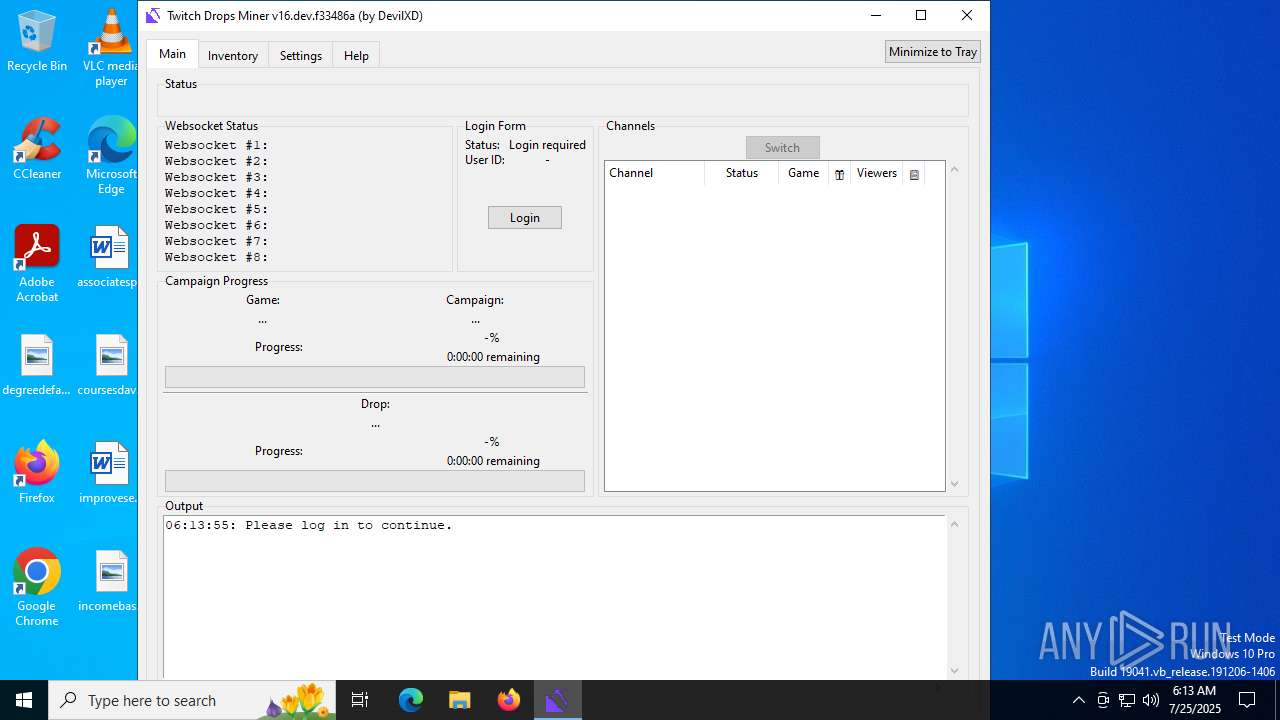
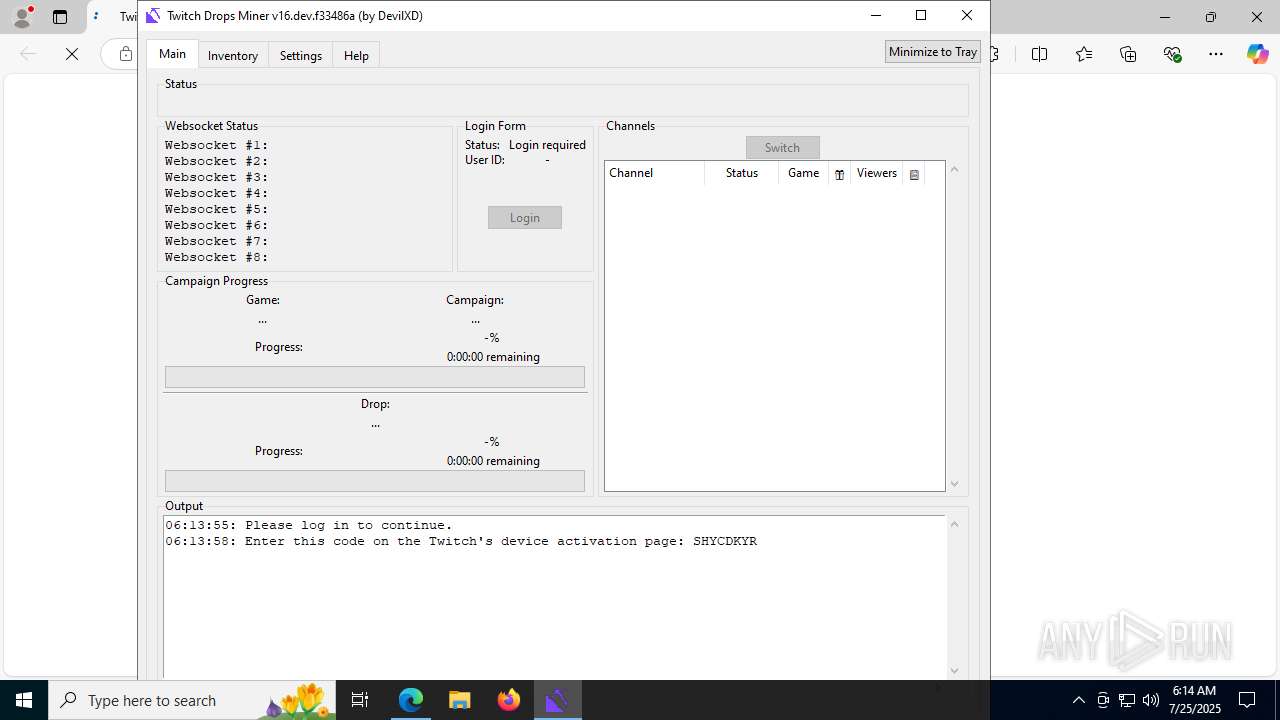
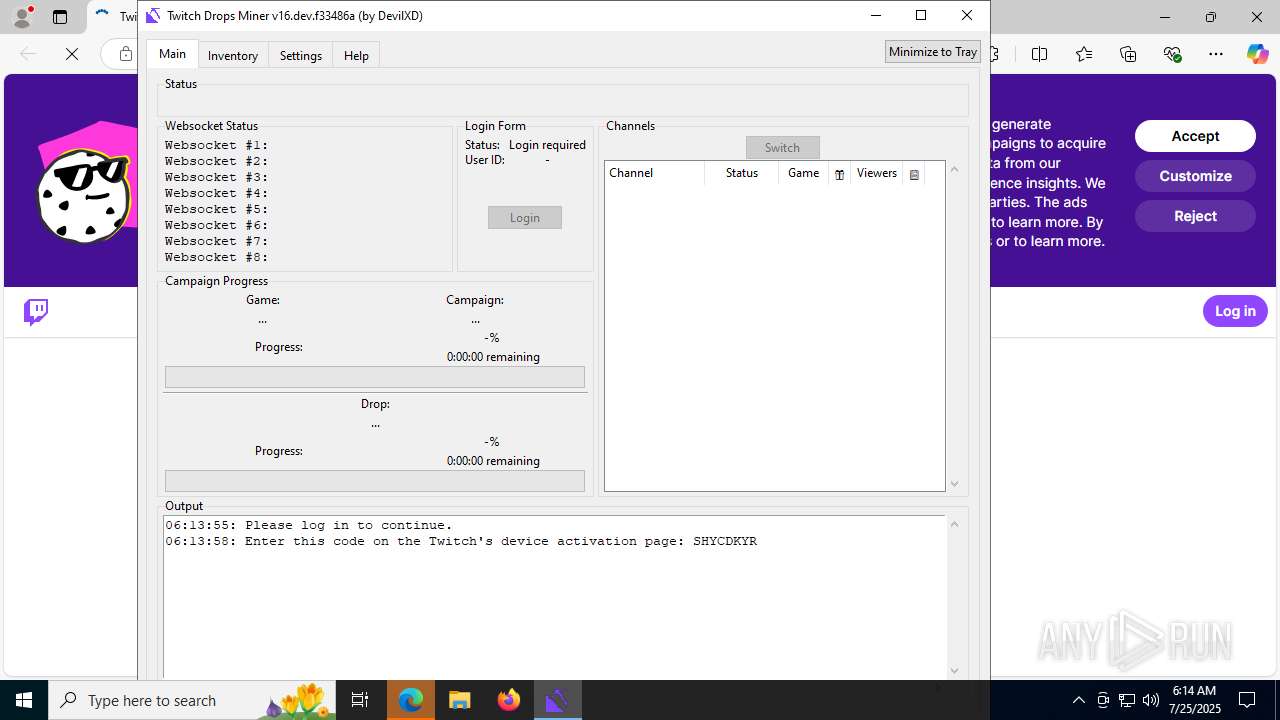
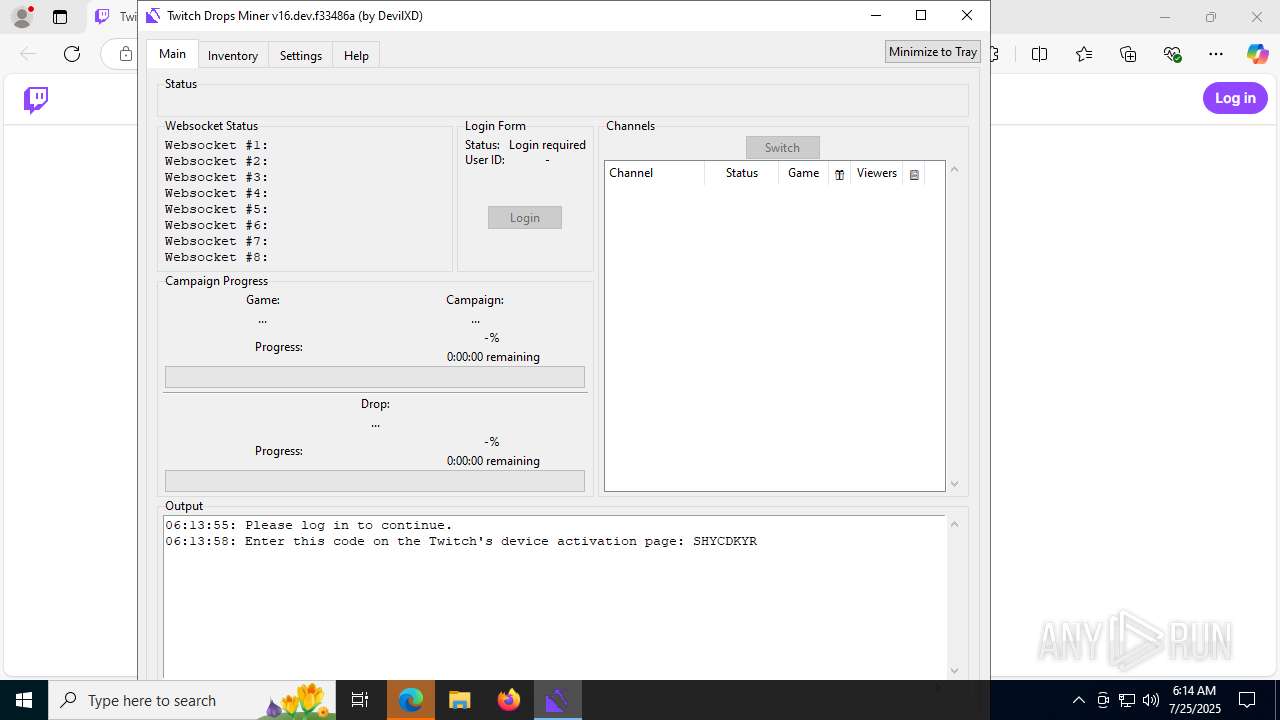
| File name: | Twitch Drops Miner (by DevilXD).exe |
| Full analysis: | https://app.any.run/tasks/3b58c34c-a602-473d-9188-83b3ce784e22 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2025, 06:13:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | ECD8942331F580C2138C8D70B119028C |
| SHA1: | 072231E8EFC35B0F2D736B8A3005F22E24EAC06A |
| SHA256: | 3202EAC5982B057C9FFAEB37D343C3F7F24962A8A6A3626EA7CCC553BE1BD570 |
| SSDEEP: | 196608:FEPHA98Rc2UgjHNOKI4q/z5ooOL49QasfGZ:EHE8nzHk/9ooQ4u1GZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
Process drops legitimate windows executable
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
Starts CMD.EXE for commands execution
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
There is functionality for taking screenshot (YARA)
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Loads Python modules
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Process drops python dynamic module
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
The process drops C-runtime libraries
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
Reads security settings of Internet Explorer
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Application launched itself
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
INFO
Checks supported languages
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
- identity_helper.exe (PID: 440)
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Reads the computer name
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
- identity_helper.exe (PID: 440)
The sample compiled with english language support
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
Create files in a temporary directory
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Checks operating system version
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
PyInstaller has been detected (YARA)
- Twitch Drops Miner (by DevilXD).exe (PID: 6788)
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Reads the software policy settings
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
- slui.exe (PID: 1964)
Reads the machine GUID from the registry
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Application launched itself
- msedge.exe (PID: 7104)
- msedge.exe (PID: 5980)
Drops encrypted JS script (Microsoft Script Encoder)
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
UPX packer has been detected
- Twitch Drops Miner (by DevilXD).exe (PID: 3556)
Reads Environment values
- identity_helper.exe (PID: 440)
Checks proxy server information
- slui.exe (PID: 1964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:24 05:27:49+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 174592 |
| InitializedDataSize: | 163840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd0d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
167
Monitored processes
29
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5920,i,11910055557343641452,12246528246784371871,262144 --variations-seed-version --mojo-platform-channel-handle=6116 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2368,i,11910055557343641452,12246528246784371871,262144 --variations-seed-version --mojo-platform-channel-handle=2308 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 856 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | Twitch Drops Miner (by DevilXD).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5128,i,11910055557343641452,12246528246784371871,262144 --variations-seed-version --mojo-platform-channel-handle=5152 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2240,i,11910055557343641452,12246528246784371871,262144 --variations-seed-version --mojo-platform-channel-handle=1428 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3556 | "C:\Users\admin\AppData\Local\Temp\Twitch Drops Miner (by DevilXD).exe" | C:\Users\admin\AppData\Local\Temp\Twitch Drops Miner (by DevilXD).exe | Twitch Drops Miner (by DevilXD).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5440,i,11910055557343641452,12246528246784371871,262144 --variations-seed-version --mojo-platform-channel-handle=5468 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6268,i,11910055557343641452,12246528246784371871,262144 --variations-seed-version --mojo-platform-channel-handle=6304 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
11 468
Read events
11 440
Write events
28
Delete events
0
Modification events
| (PID) Process: | (3556) Twitch Drops Miner (by DevilXD).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (3556) Twitch Drops Miner (by DevilXD).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3556) Twitch Drops Miner (by DevilXD).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3556) Twitch Drops Miner (by DevilXD).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5980) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5980) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
| (PID) Process: | (7104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7104) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7104) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 63F4EB2151992F00 | |||
Executable files
93
Suspicious files
256
Text files
995
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\Pythonwin\win32ui.pyd | executable | |
MD5:99F26E82BCCDF8E49024C4756383D6C4 | SHA256:0DBD89FD2B4C52915BF622DADC25A00D767236C7DE8D490089FECE5792BEEA86 | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\_hashlib.pyd | executable | |
MD5:659A5EFA39A45C204ADA71E1660A7226 | SHA256:B16C0CC3BAA67246D8F44138C6105D66538E54D0AFB999F446CAE58AC83EF078 | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\_overlapped.pyd | executable | |
MD5:F491399E85FF21AA74FF571F751C9ACE | SHA256:403B0567609CB2AA5D8FF8C992E10FAE9E3B86D7AA86CA4ACC6044821A49E36B | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\PIL\_webp.cp310-win_amd64.pyd | executable | |
MD5:C7819B69D617D9E116B170D1426A89CE | SHA256:4F47DD6132AEF5899FDB9042E3161AB6BB102106C2E1C25AF36695C677D52A1E | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\PIL\_imaging.cp310-win_amd64.pyd | executable | |
MD5:A5E6BADF6BA9A76415CDA535BE00FB96 | SHA256:BCEA3EEE4B96C36C1378C4707E29A8286BA6B3C1798752E9218FD05F2BA755E0 | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\PIL\_avif.cp310-win_amd64.pyd | executable | |
MD5:1E4CEAF4C50EDD0903B6711F10FC3604 | SHA256:C77B637F23B4C3AFB135AD5B40D09F756B66EF942F72E6CB45ACBB93604C909C | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\_elementtree.pyd | executable | |
MD5:2633985B870BBBB49E8F1F2897510DCD | SHA256:92D2DF299177BF53E899DD15037FABA591C219F4FD4A980212D394242FC687D1 | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\PIL\_imagingtk.cp310-win_amd64.pyd | executable | |
MD5:C66073671F45398E770F07FF93987E1B | SHA256:268D526FBF77755608C88F1E3595E796074D752452EB11470A7BF3C5F66F281A | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\_multiprocessing.pyd | executable | |
MD5:A77D9DD8AECE1F211E2949D54D299DD4 | SHA256:07B82738C674E58FEE4B11F259360C062D1DF22220A397434CF3A3771E52729E | |||
| 6788 | Twitch Drops Miner (by DevilXD).exe | C:\Users\admin\AppData\Local\Temp\_MEI67882\_bz2.pyd | executable | |
MD5:FBA120A94A072459011133DA3A989DB2 | SHA256:055A93C8B127DC840AC40CA70D4B0246AC88C9CDE1EF99267BBE904086E0B7D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
94
DNS requests
90
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5644 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7688 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
2400 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2400 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
7688 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3400 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:GIHFf_mzX8O-Ri73YIue9dIL3fWhgq8JSz-6ur9YqC8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4084 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5644 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5644 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.twitch.tv |
| whitelisted |
m.twitch.tv |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |