| File name: | 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos |
| Full analysis: | https://app.any.run/tasks/cdc7b747-4468-4db3-a6b6-1937d3dad096 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2025, 11:33:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 1883B0F1EFD21791604C3D8CB6F12794 |
| SHA1: | 76B5889B91F5A7DC3D5AB651F8E0A276A8D28097 |
| SHA256: | 3256B8B356CCDE6FD8C931DF82FAB40909C4FEB1783249DBD0B326437C45C62B |
| SSDEEP: | 49152:V84b1NZqzohBDBBBBBBB60B6BB6BB76JQmATmnlIUz:V84b1NZqULmnlj |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 2848)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Starts itself from another location
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Reads security settings of Internet Explorer
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
INFO
The sample compiled with english language support
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Creates files in the program directory
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
- installer0.exe (PID: 6636)
Reads the software policy settings
- slui.exe (PID: 684)
- installer0.exe (PID: 6636)
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Create files in a temporary directory
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Reads the machine GUID from the registry
- installer0.exe (PID: 6636)
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Process checks computer location settings
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Checks supported languages
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
- installer0.exe (PID: 6636)
Checks proxy server information
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
- slui.exe (PID: 684)
- installer0.exe (PID: 6636)
Reads the computer name
- installer0.exe (PID: 6636)
- 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe (PID: 1484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:01:05 11:56:12+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 532480 |
| InitializedDataSize: | 1158656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5981e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1149.8 |
| ProductVersionNumber: | 1.1.1149.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
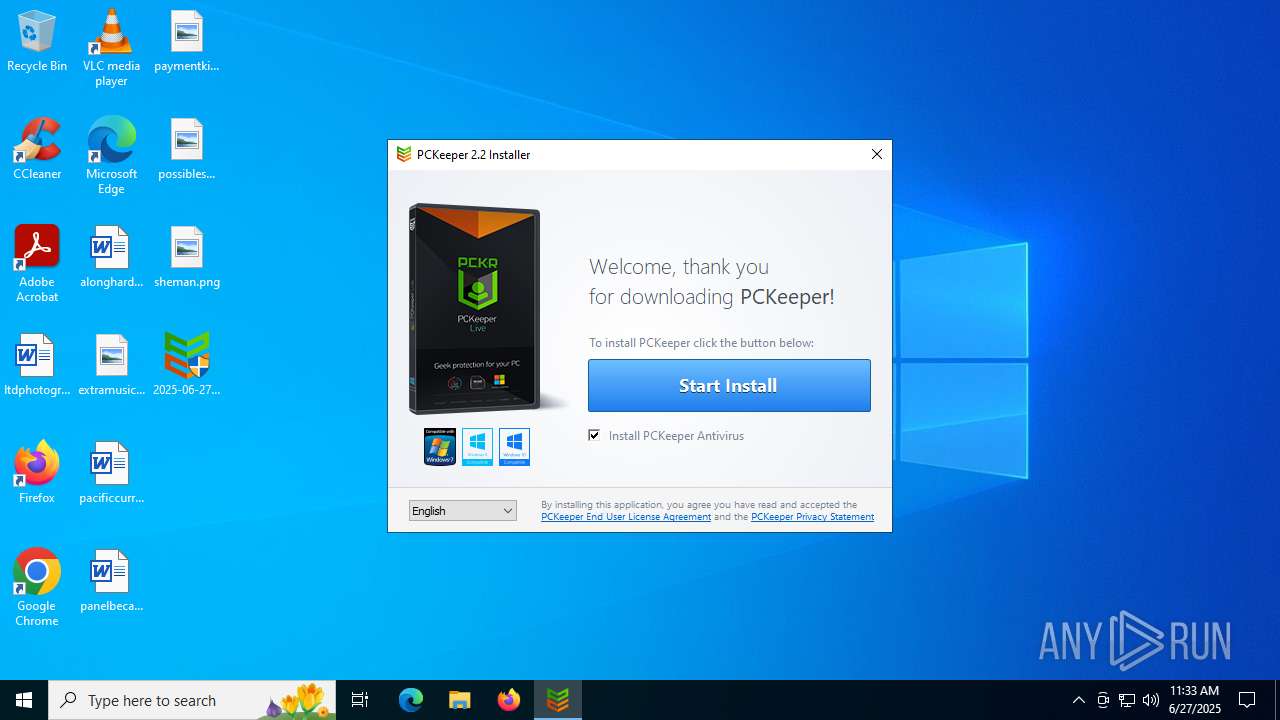
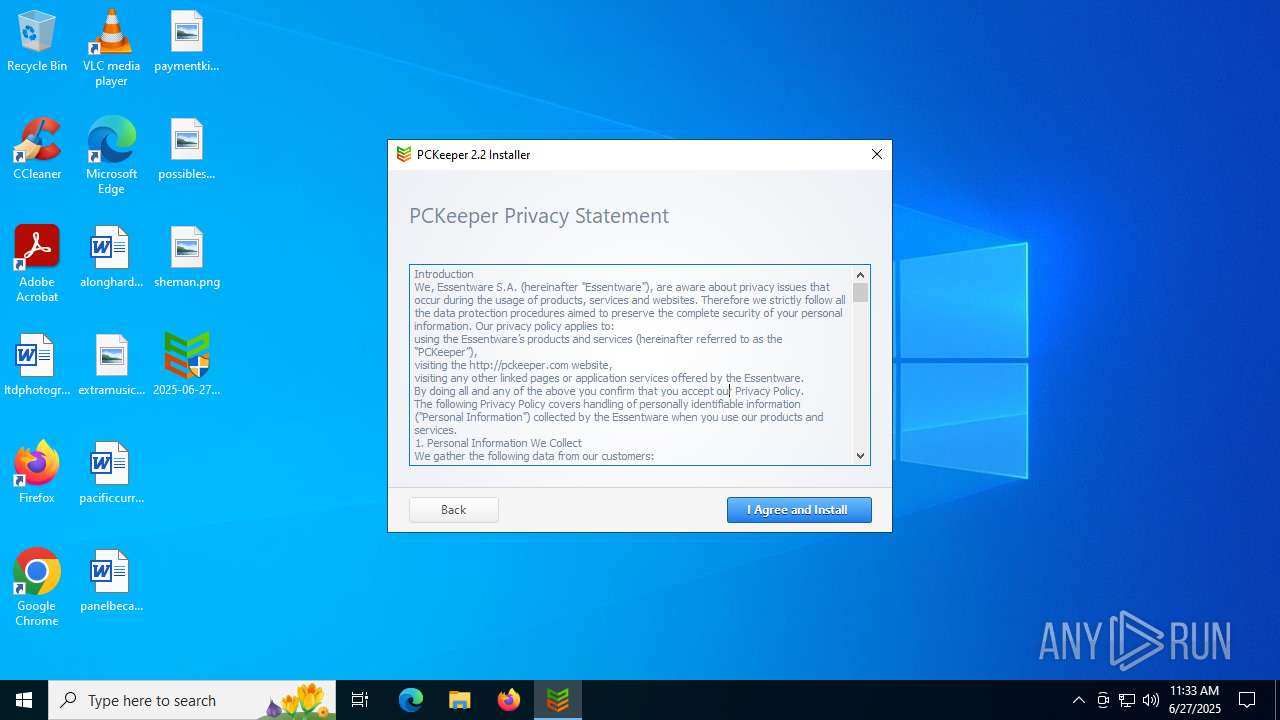
| CompanyName: | Essentware |
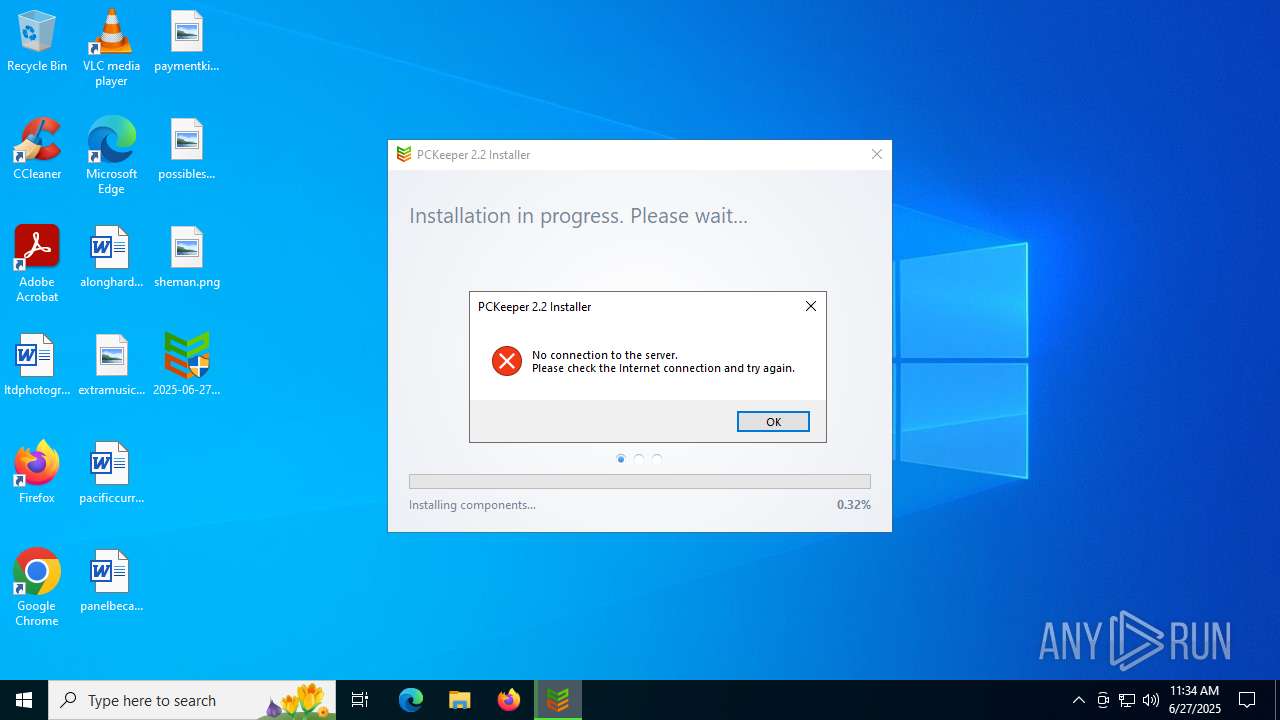
| FileDescription: | Pckeeper Internet Installer |
| FileVersion: | 1.1.1149.8 |
| InternalName: | installer.exe |
| LegalCopyright: | (c) ESSENTWARE S.A. All rights reserved. |
| OriginalFileName: | installer.exe |
| ProductName: | Pckeeper Installer |
| ProductVersion: | 1.1.1149.8 |
Total processes
135
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\Desktop\2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe" | C:\Users\admin\Desktop\2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | explorer.exe | ||||||||||||
User: admin Company: Essentware Integrity Level: HIGH Description: Pckeeper Internet Installer Exit code: 8 Version: 1.1.1149.8 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\Desktop\2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe" | C:\Users\admin\Desktop\2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | — | explorer.exe | |||||||||||
User: admin Company: Essentware Integrity Level: MEDIUM Description: Pckeeper Internet Installer Exit code: 3221226540 Version: 1.1.1149.8 Modules
| |||||||||||||||
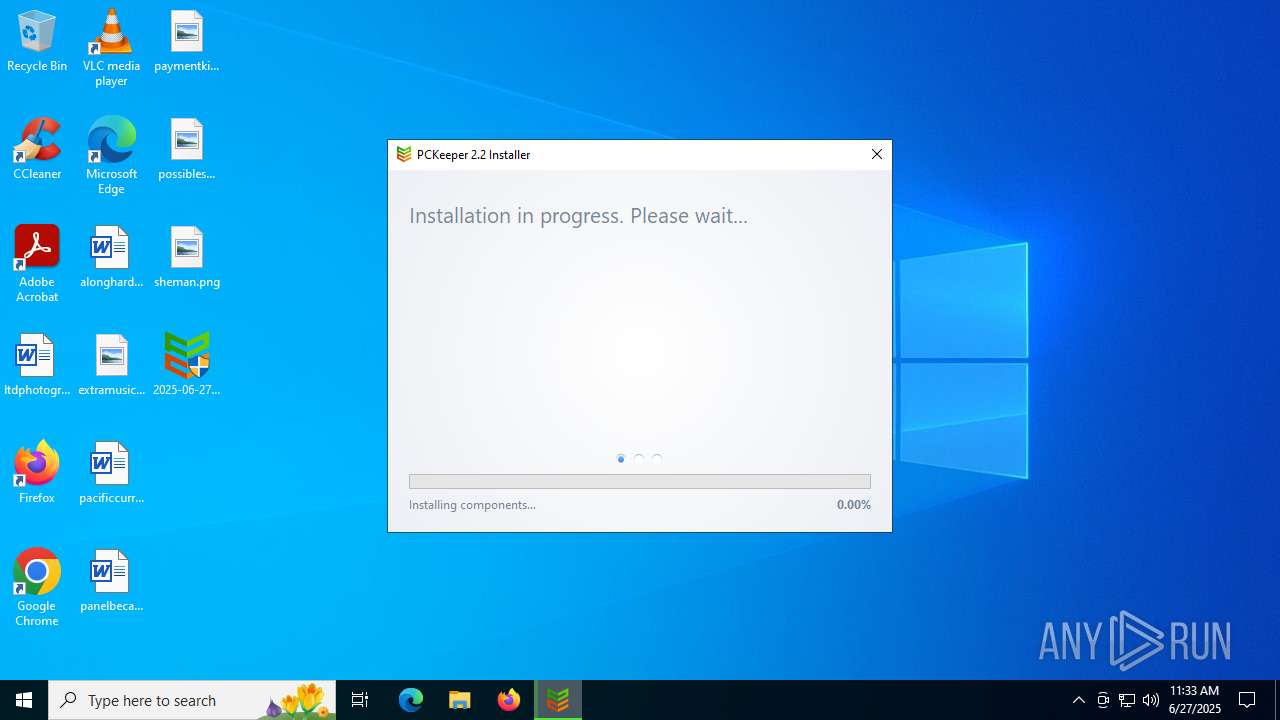
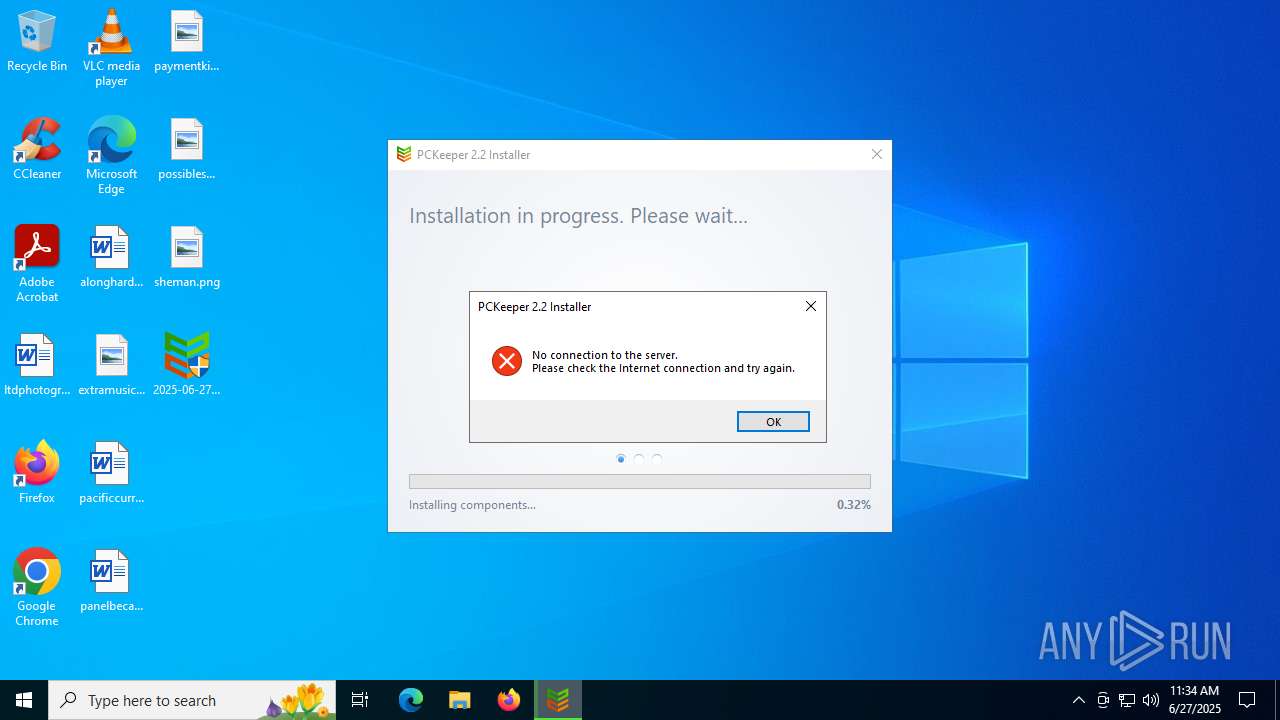
| 6636 | "C:\Users\admin\AppData\Local\Temp\installer0.exe" /R /VERACC=1.1.69.0 /VERPCK=2.2.2155.0 /VERSEC=1.1.1057.0 | C:\Users\admin\AppData\Local\Temp\installer0.exe | 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | ||||||||||||
User: admin Company: Essentware Integrity Level: HIGH Description: Pckeeper Internet Installer Exit code: 8 Version: 1.1.1149.8 Modules
| |||||||||||||||
Total events
11 812
Read events
11 800
Write events
12
Delete events
0
Modification events
| (PID) Process: | (1484) 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\AccountService |
| Operation: | write | Name: | zi_cid |
Value: 01000000DCEF96F1C7F397F5C3F79DF9CDFBCEFDD3FF3801370365053F0725093B0B3D0D6B0F72113F132D1526177919221B311D271F41211B23462511271E29192B192D162F0431003305350C370B39083B0E3D5B3F23412443724574477849784B744D7A4F69513153615533576F593C5B3D5D6F5F596106635C655F6758695E6B5E6D0C6F457110731575137742794C7B497D4E7FB981B783B085B787B189B38BEE8DEF8FA391A393A395F597AD99F99BAD9DFB9FC3A194A396A5C4A7CBA999AB99AD9EAF89B1D6B381B58EB78FB9BABB | |||
| (PID) Process: | (1484) 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\Installer |
| Operation: | write | Name: | Language |
Value: en | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\Installer |
| Operation: | write | Name: | Language |
Value: en | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\Pckeeper |
| Operation: | write | Name: | zi_inf |
Value: 5F0400004C0000000100000000000000000001FFFFFFFF00000000000000000000000000000001010000010000000000000000000000000000000101000000460069006E00640041006E006400460069007800500043004B0053006D0061006C006C000000FEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFE000100000000000001000000000000000000000000000100000100000000000065006D0070007400790053007400720069006E0067000000FEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFE4B4461B5E823552026881AD9DFFE96D5AD05AC147DC1AC032FC99AD0CF4E5226025872E9FC05B0D15321E2C7CAAE86E2392188335C2C55324B01727E1F2FD83ADD912EA1ADA8E69653DC969D22E1D43292EAFC22E4444DDBA7553B4291AF83A09EA51D6DE70A82F4EEBF6E8812D5185D9FC5AC0B0E8ED5D34E188F01B6E3358E | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\Pckeeper |
| Operation: | write | Name: | zi_id |
Value: 308.3419308.1498226065.20.mzb | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\Pckeeper |
| Operation: | write | Name: | zi_bid |
Value: 33_2144011701 | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\PCKAV |
| Operation: | write | Name: | zi_inf |
Value: 0B04000000000000000000460069006E00640041006E006400460069007800410056000000FEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFE65006D0070007400790053007400720069006E0067000000FEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFEFE51341992F391F91A4AC8721515694213D4D132A6EEA925E5DBC59686B71E4E4E57494B9C8914335F1C028C2261F6DE1AAC33D1C9423BBFC228EE5173784BC605D6E898E3E0631A44B3023F5B1BF644472ED0E6F408784AA7D643D7FDFBBE2BC883F467B0053FA36AF697540A89E92446404B79B99E1072752EABB9460CE0AA04 | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\PCKAV |
| Operation: | write | Name: | zi_id |
Value: 308.3419308.1498226065.20.mzb | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\PCKAV |
| Operation: | write | Name: | zi_bid |
Value: 33_2144011701 | |||
| (PID) Process: | (6636) installer0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Essentware\Pckeeper |
| Operation: | write | Name: | Language |
Value: en | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6636 | installer0.exe | C:\ProgramData\Essentware\Installer\installer0.exe0.llog | text | |
MD5:3F502C1D2AE766C2A75BD720C63FCBB9 | SHA256:855D13D1346C93FE1F1B34B4726F149C24E85B67735CAC4CAB55D1252E32724A | |||
| 1484 | 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | C:\Users\admin\AppData\Local\Temp\installer0.exe | executable | |
MD5:1883B0F1EFD21791604C3D8CB6F12794 | SHA256:3256B8B356CCDE6FD8C931DF82FAB40909C4FEB1783249DBD0B326437C45C62B | |||
| 1484 | 2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | C:\ProgramData\Essentware\Installer\2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe0.llog | text | |
MD5:A61721397695BD05FB08CCCF9EAA5E32 | SHA256:3854439E92320E69E2BEAC24497C278ABF25ED52A447A39F69C3CEF692D80170 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
23
DNS requests
44
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4916 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.50.88.234:443 | https://dc.services.visualstudio.com/v2/track | unknown | binary | 62 b | whitelisted |
— | — | POST | 200 | 20.50.88.234:443 | https://dc.services.visualstudio.com/v2/track | unknown | binary | 62 b | whitelisted |
— | — | POST | 200 | 20.50.88.234:443 | https://dc.services.visualstudio.com/v2/track | unknown | binary | 62 b | whitelisted |
— | — | POST | 200 | 20.50.88.234:443 | https://dc.services.visualstudio.com/v2/track | unknown | binary | 62 b | whitelisted |
— | — | POST | 200 | 20.50.88.234:443 | https://dc.services.visualstudio.com/v2/track | unknown | binary | 62 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4916 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.168.122:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.168.122:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4916 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
event.pckeeper.com |
| unknown |
crl.microsoft.com |
| whitelisted |
cdn.pckeeper.com |
| unknown |
www.microsoft.com |
| whitelisted |
app.pckeeper.com |
| unknown |
dc.services.visualstudio.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.387 Default Installer Info 5772 StatReporter.cpp CStatReporter::ThreadSendStat 78 22 "ThreadSendStat started"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.387 Default Installer Info 5712 StatReporter.cpp CStatReporter::Start 34 72 "StatReporter thread started, hThread = 0x168, stats count in the list: 0"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.465 Default Installer Info 5712 InstallingStrategy.cpp CInstallingStrategy::IsInstalledAV 152 34 "Only windows defender is installed"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Installer Info 5712 Installer.cpp wWinMain 128 72 "Installer: Build: "Jan 5 2017", "13:55:55", RELEASE version 1.1.1149.8
"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Installer Info 5712 Affid.cpp CAffid::InitializeData 58 30 "start CAffid::InitializeData()"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Installer Info 5712 Installer.cpp wWinMain 127 9 "CmdLine: "
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Installer Info 5712 Helpers.cpp DeleteOldReg 165 53 "RegOpenKeyEx SOFTWARE\Kromtech for deleting result: 2"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Installer Info 5712 Helpers.cpp DeleteOldReg 165 53 "RegOpenKeyEx SOFTWARE\Kromtech for deleting result: 2"
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Installer Info 5712 Installer.cpp Normal 344 16 "Not admin start."
|
2025-06-27_1883b0f1efd21791604c3d8cb6f12794_adposhel_black-basta_darkgate_elex_luca-stealer_mespinoza_remcos.exe | 2025.06.27 11:33:48.480 Default Analytics Default 5712 InstallingStrategy.cpp CInstallingStrategy::CInstallingStrategy 30 42 "OS Info( isX64, dwOSVersion): 1, 0x6020000"
|