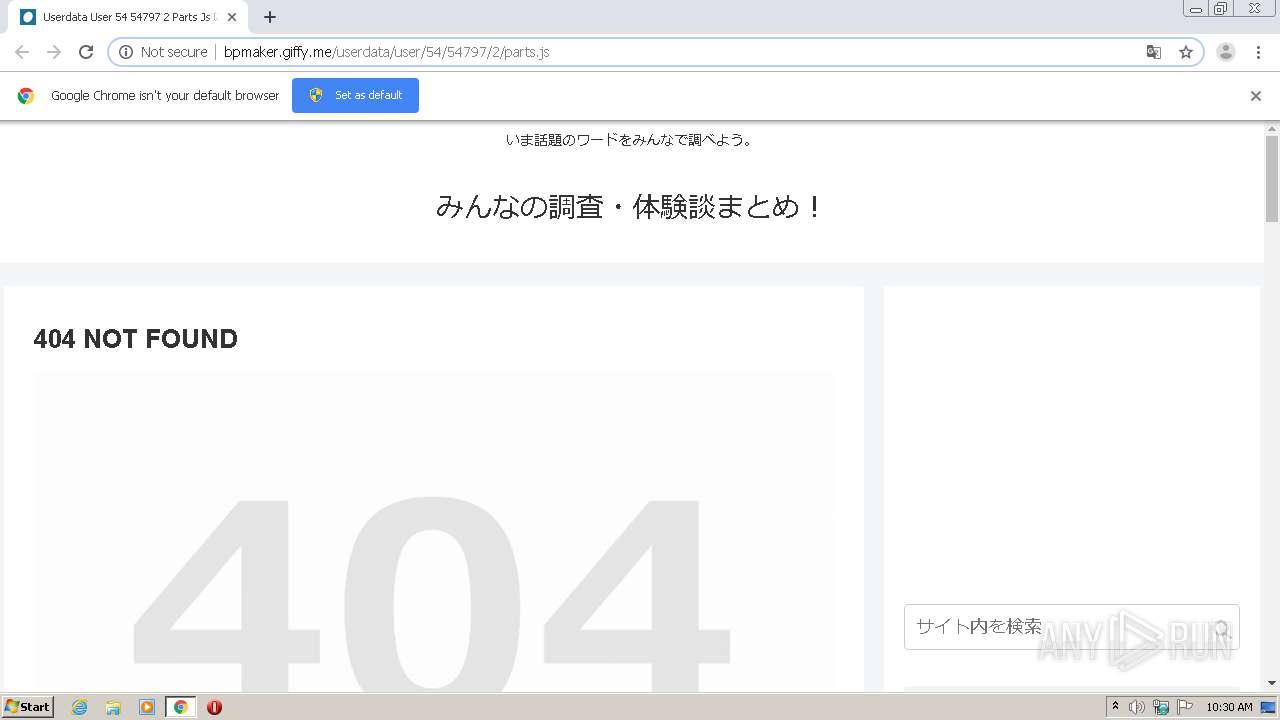
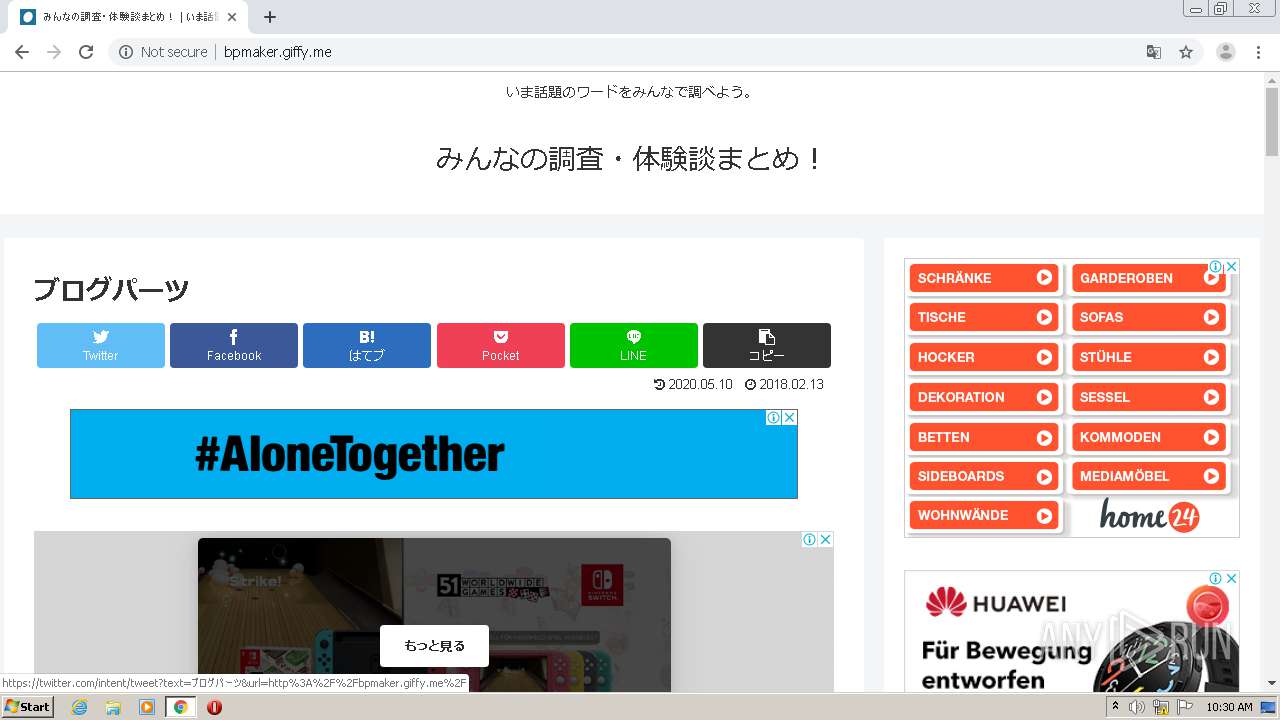
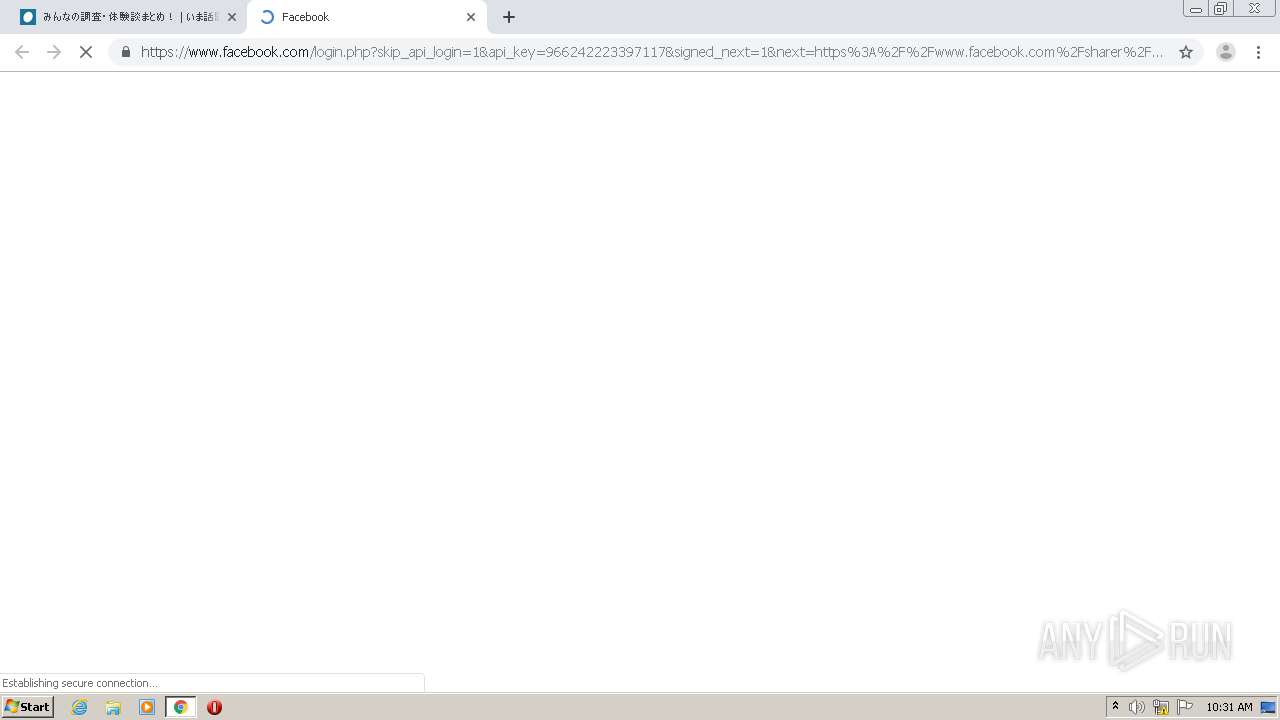
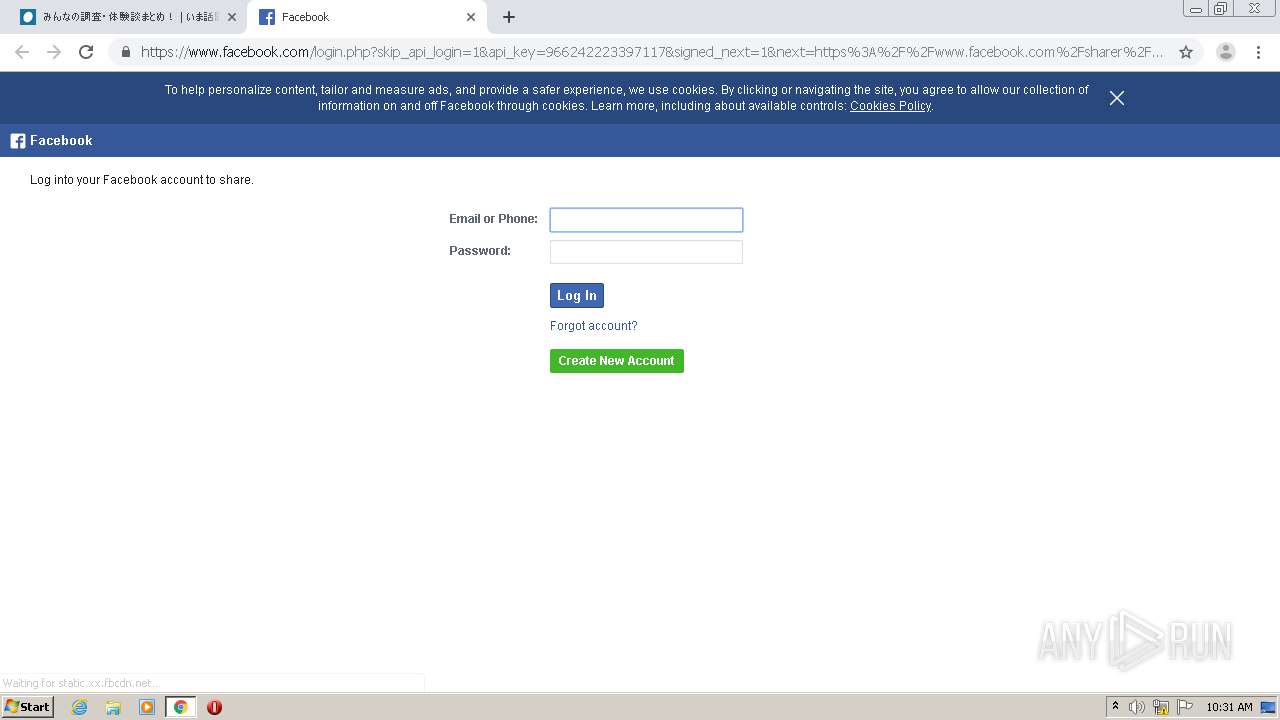
| URL: | http://bpmaker.giffy.me/userdata/user/54/54797/2/parts.js |
| Full analysis: | https://app.any.run/tasks/3f3be676-19b1-4961-9254-4ed24bcefadb |
| Verdict: | No threats detected |
| Analysis date: | June 12, 2020, 09:29:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 38932EC4BE1A8E1C730F965B89B04AD8 |
| SHA1: | 0C87BAFF32F0C280FEAC1C4B1C37968762713113 |
| SHA256: | 322DD19BFDBC2703FA0C4E2D01F524AB6AE6CA62025BC20E7EC323587B0485A9 |
| SSDEEP: | 3:N1KcnOyLCVojpAXLRIcJOuWLu:CcnOvyuXGc8ZLu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1452)
INFO
Reads the hosts file
- chrome.exe (PID: 1452)
- chrome.exe (PID: 3972)
Creates files in the user directory
- chrome.exe (PID: 1452)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1452)
Application launched itself
- chrome.exe (PID: 1452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3970175502547571927 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8483613461528135879 --mojo-platform-channel-handle=3752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17933834971243655555 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13884623546821277115 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=168624932801138933 --mojo-platform-channel-handle=4200 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7281931283168954608 --mojo-platform-channel-handle=3740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3385879100596493869 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://bpmaker.giffy.me/userdata/user/54/54797/2/parts.js" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14064924745634609943,5797815929948824460,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3282722971276412257 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1584 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
681
Read events
576
Write events
100
Delete events
5
Modification events
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1452-13236427794718500 |
Value: 259 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1452) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
449
Text files
302
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EE34B13-5AC.pma | — | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\73c0d7b1-0ed3-4a47-a83f-db9200f64997.tmp | — | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFf69ad.TMP | text | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf6b53.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
217
DNS requests
96
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | chrome.exe | GET | 301 | 104.16.87.20:80 | http://cdn.jsdelivr.net/wp/wp-slimstat/tags/4.7.5.3/wp-slimstat.min.js | US | — | — | whitelisted |
3972 | chrome.exe | GET | 301 | 104.16.87.20:80 | http://cdn.jsdelivr.net/clipboard.js/1.5.13/clipboard.min.js | US | — | — | whitelisted |
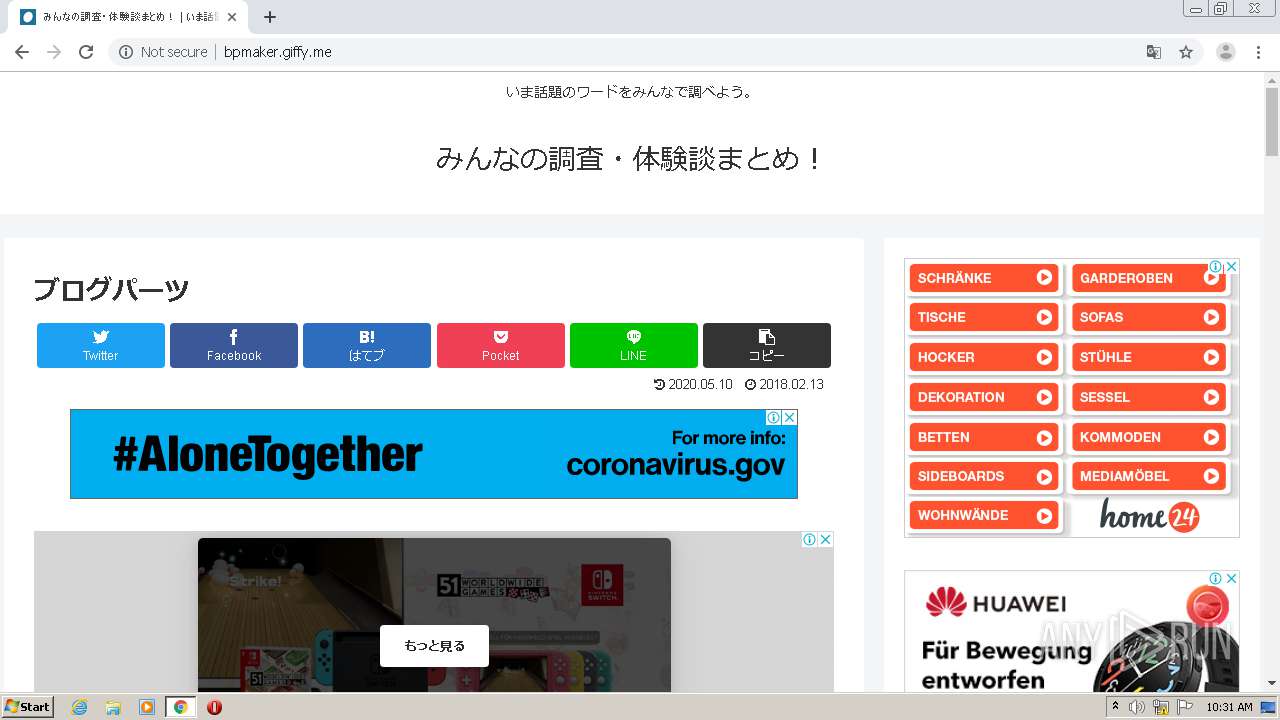
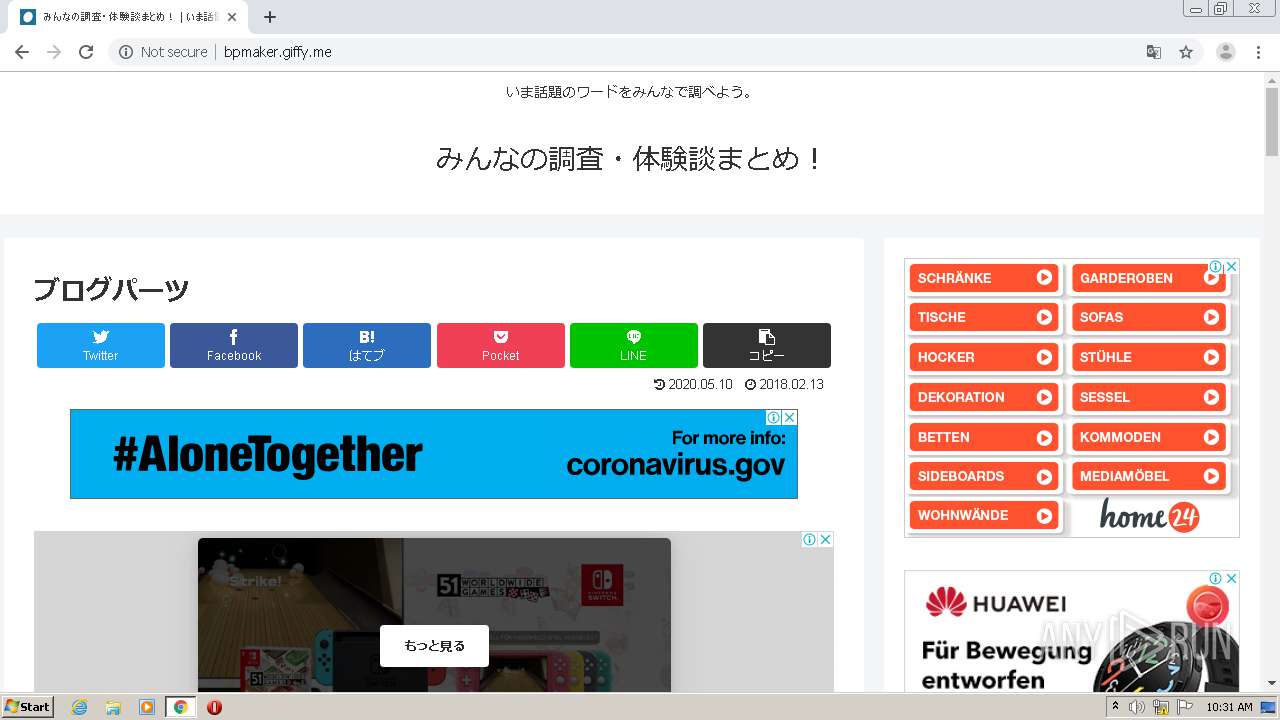
3972 | chrome.exe | GET | 200 | 183.181.98.67:80 | http://bpmaker.giffy.me/wp-content/themes/cocoon-child-master/style.css?ver=4.9.15&fver=20200510081648 | JP | text | 719 b | unknown |
3972 | chrome.exe | GET | 200 | 183.181.98.67:80 | http://bpmaker.giffy.me/wp-content/themes/cocoon-master/javascript.js?ver=4.9.15&fver=20200510081619 | JP | text | 2.72 Kb | unknown |
3972 | chrome.exe | GET | 200 | 216.58.212.130:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 39.2 Kb | whitelisted |
3972 | chrome.exe | GET | 200 | 183.181.98.67:80 | http://bpmaker.giffy.me/wp-content/themes/cocoon-master/keyframes.css?ver=4.9.15&fver=20200510081619 | JP | text | 349 b | unknown |
3972 | chrome.exe | GET | 404 | 183.181.98.67:80 | http://bpmaker.giffy.me/userdata/user/54/54797/2/parts.js | JP | html | 18.3 Kb | unknown |
3972 | chrome.exe | GET | 200 | 183.181.98.67:80 | http://bpmaker.giffy.me/wp-content/themes/cocoon-master/webfonts/icomoon/style.css?ver=4.9.15&fver=20200510081619 | JP | text | 856 b | unknown |
3972 | chrome.exe | GET | 200 | 183.181.98.67:80 | http://bpmaker.giffy.me/wp-content/themes/cocoon-master/webfonts/icomoon/fonts/icomoon.woff?n4zge5 | JP | woff | 7.58 Kb | unknown |
3972 | chrome.exe | GET | 200 | 183.181.98.67:80 | http://bpmaker.giffy.me/wp-content/themes/cocoon-child-master/keyframes.css?ver=4.9.15&fver=20200510081648 | JP | text | 130 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | chrome.exe | 183.181.98.67:80 | bpmaker.giffy.me | SAKURA Internet Inc. | JP | unknown |
3972 | chrome.exe | 104.16.132.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3972 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 172.217.16.136:80 | www.googletagmanager.com | Google Inc. | US | suspicious |
3972 | chrome.exe | 216.58.212.130:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 210.140.225.41:80 | dalb.valuecommerce.com | Yahoo Japan Corporation | JP | unknown |
3972 | chrome.exe | 210.140.225.106:80 | dalc.valuecommerce.com | Yahoo Japan Corporation | JP | unknown |
3972 | chrome.exe | 202.218.168.42:80 | aml.valuecommerce.com | Yahoo Japan Corporation | JP | unknown |
3972 | chrome.exe | 104.16.87.20:80 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bpmaker.giffy.me |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
webfonts.xserver.jp |
| suspicious |
pagead2.googlesyndication.com |
| whitelisted |
ad.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3972 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3972 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |