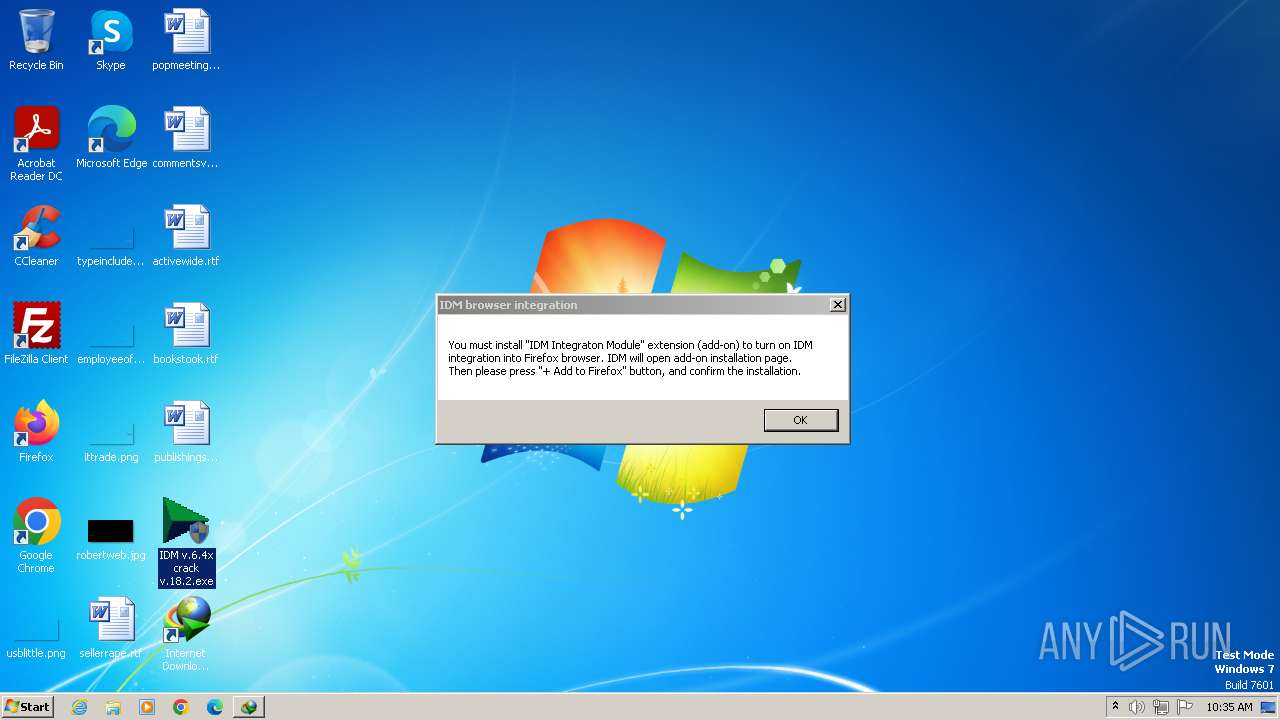
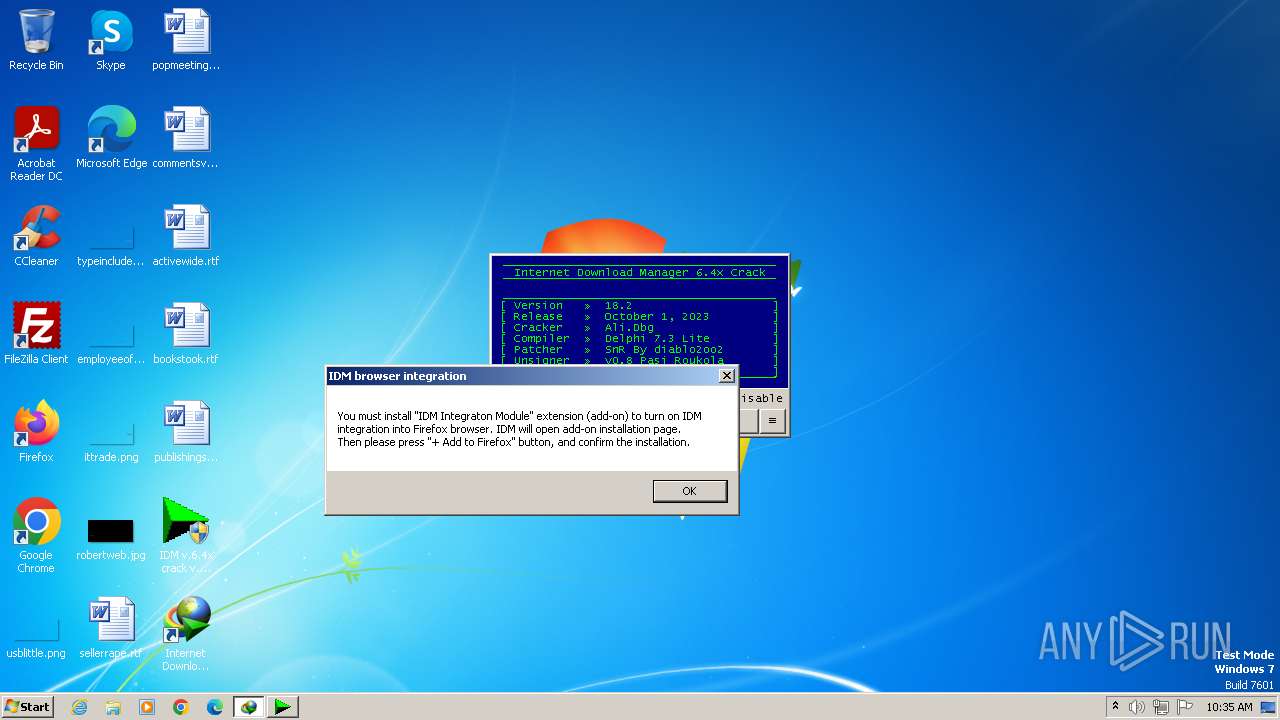
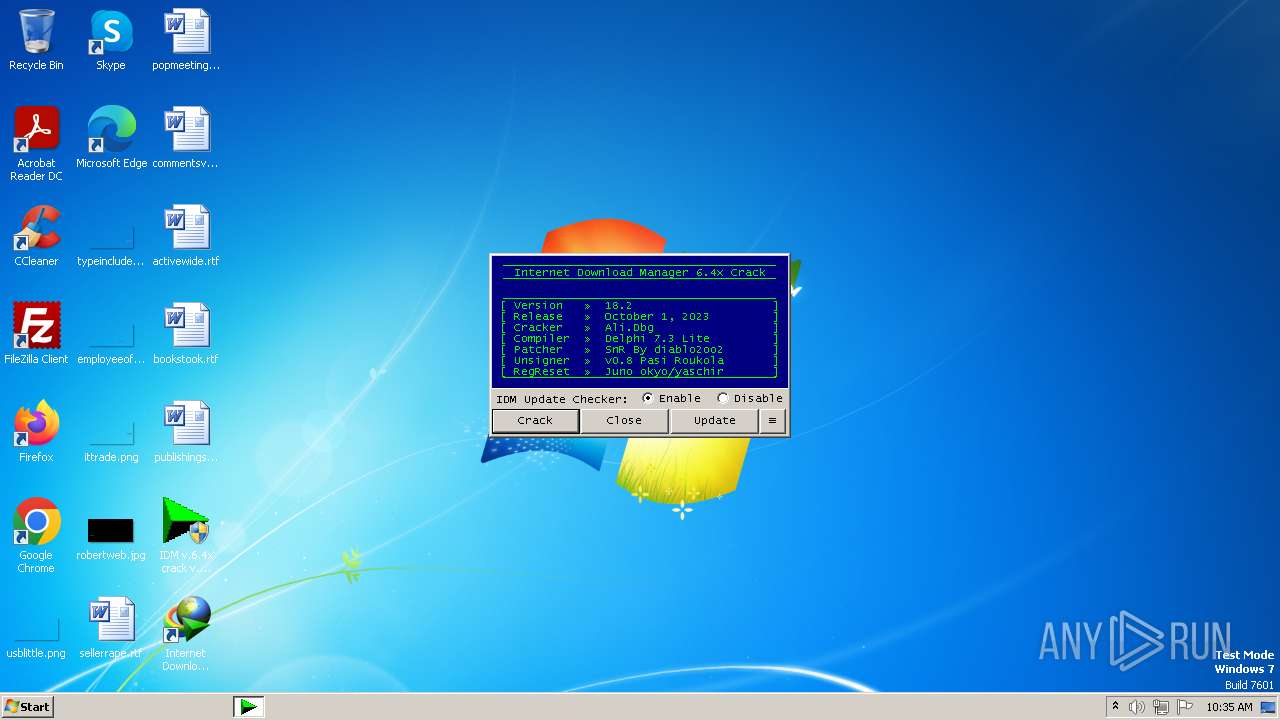
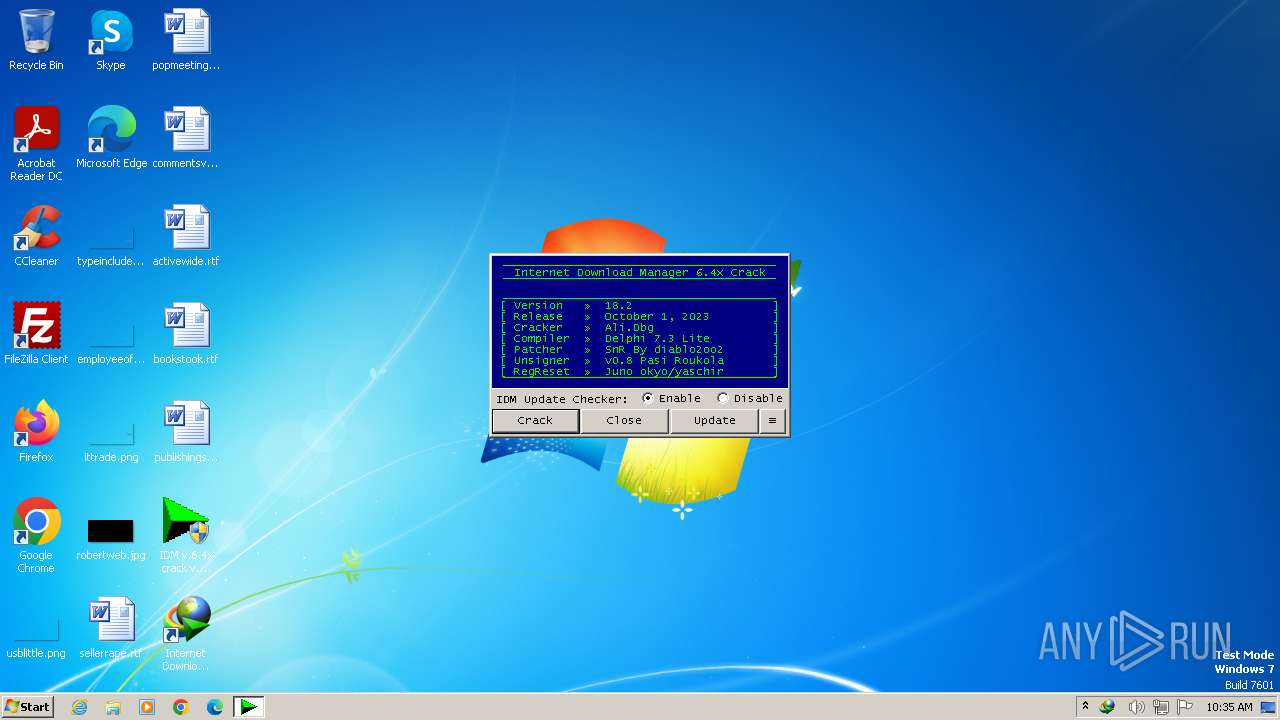
| File name: | IDM v.6.4x crack v.18.2.exe |
| Full analysis: | https://app.any.run/tasks/7f6616d1-176d-4065-853d-037750e21643 |
| Verdict: | Malicious activity |
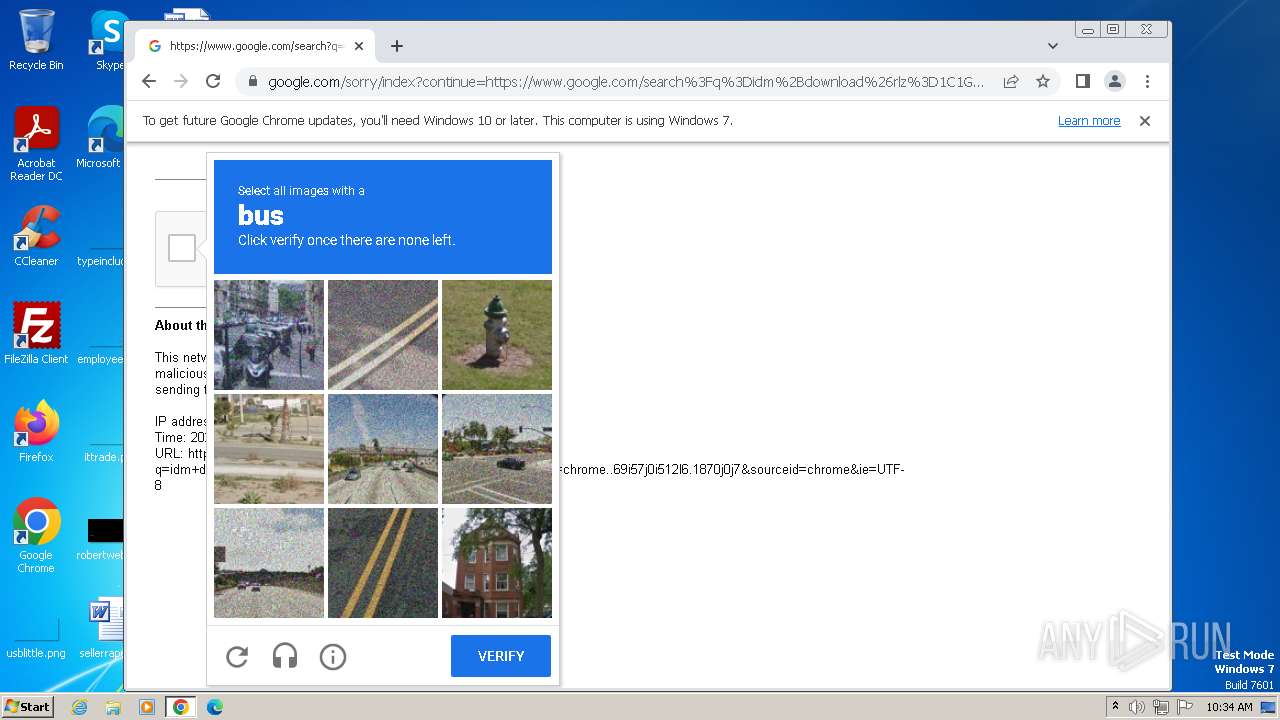
| Analysis date: | November 03, 2023, 10:33:26 |
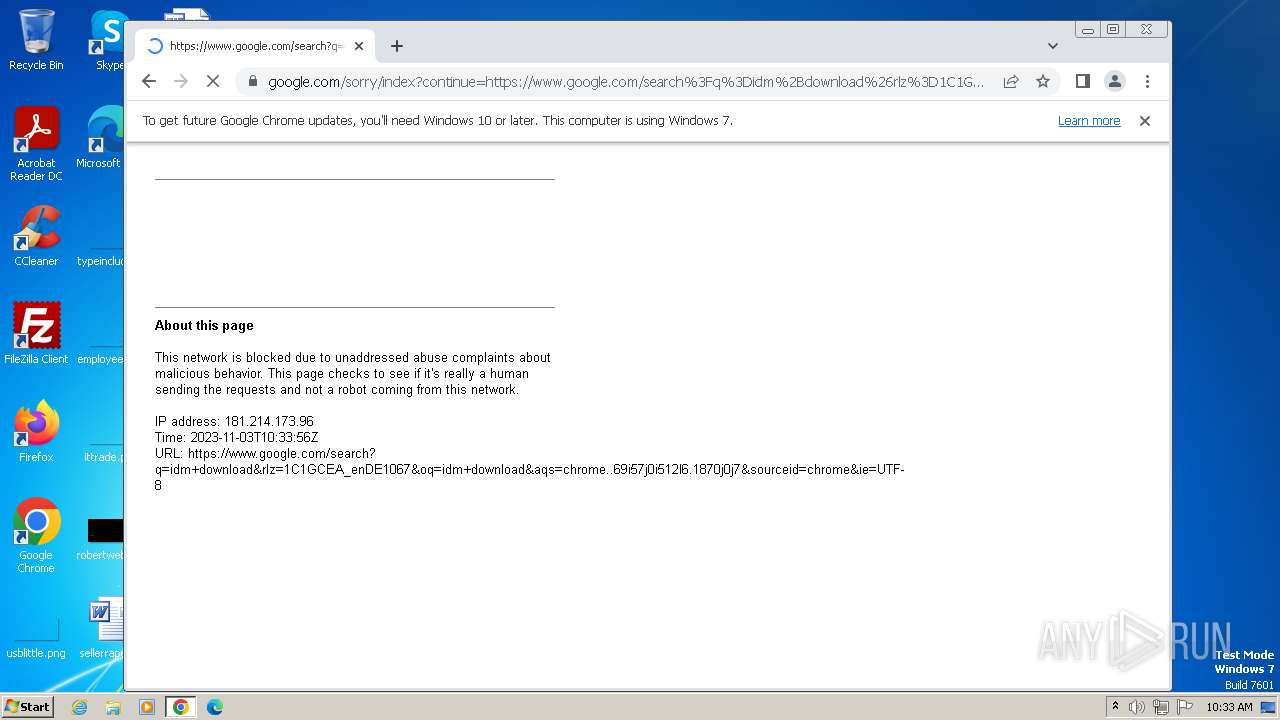
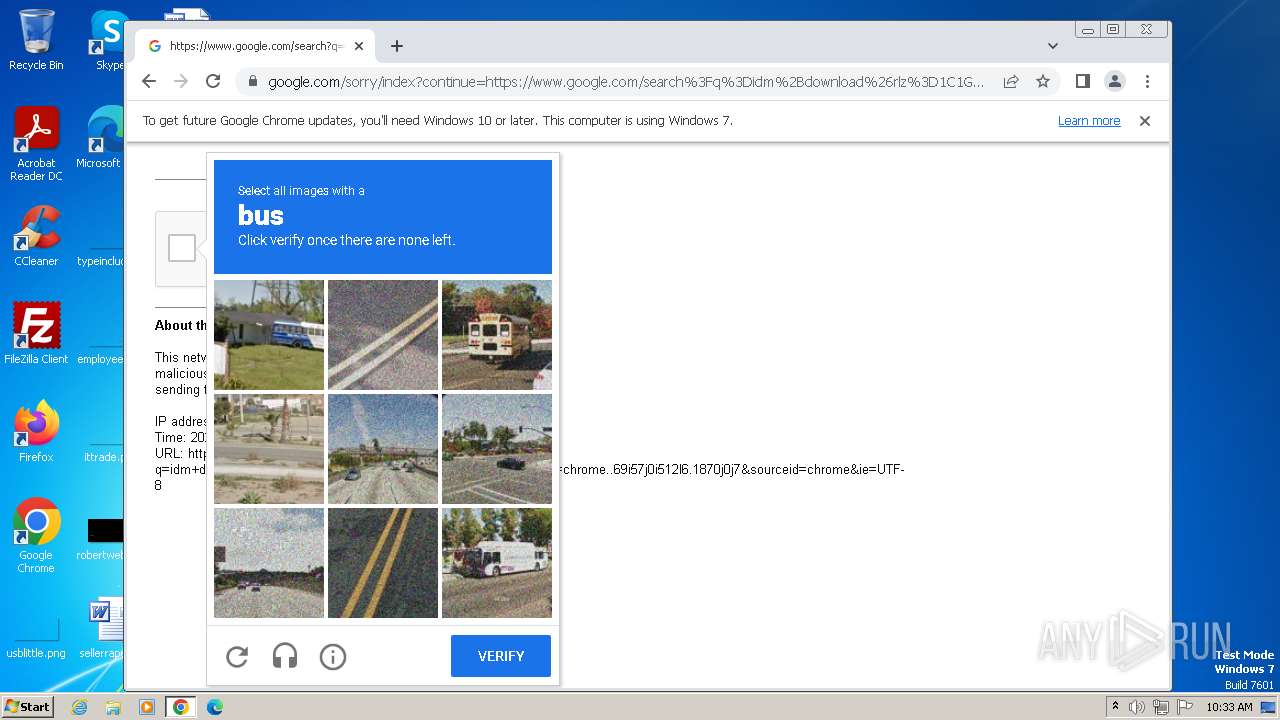
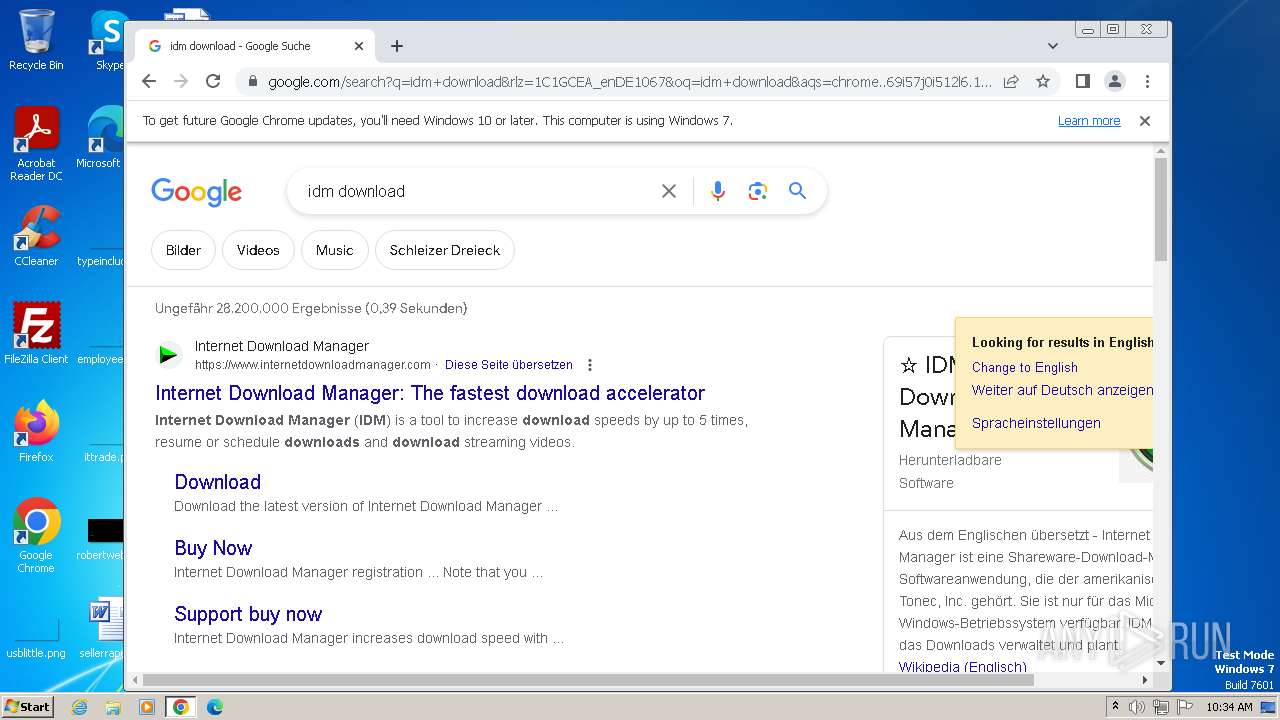
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2AB7A4477F4C4B6D7E6371D1EB141B1E |
| SHA1: | 688D3E884D9EBD66870FF0D1D4845FD7732B6F7C |
| SHA256: | 3205DBB244DE8D75BE0AFB501C4711D126CC877223F81428BF2FC761FAADB682 |
| SSDEEP: | 768:7YHVPFYTwF8PJ4GrwfBKtpohqltfW/0yuxT/7SRNBraB6Af2S:uVPFYW6xrwVkfFTjKBrLAfB |
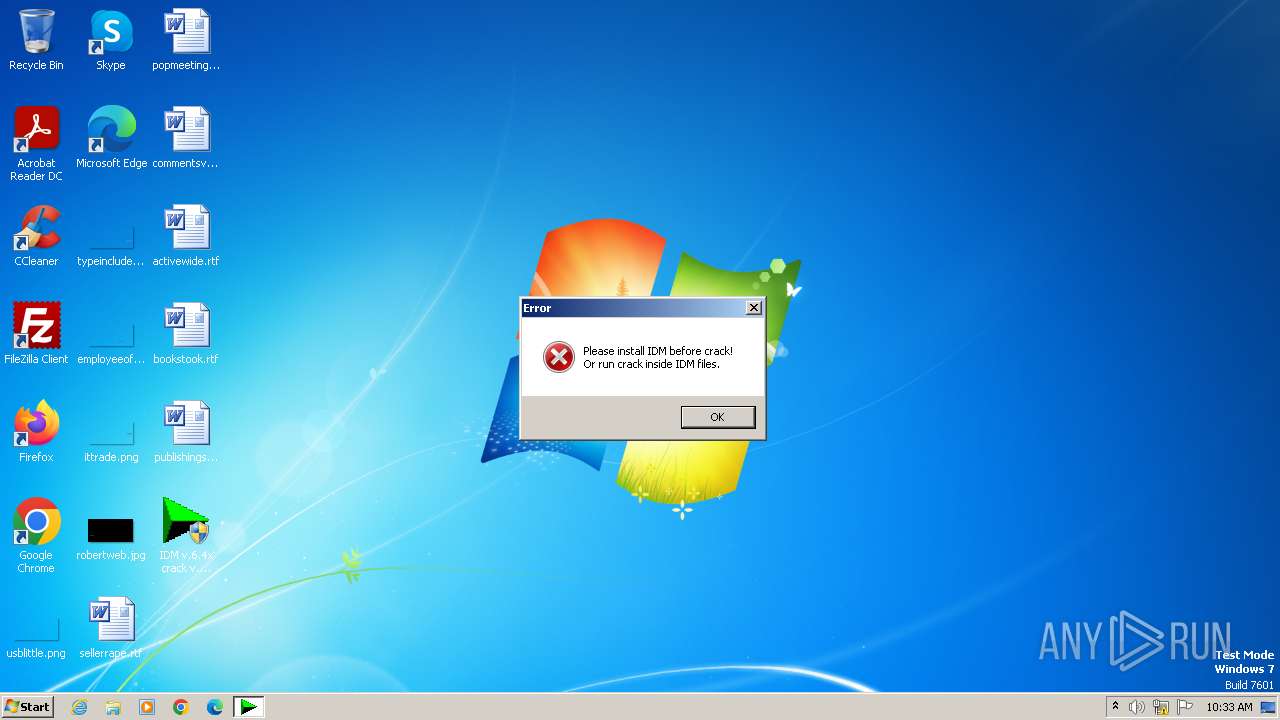
MALICIOUS
Drops the executable file immediately after the start
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- wscript.exe (PID: 2268)
- IDMan.exe (PID: 2528)
- UnSigner.exe (PID: 1752)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2268)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 2268)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 2268)
Starts NET.EXE for service management
- Uninstall.exe (PID: 2100)
- net.exe (PID: 3264)
Creates a writable file the system directory
- rundll32.exe (PID: 3912)
SUSPICIOUS
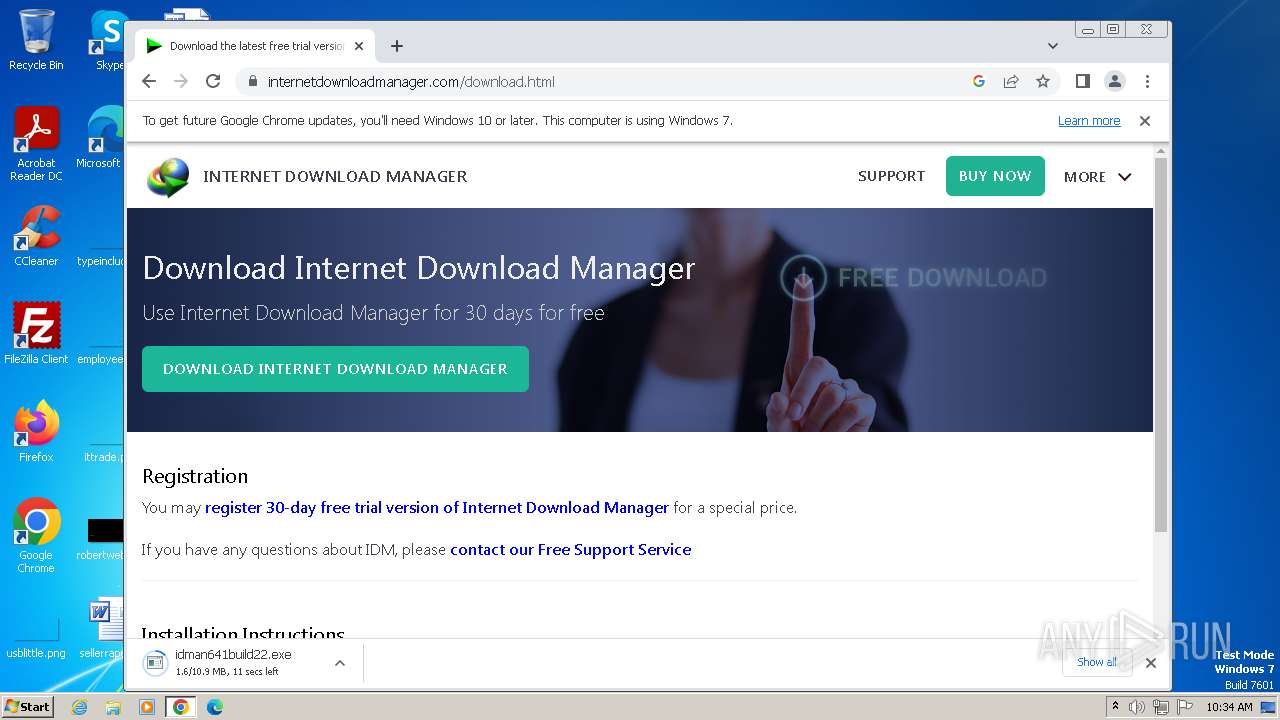
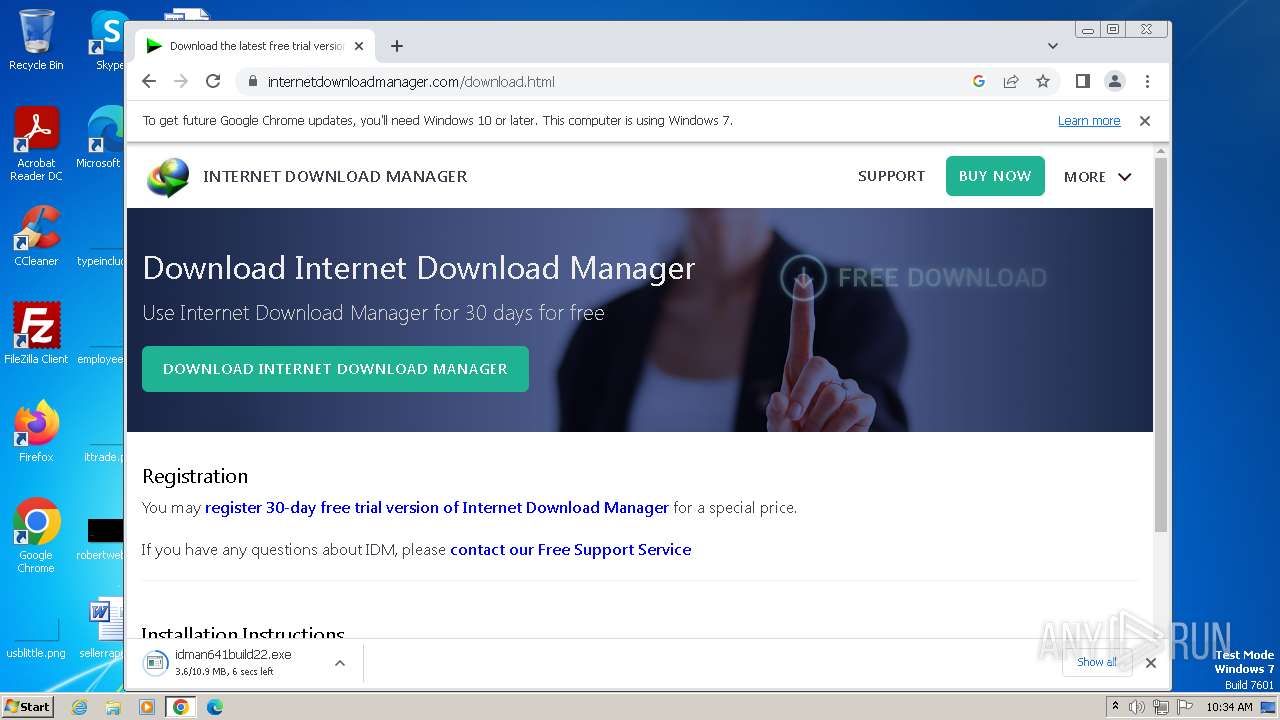
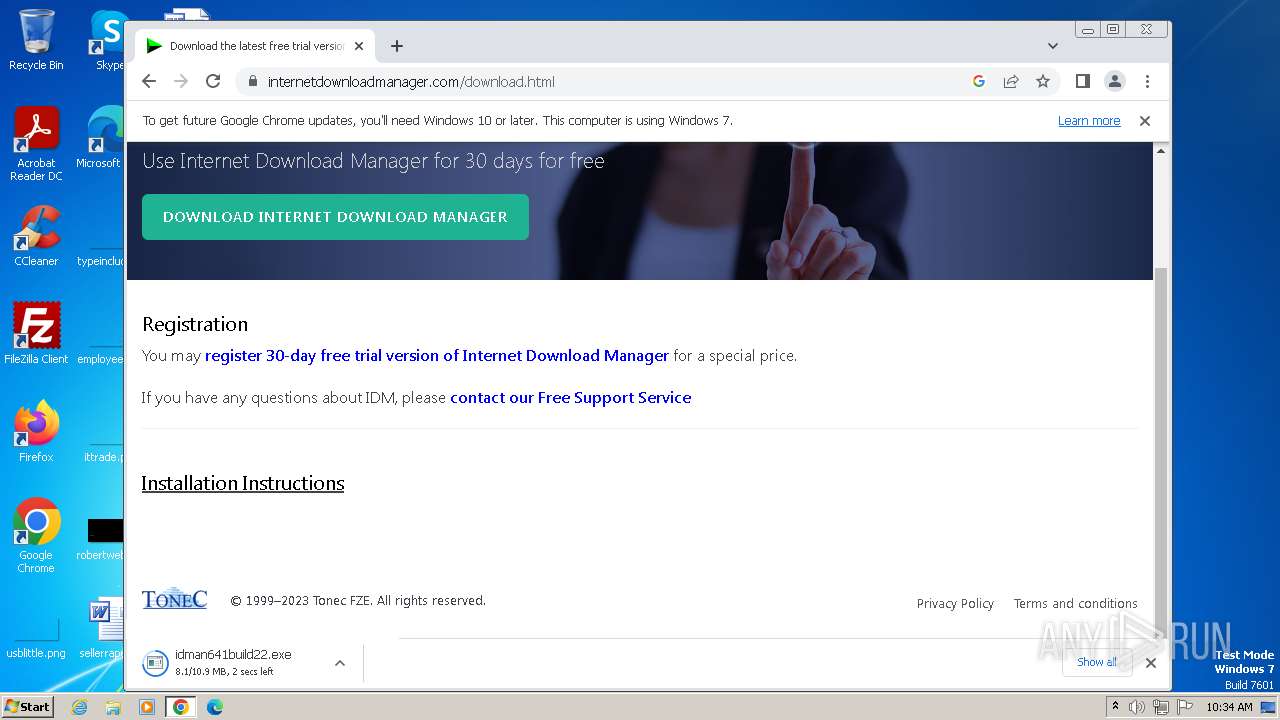
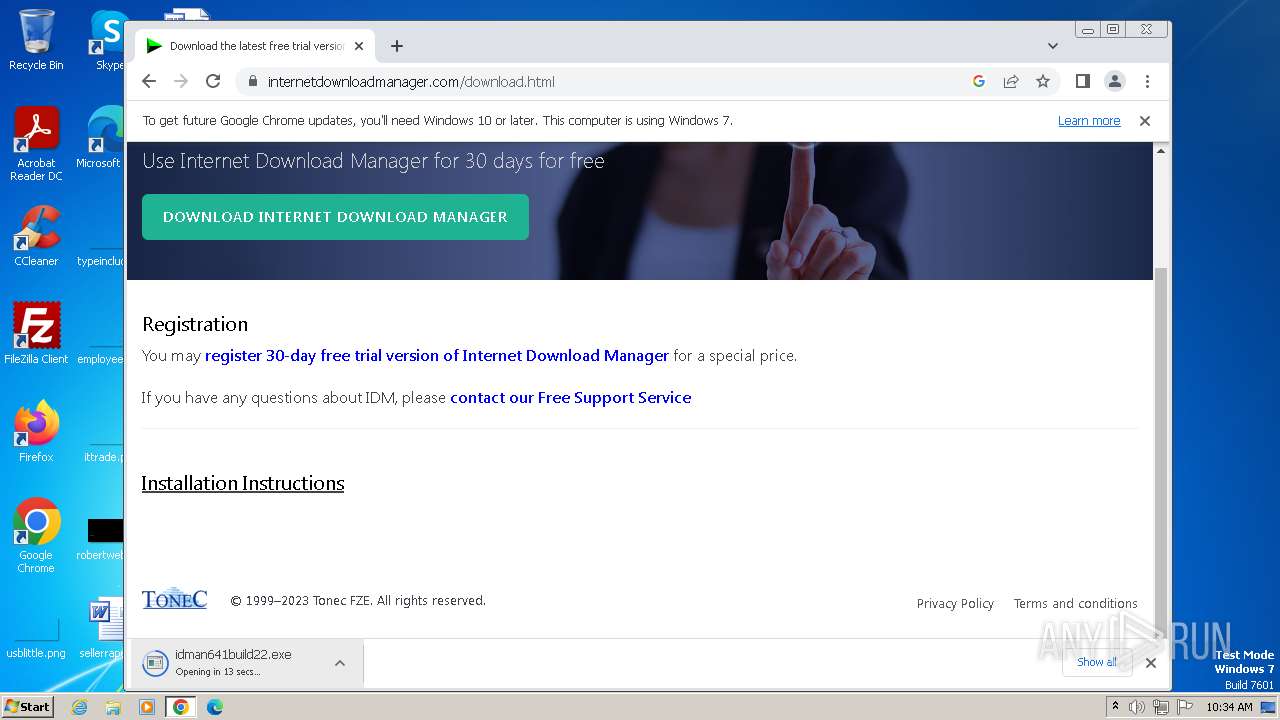
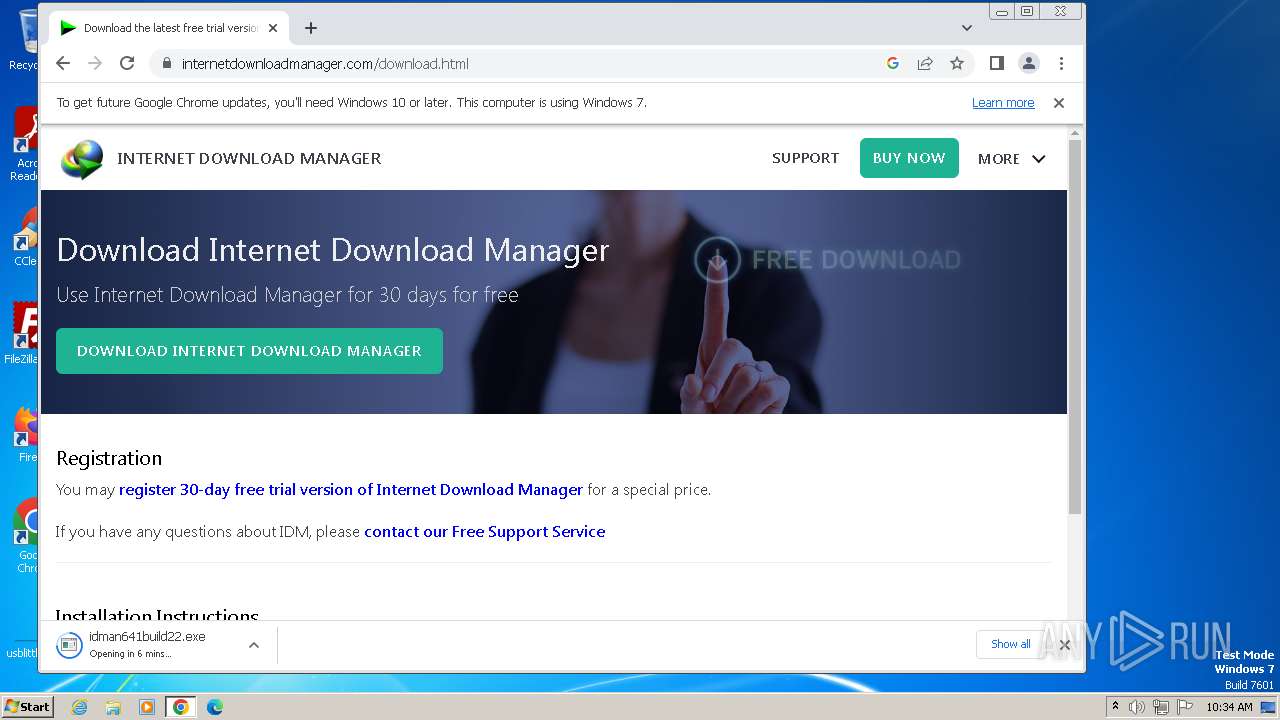
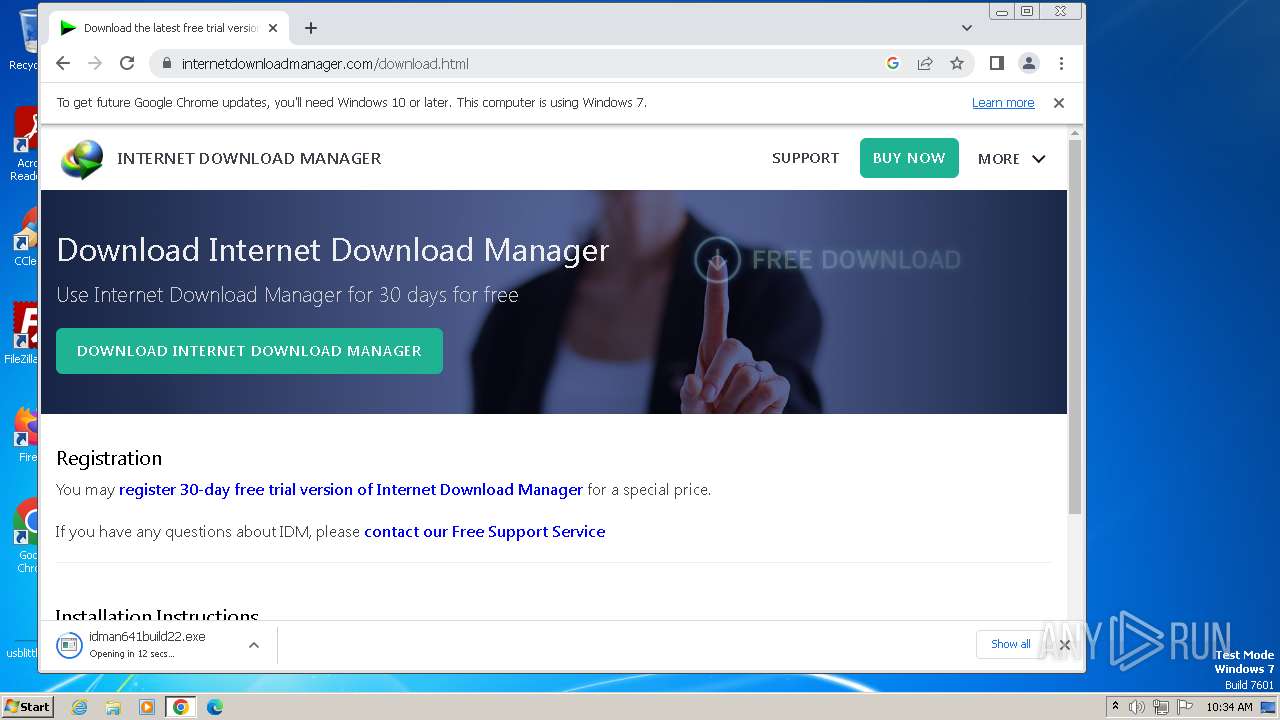
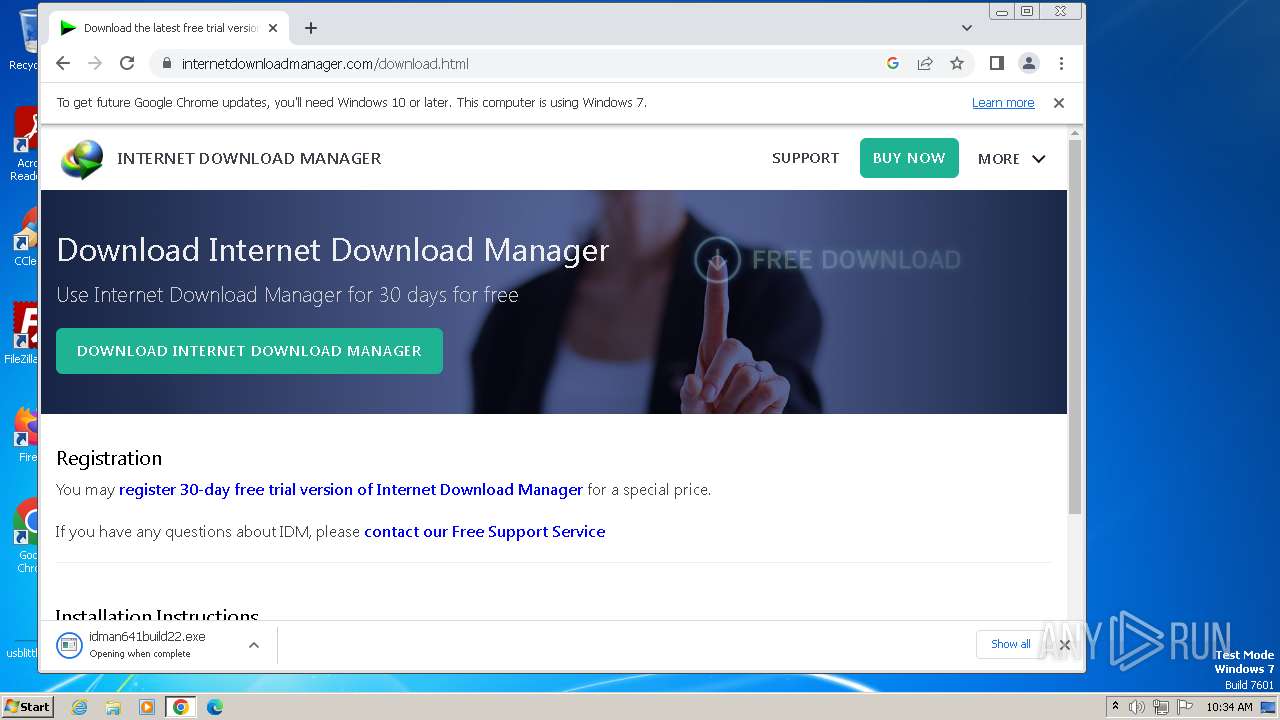
Starts application with an unusual extension
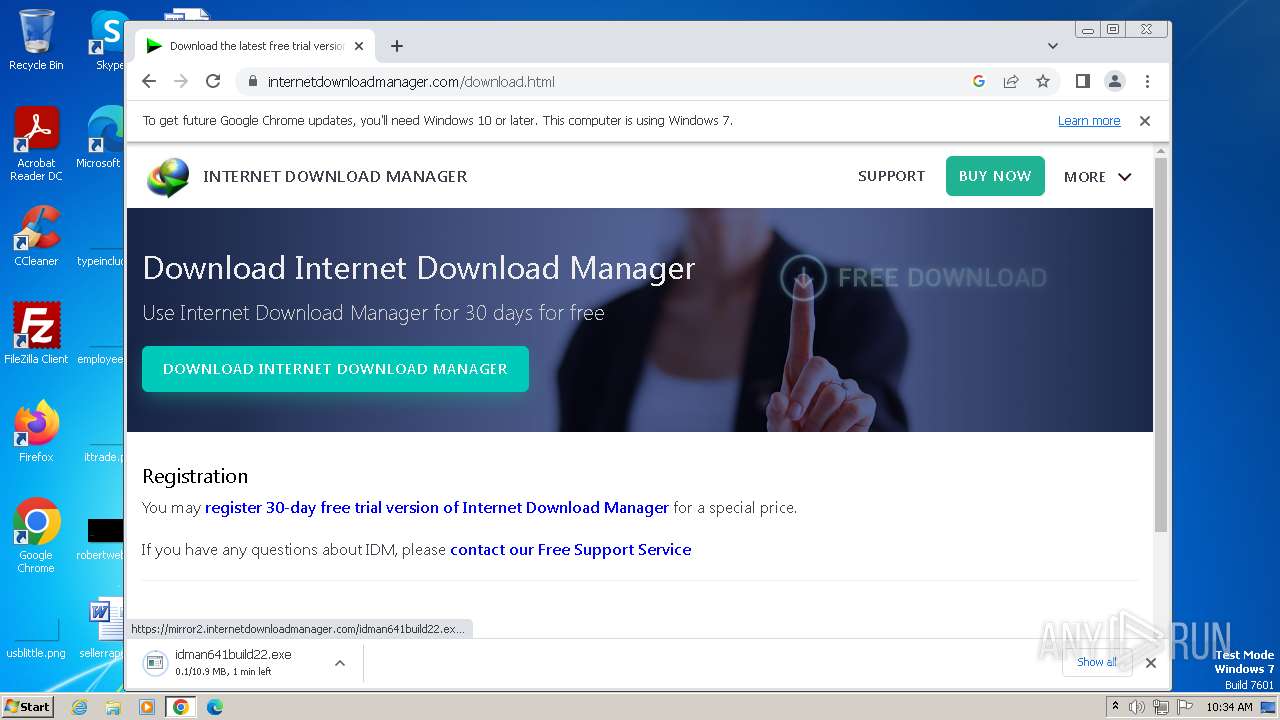
- idman641build22.exe (PID: 3684)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 3568)
Reads the Internet Settings
- IDM1.tmp (PID: 3568)
- IDMan.exe (PID: 2528)
- Uninstall.exe (PID: 2100)
- runonce.exe (PID: 3120)
- IDMan.exe (PID: 1996)
- IDM v.6.4x crack v.18.2.exe (PID: 600)
Checks Windows Trust Settings
- IDMan.exe (PID: 2528)
- IDMan.exe (PID: 1996)
Reads settings of System Certificates
- IDMan.exe (PID: 2528)
- IDMan.exe (PID: 1996)
Creates/Modifies COM task schedule object
- IDMan.exe (PID: 2528)
- Uninstall.exe (PID: 2100)
Searches for installed software
- IDM v.6.4x crack v.18.2.exe (PID: 600)
The process executes VB scripts
- IDM v.6.4x crack v.18.2.exe (PID: 600)
Reads security settings of Internet Explorer
- IDMan.exe (PID: 2528)
- IDMan.exe (PID: 1996)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2268)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2268)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2268)
Creates or modifies Windows services
- Uninstall.exe (PID: 2100)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 2100)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 3912)
Uses REG/REGEDIT.EXE to modify registry
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- cmd.exe (PID: 2680)
Starts CMD.EXE for commands execution
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- cmd.exe (PID: 2680)
Executing commands from a ".bat" file
- IDM v.6.4x crack v.18.2.exe (PID: 600)
Application launched itself
- cmd.exe (PID: 2680)
Identifying current user with WHOAMI command
- cmd.exe (PID: 3720)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2680)
Powershell version downgrade attack
- powershell.exe (PID: 3244)
Uses TASKKILL.EXE to kill process
- IDM v.6.4x crack v.18.2.exe (PID: 600)
INFO
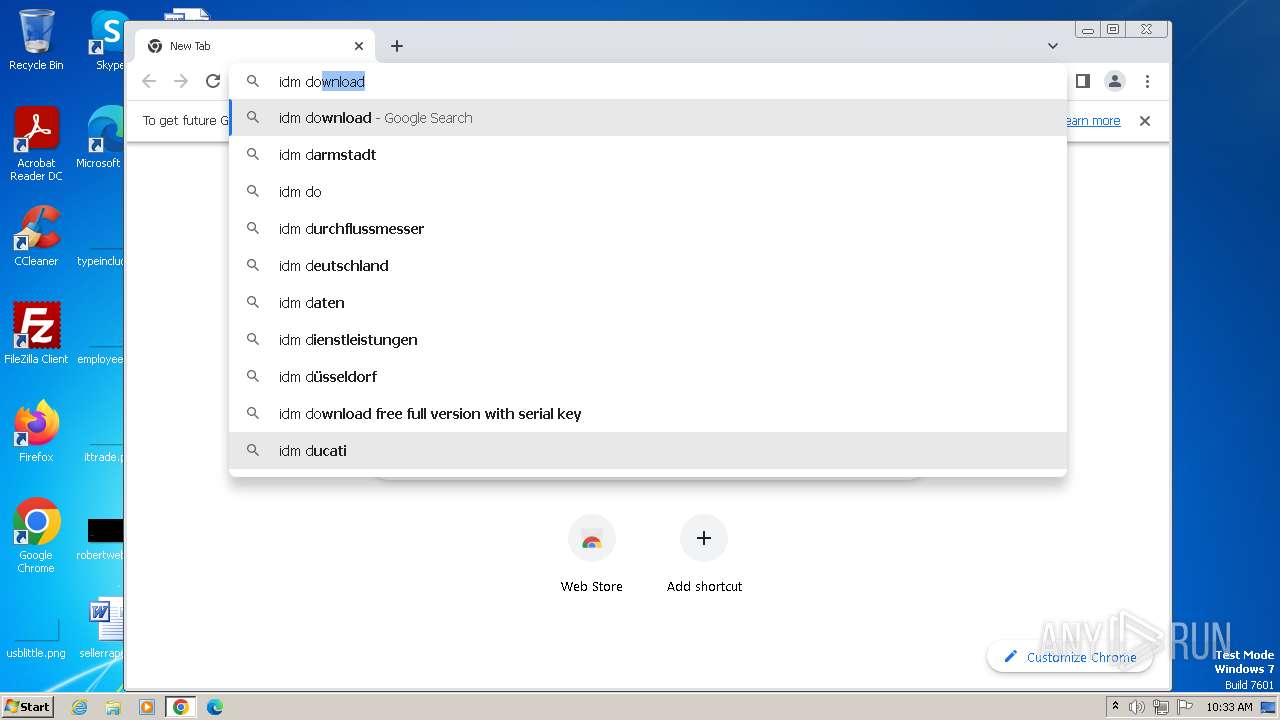
Application launched itself
- chrome.exe (PID: 3400)
- firefox.exe (PID: 3860)
- firefox.exe (PID: 3856)
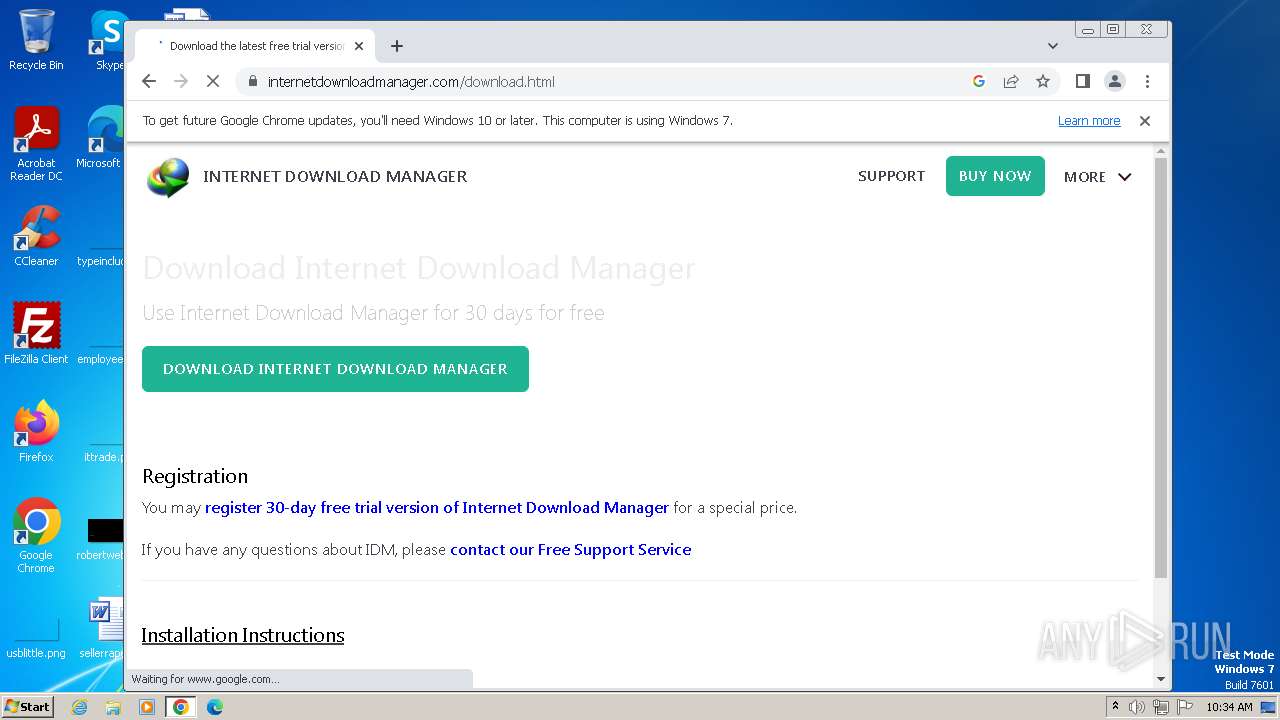
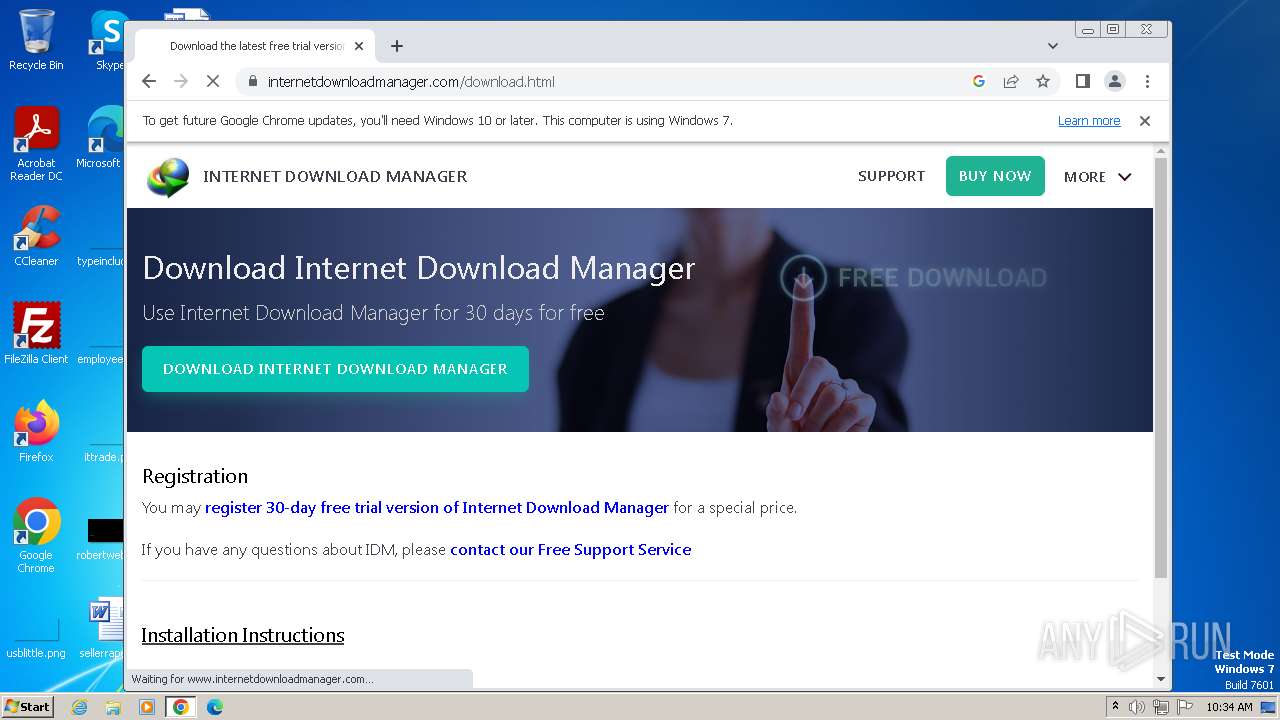
Manual execution by a user
- wmpnscfg.exe (PID: 528)
- chrome.exe (PID: 3400)
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- IDM v.6.4x crack v.18.2.exe (PID: 1008)
- firefox.exe (PID: 3860)
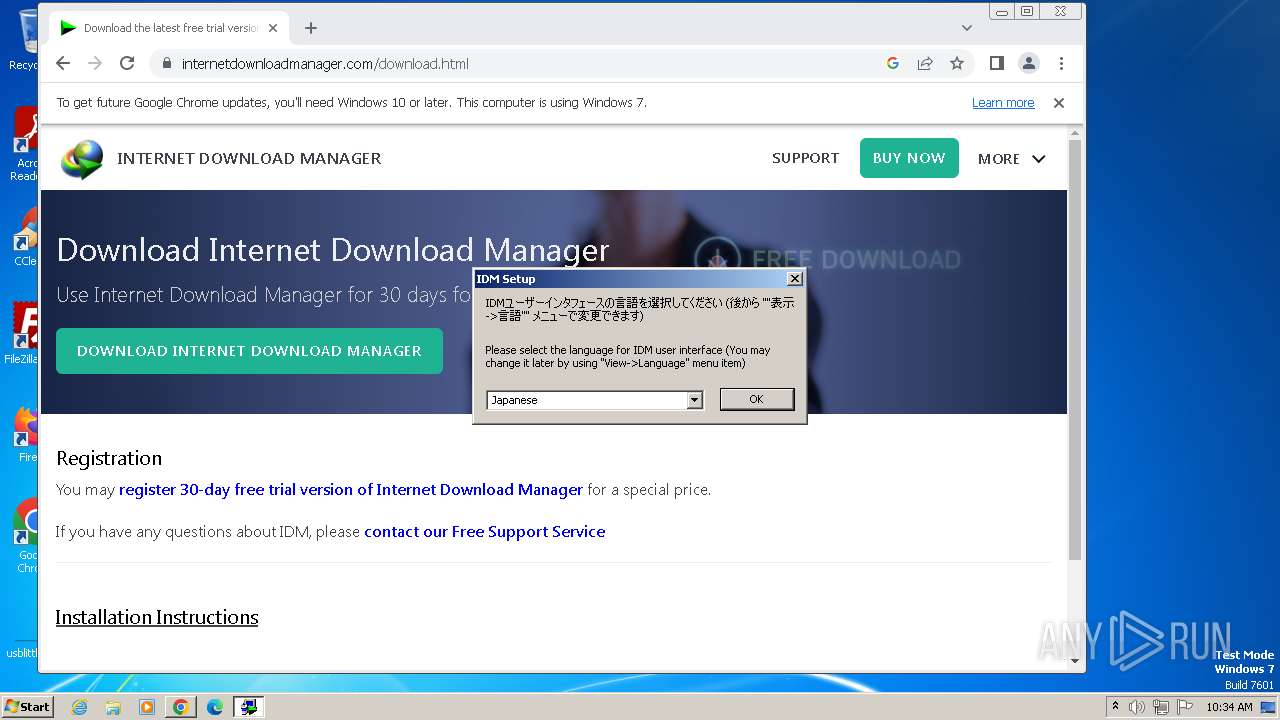
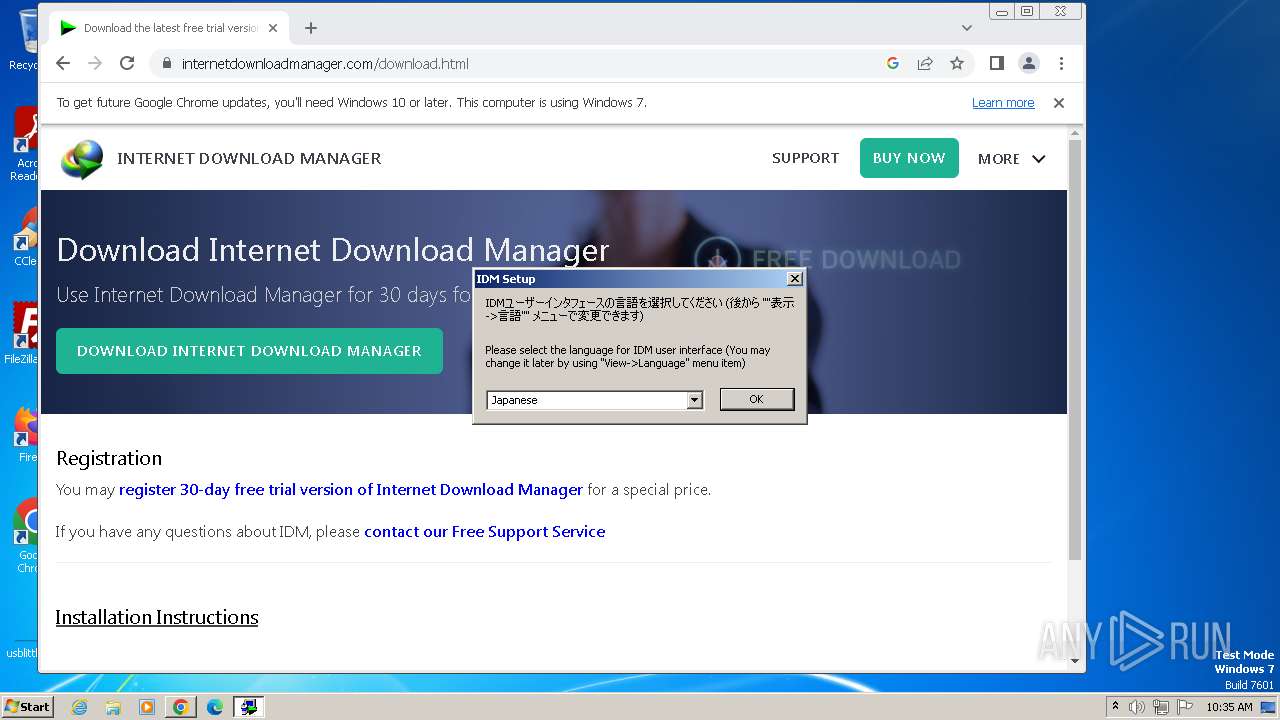
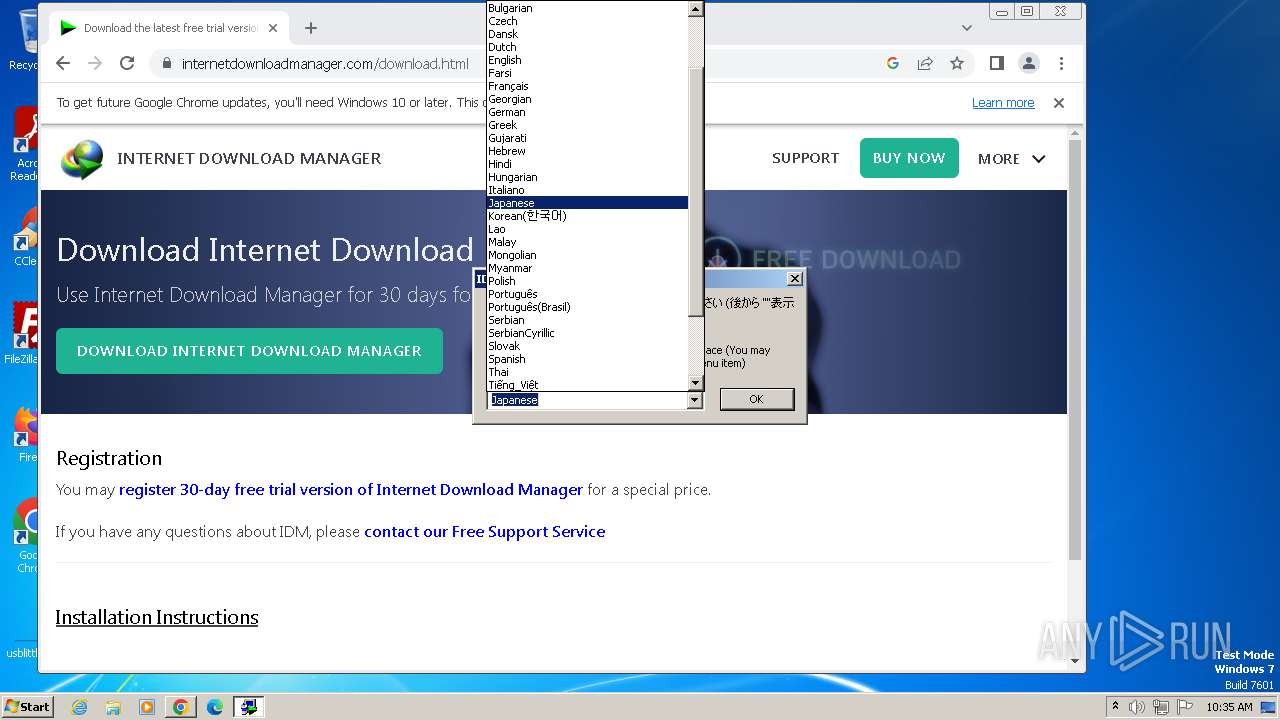
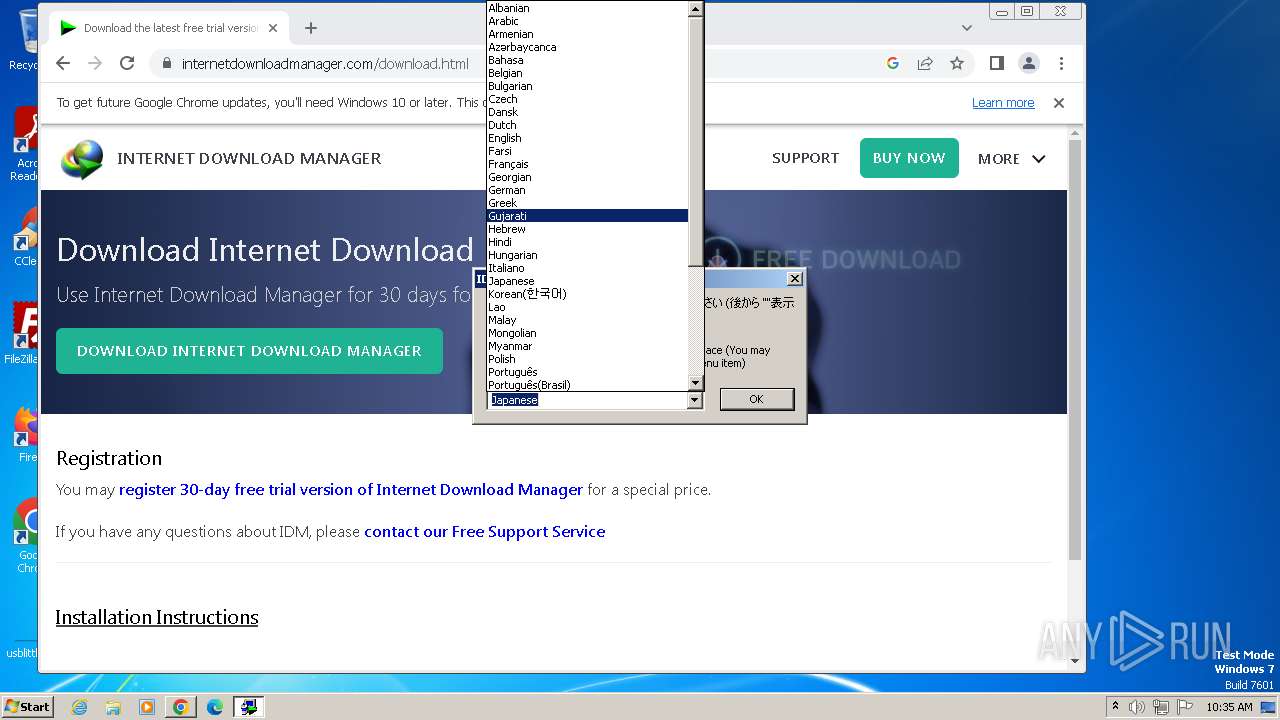
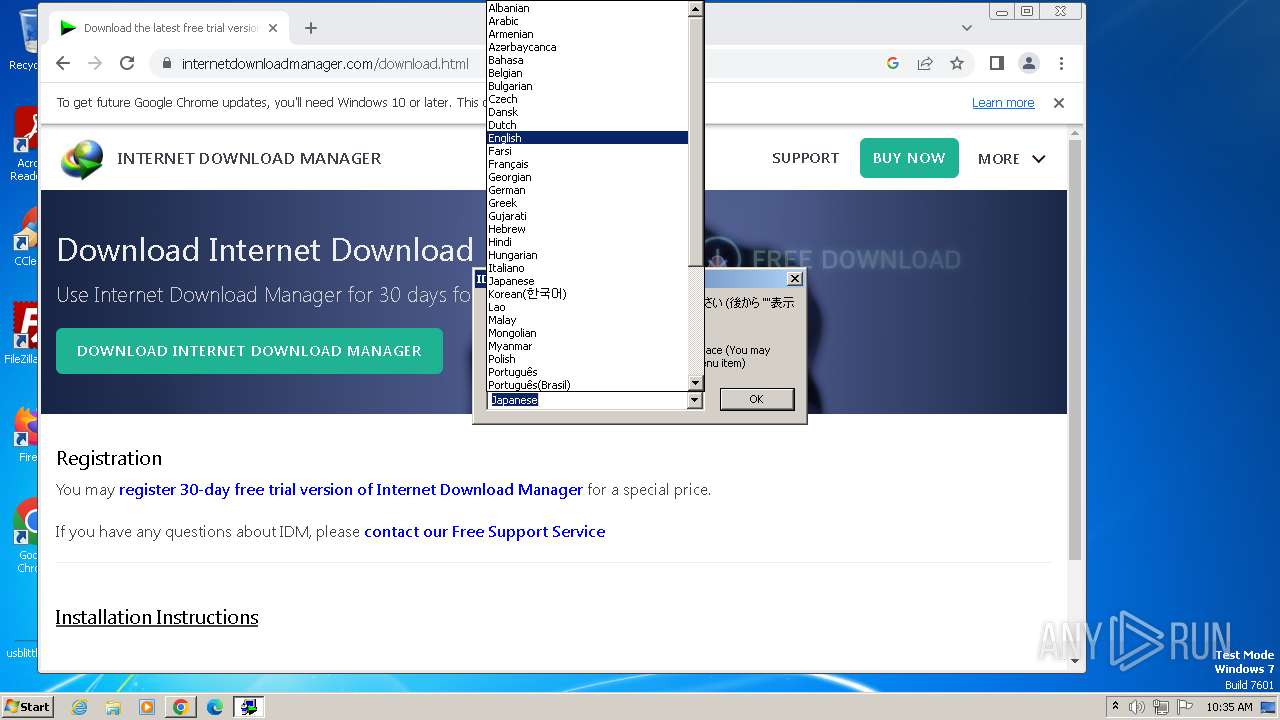
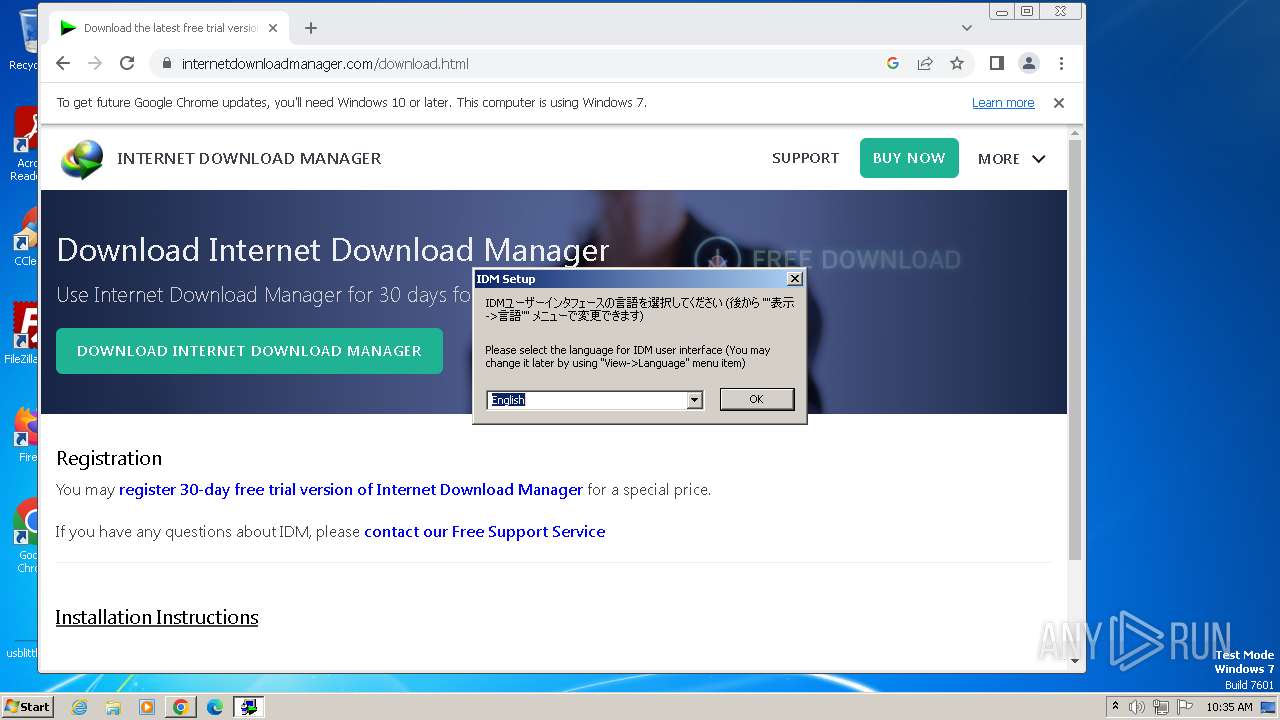
Checks supported languages
- IDM v.6.4x crack v.18.2.exe (PID: 3496)
- wmpnscfg.exe (PID: 528)
- idman641build22.exe (PID: 3684)
- IDM1.tmp (PID: 3568)
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- idmBroker.exe (PID: 3784)
- IDMan.exe (PID: 2528)
- Uninstall.exe (PID: 2100)
- MediumILStart.exe (PID: 2488)
- IDMan.exe (PID: 1996)
- IEMonitor.exe (PID: 3788)
- UnSigner.exe (PID: 1752)
Reads the computer name
- wmpnscfg.exe (PID: 528)
- IDM1.tmp (PID: 3568)
- IDMan.exe (PID: 2528)
- MediumILStart.exe (PID: 2488)
- Uninstall.exe (PID: 2100)
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- IDMan.exe (PID: 1996)
- IEMonitor.exe (PID: 3788)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 528)
- IDM1.tmp (PID: 3568)
- IDMan.exe (PID: 2528)
- MediumILStart.exe (PID: 2488)
- IDMan.exe (PID: 1996)
The process uses the downloaded file
- chrome.exe (PID: 2976)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 1936)
- chrome.exe (PID: 3544)
- chrome.exe (PID: 3400)
Create files in a temporary directory
- idman641build22.exe (PID: 3684)
- IDM1.tmp (PID: 3568)
- IDM v.6.4x crack v.18.2.exe (PID: 600)
- IDMan.exe (PID: 2528)
- IDMan.exe (PID: 1996)
Drops the executable file immediately after the start
- chrome.exe (PID: 3944)
- chrome.exe (PID: 3400)
- rundll32.exe (PID: 3912)
Creates files in the program directory
- IDM1.tmp (PID: 3568)
- IDMan.exe (PID: 2528)
- wscript.exe (PID: 2268)
Creates files or folders in the user directory
- IDM1.tmp (PID: 3568)
- IDMan.exe (PID: 2528)
Creates files in the driver directory
- rundll32.exe (PID: 3912)
Reads the time zone
- runonce.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.4) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27) |
| .exe | | | UPX compressed Win32 Executable (2.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.6) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 32256 |
| InitializedDataSize: | 39424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x89c4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
395
Monitored processes
344
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | reg query "HKCU\Software\Classes\CLSID\{84797876-C678-1780-A556-0CD06786780F}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 120 | REG DELETE "HKLM\Software\Classes\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C}" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | reg query "HKCU\Software\Classes\Wow6432Node\CLSID\{79873CC5-3951-43ED-BDF9-D8759474B6FD}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | reg query "HKLM\Software\Classes\Wow6432Node\CLSID\{84797876-C678-1780-A556-0CD06786780F}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | reg query "HKLM\Software\Classes\CLSID\{84797876-C678-1780-A556-0CD06786780F}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | reg query "HKCU\Software\Wow6432Node\Download Manager" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | reg query "HKLM\Software\Classes\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | REG DELETE "HKU\.DEFAULT\Software\Classes\CLSID\{5312C54E-A385-46B7-B200-ABAF81B03935}" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | reg query "HKCU\Software\Classes\Wow6432Node\CLSID\{E6871B76-C3C8-44DD-B947-ABFFE144860D}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 368 | REG DELETE "HKCU\Software\Download Manager" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
35 241
Read events
34 768
Write events
367
Delete events
106
Modification events
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
20
Suspicious files
282
Text files
81
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF16af8e.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF16b22e.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF16af9e.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF16afad.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:29B82603A20A26A3F99DB34525AF7448 | SHA256:9601A054A9C6AA6A65CEFAA229046476C1A089989FA6441DAD71D39F6794B980 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
77
DNS requests
144
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
3856 | firefox.exe | POST | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
3856 | firefox.exe | POST | 200 | 184.24.77.52:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3856 | firefox.exe | POST | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 5.24 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 163 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 43.6 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 21.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3400 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3944 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3944 | chrome.exe | 142.250.185.77:443 | accounts.google.com | GOOGLE | US | unknown |
3944 | chrome.exe | 172.217.18.100:443 | www.google.com | GOOGLE | US | whitelisted |
3944 | chrome.exe | 142.250.186.174:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
3944 | chrome.exe | 142.250.185.225:443 | lh5.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |