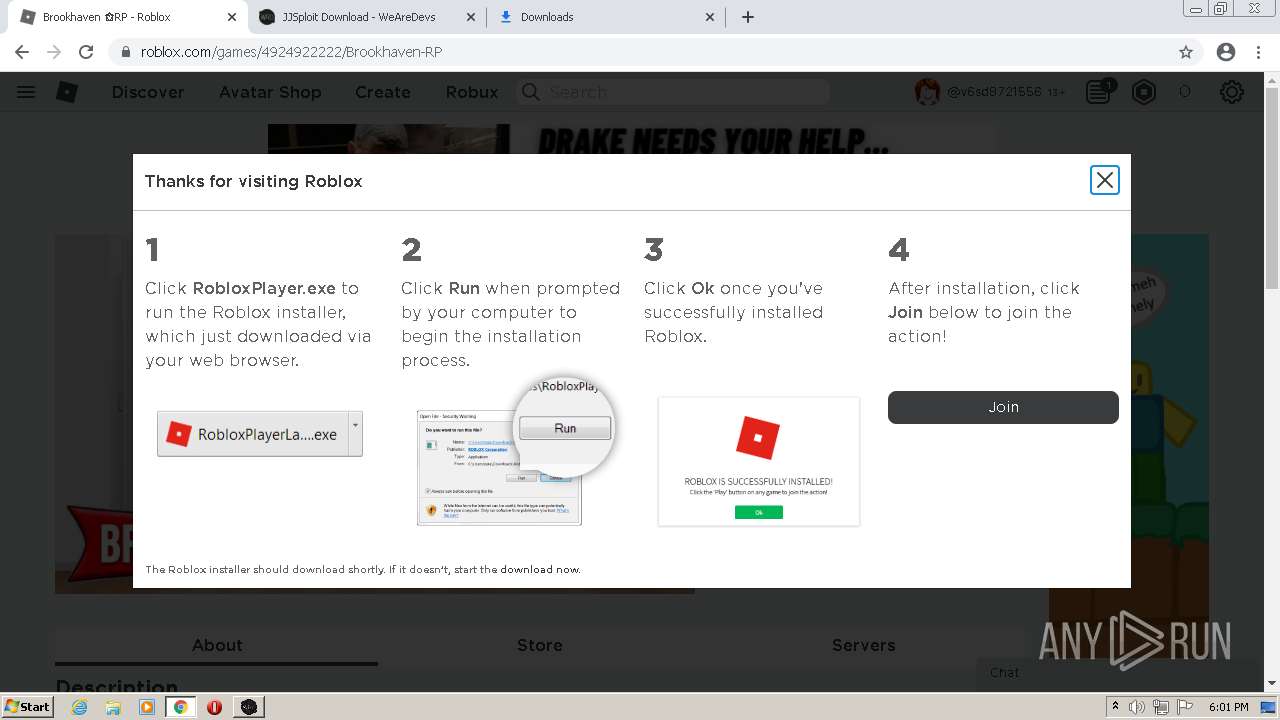
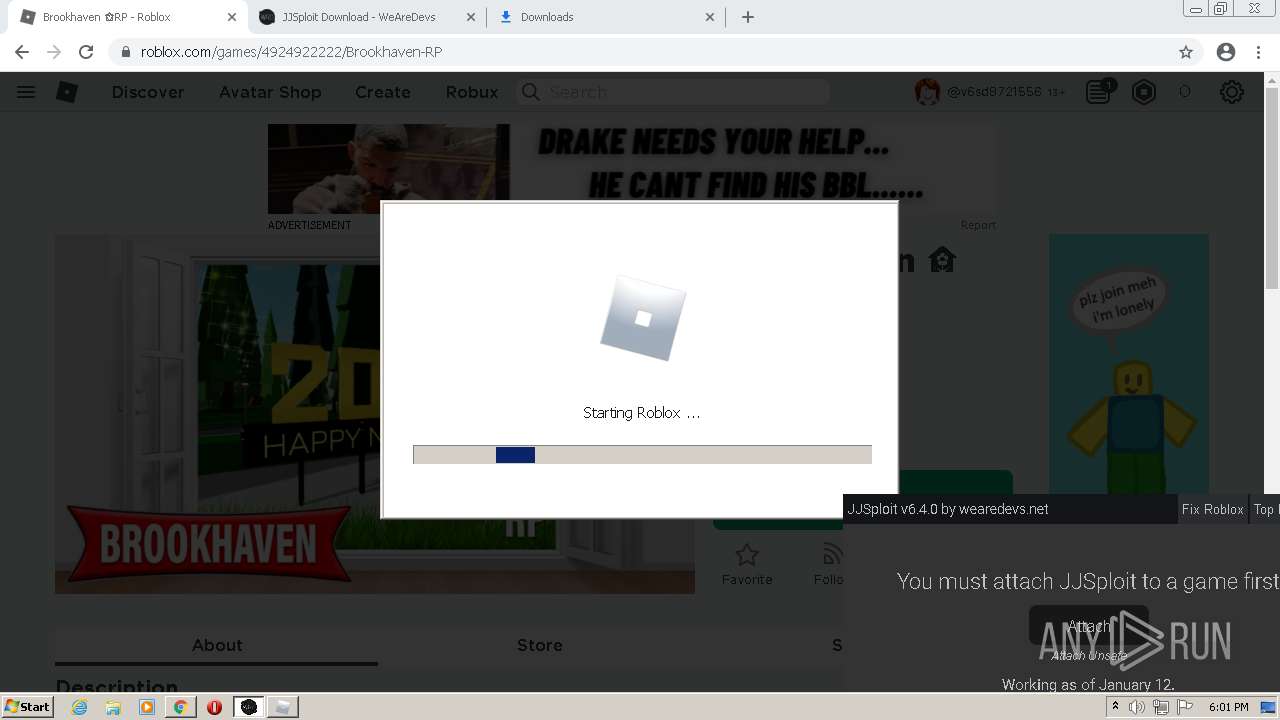
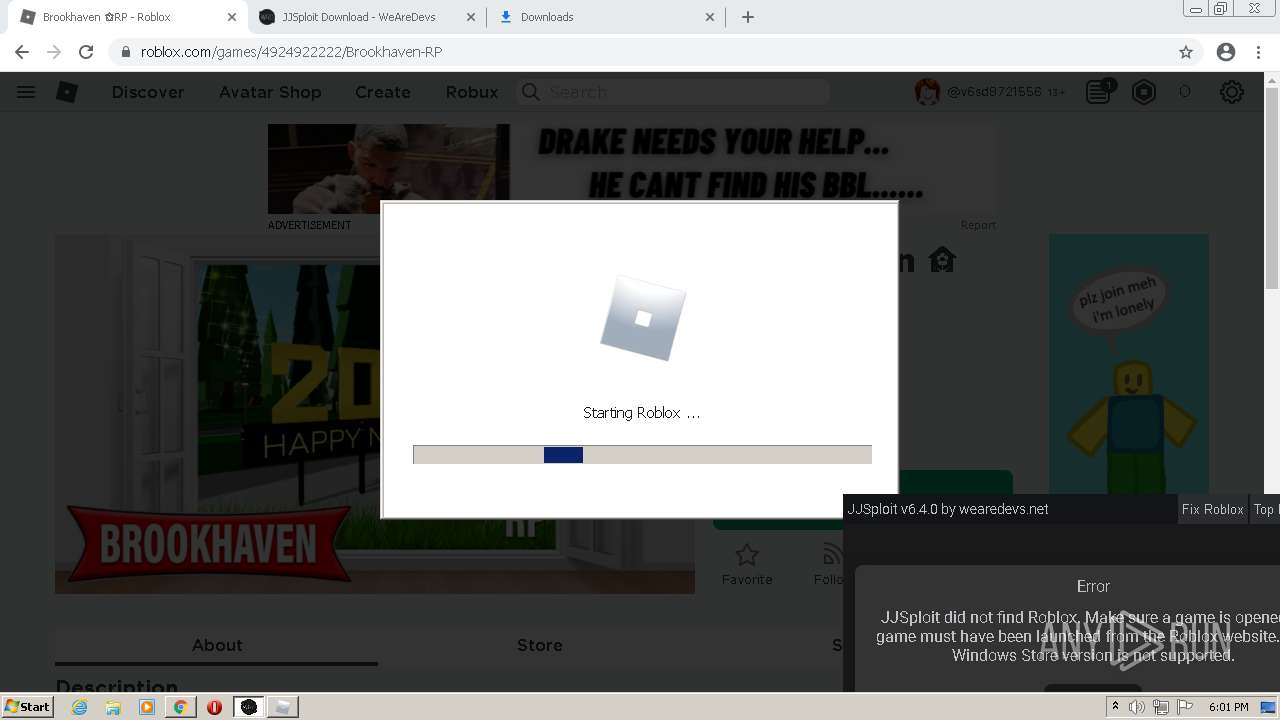
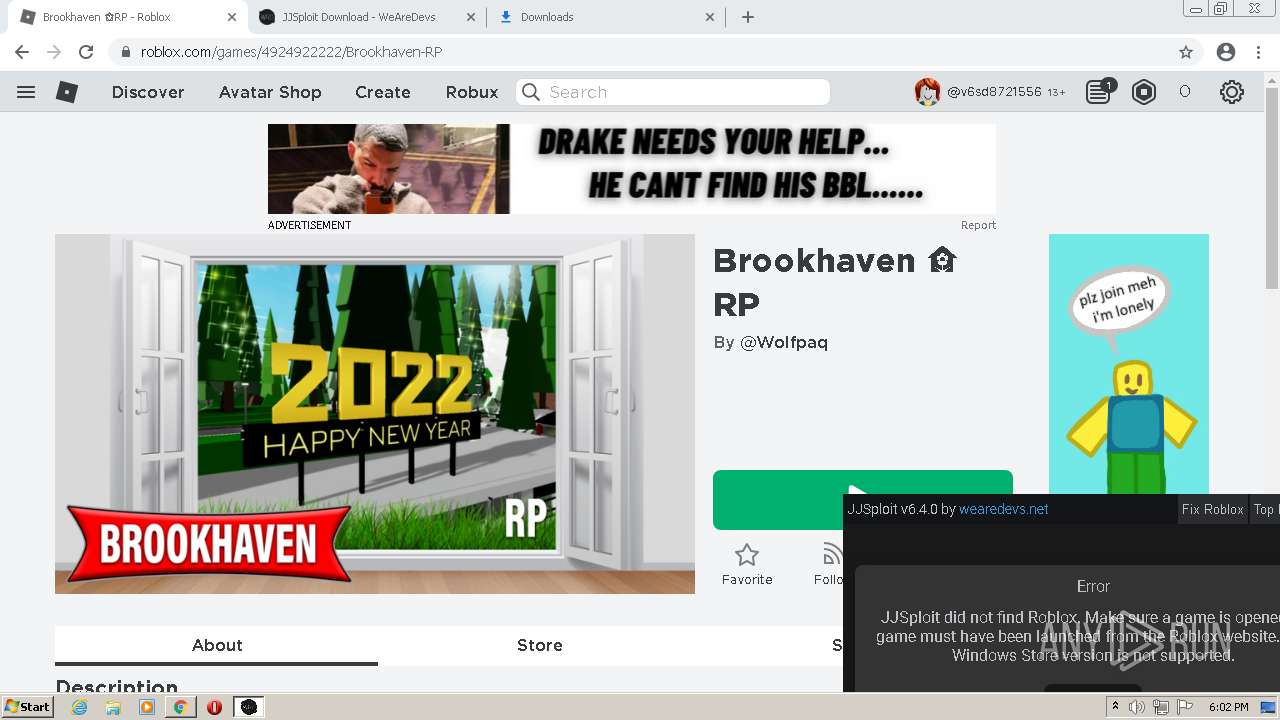
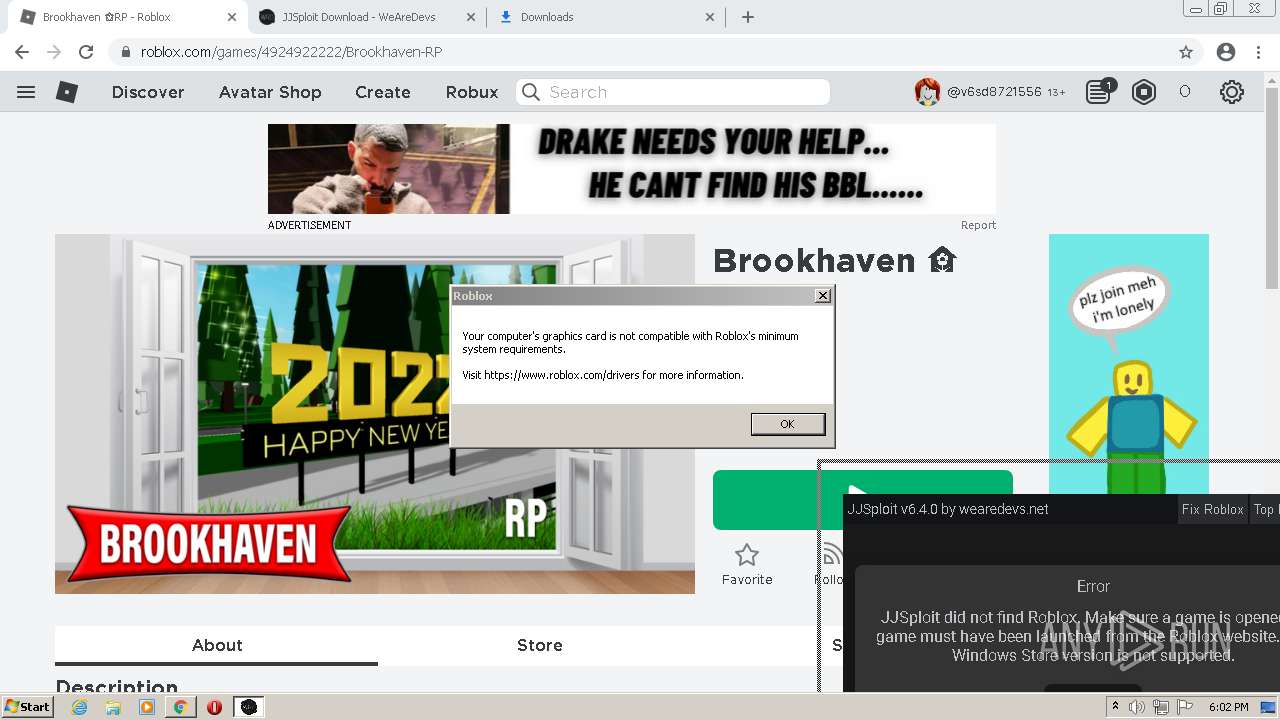
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2022, 17:57:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B2D355849C164A116F3BAFFE9309B5F8 |
| SHA1: | CC36E2BA885C2A044553354AF00E8E510C7B7C78 |
| SHA256: | 3281CE57597D516F3F3FB1F6A68775A67AE56EE7B16347FDBBB55C3AF13CC33F |
| SSDEEP: | 3:N8RDXIWKo:2CNo |
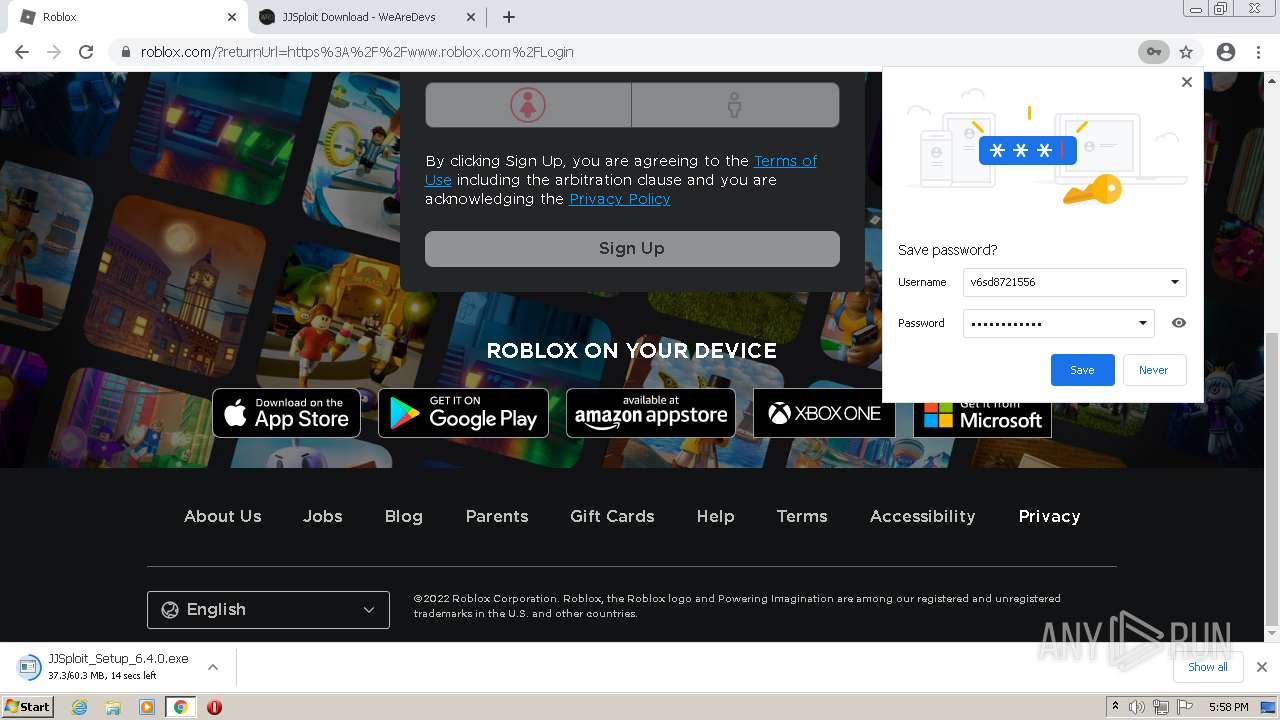
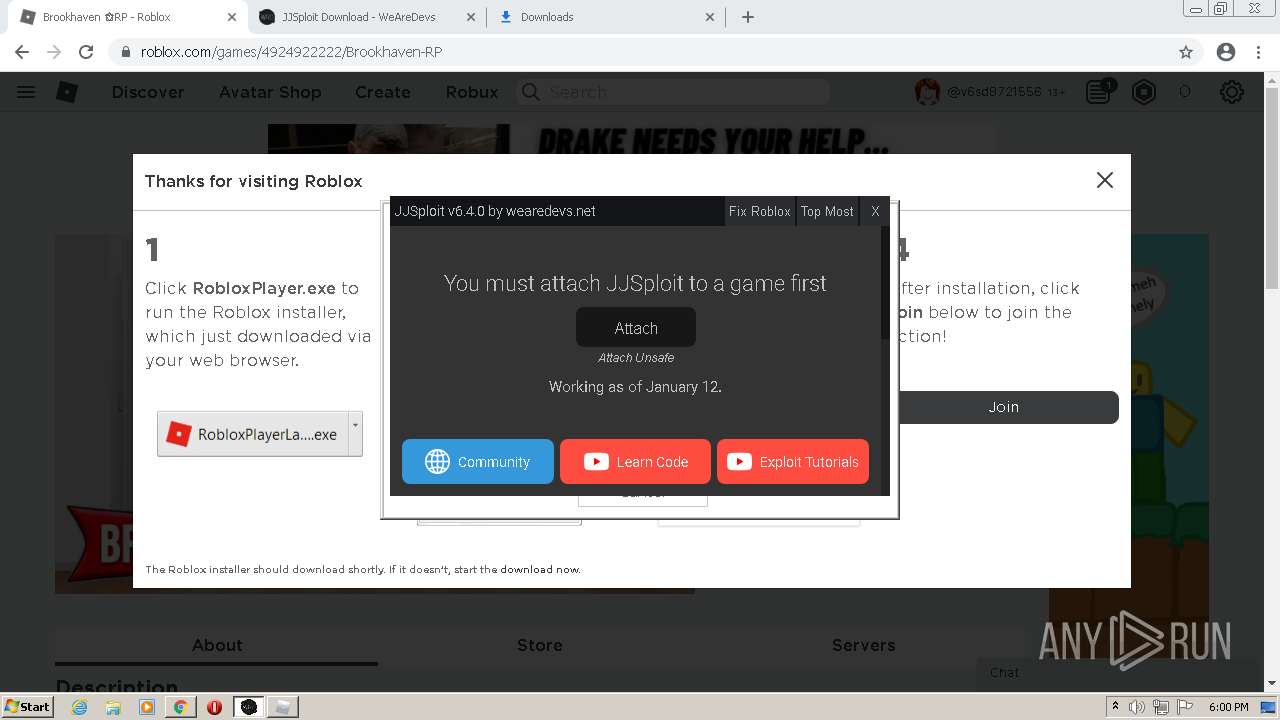
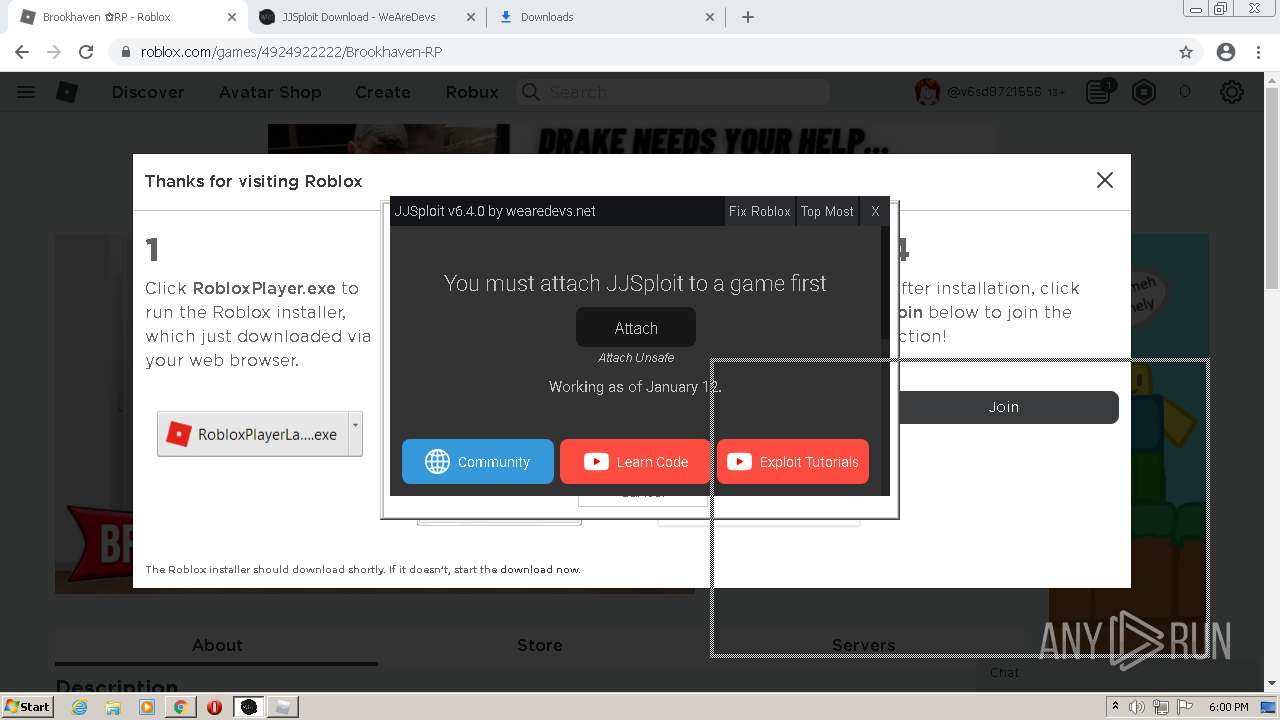
MALICIOUS
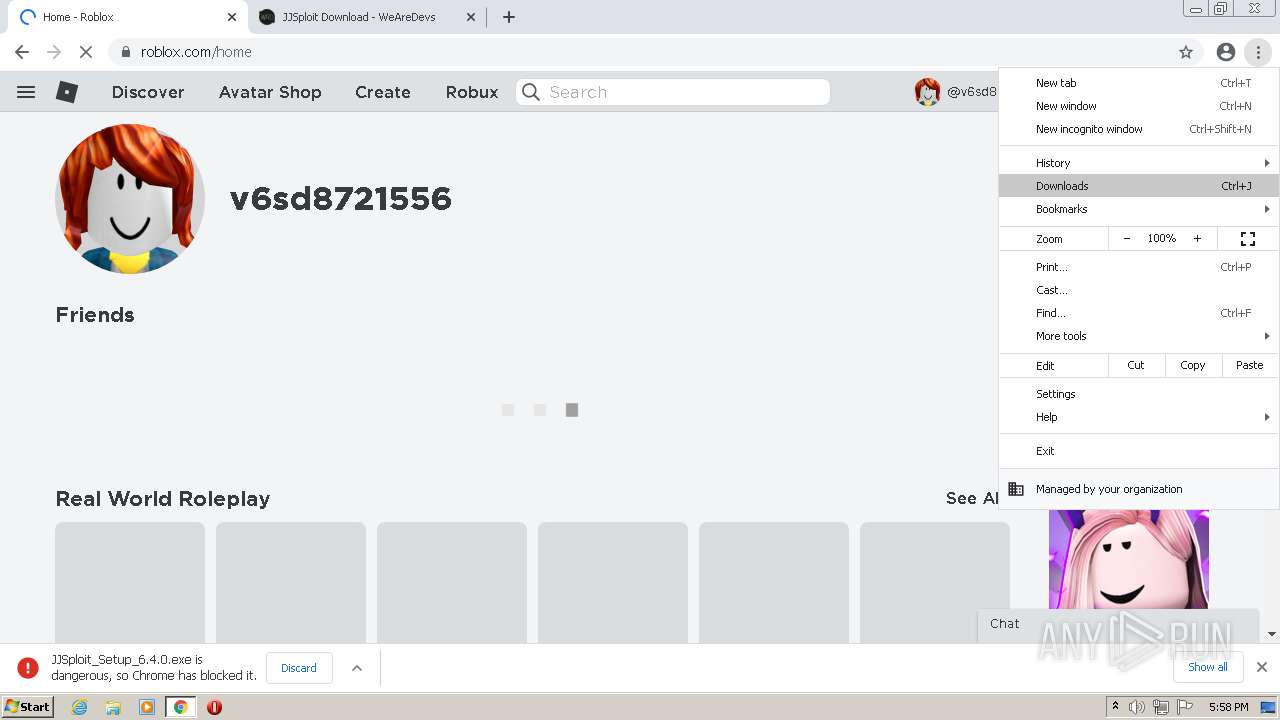
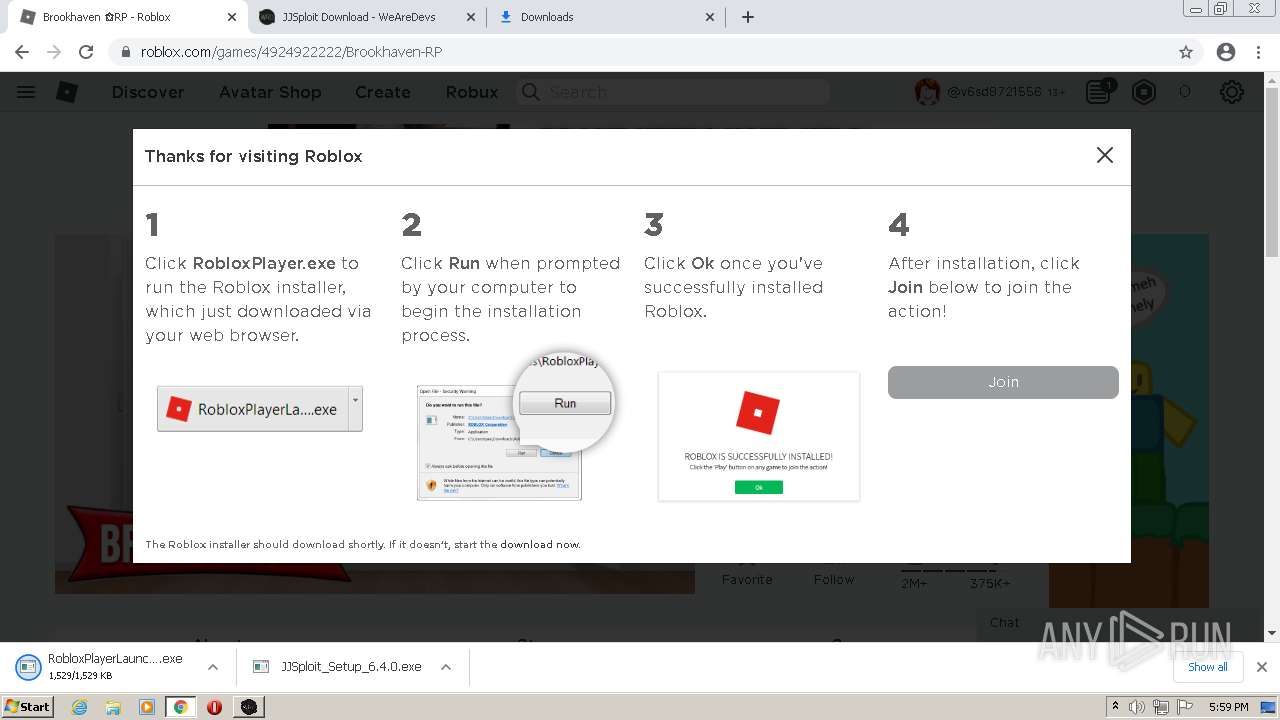
Application was dropped or rewritten from another process
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- RobloxPlayerLauncher.exe (PID: 1608)
- RobloxPlayerLauncher.exe (PID: 3100)
- RobloxPlayerLauncher.exe (PID: 2948)
- RobloxPlayerLauncher.exe (PID: 2024)
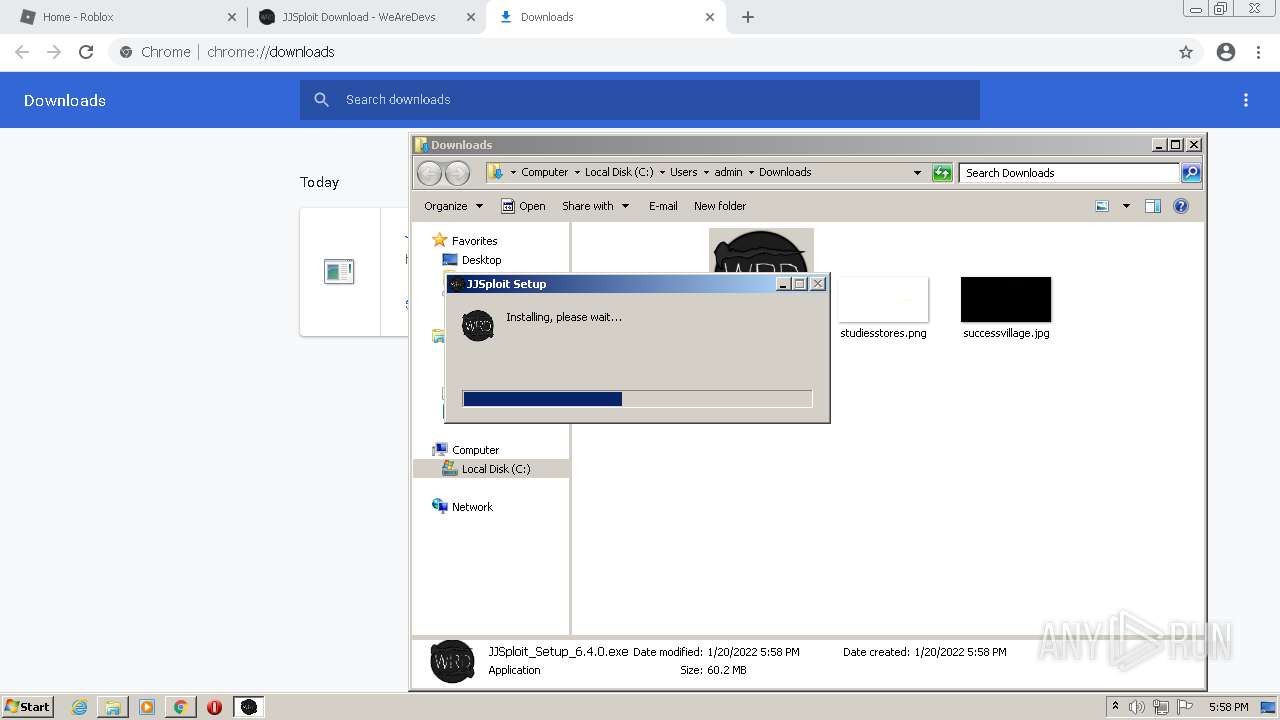
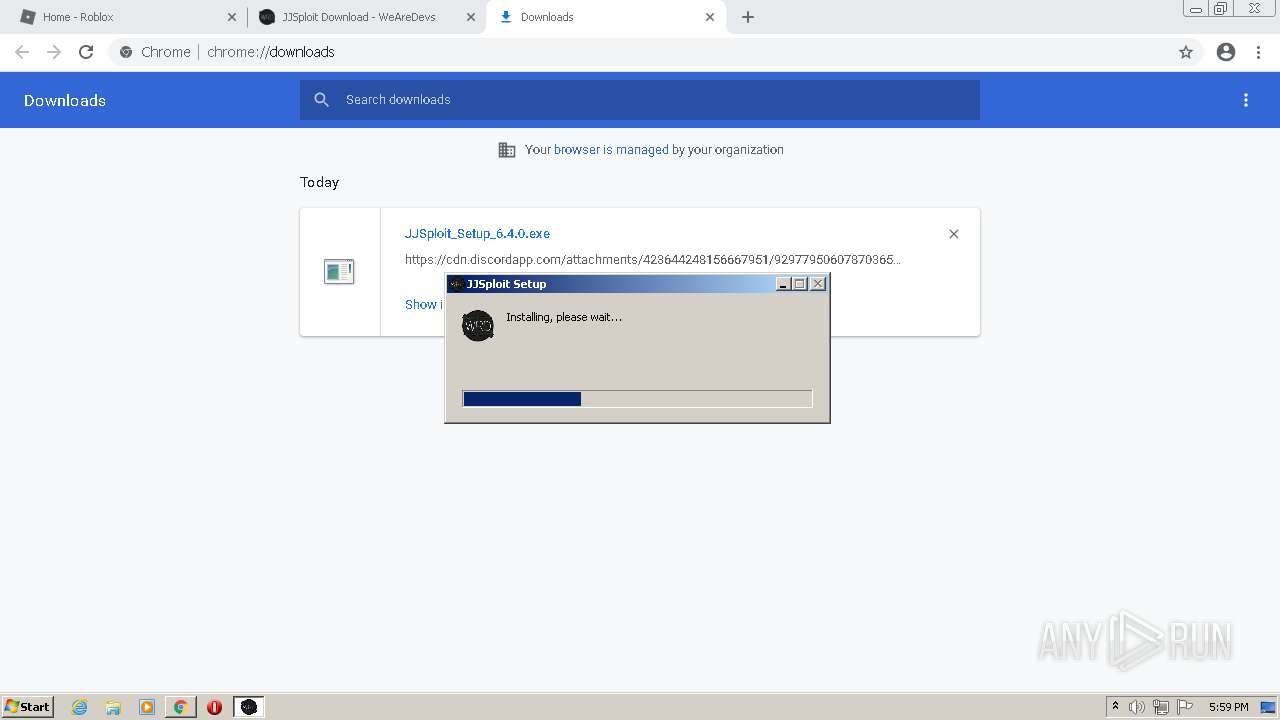
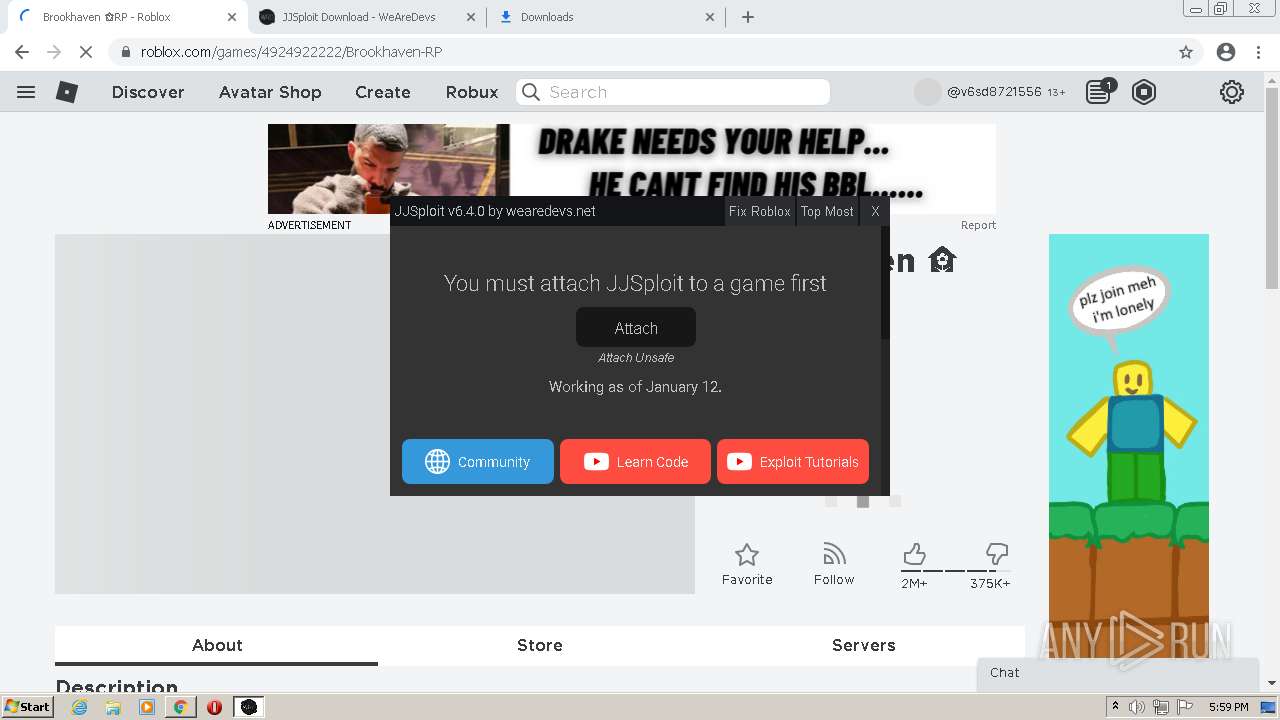
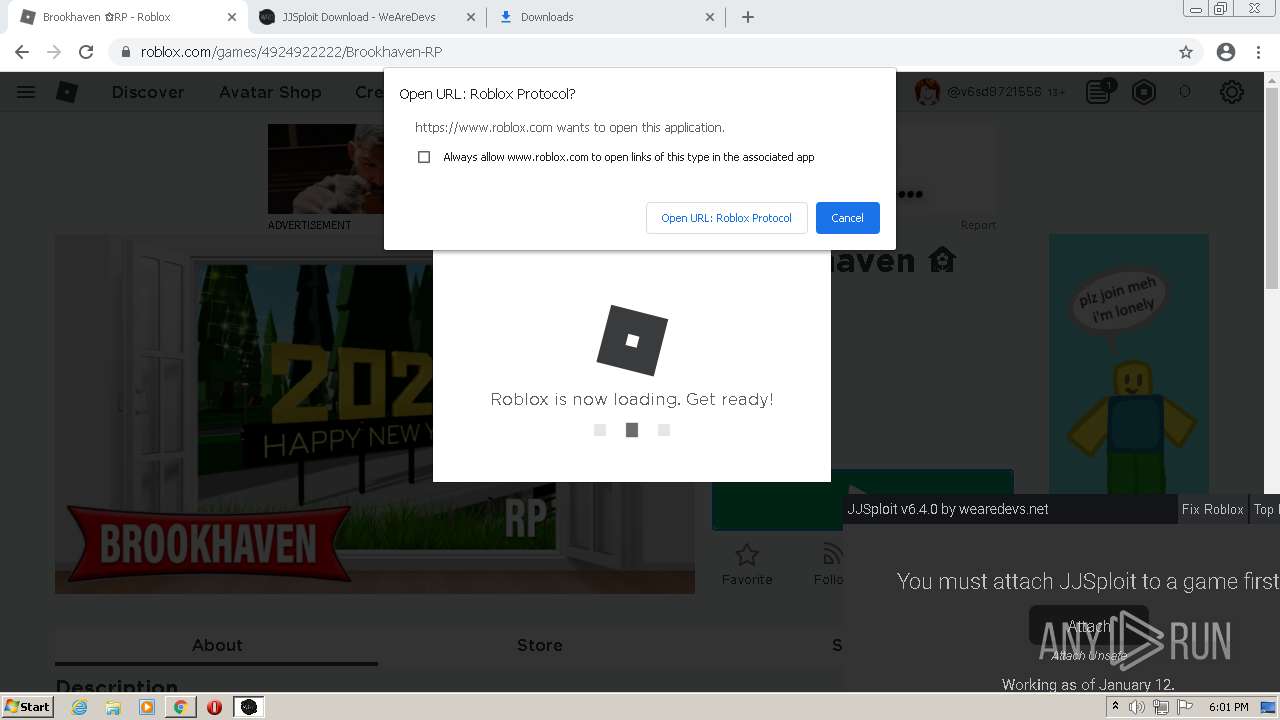
Loads dropped or rewritten executable
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- JJSploit.exe (PID: 2300)
- JJSploit.exe (PID: 776)
- JJSploit.exe (PID: 3412)
- JJSploit.exe (PID: 3880)
- JJSploit.exe (PID: 1300)
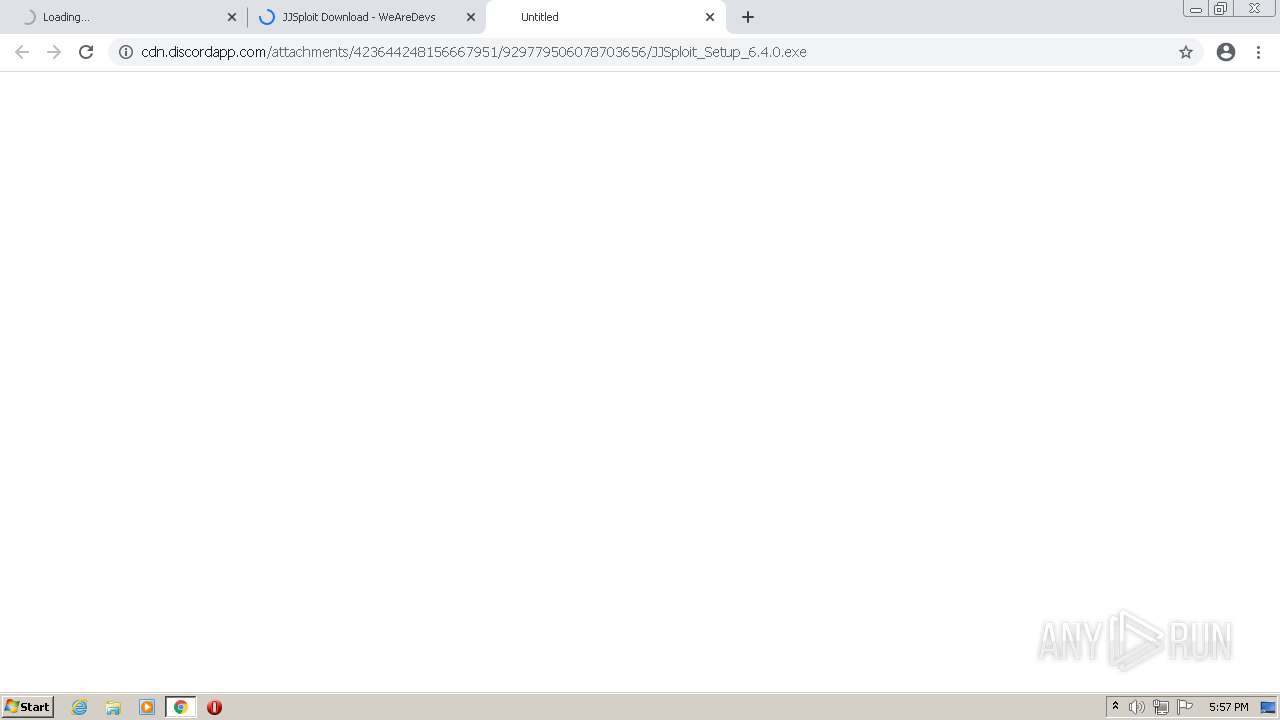
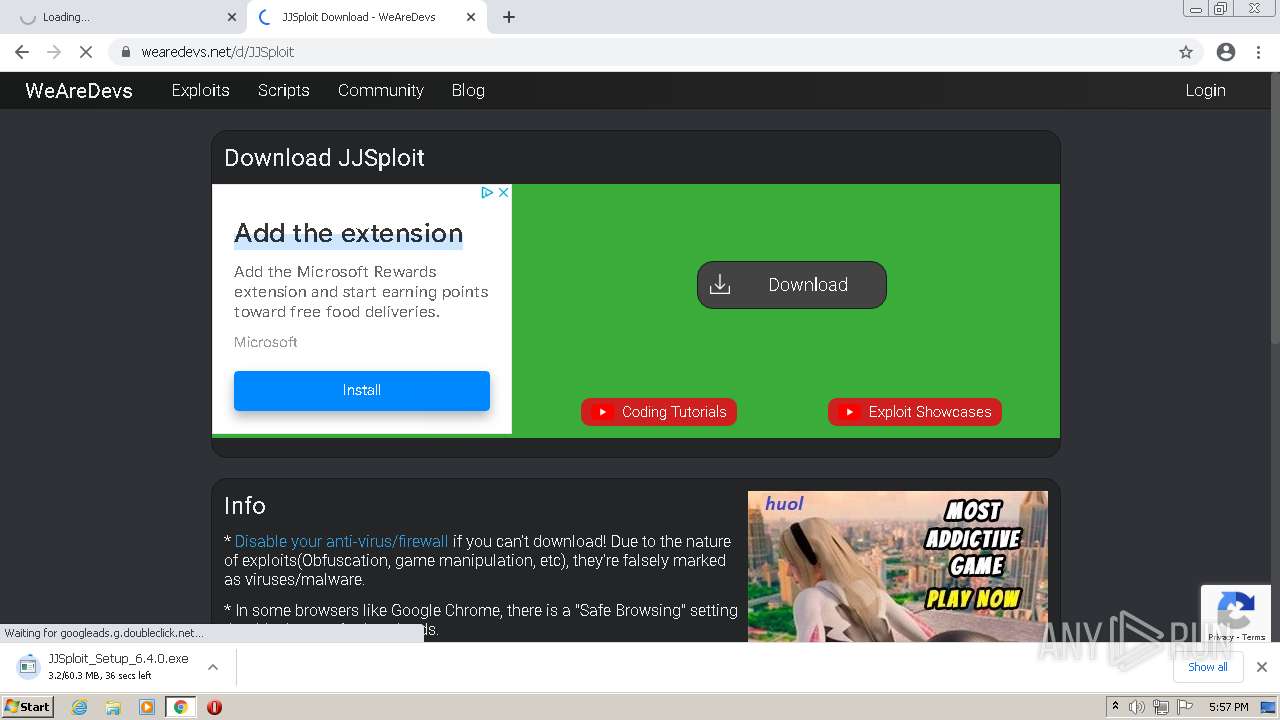
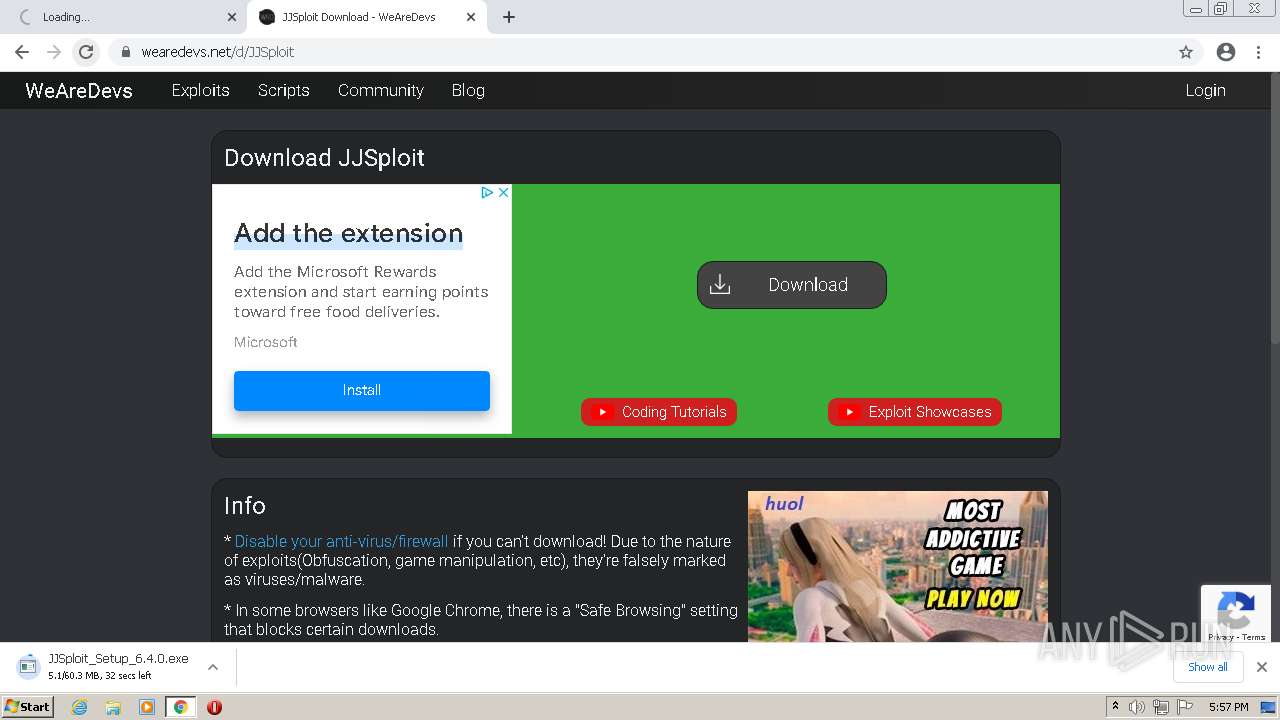
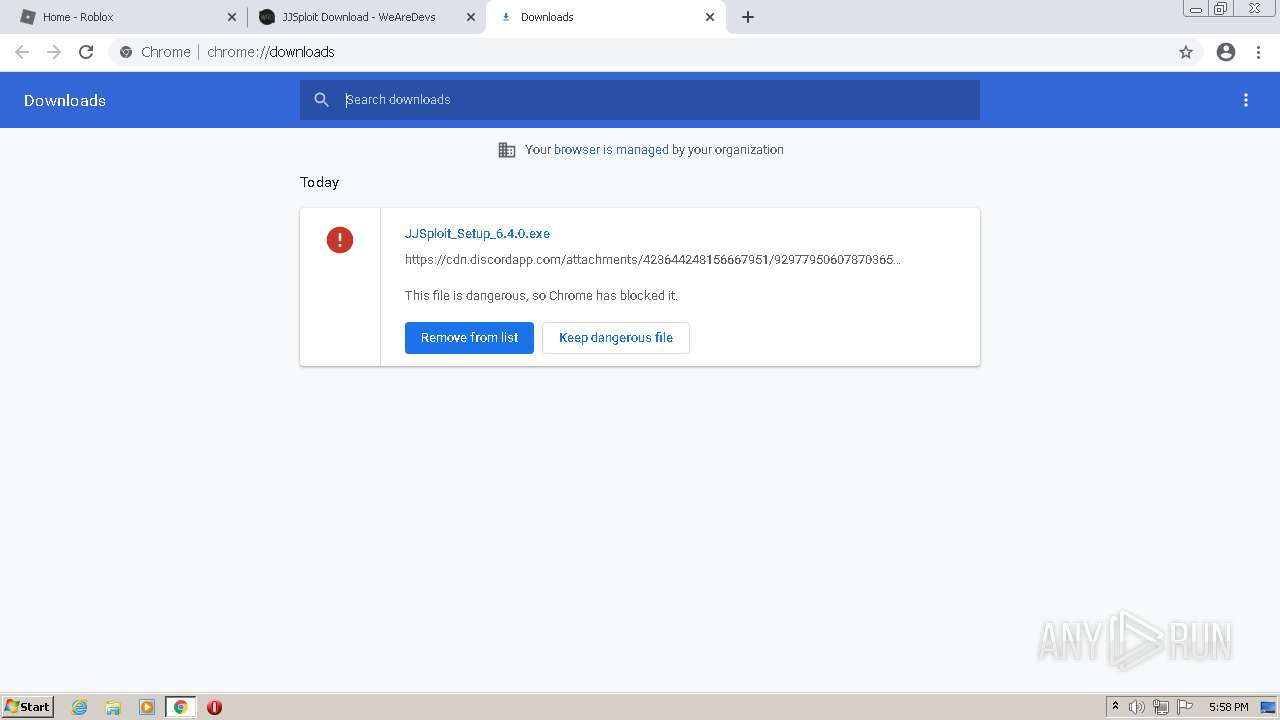
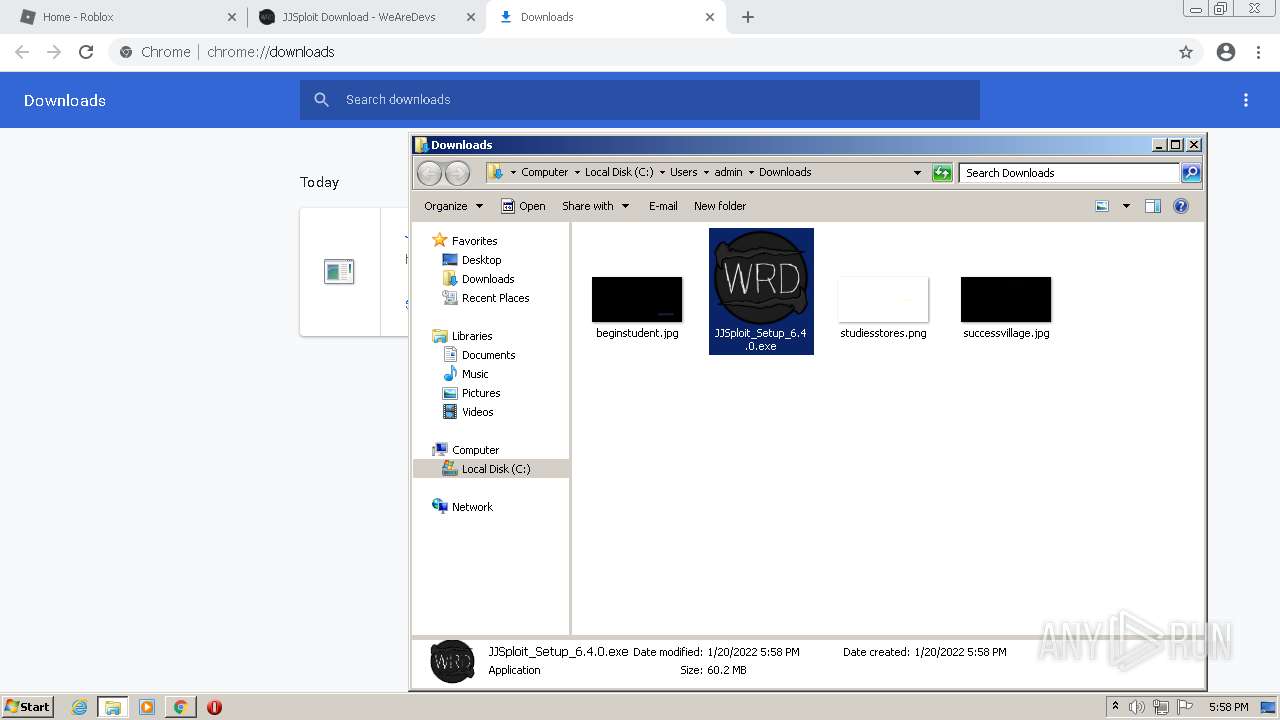
Drops executable file immediately after starts
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1704)
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- RobloxPlayerLauncher.exe (PID: 1608)
Checks supported languages
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- JJSploit.exe (PID: 2300)
- JJSploit.exe (PID: 3412)
- JJSploit.exe (PID: 3880)
- JJSploit.exe (PID: 776)
- RobloxPlayerLauncher.exe (PID: 1608)
- RobloxPlayerLauncher.exe (PID: 3100)
- JJSploit.exe (PID: 1300)
- RobloxPlayerLauncher.exe (PID: 2024)
- RobloxPlayerLauncher.exe (PID: 2948)
- RobloxPlayerBeta.exe (PID: 964)
Reads the computer name
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- JJSploit.exe (PID: 2300)
- JJSploit.exe (PID: 3412)
- JJSploit.exe (PID: 3880)
- RobloxPlayerLauncher.exe (PID: 1608)
- RobloxPlayerLauncher.exe (PID: 3100)
- JJSploit.exe (PID: 1300)
- RobloxPlayerLauncher.exe (PID: 2024)
- RobloxPlayerLauncher.exe (PID: 2948)
- RobloxPlayerBeta.exe (PID: 964)
Creates a software uninstall entry
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- RobloxPlayerLauncher.exe (PID: 1608)
Drops a file that was compiled in debug mode
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- chrome.exe (PID: 1704)
- RobloxPlayerLauncher.exe (PID: 1608)
Drops a file with a compile date too recent
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- chrome.exe (PID: 1704)
- RobloxPlayerLauncher.exe (PID: 1608)
Creates files in the user directory
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
- JJSploit.exe (PID: 2300)
- RobloxPlayerLauncher.exe (PID: 1608)
Application launched itself
- JJSploit.exe (PID: 3904)
- RobloxPlayerLauncher.exe (PID: 2024)
- RobloxPlayerLauncher.exe (PID: 1608)
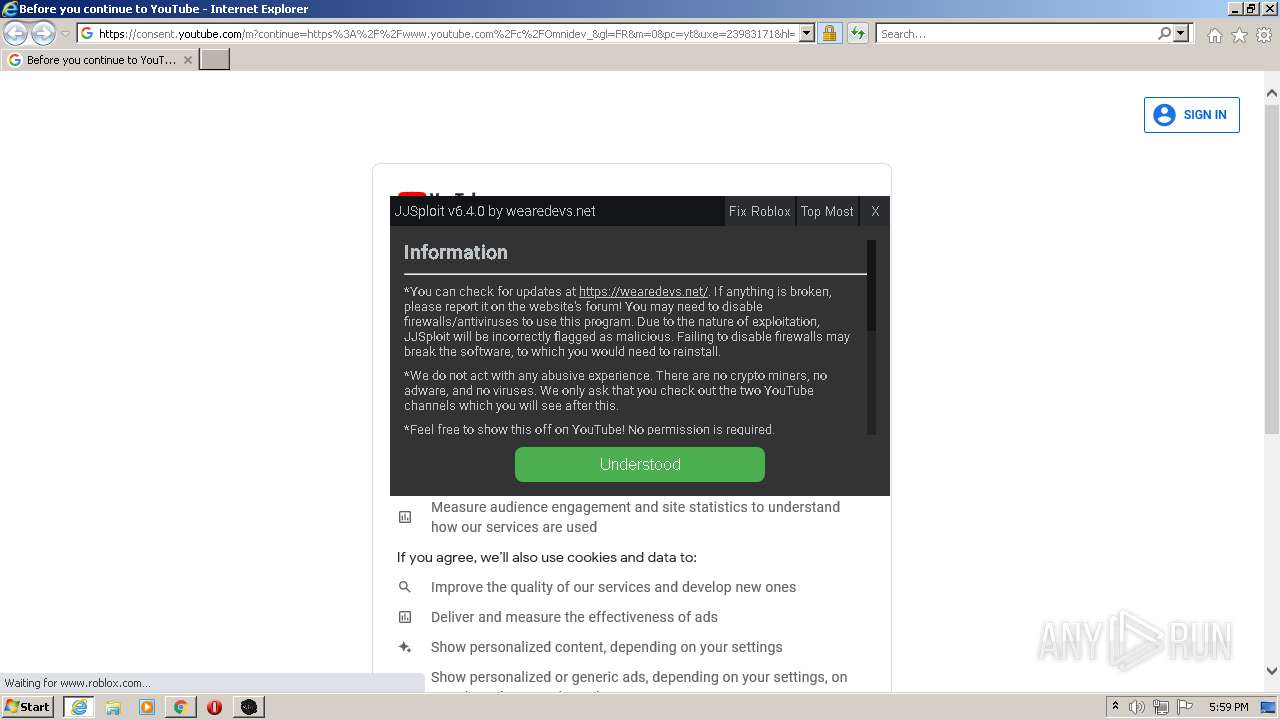
Starts Internet Explorer
- JJSploit.exe (PID: 3904)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 636)
- chrome.exe (PID: 740)
Cleans NTFS data-stream (Zone Identifier)
- RobloxPlayerLauncher.exe (PID: 1608)
Drops a file with too old compile date
- RobloxPlayerLauncher.exe (PID: 1608)
Changes default file association
- RobloxPlayerLauncher.exe (PID: 1608)
Changes IE settings (feature browser emulation)
- RobloxPlayerBeta.exe (PID: 964)
INFO
Checks supported languages
- chrome.exe (PID: 1704)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3768)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 276)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 852)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2996)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 688)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 636)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 524)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 740)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 420)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 872)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 3900)
Application launched itself
- chrome.exe (PID: 1704)
- iexplore.exe (PID: 688)
- iexplore.exe (PID: 3496)
Reads the computer name
- chrome.exe (PID: 1704)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 1304)
- iexplore.exe (PID: 688)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 636)
- chrome.exe (PID: 524)
- chrome.exe (PID: 740)
- chrome.exe (PID: 3900)
Reads the hosts file
- chrome.exe (PID: 1704)
- chrome.exe (PID: 2096)
- JJSploit.exe (PID: 3904)
- JJSploit.exe (PID: 2300)
Reads settings of System Certificates
- chrome.exe (PID: 2096)
- JJSploit.exe (PID: 2300)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 688)
- chrome.exe (PID: 1704)
- RobloxPlayerLauncher.exe (PID: 3100)
- RobloxPlayerLauncher.exe (PID: 2024)
- RobloxPlayerLauncher.exe (PID: 2948)
- RobloxPlayerBeta.exe (PID: 964)
- RobloxPlayerLauncher.exe (PID: 1608)
Reads the date of Windows installation
- chrome.exe (PID: 2560)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 688)
Checks Windows Trust Settings
- chrome.exe (PID: 1704)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 688)
- RobloxPlayerLauncher.exe (PID: 3100)
- RobloxPlayerLauncher.exe (PID: 1608)
- RobloxPlayerLauncher.exe (PID: 2024)
- RobloxPlayerBeta.exe (PID: 964)
- RobloxPlayerLauncher.exe (PID: 2948)
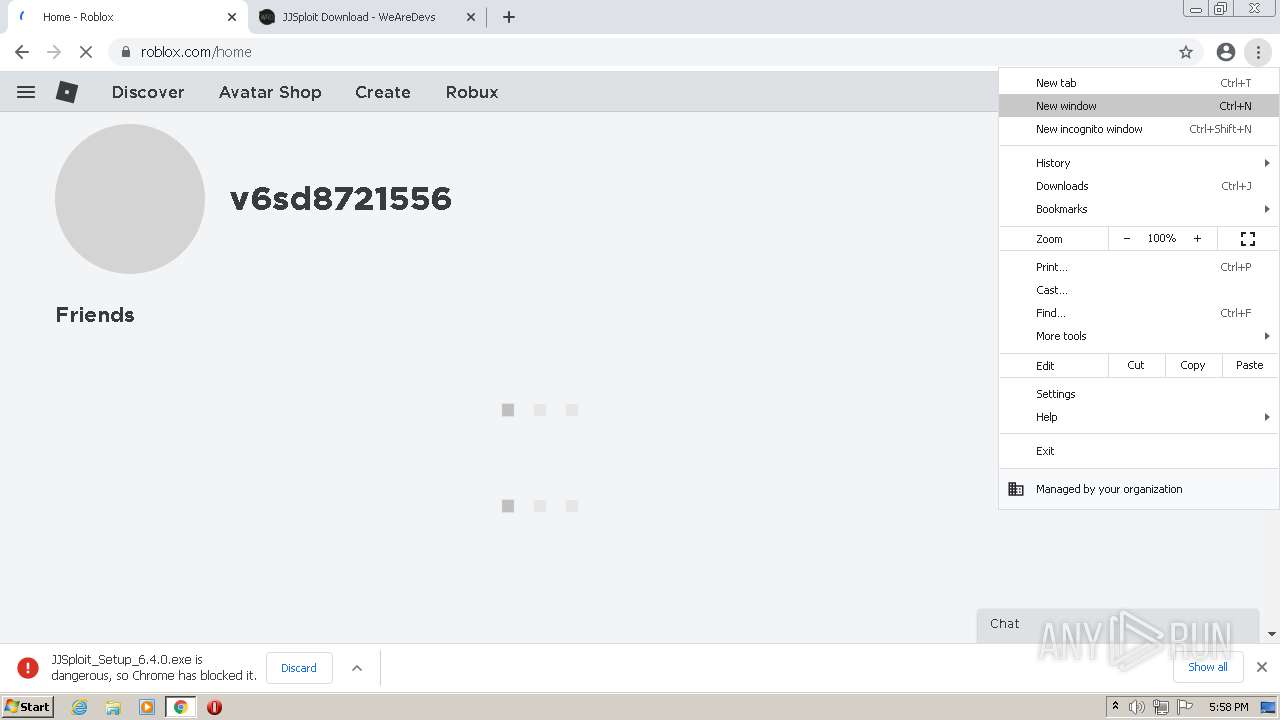
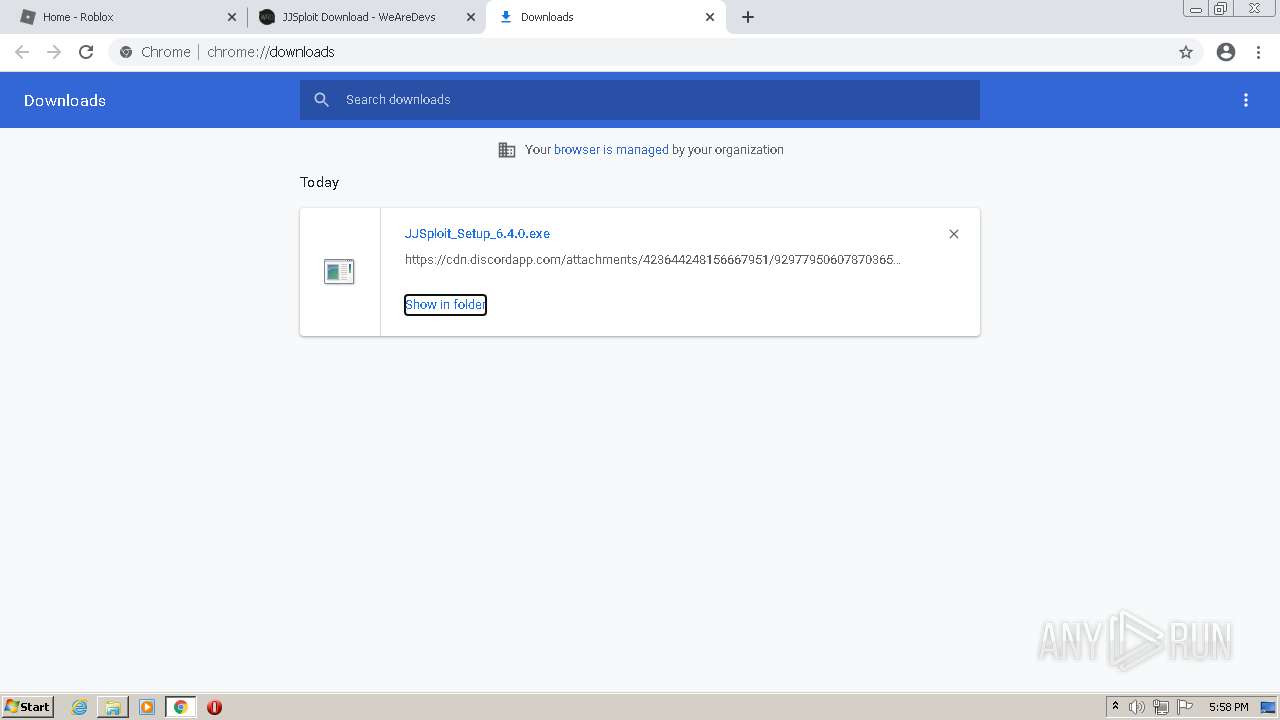
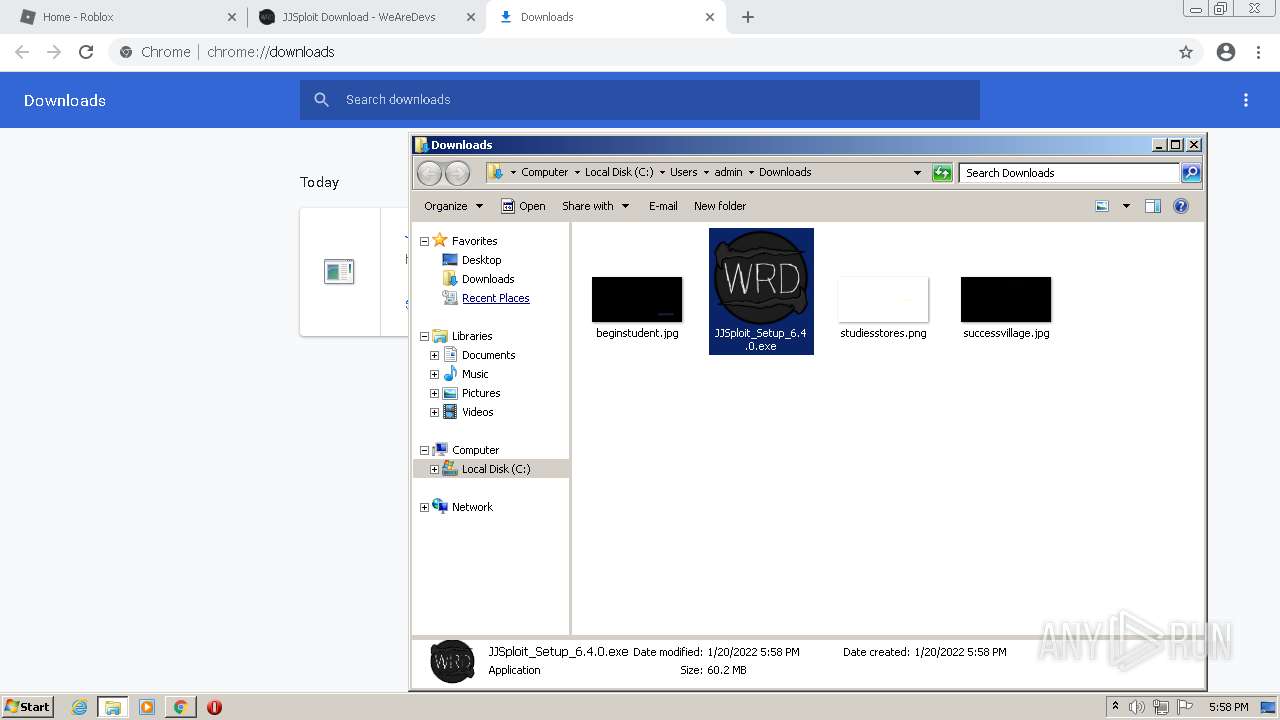
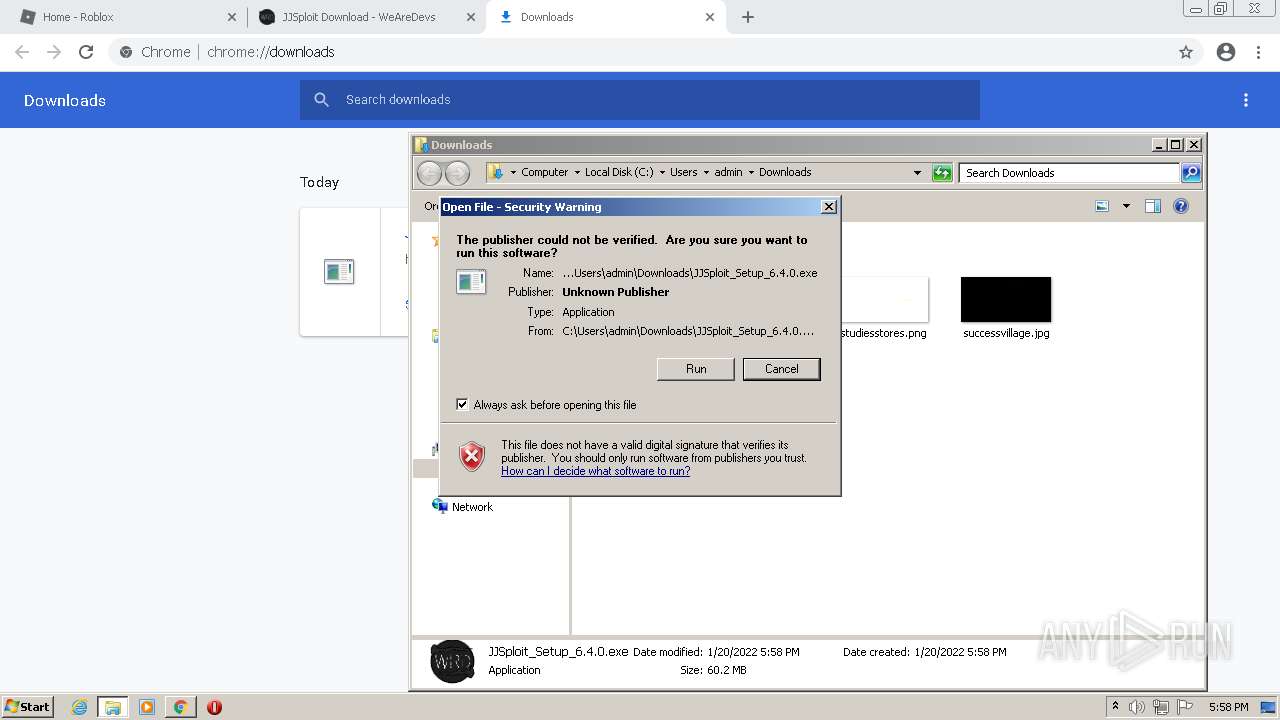
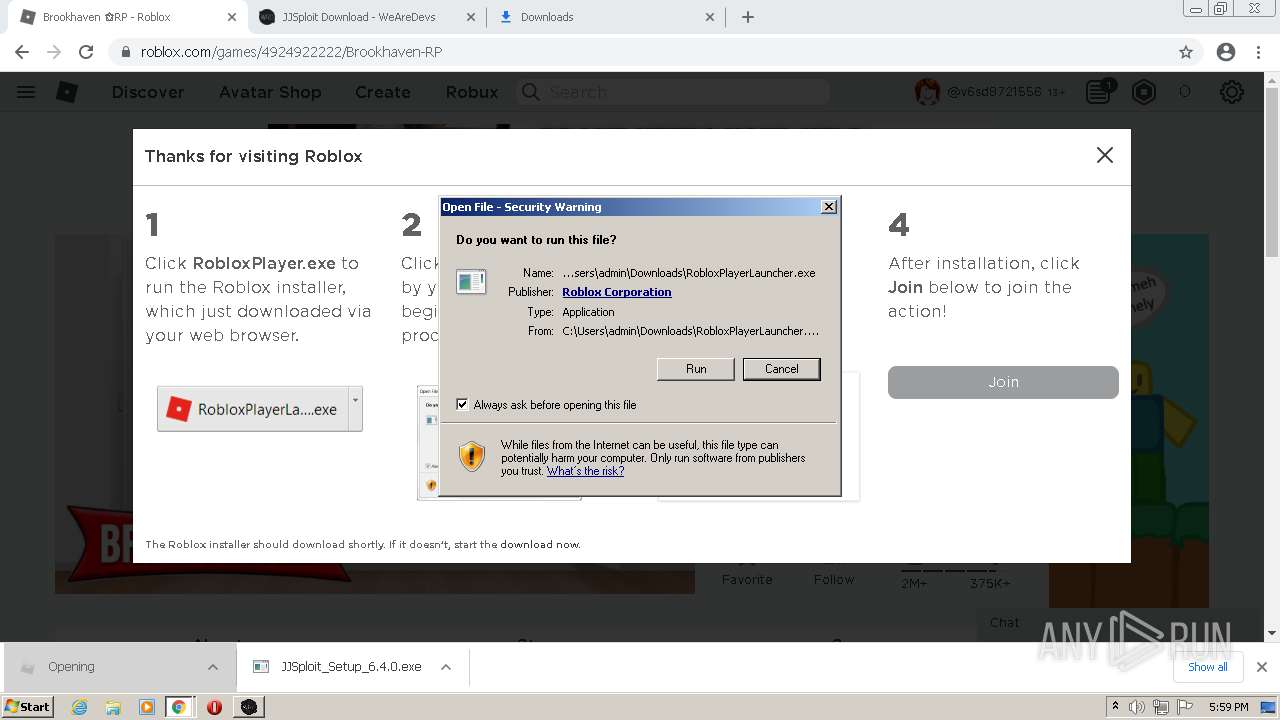
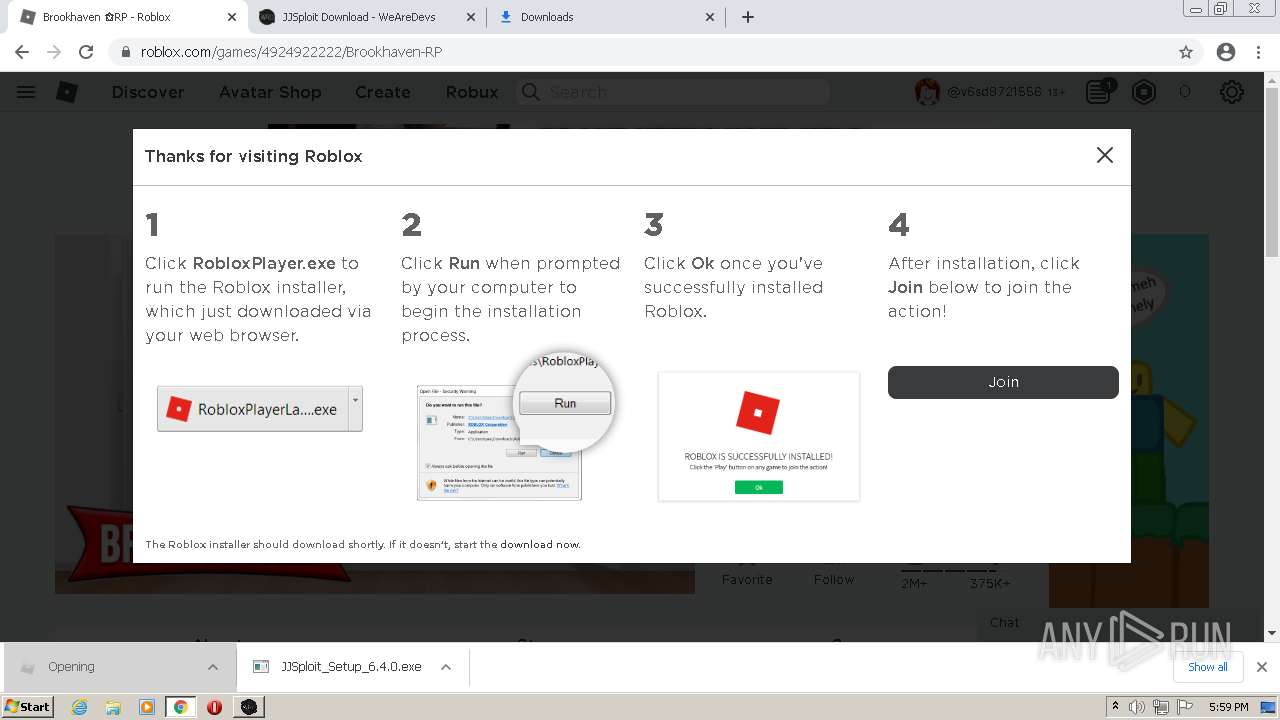
Manual execution by user
- JJSploit_Setup_6.4.0.exe (PID: 3224)
- JJSploit.exe (PID: 3904)
Changes internet zones settings
- iexplore.exe (PID: 688)
- iexplore.exe (PID: 3496)
Creates files in the user directory
- iexplore.exe (PID: 2640)
Reads internet explorer settings
- iexplore.exe (PID: 2640)
Adds / modifies Windows certificates
- iexplore.exe (PID: 688)
Changes settings of System certificates
- iexplore.exe (PID: 688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
116
Monitored processes
73
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4004 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3496 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 688 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/c/Omnidev_ | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1056,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3068 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe" --type=renderer --field-trial-handle=1044,7502469895899141959,12413302277360301835,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploit\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploit\resources\app.asar\build\preload.js" --enable-remote-module --background-color=#fff --enable-websql --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1488 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe | — | JJSploit.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit Exit code: 0 Version: 6.4.0 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
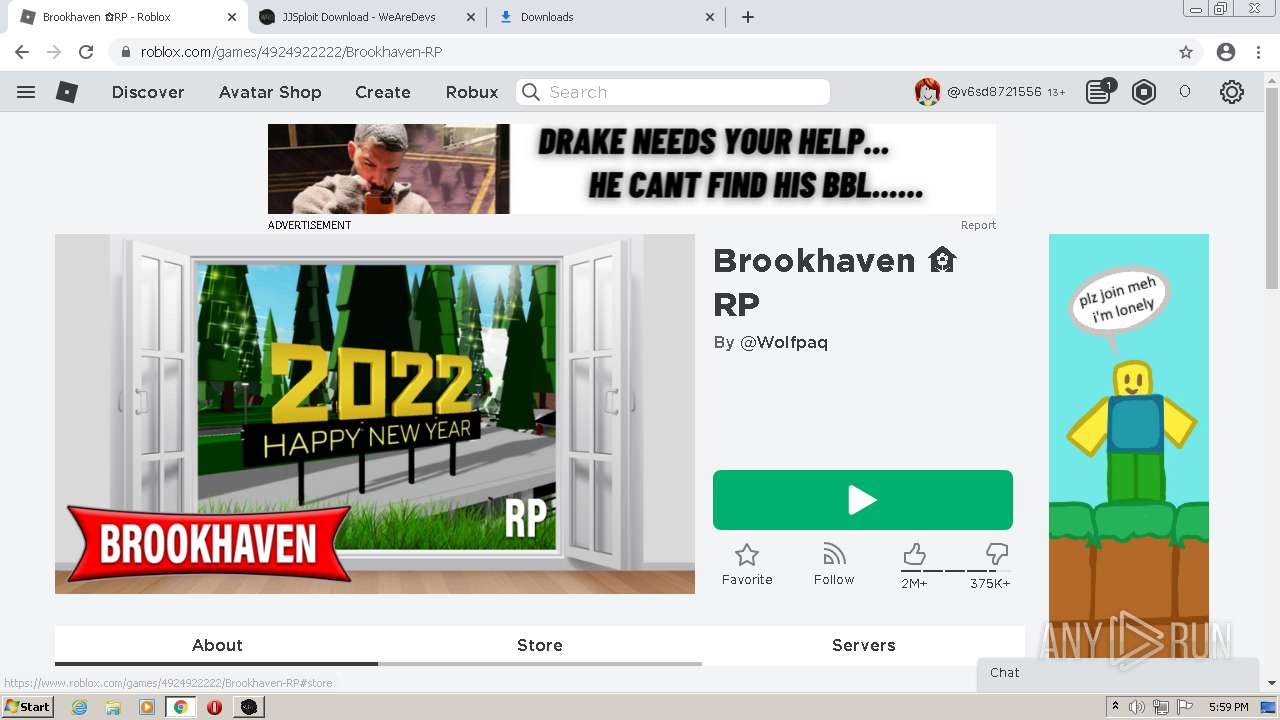
| 964 | "C:\Users\admin\AppData\Local\Roblox\Versions\version-1a42d2dceb424b0b\RobloxPlayerBeta.exe" --play -t 0AD9B49C64DC1704F73391F31CD492E7D9D08035A10EF4B86006A2B7F7B4C06D7B5CBF8CDFBF3FF50B8373171008152079685BA6E9C385201C3DEBED0372D41915158CDA67D0E468143B411ADBBDE23D6B547D53F9F85A473FD4B2305C39BB8CCB101565DB0696C8382D6C2E865F09F3E962BD06918FEFD42471A319E28C8F76FE1B06E01F7E1DA4A97E0F542E80E76FD2B0FA9D9BE90EC0CD322EB2FE9ADC8556601E23 -j https://assetgame.roblox.com/game/PlaceLauncher.ashx?request=RequestGame&browserTrackerId=125041911928&placeId=4924922222&isPlayTogetherGame=false -b 125041911928 --launchtime=1642701713761 --rloc en_us --gloc en_us | C:\Users\admin\AppData\Local\Roblox\Versions\version-1a42d2dceb424b0b\RobloxPlayerBeta.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Game Client Exit code: 1 Version: 0, 509, 0, 5090219 Modules
| |||||||||||||||
Total events
68 674
Read events
67 997
Write events
660
Delete events
17
Modification events
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
30
Suspicious files
167
Text files
246
Unknown types
100
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E9A288-6A8.pma | — | |
MD5:— | SHA256:— | |||
| 2828 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\64bc502f-9cb5-47e8-b398-ad8dbb2165a6.tmp | text | |
MD5:B9FD7DA3E7FC2D5677693D000B4CE6B8 | SHA256:1F88F2E64DF3C0AD905846917C80FCCF32189DCC3E5878AF6E18C464B7D0514D | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:B9FD7DA3E7FC2D5677693D000B4CE6B8 | SHA256:1F88F2E64DF3C0AD905846917C80FCCF32189DCC3E5878AF6E18C464B7D0514D | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF13ef64.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13ef45.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13ef45.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
235
DNS requests
167
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.78 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.92 Kb | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 7.20 Kb | whitelisted |
636 | iexplore.exe | GET | 200 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?17f59b682c2b5d60 | US | compressed | 4.70 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.1 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.7 Kb | whitelisted |
688 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
688 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgAde1VeKYIQoAAAABK4GI | US | der | 472 b | whitelisted |
2640 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG9FXshPqpwWCgAAAAEn3MY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2096 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2096 | chrome.exe | 128.116.123.3:443 | web.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
— | — | 128.116.123.3:443 | web.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
2096 | chrome.exe | 142.250.185.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 142.250.185.196:443 | www.google.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 142.250.185.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 142.250.185.238:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
web.roblox.com |
| malicious |
accounts.google.com |
| shared |
www.roblox.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RobloxPlayerBeta.exe | 2022-01-20T18:01:59.027Z,0.027592,088c,6 [FLog::Output] RobloxGitHash: 6808cda89fc399b0dd5f649acece51d2cd151e77 |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-20T18:01:59.027Z,0.027592,088c,6 [FLog::Output] The channel is production |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-20T18:01:59.103Z,0.103087,088c,6 [FLog::Error] Test log: Map check complete and successful! |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-20T18:01:59.103Z,0.103087,088c,6 [FLog::Error] Dynamic initializer test result: SUCCESS |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-20T18:01:59.103Z,0.103087,088c,6 [FLog::Output] TaskSchedulerMk2::applyAsyncTaskThreadCount( 3 ) <req: 0 active: 0> |
RobloxPlayerBeta.exe | |