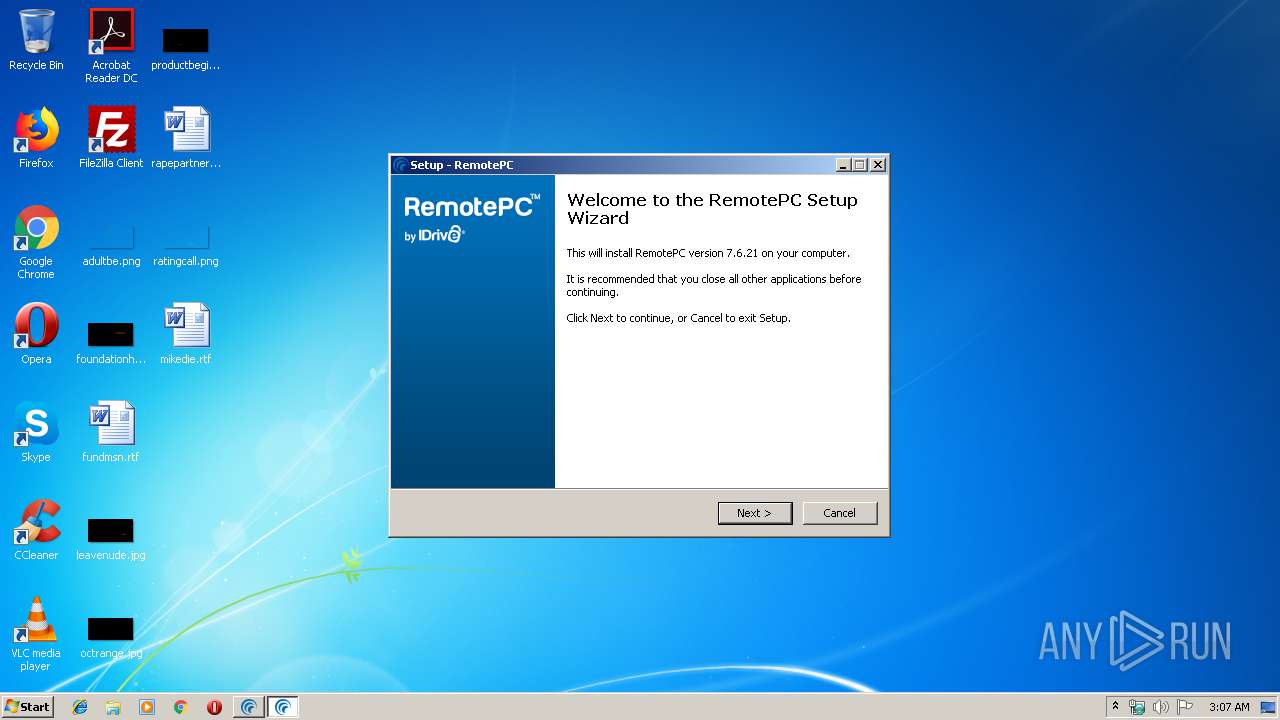
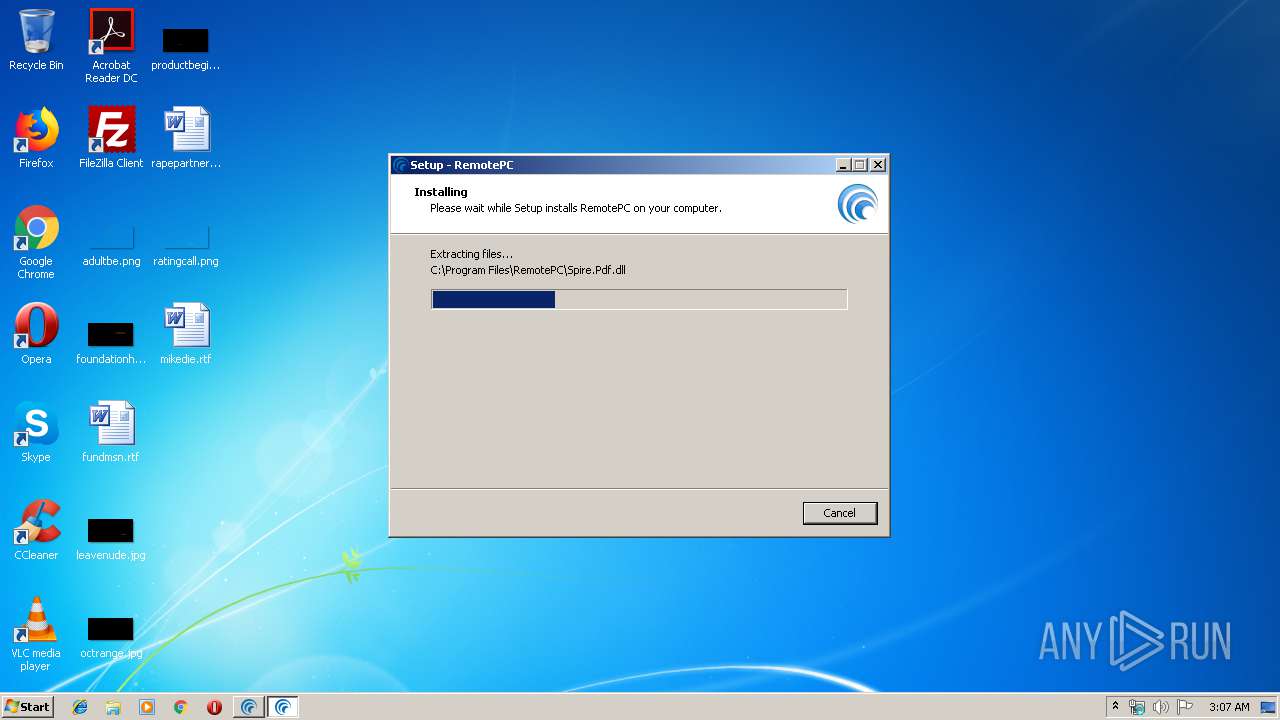
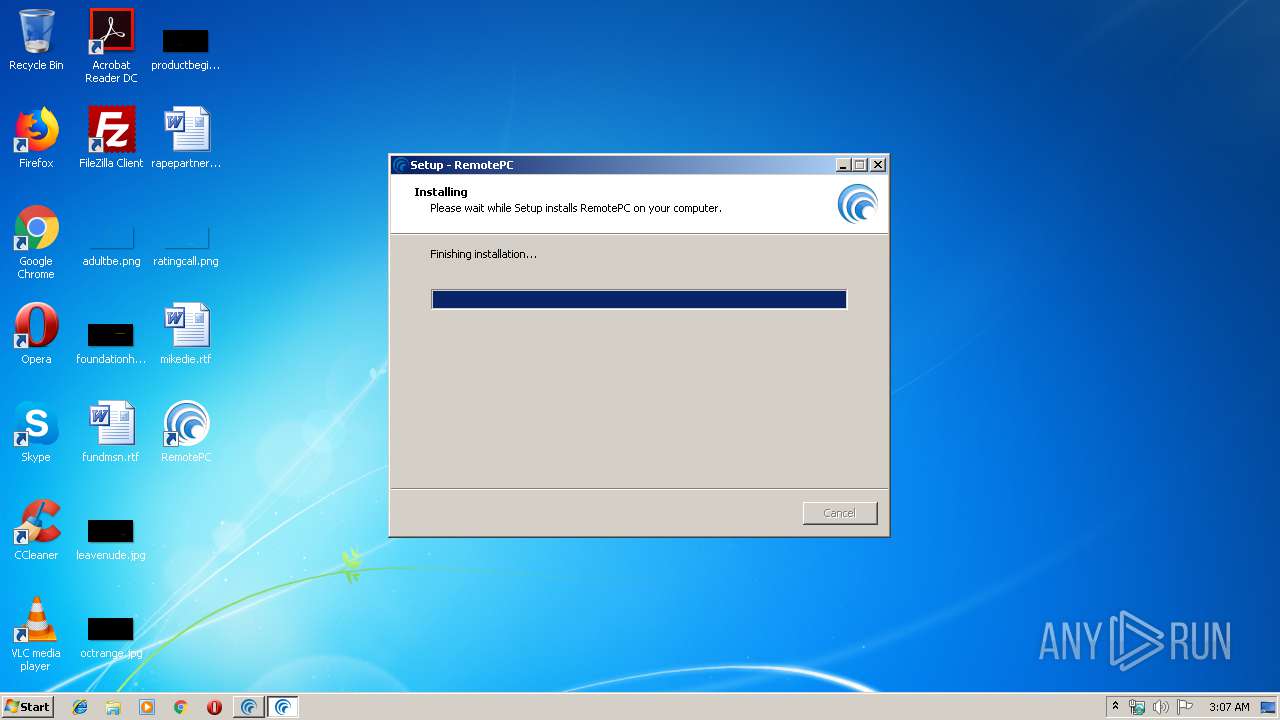
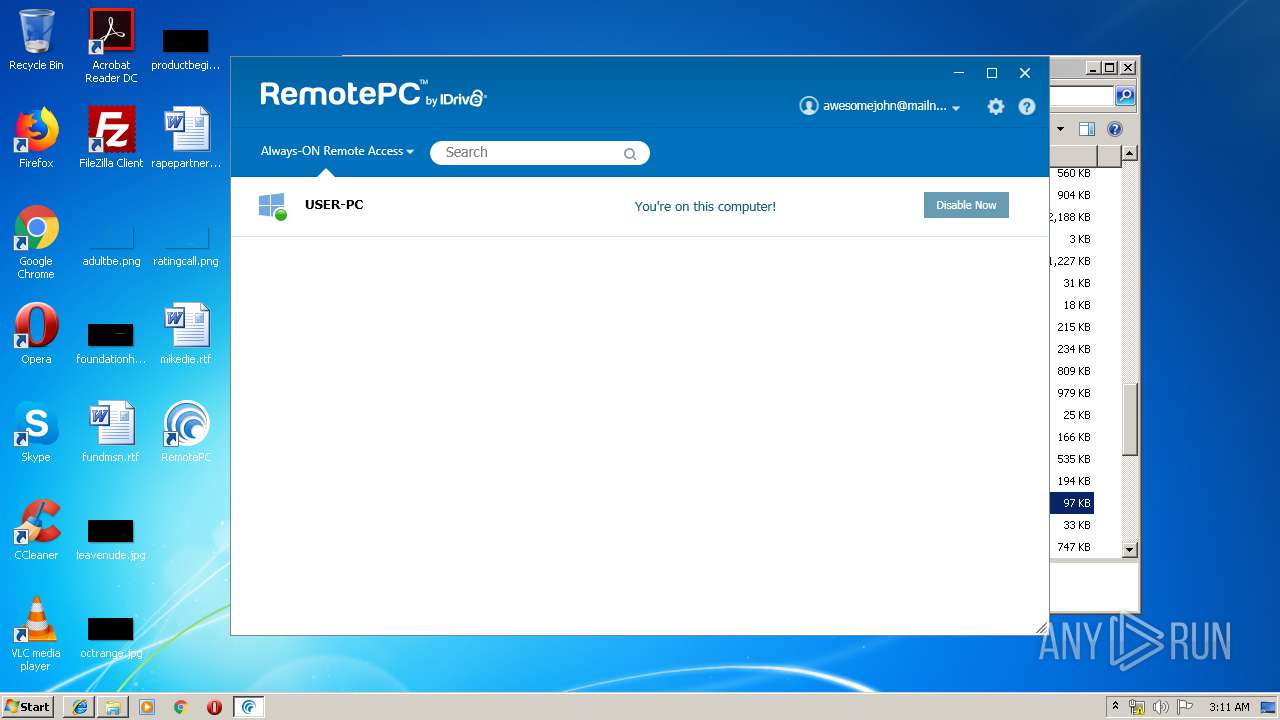
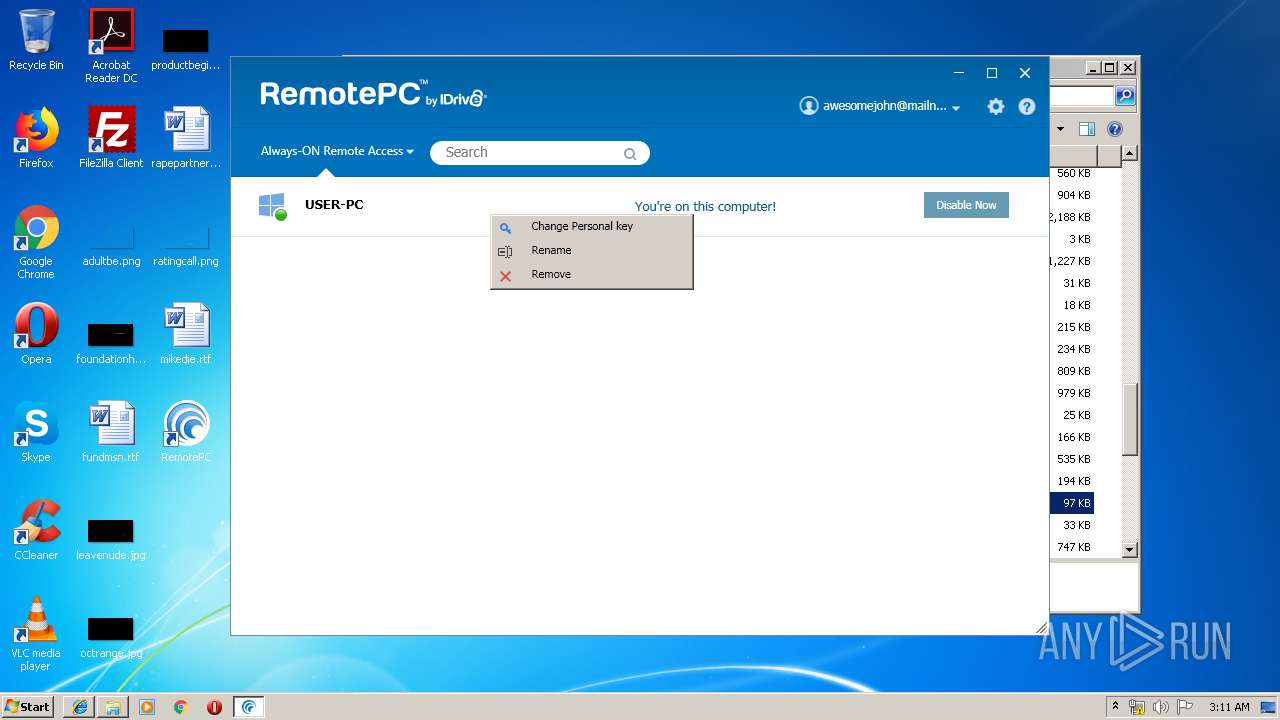
| download: | RemotePC.exe |
| Full analysis: | https://app.any.run/tasks/67f6a667-1839-4788-9986-1c0f41ceb69a |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2019, 03:06:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C7E49A18C47325B61A1E628335D53E7C |
| SHA1: | A8FD3D770DEC300E57A8517CF8AE1058009D78B3 |
| SHA256: | 324D5A764E6833BC3EC70CA59A6C37C053C0D9D3D07B982B2E041701F5196640 |
| SSDEEP: | 786432:kn+TWk074CkuG4iaHswZwwD5qmZHMAQmlkYq:k+yF4jgMmwsqmqVmlkY |
MALICIOUS
Application was dropped or rewritten from another process
- RPCFirewall.exe (PID: 976)
- RemotePCLauncher.exe (PID: 3224)
- RemotePCService.exe (PID: 2488)
- RemotePCLauncher.exe (PID: 1940)
- RPCPrinterDownloader.exe (PID: 3980)
- RemotePCUI.exe (PID: 820)
- RPCProxyLatency.exe (PID: 2004)
- RPCDownloader.exe (PID: 2304)
- RPCProxyLatency.exe (PID: 3732)
- PreUninstall.exe (PID: 3788)
Loads dropped or rewritten executable
- RemotePCService.exe (PID: 2488)
- RemotePCUI.exe (PID: 820)
- rundll32.exe (PID: 3336)
- spoolsv.exe (PID: 1204)
- RPCProxyLatency.exe (PID: 2004)
- explorer.exe (PID: 352)
- RPCProxyLatency.exe (PID: 3732)
SUSPICIOUS
Executable content was dropped or overwritten
- RemotePC.tmp (PID: 2232)
- PreUninstall.exe (PID: 3788)
- RemotePC.exe (PID: 3864)
- RemotePC1.exe (PID: 236)
- RemotePC.exe (PID: 1324)
- RemotePC1.tmp (PID: 892)
- msiexec.exe (PID: 2276)
- rundll32.exe (PID: 3336)
- spoolsv.exe (PID: 1204)
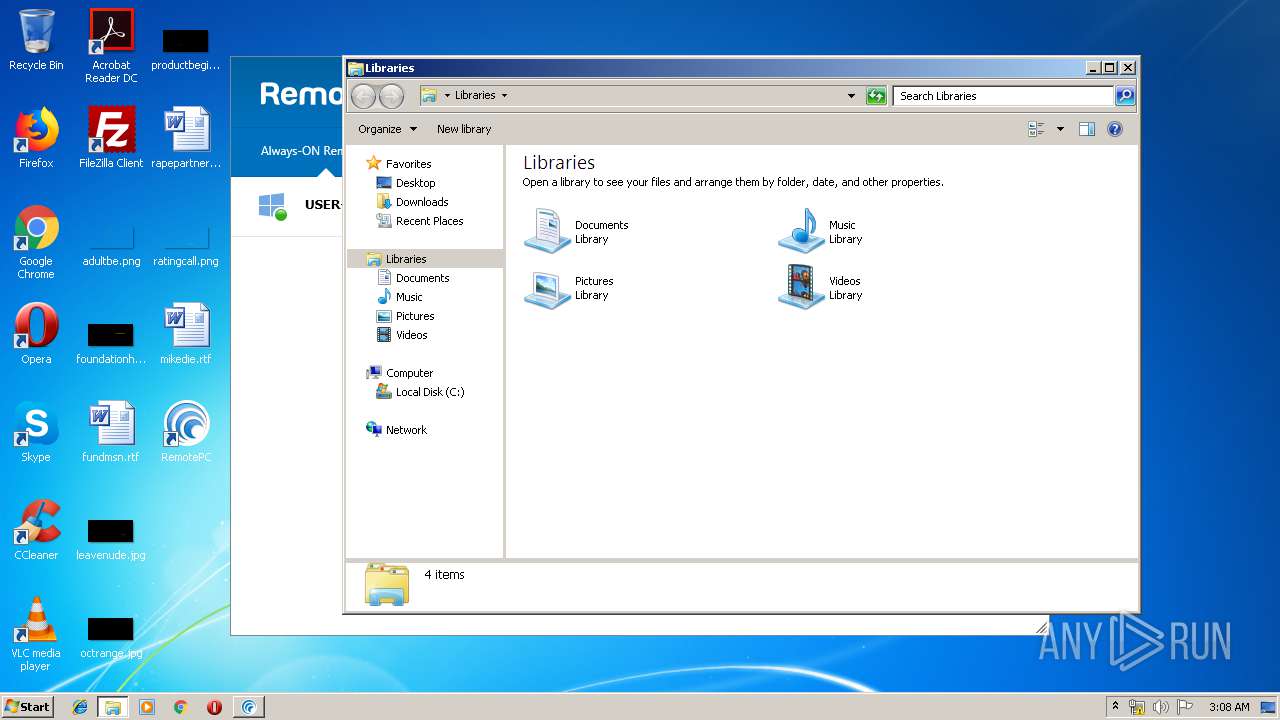
Creates files in the user directory
- RemotePC1.tmp (PID: 892)
- RemotePCLauncher.exe (PID: 3224)
Starts SC.EXE for service management
- RemotePC1.tmp (PID: 892)
Executed as Windows Service
- RemotePCService.exe (PID: 2488)
Creates files in the Windows directory
- RemotePCService.exe (PID: 2488)
- RPCPrinterDownloader.exe (PID: 3980)
- msiexec.exe (PID: 2276)
- rundll32.exe (PID: 3336)
- spoolsv.exe (PID: 1204)
Modifies the open verb of a shell class
- RemotePCLauncher.exe (PID: 3224)
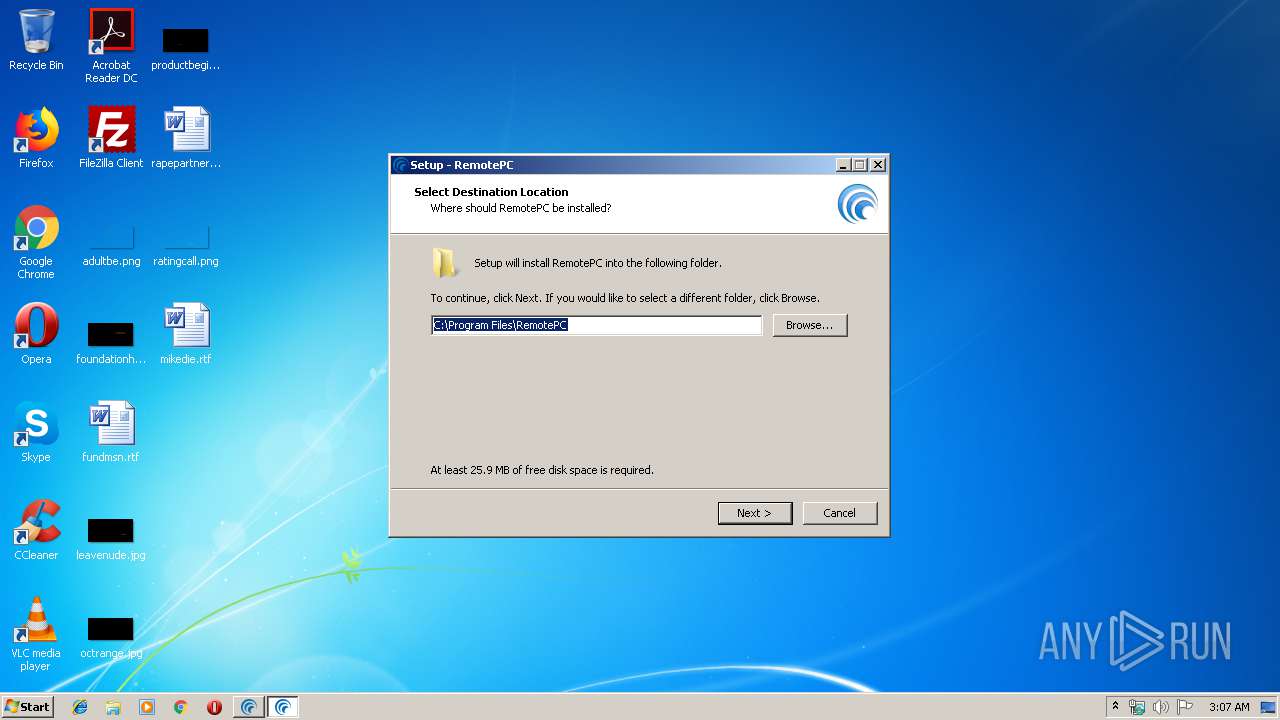
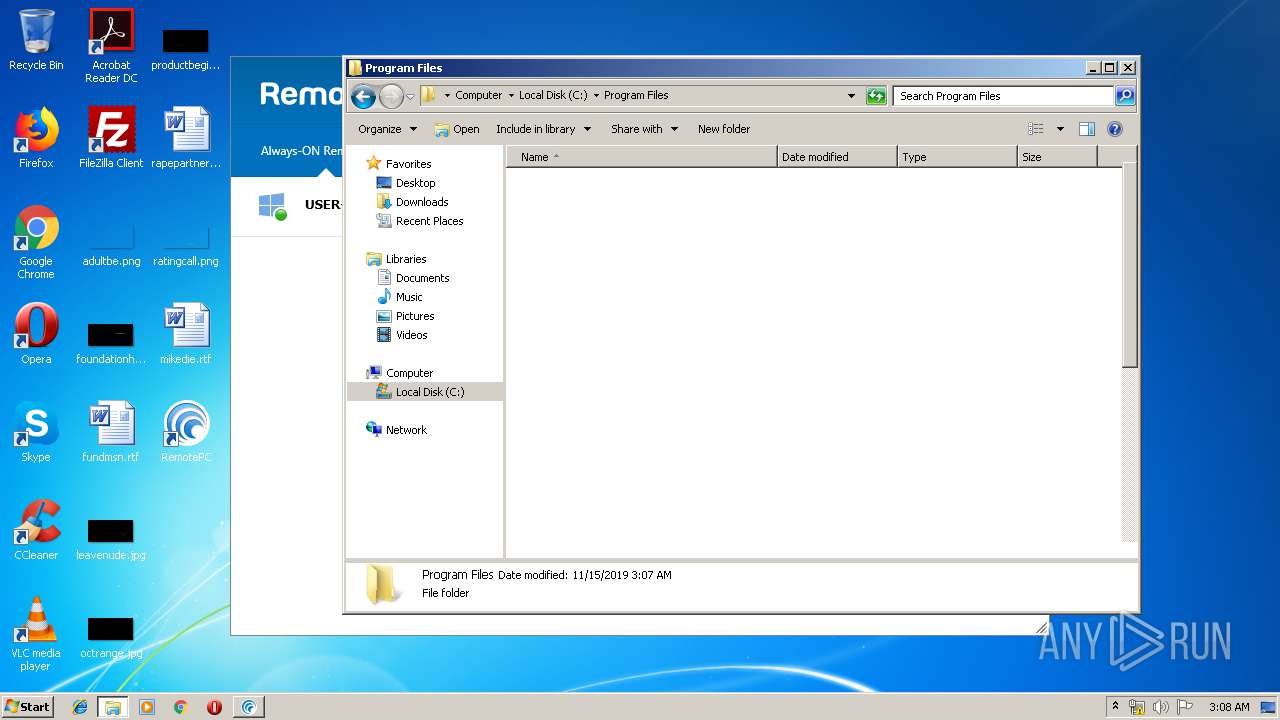
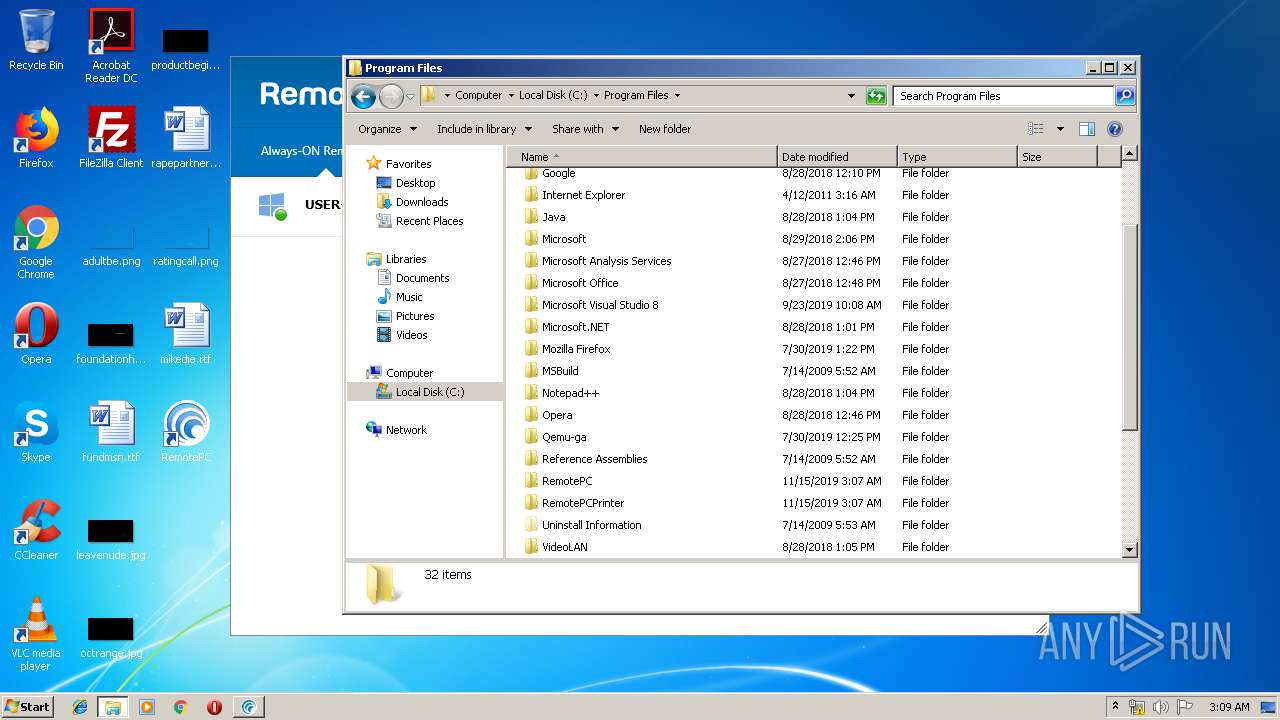
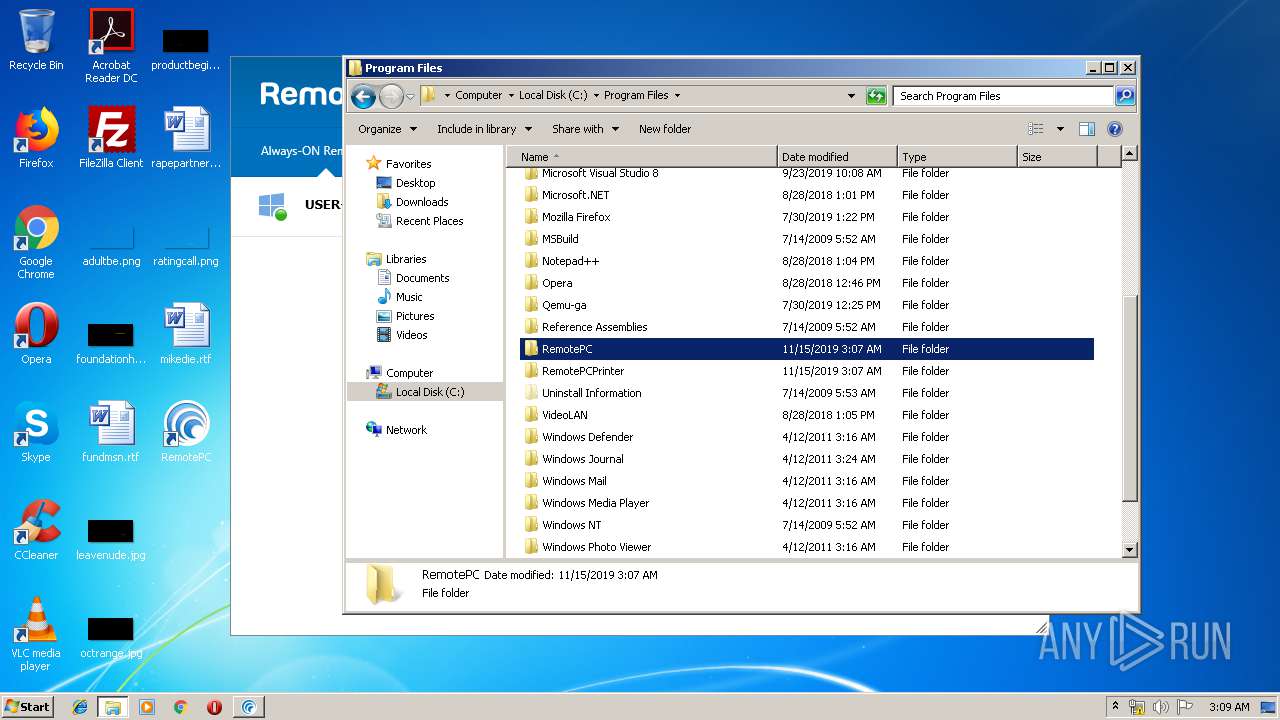
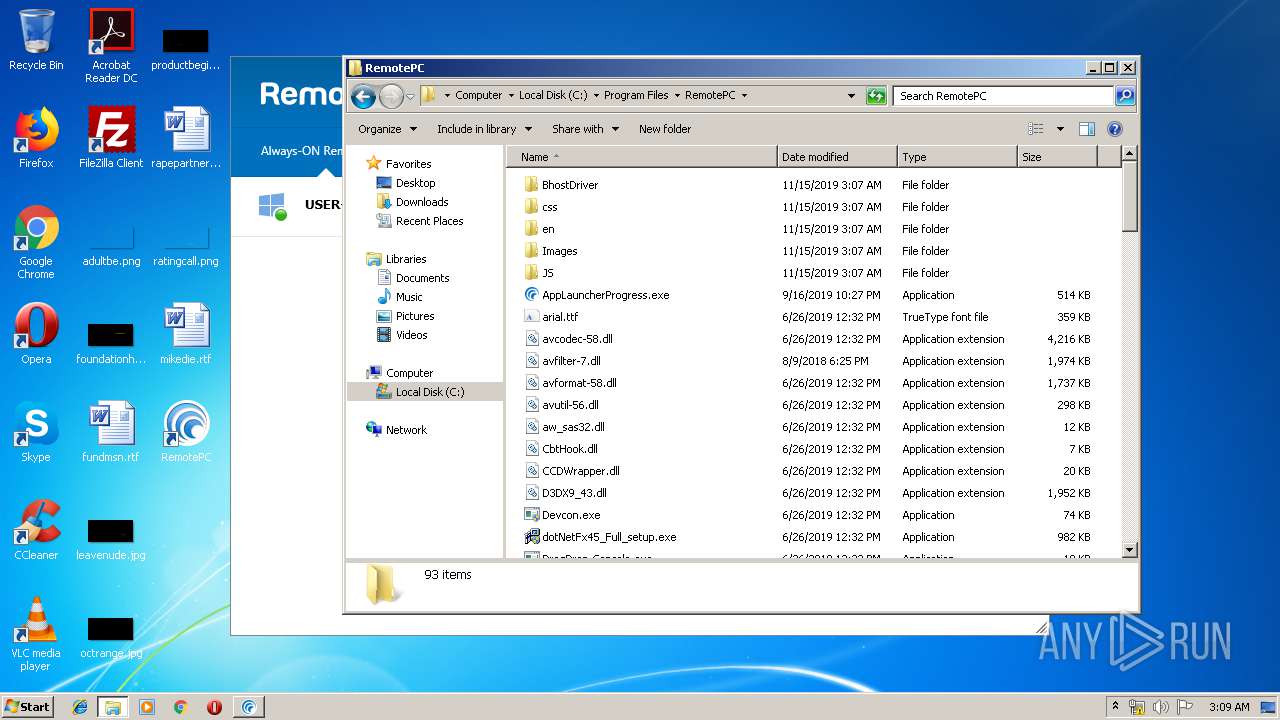
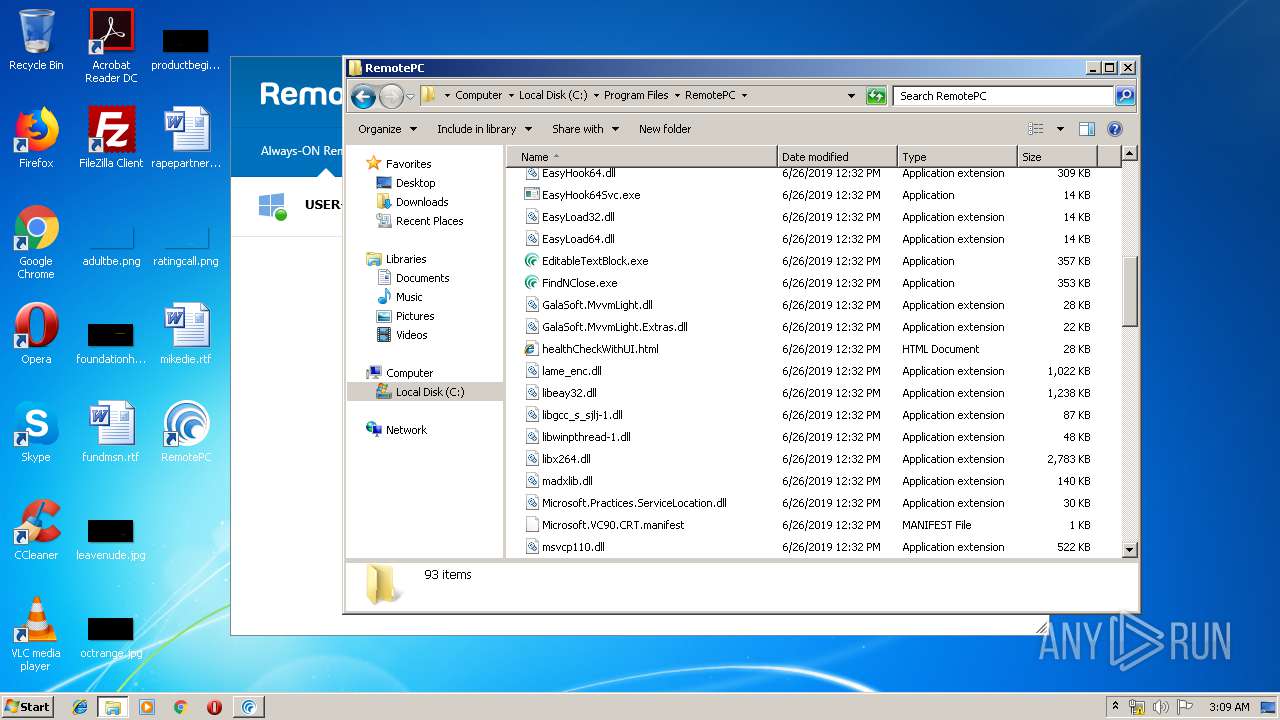
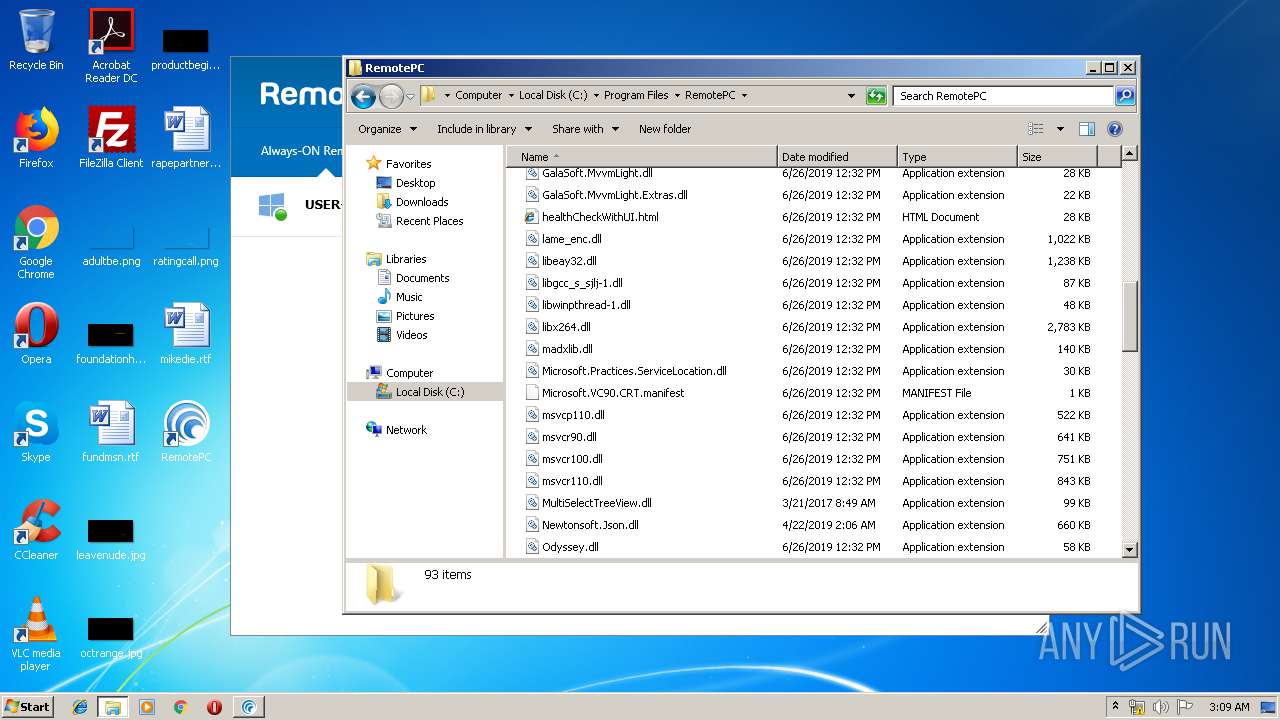
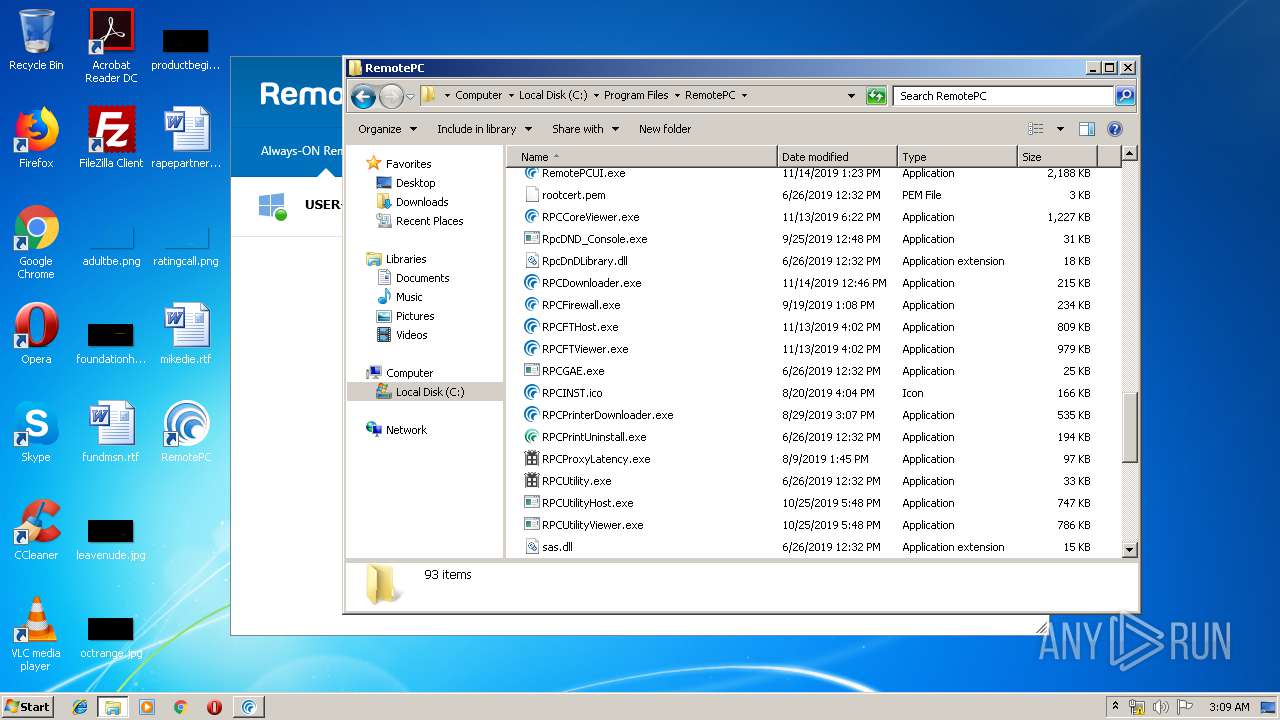
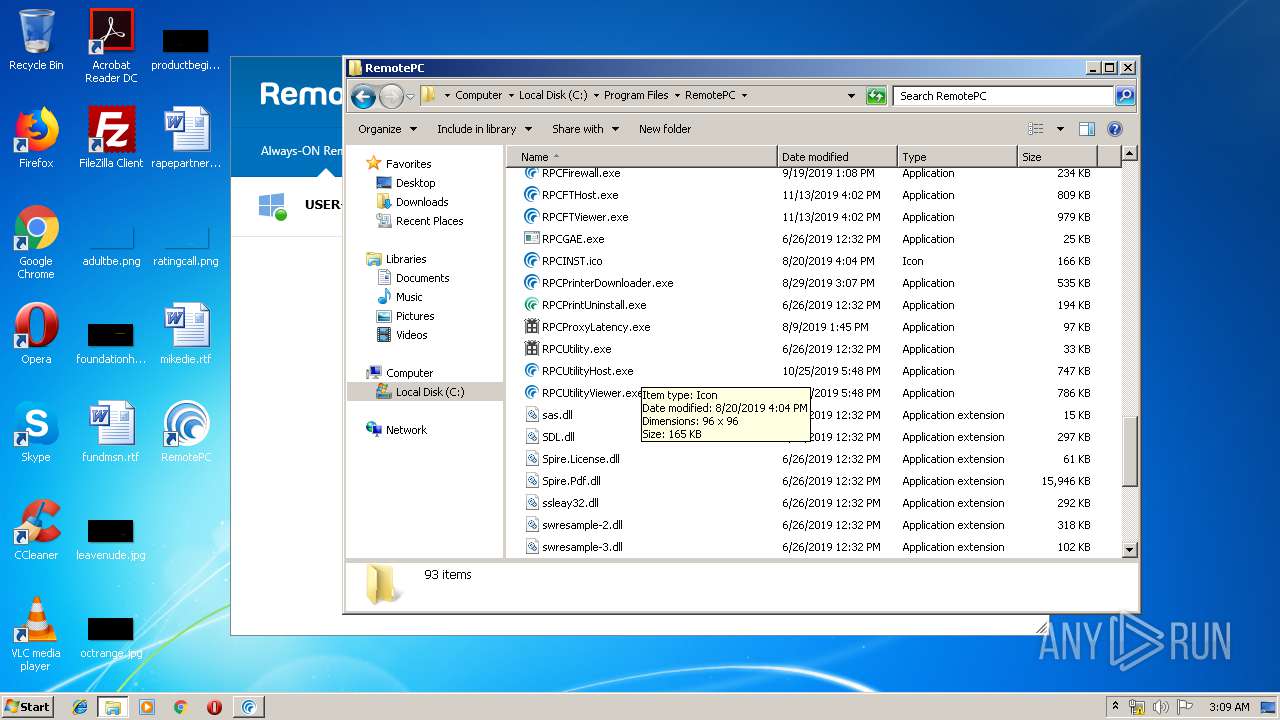
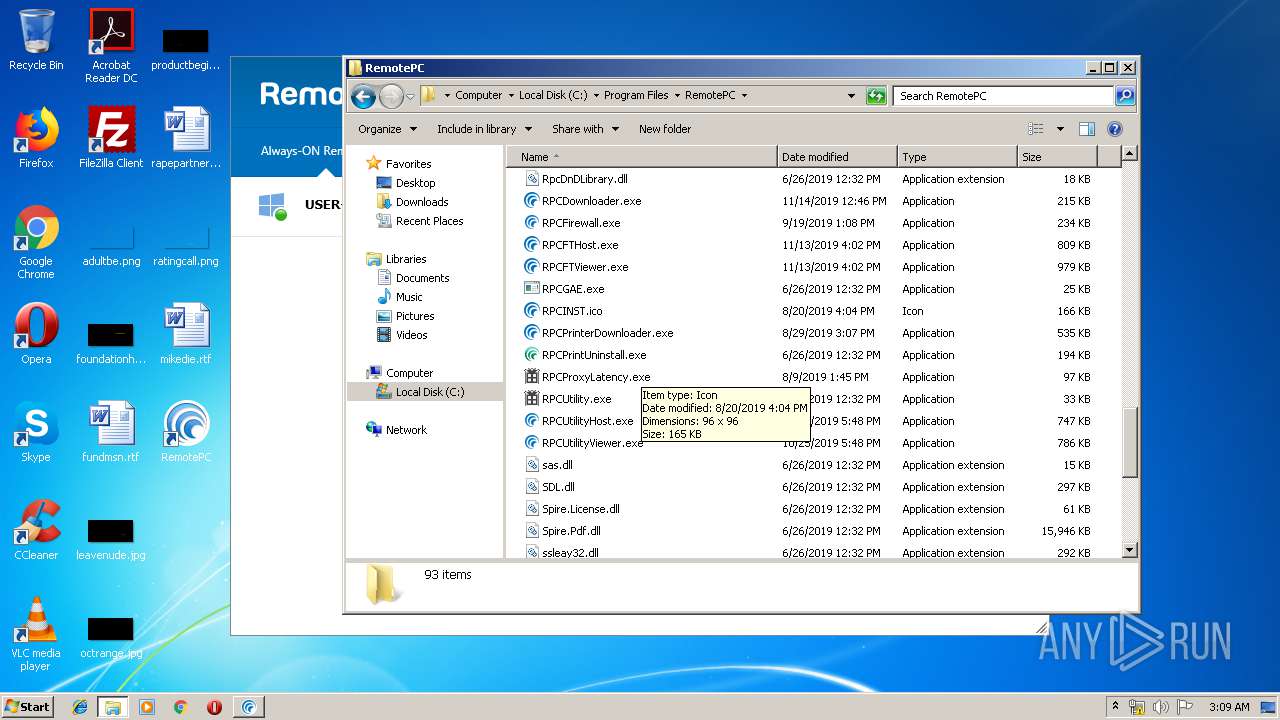
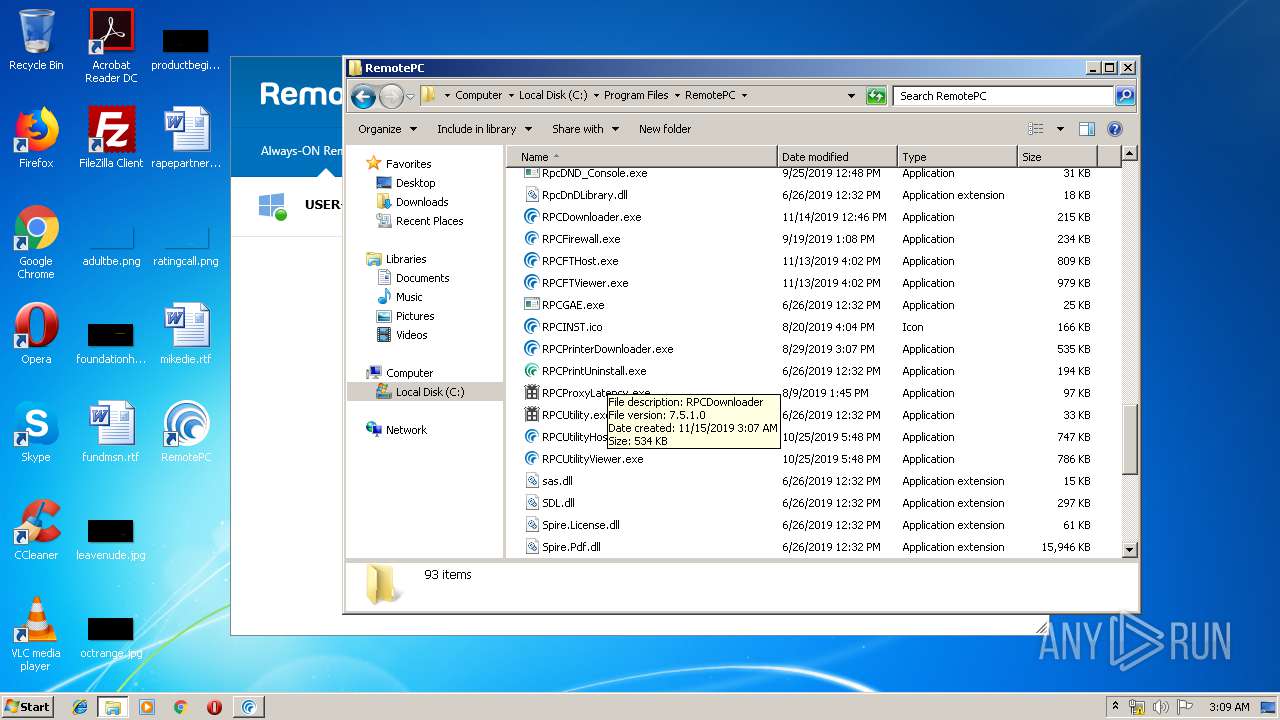
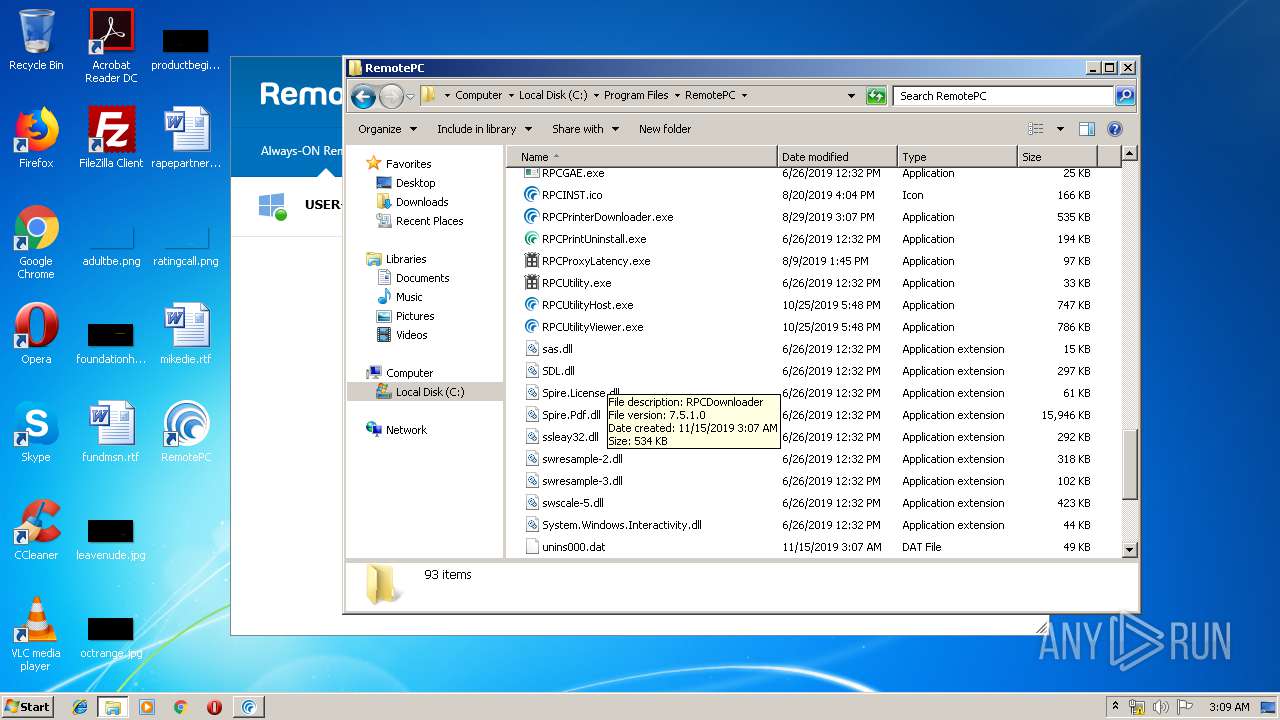
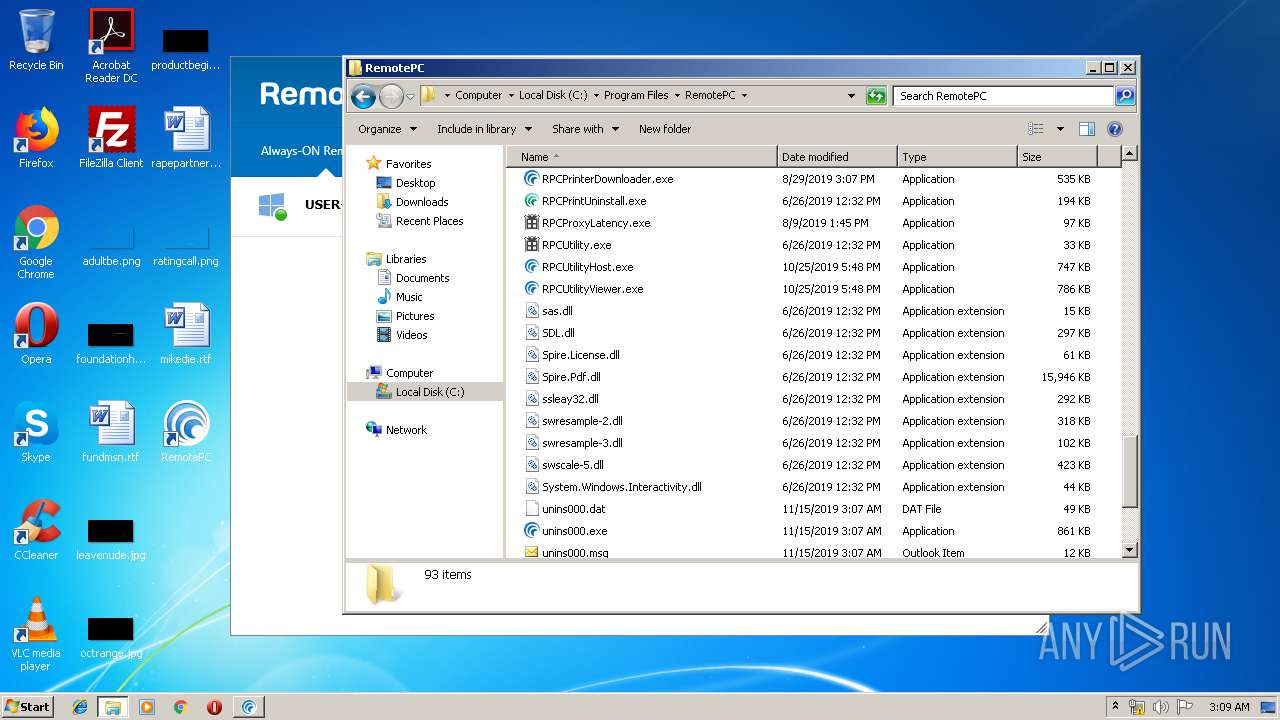
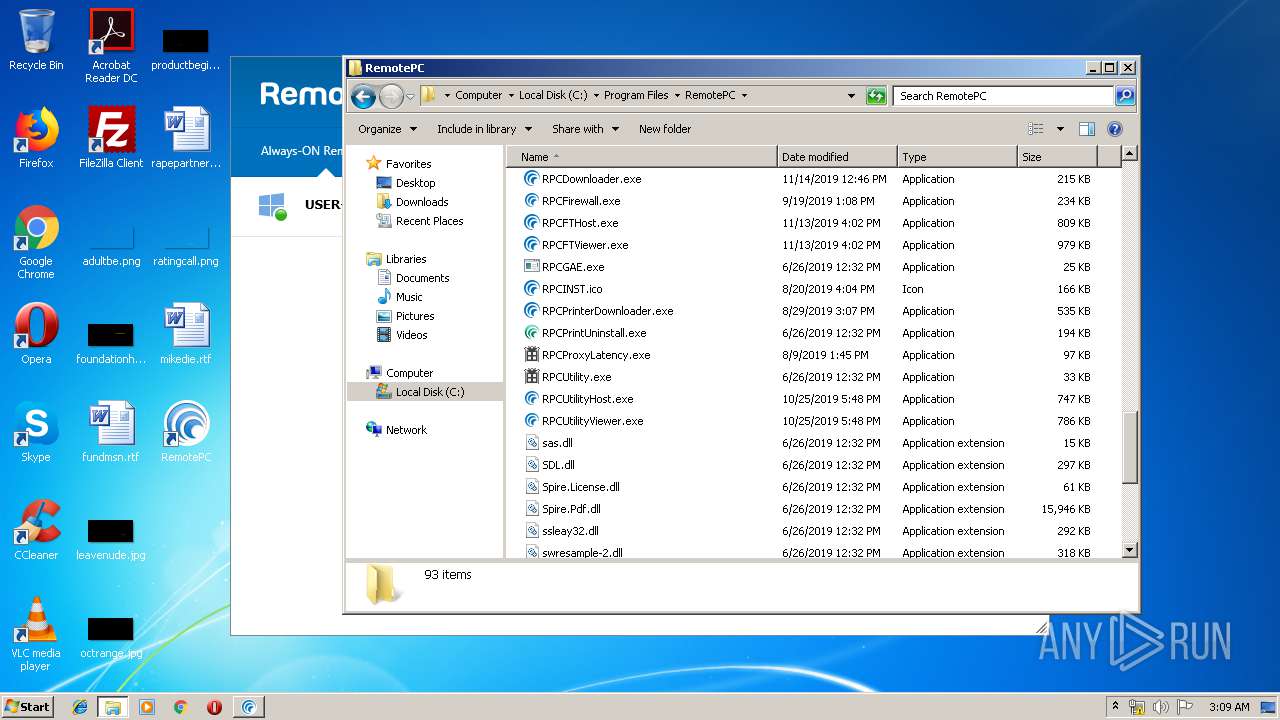
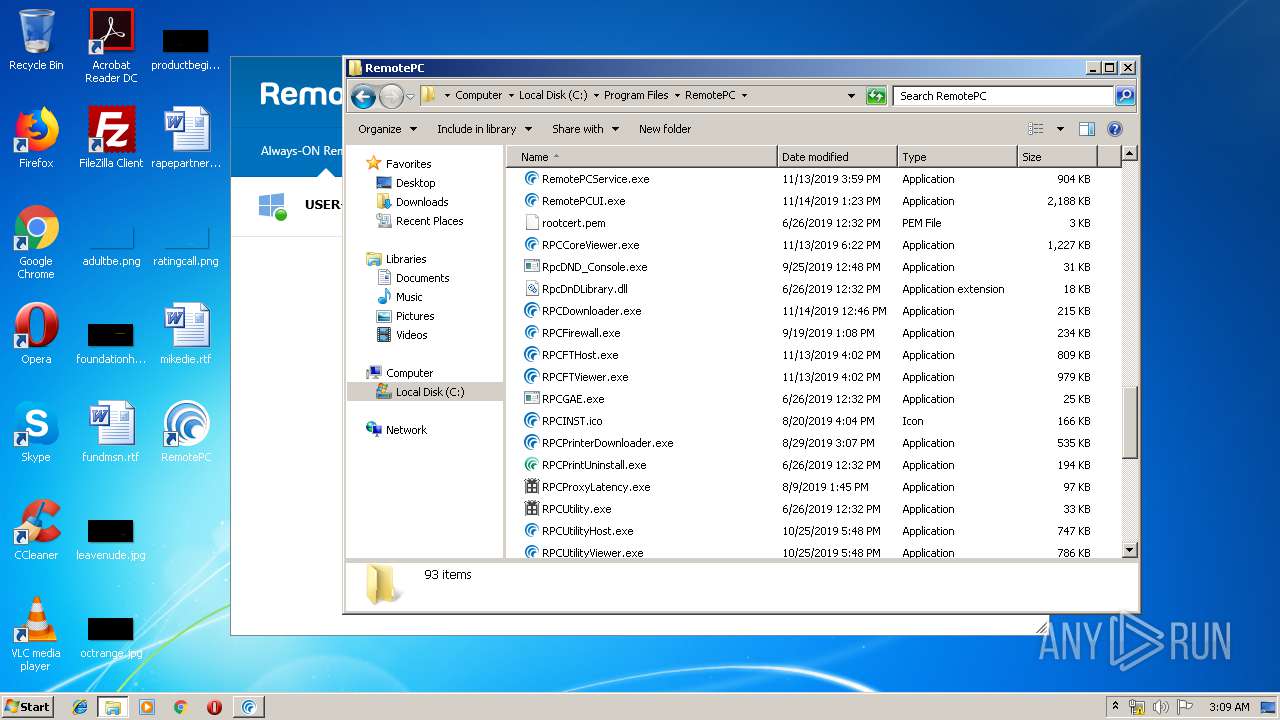
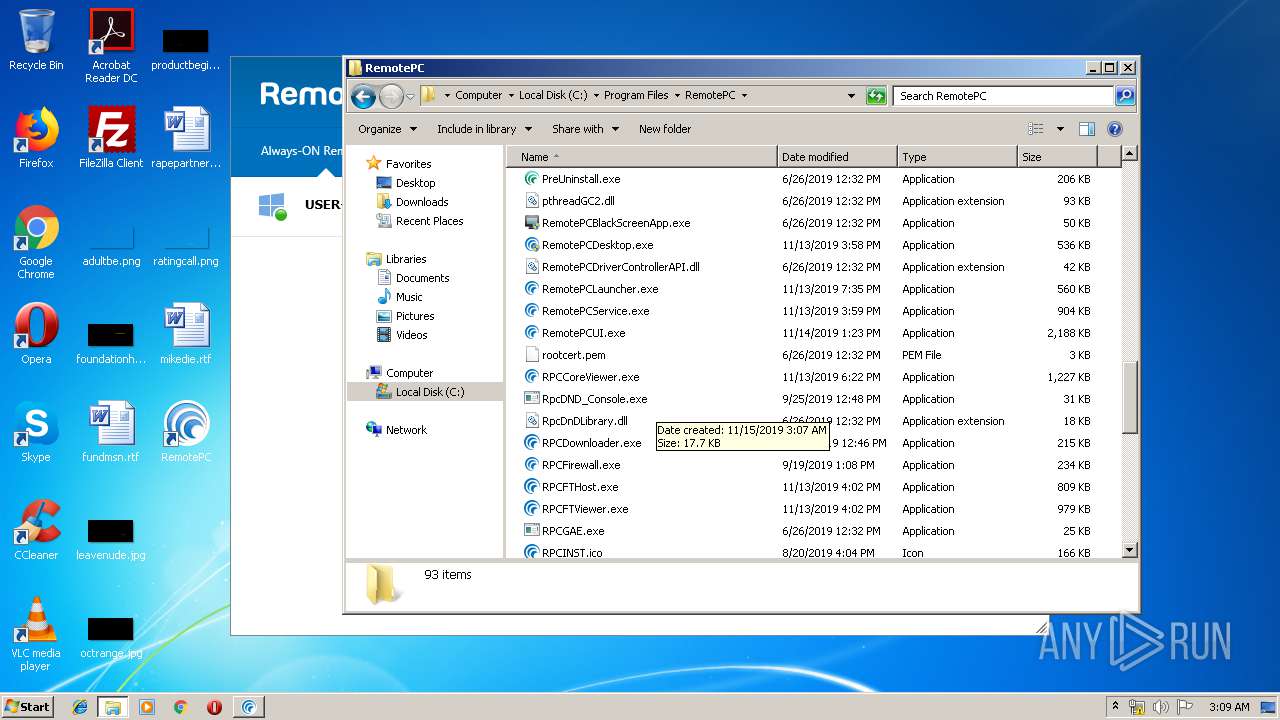
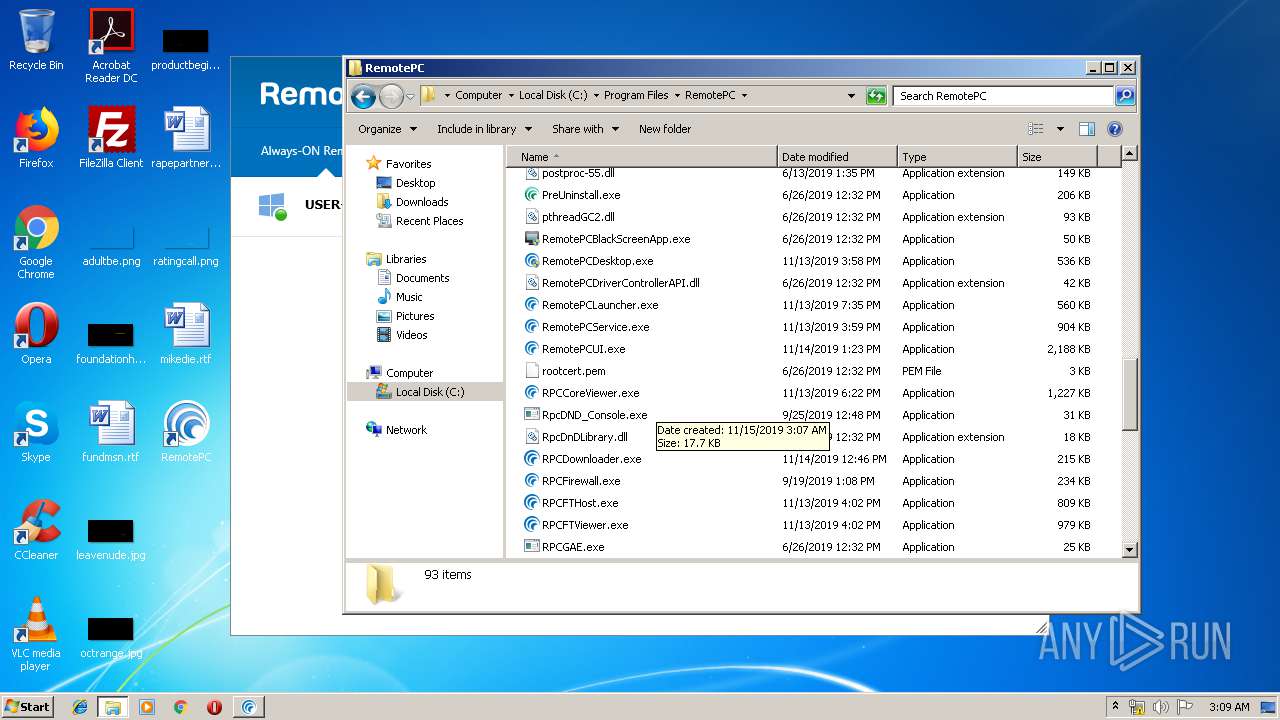
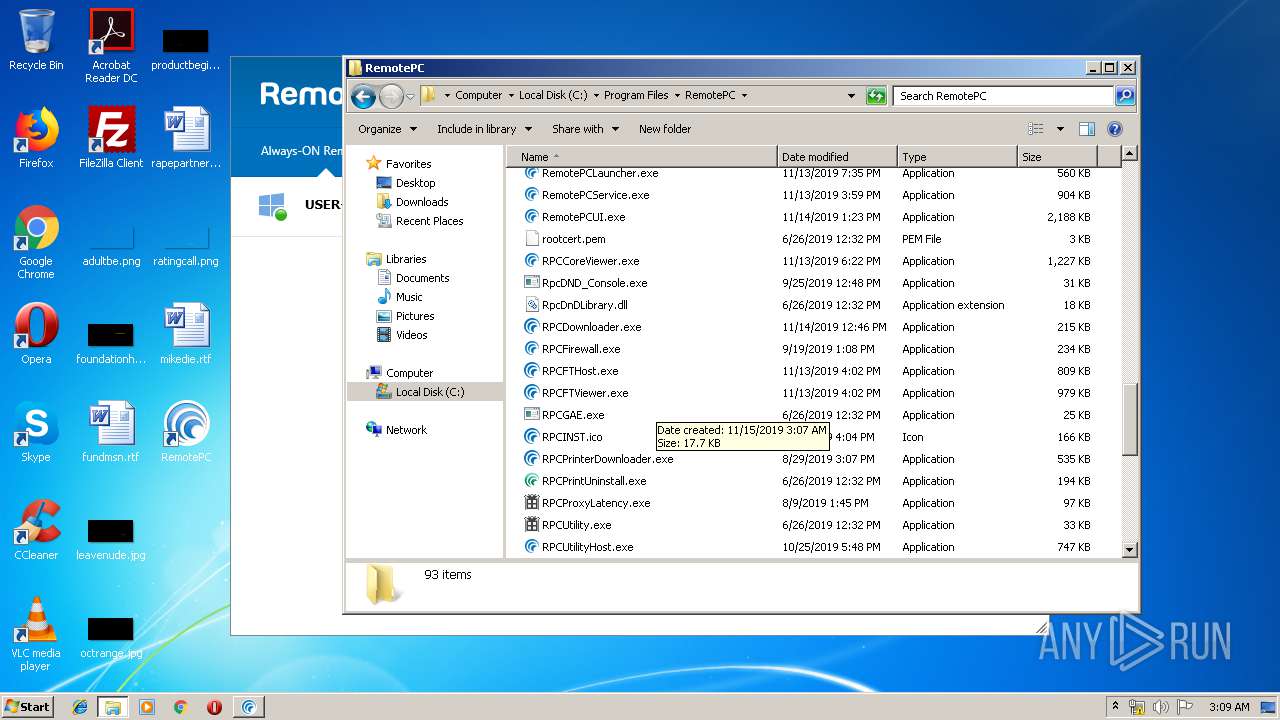
Creates files in the program directory
- RPCPrinterDownloader.exe (PID: 3980)
- RemotePCUI.exe (PID: 820)
- PreUninstall.exe (PID: 3788)
- RPCProxyLatency.exe (PID: 2004)
- RPCDownloader.exe (PID: 2304)
- RemotePCService.exe (PID: 2488)
Reads Environment values
- RPCPrinterDownloader.exe (PID: 3980)
- RemotePCUI.exe (PID: 820)
- RPCDownloader.exe (PID: 2304)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 2396)
Starts Microsoft Installer
- RPCPrinterDownloader.exe (PID: 3980)
Removes files from Windows directory
- spoolsv.exe (PID: 1204)
Starts CMD.EXE for commands execution
- RemotePCService.exe (PID: 2488)
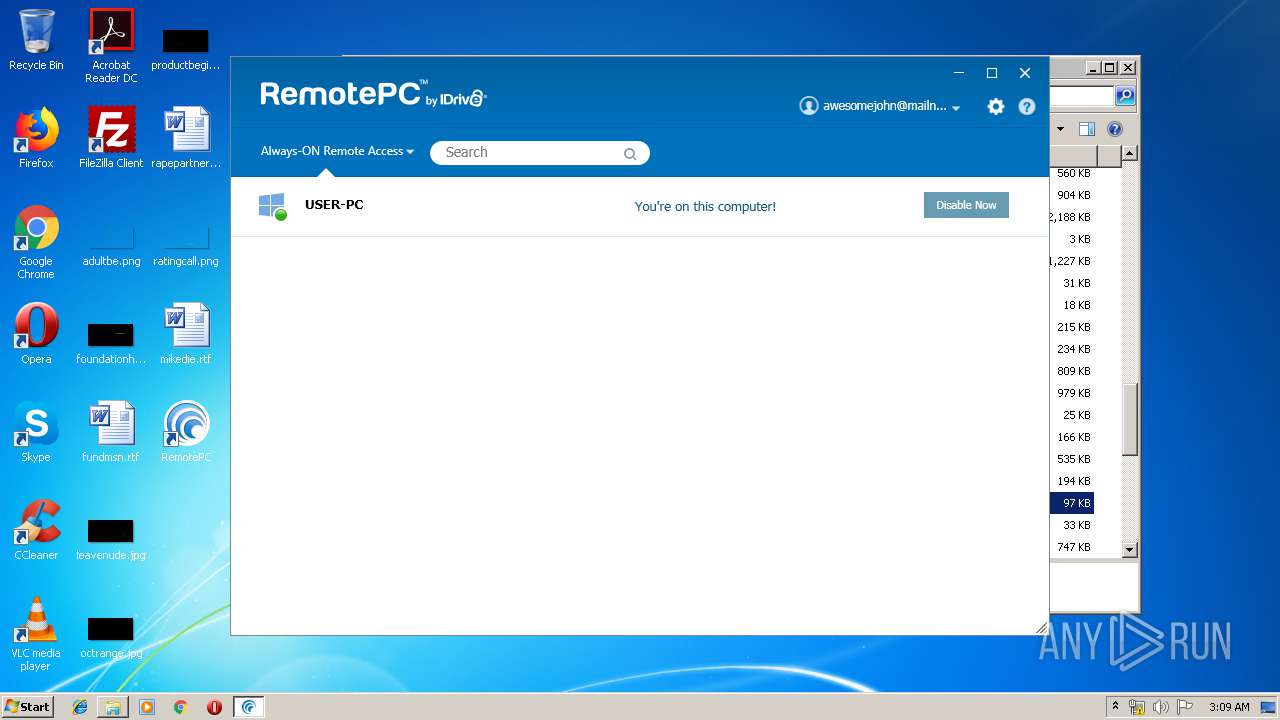
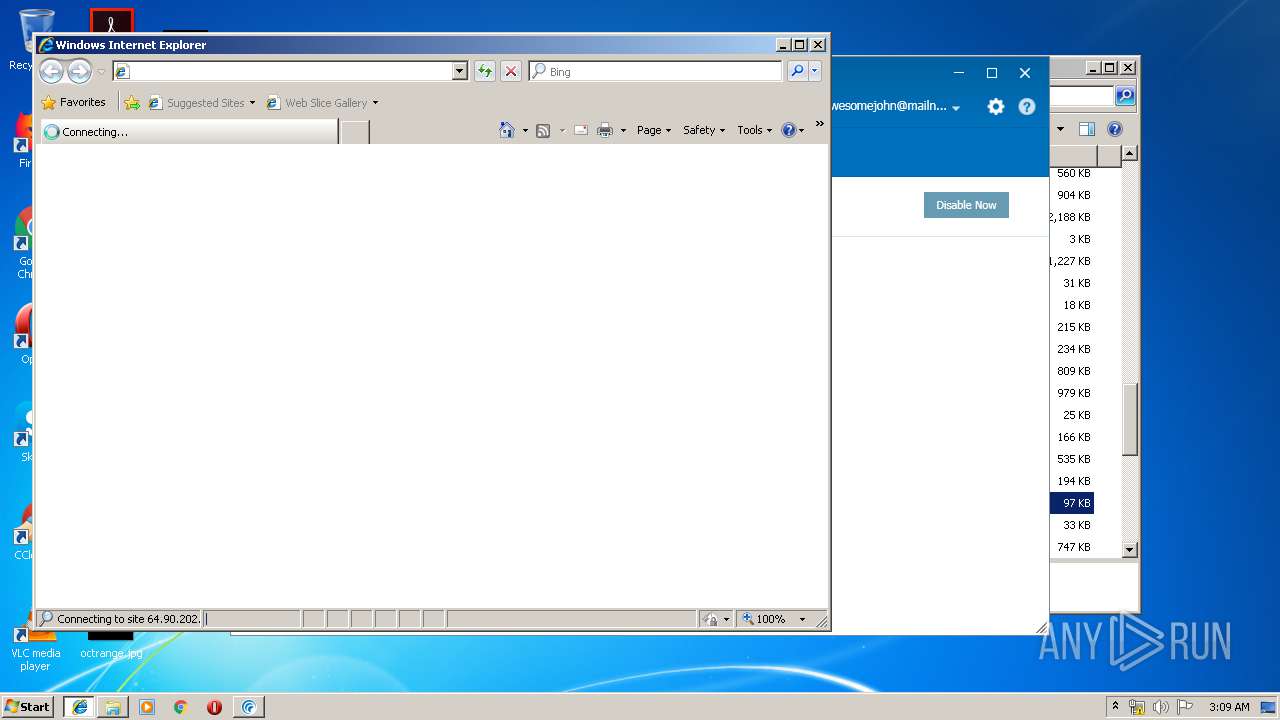
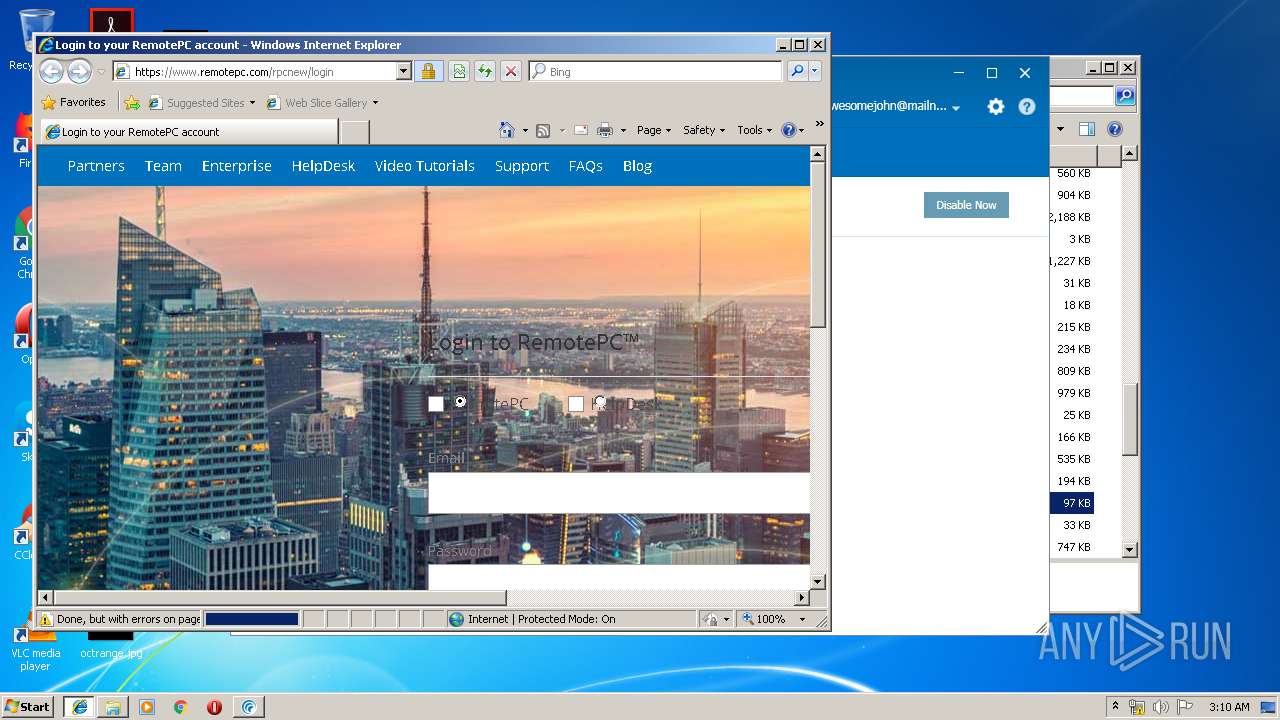
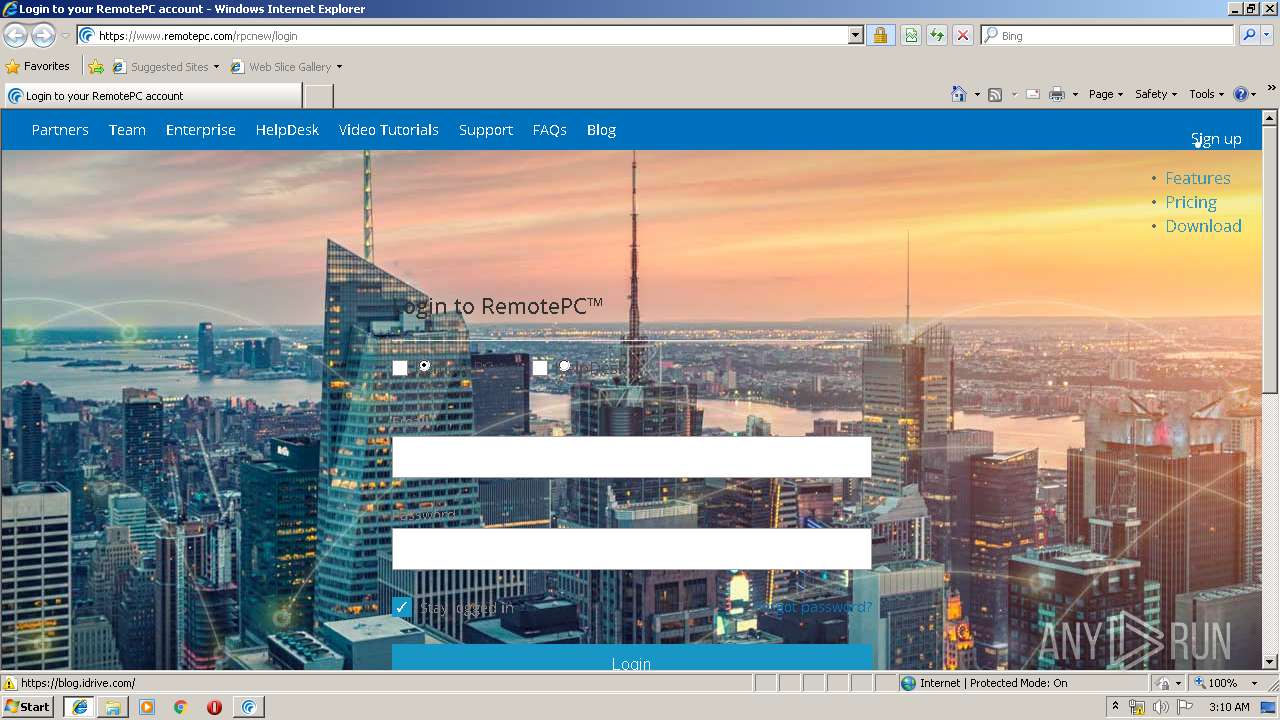
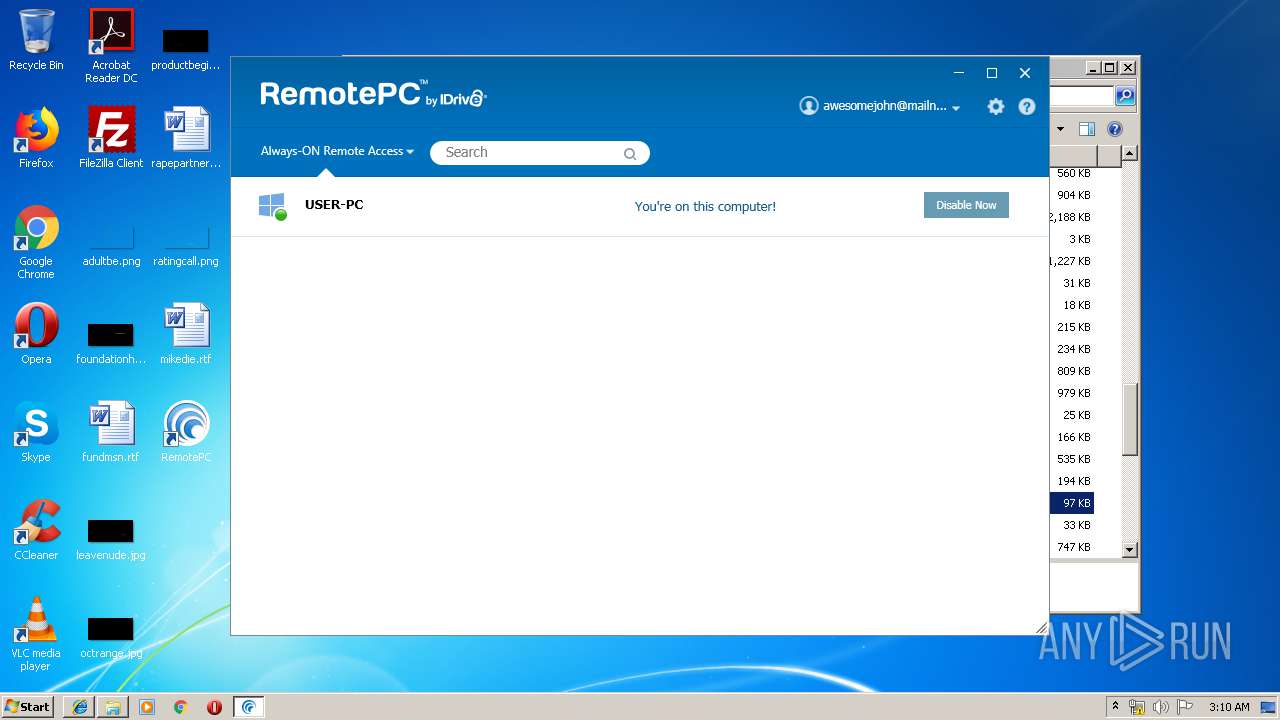
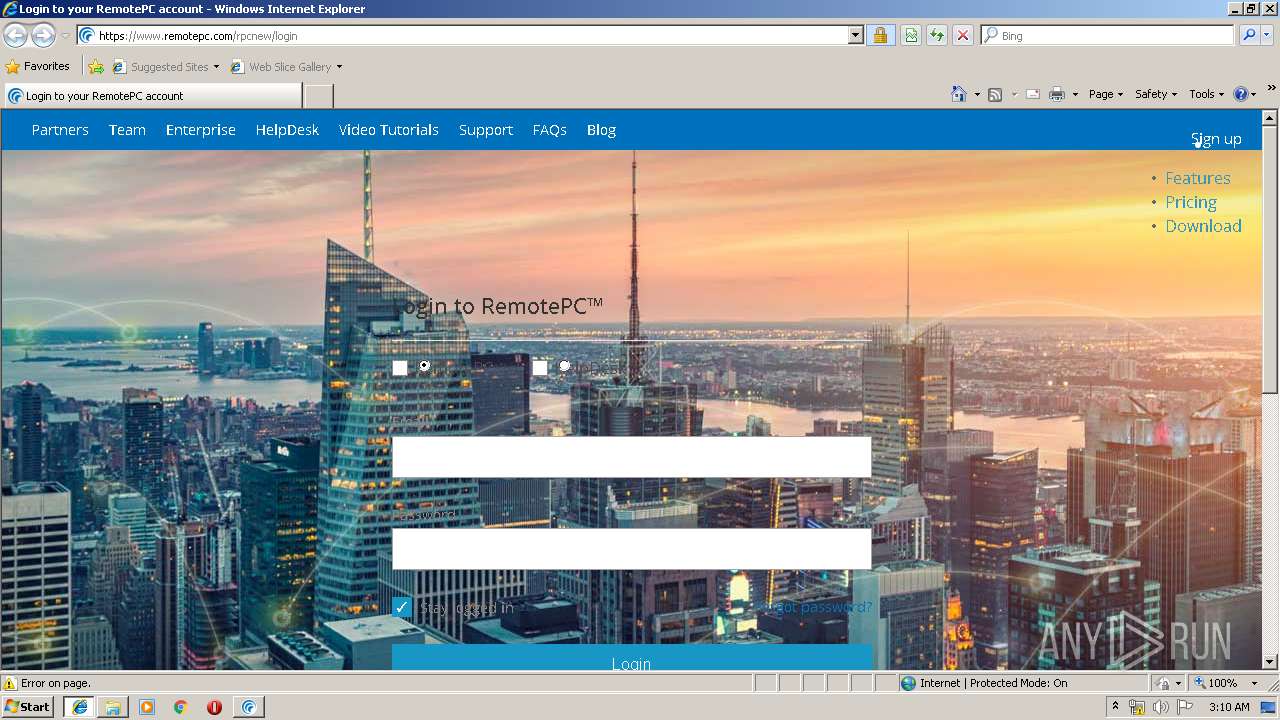
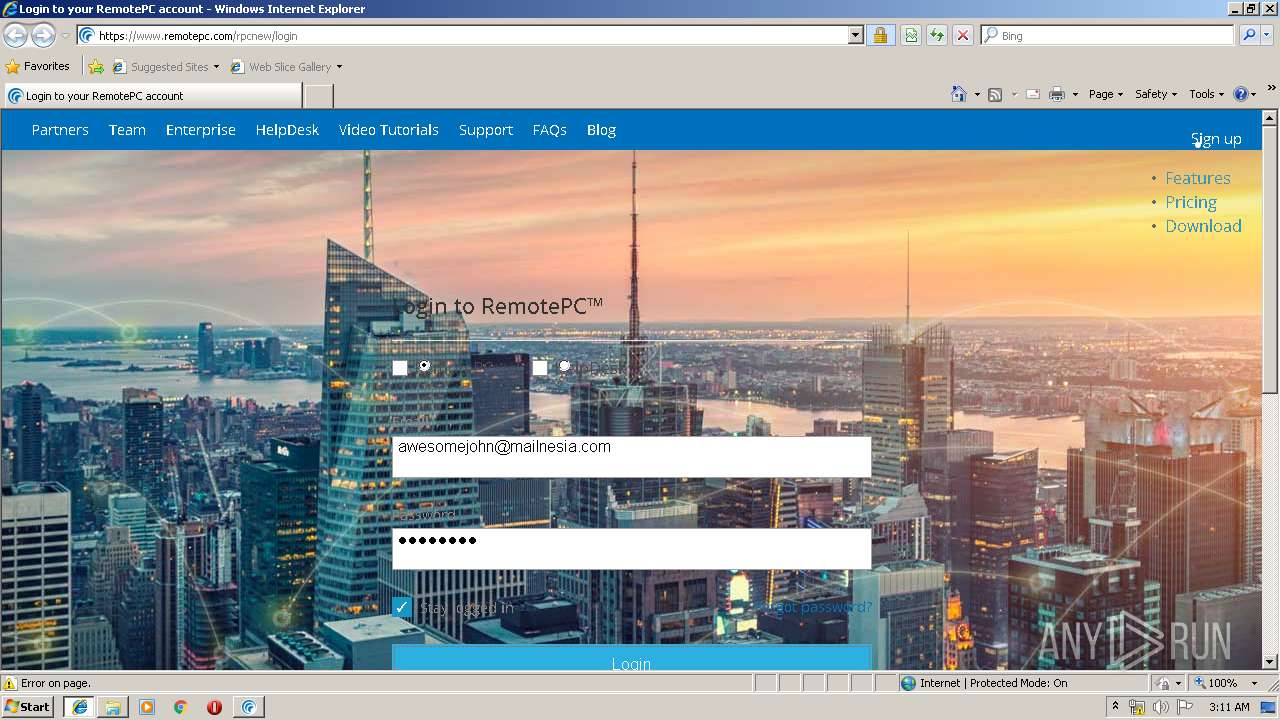
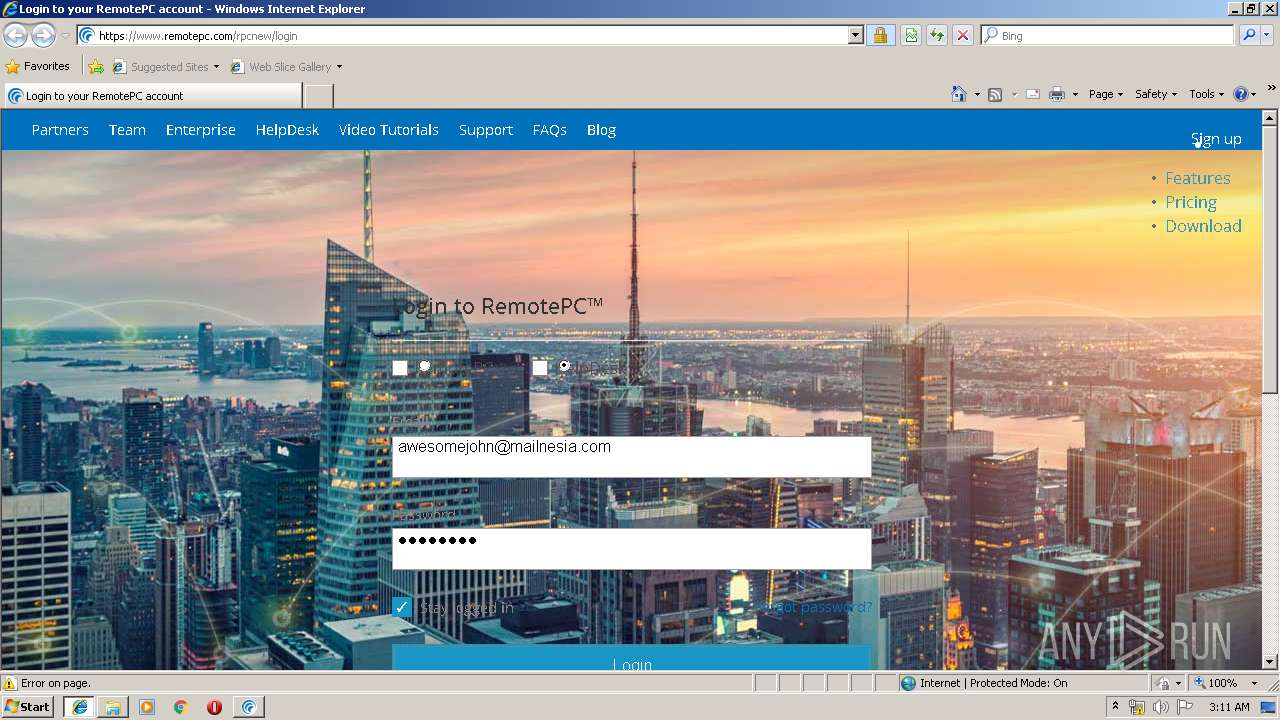
Starts Internet Explorer
- RemotePCUI.exe (PID: 820)
Reads default file associations for system extensions
- explorer.exe (PID: 352)
INFO
Application was dropped or rewritten from another process
- RemotePC.tmp (PID: 2232)
- RemotePC.tmp (PID: 1648)
- RemotePC1.tmp (PID: 892)
- RPCPrintUninstall.exe (PID: 3920)
- RemotePC1.exe (PID: 236)
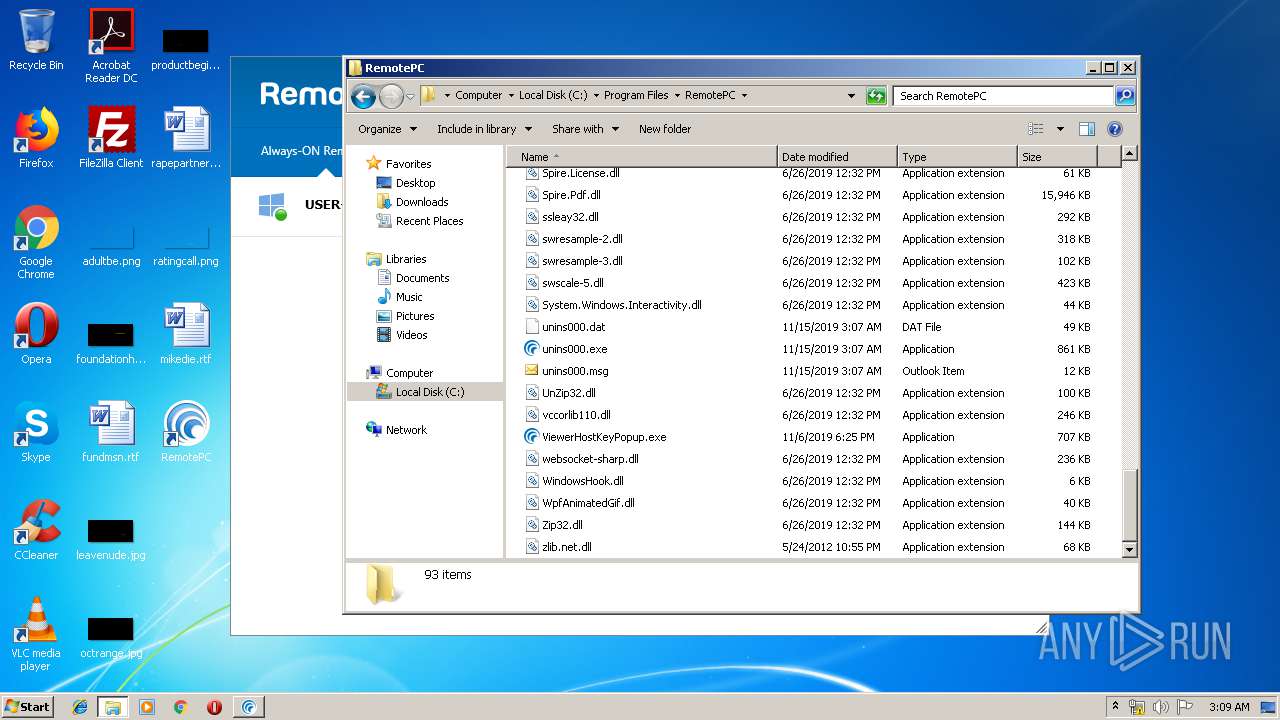
Creates a software uninstall entry
- RemotePC1.tmp (PID: 892)
- msiexec.exe (PID: 2276)
Loads dropped or rewritten executable
- RemotePC1.tmp (PID: 892)
- RemotePC.tmp (PID: 2232)
Reads settings of System Certificates
- RPCPrinterDownloader.exe (PID: 3980)
- RemotePCService.exe (PID: 2488)
- RPCDownloader.exe (PID: 2304)
- iexplore.exe (PID: 1400)
- RemotePCUI.exe (PID: 820)
Creates files in the program directory
- RPCPrintUninstall.exe (PID: 3920)
- msiexec.exe (PID: 2276)
- RemotePC1.tmp (PID: 892)
Dropped object may contain Bitcoin addresses
- RemotePC1.tmp (PID: 892)
Application launched itself
- msiexec.exe (PID: 2276)
Manual execution by user
- explorer.exe (PID: 2724)
Reads Internet Cache Settings
- iexplore.exe (PID: 3368)
Reads internet explorer settings
- iexplore.exe (PID: 3368)
Changes internet zones settings
- iexplore.exe (PID: 1400)
Creates files in the user directory
- iexplore.exe (PID: 3368)
- iexplore.exe (PID: 1400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (91.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (3.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 180224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.6.21.0 |
| ProductVersionNumber: | 7.6.21.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IDrive Software |
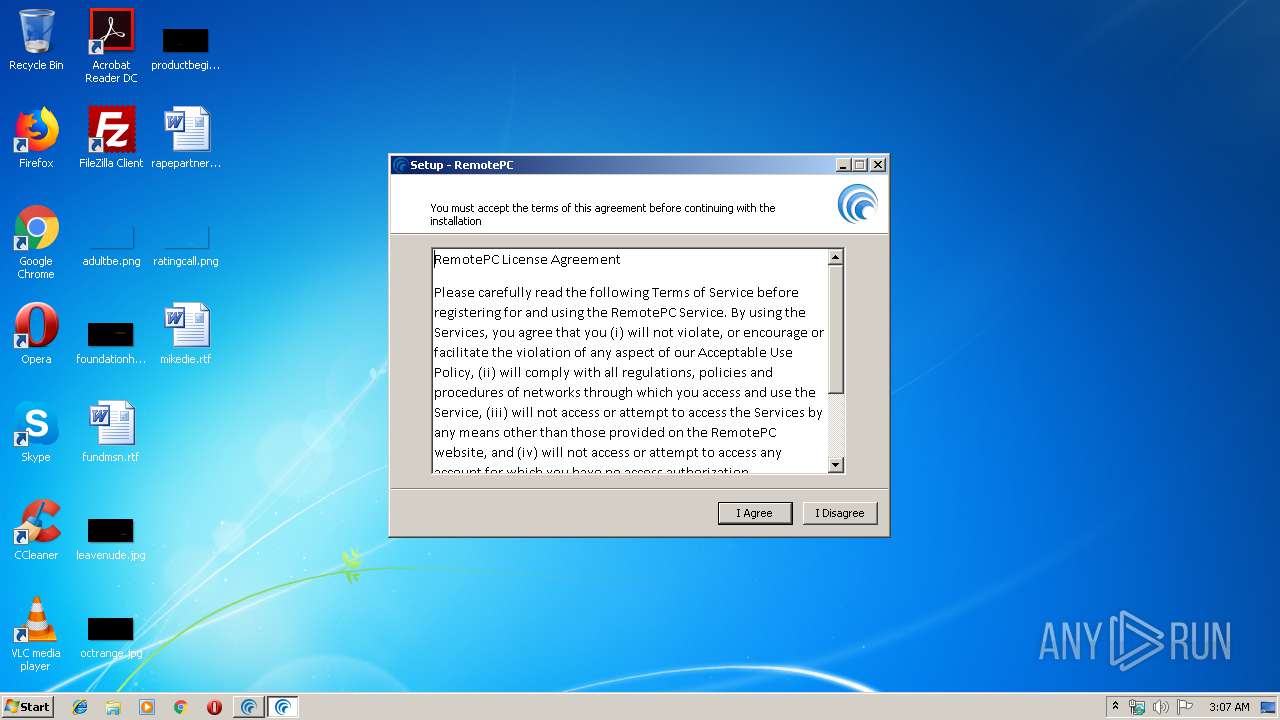
| FileDescription: | RemotePC Setup |
| FileVersion: | 7.6.21.0 |
| LegalCopyright: | |
| ProductName: | RemotePC |
| ProductVersion: | 7.6.21 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IDrive Software |
| FileDescription: | RemotePC Setup |
| FileVersion: | 7.6.21.0 |
| LegalCopyright: | - |
| ProductName: | RemotePC |
| ProductVersion: | 7.6.21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63177 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75182 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0002AE74 | 0x0002B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.73749 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.01588 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.50499 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.8704 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.46052 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.98277 | 39738 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.58876 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.59342 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.82583 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.88003 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
76
Monitored processes
31
Malicious processes
10
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\AppData\Local\Temp\is-VM019.tmp\RemotePC1.exe" /NORESTART | C:\Users\admin\AppData\Local\Temp\is-VM019.tmp\RemotePC1.exe | RemotePC.tmp | ||||||||||||
User: admin Company: IDrive Software Integrity Level: HIGH Description: RemotePC Setup Exit code: 0 Version: 7.6.21.0 Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | "C:\Windows\system32\sc.exe" start RPCService | C:\Windows\system32\sc.exe | — | RemotePC1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
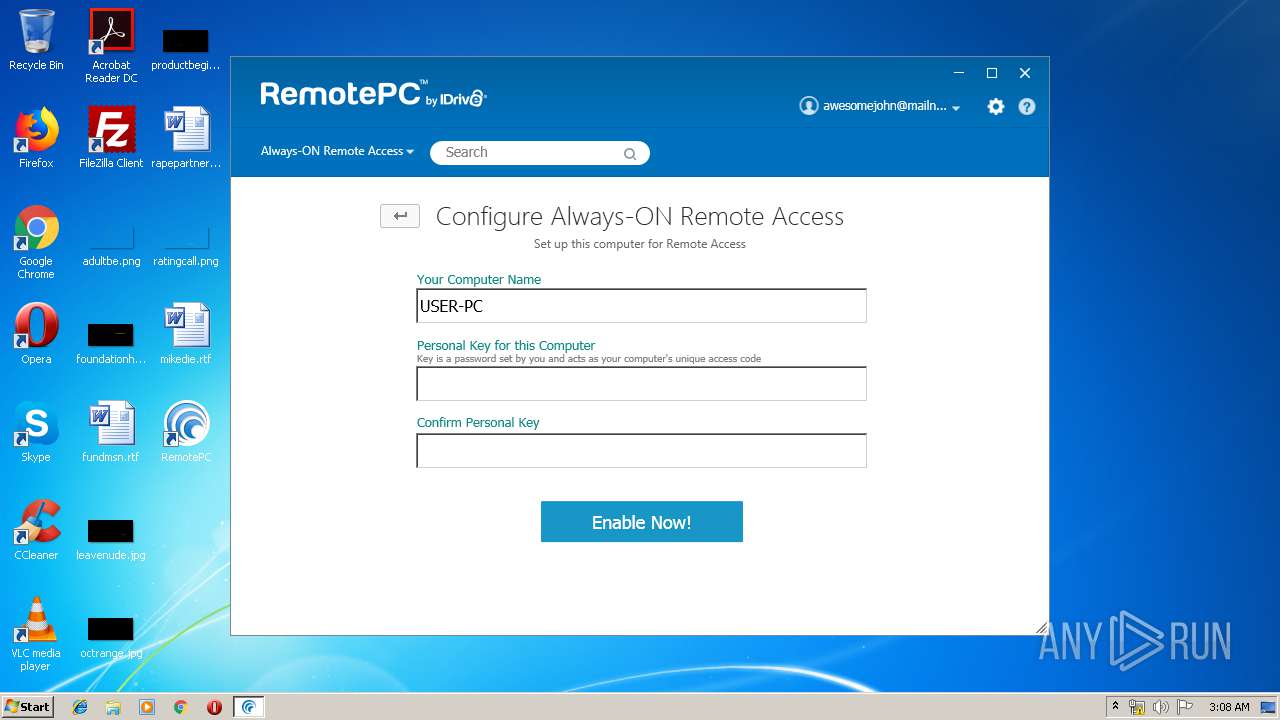
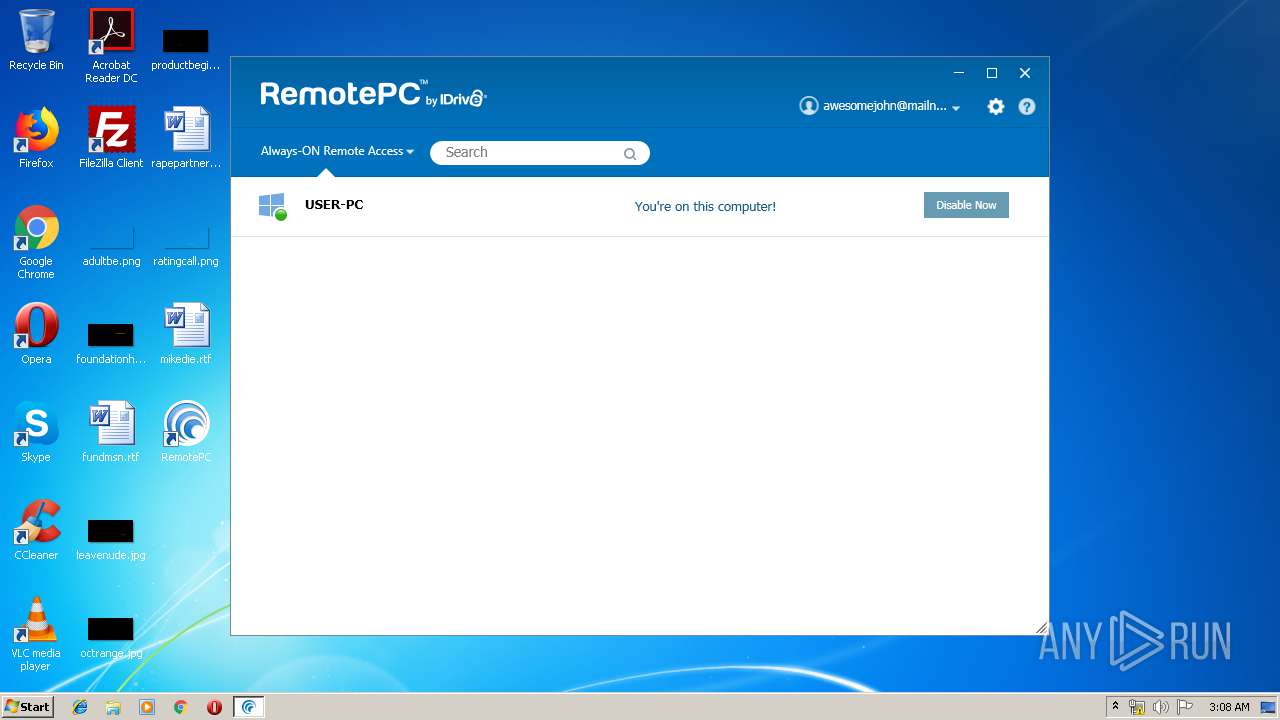
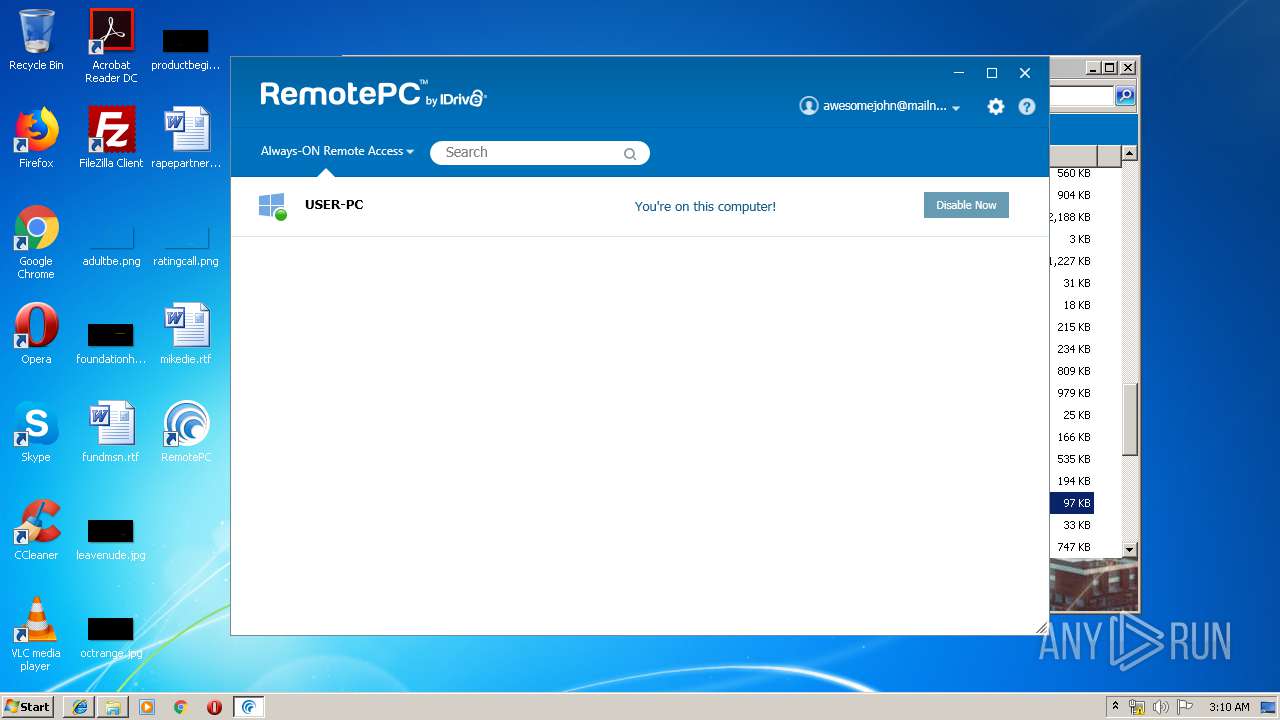
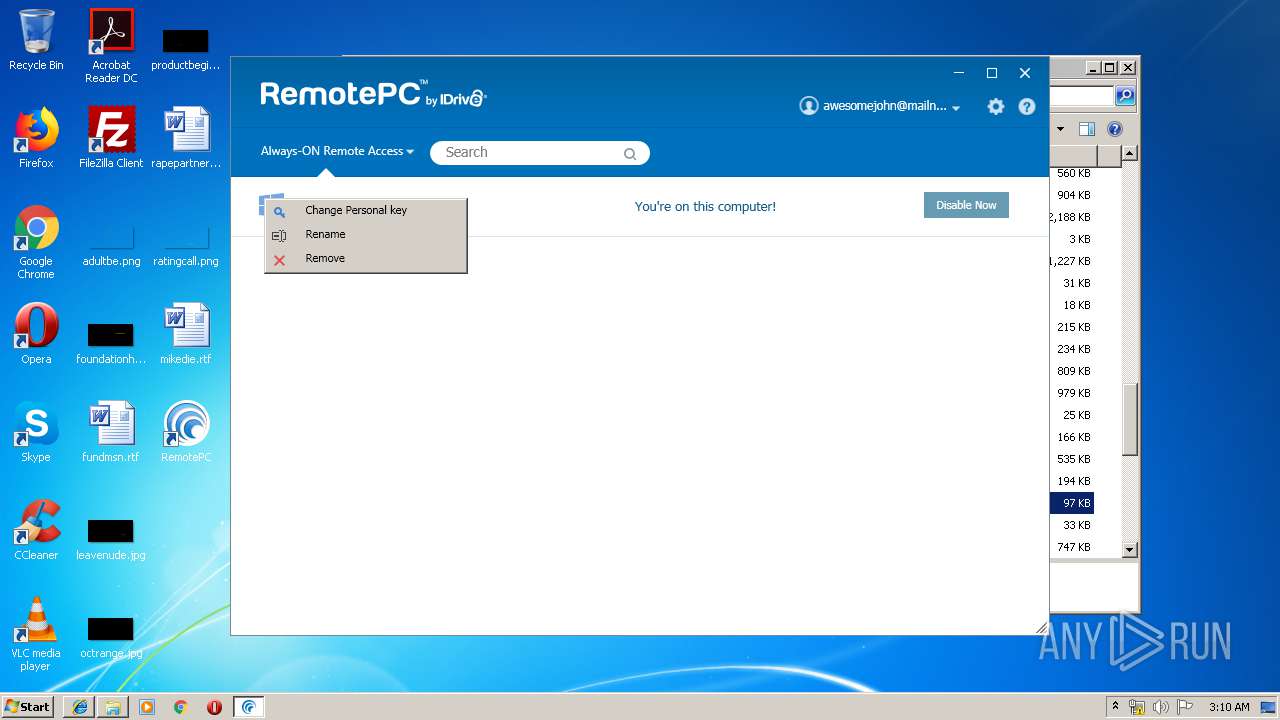
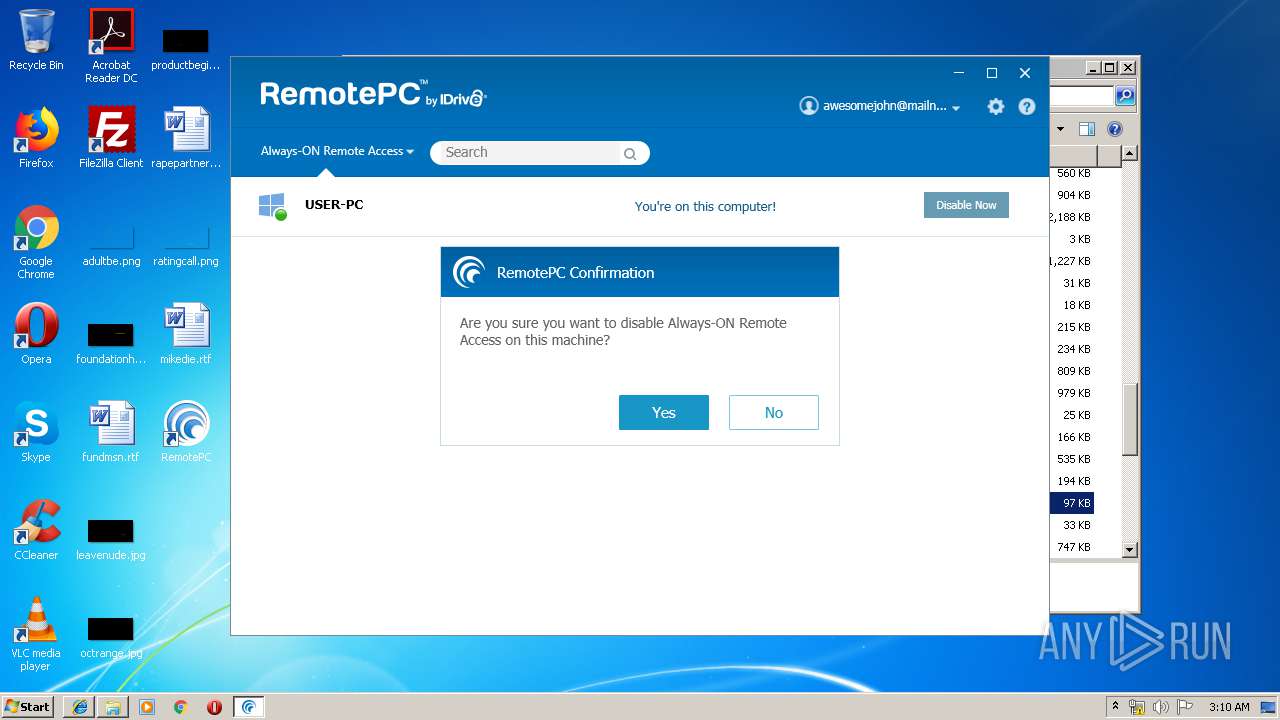
| 820 | "C:\Program Files\RemotePC\RemotePCUI.exe" | C:\Program Files\RemotePC\RemotePCUI.exe | RemotePCService.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RemotePCSuite Exit code: 0 Version: 7.5.5.0 Modules
| |||||||||||||||
| 892 | "C:\Users\admin\AppData\Local\Temp\is-7QERV.tmp\RemotePC1.tmp" /SL5="$3014C,24134993,221696,C:\Users\admin\AppData\Local\Temp\is-VM019.tmp\RemotePC1.exe" /NORESTART | C:\Users\admin\AppData\Local\Temp\is-7QERV.tmp\RemotePC1.tmp | RemotePC1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files\RemotePC\RPCFirewall.exe" | C:\Program Files\RemotePC\RPCFirewall.exe | — | RemotePC1.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1204 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\AppData\Local\Temp\RemotePC.exe" /SPAWNWND=$D011E /NOTIFYWND=$4012C | C:\Users\admin\AppData\Local\Temp\RemotePC.exe | RemotePC.tmp | ||||||||||||
User: admin Company: IDrive Software Integrity Level: HIGH Description: RemotePC Setup Exit code: 1 Version: 7.6.21.0 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | RemotePCUI.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | bcdedit /deletevalue safeboot | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 305
Read events
2 732
Write events
546
Delete events
27
Modification events
| (PID) Process: | (2232) RemotePC.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B808000088CF68C0619BD501 | |||
| (PID) Process: | (2232) RemotePC.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 896A0E3F0DC733496BF329AE4CC9C9518284587DD9B5C8D75FFC50E6A5C3FD06 | |||
| (PID) Process: | (2232) RemotePC.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 7C0300002EC7C8C2619BD501 | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 80EA6872024F25AC2C234A3972AB55A2F4B9993091C244CC6782C816BF726B5F | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\RemotePC\RPCFirewall.exe | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 188C0FEC70AD1485FDBBA907D4B39D060523B9FC18C321EC4711D47E2A189331 | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\RemotePC |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\RemotePC | |||
| (PID) Process: | (892) RemotePC1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\RemotePC |
| Operation: | write | Name: | AppDataPath |
Value: C:\ProgramData\RemotePC\ | |||
Executable files
113
Suspicious files
4
Text files
216
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-Q0U1H.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-TMN8H.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-HCTNP.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-IUG1D.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-P8D3L.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-9EEA8.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\is-CMBJF.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\BhostDriver\is-RUQAQ.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\BhostDriver\is-SUPDQ.tmp | — | |
MD5:— | SHA256:— | |||
| 892 | RemotePC1.tmp | C:\Program Files\RemotePC\BhostDriver\is-H1842.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2 345
DNS requests
226
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1400 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
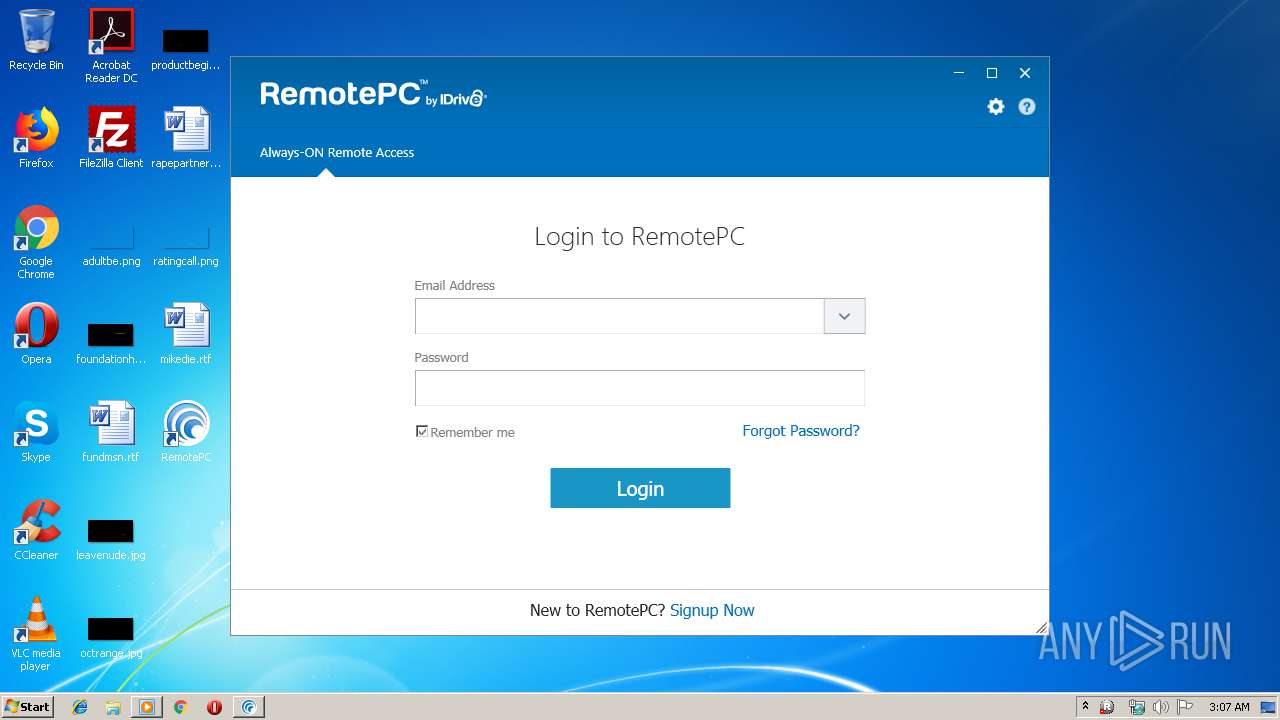
820 | RemotePCUI.exe | 64.90.202.5:443 | www1.remotepc.com | ViaWest | US | suspicious |
820 | RemotePCUI.exe | 64.90.202.6:443 | web1.remotepc.com | ViaWest | US | suspicious |
3980 | RPCPrinterDownloader.exe | 64.90.202.6:443 | web1.remotepc.com | ViaWest | US | suspicious |
820 | RemotePCUI.exe | 148.66.234.220:443 | broker16.remotepc.com | ViaWest | US | suspicious |
2488 | RemotePCService.exe | 64.90.202.6:443 | web1.remotepc.com | ViaWest | US | suspicious |
2488 | RemotePCService.exe | 148.66.234.220:443 | broker16.remotepc.com | ViaWest | US | suspicious |
2004 | RPCProxyLatency.exe | 173.242.23.165:80 | orangeburg.remotepc.com | Green House Data, Inc. | US | unknown |
2004 | RPCProxyLatency.exe | 64.90.202.5:443 | www1.remotepc.com | ViaWest | US | suspicious |
2004 | RPCProxyLatency.exe | 162.250.2.130:80 | miami.remotepc.com | ANEXIA Internetdienstleistungs GmbH | US | suspicious |
2004 | RPCProxyLatency.exe | 163.47.117.31:80 | adelaide.remotepc.com | — | AU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web1.remotepc.com |
| suspicious |
www.remotepc.com |
| suspicious |
www1.remotepc.com |
| suspicious |
broker16.remotepc.com |
| suspicious |
version.remotepc.com |
| suspicious |
california.remotepc.com |
| suspicious |
miami.remotepc.com |
| suspicious |
orangeburg.remotepc.com |
| unknown |
adelaide.remotepc.com |
| unknown |
guadalajara.remotepc.com |
| suspicious |
Threats
9 ETPRO signatures available at the full report
Process | Message |
|---|---|
spoolsv.exe | dll main |
spoolsv.exe | hello2 |
spoolsv.exe | InitializePrintMonitor2 |
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |
rundll32.exe | Port monitor successfully installed.
|
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |
rundll32.exe | Printer drivers copied or already exist.
|
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |
rundll32.exe | Redirection port added.
|
rundll32.exe | RemotePCPrinterCore Verbose: 16 : |