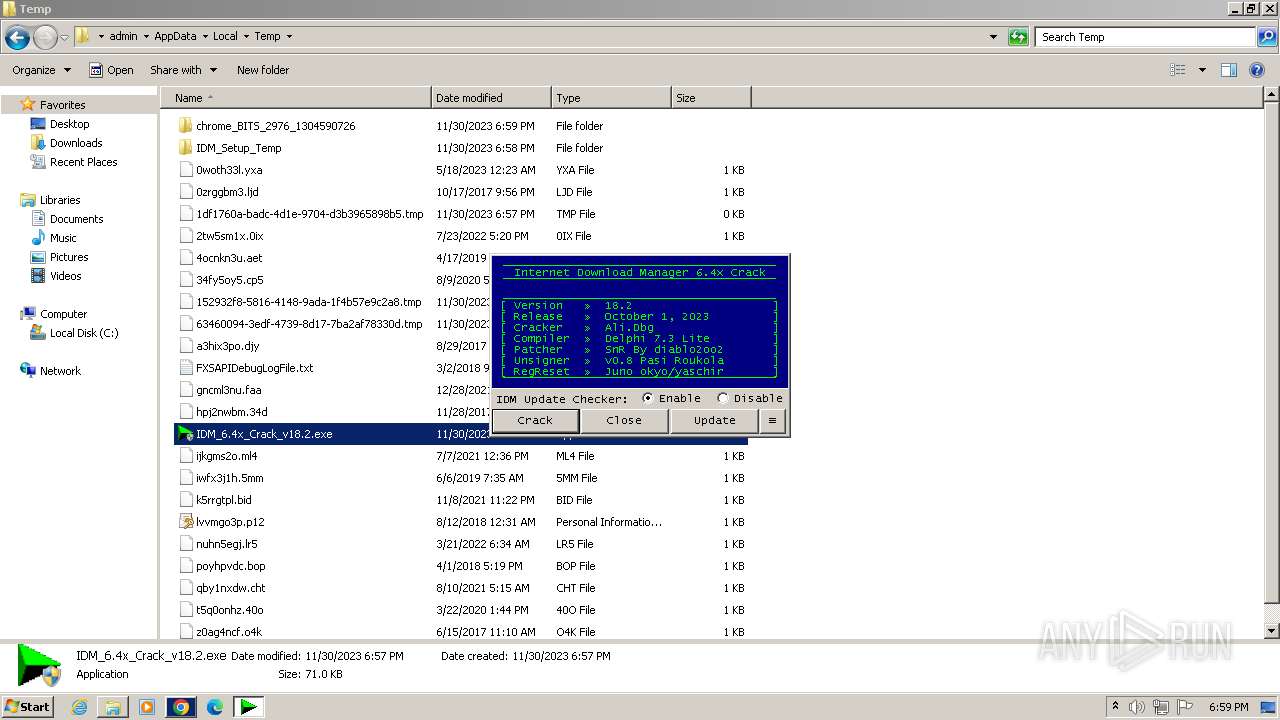
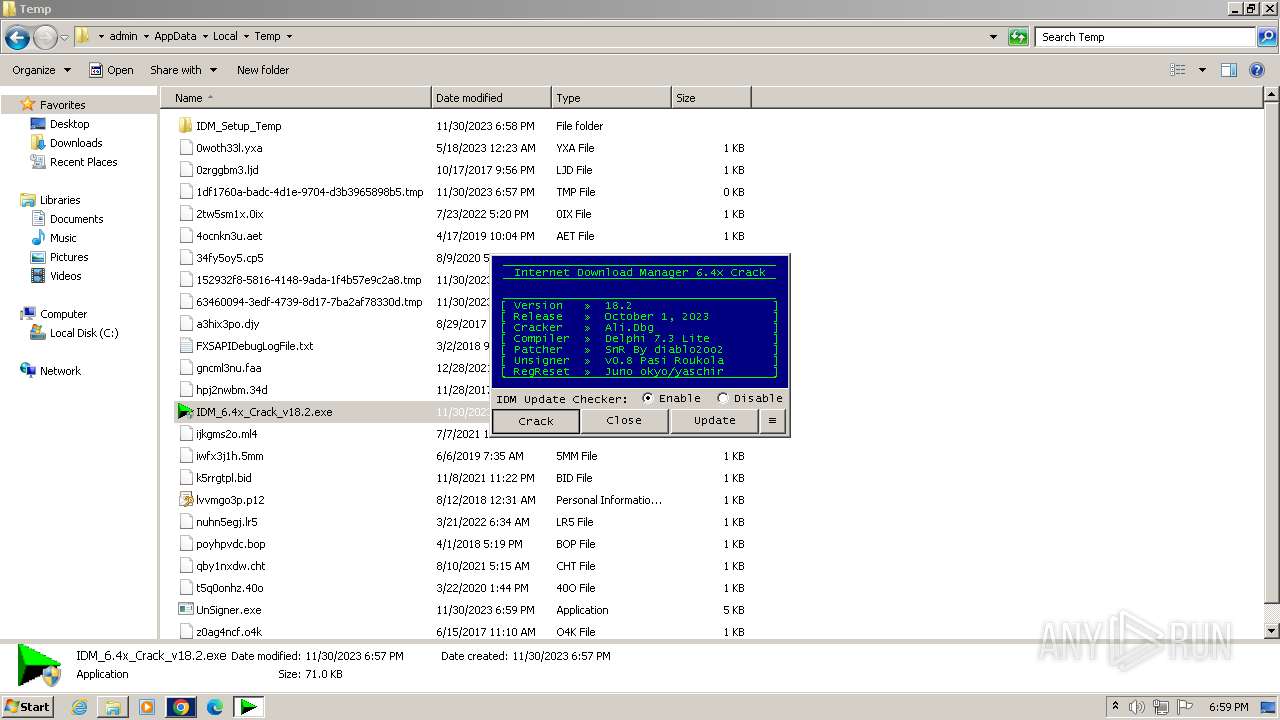
| File name: | IDM_6.4x_Crack_v18.2.exe |
| Full analysis: | https://app.any.run/tasks/60f1c1de-e0b7-4d31-b132-eb924af50ab0 |
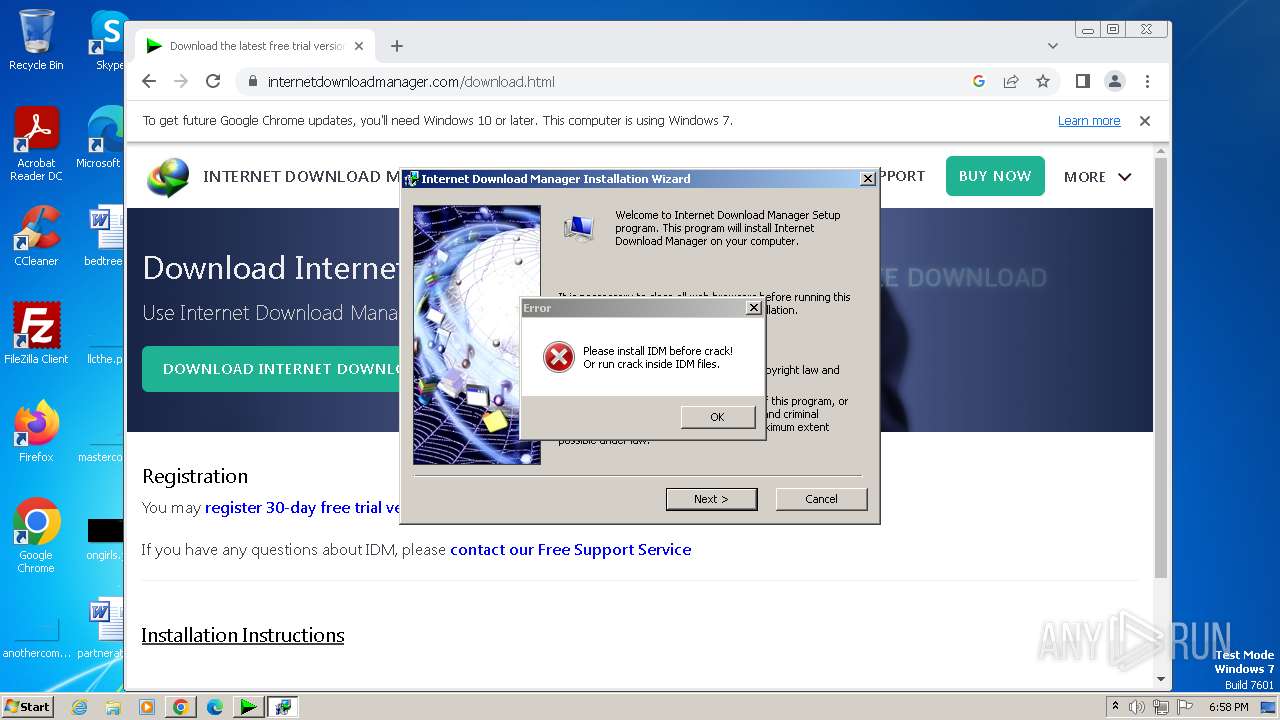
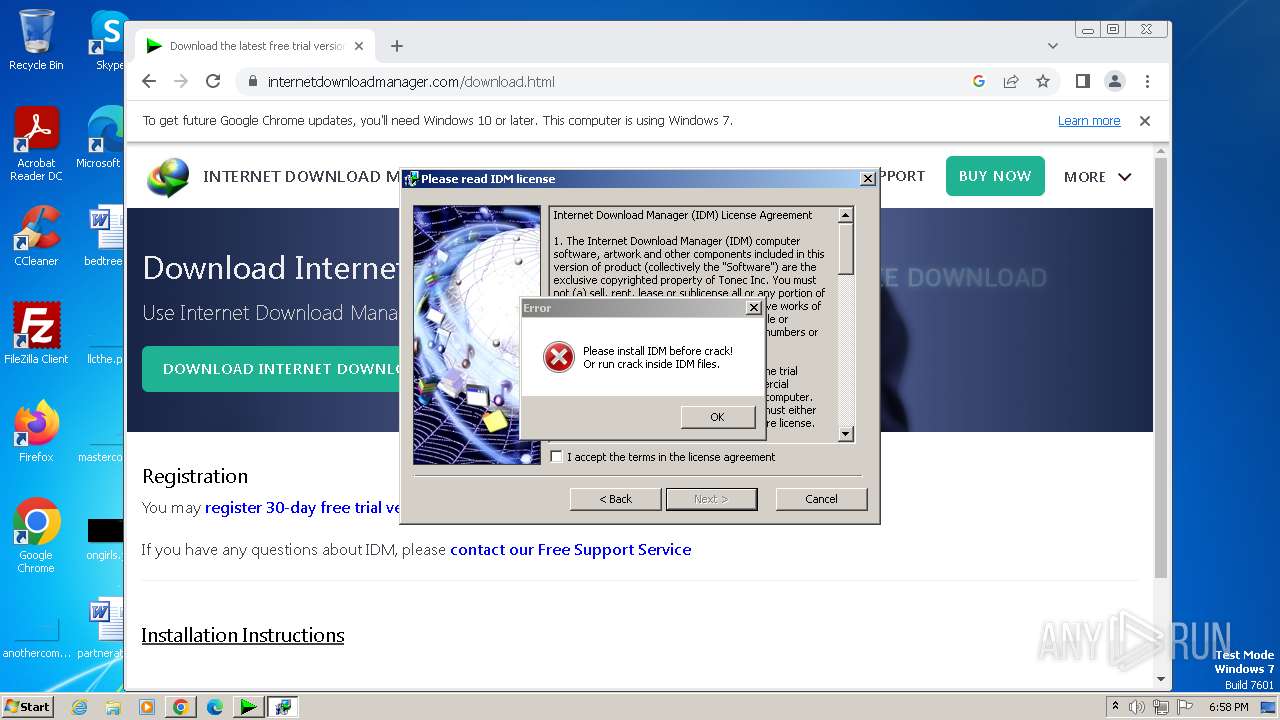
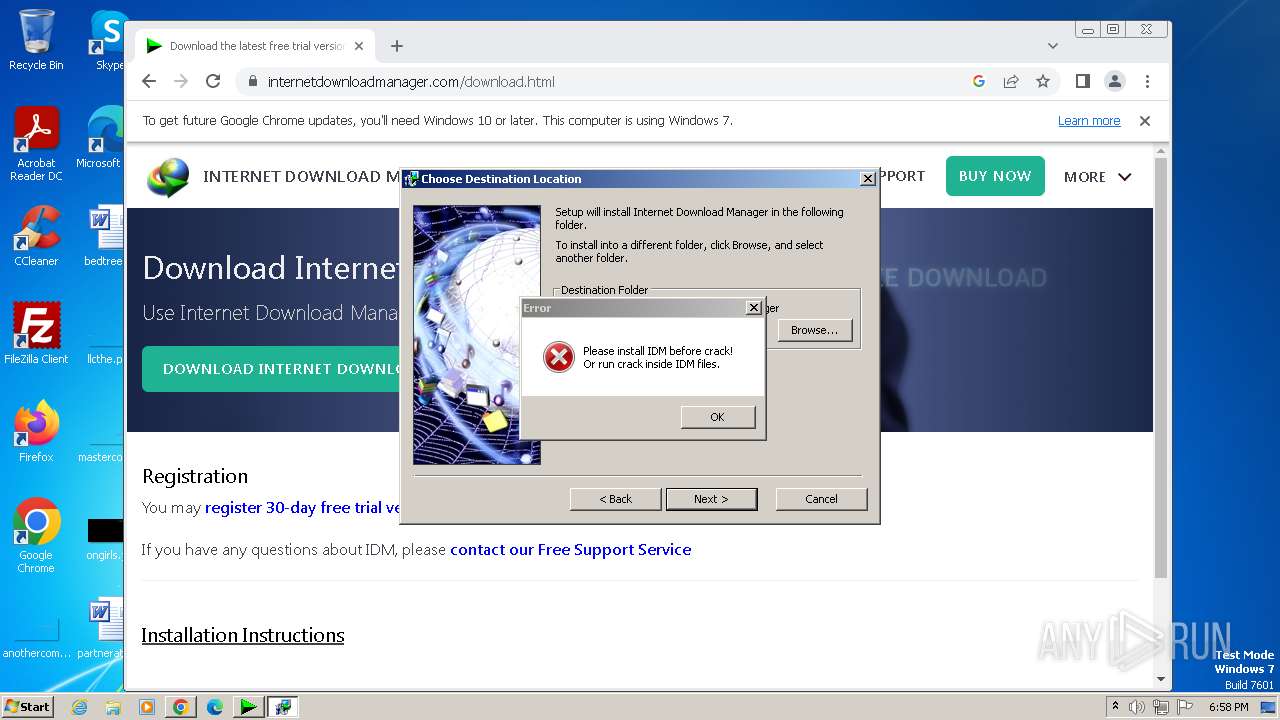
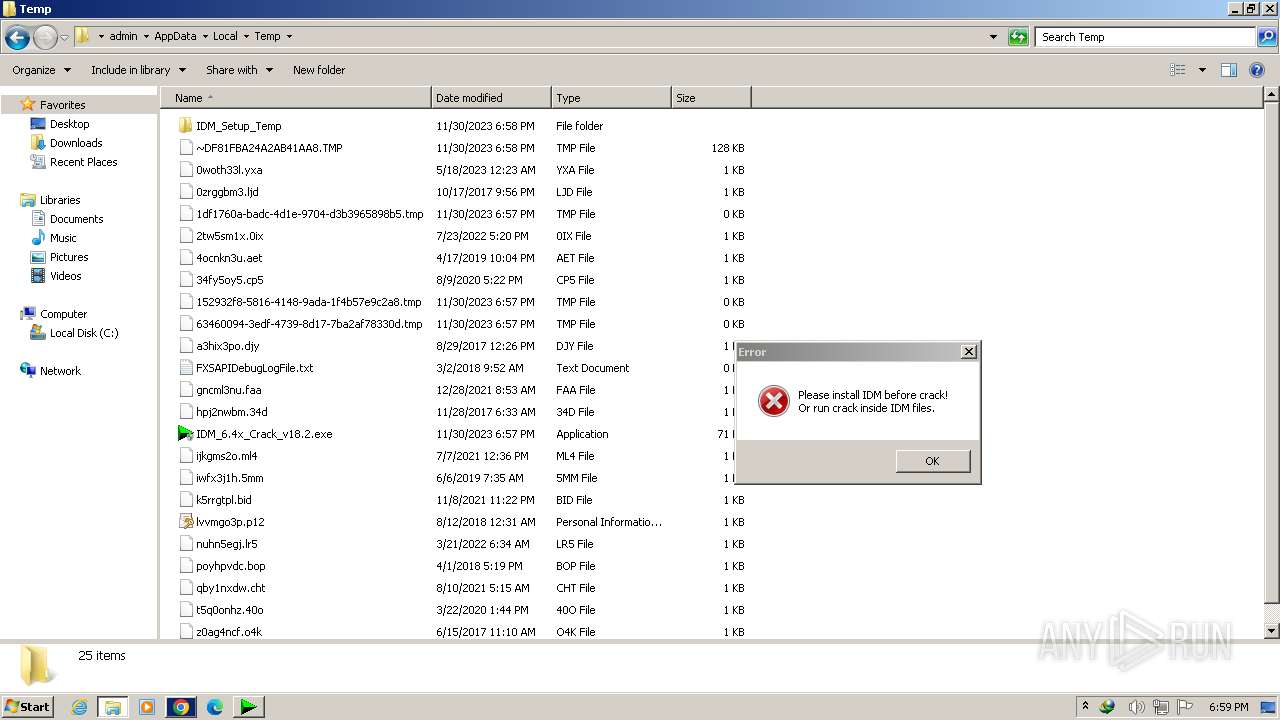
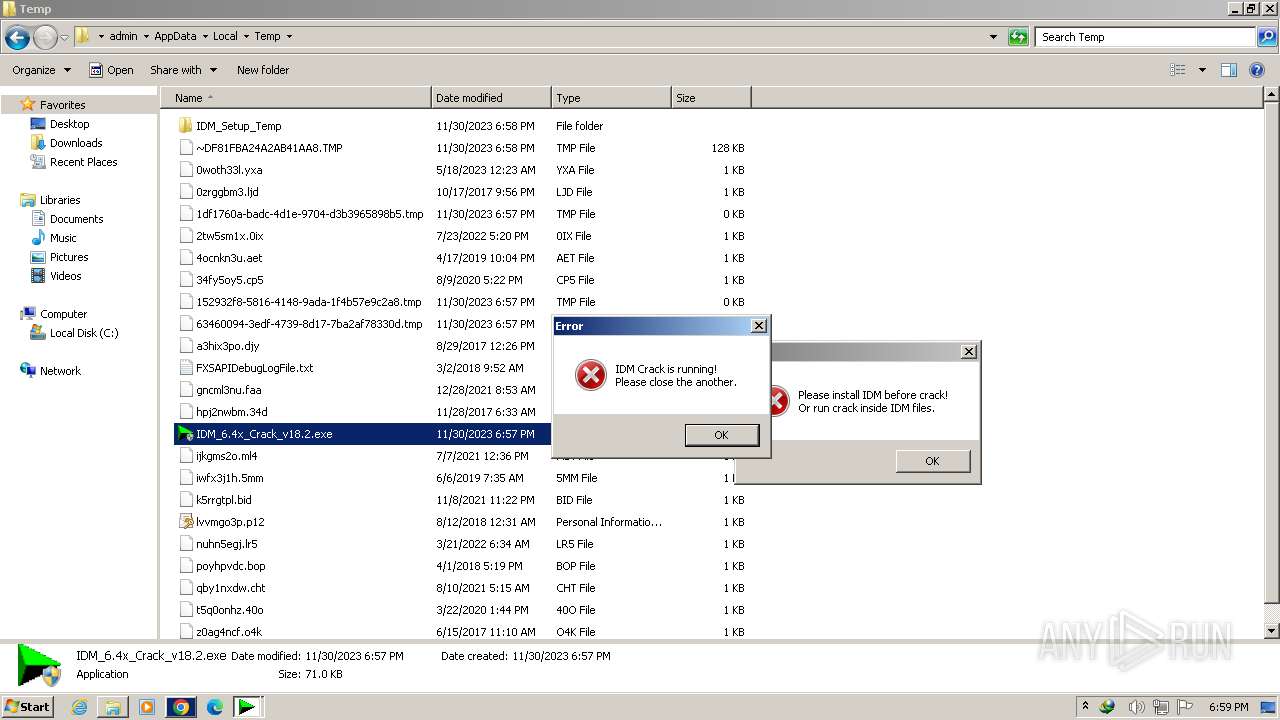
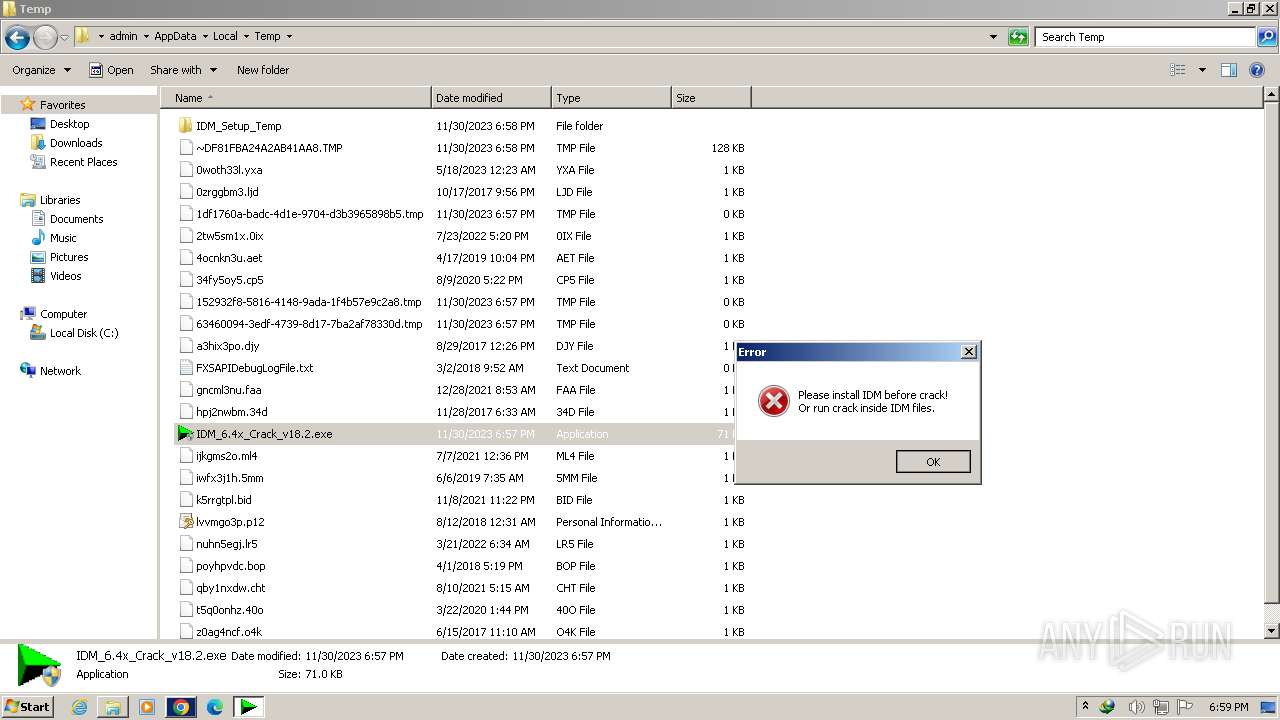
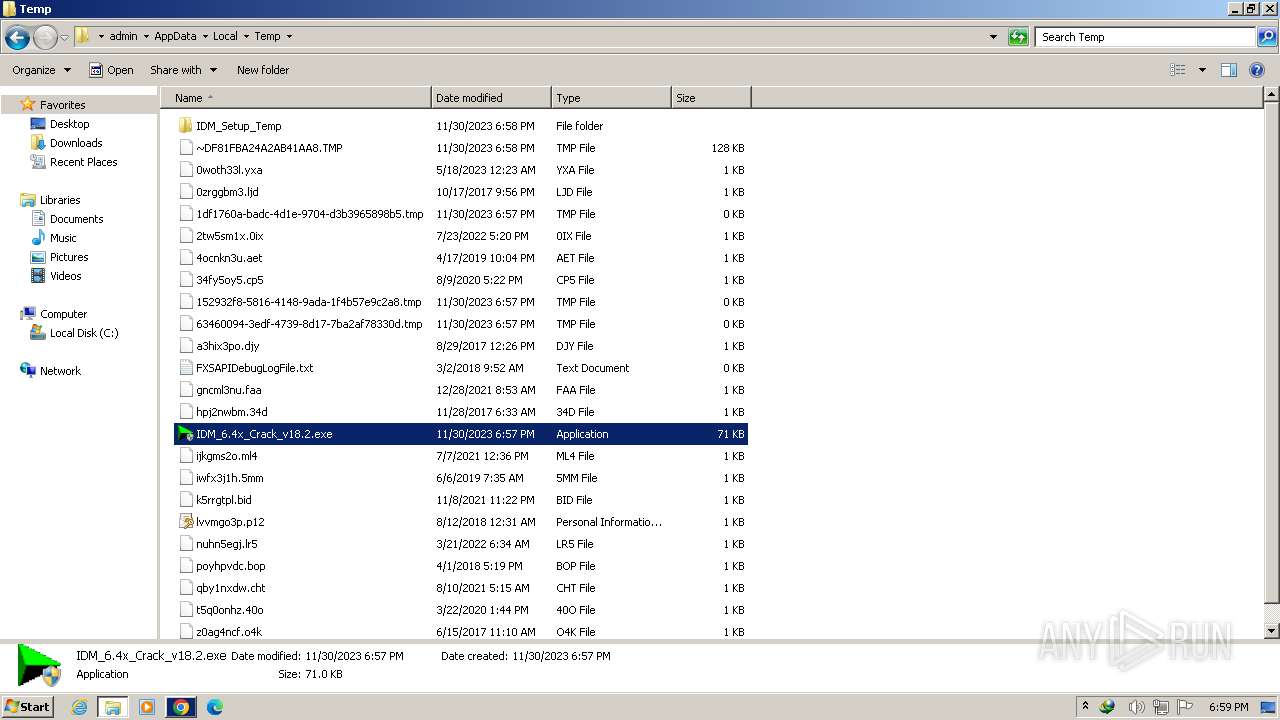
| Verdict: | Malicious activity |
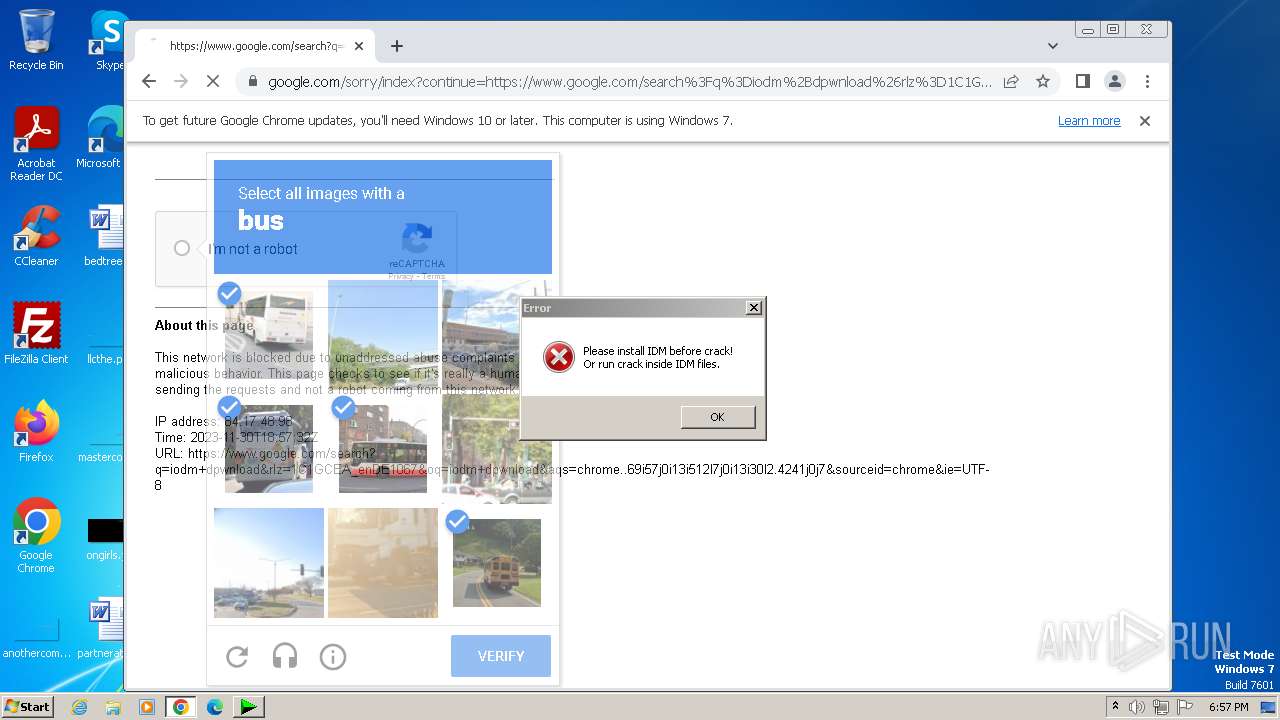
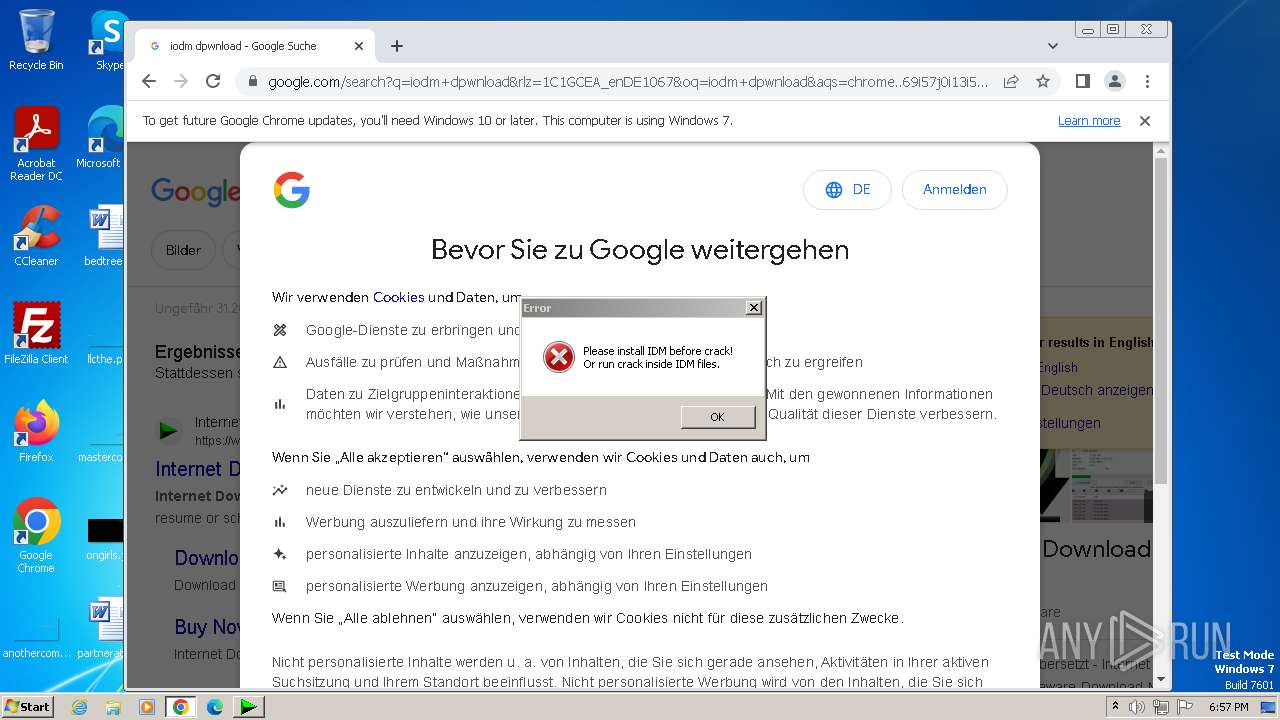
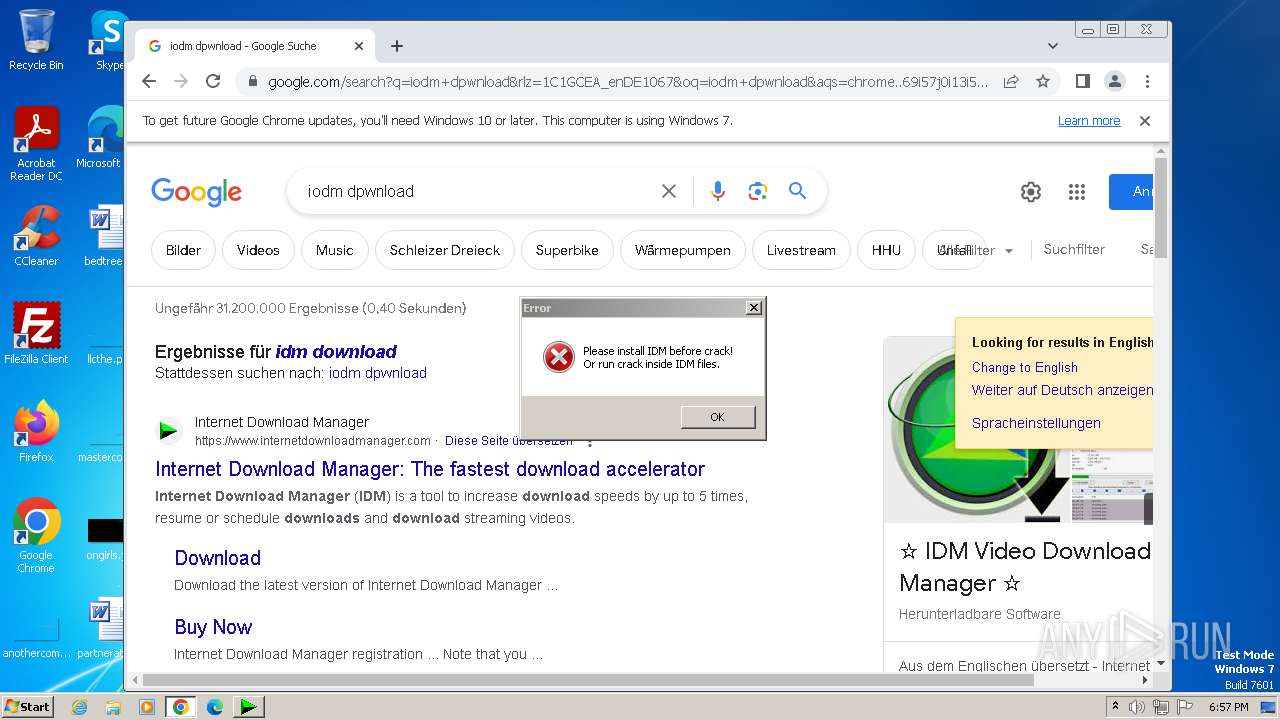
| Analysis date: | November 30, 2023, 18:57:08 |
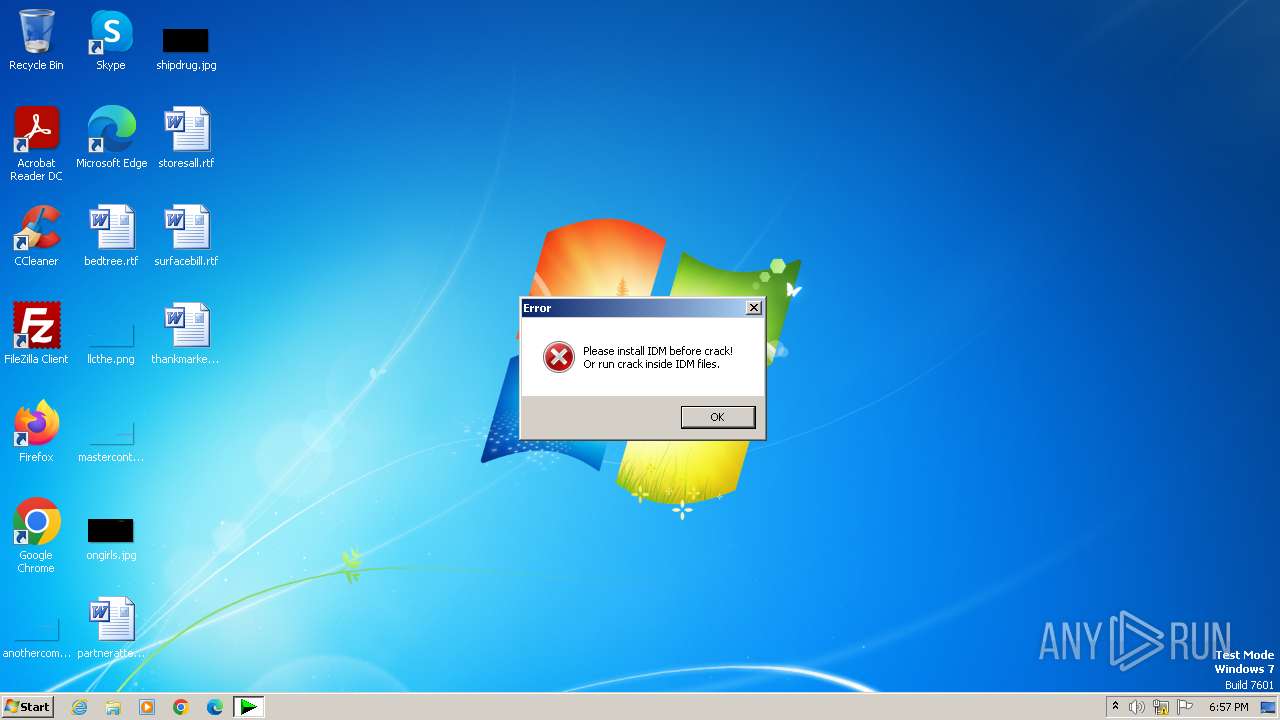
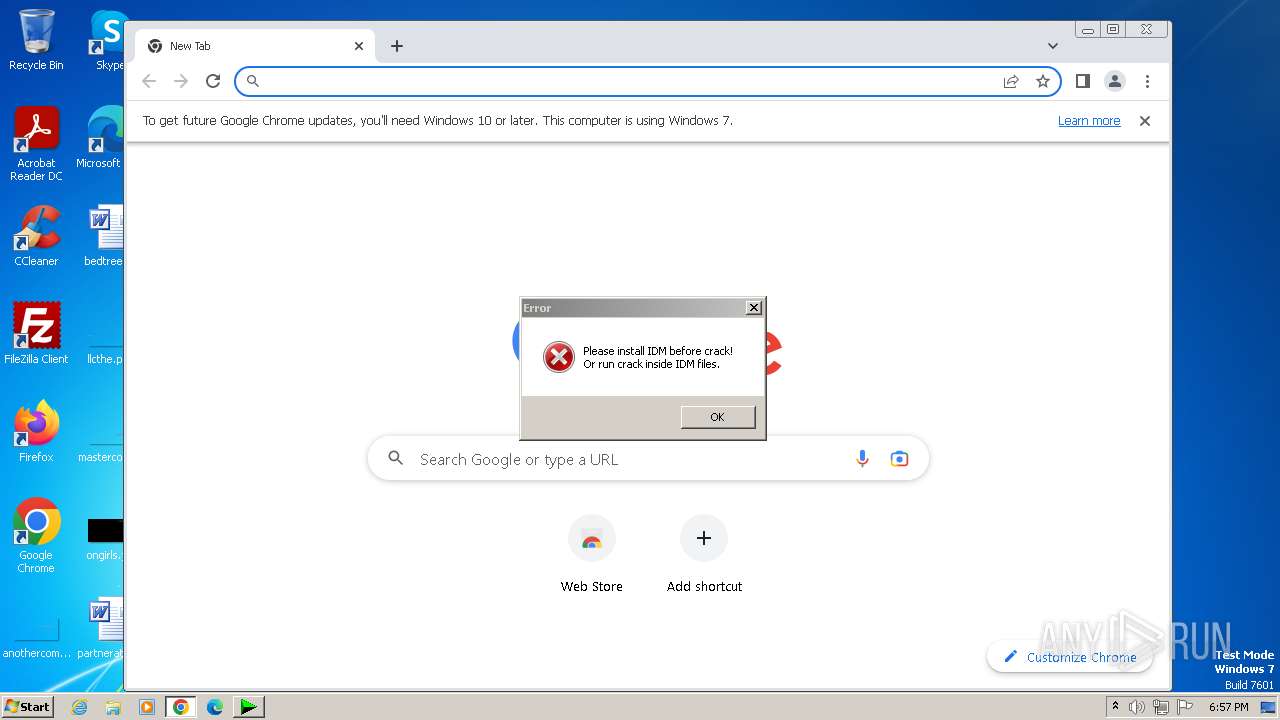
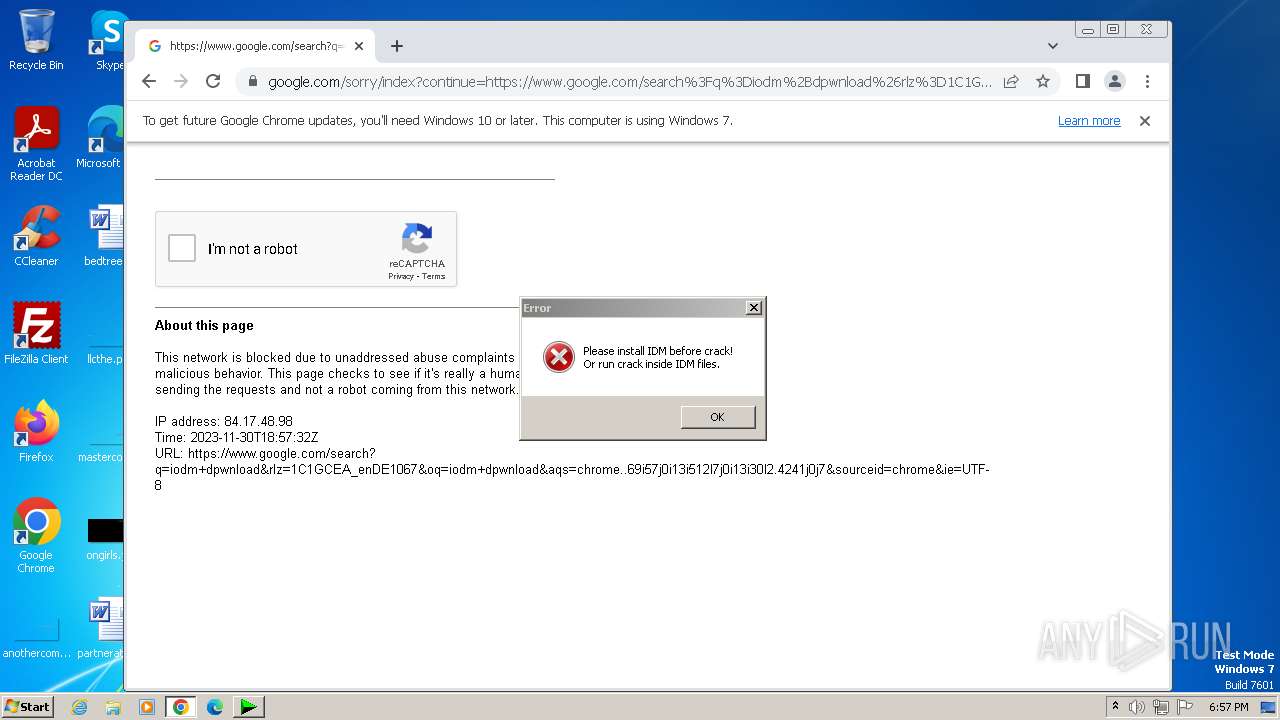
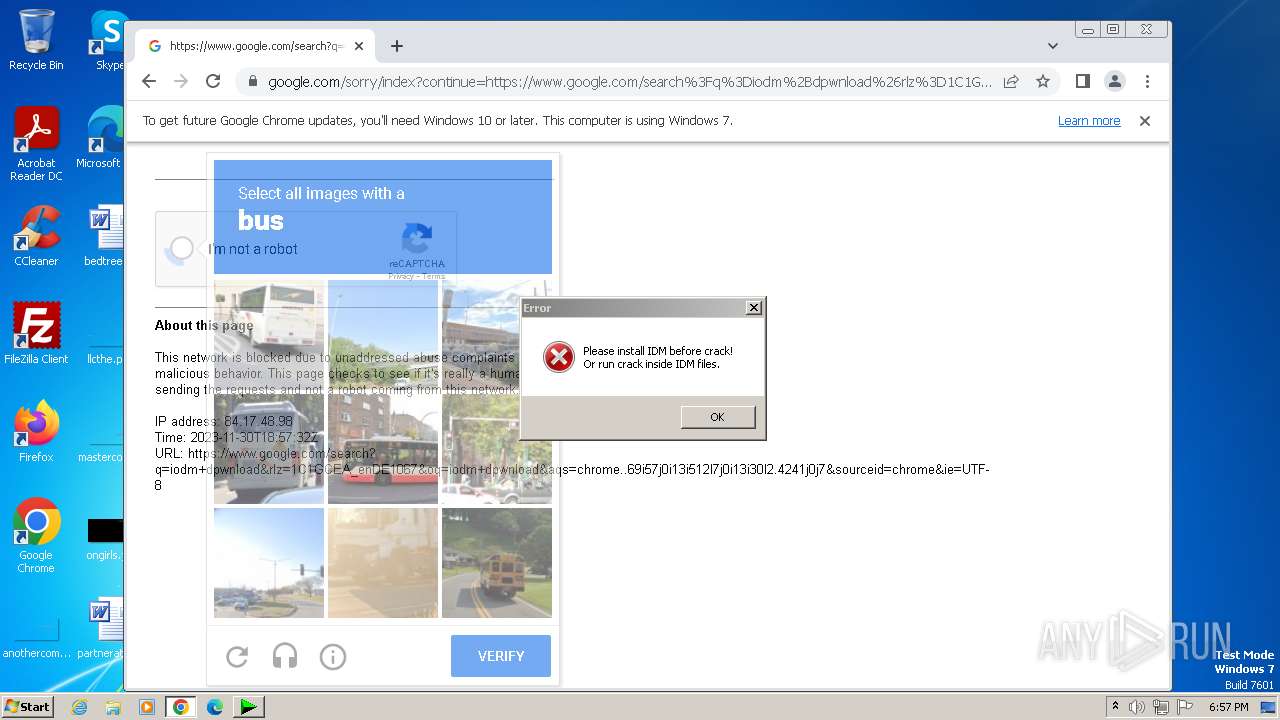
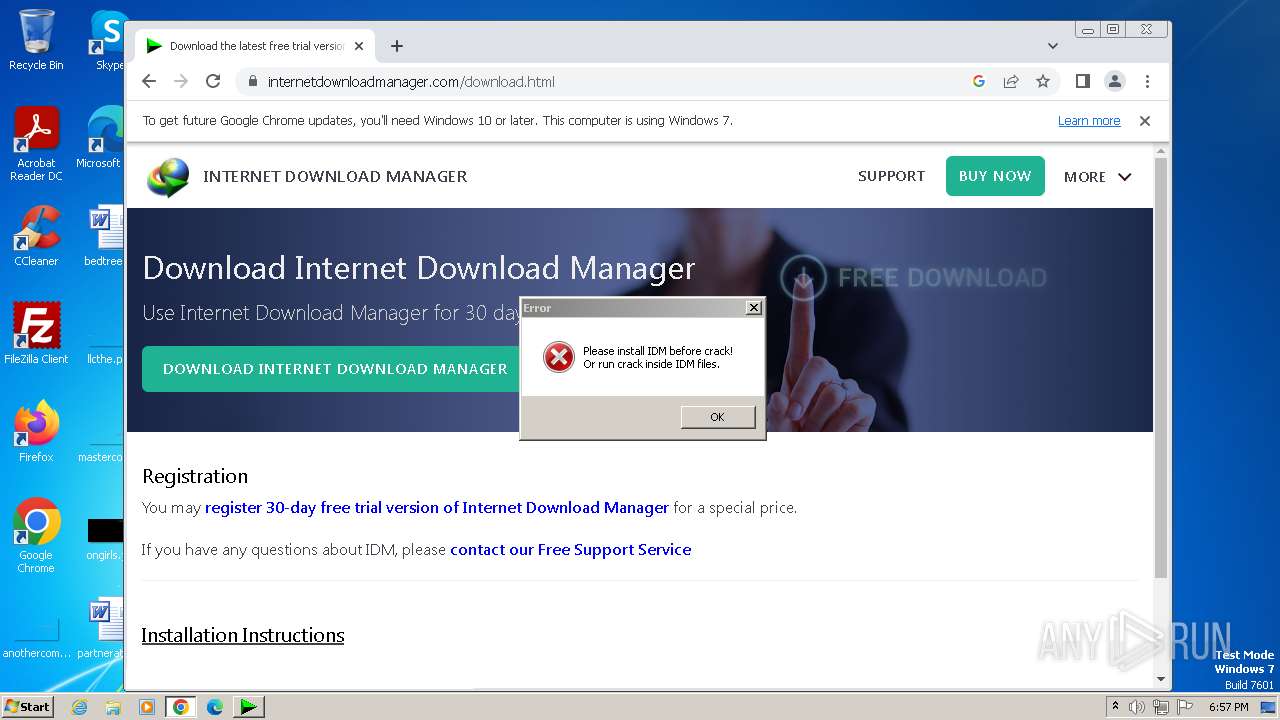
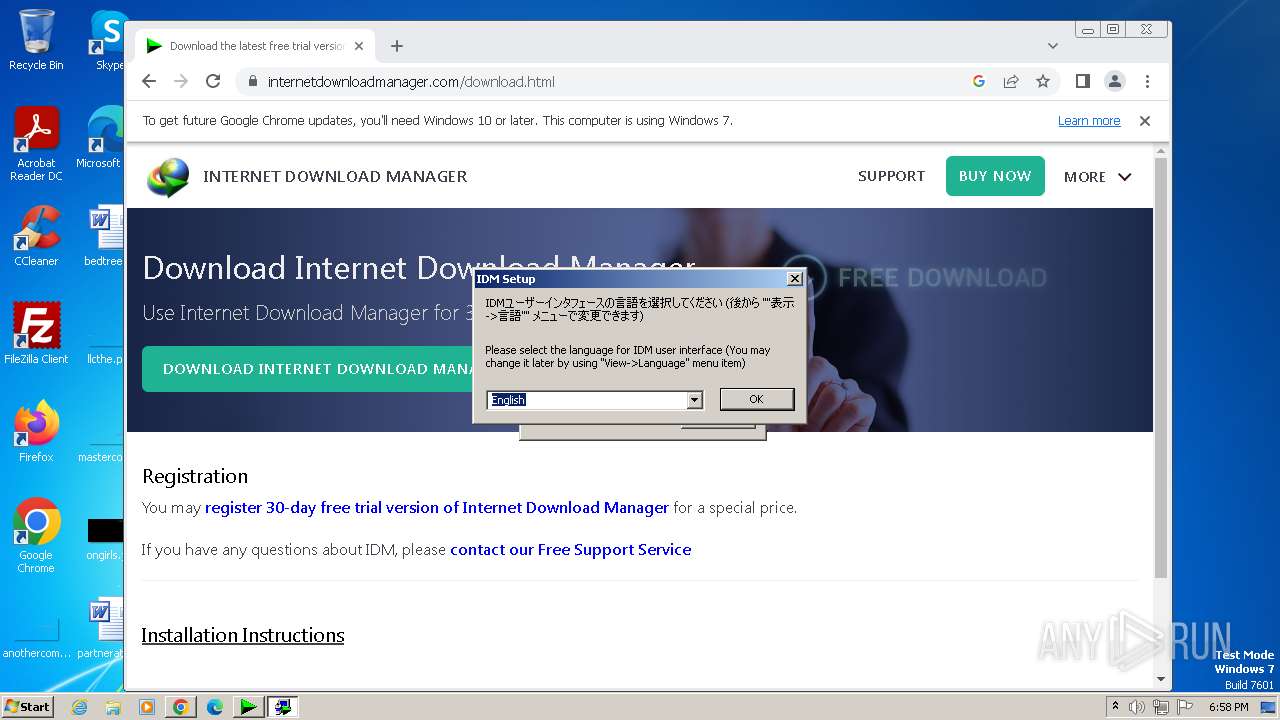
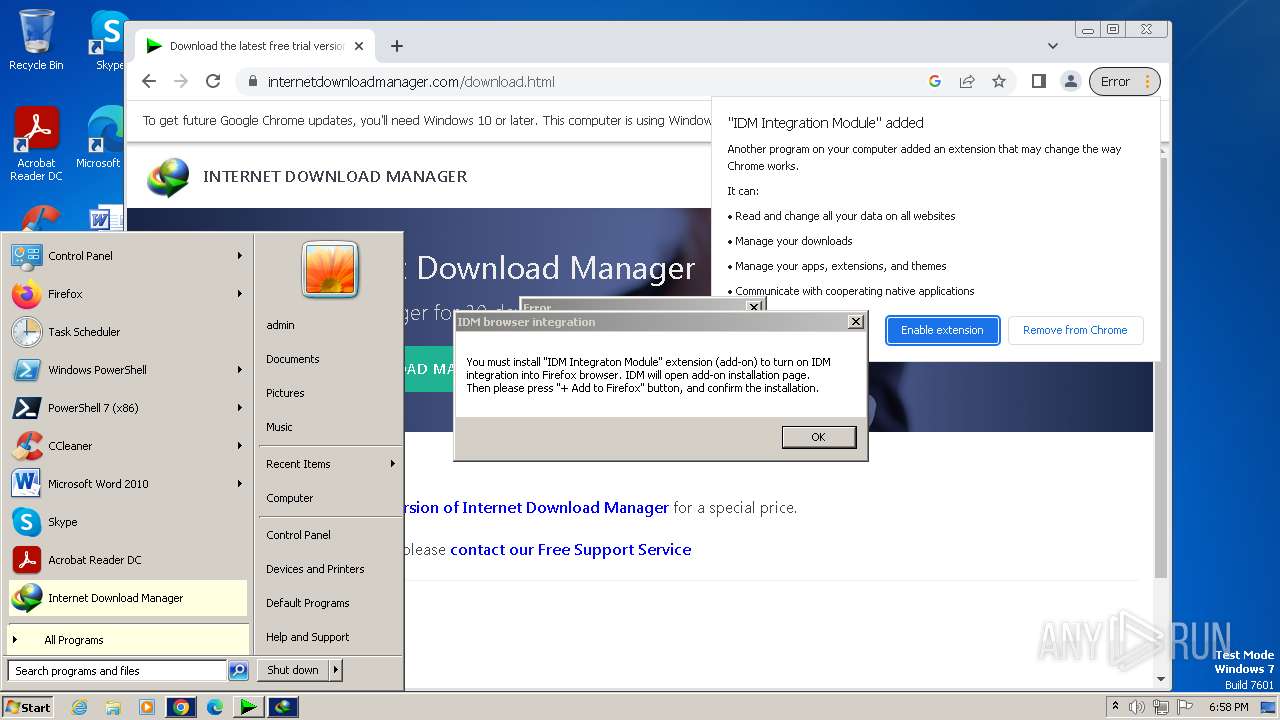
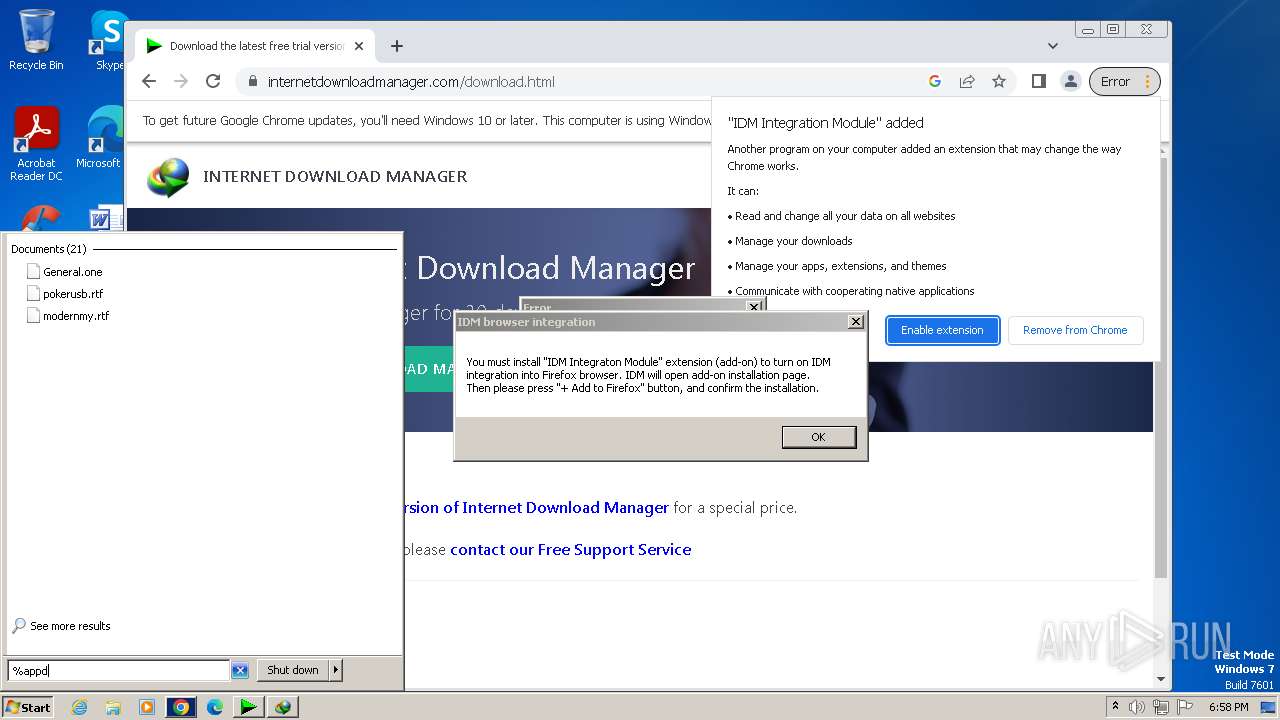
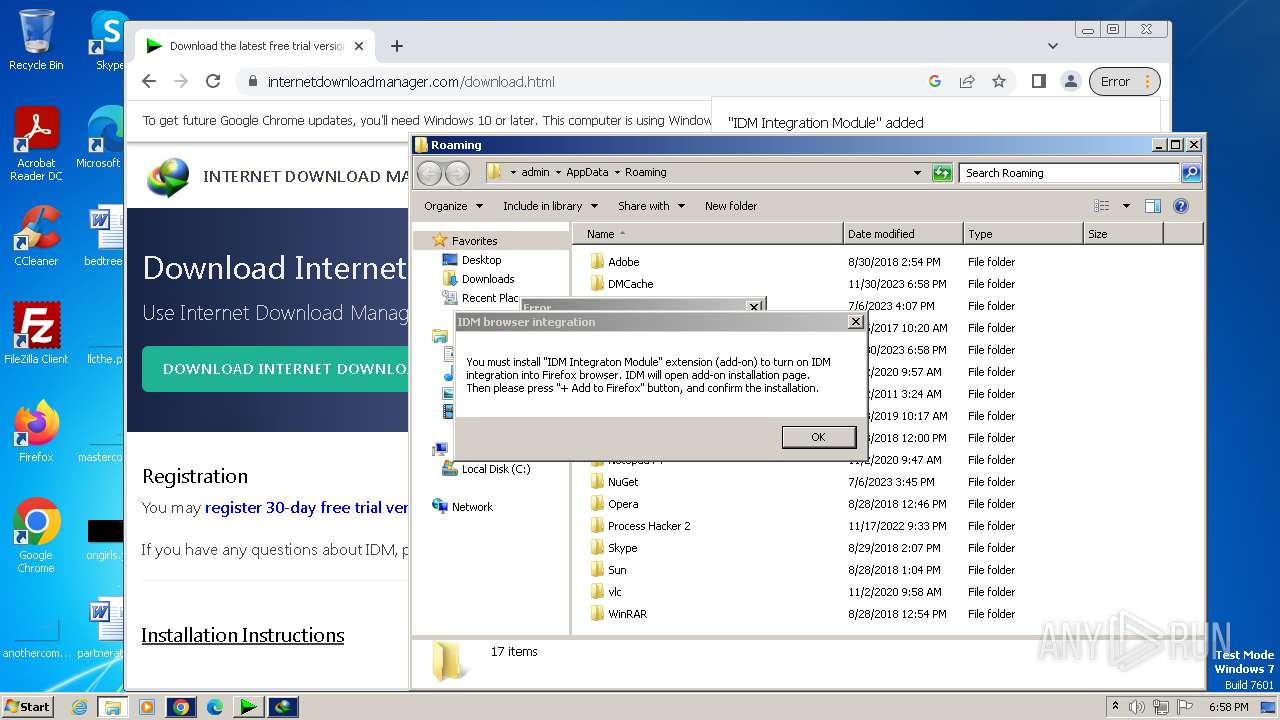
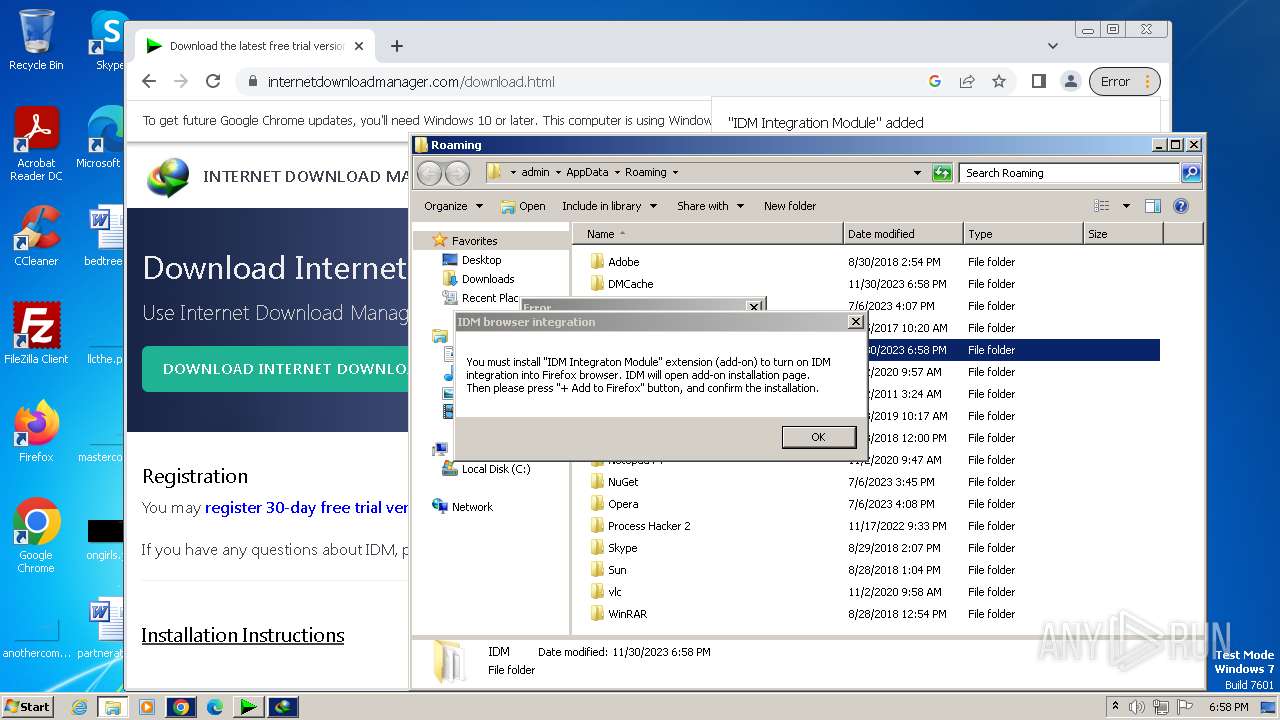
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2AB7A4477F4C4B6D7E6371D1EB141B1E |
| SHA1: | 688D3E884D9EBD66870FF0D1D4845FD7732B6F7C |
| SHA256: | 3205DBB244DE8D75BE0AFB501C4711D126CC877223F81428BF2FC761FAADB682 |
| SSDEEP: | 768:7YHVPFYTwF8PJ4GrwfBKtpohqltfW/0yuxT/7SRNBraB6Af2S:uVPFYW6xrwVkfFTjKBrLAfB |
MALICIOUS
Creates a writable file in the system directory
- rundll32.exe (PID: 2744)
Starts NET.EXE for service management
- Uninstall.exe (PID: 2004)
- net.exe (PID: 2956)
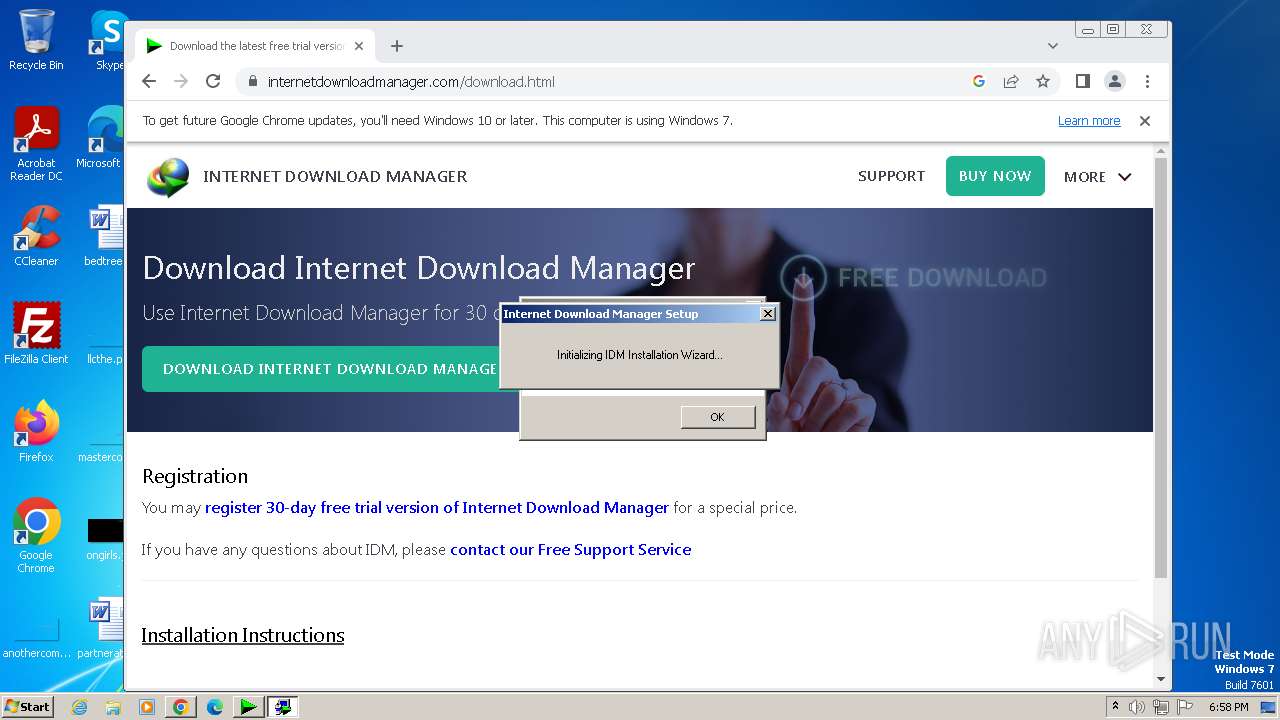
Drops the executable file immediately after the start
- IDMan.exe (PID: 2040)
- wscript.exe (PID: 2988)
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
- UnSigner.exe (PID: 3296)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 2988)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3008)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3008)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 2988)
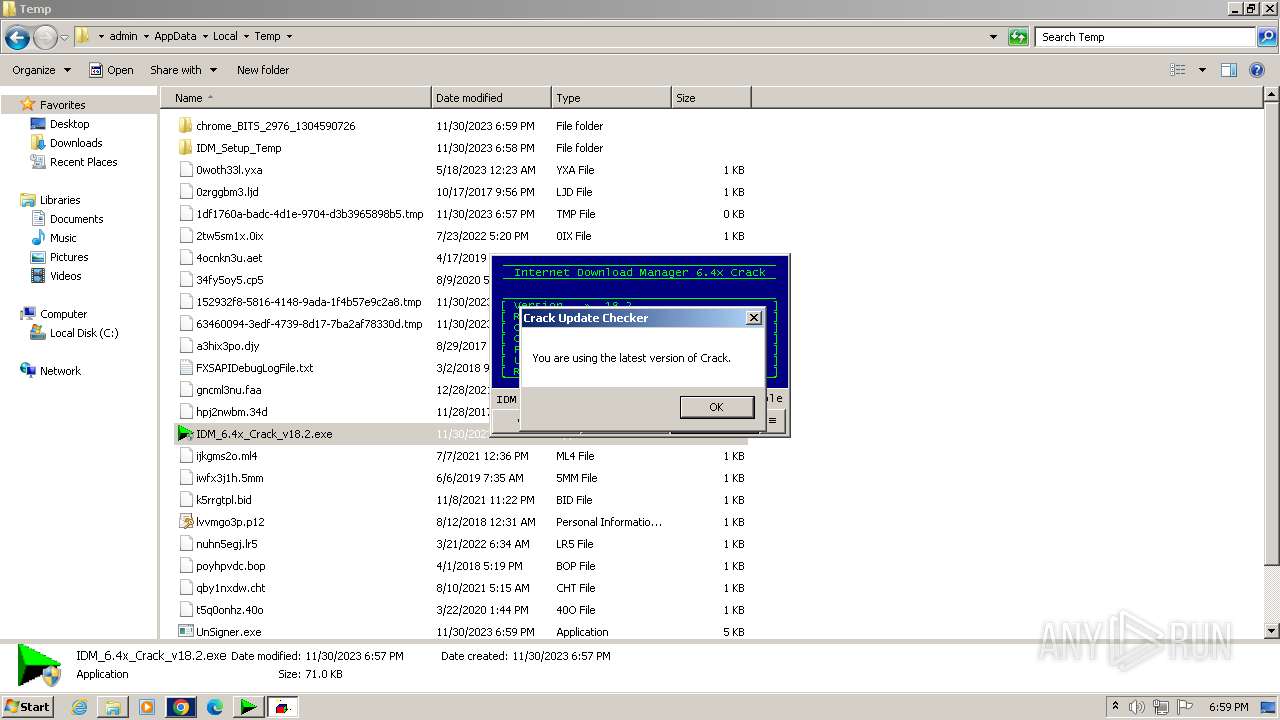
Unusual connection from system programs
- wscript.exe (PID: 3008)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3008)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3008)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3008)
SUSPICIOUS
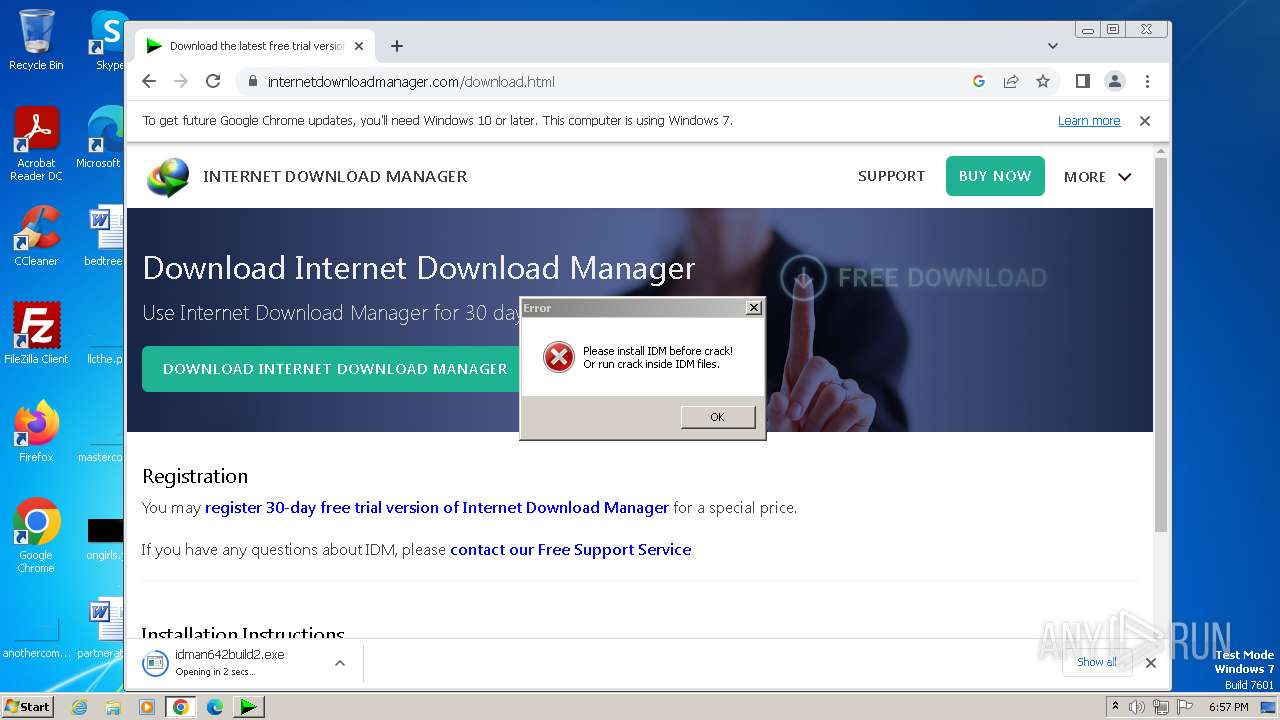
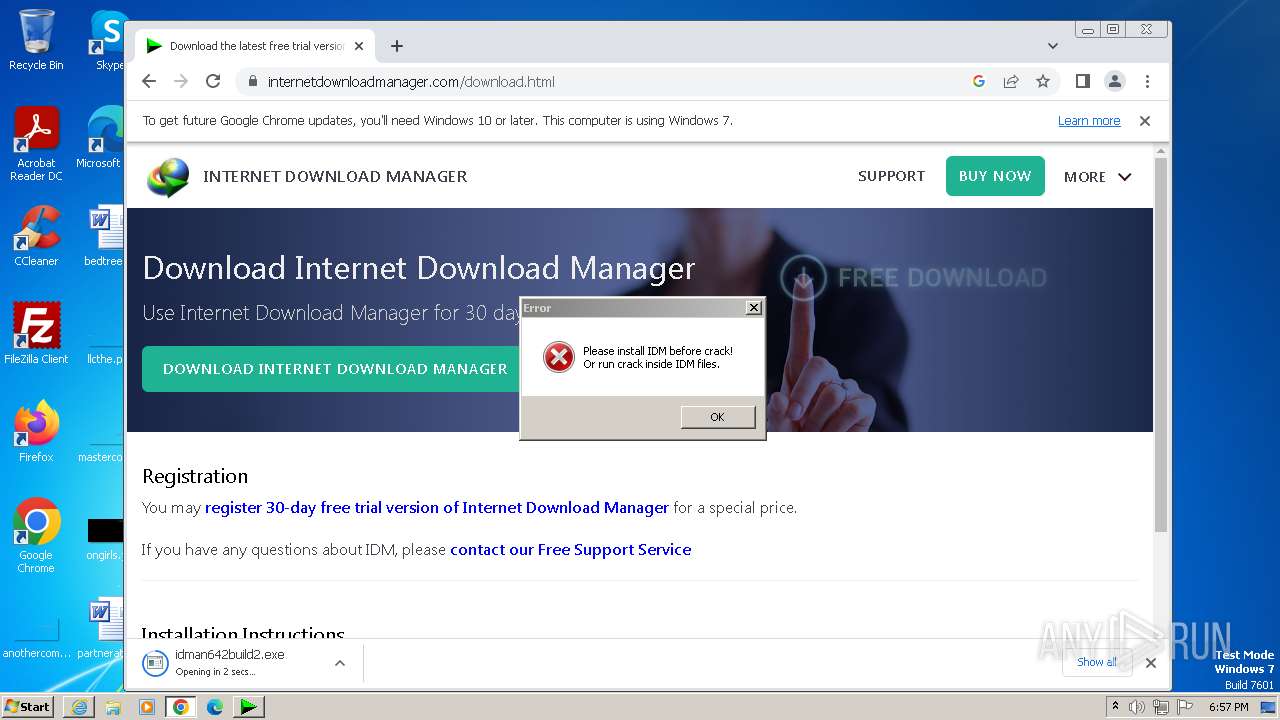
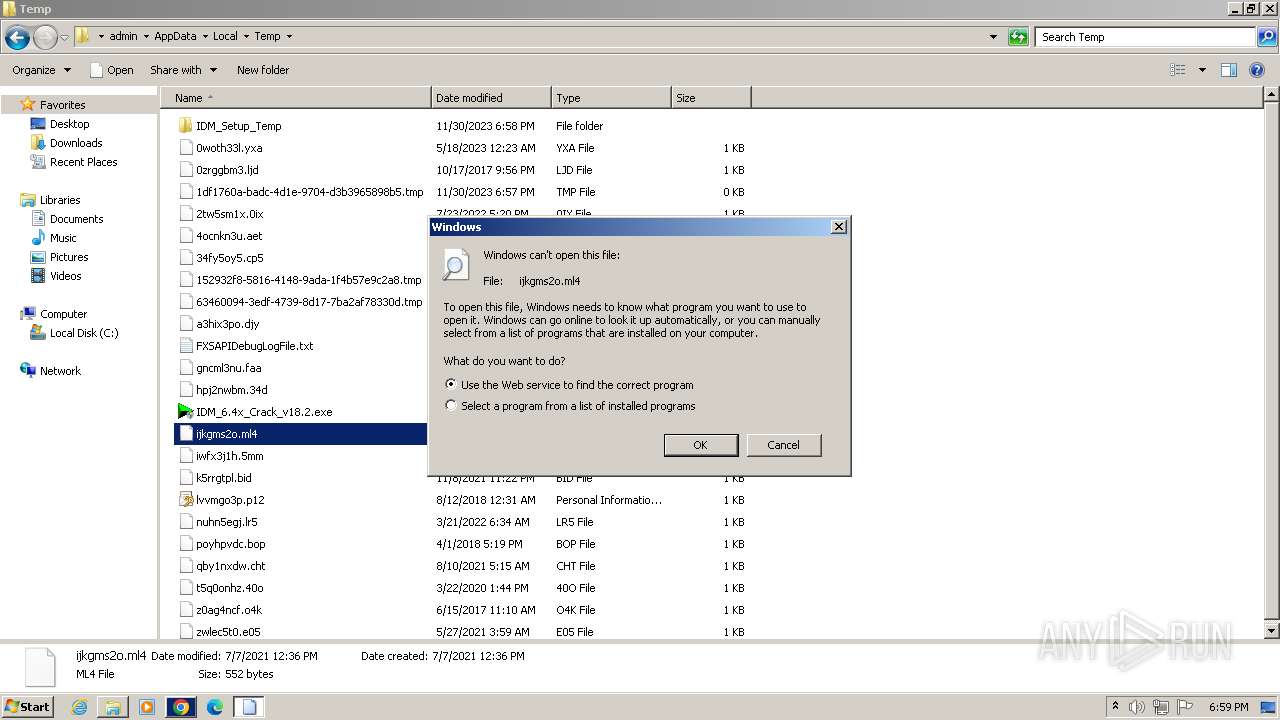
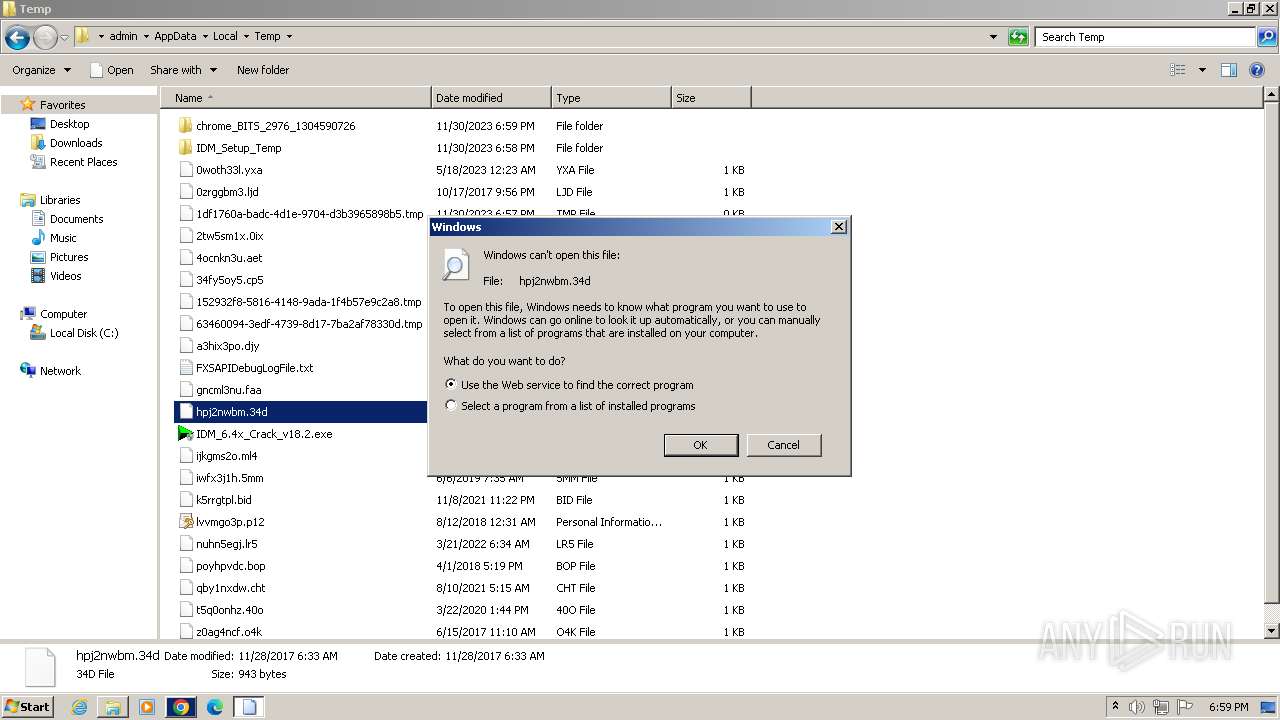
Starts application with an unusual extension
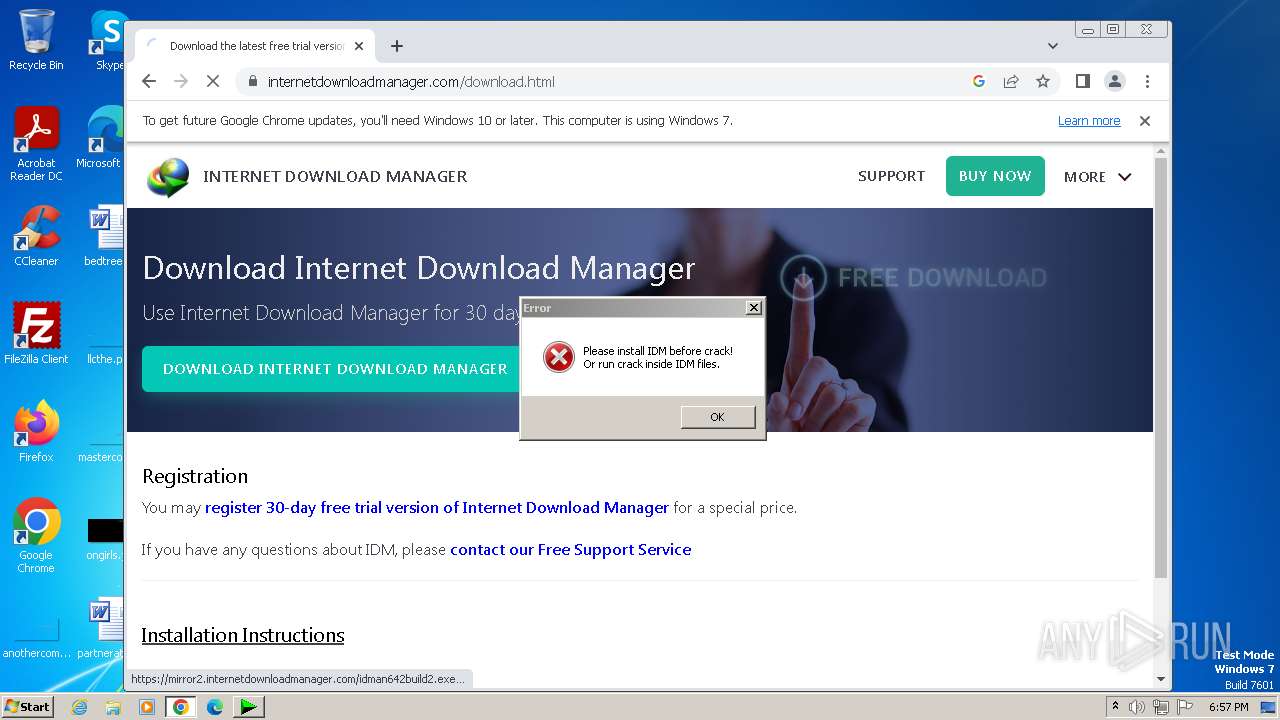
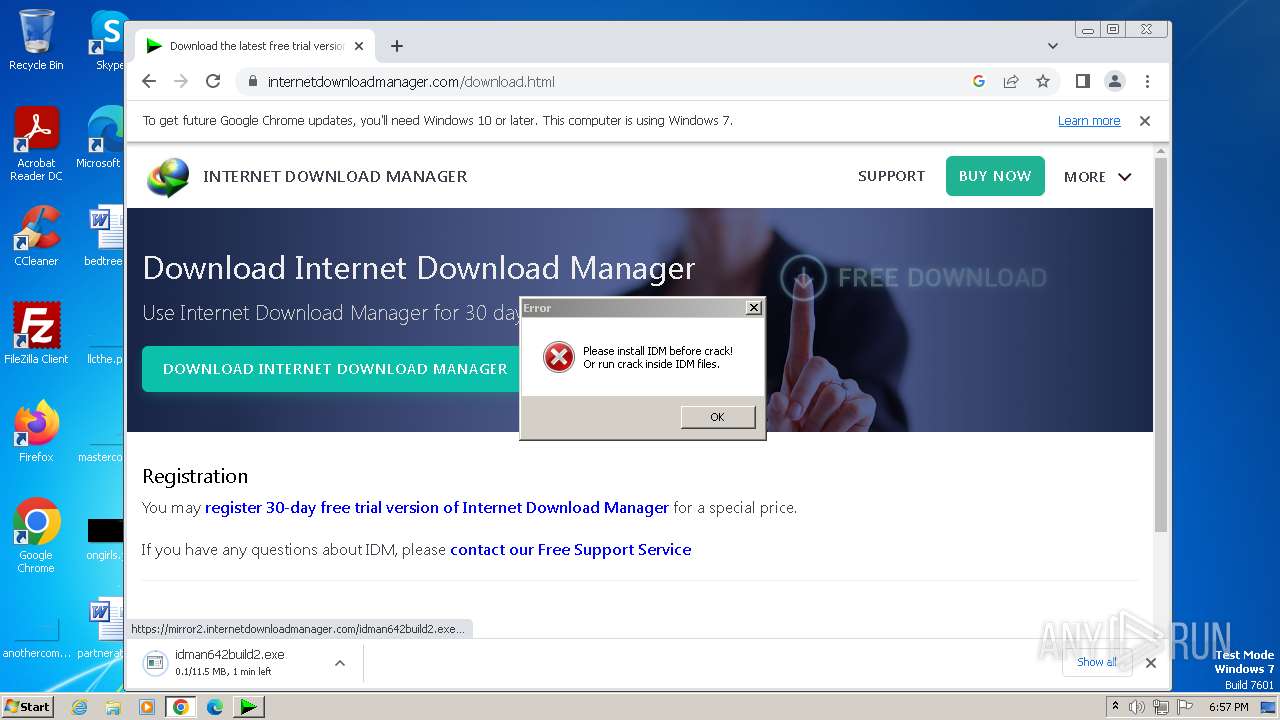
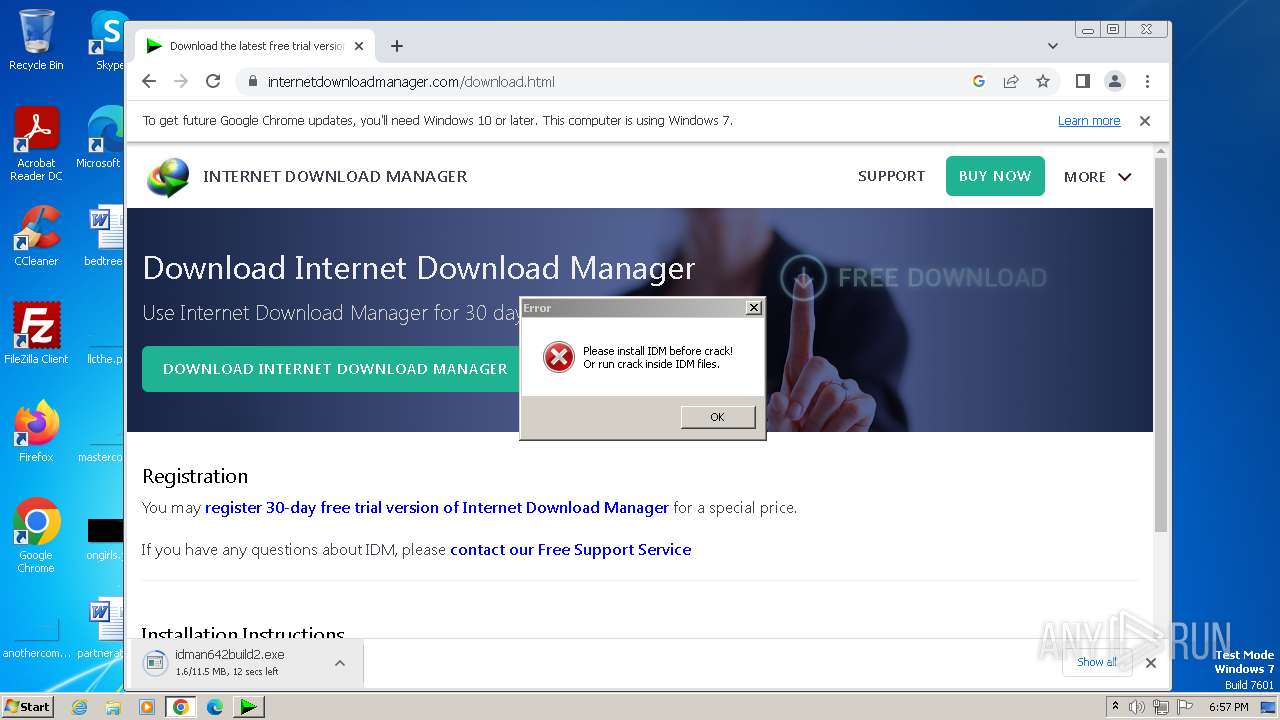
- idman642build2.exe (PID: 2988)
The process creates files with name similar to system file names
- IDM1.tmp (PID: 3152)
Reads the Internet Settings
- IDM1.tmp (PID: 3152)
- Uninstall.exe (PID: 2004)
- runonce.exe (PID: 3060)
- IDMan.exe (PID: 2040)
- IDMan.exe (PID: 1032)
- wscript.exe (PID: 3008)
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
Checks Windows Trust Settings
- IDMan.exe (PID: 2040)
- IDMan.exe (PID: 1032)
Reads security settings of Internet Explorer
- IDMan.exe (PID: 2040)
- IDMan.exe (PID: 1032)
Reads settings of System Certificates
- IDMan.exe (PID: 2040)
- IDMan.exe (PID: 1032)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 2004)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 2744)
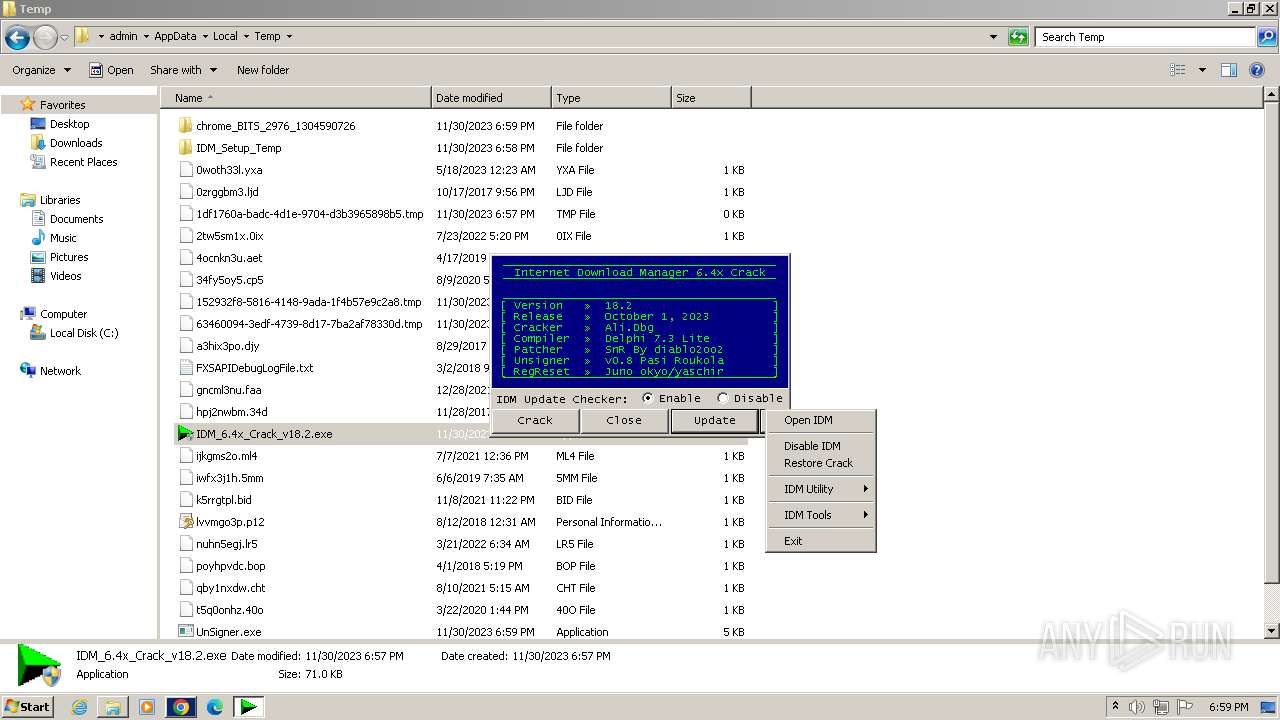
Creates or modifies Windows services
- Uninstall.exe (PID: 2004)
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 2004)
- IDMan.exe (PID: 2040)
Searches for installed software
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
The process executes VB scripts
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2988)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3008)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2988)
- wscript.exe (PID: 3008)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 3008)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
- cmd.exe (PID: 1228)
Uses TASKKILL.EXE to kill process
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
- cmd.exe (PID: 1228)
Application launched itself
- cmd.exe (PID: 1228)
Identifying current user with WHOAMI command
- cmd.exe (PID: 4020)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1228)
Powershell version downgrade attack
- powershell.exe (PID: 2552)
INFO
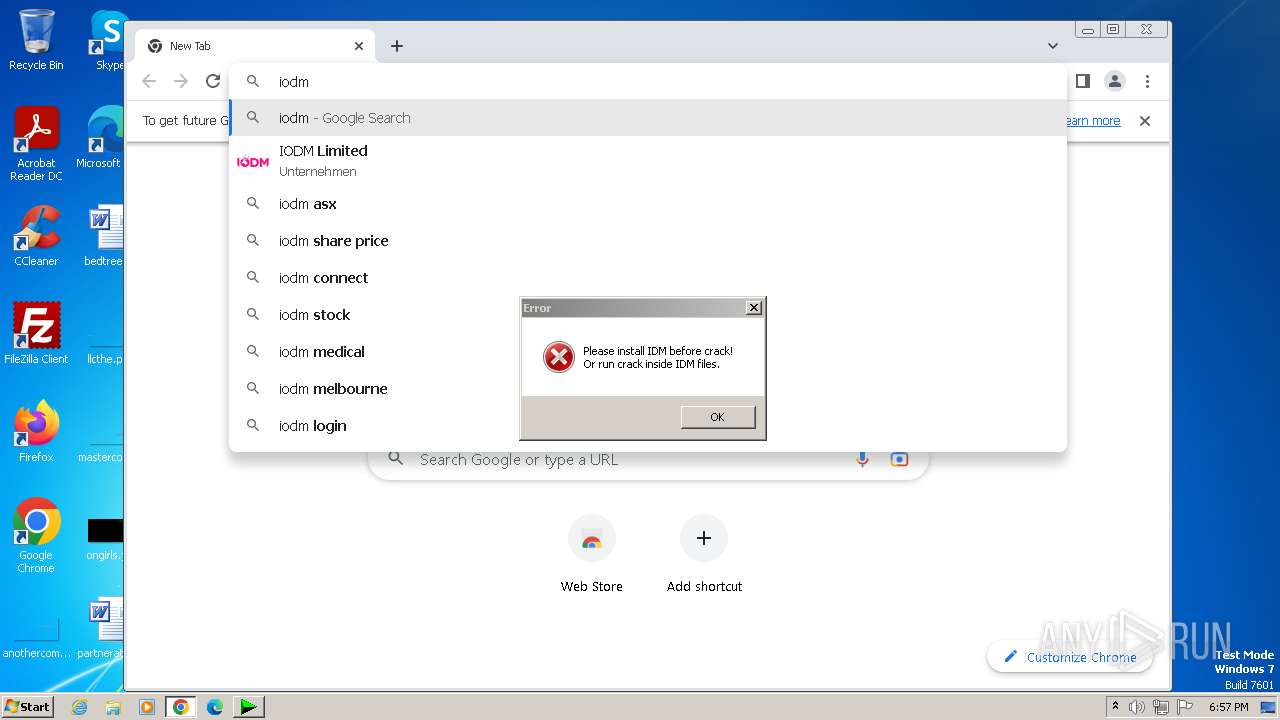
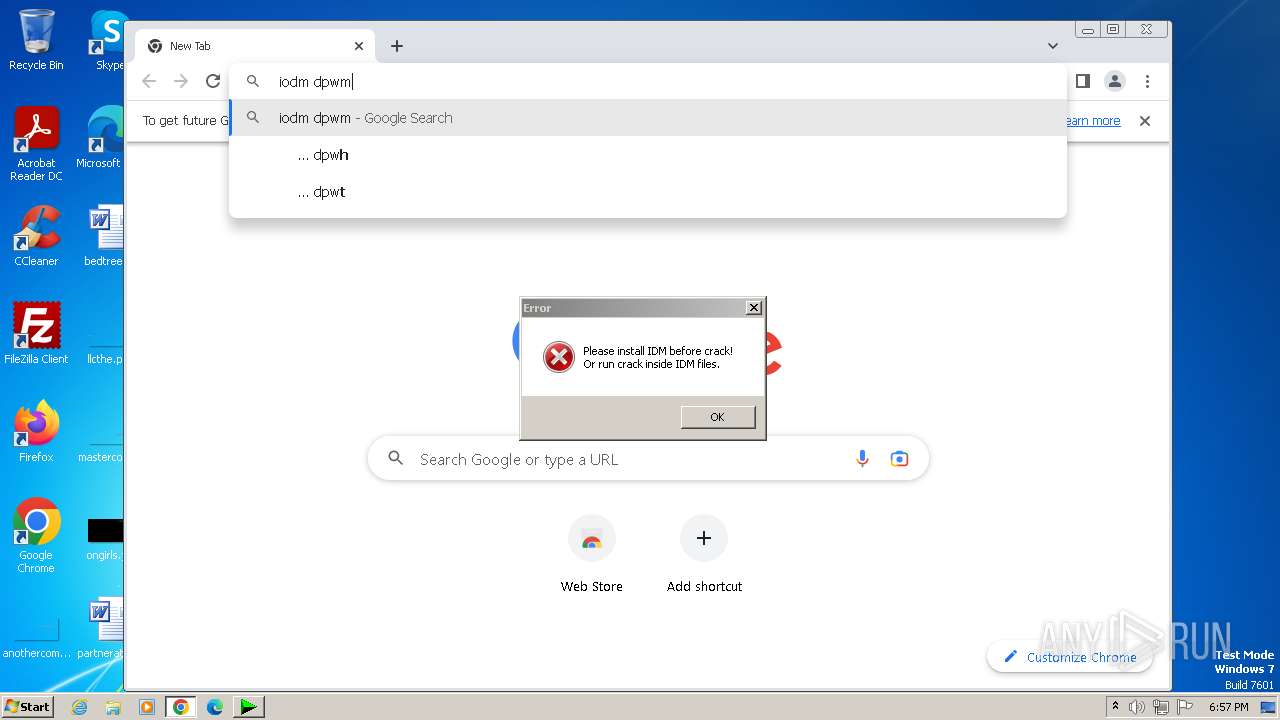
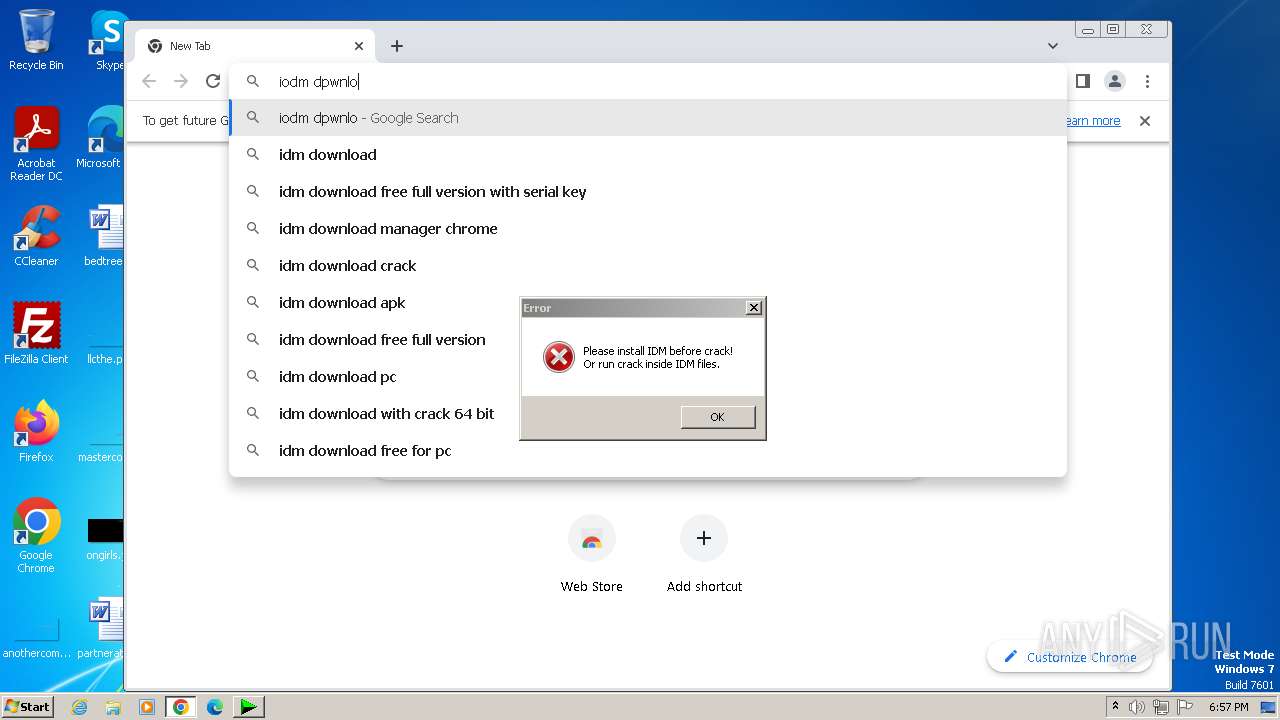
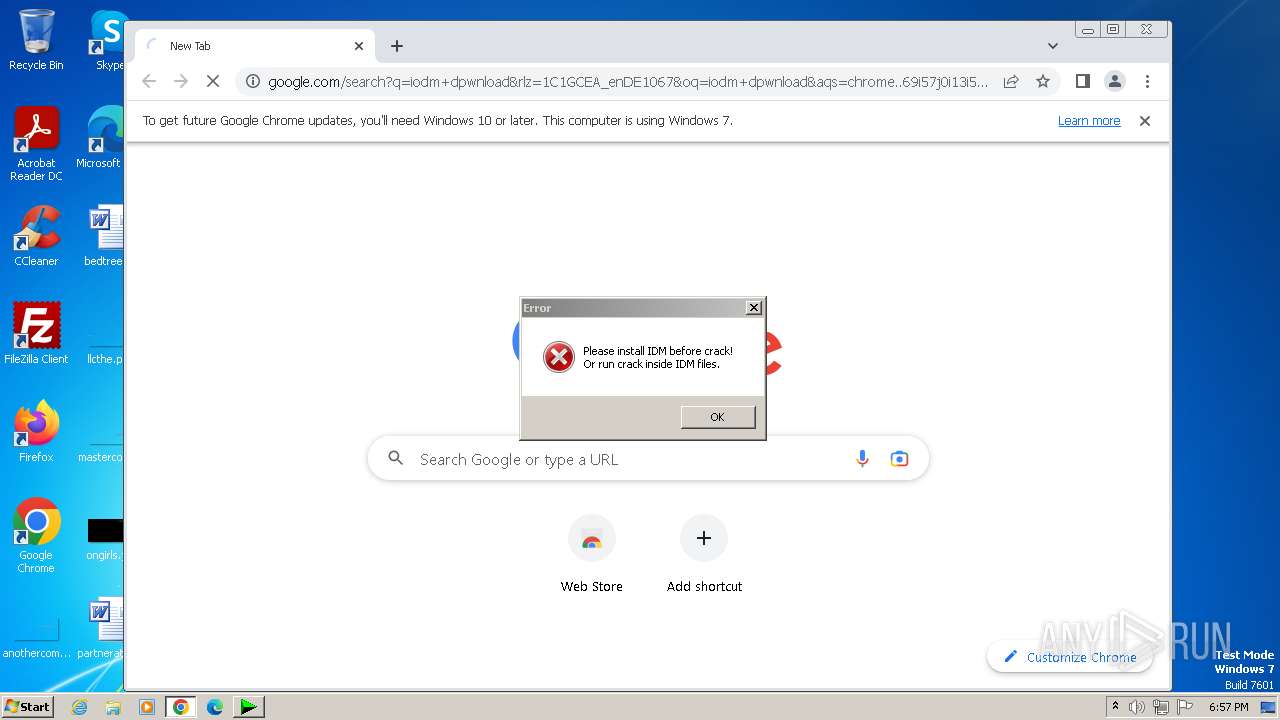
Manual execution by a user
- wmpnscfg.exe (PID: 3092)
- chrome.exe (PID: 2976)
- firefox.exe (PID: 2680)
- verclsid.exe (PID: 2052)
- IDM_6.4x_Crack_v18.2.exe (PID: 2348)
- IDM_6.4x_Crack_v18.2.exe (PID: 2736)
- rundll32.exe (PID: 2052)
- IDM_6.4x_Crack_v18.2.exe (PID: 2388)
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
- rundll32.exe (PID: 3632)
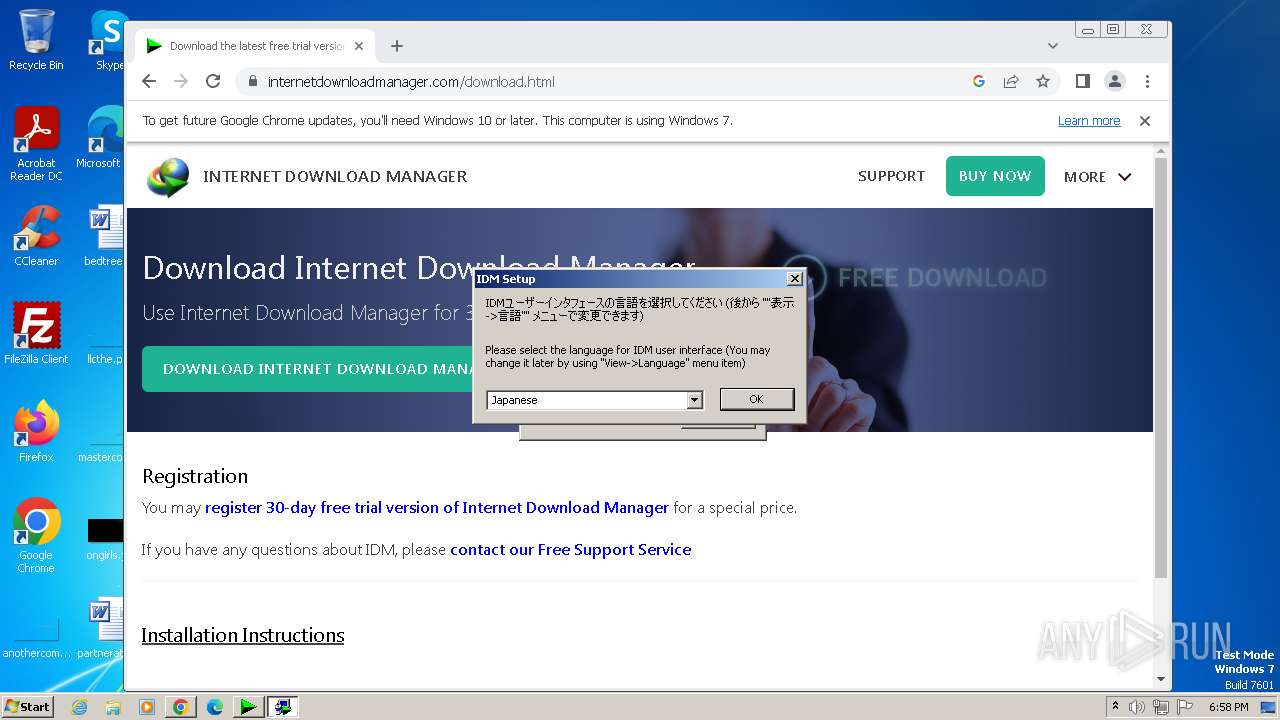
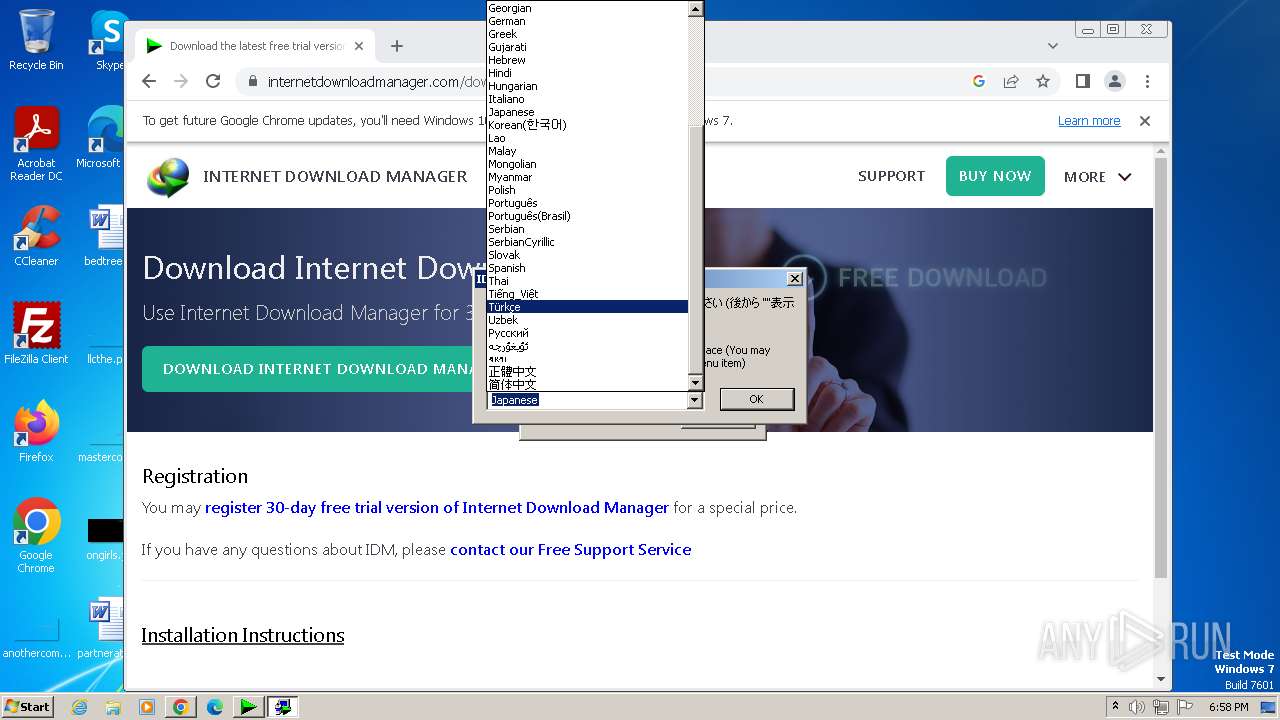
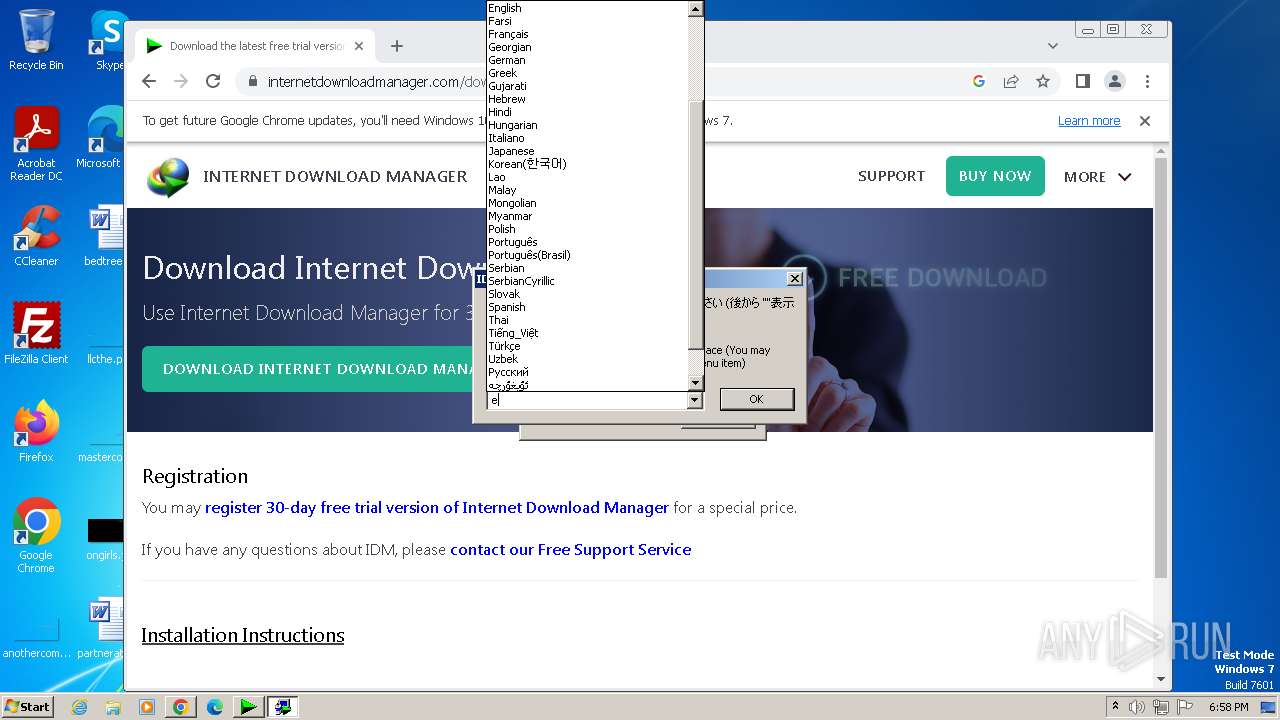
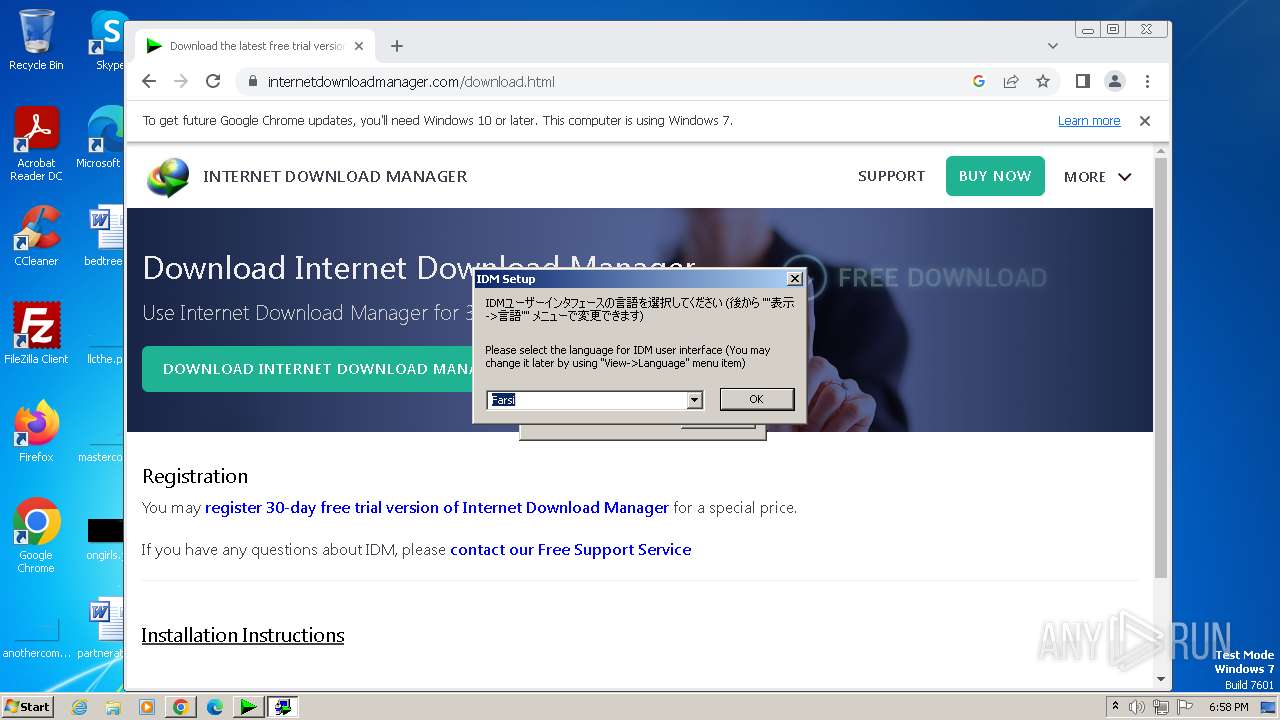
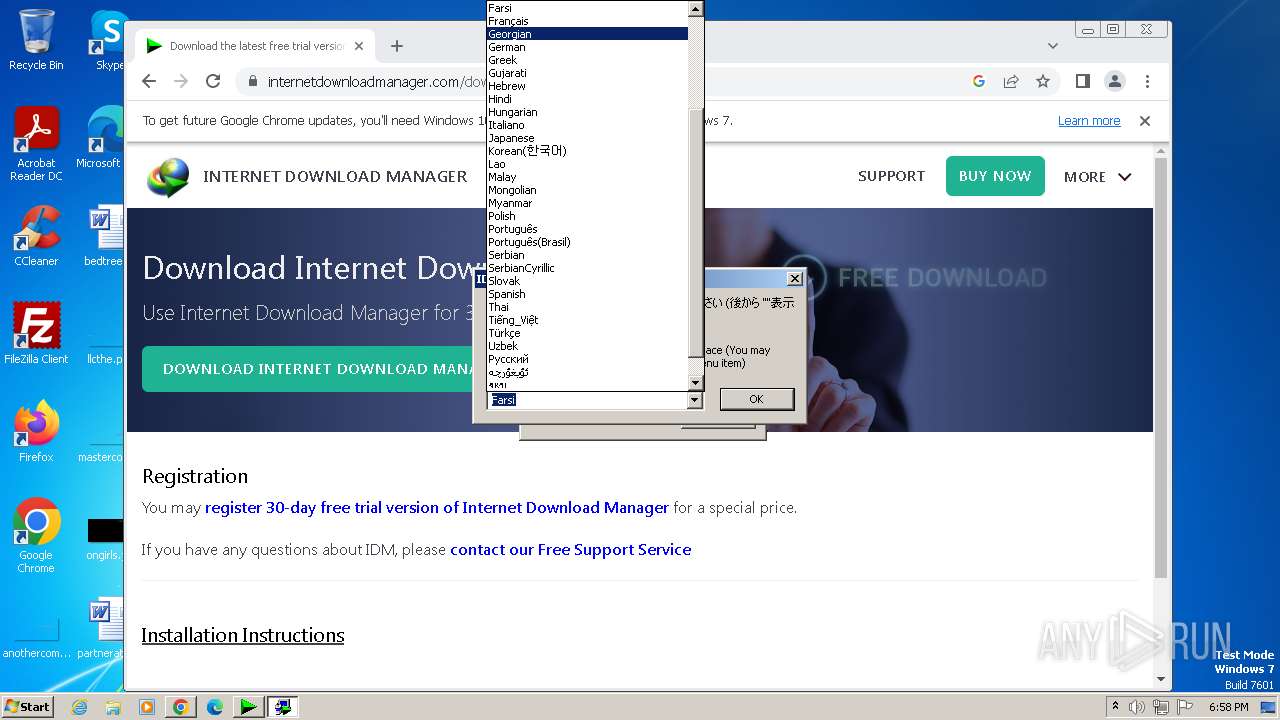
Checks supported languages
- IDM_6.4x_Crack_v18.2.exe (PID: 2720)
- wmpnscfg.exe (PID: 3092)
- idman642build2.exe (PID: 2988)
- IDM1.tmp (PID: 3152)
- idmBroker.exe (PID: 3736)
- IDMan.exe (PID: 2040)
- Uninstall.exe (PID: 2004)
- MediumILStart.exe (PID: 1784)
- IDM_6.4x_Crack_v18.2.exe (PID: 2736)
- IDMan.exe (PID: 1032)
- IEMonitor.exe (PID: 2992)
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
- UnSigner.exe (PID: 3296)
Drops the executable file immediately after the start
- chrome.exe (PID: 2976)
- chrome.exe (PID: 476)
- rundll32.exe (PID: 2744)
The process uses the downloaded file
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3128)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3092)
- IDM1.tmp (PID: 3152)
- IDMan.exe (PID: 2040)
- MediumILStart.exe (PID: 1784)
- IDMan.exe (PID: 1032)
Application launched itself
- chrome.exe (PID: 2976)
- firefox.exe (PID: 2680)
- firefox.exe (PID: 2624)
Reads the computer name
- wmpnscfg.exe (PID: 3092)
- IDM1.tmp (PID: 3152)
- IDMan.exe (PID: 2040)
- Uninstall.exe (PID: 2004)
- MediumILStart.exe (PID: 1784)
- IDMan.exe (PID: 1032)
- IEMonitor.exe (PID: 2992)
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
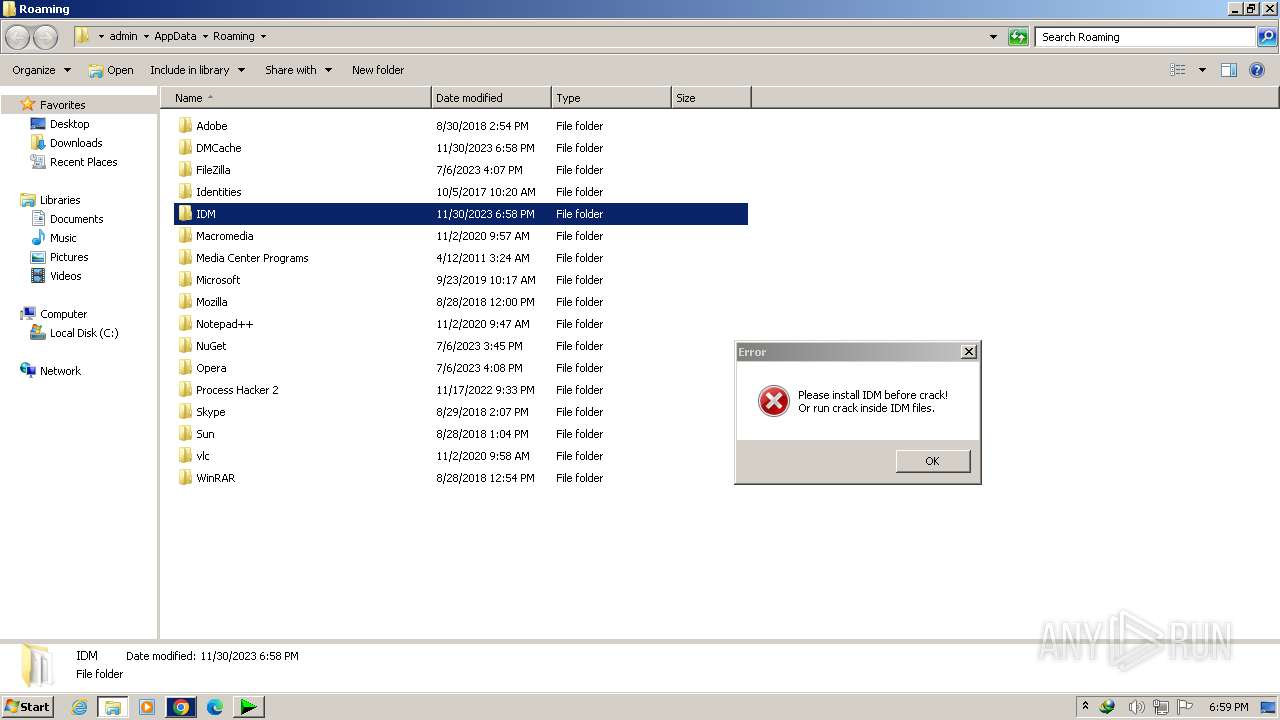
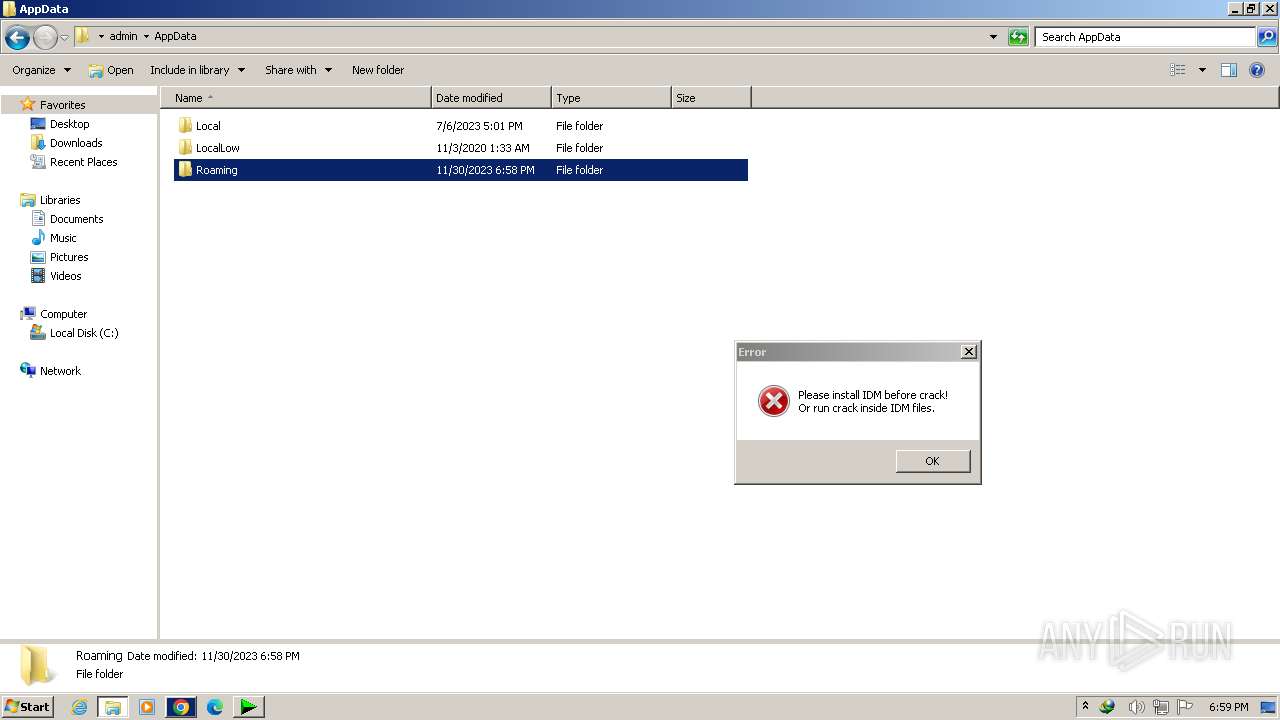
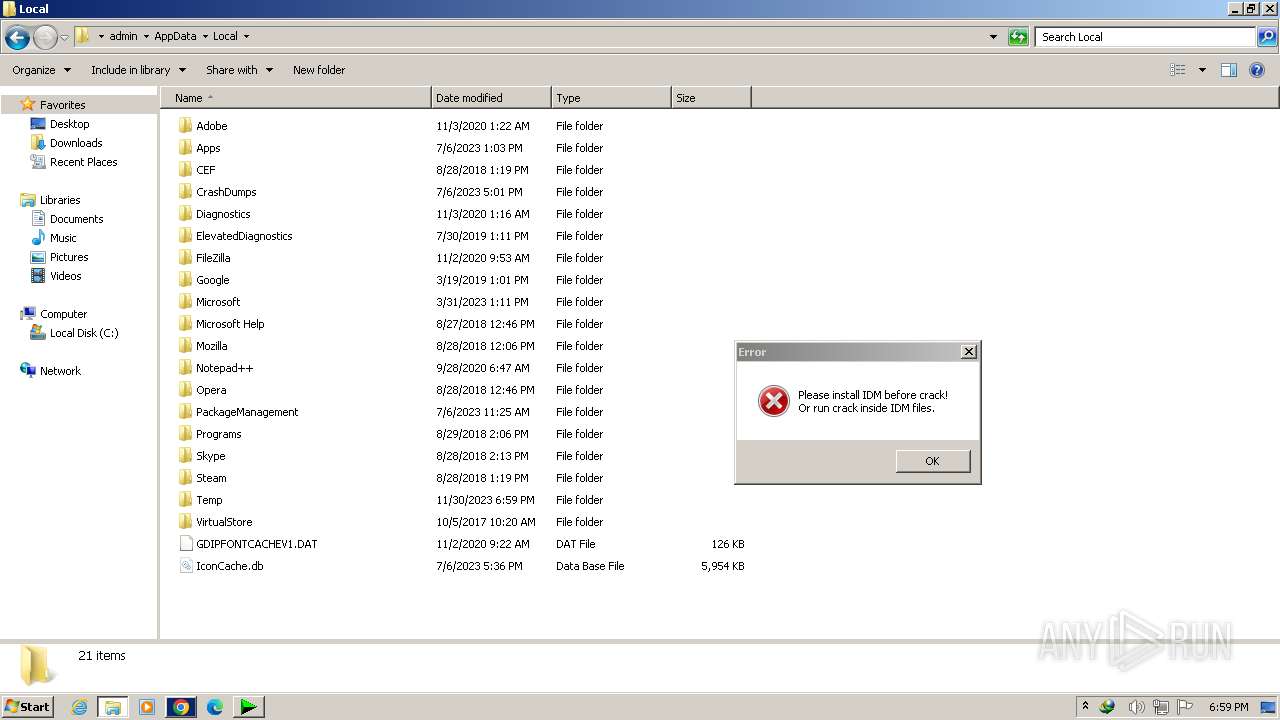
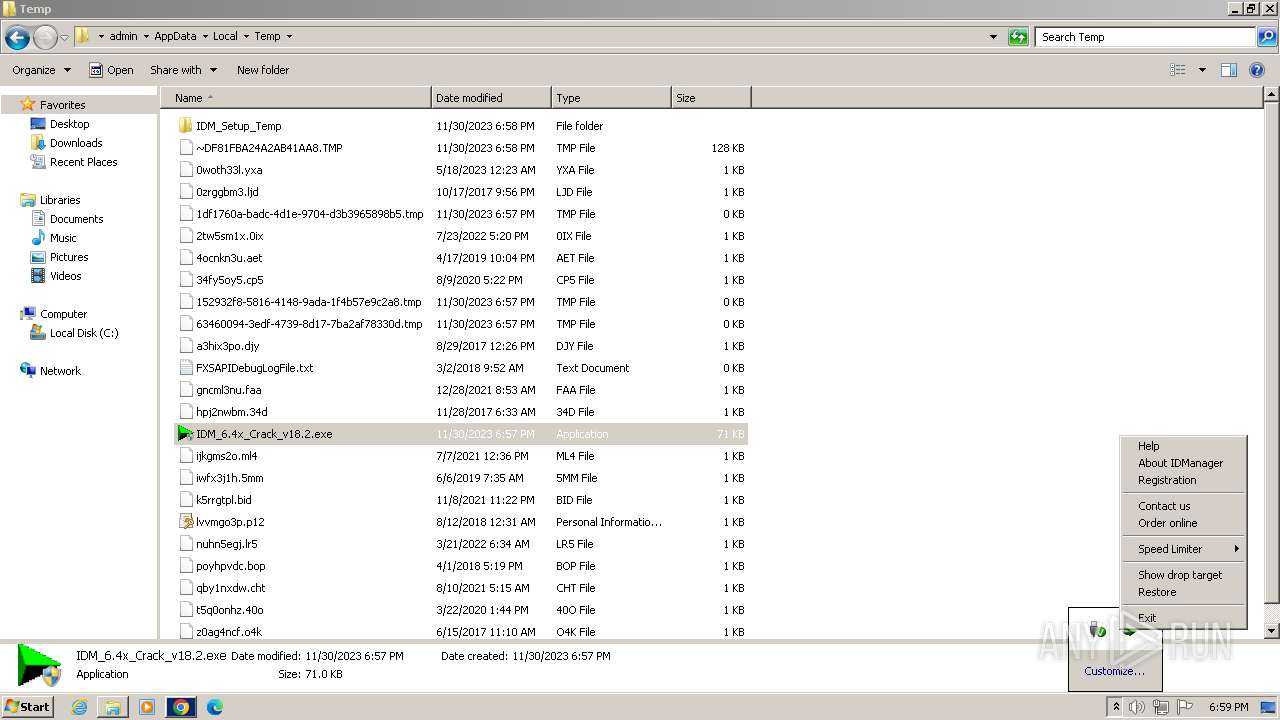
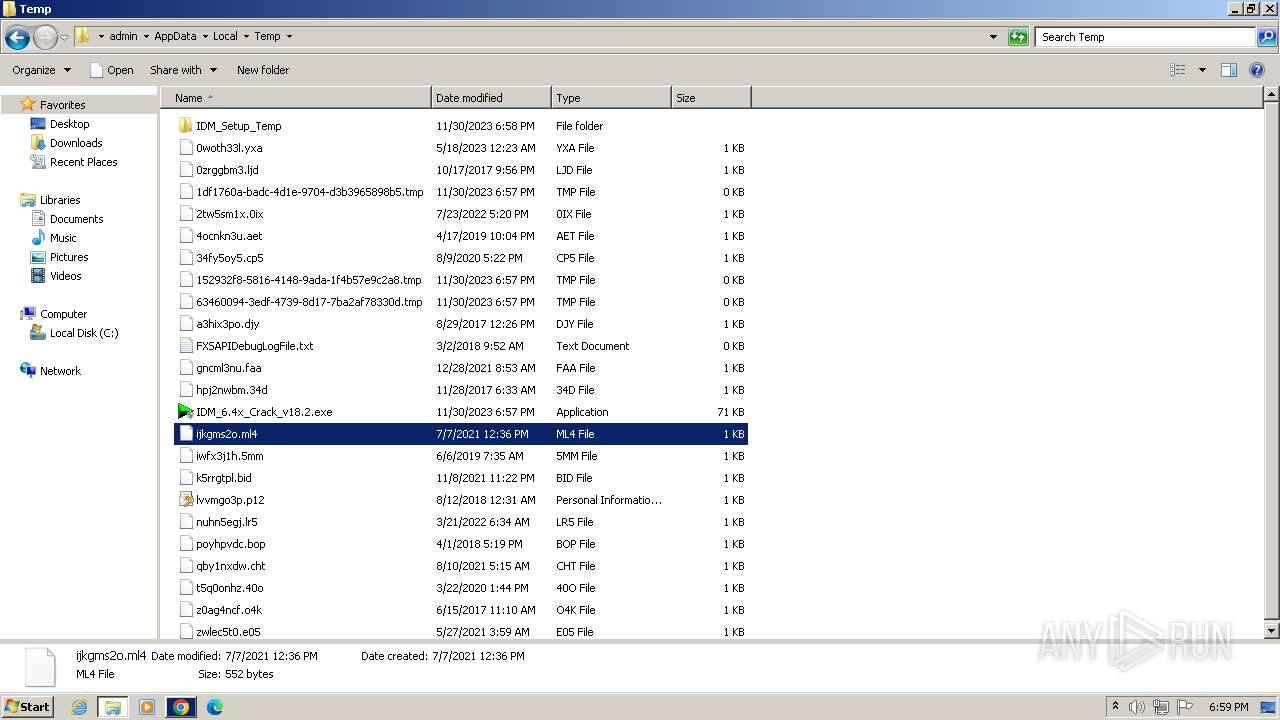
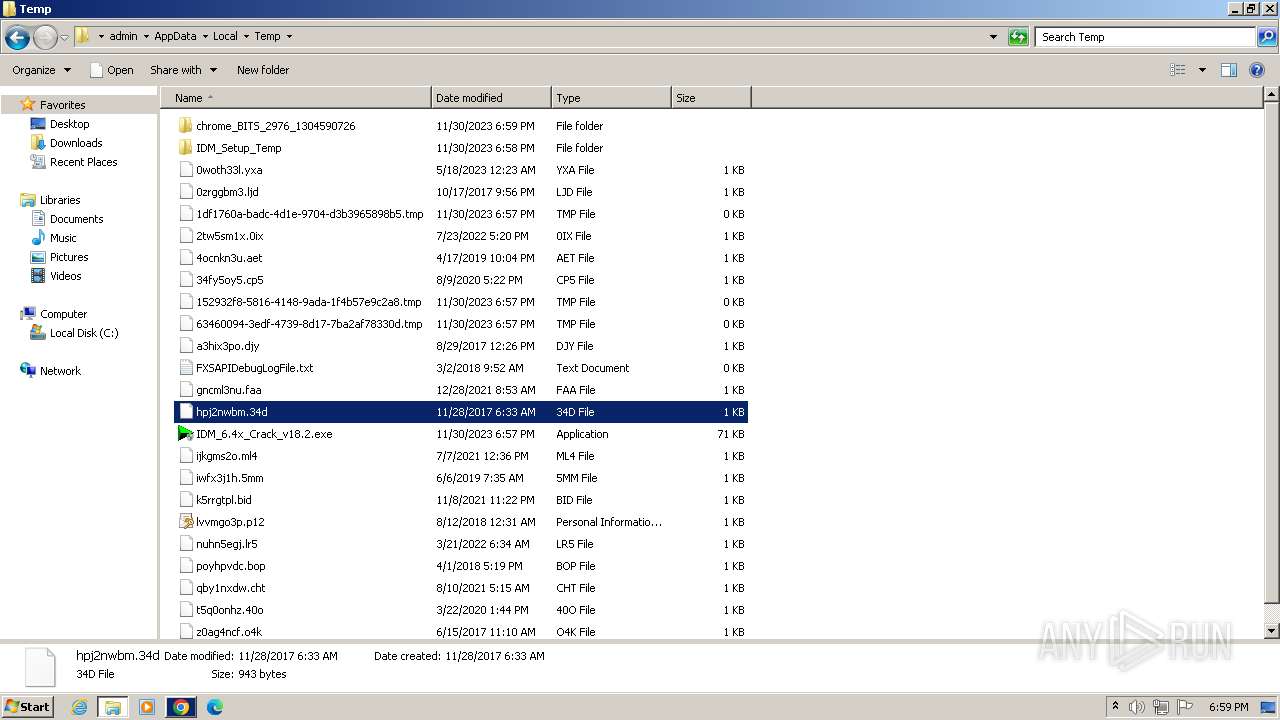
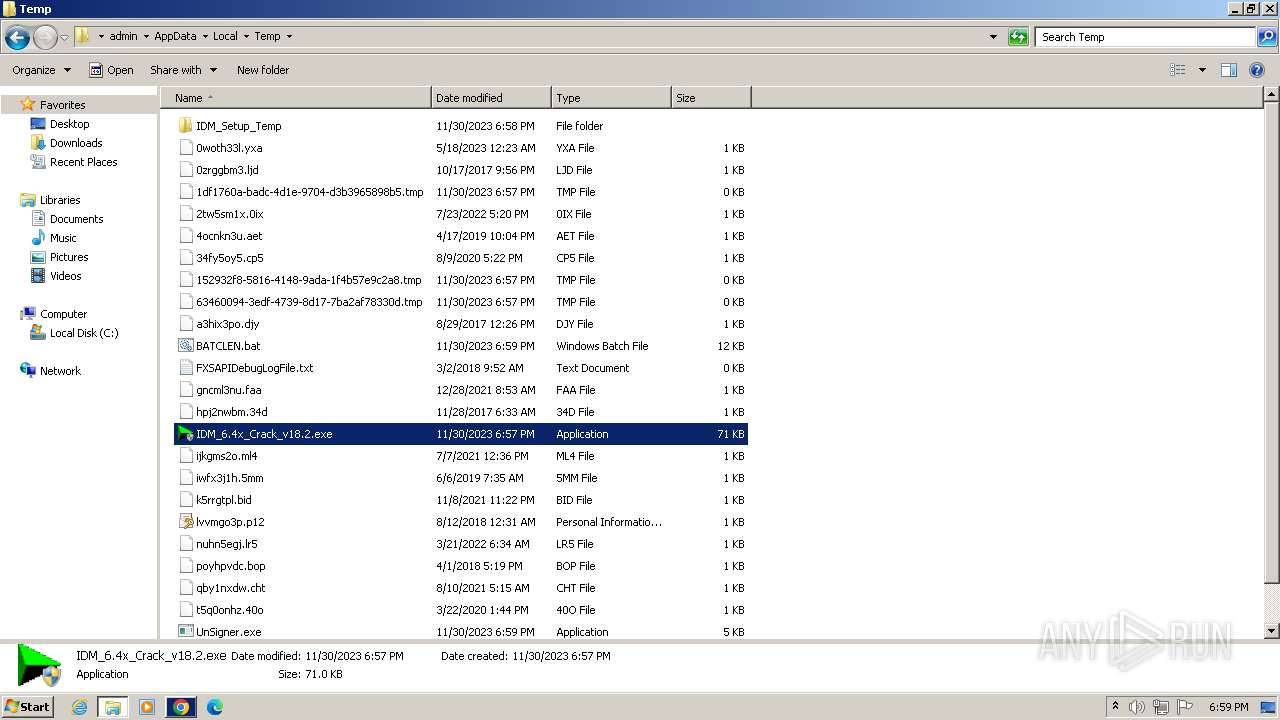
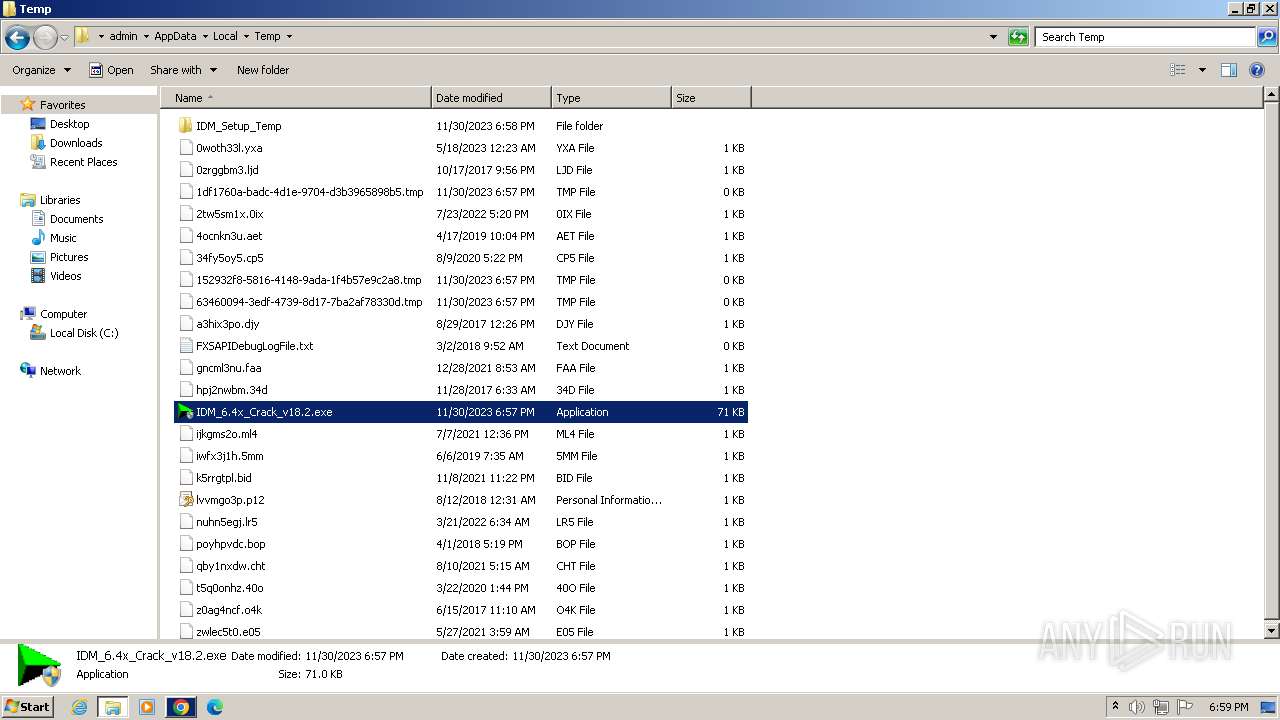
Create files in a temporary directory
- idman642build2.exe (PID: 2988)
- IDM1.tmp (PID: 3152)
- IDMan.exe (PID: 2040)
- IDMan.exe (PID: 1032)
- IDM_6.4x_Crack_v18.2.exe (PID: 2848)
Creates files in the program directory
- IDM1.tmp (PID: 3152)
- IDMan.exe (PID: 2040)
- wscript.exe (PID: 2988)
Creates files or folders in the user directory
- IDM1.tmp (PID: 3152)
- IDMan.exe (PID: 2040)
- IDMan.exe (PID: 1032)
Creates files in the driver directory
- rundll32.exe (PID: 2744)
Reads the time zone
- runonce.exe (PID: 3060)
Checks proxy server information
- wscript.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.4) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27) |
| .exe | | | UPX compressed Win32 Executable (2.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.6) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 32256 |
| InitializedDataSize: | 39424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x89c4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
416
Monitored processes
355
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1088 --field-trial-handle=1120,i,2415671248453217230,17829108206223347100,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 124 | reg query "HKLM\Software\Internet Download Manager" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 148 | reg query "HKU\.DEFAULT\Software\Wow6432Node\Download Manager" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | reg query "HKLM\Software\Classes\CLSID\{436D67E1-2FB3-4A6C-B3CD-FF8A41B0664D}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | reg query "HKU\.DEFAULT\Software\Classes\Wow6432Node\CLSID\{436D67E1-2FB3-4A6C-B3CD-FF8A41B0664D}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1996 --field-trial-handle=1120,i,2415671248453217230,17829108206223347100,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 304 | reg query "HKLM\Software\Classes\CLSID\{7B8E9164-324D-4A2E-A46D-0165FB2000EC}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | REG DELETE "HKU\.DEFAULT\Software\Classes\Wow6432Node\CLSID\{84797876-C678-1780-A556-0CD06786780F}" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | REG DELETE "HKCU\Software\Classes\Wow6432Node\CLSID\{7B8E9164-324D-4A2E-A46D-0165FB2000EC}" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | reg query "HKU\.DEFAULT\Software\Classes\CLSID\{7B8E9164-324D-4A2E-A46D-0165FB2000EC}" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
41 339
Read events
40 739
Write events
463
Delete events
137
Modification events
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
22
Suspicious files
366
Text files
98
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bf4ad.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1bf653.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1bf5b7.TMP | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1bf4ad.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65635E713D5CFC914717D1CC4CAC6989 | SHA256:4CB3EEB0369758290ABD7868DFD85D663C4AEF6C727FFF43BE693FDDBD0A6C28 | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:ACAE205AB6BCFD21F8AC19ABBC47BC6A | SHA256:4972E7A3802340F7C5C214DD0CAC645F537BA6937F38CCCC36B0CACEF079F41E | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f58a3526-f682-4246-8bc1-ff677a7eb75a.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
76
DNS requests
134
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 9.87 Kb | unknown |
2040 | IDMan.exe | GET | 200 | 2.22.242.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?10a1e2b4cd35903f | DE | compressed | 65.2 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 10.0 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 6.15 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 10.0 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 14.9 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 163 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 77.8 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | US | binary | 215 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
476 | chrome.exe | 216.58.206.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2976 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
476 | chrome.exe | 142.250.186.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
476 | chrome.exe | 172.217.16.132:443 | www.google.com | GOOGLE | US | whitelisted |
476 | chrome.exe | 142.250.184.195:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
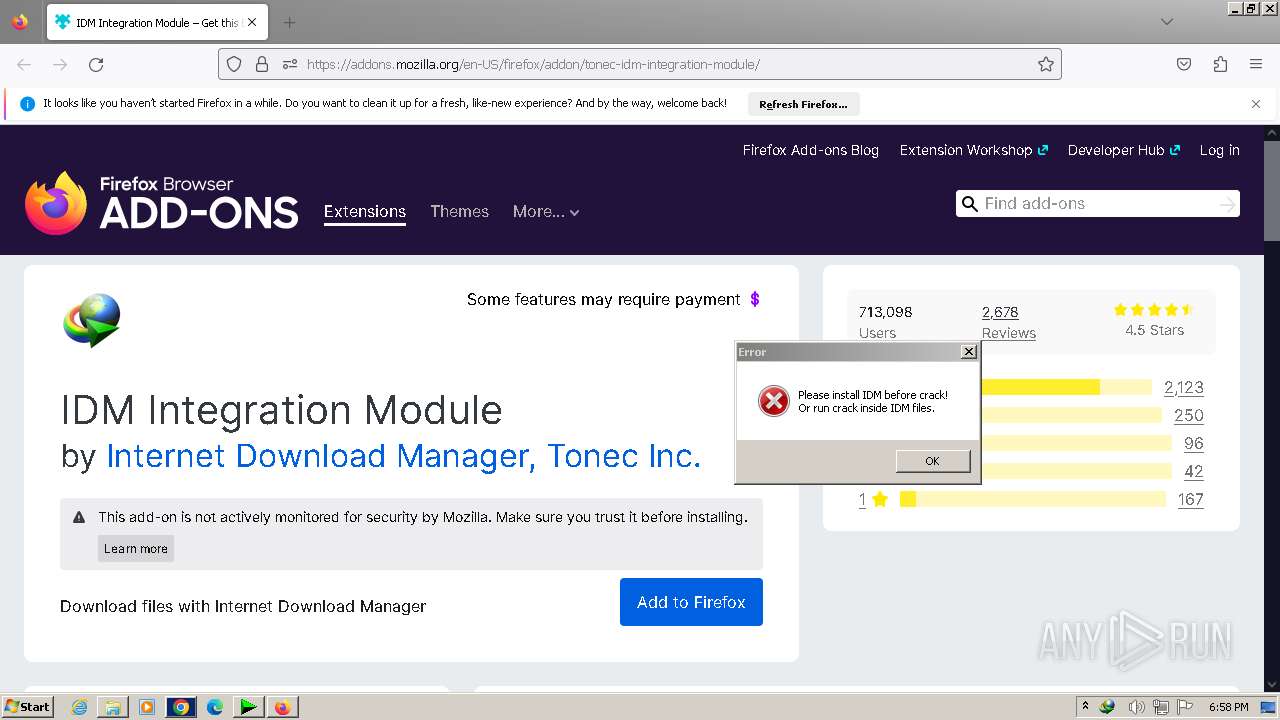
www.internetdownloadmanager.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |