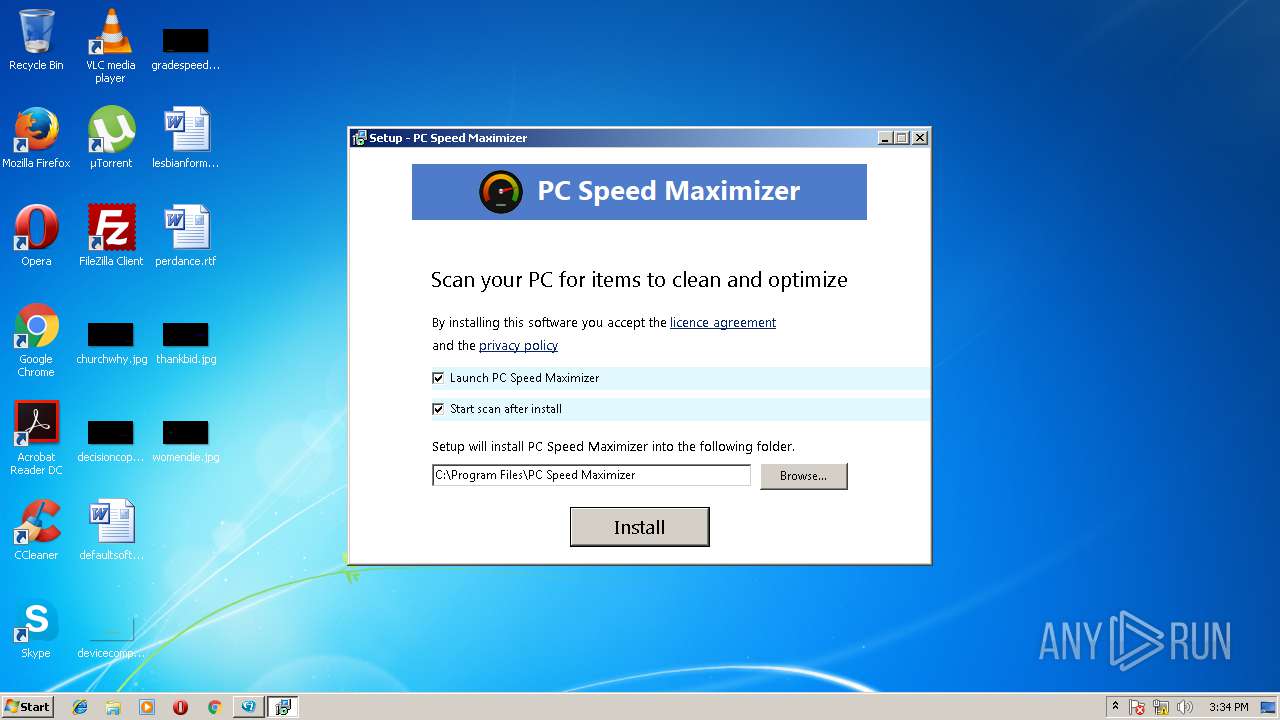
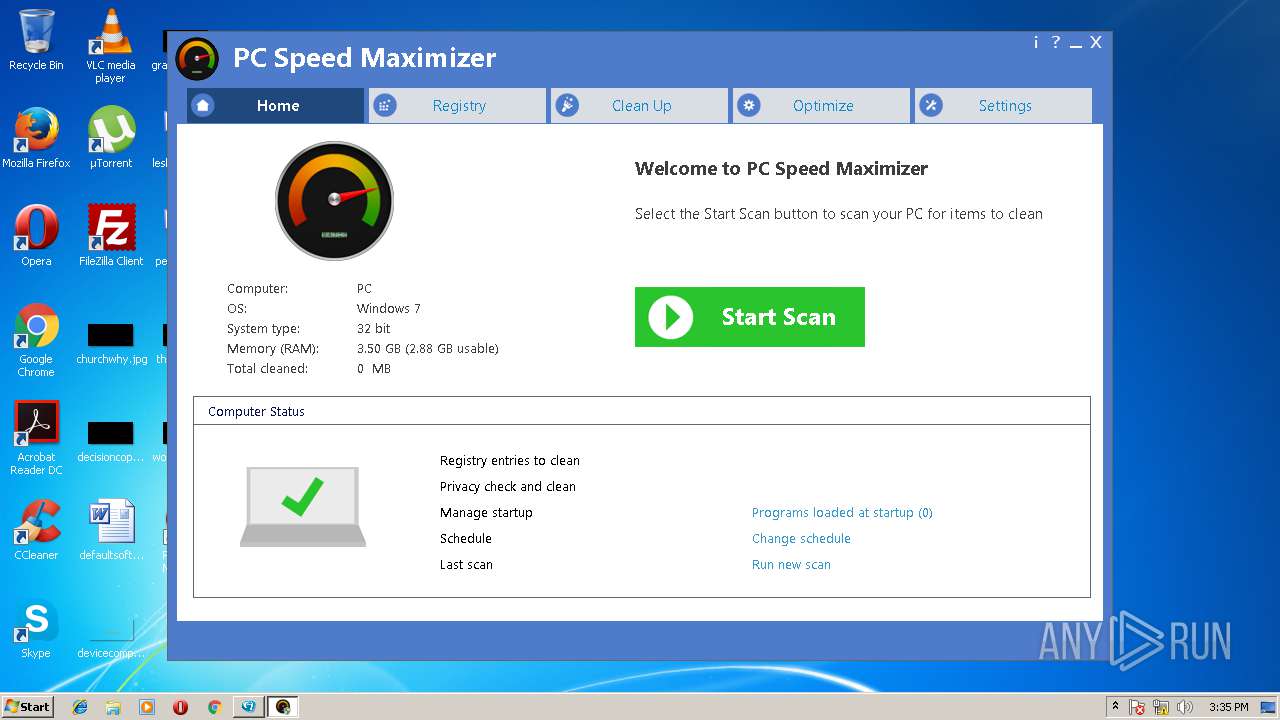
| download: | PC_Speed_Maximizer_5_CHIP_New.exe |
| Full analysis: | https://app.any.run/tasks/9eb24519-b309-4f13-8449-c09e71b36dc8 |
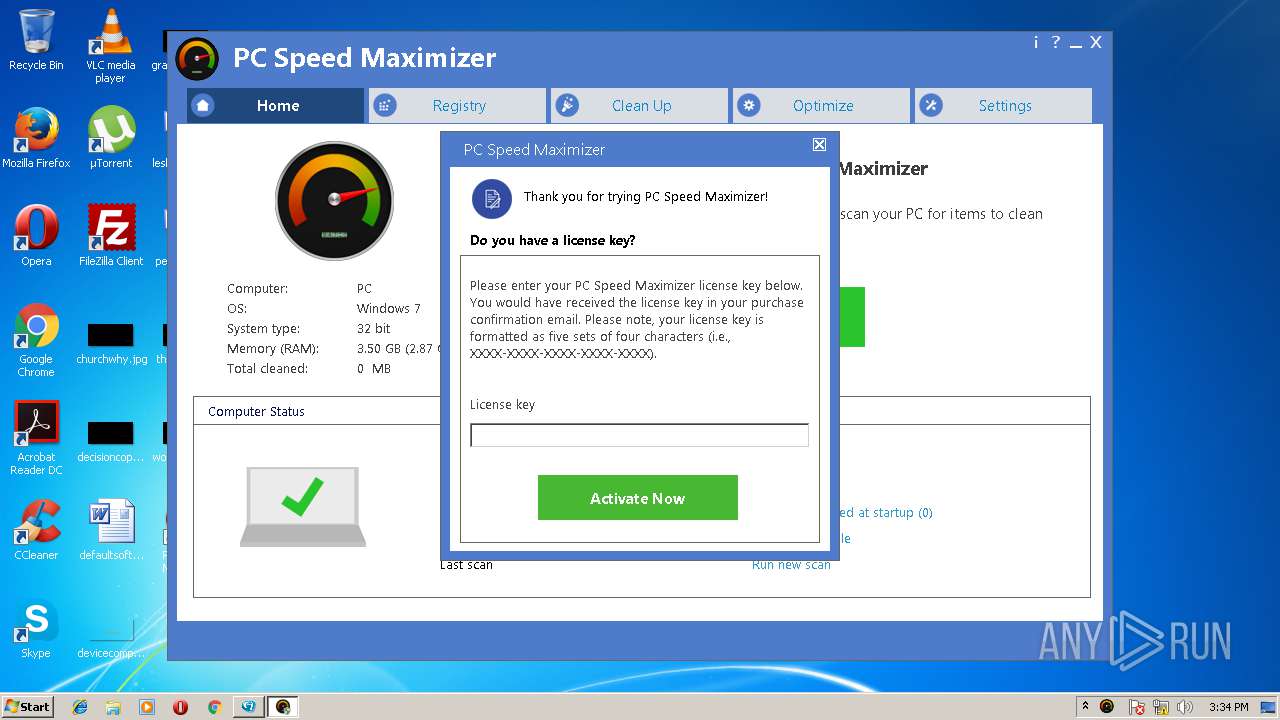
| Verdict: | Suspicious activity |
| Analysis date: | June 16, 2018, 14:33:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B338DA41F7EB697C2344F502044D751F |
| SHA1: | DA0E55D411817D7BD689BF0AFF4C95F6B3E44F08 |
| SHA256: | 323F25758344FC85ACFF95250C855C8E18369EF74A5A8277708806A9CEF65C91 |
| SSDEEP: | 98304:ae0qu46jxpJ556KaVZj5UYPGEA3ceNdqJNr1:aexv6jxTvy5m35qJNx |
MALICIOUS
Loads dropped or rewritten executable
- PC_Speed_Maximizer_5_CHIP_New.exe (PID: 3688)
- PCSpeedMaximizer.exe (PID: 4036)
Application was dropped or rewritten from another process
- Start.exe (PID: 3920)
- PCSM502_COV_Retail.exe (PID: 2180)
- PCSM502_COV_Retail.exe (PID: 3896)
- SPMSchedule.exe (PID: 1572)
- PCSpeedMaximizer.exe (PID: 4036)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3132)
Uses Task Scheduler to run other applications
- PCSpeedMaximizer.exe (PID: 4036)
Changes settings of System certificates
- PCSpeedMaximizer.exe (PID: 4036)
SUSPICIOUS
Reads internet explorer settings
- Start.exe (PID: 3920)
- PCSpeedMaximizer.exe (PID: 4036)
Reads Internet Cache Settings
- Start.exe (PID: 3920)
Executable content was dropped or overwritten
- PCSM502_COV_Retail.exe (PID: 2180)
- PC_Speed_Maximizer_5_CHIP_New.exe (PID: 3688)
- PCSM502_COV_Retail.exe (PID: 3896)
- PCSM502_COV_Retail.tmp (PID: 2824)
Reads Windows owner settings
- PCSM502_COV_Retail.tmp (PID: 2824)
Reads the Windows organization settings
- PCSM502_COV_Retail.tmp (PID: 2824)
Adds / modifies Windows certificates
- PCSpeedMaximizer.exe (PID: 4036)
Creates files in the user directory
- PCSpeedMaximizer.exe (PID: 4036)
Application launched itself
- software_reporter_tool.exe (PID: 3724)
INFO
Dropped object may contain URL's
- PC_Speed_Maximizer_5_CHIP_New.exe (PID: 3688)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 3644)
- PCSM502_COV_Retail.tmp (PID: 2824)
- PCSpeedMaximizer.exe (PID: 4036)
- chrome.exe (PID: 2988)
Reads Internet Cache Settings
- iexplore.exe (PID: 3644)
Reads internet explorer settings
- iexplore.exe (PID: 3644)
Changes internet zones settings
- iexplore.exe (PID: 1440)
Application was dropped or rewritten from another process
- PCSM502_COV_Retail.tmp (PID: 2824)
- PCSM502_COV_Retail.tmp (PID: 860)
Creates files in the user directory
- iexplore.exe (PID: 3644)
Creates files in the program directory
- PCSM502_COV_Retail.tmp (PID: 2824)
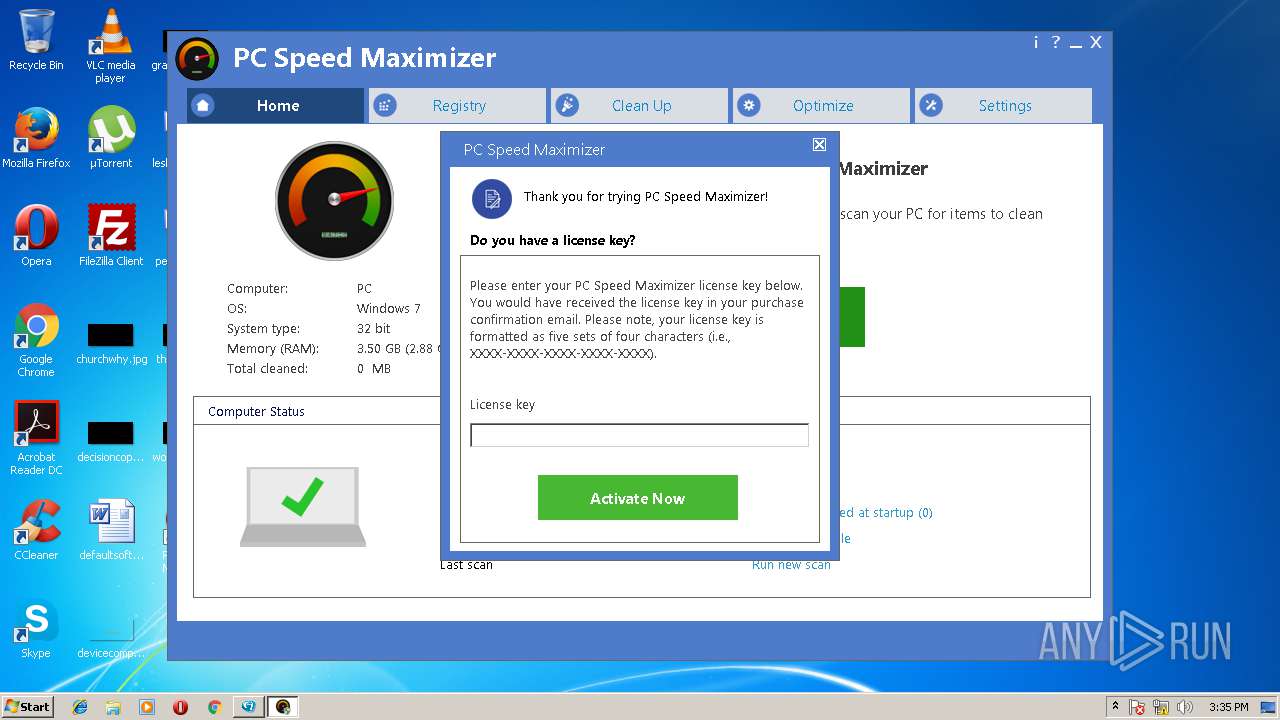
Creates a software uninstall entry
- PCSM502_COV_Retail.tmp (PID: 2824)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 3724)
Application launched itself
- chrome.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:29 11:14:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 546304 |
| InitializedDataSize: | 432128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6fb2b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build, Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
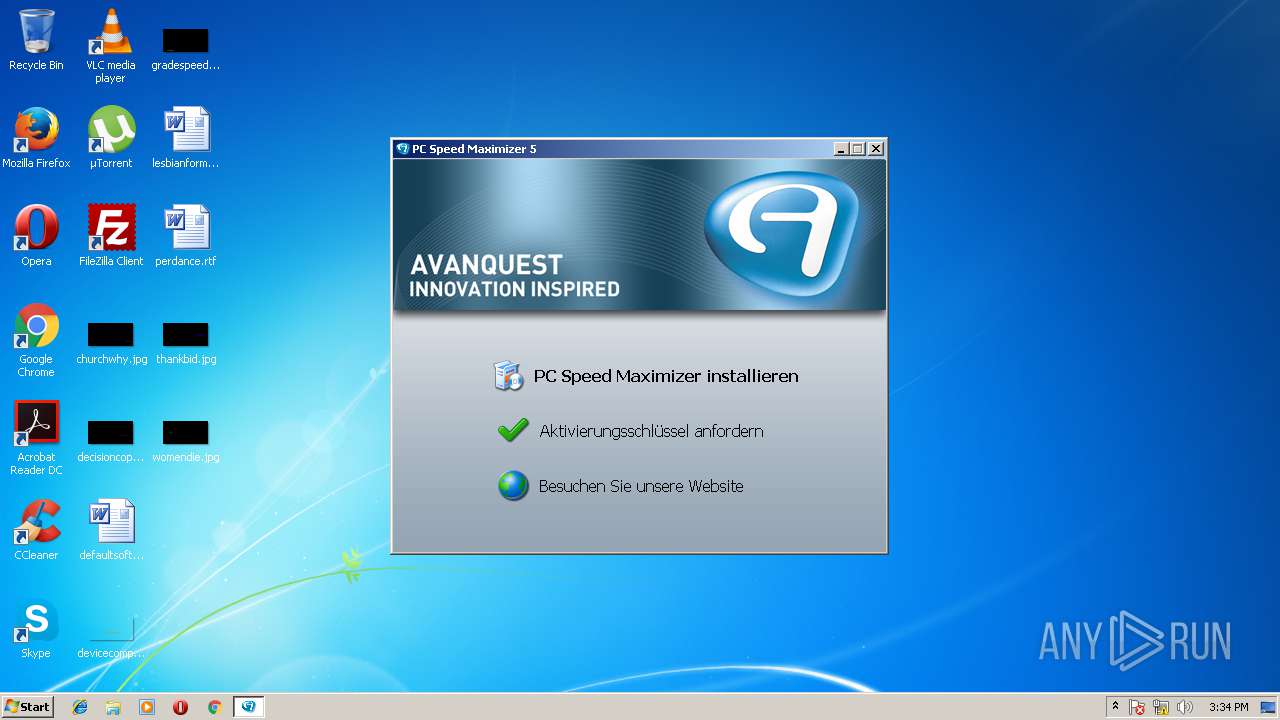
| ProductName: | PC Speed Maximizer 5 |
| ProductVersion: | 5 |
| Comments: | PC Speed Maximizer 5 |
| FileDescription: | PC Speed Maximizer 5 |
| InternalName: | Setup.exe |
| OriginalFileName: | Setup.exe |
| FileVersion: | 5 |
| CompanyName: | Avanquest Software |
| LegalCopyright: | Copyright © Avanquest Software 2018 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Nov-2017 10:14:06 |
| Detected languages: |
|
| Debug artifacts: |
|
| ProductName: | PC Speed Maximizer 5 |
| ProductVersion: | 5 |
| Comments: | PC Speed Maximizer 5 |
| FileDescription: | PC Speed Maximizer 5 |
| InternalName: | Setup.exe |
| OriginalFilename: | Setup.exe |
| FileVersion: | 5 |
| CompanyName: | Avanquest Software |
| LegalCopyright: | Copyright © Avanquest Software 2018 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Nov-2017 10:14:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00085556 | 0x00085600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61491 |
.rdata | 0x00087000 | 0x0002059A | 0x00020600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54313 |
.data | 0x000A8000 | 0x00024F48 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.76587 |
.rsrc | 0x000CD000 | 0x0003F9B4 | 0x0003FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.32522 |
.reloc | 0x0010D000 | 0x00006994 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.77301 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.42047 | 1325 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.15965 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.37186 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.36807 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.04226 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 7.94825 | 28984 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.87244 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.46852 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 3.16151 | 554 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.14237 | 552 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
DIRPACN.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
62
Monitored processes
24
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | "C:\Users\admin\AppData\Local\Temp\is-MKSKS.tmp\PCSM502_COV_Retail.tmp" /SL5="$70174,2758800,121344,C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\Data\DEU\PCSM502_COV_Retail.exe" | C:\Users\admin\AppData\Local\Temp\is-MKSKS.tmp\PCSM502_COV_Retail.tmp | — | PCSM502_COV_Retail.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1608,11496631122164120841,8652899428344485613,131072 --service-pipe-token=3A975088016C14E28C4E2944C3B26500 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=3A975088016C14E28C4E2944C3B26500 --renderer-client-id=7 --mojo-platform-channel-handle=1972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1572 | "C:\Program Files\PC Speed Maximizer\SPMSchedule.exe" | C:\Program Files\PC Speed Maximizer\SPMSchedule.exe | — | PCSM502_COV_Retail.tmp | |||||||||||
User: admin Company: Avanquest Software Integrity Level: HIGH Description: PC Speed Maximizer automatic scan and notifications Exit code: 1073807364 Version: 5.0.2.0 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\Data\DEU\PCSM502_COV_Retail.exe" | C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\Data\DEU\PCSM502_COV_Retail.exe | Start.exe | ||||||||||||
User: admin Company: Avanquest Software Integrity Level: MEDIUM Description: PC Speed Maximizer Exit code: 0 Version: 5.0.2 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f807d7c,0x6f807da4,0x6f807d8c | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1608,11496631122164120841,8652899428344485613,131072 --service-pipe-token=00D5175BE25BB0FA954F3374FB96BE6B --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=00D5175BE25BB0FA954F3374FB96BE6B --renderer-client-id=4 --mojo-platform-channel-handle=1620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1608,11496631122164120841,8652899428344485613,131072 --service-pipe-token=10C7480785EAF86B7CF86FF3A7240253 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=10C7480785EAF86B7CF86FF3A7240253 --renderer-client-id=2 --mojo-platform-channel-handle=1284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2824 | "C:\Users\admin\AppData\Local\Temp\is-1MPFR.tmp\PCSM502_COV_Retail.tmp" /SL5="$E0228,2758800,121344,C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\Data\DEU\PCSM502_COV_Retail.exe" /SPAWNWND=$19020C /NOTIFYWND=$70174 | C:\Users\admin\AppData\Local\Temp\is-1MPFR.tmp\PCSM502_COV_Retail.tmp | PCSM502_COV_Retail.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2844 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
2 904
Read events
2 422
Write events
464
Delete events
18
Modification events
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3688) PC_Speed_Maximizer_5_CHIP_New.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PC_Speed_Maximizer_5_CHIP_New_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
9
Suspicious files
73
Text files
120
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\{d88cfdc4-4008-4927-920E-A5C71A271F83}\Binary.tmp | — | |
MD5:— | SHA256:— | |||
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\{d88cfdc4-4008-4927-920E-A5C71A271F83}\German.001 | — | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@register.avanquest[1].txt | — | |
MD5:— | SHA256:— | |||
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\CDBrowser\Home.htm | html | |
MD5:— | SHA256:— | |||
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\autorun.inf | ini | |
MD5:— | SHA256:— | |||
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\{d88cfdc4-4008-4927-920E-A5C71A271F83}\German.lng | executable | |
MD5:— | SHA256:— | |||
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\PC Speed Maximizer 5\Start.exe | executable | |
MD5:— | SHA256:— | |||
| 3688 | PC_Speed_Maximizer_5_CHIP_New.exe | C:\Users\admin\AppData\Local\Temp\{d88cfdc4-4008-4927-920E-A5C71A271F83}\setup.cfg | text | |
MD5:— | SHA256:— | |||
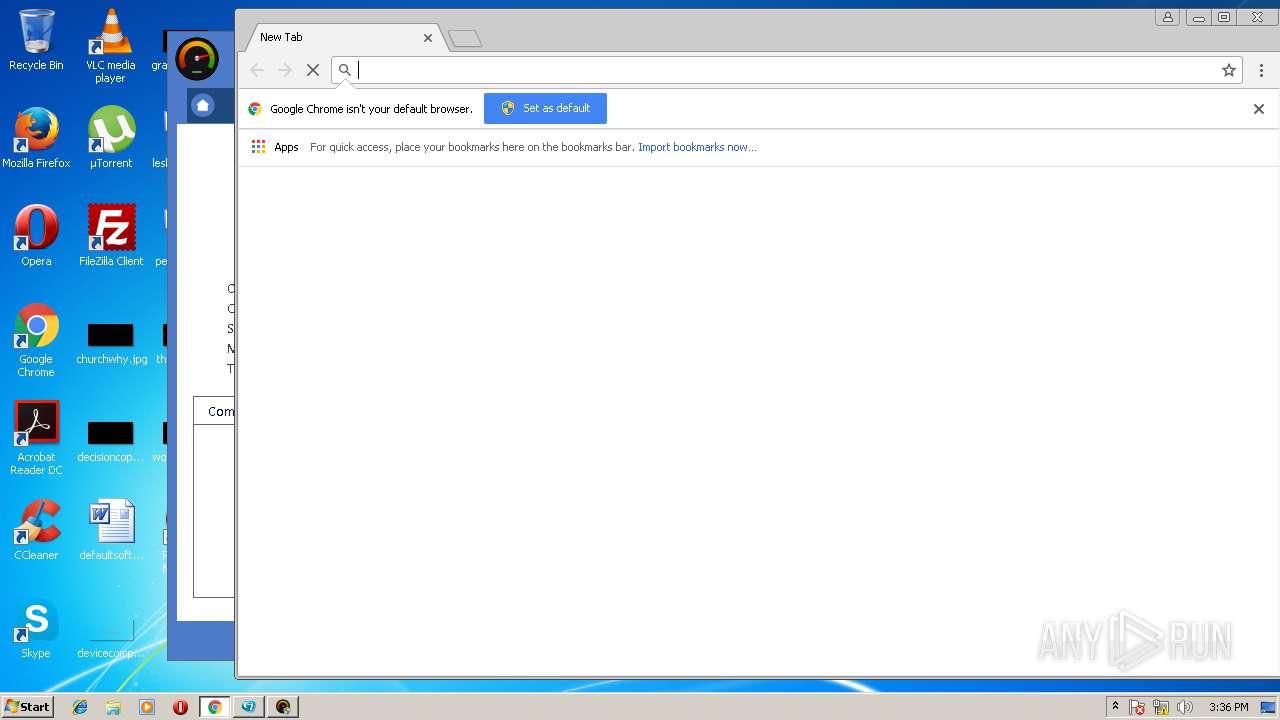
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
188
DNS requests
146
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | chrome.exe | GET | — | 217.195.25.244:80 | http://register.avanquest.com/images/Mailings/Mailings/background_598.gif | FR | — | — | unknown |
2988 | chrome.exe | GET | — | 217.195.25.244:80 | http://register.avanquest.com/images/Mailings/Mailings/background_598.gif | FR | — | — | unknown |
2988 | chrome.exe | GET | — | 217.195.25.244:80 | http://register.avanquest.com/images/Mailings/Mailings/background_598.gif | FR | — | — | unknown |
4036 | PCSpeedMaximizer.exe | GET | 200 | 94.130.13.79:80 | http://stats.smartpctools.com/si?p=PCSM5_COV_RETAIL&b=5.0.2&c=June2018 | DE | text | 18 b | unknown |
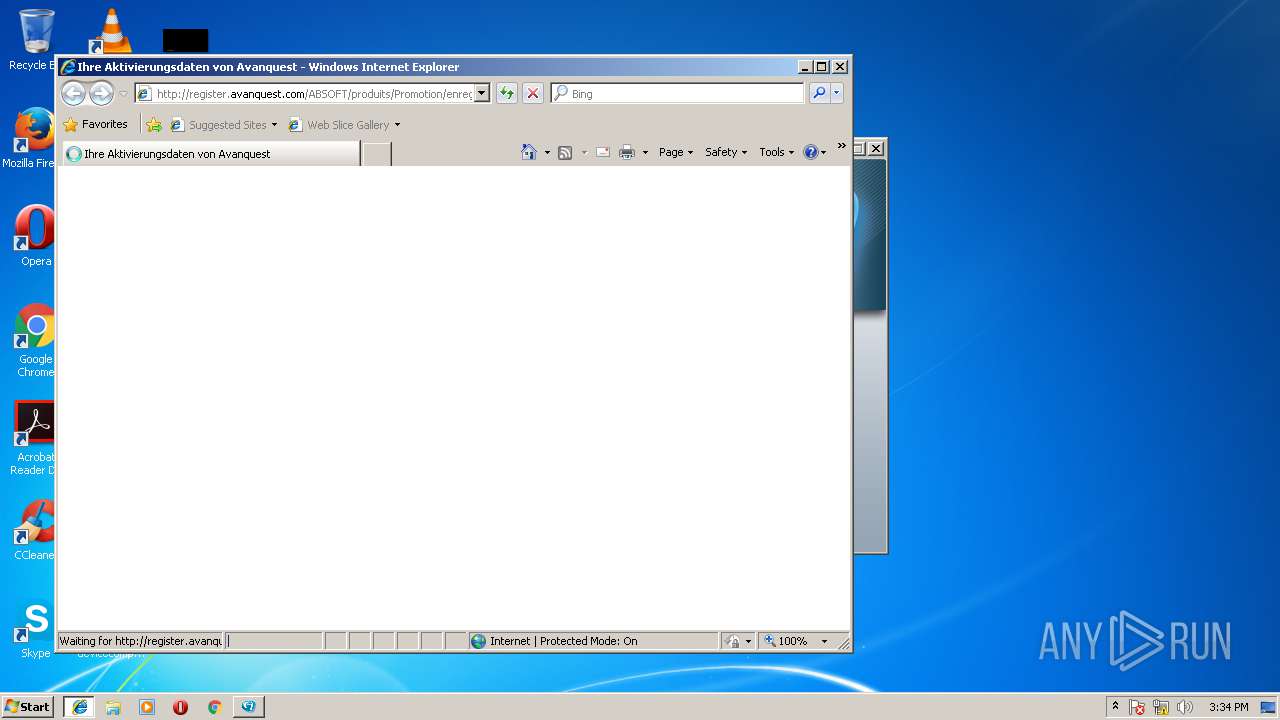
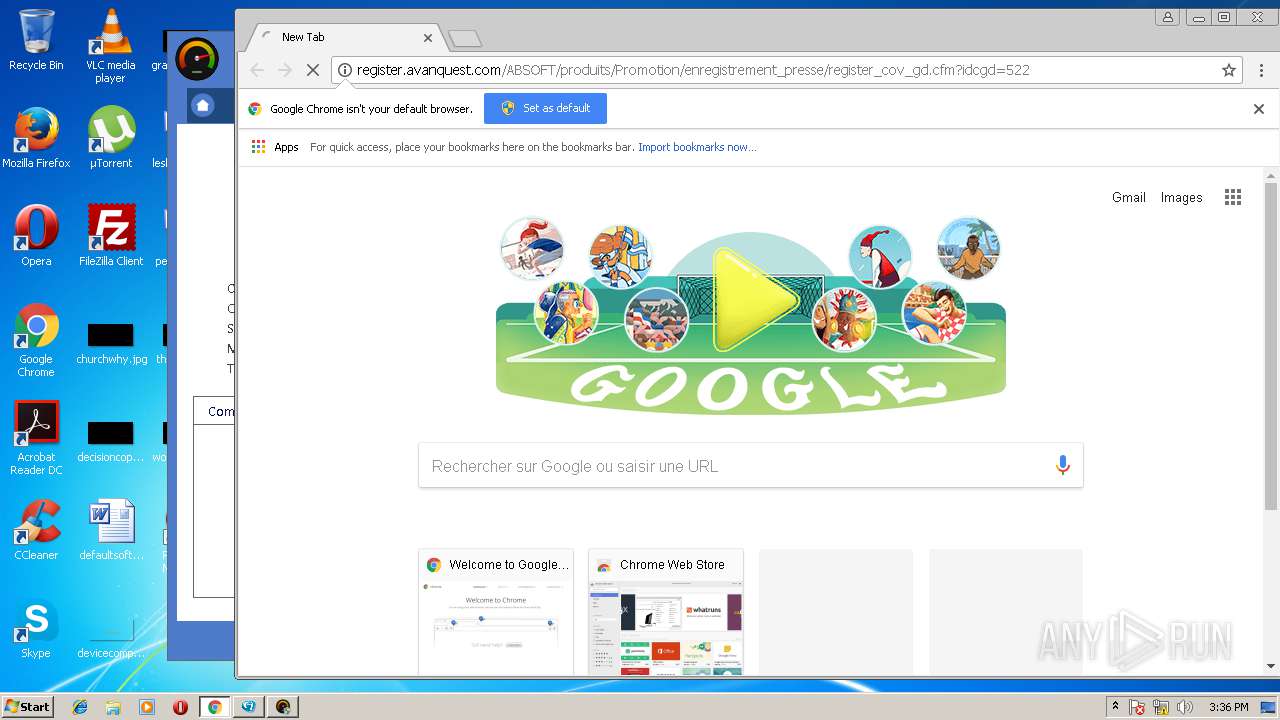
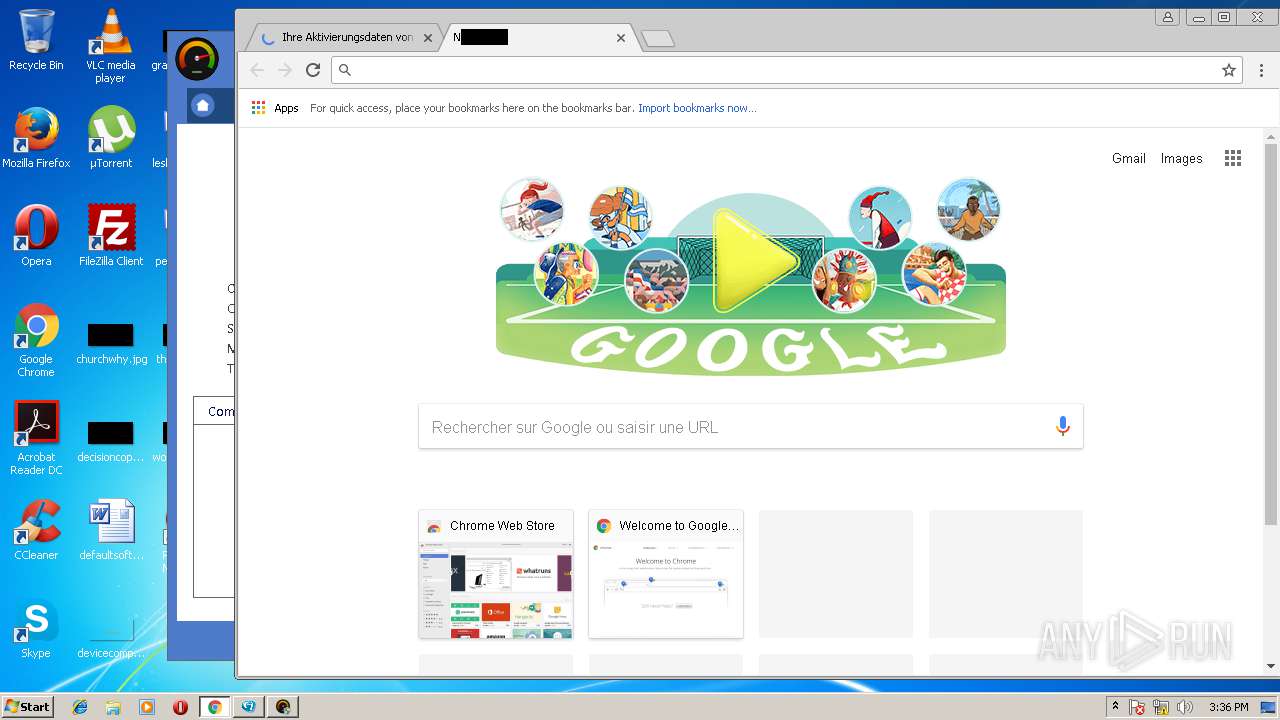
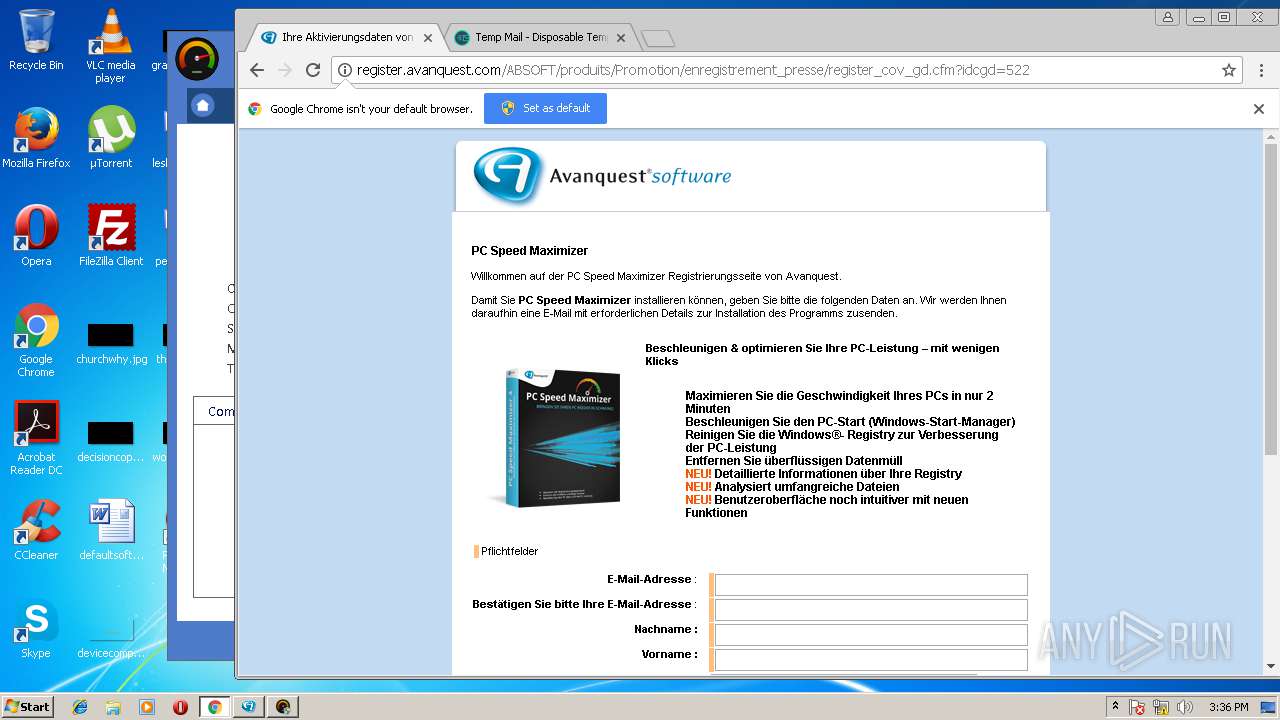
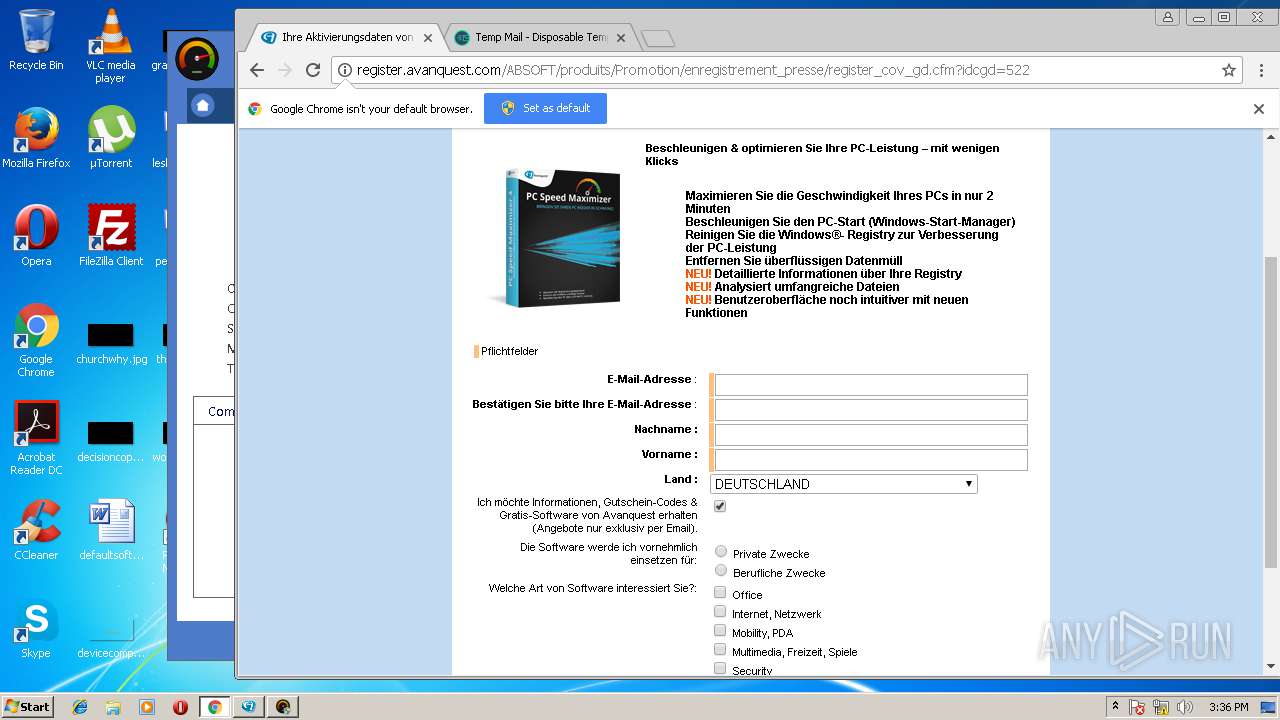
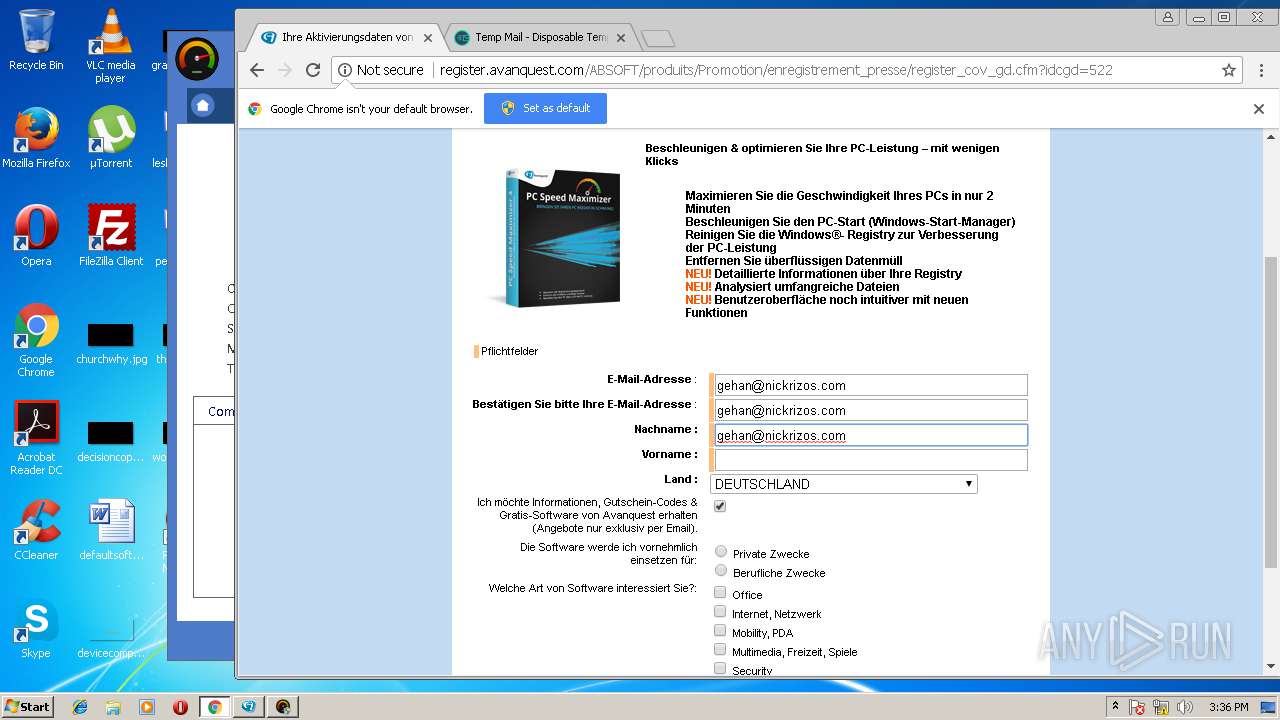
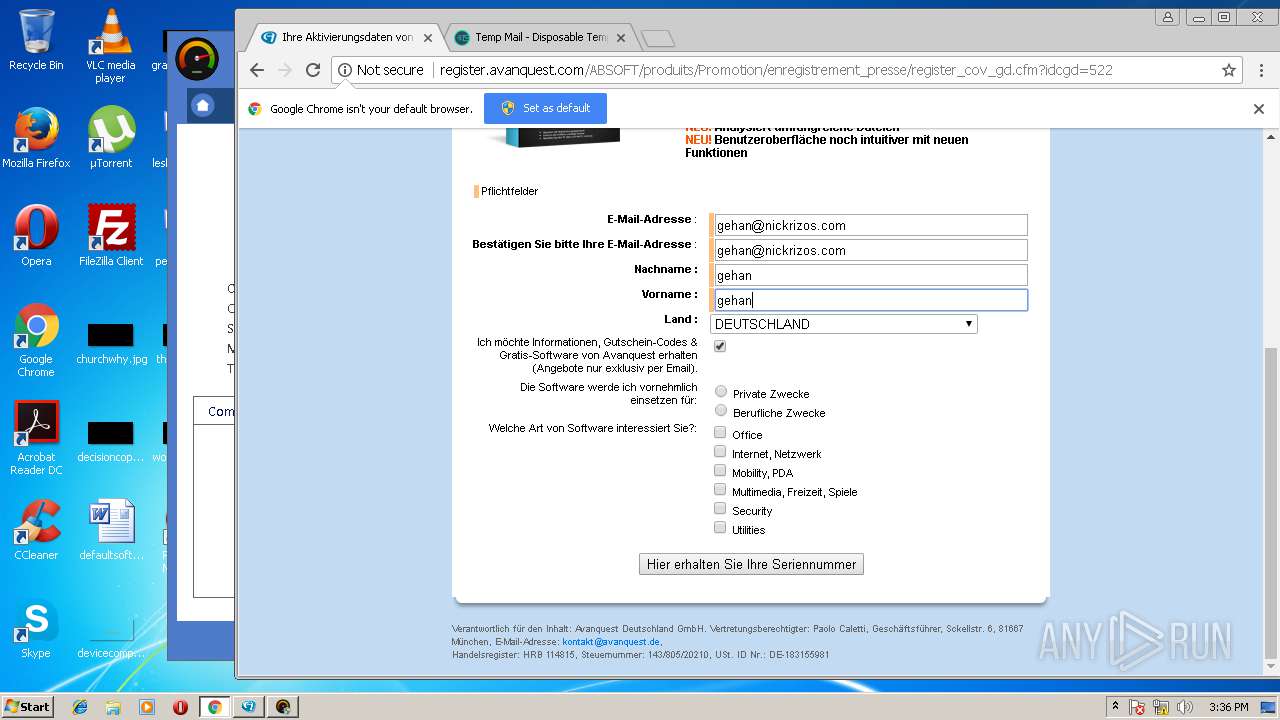
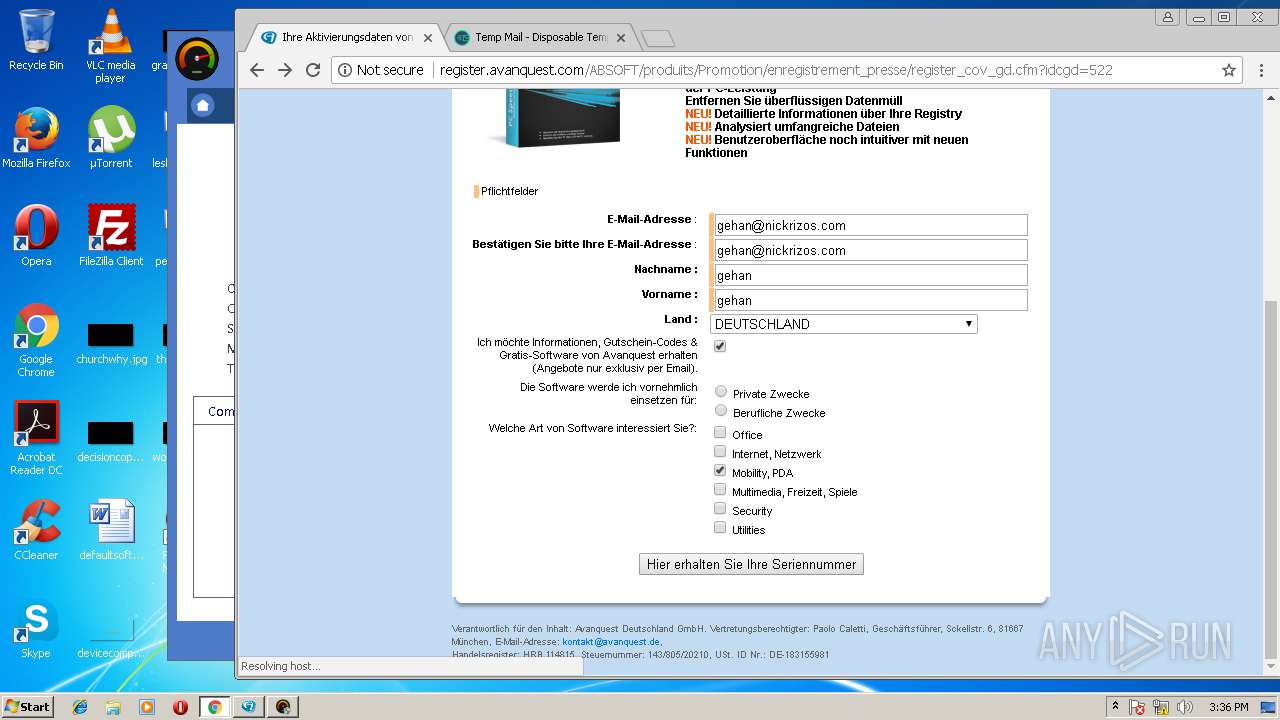
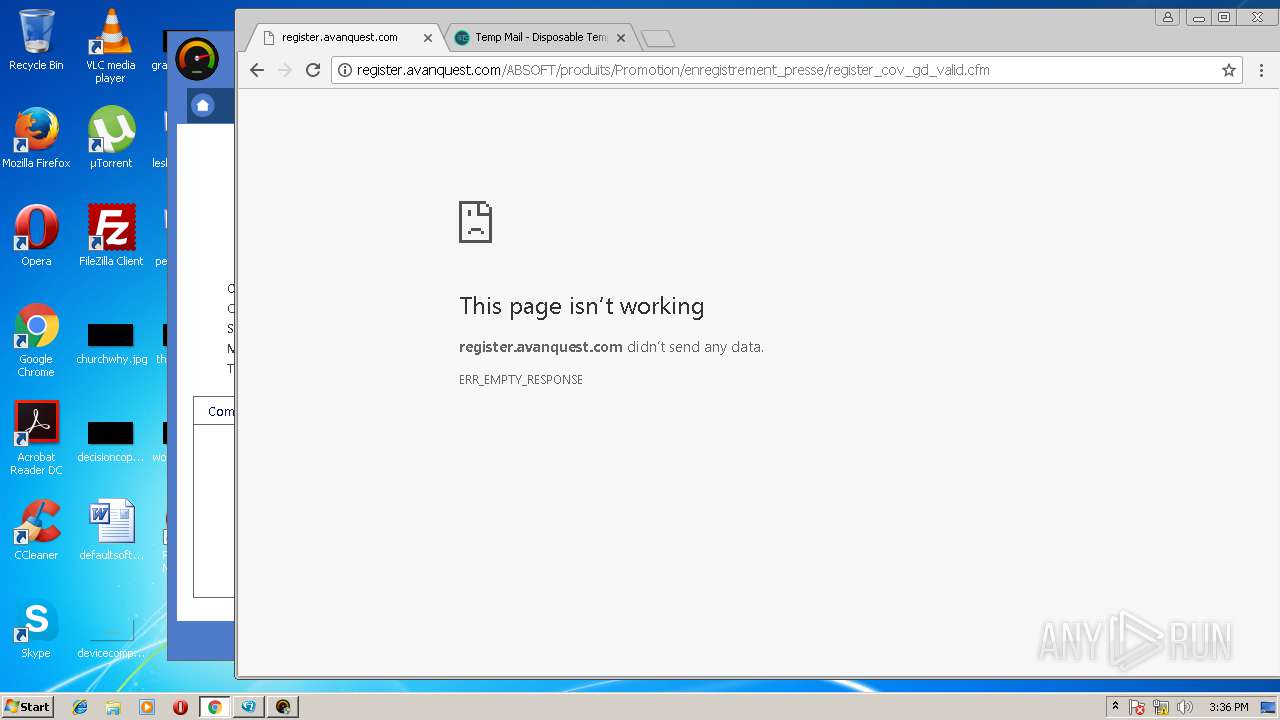
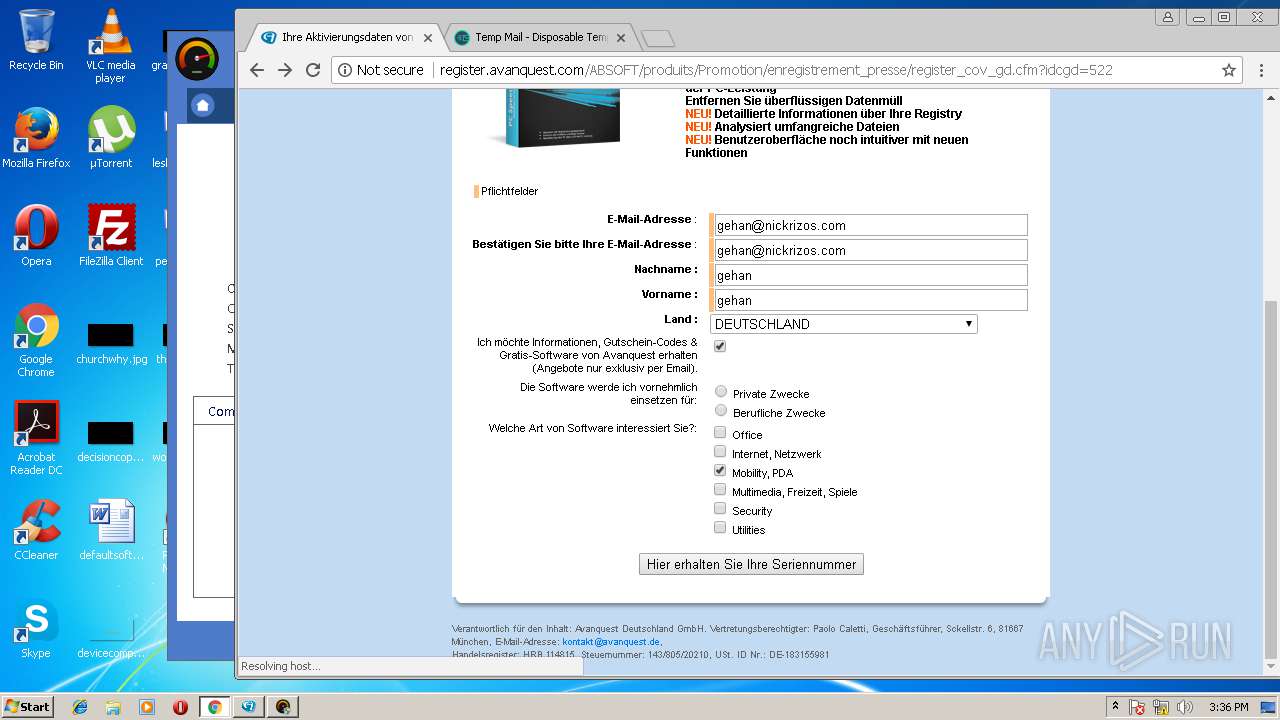
2988 | chrome.exe | GET | 200 | 217.195.25.244:80 | http://register.avanquest.com/ABSOFT/produits/Promotion/enregistrement_presse/register_cov_gd.cfm?idcgd=522 | FR | html | 18.2 Kb | unknown |
3644 | iexplore.exe | GET | 200 | 217.195.25.244:80 | http://register.avanquest.com/ABSOFT/produits/Promotion/enregistrement_presse/register_cov_gd.cfm?idcgd=522 | FR | html | 18.2 Kb | unknown |
2988 | chrome.exe | GET | 200 | 217.195.25.244:80 | http://register.avanquest.com/images/Mailings/Mailings/bottom.gif | FR | image | 811 b | unknown |
3644 | iexplore.exe | GET | 200 | 217.195.25.244:80 | http://register.avanquest.com/Tools/js/fenetre.js | FR | text | 4.10 Kb | unknown |
3644 | iexplore.exe | GET | 200 | 217.195.25.244:80 | http://register.avanquest.com/Tools/js/hbx.js | FR | text | 152 b | unknown |
4036 | PCSpeedMaximizer.exe | GET | 302 | 217.195.25.241:80 | http://webtools.avanquest.com/install_success.cfm?redirectId=Avanquest/PC_Speed_Maximizer_Buy_ML_05_COV.htm&target=http://onesafe-software.com/Install/cleaner/install_success.cfm&campaignid=PPI&dcid=¶murl=1&mkey1=DEFAULT_REDIRECT_TRACKING | FR | text | 83 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3688 | PC_Speed_Maximizer_5_CHIP_New.exe | 104.89.34.252:80 | www.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
4036 | PCSpeedMaximizer.exe | 217.195.25.241:443 | webtools.avanquest.com | SPIE Cloud Services SAS | FR | malicious |
3644 | iexplore.exe | 217.195.25.244:80 | register.avanquest.com | SPIE Cloud Services SAS | FR | unknown |
4036 | PCSpeedMaximizer.exe | 94.130.13.79:80 | stats.smartpctools.com | Hetzner Online GmbH | DE | unknown |
1440 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4036 | PCSpeedMaximizer.exe | 217.195.25.241:80 | webtools.avanquest.com | SPIE Cloud Services SAS | FR | malicious |
4036 | PCSpeedMaximizer.exe | 217.195.25.235:80 | onesafe-software.com | SPIE Cloud Services SAS | FR | unknown |
4036 | PCSpeedMaximizer.exe | 205.185.208.52:80 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
4036 | PCSpeedMaximizer.exe | 172.217.22.98:443 | adservice.google.fr | Google Inc. | US | whitelisted |
4036 | PCSpeedMaximizer.exe | 216.58.210.6:443 | 5352376.fls.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
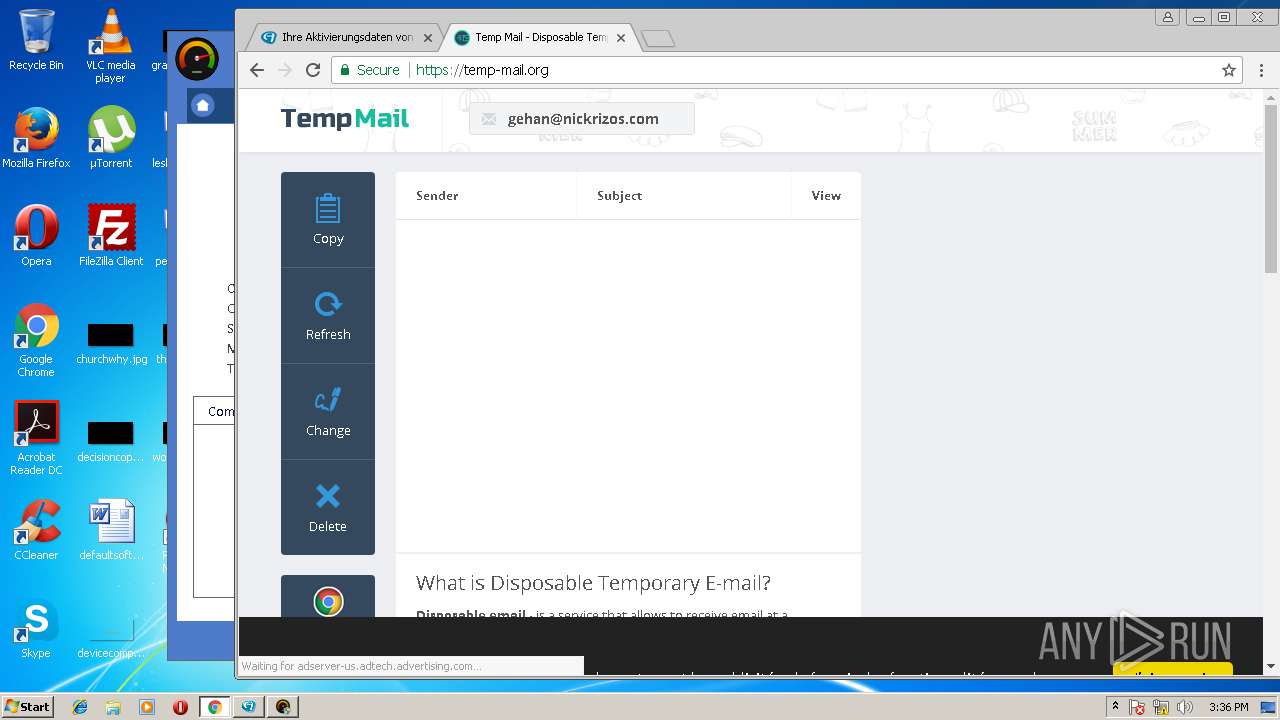
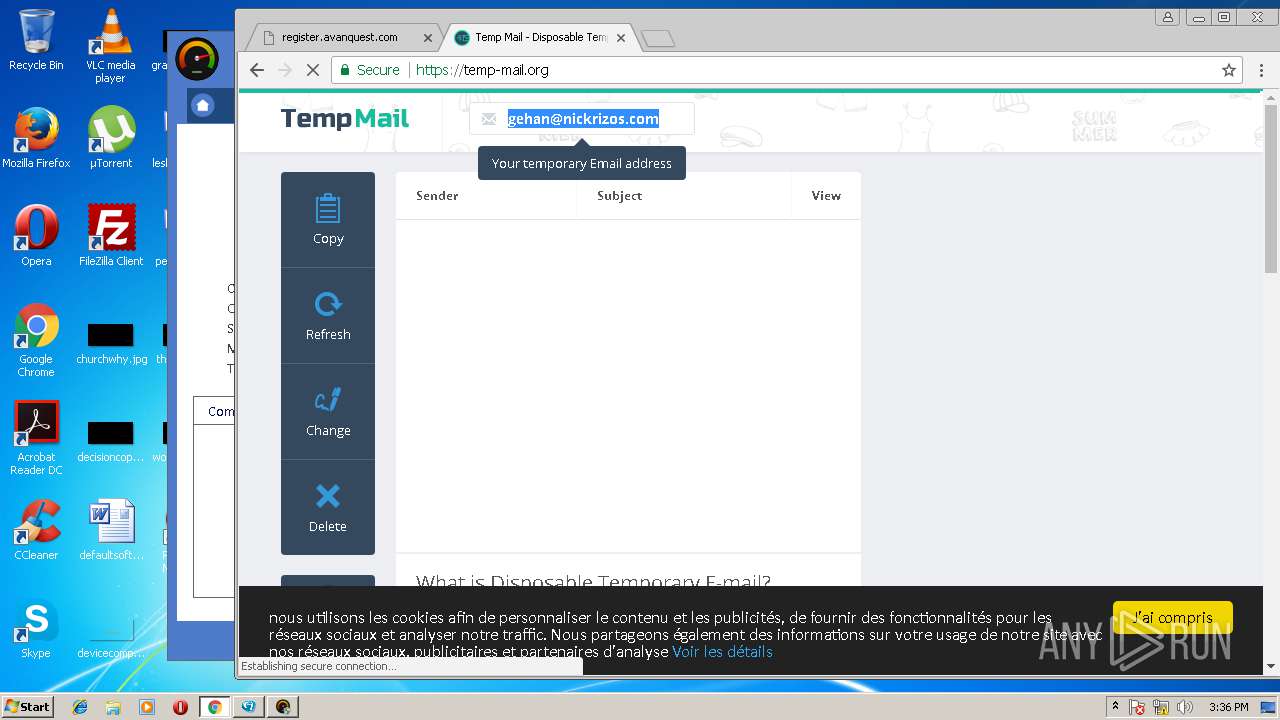
register.avanquest.com |
| unknown |
www.bvrp.fr |
| unknown |
webtools.avanquest.com |
| unknown |
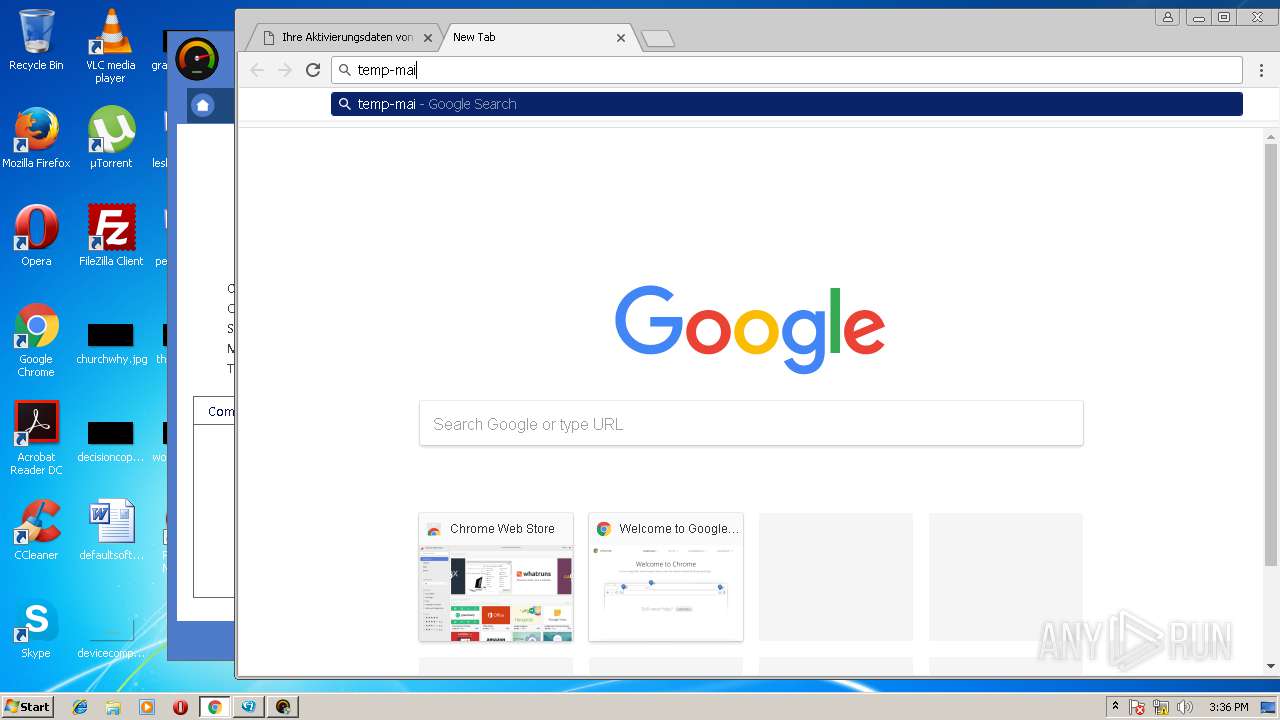
onesafe-software.com |
| unknown |
stats.smartpctools.com |
| unknown |
code.jquery.com |
| whitelisted |
5352376.fls.doubleclick.net |
| suspicious |
adservice.google.com |
| whitelisted |