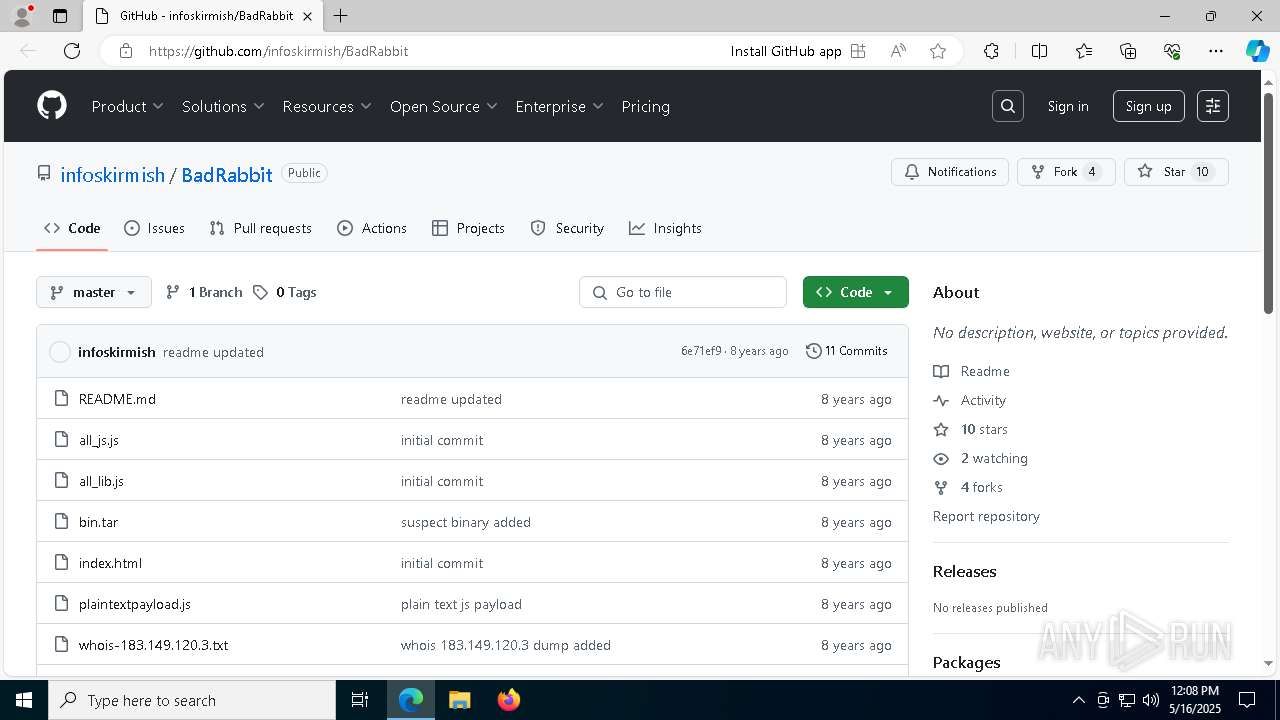
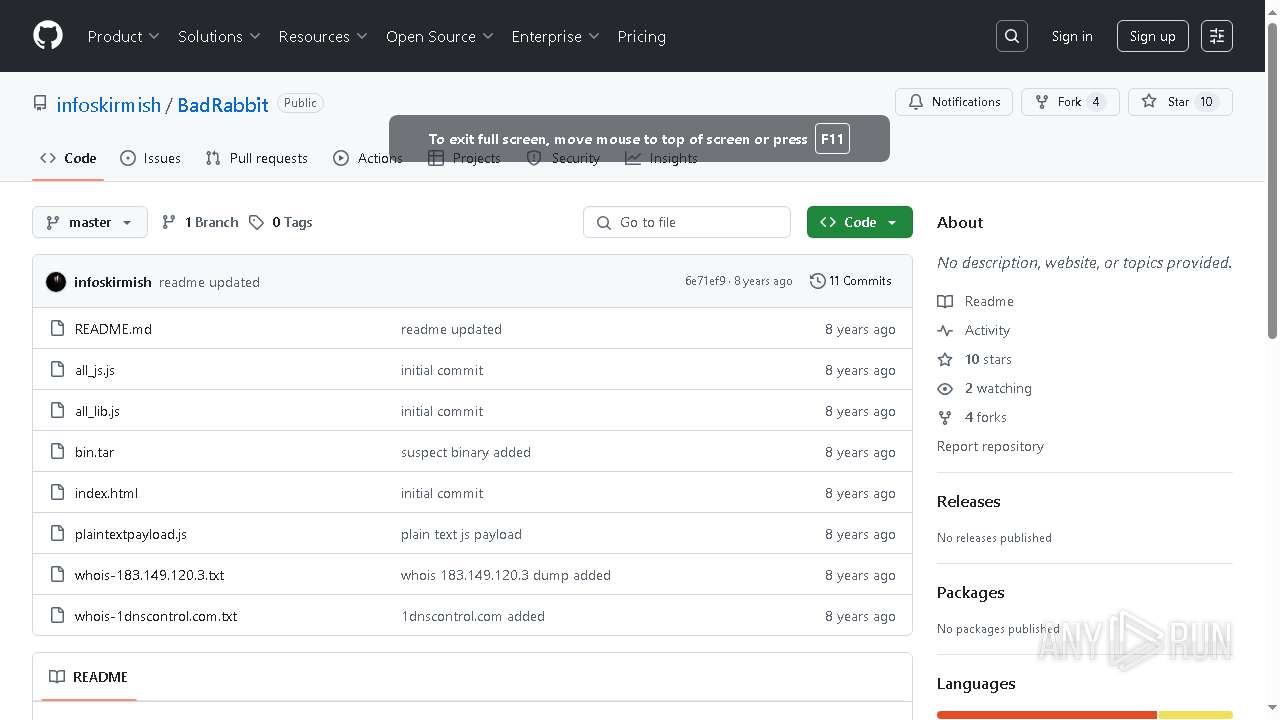
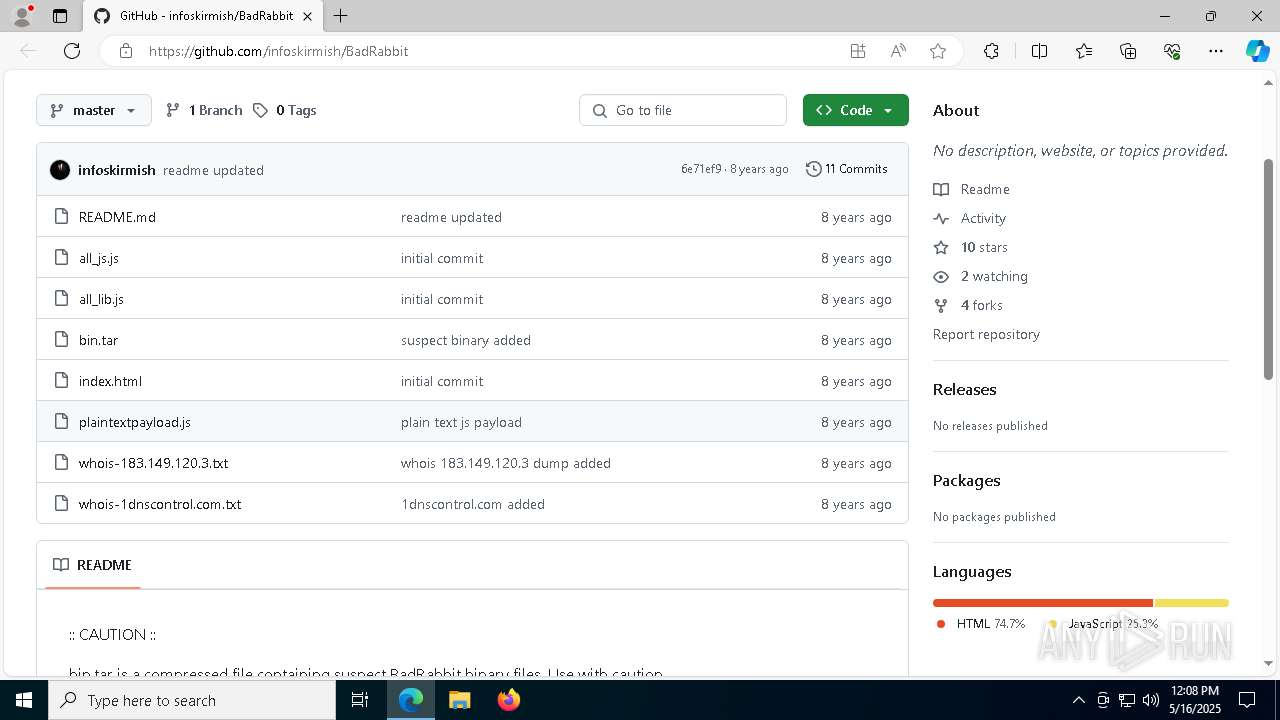
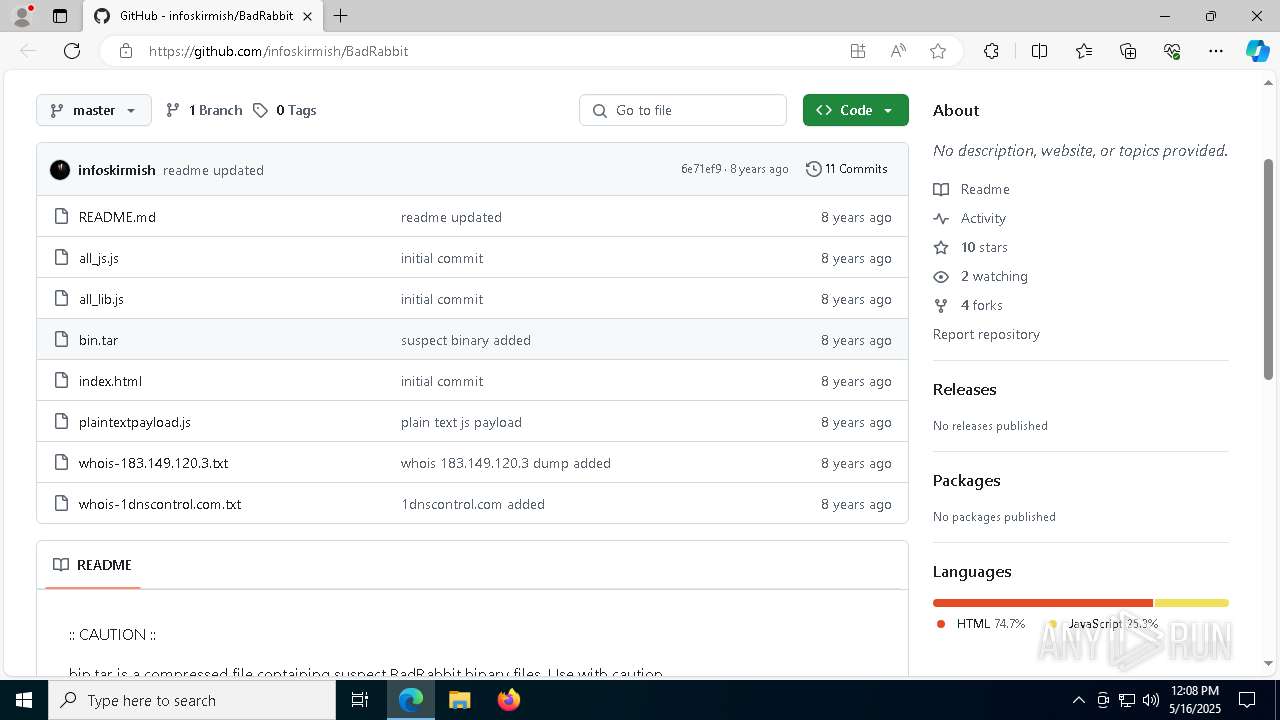
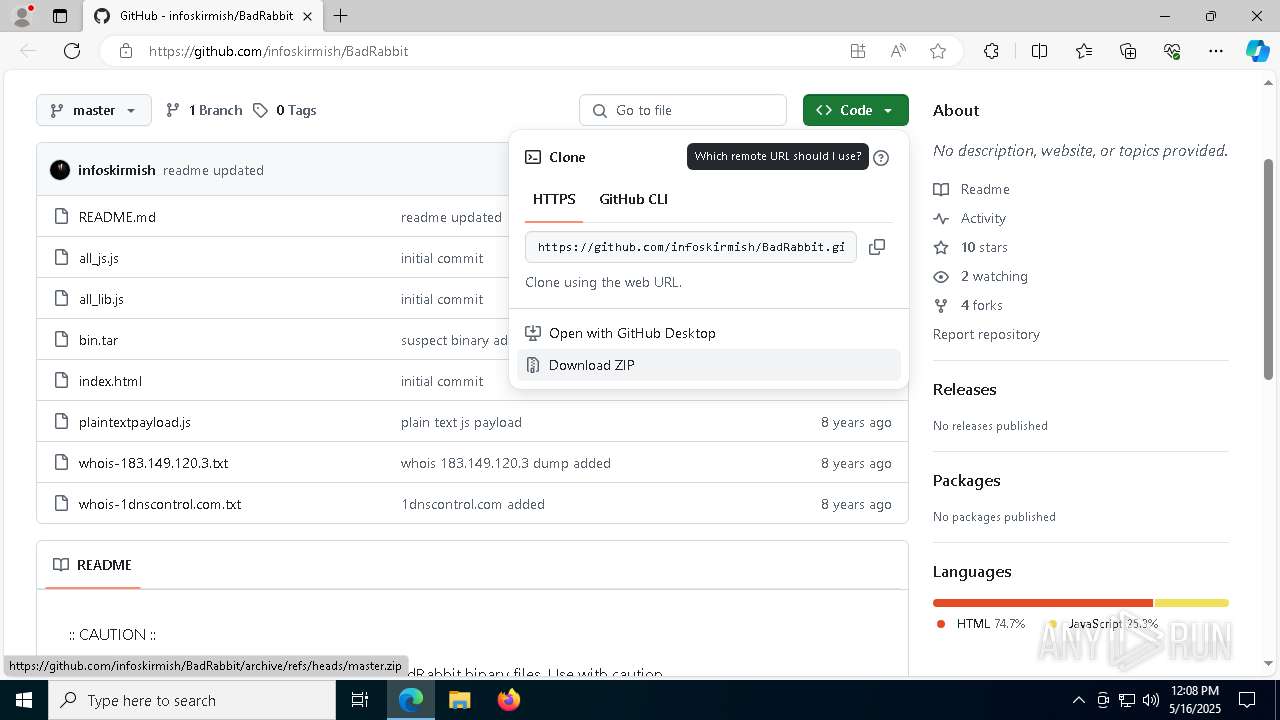
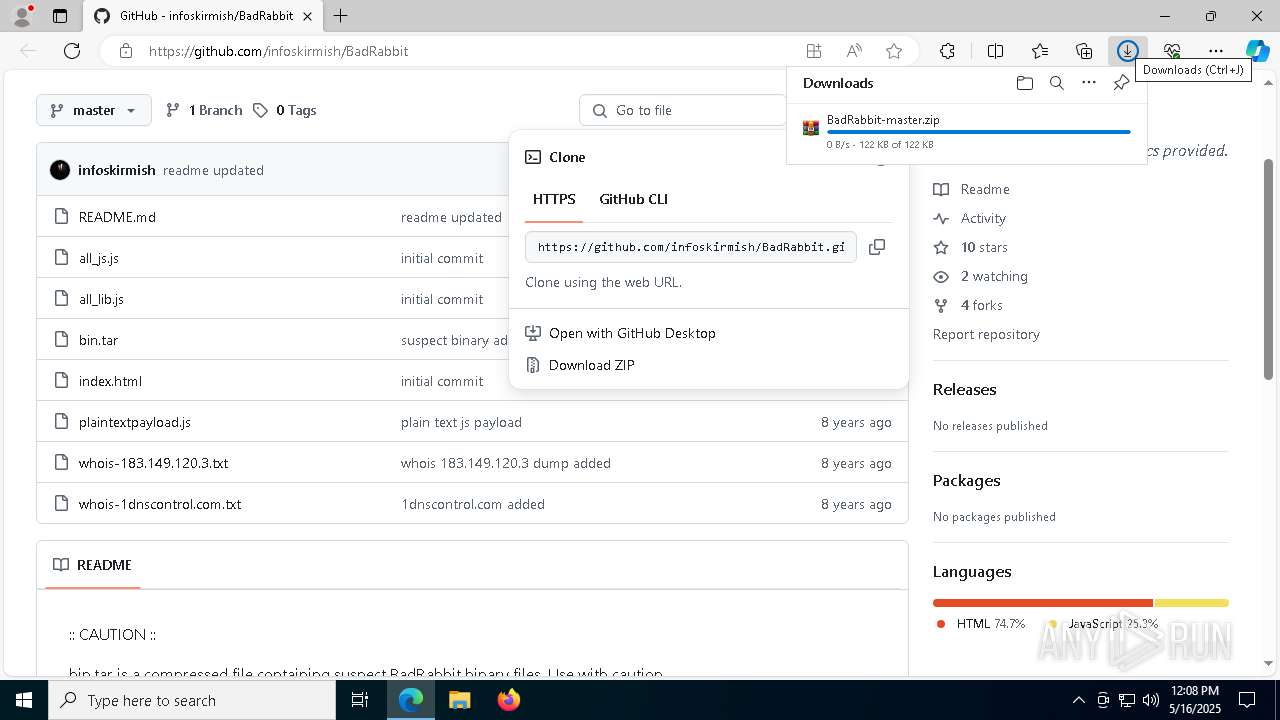
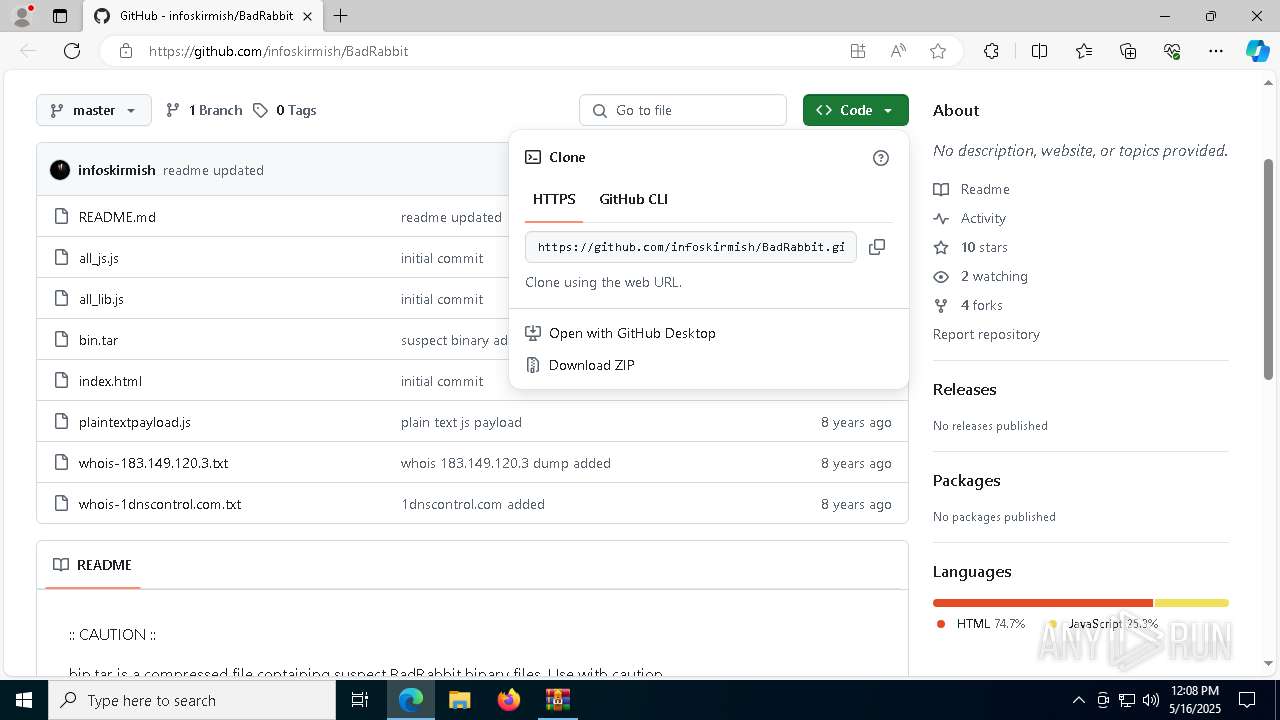
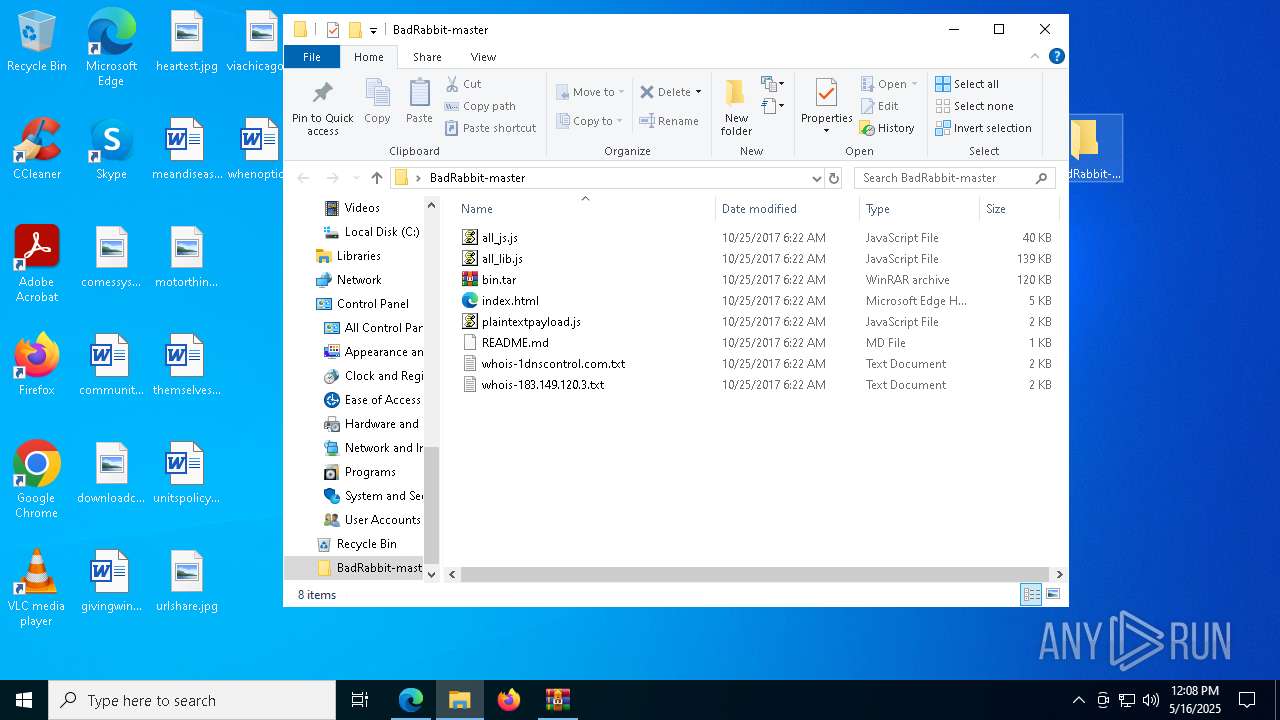
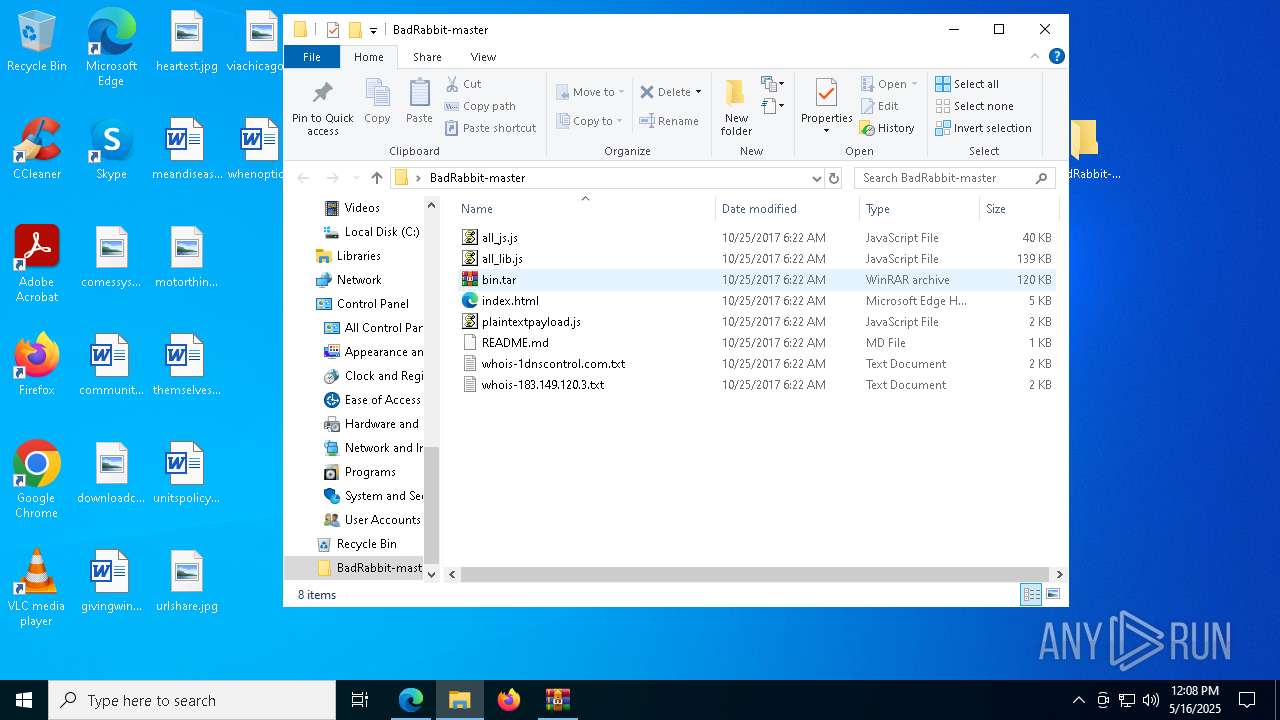
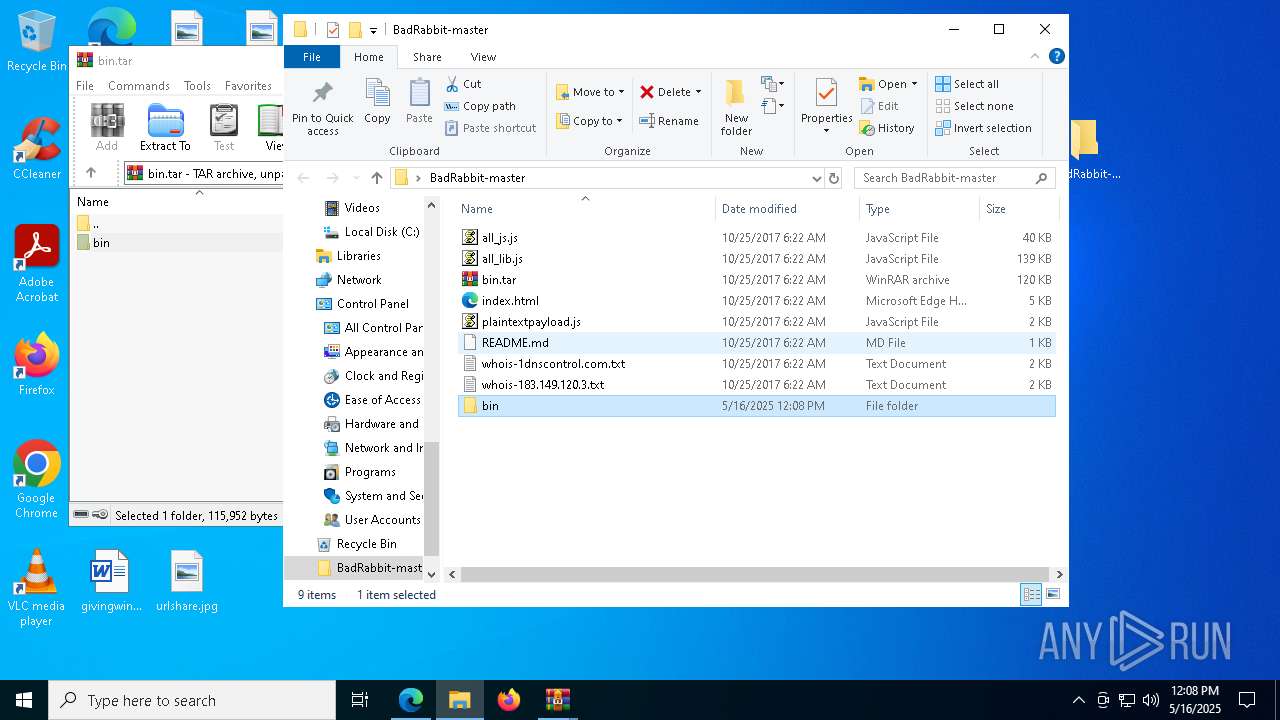
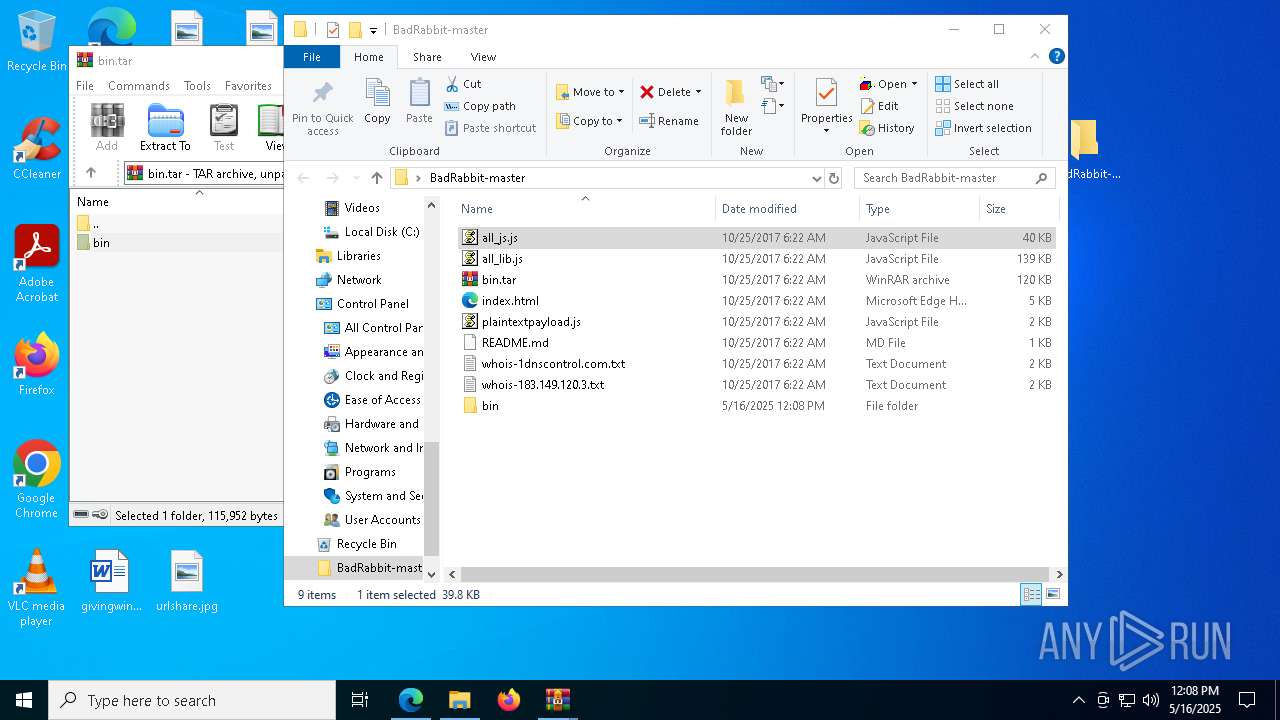
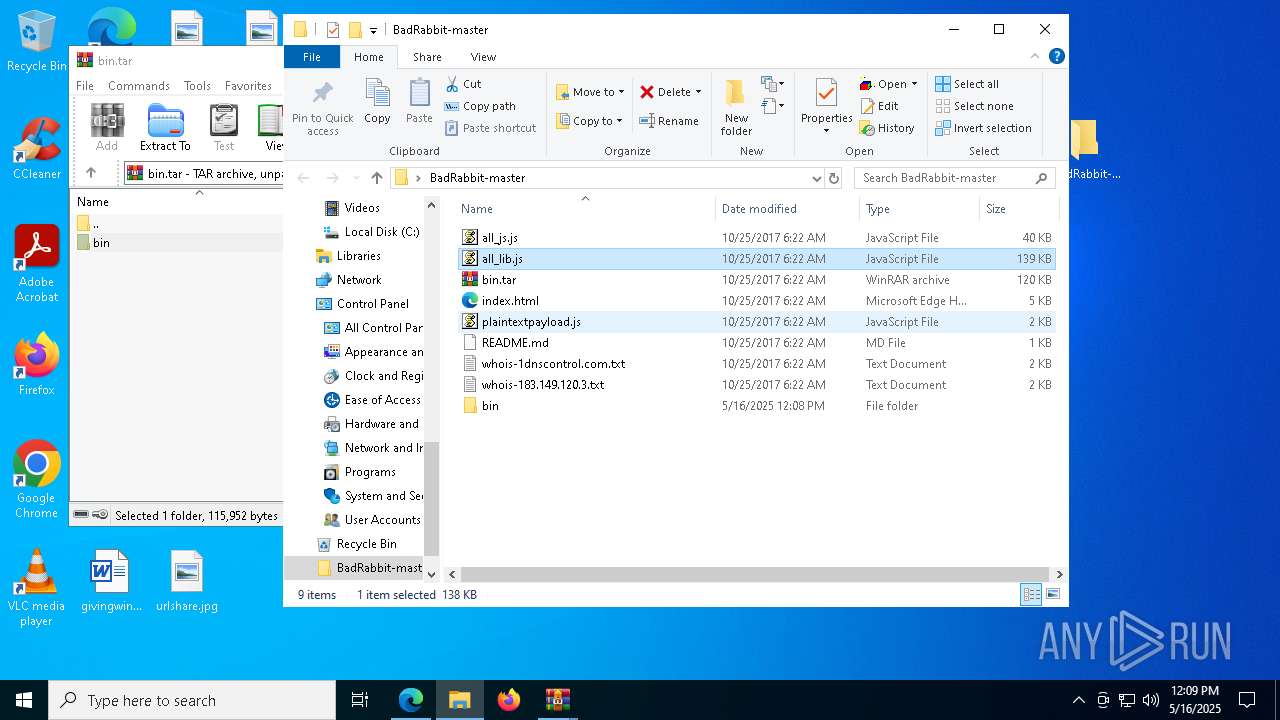
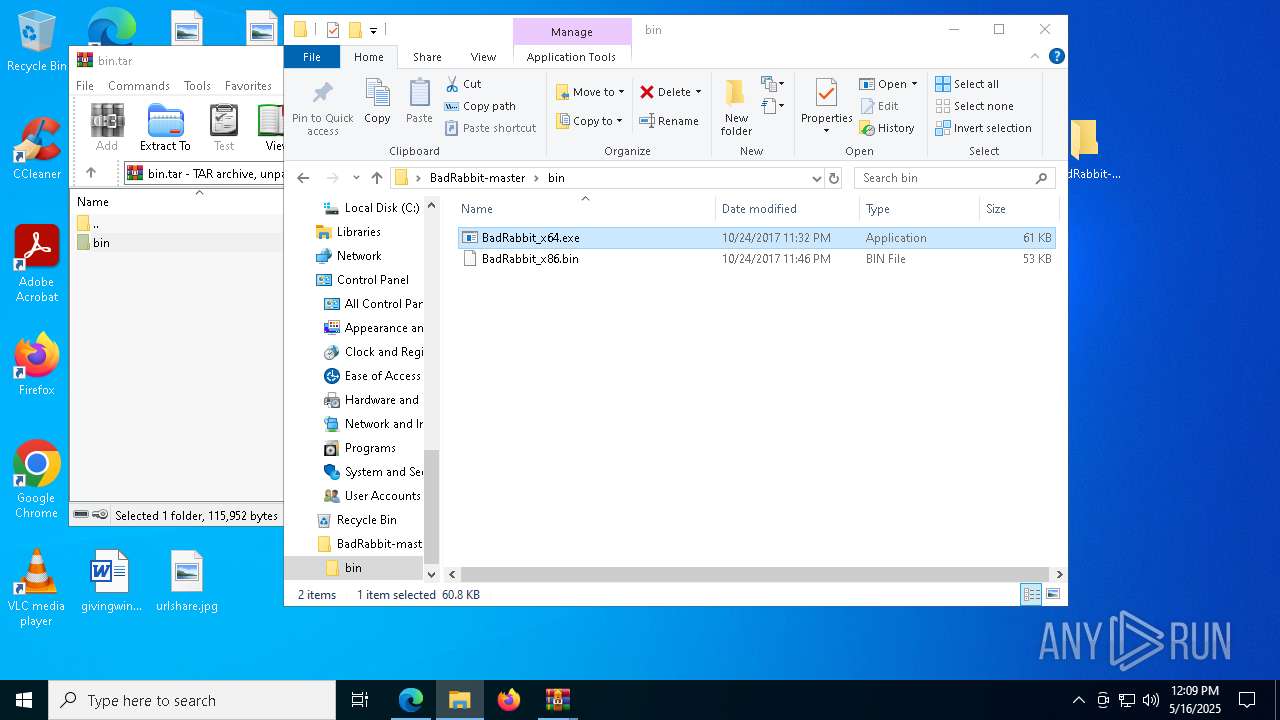
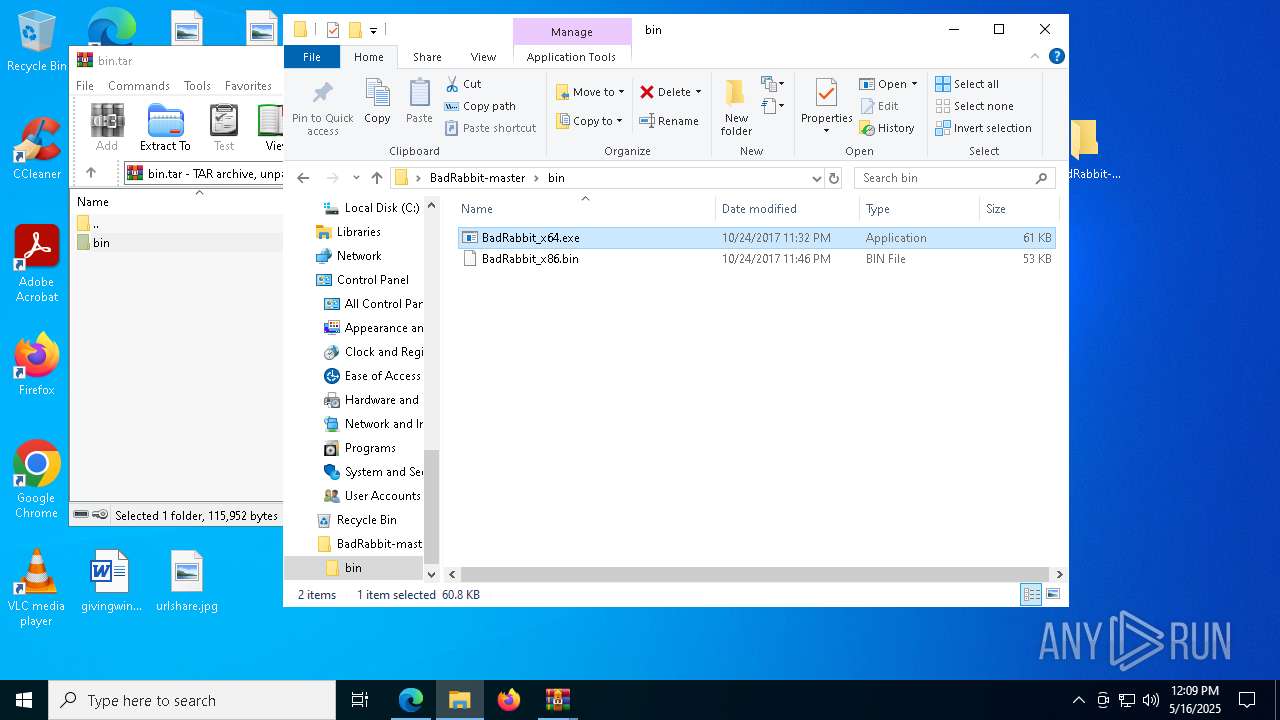
| URL: | https://github.com/infoskirmish/BadRabbit |
| Full analysis: | https://app.any.run/tasks/8cc61833-80ae-40af-a82d-c6ff6c9fd9a9 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 12:08:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E64A95031DBF9B748A80F1CF5C8EA3AE |
| SHA1: | AA70BEF04773DAEE7F0DF31E9AD353610A5EE3B1 |
| SHA256: | 320762C4FF42A36687E3881747BF06C8B1BE1ADB6D27CE0AFB9BDC2D3A3377BE |
| SSDEEP: | 3:N8tEd89r4n:2uq9cn |
MALICIOUS
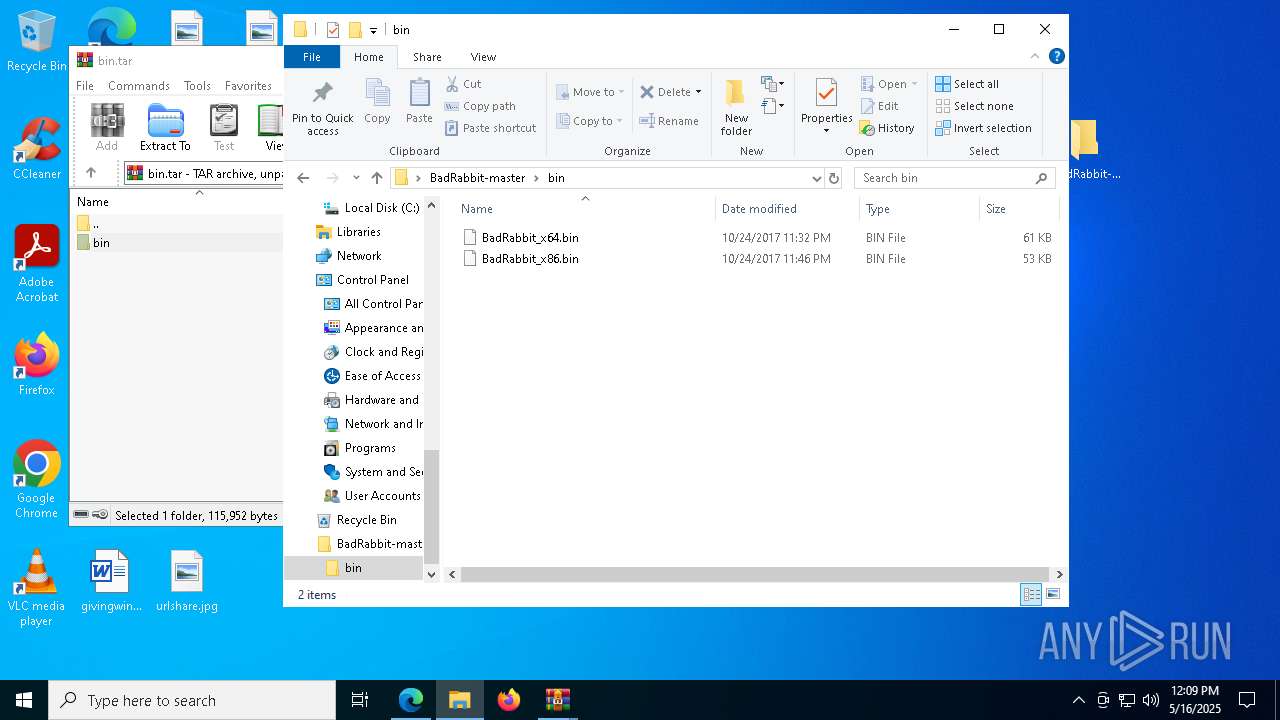
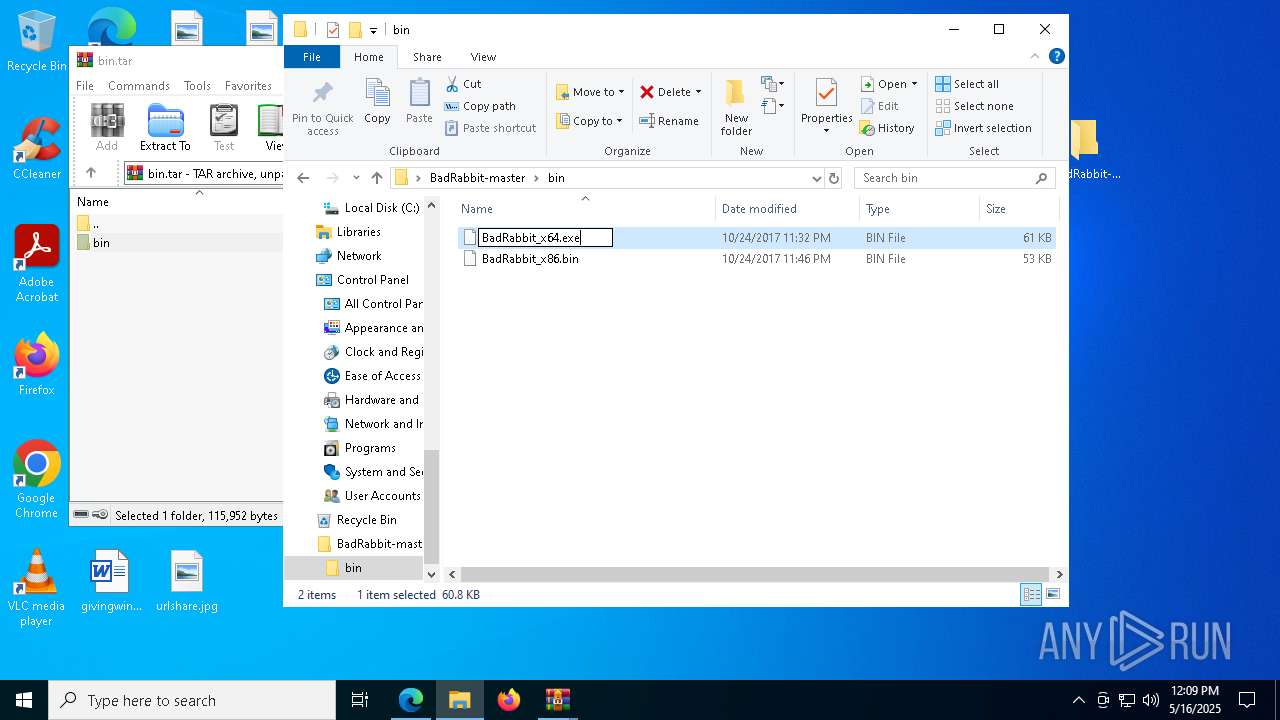
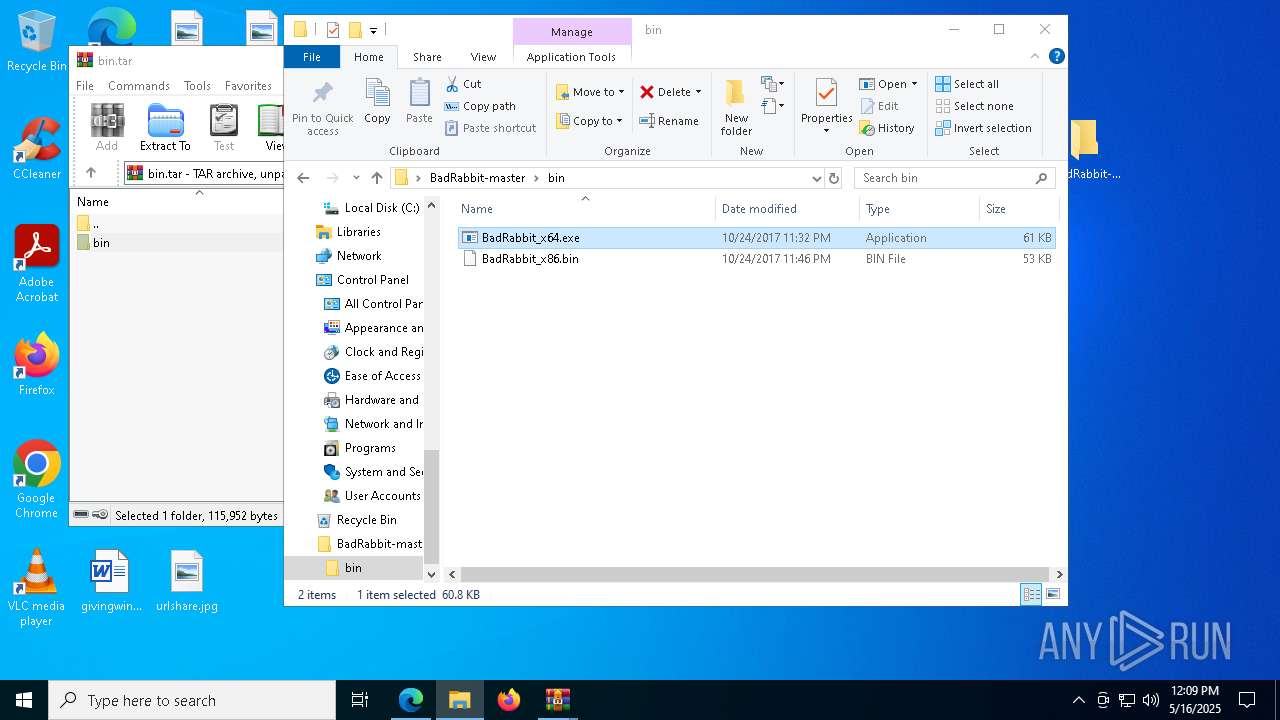
Executing a file with an untrusted certificate
- BadRabbit_x64.exe (PID: 5280)
- BadRabbit_x64.exe (PID: 6652)
- BadRabbit_x64.exe (PID: 4200)
- BadRabbit_x64.exe (PID: 3900)
- BadRabbit_x64.exe (PID: 5776)
- BadRabbit_x64.exe (PID: 5740)
- BadRabbit_x64.exe (PID: 7608)
- BadRabbit_x64.exe (PID: 5304)
- BadRabbit_x64.exe (PID: 4304)
- BadRabbit_x64.exe (PID: 4024)
- BadRabbit_x64.exe (PID: 7812)
- BadRabbit_x64.exe (PID: 7840)
- BadRabbit_x64.exe (PID: 3800)
- BadRabbit_x64.exe (PID: 1764)
- BadRabbit_x64.exe (PID: 4208)
- BadRabbit_x64.exe (PID: 7000)
- BadRabbit_x64.exe (PID: 1748)
- BadRabbit_x64.exe (PID: 2084)
- BadRabbit_x64.exe (PID: 7620)
- BadRabbit_x64.exe (PID: 1040)
- BadRabbit_x64.exe (PID: 4284)
- BadRabbit_x64.exe (PID: 684)
- BadRabbit_x64.exe (PID: 8052)
- BadRabbit_x64.exe (PID: 7240)
- BadRabbit_x64.exe (PID: 6004)
- BadRabbit_x64.exe (PID: 300)
- BadRabbit_x64.exe (PID: 1012)
- BadRabbit_x64.exe (PID: 7104)
- BadRabbit_x64.exe (PID: 6612)
- BadRabbit_x64.exe (PID: 5392)
- BadRabbit_x64.exe (PID: 6424)
- BadRabbit_x64.exe (PID: 7780)
- BadRabbit_x64.exe (PID: 7924)
- BadRabbit_x64.exe (PID: 736)
- BadRabbit_x64.exe (PID: 1512)
- BadRabbit_x64.exe (PID: 6960)
- BadRabbit_x64.exe (PID: 1616)
- BadRabbit_x64.exe (PID: 5452)
- BadRabbit_x64.exe (PID: 7832)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- msedge.exe (PID: 7148)
Checks supported languages
- identity_helper.exe (PID: 8096)
Reads the computer name
- identity_helper.exe (PID: 8096)
Reads Environment values
- identity_helper.exe (PID: 8096)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7148)
- OpenWith.exe (PID: 4608)
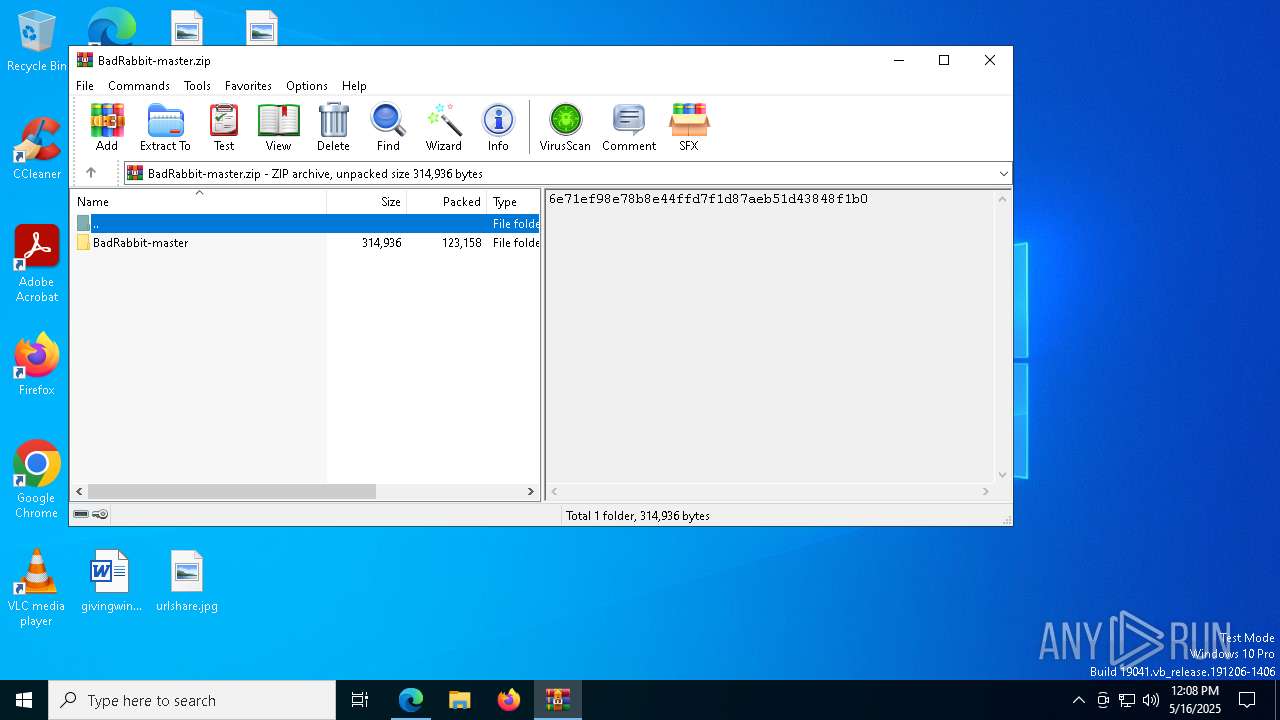
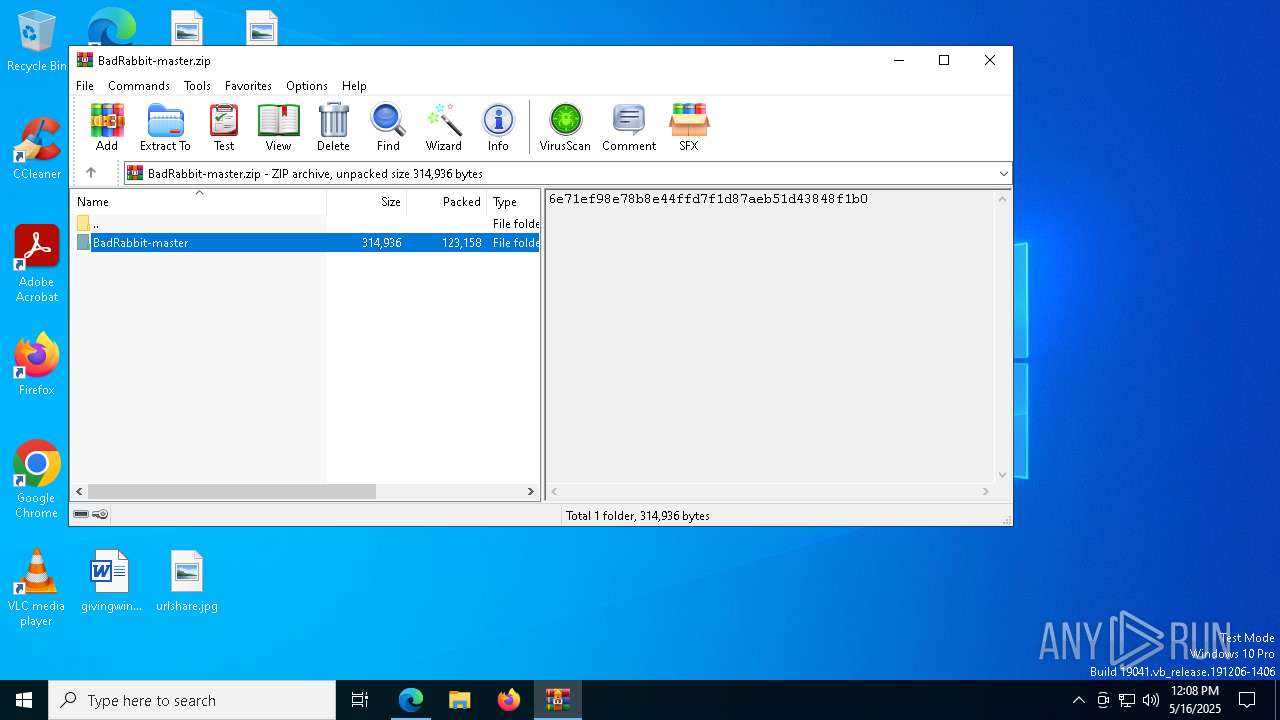
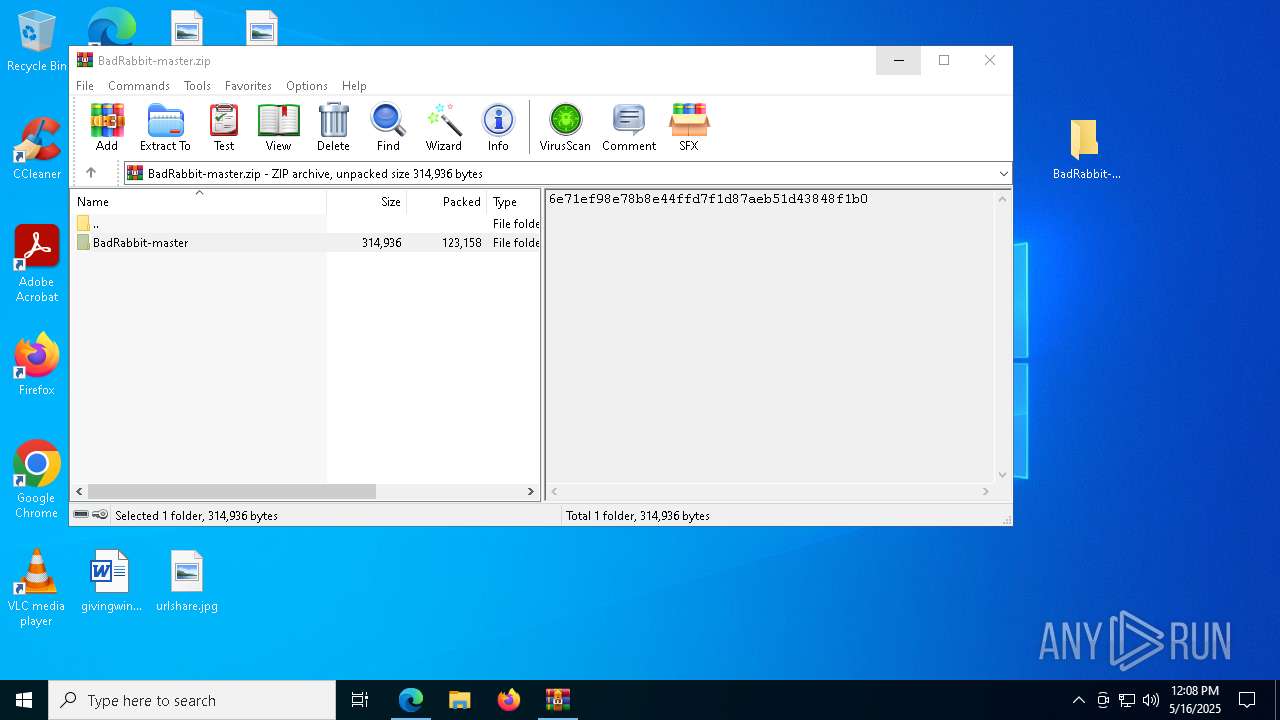
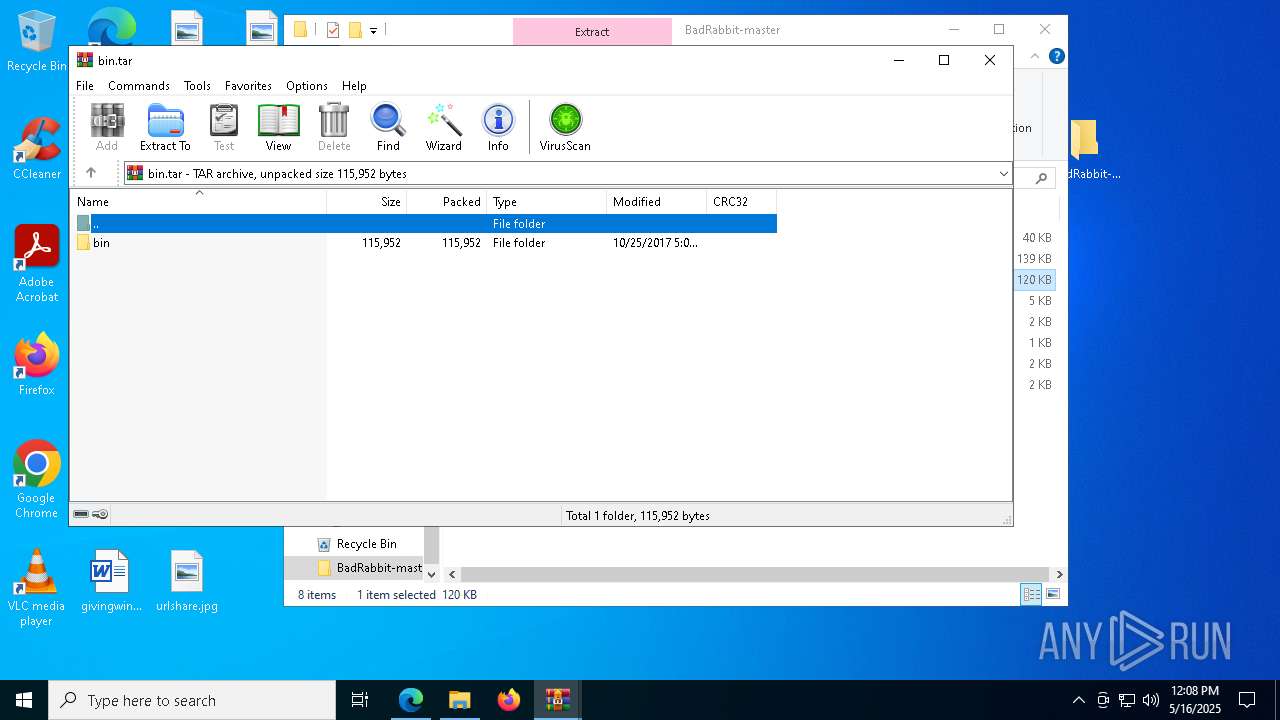
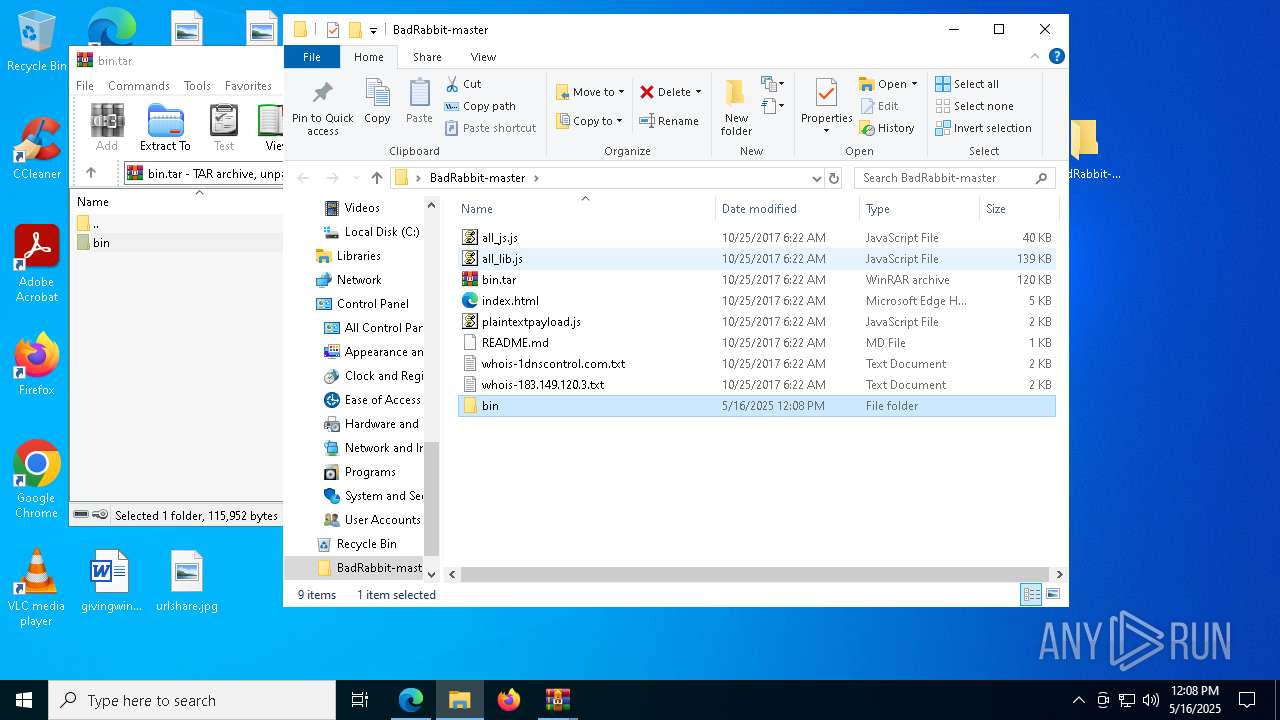
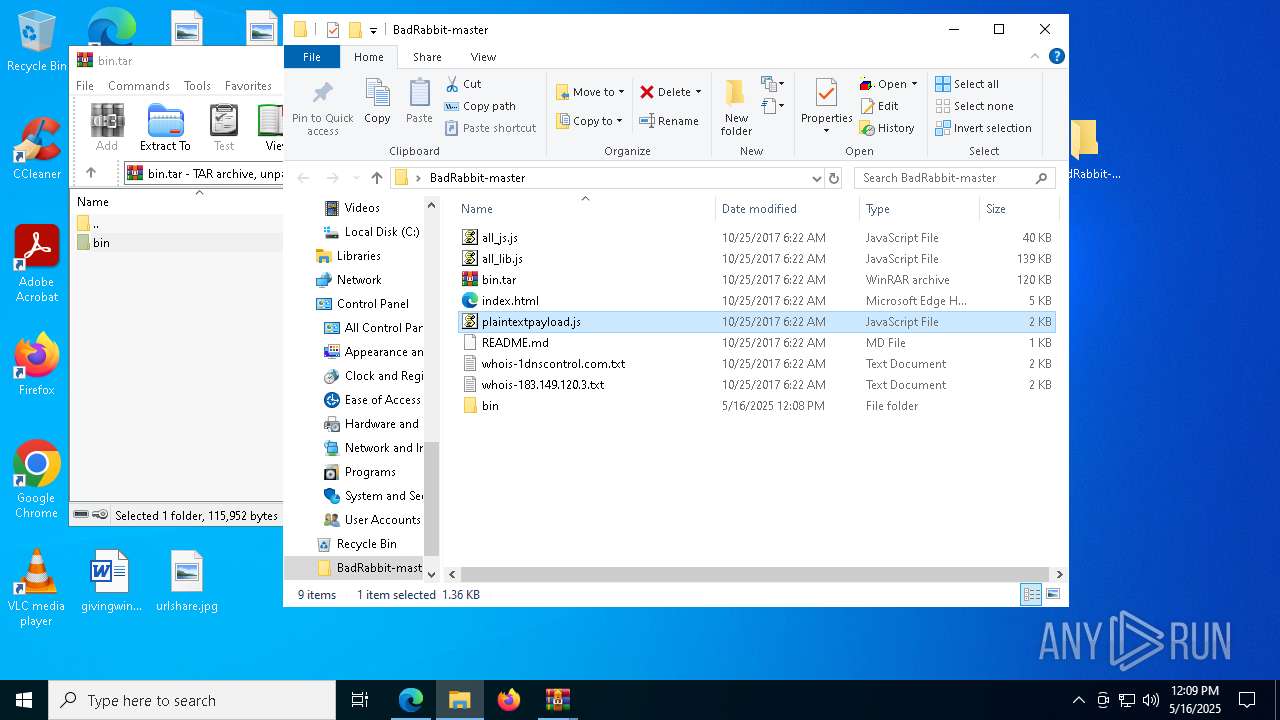
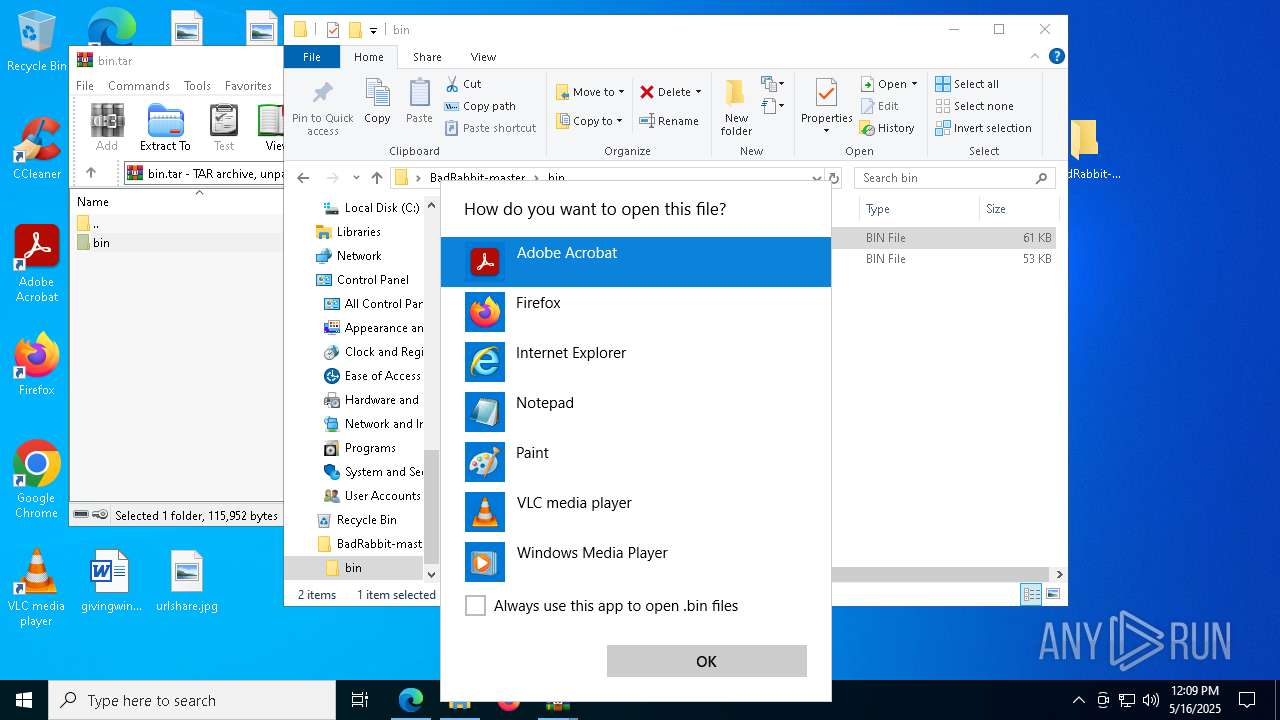
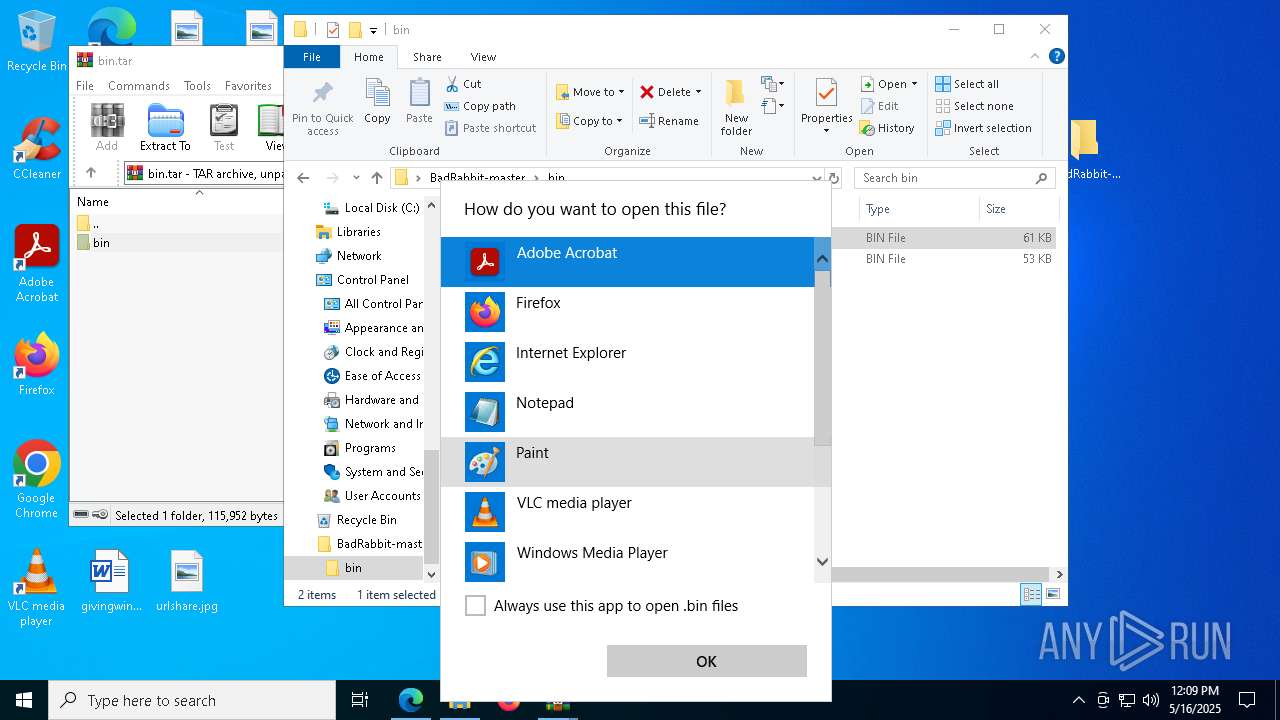
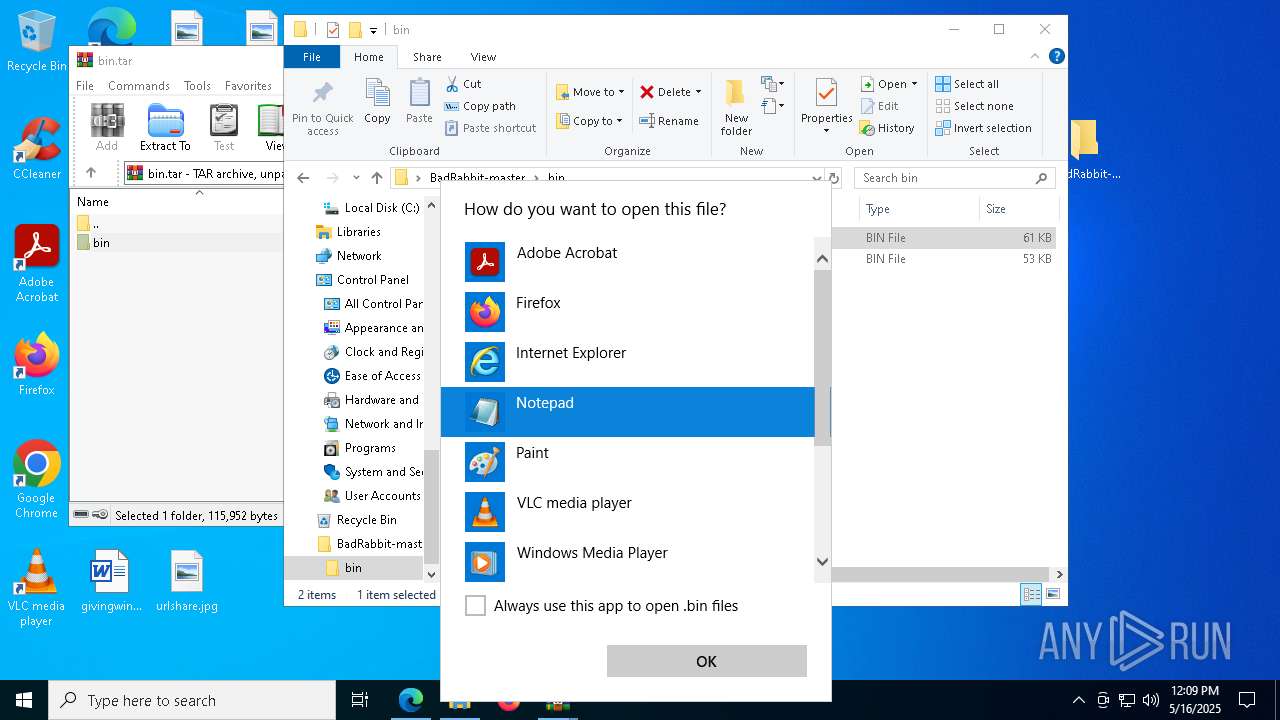
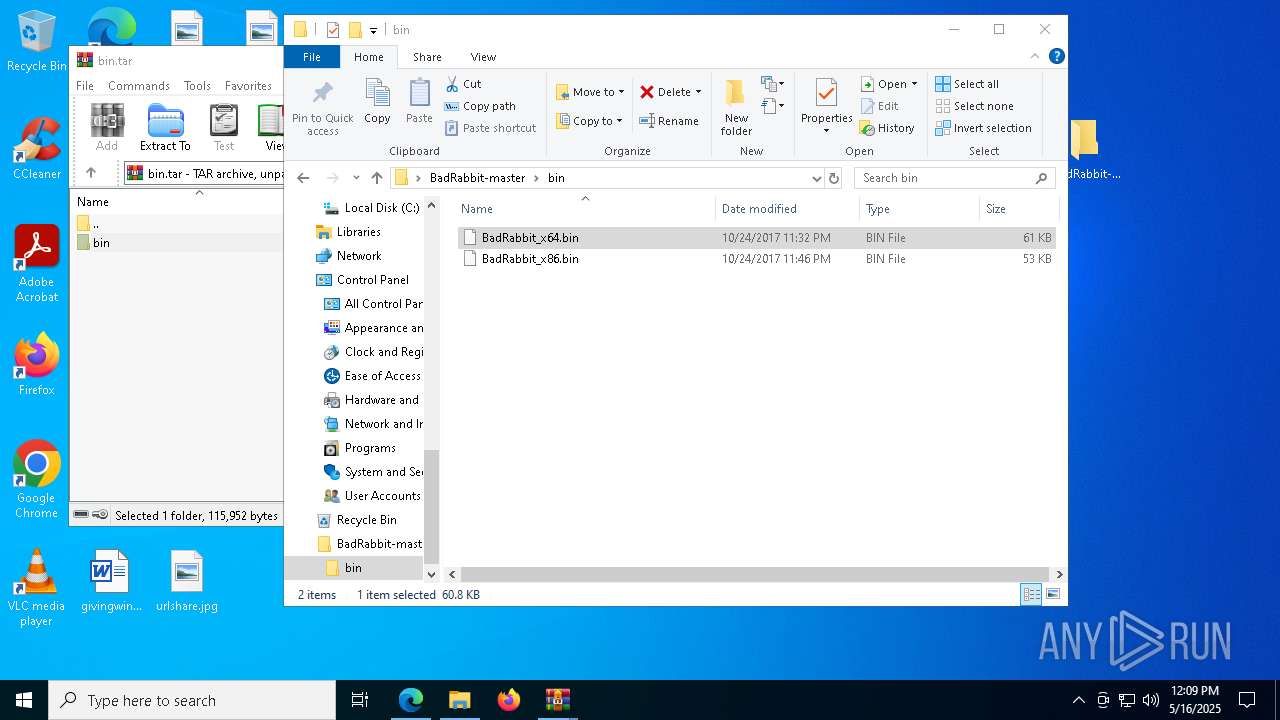
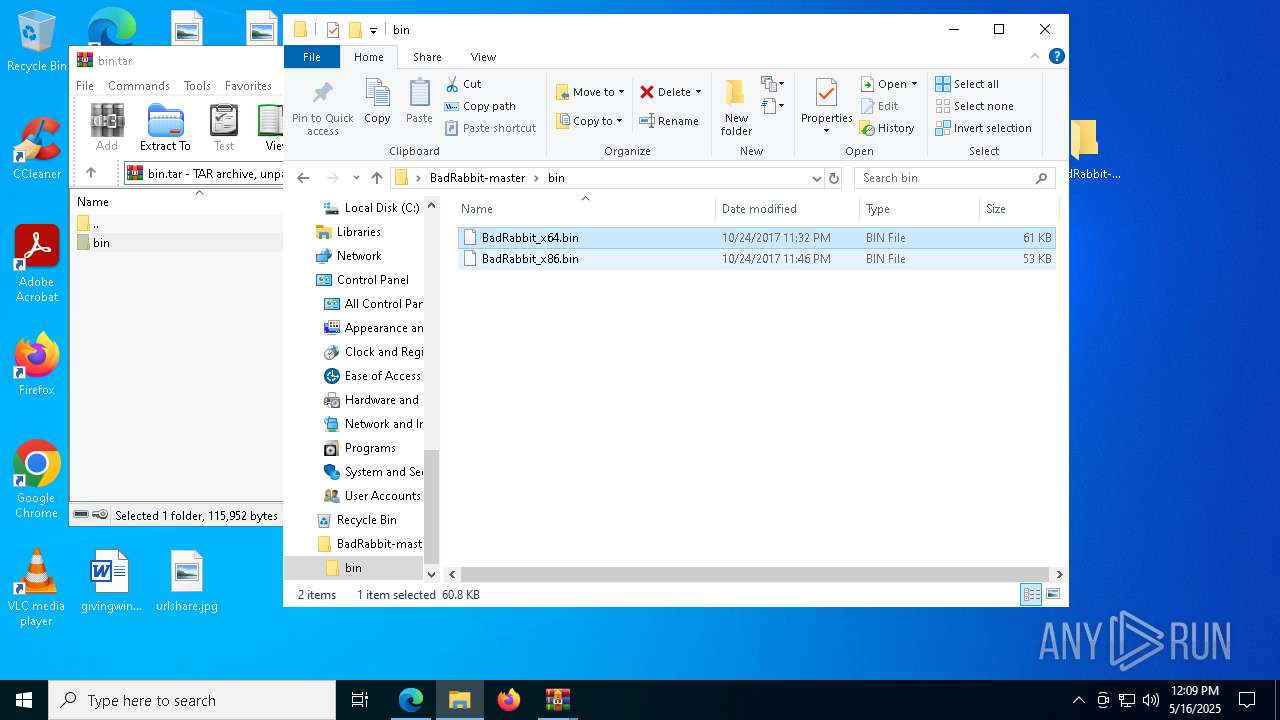
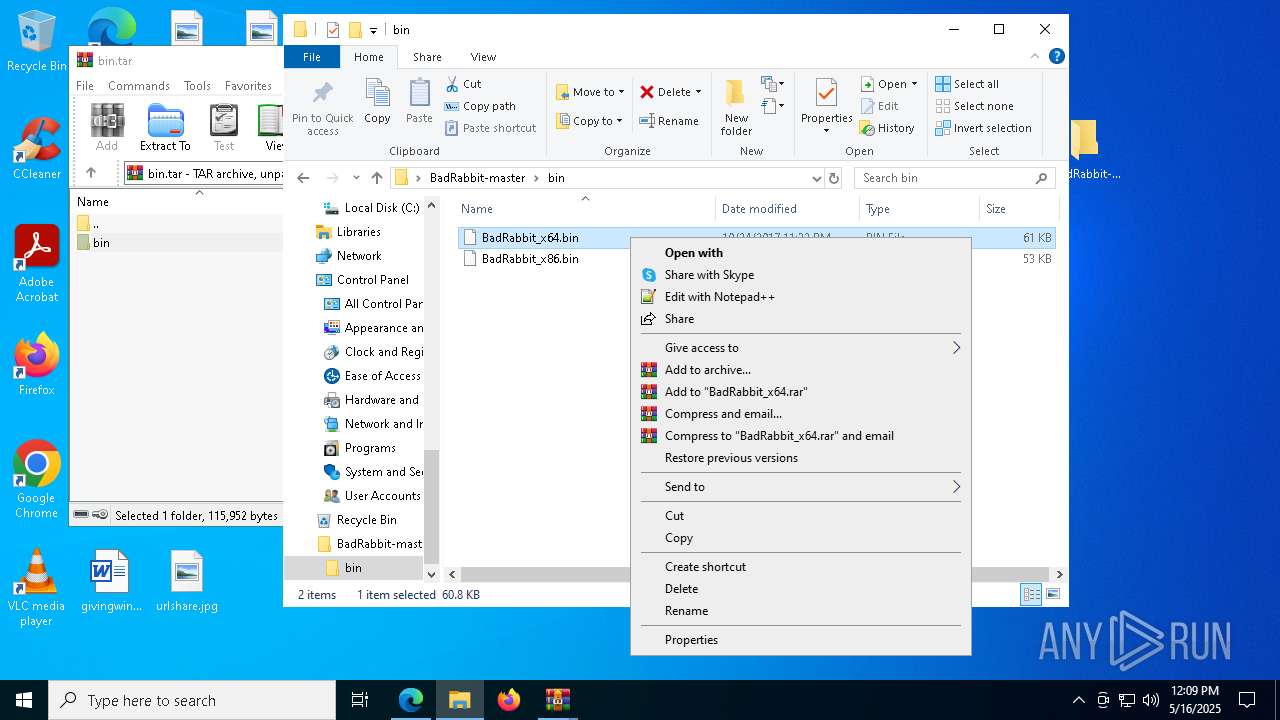
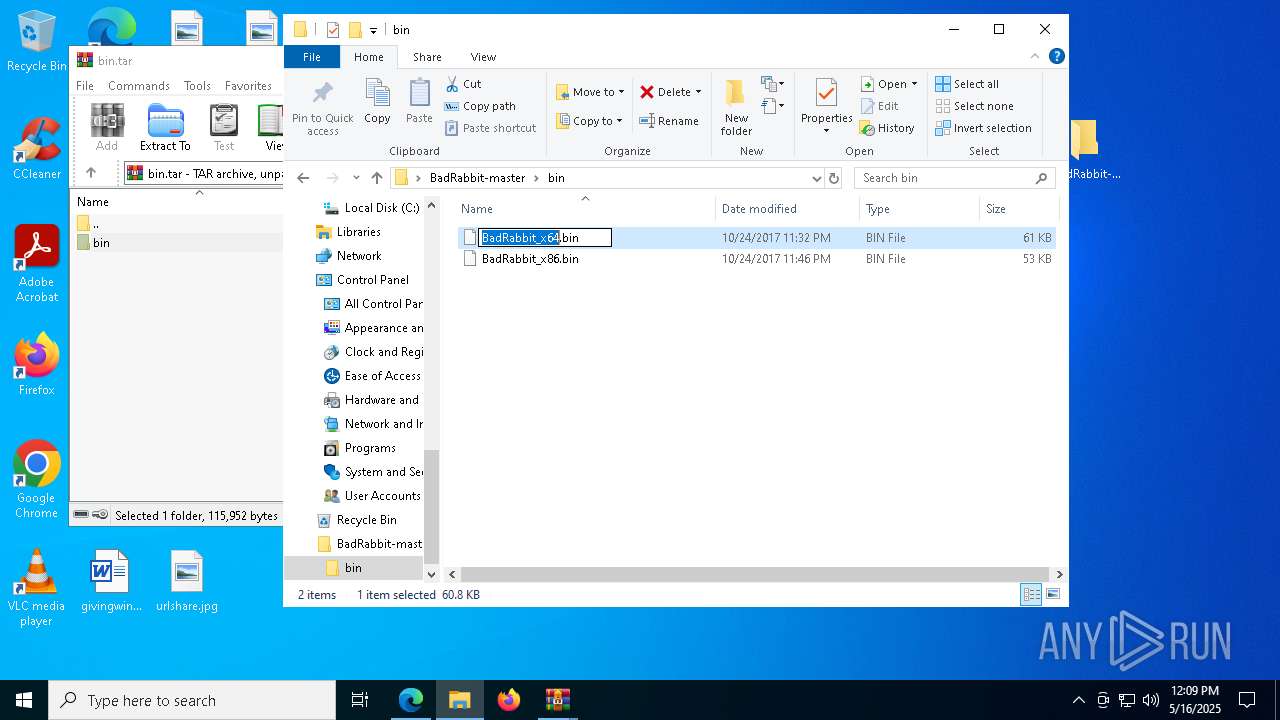
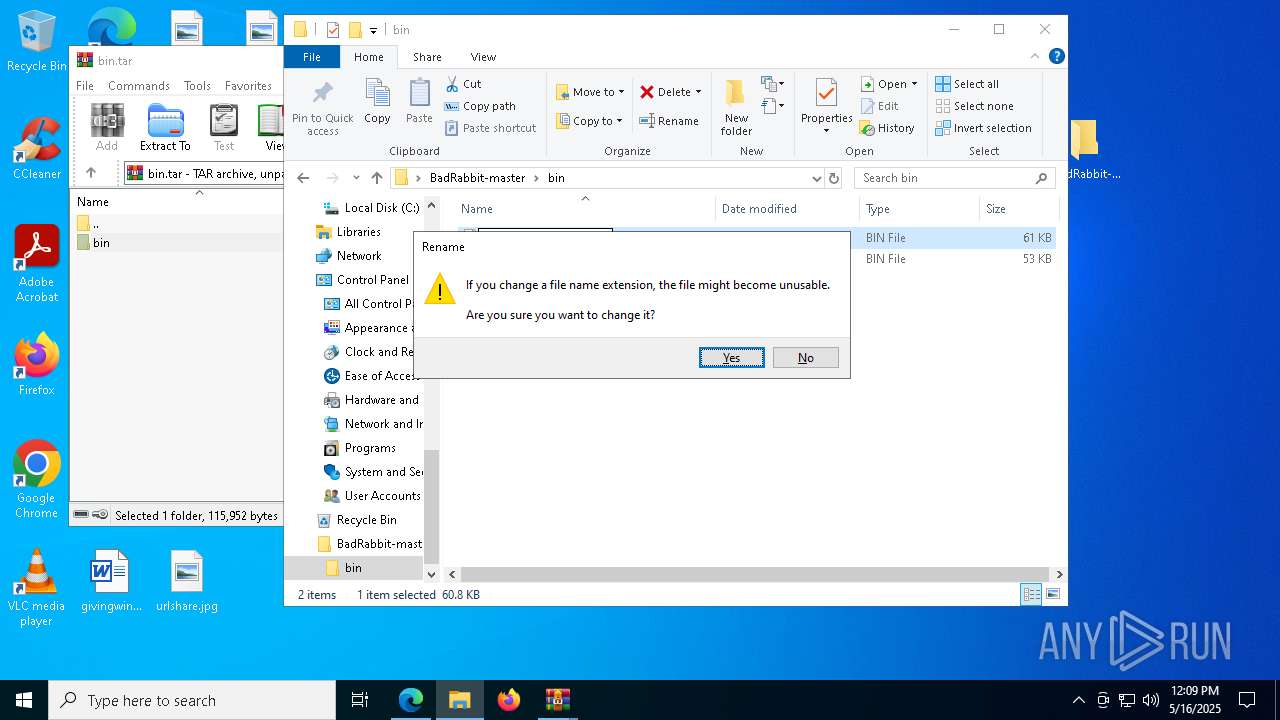
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4336)
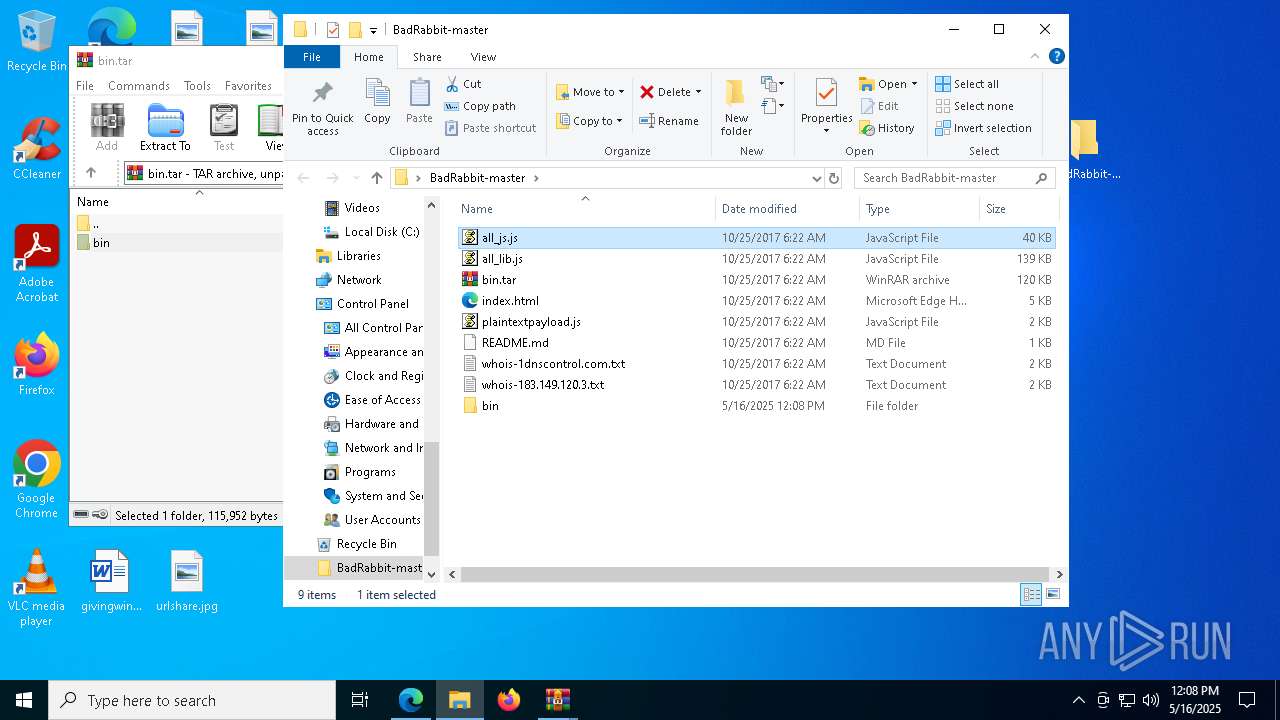
Manual execution by a user
- WinRAR.exe (PID: 4336)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 3888)
- wscript.exe (PID: 7616)
- BadRabbit_x64.exe (PID: 5776)
- BadRabbit_x64.exe (PID: 5280)
- BadRabbit_x64.exe (PID: 6652)
- BadRabbit_x64.exe (PID: 4200)
- BadRabbit_x64.exe (PID: 7608)
- BadRabbit_x64.exe (PID: 3900)
- BadRabbit_x64.exe (PID: 5740)
- BadRabbit_x64.exe (PID: 7000)
- BadRabbit_x64.exe (PID: 7812)
- BadRabbit_x64.exe (PID: 5304)
- BadRabbit_x64.exe (PID: 4304)
- BadRabbit_x64.exe (PID: 7840)
- BadRabbit_x64.exe (PID: 4024)
- BadRabbit_x64.exe (PID: 3800)
- BadRabbit_x64.exe (PID: 1764)
- BadRabbit_x64.exe (PID: 4208)
- BadRabbit_x64.exe (PID: 2084)
- BadRabbit_x64.exe (PID: 1012)
- BadRabbit_x64.exe (PID: 1040)
- BadRabbit_x64.exe (PID: 4284)
- BadRabbit_x64.exe (PID: 684)
- BadRabbit_x64.exe (PID: 7620)
- BadRabbit_x64.exe (PID: 8052)
- BadRabbit_x64.exe (PID: 7240)
- BadRabbit_x64.exe (PID: 6004)
- BadRabbit_x64.exe (PID: 1748)
- BadRabbit_x64.exe (PID: 5392)
- BadRabbit_x64.exe (PID: 6612)
- BadRabbit_x64.exe (PID: 6424)
- BadRabbit_x64.exe (PID: 7780)
- BadRabbit_x64.exe (PID: 7924)
- BadRabbit_x64.exe (PID: 7104)
- BadRabbit_x64.exe (PID: 1512)
- BadRabbit_x64.exe (PID: 6960)
- BadRabbit_x64.exe (PID: 736)
- BadRabbit_x64.exe (PID: 300)
- BadRabbit_x64.exe (PID: 1616)
- BadRabbit_x64.exe (PID: 7832)
- BadRabbit_x64.exe (PID: 5452)
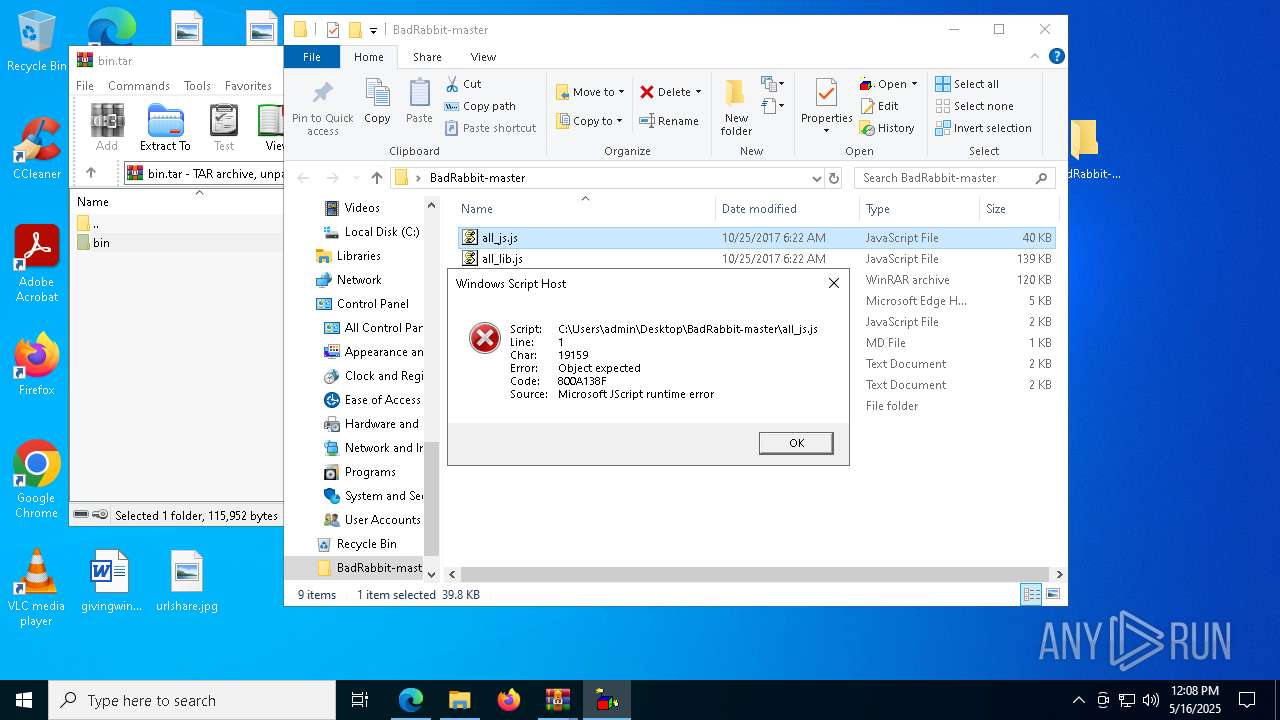
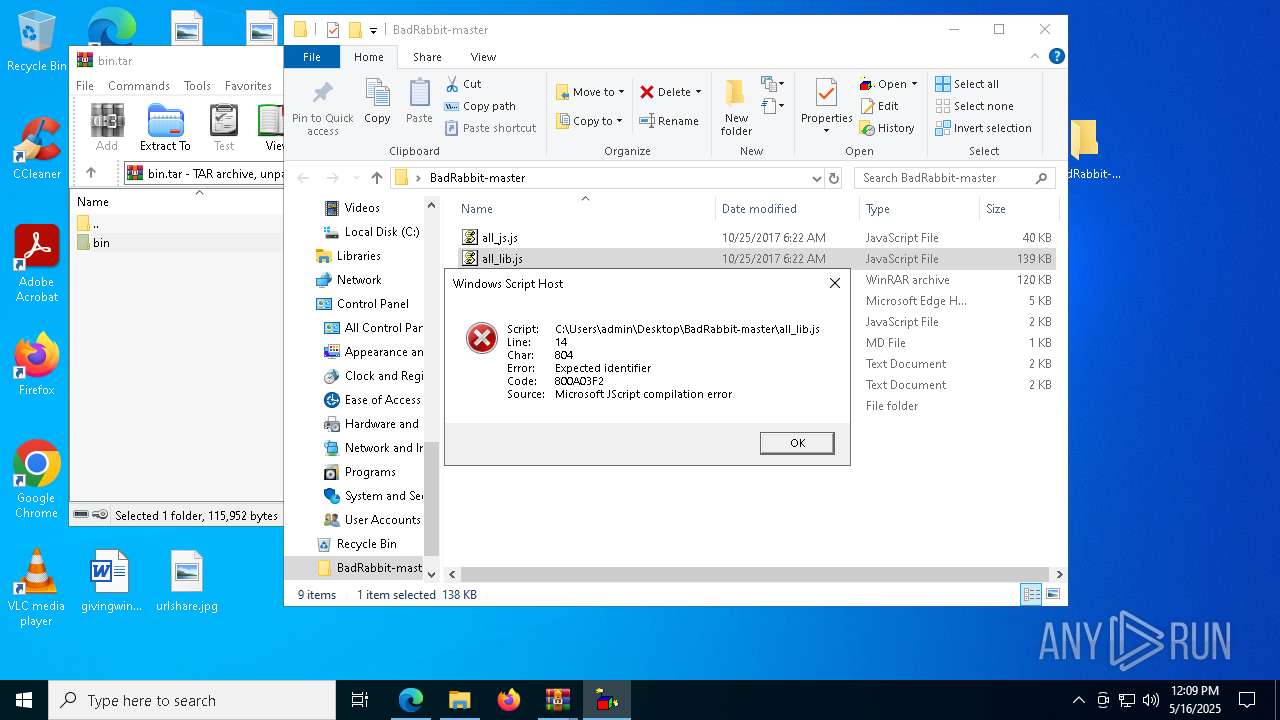
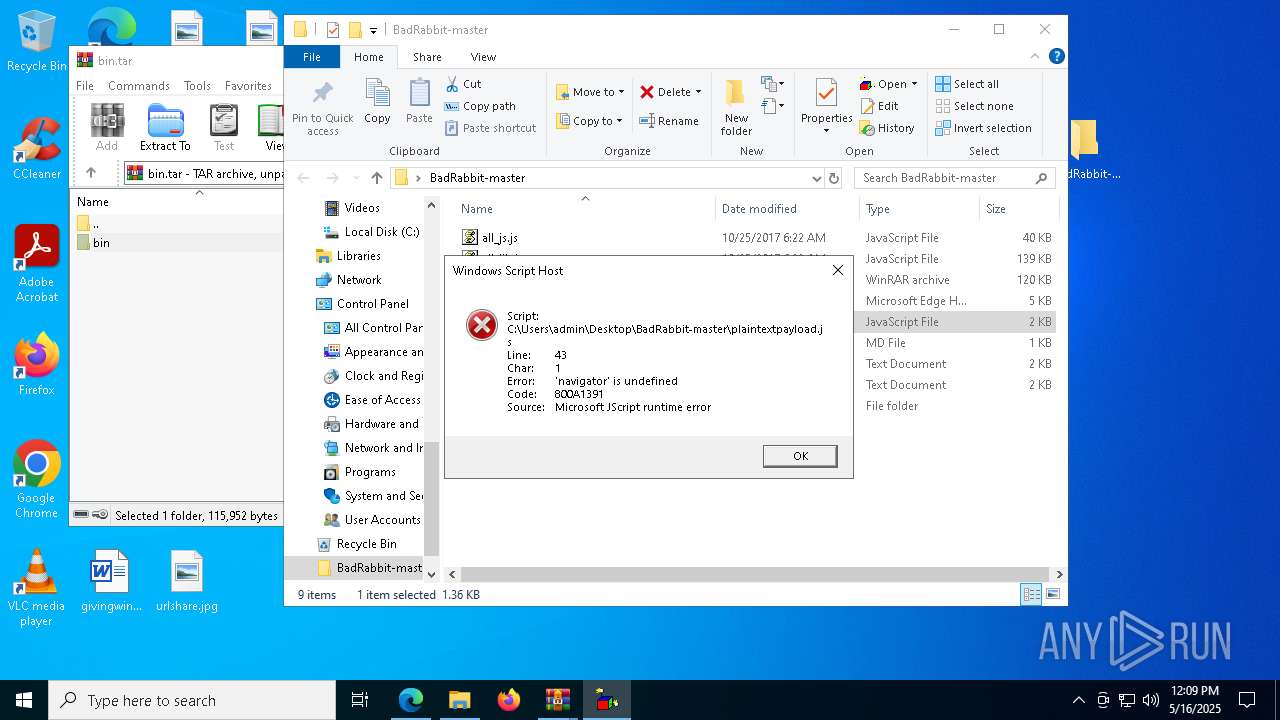
JScript runtime error (SCRIPT)
- wscript.exe (PID: 2908)
- wscript.exe (PID: 7616)
Reads the software policy settings
- slui.exe (PID: 5176)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4724)
- OpenWith.exe (PID: 4608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
261
Monitored processes
128
Malicious processes
0
Suspicious processes
39
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe" | C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BadRabbit_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BadRabbit_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe" | C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BadRabbit_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe" | C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BadRabbit_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | BadRabbit_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe" | C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe" | C:\Users\admin\Desktop\BadRabbit-master\bin\BadRabbit_x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
11 738
Read events
11 700
Write events
38
Delete events
0
Modification events
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A8AC72EBD5932F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F0057BEBD5932F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656046 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FCB5DF26-095F-4D35-B41A-0A83A5884D1C} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656046 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E90F4950-3A01-4B63-A715-C8D55A9098A7} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656046 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BB86F709-4943-4DA7-9A69-A78363045EFD} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656046 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {120507AE-3B0E-42E9-AF91-AA45B245E64A} | |||
Executable files
8
Suspicious files
206
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6af.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b6af.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b6af.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6ee.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
67
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
780 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747698237&P2=404&P3=2&P4=TuWoofbuVQBQ%2f4QHfqclnTrY15Z0EpgB5wKD5lFWAvF8jsR74E9y9ZNx8KmHYAvStF0a6BoKNbYZuNicX2jemA%3d%3d | unknown | — | — | whitelisted |
780 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747698237&P2=404&P3=2&P4=TuWoofbuVQBQ%2f4QHfqclnTrY15Z0EpgB5wKD5lFWAvF8jsR74E9y9ZNx8KmHYAvStF0a6BoKNbYZuNicX2jemA%3d%3d | unknown | — | — | whitelisted |
780 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747698237&P2=404&P3=2&P4=TuWoofbuVQBQ%2f4QHfqclnTrY15Z0EpgB5wKD5lFWAvF8jsR74E9y9ZNx8KmHYAvStF0a6BoKNbYZuNicX2jemA%3d%3d | unknown | — | — | whitelisted |
780 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747698237&P2=404&P3=2&P4=TuWoofbuVQBQ%2f4QHfqclnTrY15Z0EpgB5wKD5lFWAvF8jsR74E9y9ZNx8KmHYAvStF0a6BoKNbYZuNicX2jemA%3d%3d | unknown | — | — | whitelisted |
780 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747698237&P2=404&P3=2&P4=TuWoofbuVQBQ%2f4QHfqclnTrY15Z0EpgB5wKD5lFWAvF8jsR74E9y9ZNx8KmHYAvStF0a6BoKNbYZuNicX2jemA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7148 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7312 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |