| File name: | dl.jalecdn.com |
| Full analysis: | https://app.any.run/tasks/939fa1a3-9324-4318-a3b6-1a70357060a9 |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2025, 09:12:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 9 sections |
| MD5: | 297941B7A2C5774E3D41FF8230A4AC33 |
| SHA1: | 9514F5A3FA49BDB5DFD93ABC47A6076391068DBB |
| SHA256: | 323F59C94DE8FE877E4255548502051F17789D5FD8F0FCD60E7DF5EE2B50DA44 |
| SSDEEP: | 786432:5WPLt9qb/nj1jMOxOBFHmhST4u/xdxrkj8XznOjD8qp:5WDtm/j1oKgFH140xdxrVznOjPp |
MALICIOUS
Executing a file with an untrusted certificate
- dl.jalecdn.com.exe (PID: 7004)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- dl.jalecdn.com.exe (PID: 7156)
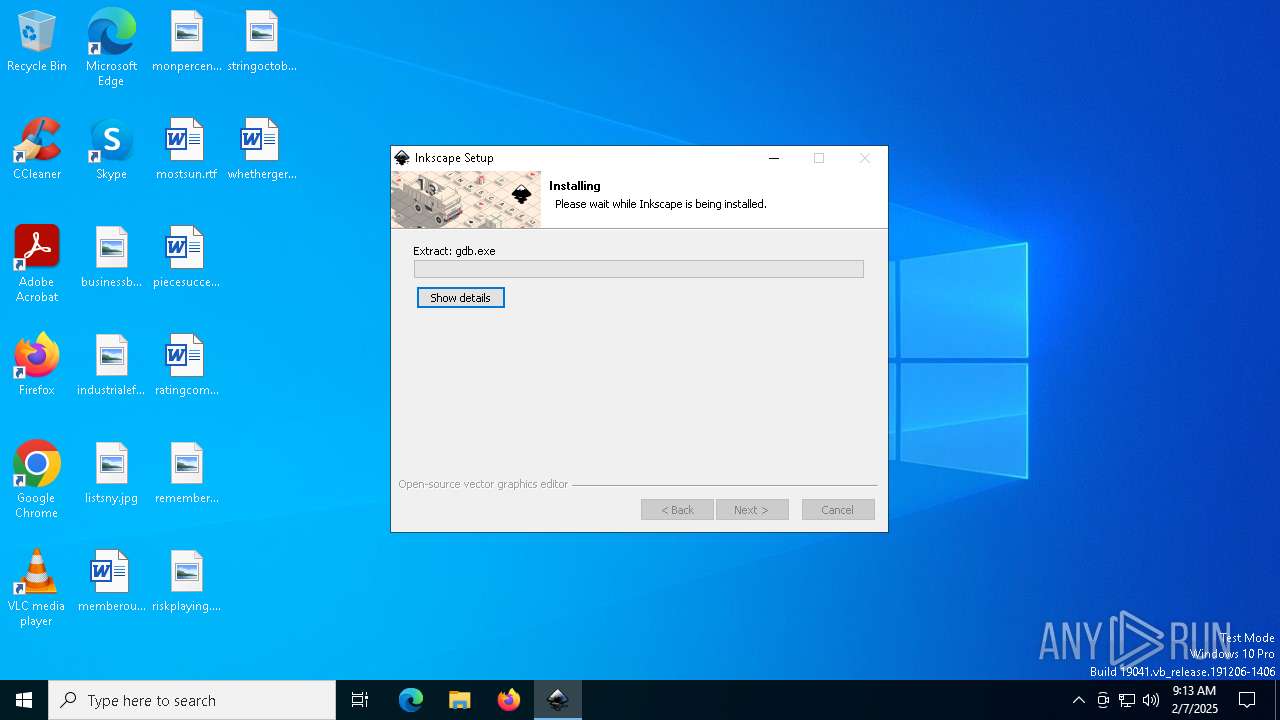
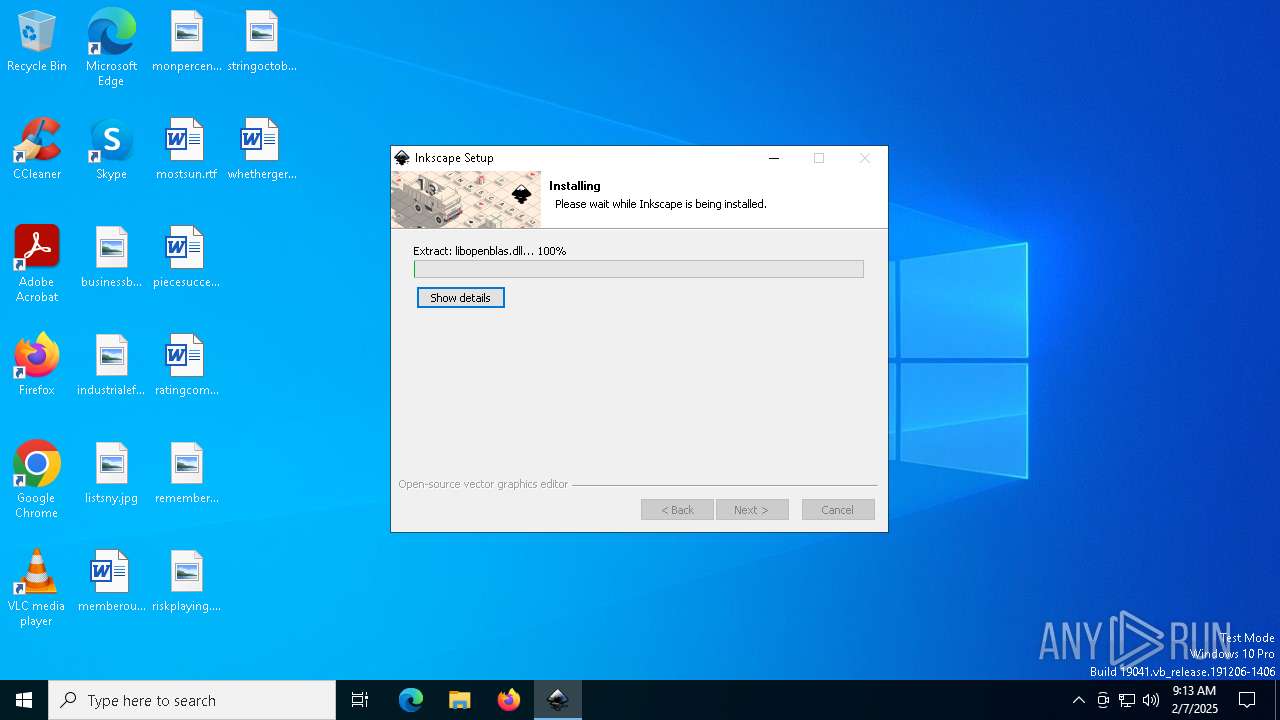
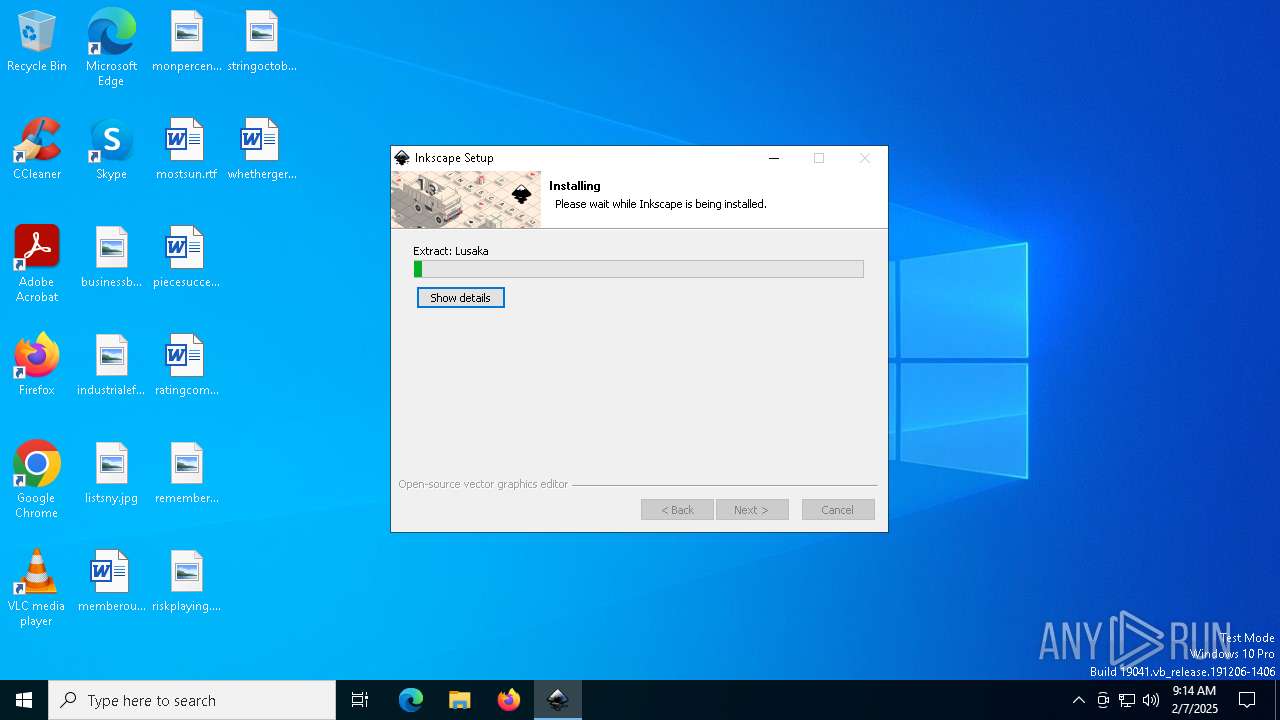
Executable content was dropped or overwritten
- dl.jalecdn.com.exe (PID: 7156)
INFO
Reads the computer name
- dl.jalecdn.com.exe (PID: 7156)
Checks supported languages
- dl.jalecdn.com.exe (PID: 7156)
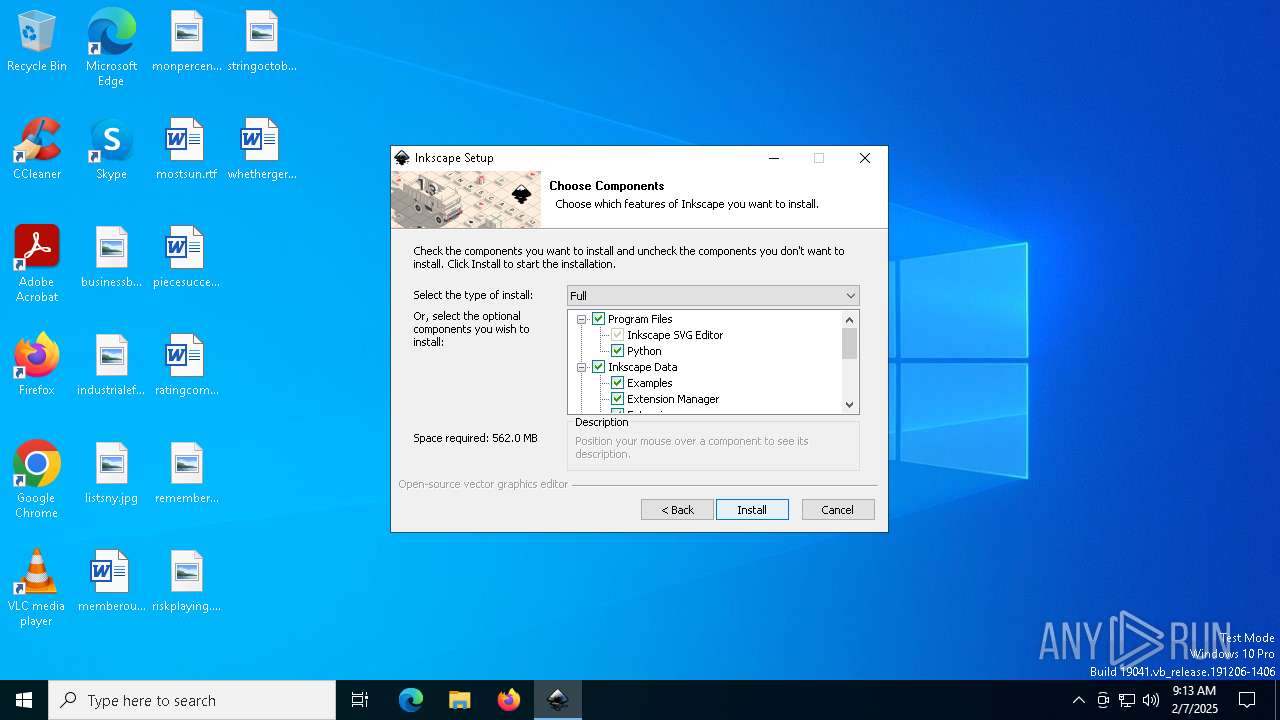
Creates files in the program directory
- dl.jalecdn.com.exe (PID: 7156)
Create files in a temporary directory
- dl.jalecdn.com.exe (PID: 7156)
The sample compiled with english language support
- dl.jalecdn.com.exe (PID: 7156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:07:14 21:03:59+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.4 |
| CodeSize: | 35840 |
| InitializedDataSize: | 72192 |
| UninitializedDataSize: | 402432 |
| EntryPoint: | 0x441d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
115
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7004 | "C:\Users\admin\Downloads\dl.jalecdn.com.exe" | C:\Users\admin\Downloads\dl.jalecdn.com.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7156 | "C:\Users\admin\Downloads\dl.jalecdn.com.exe" | C:\Users\admin\Downloads\dl.jalecdn.com.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
162
Read events
162
Write events
0
Delete events
0
Modification events
Executable files
153
Suspicious files
143
Text files
3 287
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7156 | dl.jalecdn.com.exe | C:\Users\admin\AppData\Local\Temp\nsgE6EA.tmp\ioSpecial.ini | text | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 7156 | dl.jalecdn.com.exe | C:\Users\admin\AppData\Local\Temp\nsgE6EA.tmp\UserInfo.dll | executable | |
MD5:7A5F8A22671AF594A1084D3EBEA9AC1D | SHA256:62A37D6464040C66EE207479C1648697C730D5AB391A918D808669FCC899A6AB | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\Run Inkscape with GTK Inspector.bat | text | |
MD5:449E75B2079CFC103A39D35943115AEF | SHA256:8EF4D3C7DD76CEE17241172AE8A77F458A9FD25DD65C2F57D5BCE4EB132EBF68 | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\bin\gdb.exe | executable | |
MD5:6431E8DA6AB0BF1433CFCABA3FA8FEF5 | SHA256:0C6005FB2C41641C13C9B1E3309364B4863306BE29505F48DC504938E4774533 | |||
| 7156 | dl.jalecdn.com.exe | C:\Users\admin\AppData\Local\Temp\nsgE6EA.tmp\InstallOptions.dll | executable | |
MD5:98974BB71EFC5EBCB4E66139E6CBC3CB | SHA256:CCB9F69A4D1578212E981FA2C5344CB8204A0CE0F85729AD3D0223B946B22092 | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\bin\gspawn-win64-helper.exe | executable | |
MD5:B34CB3CC414B61B40C66805A09AD9232 | SHA256:B8BA49037080E267392FCA59946A34D044ED03C840DF7CE58BC6B8C6B4027BCB | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\NEWS.md | text | |
MD5:51344D28FBB14049420472AD728B2CF1 | SHA256:EF7CB93C78F855426F68562A6CA9BAD87A8AA05232048608668E790C2FD18086 | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\Run Inkscape !.bat | text | |
MD5:CCC4E5DAC37E2533FF09023EBBD7A23B | SHA256:B6A8B3B2E6AF202CF96B58D1731517252A630BD6213A42C93D9D6836CA5474E0 | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\bin\gdb_create_backtrace.bat | text | |
MD5:D08A37292F29D0DF9BC5A3FACB28F2B4 | SHA256:4F1E765AF5C4A03E5F2FB5C7EA42BB5E061CBD929456217AB7C6CC320D12AAAD | |||
| 7156 | dl.jalecdn.com.exe | C:\Program Files\Inkscape\bin\imagequant.dll | executable | |
MD5:EAE88190F0326C097FFB3CCB6713B51C | SHA256:CDC3AD0C416137A9846FCCEF4F182E58A19405A297A9EC46937D9A9717B7F331 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
26
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3988 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | — | AKAMAI-AS | DE | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
1176 | svchost.exe | 20.190.159.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.69.42.241:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |